1. Introduction
DNA synthesis has changed rapidly in the past few decades[
1], opening new opportunities like synthetic biology[
2], alongside new challenges. The field of molecular biology has seen significant progress in optimizing genetic sequences[
3] Codon optimization exploits degeneracy in the genetic code to tailor DNA sequences for improved expression in heterologous hosts[
4,
5,
6]. The method adjusts synonymous codon frequencies to match host codon usage bias, thereby increasing protein yield and translational efficiency[
7,
8,
9,
10]. Such approaches underpin major applications in gene therapy, vaccine development, and industrial biotechnology, including mRNA vaccines and recombinant protein production systems.
Historically, codon optimization algorithms prioritize metrics such as the Codon Adaptation Index (CAI)[
11], GC content, and minimization of unfavorable mRNA secondary structure[
12]. Advances include deep learning models that capture sequential codon context for refined optimization[
13,
14,
15]. Despite these improvements, most tools remain insensitive to potential functional motifs introduced on the complementary strand, particularly those that could act as antisense promoters. We focus on
E. coli, since it is a well-studied model organism[
16,
17], just for the case study, but the same software tools and conclusions apply to all other organisms.
Promoter motifs such as the bacterial ‘−10’ element ‘TATAAT’ are critical regulatory elements for transcription initiation[
18]. When observed in reverse complement (‘ATTATA’)[
19], they may function as unintended antisense promoters. Although motif engineering has been considered in some codon design contexts, the explicit risk of inadvertently creating antisense promoters and other motifs has not yet been systematically characterized. Moreover, many free and commercialized codon optimization tools are widely used as is, although they do not always scan for many relevant motifs. These tools' typical users, the average biologist, are often naïve and tend to trust the output sequence blindly.
The convergence of synthetic biology and cyber-security has given rise to a new interdisciplinary domain: cyber-bio-security[
20,
21,
22,
23,
24]. Within this space, codon optimization emerges not only as a tool for improving protein expression but also as a potential vector for unintended regulatory behavior and malicious exploitation. As the capacity to synthesize and edit DNA becomes more accessible and codon optimization is increasingly performed using automated tools, the potential for errors or security loopholes grows. The rise of cyber-biosecurity highlights threats at the intersection of information security and biology. Synthetic DNA can encode harmful elements—not only biological agents but also computational payloads, like those used for SW storage[
25]. While most research focuses on software and hardware vulnerabilities, the prospect of intentional manipulation of biological regulatory elements via sequence design remains understudied. Another important factor is the flourishing of Artificial Intelligence (AI)[
9]. The usage of machine learning to detect anomalies in synthetic DNA can be very useful. By training classifiers on statistical properties of natural versus synthetic sequences, even subtle deviations introduced during optimization could be detected computationally. A key contribution of that work is the demonstration that synthetic DNA could be engineered to exploit vulnerabilities in bioinformatics software, including buffer overflows triggered during sequence parsing. Their proof-of-concept attack transformed a DNA sequence into a vehicle for remote code execution—blurring the line between biological and computational domains. From a methodological standpoint, their work reinforces the necessity of anomaly detection algorithms in bioinformatics pipelines.
At a broader conceptual level, Elgabry et al. [
22] framed synthetic biology as a potential enabler of novel forms of cybercrime. Their review presented a criminological perspective on technologies such as gene editing, bio-malware, and antisense-driven payloads, outlining scenarios where biological material could be used to circumvent security protocols or mislead forensic analysis. They emphasized the importance of developing preemptive security measures grounded in both biology and criminology. Beyond identifying threats, some researchers have explored how biological principles can inform computational defense mechanisms[
26]. They proposed a bio-inspired framework for intrusion detection in network security, in which digital data was encoded as amino acid sequences and analyzed using models adapted from molecular biology. Their approach leveraged the inherent pattern recognition capabilities of bioinformatics tools to enhance detection accuracy in cybersecurity contexts. Although not directly related to DNA manipulation, this methodological crossover is significant. It suggests that tools developed for motif detection and codon analysis in synthetic biology can be repurposed or adapted to other domains, and vice versa.
In this work, we address two questions: (i) Does codon optimization inadvertently generate antisense promoter motifs? (ii) Can such motifs be deliberately injected into coding sequences without altering the encoded protein? [
Figure 1] We present a computational framework that examines both biological and security implications of codon redesign, supported by quantitative data and analytical modeling.
We present various simulations performed using codon-optimization tools available online, both open-source and commercial. In addition, we tested and calculated the probability of various motifs in DNA sequences. Our delivery is an application that contains several testing options for customers, including comparing sequences between different optimization tools, searching for problematic motifs, and performing attempts to inject promoter motifs into the complementary strand without changing the original protein sequence.
2. Materials and Methods
2.1. The Promoter ‘-10’ Motif: An Example Used for our Proof of Concept (POC)
Promoters play a critical regulatory role in gene expression by controlling when, where, and to what extent a gene is transcribed. Promoters typically contain specific motifs [
17] recognized by transcriptional machinery. In bacteria, a promoter consists of:
The -10 Region: A sequence positioned ~10 nucleotides upstream, which is crucial for DNA unwinding and formation of the open transcription complex.
The -35 Region: A sequence located ~35 nucleotides upstream of the transcription start site, responsible for initial recognition by RNA polymerase sigma factor.
As a case study, we focus on the ‘-10’ motif for various reasons. Expanding the results to longer promoters and/or enhancers is straightforward.
2.2. Dataset Choice and Preprocessing
We compiled a dataset of 484,741 coding sequences from
Escherichia coli via the online database[
27]. We focused on
E. coli due to its well-characterized genome. Sequences shorter than 300 bp or containing ambiguous nucleotides were excluded. When focused on the classical ‘-10’ motif, we looked for Motif-free sequences and excluded those containing the reverse-complement motif, i.e., 'ATTATA'.
2.3. Codon Optimization Framework: Analyzing Popular Tools' Output Sequences
Codon optimization alters the codon usage of a gene to align with the preferred codons of the host organism [
28], thereby potentially improving protein production. Different amino acids have codon usage biases, so adjusting the gene's codons to match these biases can significantly improve expression efficiency. There are many types of optimization tools, and the algorithm by which each tool works is different. Some tools can only be used as a ‘black box’, meaning the customer cannot know what considerations were made in optimizing a protein for a specific organism. These ‘black box’ observations lead us to a limited set of conclusions since these tools often use random seeds, meaning the optimization results for a given protein vary with time. On the other hand, there are open-source tools. Our research utilized an open-source codon optimization. We used a custom Python-based tool named Codon Optimization QA. This tool incorporates codon usage tables for the model organism of choice and optimizes sequences based on a composite score including CAI, GC content, and synonymous codon distribution. Evaluation of codon optimization tools focused in this study on two optimization tools that have been selected for evaluation:
Codon Transformer[
15] – An open-source tool, which allows modifications to its original code if necessary.
Codon Optimization of Vector Builder[
29] – A proprietary tool with a closed-source interface, where the user inputs the protein to be optimized and specifies the target host organism.
A toy example we ran to compare these two tools is the expression of an insulin protein that the host organism is Homo sapiens[
30], aiming to evaluate the differences between the optimized DNA sequences for
E. coli produced by these two tools.
2.4. New Quality Assurance (QA) Open Source Software Tool for Codon Optimization
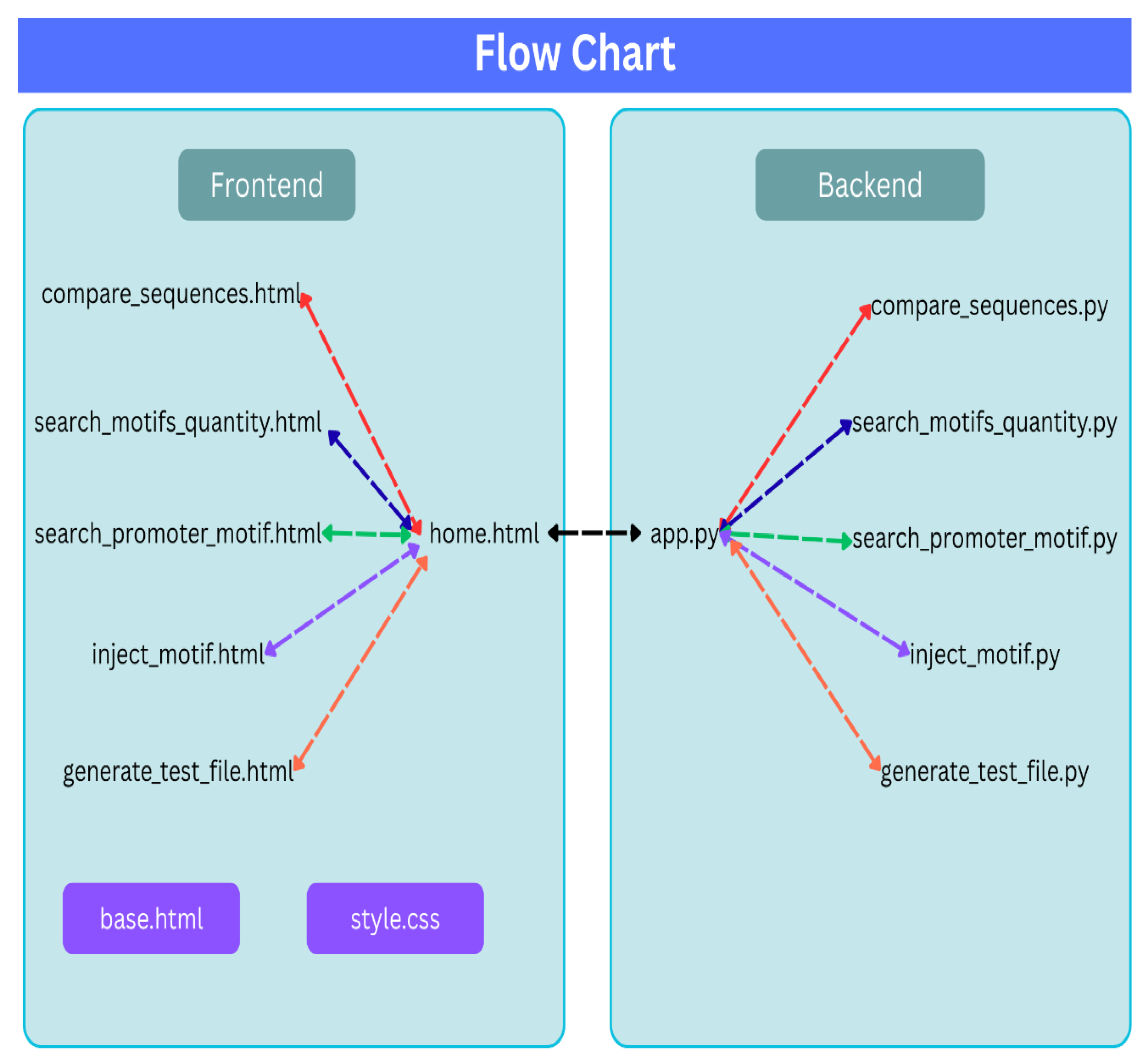
Our main contribution to the community is a new QA open source software tool, which has been developed for testing any synthetic DNA sequence that was produced by any codon optimizer application. During the research, tests and statistics were performed on various sequences. The tests can be performed by a script written in Python, consisting of two main parts, as drawn in
Figure 2 and explained below:
- (a)
Backend - This part includes the logic for the various tests, including:
- •
Manipulations on sequences.
- •
Software interface with optimization tools.
- •
Searching for promoter motif in different positions in sequences.
- •
Injection attempt of promoter motif in different positions in sequences.
- (b)
Frontend – This part presents the product to the client in the form of a Server that opens and displays the results on the WEB based on Hyper Text Markup Language (HTML) and Cascading Style Sheets (CSS).
There are two ways to access the Web application:
The open source described in the SI implements an application that can be accessed using the two methods described above.
Since it is an open source and we envision a design process that will continue as a collaborative effort, it is important to highlight the design principles. As shown in
Figure 2, the application is designed with the following emphasis:
Modular structure and division between backend and frontend.
For each option available on the home page of the Web, a separate Python script was written to enable a proper development and debugging process.
For convenience, the developer who wants to run the application will also be required to run only one script - "app.py", which is responsible for the integration and combination of all the scripts written in the project.
After running the application, you can access the local host URL on the Web:
http://127.0.0.1:5000/ . At this point, the application home page opens, which describes all existing functions that constitute the research results.
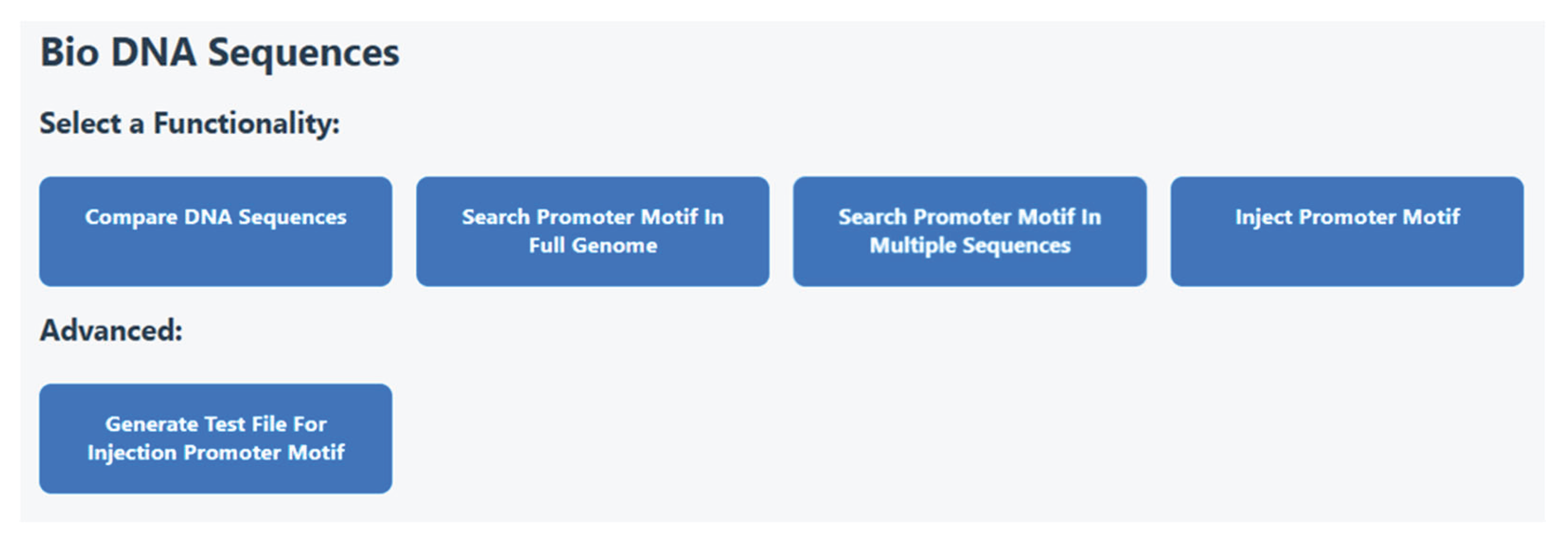
Figure 3 shows the home page that will be opened when there is a login to the application. The user can compare DNA sequences, can search motifs in the full genome or in specific sequences. In addition, a promoter can be injected into a sequence of choice. The advanced option is generating a test file for such injection.
We focus below on three main functions that can be considered the core components of the algorithm. The first one is motif detection. The second one is about silent motif injections. The third one is a function to secure your lab from unintended or malicious injections.
2.4.1. Antisense Promoter Motif Detection Algorithm
We use the motif detection function for two main purposes. Firstly, explore natural DNA sequences. It enables us to see if there is a natural evolutionary pressure against certain sequences that should be avoided for any reason. Secondly, scan optimized sequences and detect problematic motifs like anti-sense promoter. It enables us to test various optimization tools, prevent the usage of problematic sequences, and predict their impact in advance. As an example, we scanned for the 'ATTATA' motif using a sliding 6-mer window. Motif frequencies were calculated per sequence and across the genome to establish baseline occurrence. Our SW is available with some high-level description in the SI part.
2.4.2. Motif injection algorithm: Silent injection probability
This tool tests the option of injecting a promoter motif into DNA sequences without changing the original protein sequence. The output refers both to the percentage of success and to the success for each specific sequence. It analyzes in which sequences the injection attempt was successful, and in which cases and locations this happened for those sequences. Injection simulations were conducted using an algorithm that iteratively substitutes synonymous codons in a target window to produce a reverse complement matching the target motif. We evaluated all possible codon combinations that encode the same amino acid chain while forming 'ATTATA' on the antisense strand.
2.4.3. Motif Defense Module: A software Tool to Protect Your Lab
To detect potential injections, we implemented a screening function that analyzes whether synonymous substitutions could feasibly produce antisense motifs. This tool flags sequences at risk and estimates the number of substitutions required for successful injections. Based on the software provided, we can also suggest alternative sequences in the case of motif injection.
3. Results
We present the results of our algorithms for large-scale data we found on the website. These results reveal insights regarding natural sequences as well as demonstrate their efficiency in the case of synthetic sequences.
3.1. Natural Occurrence of Antisense Promoter Motifs and Injection Feasibility in Motif-Free Sequences
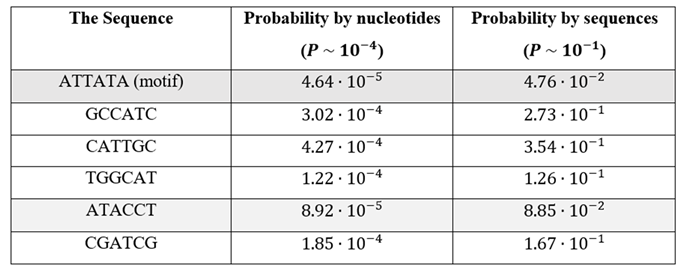
The first test focused on the natural occurrence of antisense promoters. It enables to identify for each motif the evolutionary pressure against each motif and can lead to a better understanding of codon bias in various organisms. Among the 484,741 coding sequences analyzed, 23,057 (4.76%) contained the reverse-complement motif 'ATTATA' (
Table 1). These sequences were excluded from subsequent injection tests. The motif's rarity supports the hypothesis that antisense promoters are naturally avoided in coding DNA. All other motifs in the table were detected much more often and very close to the theoretical random calculation. Please note that the motif ‘ATACCT’ can also lead to ‘-10’ motif, which is aligned with its low probability.
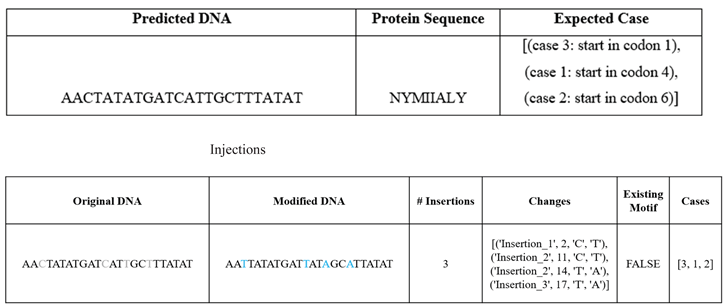
In the remaining 461,684 motif-free sequences, silent motif injection was achievable in 356,797 cases (77.28%) through synonymous substitutions. Three simple examples of such injections for SW validation are shown in
Table 2.
3.2. Comparison with Random k-Mer Frequencies
We calculate the probability of each injection using the following procedure, demonstrated here for a specific 6-mer motif. To determine the probability of finding the anti-sense promoter motif, ‘ATTATA’, within a randomly generated sequence composed of amino acid codons. The probability calculations are based on the following naïve assumptions:
To find the probability of obtaining the motif randomly, it is necessary to determine how this sequence can be formed across different codon alignments. There are three frame shifts to be analyzed:
Case 1: Two Complete Codons: ‘ATT’ – ‘ATA’
Case 2: Across Three Codons: ‘_ _ A’ – ‘TTA’ – ‘TA _’
Case 3: Across Three Codons: ‘_ AT’ – ‘TAT’ – ‘A _ _’
For each of these cases, it is required to calculate the probability based on amino acid distributions.
For case 1:
‘ATT’ is a codon for Ile (I). ‘ATA’ is also a codon for Isoleucine Ile (I). Because according to codon usage bias Ile has three codons (ATT, ATC, ATA), so the probability of selecting ‘ATT’ or ‘ATA’ is 1/3 each. Since we assume that the probability of getting each amino acid is equal, then the probability for each amino acid is 1/20. Therefore, the overall probability in this case will be calculated as follows:
For case 2:
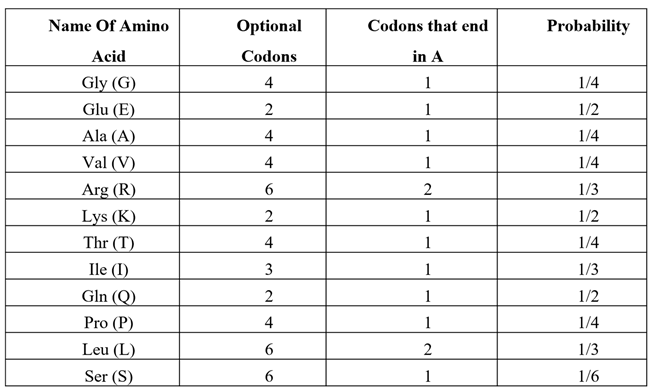
The amino acids with a codon ending with ‘A’ are listed in
Table 3. We can now calculate the probability of a codon ending with ‘A’:
Next probability to calculate is for ‘TTA’, which is a codon for Leu (L). Because according to codon usage bias Leu (L) has 6 codons, the probability of selecting ‘TTA’ is:
The amino acid that starts with ‘TA’ is only Tyr (Y). Since we assume that the probability of getting each amino acid is equal, then the probability will be:
Therefore, the overall probability in this case would be calculated as follows by considering the three probabilities found above:
For case 3:
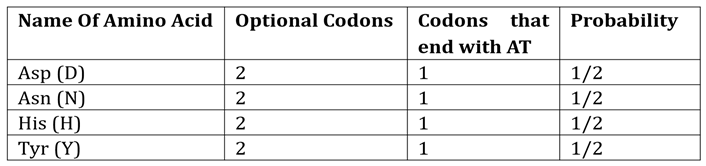
The amino acids that end with ‘AT’ are listed in
Table 4. Based on this table we calculate the probability:
The codon ‘TAT’ is for Tyr (Y). Since Leu (L) has 2 codons, the probability of selecting TAT is:
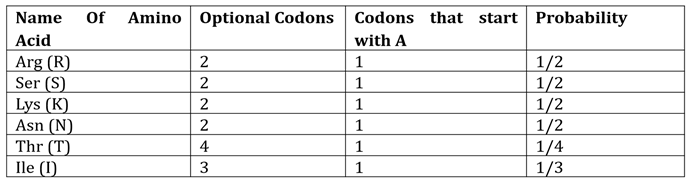
Lastly, the amino acids that start with ‘A’ are shown in
Table 5. It yields the following calculation:
Therefore, the overall probability in this case would be calculated as follows by considering the three probabilities found above:
The overall probability would be to test the union of the three cases:
For comparison, the theoretical probability of randomly finding a six-nucleotide sequence assuming an equal distribution of nucleotides is:
We can now revisit the results of
Table 1 for various 6-mers. Our control analysis using random 6-mers revealed that sequences like ‘GCCATC’ and ‘TGGCAT’ occurred at frequencies up to 3× higher than ‘ATTATA’ and very close to the random calculation. It confirms the underrepresentation of certain motifs and likely selective pressure against antisense promoter formation. The only random 6-mer that is relatively close to ‘ATTATA’ is ‘ATACCT’, which has only 2 times higher probability. This specific sequence seems to create a sequence close enough to ‘-10’ site promoter motif for
E.coli.
4. Discussion
Our findings reveal a significant and underrecognized vulnerability in codon optimization pipelines. While these tools aim to improve gene expression by refining synonymous codon usage, they unintentionally enable the creation of functional motifs on the antisense strand, such as bacterial promoter-like sequences. The widespread feasibility of silently injecting 'ATTATA' across coding regions, with no effect on protein output, underscores this threat.
Biological implications include unintended transcriptional activity, interference with native gene regulation, and synthetic noise in engineered circuits. From a cyber-biosecurity perspective, this opens the door to adversarial attacks where malicious motifs are embedded into synthetic constructs — a form of sequence-level 'backdoor' akin to steganography in software systems.
Current design tools often ignore complementary strand effects. A defense module that can be easily implemented based on our detection algorithm should be incorporated into bio foundry pipelines. Future work can easily expand to other motif types (e.g., riboswitches, terminators), eukaryotic systems, and automated prevention mechanisms using AI-guided codon selection.
We envision the open source code provided here becoming the basis of a much bigger set of QA tools that will be used by every lab before ordering DNA to decrease the probability of experimental failures. In addition, this set of tools can assist biologist understanding evolutionary pressure against certain motifs, leading to a better understanding of the genetic code.
5. Conclusions and Future Research Directions
Codon optimization has become indispensable in synthetic biology, yet our study highlights that it also presents hidden risks. Antisense promoter motifs such as 'ATTATA' can be introduced without altering protein sequence in over 77% of motif-free sequences. We propose a framework for motif detection, injection simulation, and defense screening strategy. Integrating such tools into standard codon optimization workflows is essential to safeguard biotechnology and basic biological research from inadvertent or malicious motif insertion.
Future research directions based on the open source code provided include the following:
Dive deeper into understanding the genetic code and various motifs with probabilities very different than random (both much higher and much lower).
Developing more QA tools to minimize the potential damage of synthetic DNA sequences that might encode surprises for biologists using these tools.
Identify other bio-informatics tools that should be examined within this framework to ensure their high quality and minimize their damage potential.
Supplementary Materials
The supporting information is described and can be downloaded. Details in the SI document.
Author Contributions
Conceptualization, Y.D.; methodology, all; software, E.C. and R.G.; validation, all; formal analysis, all; investigation, all; resources, all.; data curation, all; writing—original draft preparation, all; writing—review and editing, all; visualization, all; supervision, Y.D.; project administration, all; funding acquisition, Y.D. All authors have read and agreed to the published version of the manuscript.
Funding
This research was funded by the Israel Science Foundation (ISF), HIT research internal funds, the Ariel University–HIT Joint Research Grant, the Ministry of Innovation, Science and Technology (MOST), the Planning and Budgeting Committee (PBC/VATAT), the Directorate of Defense R&D (MAFAT), and Tevuna.
Data Availability Statement
The data supporting the findings of this study include publicly available protein and gene annotation data obtained from the UniProt database, as well as genomic sequences retrieved from the NCBI database. In addition, synthetic DNA sequences were generated programmatically for validation and testing purposes. No sensitive or personal data was used. All scripts and algorithms developed for data generation, motif insertion, and motif analysis were created by the authors as part of the research and are available from the corresponding author upon reasonable request. No additional datasets were generated.
Conflicts of Interest
The authors declare no conflicts of interest. The funders had no role in the design of the study; in the collection, analyses, or interpretation of data; in the writing of the manuscript; or in the decision to publish the results.
References
- Carlson, R. The changing economics of DNA synthesis. Nat Biotechnol 2009, 27, 1091–1094. [Google Scholar] [CrossRef] [PubMed]
- Cameron, DE; Bashor, CJ; Collins, JJ. A brief history of synthetic biology. Nat Rev Microbiol 2014, 12, 381–390. [Google Scholar] [CrossRef] [PubMed]
- Elgabry, M; Nesbeth, D; Johnson, SD. A Systematic Review of the Criminogenic Potential of Synthetic Biology and Routes to Future Crime Prevention. In Front Bioeng Biotechnol; Frontiers Media S.A, 2020. [Google Scholar] [CrossRef]
- Watts, A; Sankaranarayanan, S; Watts, A; Raipuria, RK. Optimizing protein expression in heterologous system: Strategies and tools. Meta Gene 2021, 29, 100899. [Google Scholar] [CrossRef]
- Condon, A; Thachuk, C. Efficient codon optimization with motif engineering. Journal of Discrete Algorithms 2012, 16, 104–112. [Google Scholar] [CrossRef]
- Angov, E. Codon usage: Nature’s roadmap to expression and folding of proteins. Biotechnol J 2011, 6, 650–659. [Google Scholar] [CrossRef]
- Tuller, T; Carmi, A; Vestsigian, K; Navon, S; Dorfan, Y; Zaborske, J; Pan, T; Dahan, O; Furman, I; Pilpel, Y. An Evolutionarily Conserved Mechanism for Controlling the Efficiency of Protein Translation. Cell 2010, 141, 344–354. [Google Scholar] [CrossRef]
- Goodman, DB; Church, GM; Kosuri, S. Causes and Effects of N-Terminal Codon Bias in Bacterial Genes. Science (1979) 2013, 342, 475–479. [Google Scholar] [CrossRef]
- Quax, TEF; Claassens, NJ; Söll, D; van der Oost, J. Codon Bias as a Means to Fine-Tune Gene Expression. Mol Cell 2015, 59, 149–161. [Google Scholar] [CrossRef]
- Plotkin, JB; Kudla, G. Synonymous but not the same: the causes and consequences of codon bias. Nat Rev Genet 2011, 12, 32–42. [Google Scholar] [CrossRef]
- Masłowska-Górnicz, A; van den Bosch, MRM; Saccenti, E; Suarez-Diez, M. A large-scale analysis of codon usage bias in 4868 bacterial genomes shows association of codon adaptation index with GC content, protein functional domains and bacterial phenotypes. Biochimica et Biophysica Acta (BBA) - Gene Regulatory Mechanisms 2022, 1865, 194826. [Google Scholar] [CrossRef]
- Mo, O; Zhang, Z; Cheng, X; Zhu, L; Zhang, K; Zhang, N; Li, J; Li, H; Fan, S; Li, X; Hao, P. mRNAdesigner: an integrated web server for optimizing mRNA design and protein translation in eukaryotes. Nucleic Acids Res 2025, 53, W415–W426. [Google Scholar] [CrossRef]
- Han, X; Shao, X; Liu, S; Shi, Z; Huang, R; Chu, H; Zhang, H; Wang, R; Li, H; Liao, X; Cheng, J; Jiang, H. DeepCodon: A deep learning codon-optimization model to enhance protein expression. BioDesign Research 2025, 7, 100042. [Google Scholar] [CrossRef]
- Karaşan, O; Şen, A; Tiryaki, B; Cicek, AE. A unifying network modeling approach for codon optimization. Bioinformatics 2022, 38, 3935–3941. [Google Scholar] [CrossRef]
- Fallahpour, A; Gureghian, V; Filion, GJ; Lindner, AB; Pandi, A. CodonTransformer: a multispecies codon optimizer using context-aware neural networks. Nat Commun 2025, 16, 3205. [Google Scholar] [CrossRef] [PubMed]
- Welch, M; Govindarajan, S; Ness, JE; Villalobos, A; Gurney, A; Minshull, J; Gustafsson, C. Design Parameters to Control Synthetic Gene Expression in Escherichia coli. PLoS One 2009, 4, e7002. [Google Scholar] [CrossRef]
- Browning, DF; Busby, SJW. The regulation of bacterial transcription initiation. Nat Rev Microbiol 2004, 2, 57–65. [Google Scholar] [CrossRef] [PubMed]
- Zhou, X; Feng, R; Ding, N; Cao, W; Liu, Y; Zhou, S; Deng, Y. Deep learning guided programmable design of Escherichia coli core promoters from sequence architecture to strength control. Nucleic Acids Res 2025, 53, gkaf863. [Google Scholar] [CrossRef] [PubMed]
- DJ, E; DA, M; PM, J; WJ, T. Widespread Antisense Transcription in Escherichia coli. mBio 2010, 1. [Google Scholar] [CrossRef]
- Anjum, N; Alshahrani, H; Shaikh, A; Mahreen-Ul-Hassan; Kiran, M; Raz, S; Alam, A. Cyber-Biosecurity Challenges in Next-Generation Sequencing: A Comprehensive Analysis of Emerging Threat Vectors. IEEE Access 2025, 13, 52006–52035. [Google Scholar] [CrossRef]
- Peccoud, J; Gallegos, JE; Murch, R; Buchholz, WG; Raman, S. Cyberbiosecurity: From Naive Trust to Risk Awareness. Trends Biotechnol 2018, 36, 4–7. [Google Scholar] [CrossRef]
- Elgabry, M; Nesbeth, D; Johnson, SD. A Systematic Review of the Criminogenic Potential of Synthetic Biology and Routes to Future Crime Prevention. In Front Bioeng Biotechnol Volume; 2020; pp. 8–2020. [Google Scholar]
- Puzis, R; Farbiash, D; Brodt, O; Elovici, Y; Greenbaum, D. Increased cyber-biosecurity for DNA synthesis. Nat Biotechnol 2020, 38, 1379–1381. [Google Scholar] [CrossRef] [PubMed]
- Murch, RS; So, WK; Buchholz, WG; Raman, S; Peccoud, J. Cyberbiosecurity: An Emerging New Discipline to Help Safeguard the Bioeconomy. In Front Bioeng Biotechnol Volume; 2018; pp. 6–2018. [Google Scholar]
- Doricchi, A; Platnich, CM; Gimpel, A; Horn, F; Earle, M; Lanzavecchia, G; Cortajarena, AL; Liz-Marzán, LM; Liu, N; Heckel, R; Grass, RN; Krahne, R; Keyser, UF; Garoli, D. Emerging Approaches to DNA Data Storage: Challenges and Prospects. ACS Nano 2022, 16, 17552–17571. [Google Scholar] [CrossRef] [PubMed]
- Ibaisi, TAL; Kuhn, S; Kaiiali, M; Kazim, M. Network Intrusion Detection Based on Amino Acid Sequence Structure Using Machine Learning. Electronics (Basel) 2023, 12. [Google Scholar] [CrossRef]
- DB source: Database. 6 February 2026. Available online: https://www.uniprot.org/uniprotkb?query=Escherichia+coli+%28strain+K12%29&facets=reviewed%3Atrue%2Cmodel_organism%3A83333.
- Chakravarty, PR. What is Codon Bias: Implications in Gene Cloning; 2023. [Google Scholar]
- VectorBuilder. Codon Optimization Tool. 2025. Available online: https://en.vectorbuilder.com/tool/codon-optimization.html.
- Consortium, U. UniPort entry P01308. 2025. Available online: https://rest.uniprot.org/uniprotkb/P01308.fasta.
|
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).