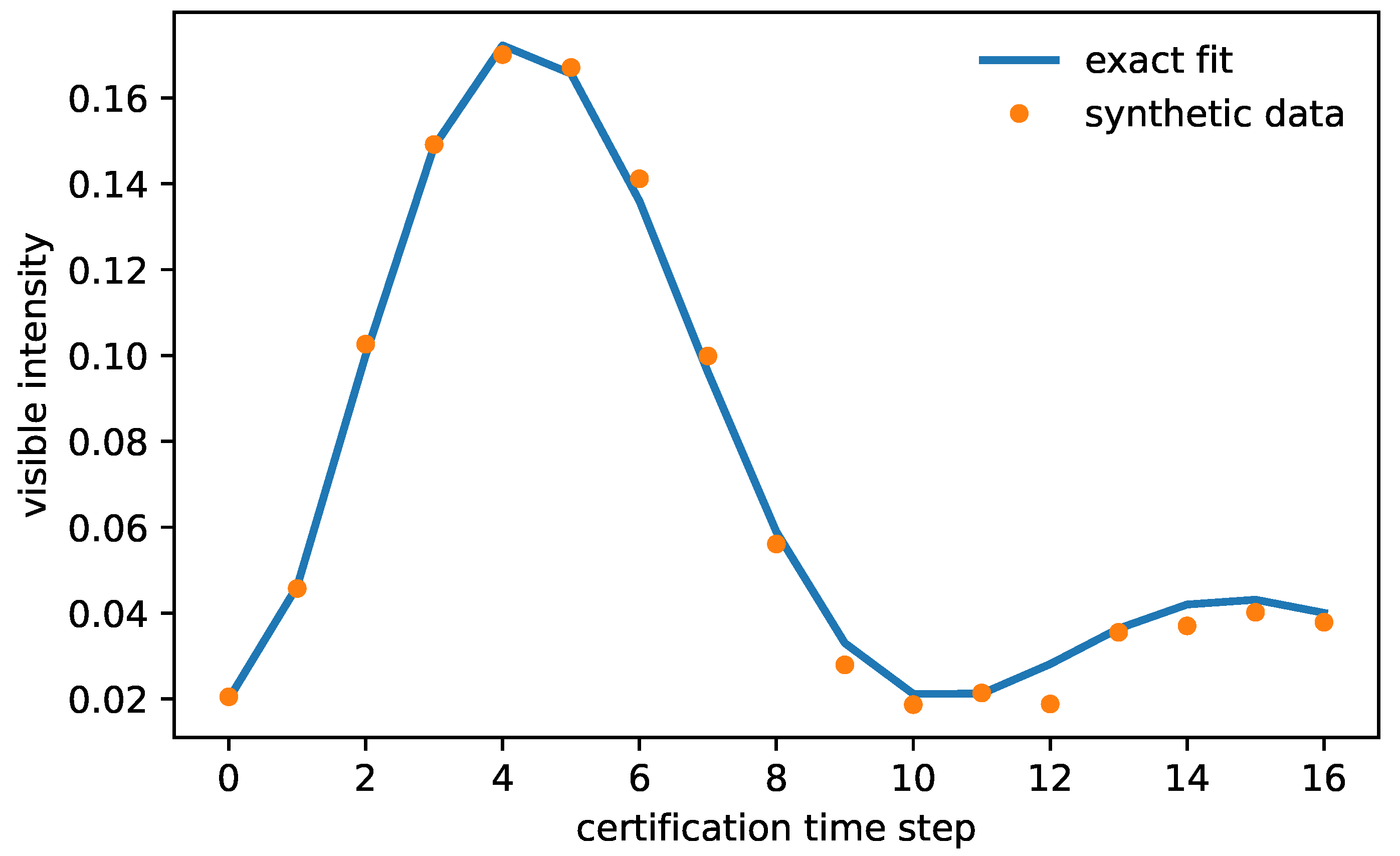
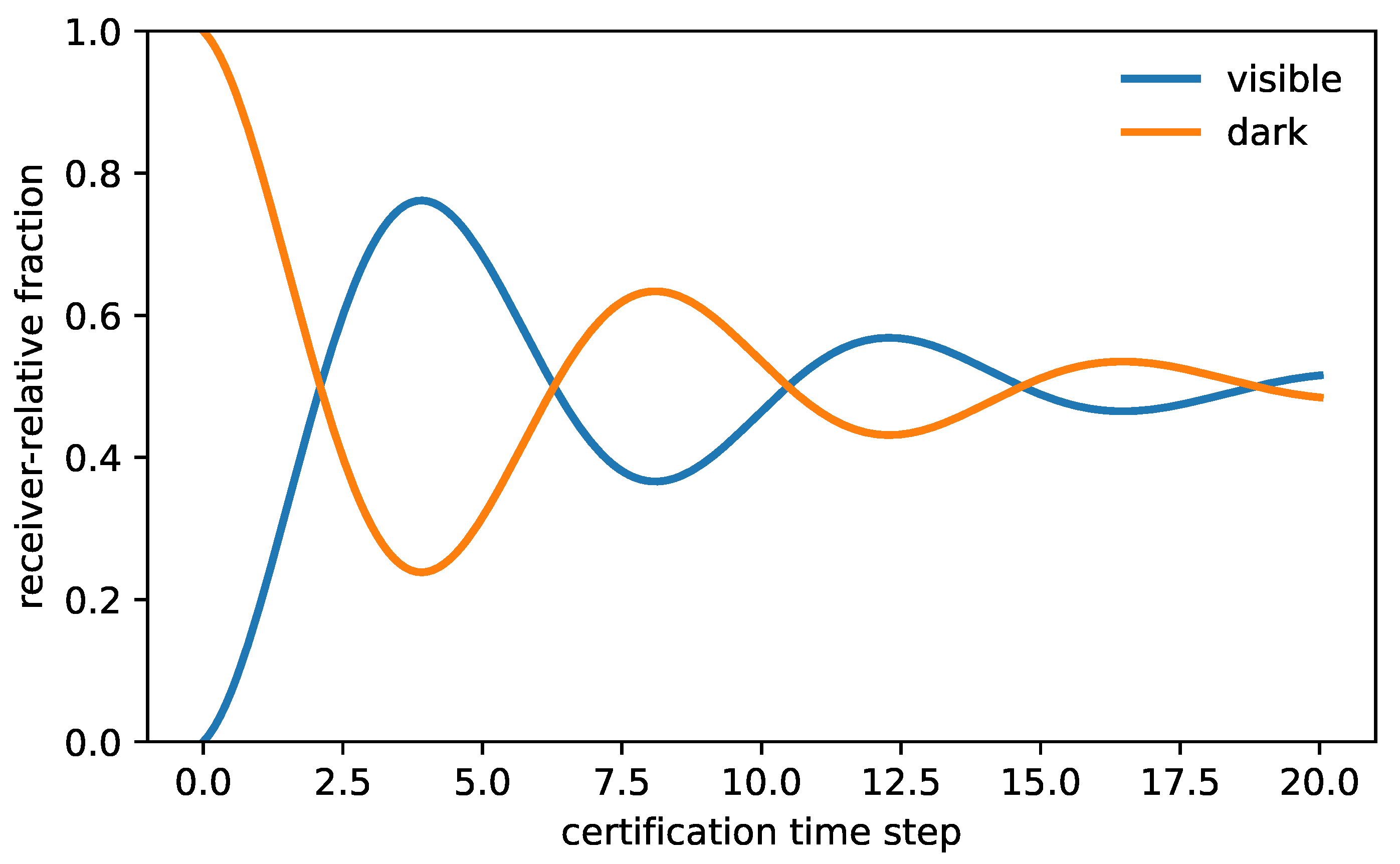
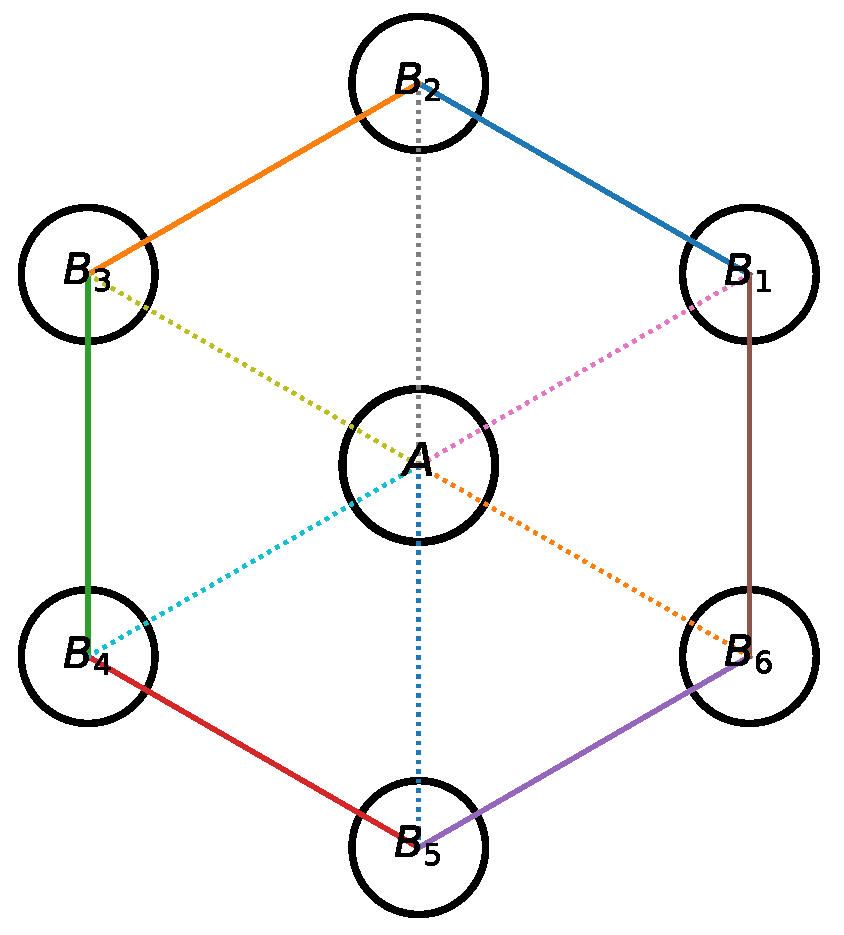
The benchmark becomes scientifically useful only when its observables are explicit and its rejection tests are hard. The reproducibility bundle included with this submission is a synthetic stress test of the inverse pipeline, not an external physics dataset. Within that numerical design the observable stack includes cell-resolved visible intensities, total intensities, mode gaps, decay rates, and profile-likelihood diagnostics for the five parameters.
Table 2.
Parameter recovery for the bundled reproducible synthetic benchmark. These numbers document internal identifiability and inversion stability on a controlled numerical design; they are not presented as experimental evidence. The full-model fit gives with 595 degrees of freedom, corresponding to .
| Parameter |
Planted value |
Fitted value |
Std. error |
Absolute error |
|
0.9500 |
0.9487 |
0.0194 |
0.0013 |
|
0.3000 |
0.2994 |
0.0091 |
0.0006 |
|
0.3600 |
0.3852 |
0.0569 |
0.0252 |
|
0.2700 |
0.2689 |
0.0045 |
0.0011 |
|
m
|
0.1800 |
0.1713 |
0.0362 |
0.0087 |
Branchwise rest-gap reconstruction and what it does not determine
For
, Equation (
79) reduces at leading order to
What is derived here is the branchwise reconstruction map together with the protocol required to measure . What is not derived is a species assignment for that branch. In particular, the present closure does not derive electron, muon, tau, proton, or dark-matter masses from foundational QICT or from receiver-side linear data alone; Proposition 20 excludes such a claim without additional microscopic representation data and branch-identification input.
Proposition 12 (Scope of the reduced-rest-gap mass law)
. Equation (93) determines a rest mass only after four additional pieces of data have been fixed: an isolated audited branch, a calibrated effective front speed, a validated small-signal regime, and an independent microscopic identification of the branch whose mass is being quoted. Without those extra inputs the formula defines a reconstruction map, not a species-level numerical prediction.
Proof. Theorem 14 gives the reconstruction formula once is measured for an isolated branch. Proposition 20 shows that absolute species assignments are not identifiable from the explicit receiver-side linear observable stack alone. The remaining ingredients enter operationally through Proposition 18 and Theorem 23, which require front-speed calibration, branch isolation, and small-signal control before the reconstructed can be interpreted physically. □
Proposition 13 (Common-contour no-go statement for species masses)
. Let denote the common audited contour data of the receiver-side closure: six contour cells, three opposite pairs, the declared ring-link groups, and the spoke-sector mediator splitting. If a proposed species mass law had the form
with no branch-specific input, then all isolated audited branches would carry the same mass. Therefore any extension that assigns distinct masses to different branches must depend on additional branch-specific topological or representation-theoretic data beyond the common contour topology alone.
Proof. The datum
is, by definition, shared by every branch living on the same audited contour. The right-hand side of Equation (
94) is therefore independent of the branch label
a . Hence
for every pair of branches
, contradicting the possibility of distinct species masses. Distinct branch masses therefore require additional branch-specific data not contained in the common contour invariants. □
Theorem 17 (Primitive-scale rigidity of the lifted ladder)
. Assume Assumption A1 for a connected set of elementary branches containing a primitive reference branch with . Suppose the same dataset also admitted a second description of the same measured reduced rest-gap times of the form
and for every branch in the connected set,
In particular, once the total extraction uncertainty drops below the half-integer separation scale, the primitive scale and all integer cores are unique.
Proof. Apply the lifted representation to the reference branch
. Because both descriptions set the primitive core equal to one, the measured quantity
gives
which is the first claim. Substituting this relation into the two descriptions for a general branch
a yields
Expanding the right-hand side to first order gives
, which is equivalent to (
97). If the total error is
, the nearest-integer uniqueness theorem forces
for every branch. □
Definition 4 (Branchwise topological or representation index)
. A branchwise topological or representation index is a map
from admissible branch-specific microscopic lift data to positive integers. The symbol is intentionally abstract: it may encode, for example, a finite covering degree, a winding sector, a twisted holonomy class, a Fredholm- or Dirac-type index, or any equivalent microscopic representation datum that is invisible to the common receiver-accessible linear stack but branch-specific enough to distinguish isolated audited branches.
Assumption A1 (Optional branchwise topological-lift postulate)
. The branchwise reconstruction law of Theorem 14 is now supplemented by one additional closure-level postulate. There exists a maximal elementary reduced rest-gap time realized by the lightest elementary audited branch, together with a branchwise index map of Definition 4, such that every elementary isolated audited branch satisfies
Define the associated elementary mass scale by
This postulate is not claimed as a theorem of foundational QICT or of the receiver-accessible linear sector by itself. It is an additional closure rule whose consequences can nevertheless be falsified sharply.
Theorem 18 (Optional branchwise topological-lift mass law and dressed integer core)
. Assume Assumption A1. Then every elementary isolated audited branch obeys the exact dressed core formula
where inherits exactly the controlled damping, threshold, and lattice corrections of Theorem 14. Expanding for gives
In particular, at leading order in the audited weak-damping, small-threshold, and weak-dressing regime,
Thus the integer is the branchwise topological core label, while the observable noninteger offset is carried by the controlled dressing together with the already existing audited corrections .
Proof. Substituting Equation (
99) into the leading term of Theorem 14 gives
The remainder terms in Theorem 14 are unaffected by this substitution, so they collect into the branch-dependent correction
. Equation (
102) follows from the geometric expansion
. □
Corollary 12 (Discrete ratio law and primitive-reference integer test)
. For any two elementary isolated branches a and b satisfying Assumption A1, one has
If is an elementary reference branch with primitive core label , then the estimator
is near the integer for every other elementary branch, with the residual noninteger drift controlled by together with the same audited extraction corrections as before. Failure of stable near-integer behavior after successful distance collapse and amplitude collapse falsifies the quantized extension, even if the underlying explicit linear closure remains viable.
Proof. Equation (
104) follows by dividing Equation (
101) for two branches and using Equation (
99). The second statement is the special case
, for which Equation (
104) gives
up to the same audited corrections as before. The statement about falsifiability is immediate: if the same branch does not admit a stable near-integer label under the controlled extraction protocol of Proposition 18 and Theorem 23, then Assumption A1 fails even though the audited inverse problem itself may still be correct. □
Theorem 19 (Nearest-integer identifiability from a primitive reference)
. Assume Assumption A1 and let be a primitive elementary reference branch with . Then the estimator (105) obeys
where is of the same controlled weak-damping, threshold, amplitude, and lattice order that enters Theorem 14. In particular, if the total extraction error satisfies
then the nearest integer to is unique and equals the core label .
Proof. Starting from Equation (
105) and using Equation (
99) with
gives
Expanding
yields Equation (
106). The uniqueness statement follows because open intervals of radius
centered at distinct integers are disjoint. □
Proposition 14 (Cross-platform integer-core compatibility test)
. Assume a primitive reference branch with , and let denote the estimator (105) extracted for branch a on platform p with Gaussian uncertainty . For any candidate integer , define
Under the lifted extension and after successful collapse diagnostics, the correct integer core should make statistically ordinary, whereas statistically significant excess for every nearby integer falsifies the lifted extension for that branch.
Proof. If the lifted extension is correct for branch
a , then each platform measures the same integer core
up to the dressed offsets and the controlled audited extraction corrections summarized in Theorem 19. Once those corrections are incorporated into the reported Gaussian uncertainties, the residuals
are mean-zero fluctuations and the weighted quadratic form (
108) is the standard compatibility statistic for one shared discrete label. If no nearby integer yields an ordinary value of
, then no platform-independent integer core is compatible with the data. □
Proposition 15 (Elementary/composite diagnostic relative to the ladder). Within the quantized extension, a branch may be treated as elementary only if the same integer core label is stable under threshold variation, amplitude variation, and platform transfer after front-delay subtraction. A composite sector need not admit such a single integer core because its outer size scale and its inverse rest-gap length are distinct observables by Proposition 11; a short-distance core may obey the branchwise gap law while the composite radius remains parametrically larger.
Proof. If a branch is elementary in the sense of Assumption A1, then Equations (
99) and (
105) assign it one integer core
independently of the particular admissible threshold or amplitude used in the audited extraction. The collapse theorem guarantees that the extracted
is branch-specific and platform-independent to leading order, so the same must hold for
. By contrast, Proposition 11 proves that composite size data and inverse rest-gap data are distinct observables. A composite branch can therefore possess one short-distance gap scale without being exhausted by a single outer-radius or form-factor scale, which is exactly why the integer ladder is a sharper candidate diagnostic for elementary branches than for composite ones. □
Proposition 16 (Illustrative dressed integer cores for the metrological sample)
. Take the electron branch only as a metrological reference, so that and . Then the externally known conversion sample is consistent with the dressed-core decomposition
These values are illustrative dressed offsets, not foundational predictions.
Proof. For a chosen integer core
, solve Equation (
101) at leading audited order for the dressing variable:
. Taking
and the nearest integers
gives the quoted numbers directly from the metrological conversion sample. □
Table 3.
Illustrative dressed integer-core check for the metrological conversion sample obtained by taking the electron branch as the reference branch, so that and . The integers 207, 3477, and 1836 are treated only as candidate branchwise core labels, while the small noninteger residuals are absorbed into the dressed offsets . The exercise is numerically striking but remains outside the theorem chain because the input masses are external.
Table 3.
Illustrative dressed integer-core check for the metrological conversion sample obtained by taking the electron branch as the reference branch, so that and . The integers 207, 3477, and 1836 are treated only as candidate branchwise core labels, while the small noninteger residuals are absorbed into the dressed offsets . The exercise is numerically striking but remains outside the theorem chain because the input masses are external.
| Branch relative to e |
|
core integer
|
[MeV] |
|
relative mismatch |
|
206.7683 |
207 |
105.7768 |
|
|
|
3477.2283 |
3477 |
1776.7434 |
|
|
| proton-like core |
1836.1527 |
1836 |
938.1941 |
|
|
The table above should therefore be read strictly as a postdictive consistency check on the optional topological-lift extension, not as foundational evidence for the observed lepton or baryon spectrum. Its scientific value is diagnostic rather than confirmatory: it shows what an eventual species-resolved experimental campaign would have to confirm or reject. In particular, the quantized extension makes six additional predictions beyond the core explicit closure: stable integer core labels under the distance-collapse and amplitude-collapse protocol, primitive-reference estimators that become uniquely identifiable once the half-integer criterion (
107) is satisfied, statistically ordinary cross-platform compatibility scores
for one and only one nearby integer, small dressed offsets rather than uncontrolled noninteger drift, a clean separation between integer-stable elementary branches and composite sectors with additional outer-size information, and failure of the extension whenever no common
organizes the extracted reduced rest-gap times.
Theorem 20 (Quantized-lift external signature stack)
. Assume Assumption A1 and successful audited front-delay subtraction. Then the lifted extension predicts the following four quantitative external signatures for every elementary branch a: (i) primitive-reference ratio rigidity,
where collects the controlled dressing and audited extraction corrections; (ii) threshold and amplitude stability, meaning that the estimator changes only at the same controlled order under admissible threshold and amplitude variations; (iii) cross-platform integer compatibility, meaning that one and only one nearby integer yields an ordinary value of once the quoted uncertainties are used; and (iv) ratio closure,
for every pair of elementary branches . A statistically significant violation of any one of these signatures rejects the lifted extension even if the explicit receiver-side linear closure itself remains viable.
Proof. Item (i) is exactly Corollary 12 specialized to a primitive reference branch. Item (ii) combines Corollary 12 with the collapse theorem for the reduced rest-gap extraction. Item (iii) is Proposition 14. Item (iv) is the pairwise ratio law of Corollary 12. The final falsification statement is immediate: each item is a necessary consequence of the lifted extension, so a statistically significant failure of any one of them rules out that extension while leaving the weaker explicit closure untouched. □
Assumption 2 (Optional charge-preserving family-tower postulate)
. Fix one conserved audited charge sector of the lifted extension. Assume that there exists a finite ordered list of isolated elementary branches
sharing the same conserved audited charge data , the same primitive scale , and strictly increasing core labels
Assume further that the first three such branches below the first compositeness threshold exhaust the elementary family content of that charge sector.
Theorem 21 (Conditional family-level species assignment from ordered integer cores)
. Assume Assumptions A1 and A2. Then the elementary branches in the sector admit a unique closure-level assignment to the labels electron-like, muon-like, and tau-like: they are precisely the first, second, and third elements of the ordered family tower, equivalently the branches with the three smallest core labels and therefore the three smallest reconstructed masses in that sector. Moreover, if the primitive branch is chosen as the reference branch and the estimators of and satisfy the half-integer criterion around integers and , then
and the assignment is unique inside the lifted extension.
Proof. Assumption A2 supplies a strictly ordered elementary tower in one fixed conserved charge sector. By Theorem 18, the leading reconstructed mass is monotone in the core label
up to the controlled dressed and audited corrections. Therefore the first three branches of the tower are unambiguously the lightest three elementary branches in that sector, and no alternative assignment preserves both the order in
and the common charge data. If the half-integer criterion of Theorem 19 identifies
and
uniquely with nearby integers
and
, then Corollary 12 yields Equation (
113). The uniqueness statement follows because a different assignment would either violate the strict order
or assign the same branch two distinct nearest integers. □
Proposition 17 (Conditional proton-like composite-core identification). Assume Assumption A1. Let C be a branch carrying one stable short-distance core label under the primitive-reference protocol, but also an independent outer size scale satisfying over the same admissible regime. Then C cannot be elementary in the sense of Assumption A2; it is necessarily composite in the closure-level sense of Proposition 15. If, in addition, C belongs to a baryonic audited charge sector and the nearest-integer criterion identifies uniquely with an integer , then the closure-level label proton-like composite core is unique for that short-distance branch.
Proof. Proposition 11 proves that the inverse rest-gap length and the outer size radius are distinct observables in general. A branch with one stable short-distance core but a parametrically larger independent outer size therefore cannot be exhausted by a single elementary gap label, which is exactly the compositeness diagnostic of Proposition 15. The final statement is purely classificatory: once the conserved audited charge sector is baryonic and the short-distance core is uniquely identified by the half-integer criterion, no second branch in the same regime can carry the same closure-level proton-like core label without violating the uniqueness of the integer-core assignment. □
Theorem 22 (Joint external exclusion of common-topology-only alternatives). Consider any alternative in which branch masses and branch classifications depend only on the common contour topology and on continuous extraction corrections, with no branch-specific integer lift data. Such an alternative cannot account for the simultaneous observation of all four signatures:
-
(i)
two or more half-integer-resolved stable integer cores in one fixed charge sector,
-
(ii)
primitive-reference ratio closure for those branches,
-
(iii)
cross-platform compatibility for the same integer cores, and
-
(iv)
a branch with one stable short-distance core together with an independent outer size scale .
Therefore the conjunction of these four observations would exclude any common-topology-only explanation and would single out the need for branch-specific lift data of the type introduced in Definition 4.
Proof. The no-go statement preceding Definition 4 already shows that dependence on common contour topology alone cannot distinguish species masses: every branch would inherit the same value of any mass functional built only from the common contour invariants. Hence item (i) is already impossible in a common-topology-only theory once two distinct stable integer cores are resolved. If one nevertheless tried to attribute the observed integers to continuous extraction corrections alone, items (ii) and (iii) would fail generically because a continuous branch parameter carries no platform-independent discrete label whose ratios close to exact integers after primitive normalization. Finally, item (iv) is excluded by Proposition 11: a theory with no branch-specific lift data and no elementary/composite split has no mechanism to separate a short-distance core scale from an independent outer composite radius. Thus the simultaneous validity of (i)–(iv) forces the introduction of branch-specific microscopic data beyond the common contour topology. □
Proposition 18 (Operational extraction protocol for reduced rest-gap time). Assume that an isolated branch a can be prepared, that the effective front speed can be calibrated from ballistic arrival data, and that a channel-selective receiver records the branch response at distance L. Then the reduced rest-gap time is obtained operationally by
-
1.
measuring the front delay from the earliest receiver arrivals at several L,
-
2.
choosing a threshold η below the first response peak and extracting the threshold-crossing time ,
-
3.
estimating the local response amplitude from the same branch,
-
4.
-
5.
and extrapolating to the weak-damping, small-threshold regime.
so the rest mass follows from Equation (93) after calibrating .
Proof. This is a direct operational restatement of Theorem 13. The only additional ingredient is the explicit front-delay subtraction, which isolates the local branch oscillation from the ballistic travel time. Once that subtraction is performed, the threshold-crossing equation reduces to the same weak-damping expansion used in the proof of Theorem 13. □
Theorem 23 (Distance-collapse and amplitude-collapse diagnostics)
. Under the assumptions of Proposition 18 and the audited small-signal condition of Proposition 21, the estimator extracted from a preparation of amplitude ε at certified distance L obeys
Hence, after front-delay subtraction, the inferred reduced rest-gap time must be distance-independent and amplitude-independent to leading order. Any statistically significant residual dependence on L or on ε falsifies at least one of branch isolation, front-speed calibration, or the audited small-signal closure.
Proof. Proposition 18 gives the weak-damping and small-threshold expansion at fixed audited branch. Proposition 21 shows that finite-amplitude corrections enter the receiver observables only at in the audited small-signal regime. Combining the two statements yields the claimed expansion and the collapse criterion. □
Two concrete realization templates already fit this protocol without changing the mathematics. In a coupled-resonator, qubit-ring, or cold-atom contour implementation, the certified distance L is a physical arc length or hop count, the two internal channels are encoded in internal states, and branch spectroscopy is performed by mode-selective driving and readout. In a time-multiplexed or waveguide realization, the same quantities are synthetic: L is a step distance, internal channels are polarization or path labels, and branch spectroscopy is obtained from Floquet or quasienergy resolution. In both cases the decisive observable is the same collapse test, not the engineering details.
Proposition 19 (Local identifiability on the benchmark design)
. For the observable design used in the reproducibility bundle, the finite-difference Jacobian of the residual map at the fitted point has strictly positive singular values
with condition number . Therefore the observable map is locally full rank and the five benchmark parameters are locally identifiable on the chosen synthetic design.
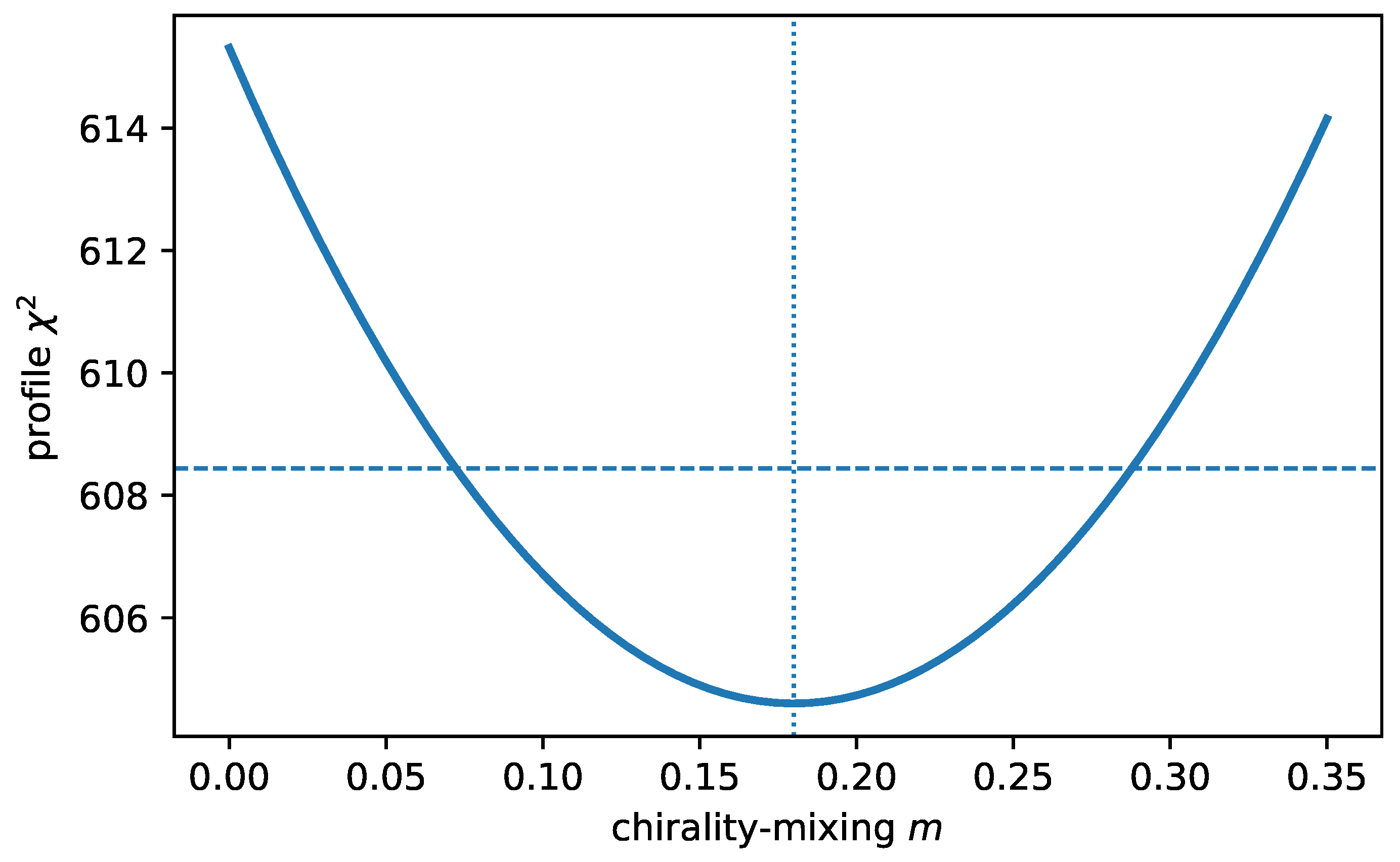
Figure 4.
Profile-likelihood scan for the chirality-mixing parameter m . The minimum occurs near the planted value and the single-parameter threshold is crossed well before on the bundled synthetic design.
Figure 4.
Profile-likelihood scan for the chirality-mixing parameter m . The minimum occurs near the planted value and the single-parameter threshold is crossed well before on the bundled synthetic design.
The nested-model diagnostics go beyond goodness of fit alone. On the present synthetic design,
The full model is therefore statistically preferred over both the no-mixing and no-drift restrictions on this design.
Corollary 13 (Quantitative falsification criteria). The explicit closure is falsified if any of the following occurs.
-
1.
Contractivity failure. If for any of the six momenta, the dissipative audited benchmark is rejected.
-
2.
Short-time curvature failure. A right-handed initial state must satisfy the universal onset law (55). A statistically significant linear onset falsifies the receiver map.
-
3.
Spectral inversion failure. If the extracted modal data violate (58)–(62), the five-parameter benchmark is not self-consistent.
-
4.
Drift-sign inconsistency. The sign of ν fixes the handedness of the cell asymmetry. Datasets requiring both signs simultaneously reject the benchmark.
-
5.
Dark-invariance failure. In the limit , a right-handed excitation must remain invisible to the left-handed receiver up to the noise floor.
-
6.
Nested-model failure. If the likelihood-ratio diagnostics do not improve materially over the restrictions or on the claimed sensitivity regime, no weak-chiral inference should be asserted.
-
7.
Hydrodynamic-coefficient failure. The fitted low-k spectrum must yield in the domain claimed to be diffusive. Failure rejects the long-wavelength interpretation.
These criteria connect the analytic closure to measurement. In particular, they turn spectral reconstruction into an explicit experimental and numerical protocol.
Theorem 24 (Operational universality of the explicit linear sector). Consider two explicit closures and whose receiver-accessible linear dynamics on the certified contour admit generators of the class analyzed above. Suppose that they have the same audited spectral invariants and therefore the same reconstructed tuple , together with the same low-wavelength coefficients . Then every receiver-accessible linear observable built from the certified benchmark sector agrees in the two closures up to the same order at which the long-wavelength truncation is taken. In that sense the audited framework defines an operational universality class.
Proof. By the spectral reconstruction theorem, identical audited spectral invariants imply identical reconstructed parameters . The exact propagator, visible/receiver-dark fractions, and nested-model likelihoods derived in the benchmark sector are functions of those parameters alone, so they coincide in the two closures. In the long-wavelength regime, the reduced envelope dynamics depends only on to the truncation order used in its derivation. Matching those coefficients therefore makes the coarse receiver observables coincide to that same order. Hence microscopic implementation details that do not modify the audited spectra and hydrodynamic coefficients are operationally invisible to the certified receiver. □
Corollary 14 (Physical content of the explicit linear sector). Within the explicit linear sector, the closure specifies a local exchange law, a symmetry-breaking mediator spectrum, an exact inverse problem, and a universality class of receiver observables. These ingredients are sufficient to make the framework predictive at the level of explicit receiver observables.
Proposition 20 (Receiver-side non-identifiability boundary). Let denote the full explicit receiver-accessible linear observable stack used in this paper: exact propagators, visible/receiver-dark fractions, modal gaps, decay rates, hydrodynamic coefficients, reduced rest-gap times, and all derived inversion formulas. If two microscopic completions induce the same certified contour generator and the same receiver map on the audited sector, then every observable in agrees exactly in the two completions. Therefore anomaly coefficients, family multiplicities, flavor textures, mixing matrices, and absolute mass values are not identifiable from alone; they require additional microscopic representation data beyond the explicit receiver-side linear sector.
Proof. Every observable entering is constructed explicitly from the audited generator and receiver map: the exact propagator from , the spectral invariants from the eigenvalues of , the hydrodynamic coefficients from the small- k expansion of those eigenvalues, and the visible/receiver-dark fractions from composition with the receiver projector. If two microscopic completions leave and the receiver map unchanged on the audited sector, then all of these functionals coincide identically. Quantities that depend on additional microscopic representation content but do not feed back into the audited generator cannot therefore be reconstructed from . □
Proposition 21 (Small-signal stability against weak nonlinearities)
. Let the certified receiver dynamics near the audited background obey
with G in the explicit linear class and initial preparation norm . Then for fixed times ,
and every receiver observable linear in the one-particle amplitudes, as well as every spectral quantity extracted from the linear response, agrees with the explicit linear closure up to corrections.
Proof.
For sufficiently small initial data, local well-posedness and Gronwall control imply on fixed time intervals, hence the integral term is . Therefore the linear propagator controls the entire small-signal response to leading order. Receiver observables extracted from linear response inherit the same error order. □
The restriction to the linear sector should therefore be read as a controlled small-signal statement rather than as a claim that all physically relevant QICT dynamics is linear. Strong nonlinear regimes, dense scattering, or black-hole-like sectors may well require additional closure data, but they cannot modify the leading explicit signatures without first appearing as explicit amplitude dependence or distance-collapse failure in the sense of Proposition 21 and Theorem 23. In that sense the nonlinear limitation is itself experimentally monitored rather than silently ignored.