Submitted:
03 March 2026
Posted:
04 March 2026
Read the latest preprint version here
Abstract
Keywords:
1. Introduction
II. Why Linux Seems Attractive for Avionics
A. Engineering Richness and Rapid Development
B. Advances in Real-Time Responsiveness
C. Cost, Reuse, and Availability of Expertise
III. What Airworthiness Really Requires
IV. Core Limitations of Linux in Safety-Critical Avionics
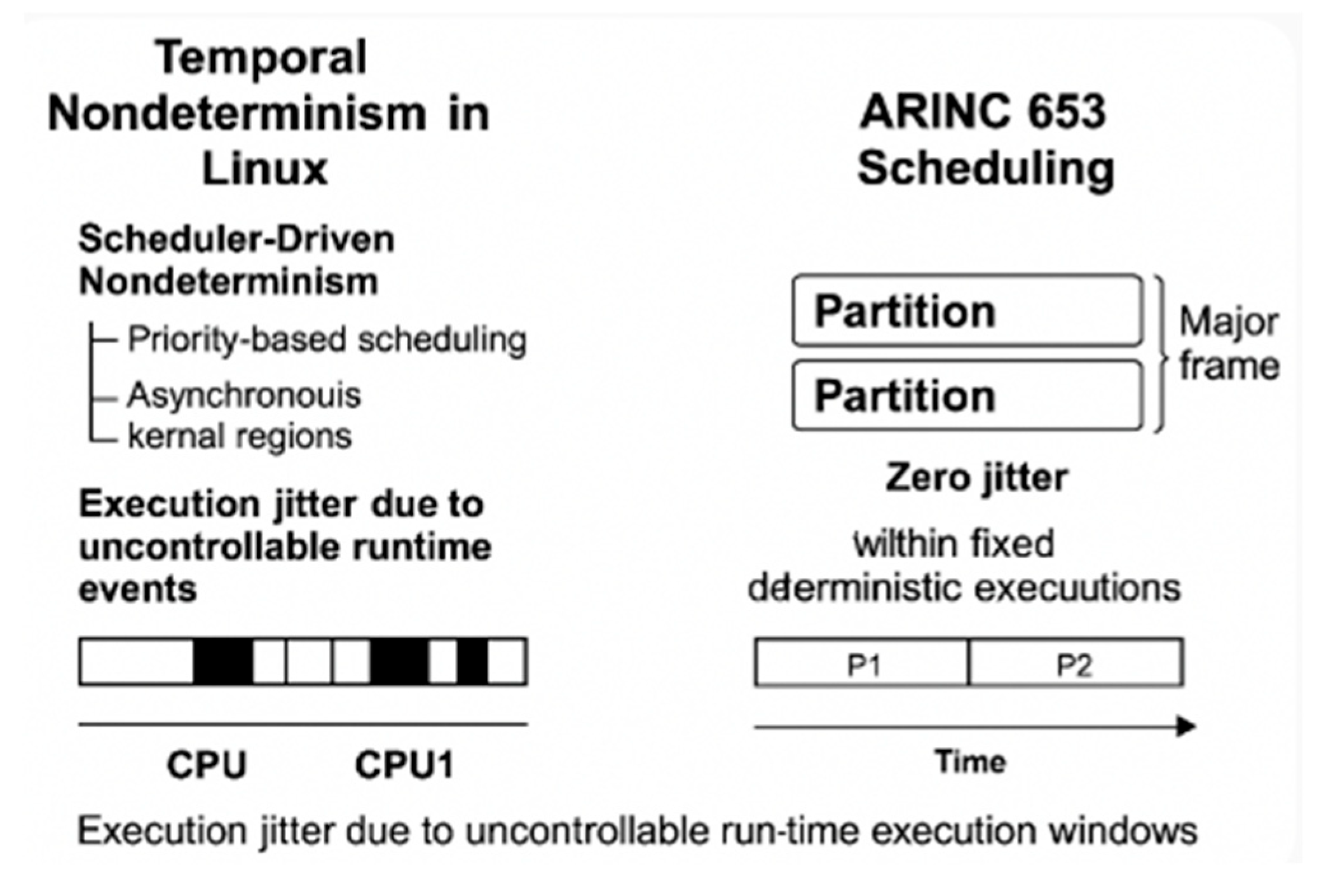
A. Lack of Temporal Determinism
- Deterministic timing with tight WCET bounds and bounded scheduling/interrupt latency.
- Partition-level fault confinement with hardware-enforced separation and no cross-partition propagation.
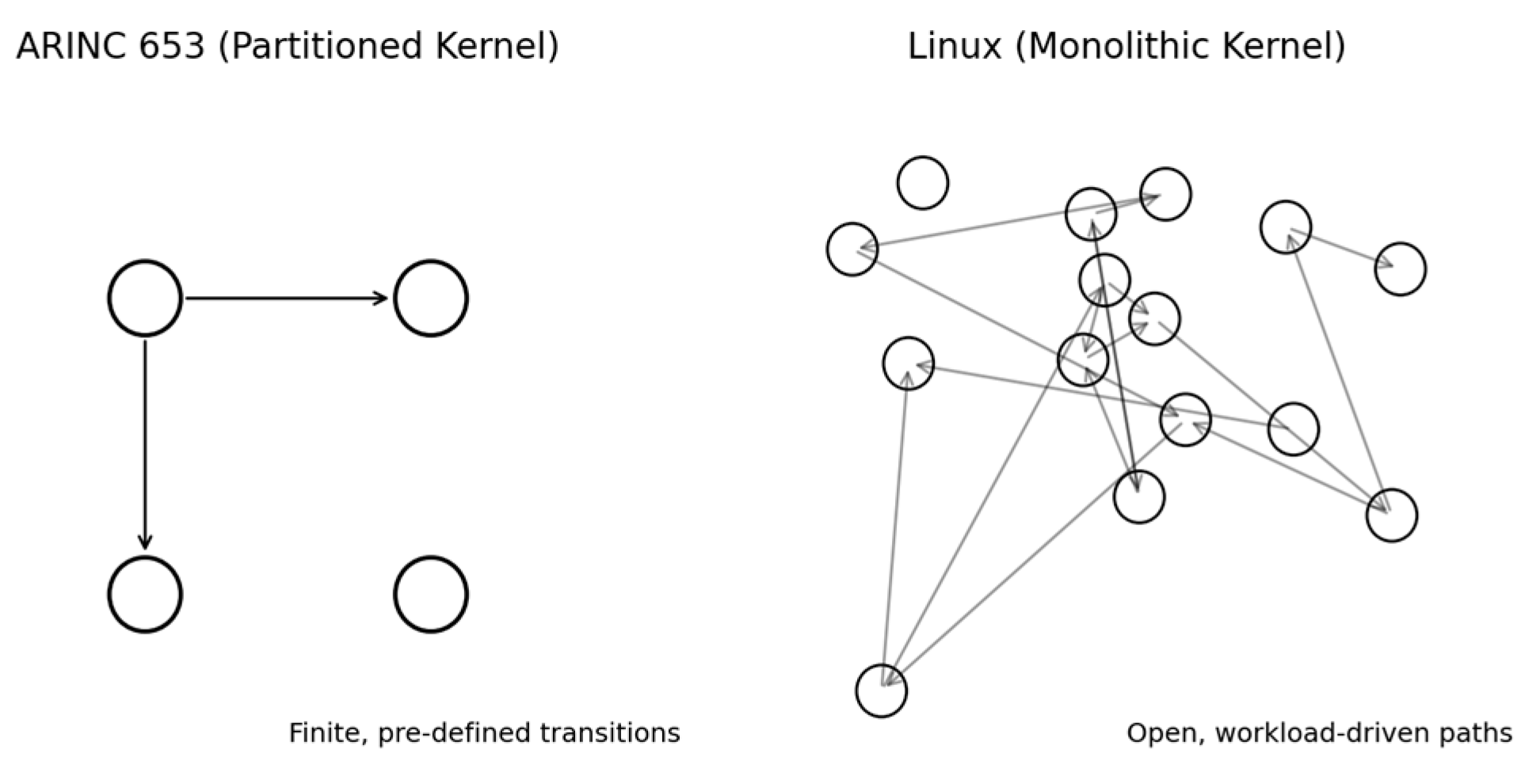
- A finite, fully analyzable behavioral model (closed semantics) suitable for formal analysis and exhaustive testing.
- Freeze-able, long-term stable baselines with strictly controlled change.
- Version-locked, auditable, DO-330-qualifiable toolchains enabling deterministic, reproducible builds.
- Timing model elements (scheduler preemption paths, interrupt/softirq/workqueues, memory events)
- Spatial isolation mechanisms (MMU/MPU boundaries, page-mapping mutability)
- Failure containment boundaries (kernel/global state sharing)
- Baseline stability (patch cadence, configuration freeze)
- Build/toolchain determinism (multi-tool pipelines, DO-330 qualification scope)
- Map traits → objectives: timing determinism, partition-level isolation, closed semantics, stable baselines, qualifiable toolchains
- For each objective: analyze worst-case behavior, fault propagation, state-space boundedness, configuration control, tool evidence
- Rate risk: low/medium/high, with rationale and affected subsystems
- Consolidated findings per objective (pass/blockers)
- Mitigation options (partitioned kernels, separation kernels, certified RTOS platforms)
- Decision aid: proceed for non-critical functions/redesign for DAL A/B
- spinlock-protected critical sections,
- per-CPU data updates,
- scheduler state transitions, and
- low-level exception-handling paths.
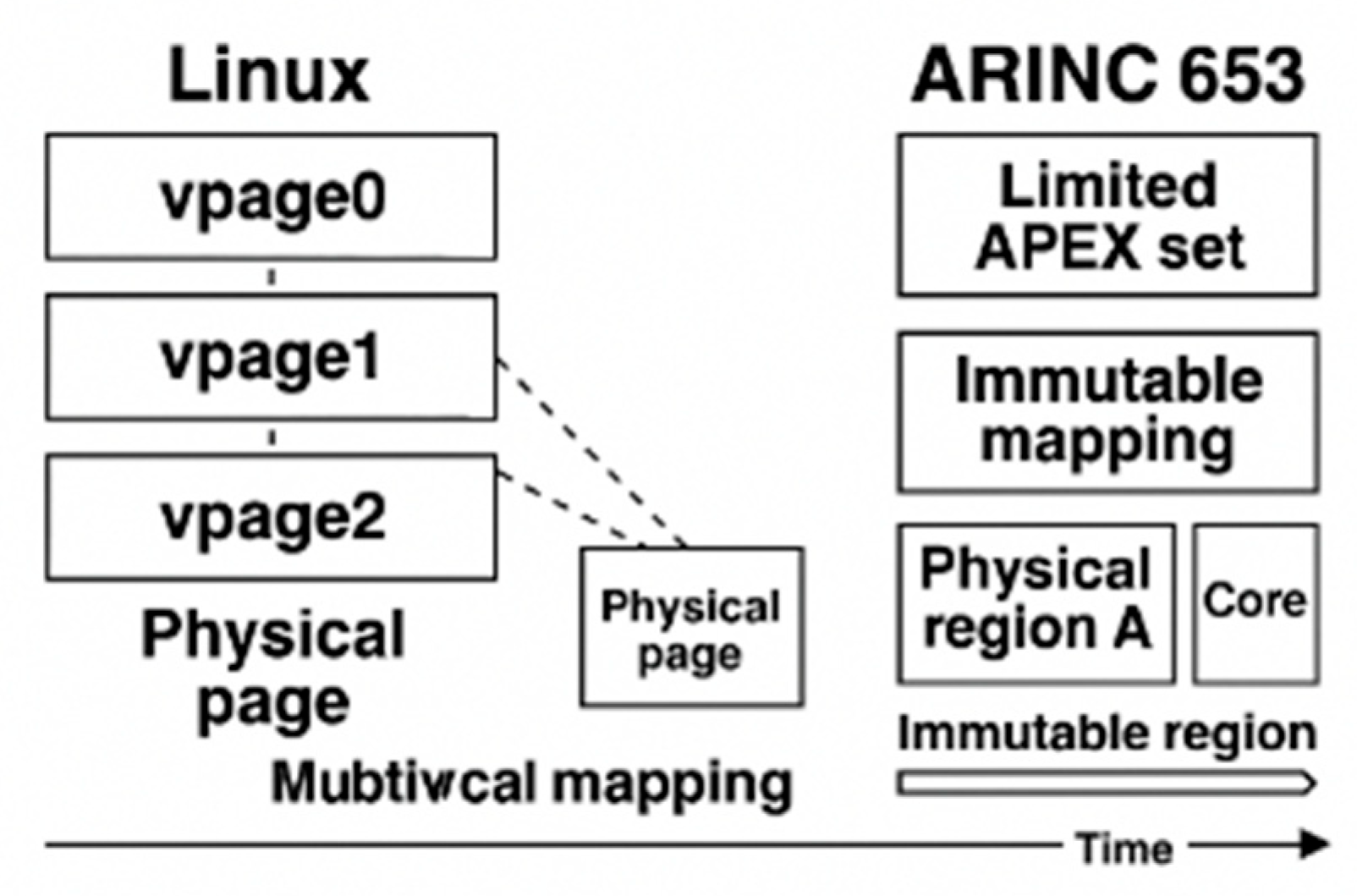
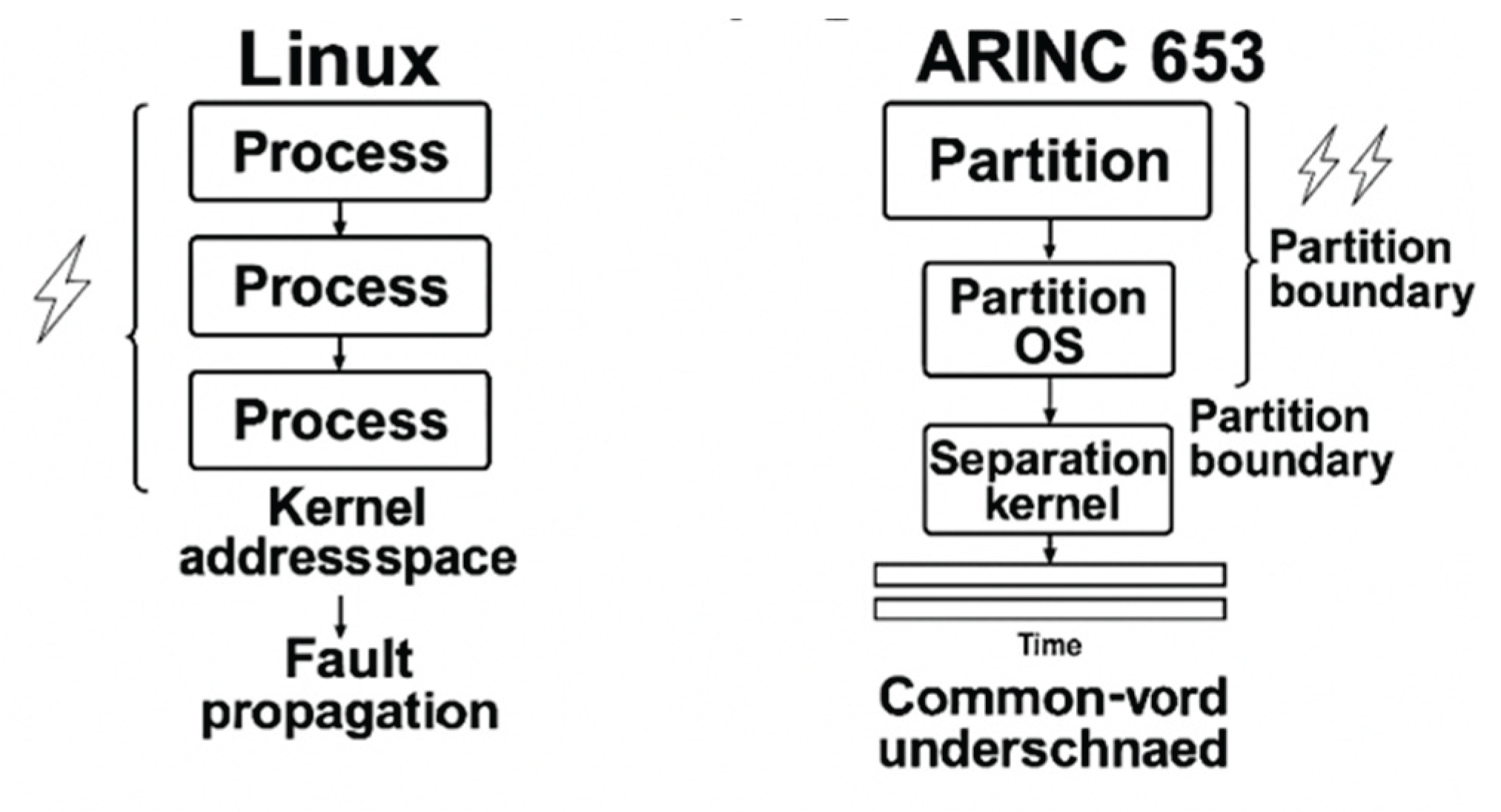
B. No Physical Memory Isolation
- Demand paging and on-demand allocation. Page tables are populated lazily, and physical pages may be allocated, remapped, or reclaimed during runtime based on memory pressure and process behavior.
- Page reclaim and compaction. Under memory pressure, the kernel evicts or relocates physical pages, invoking reclaim, compaction, or write-back paths that modify page-table mappings without application involvement.
- Dynamic page-table updates and TLB shootdowns. Linux frequently updates page attributes, permission bits, and mapping structures, triggering cross-CPU TLB invalidations and modifying the effective physical-memory layout during operation.
- Shared kernel-memory structures. The kernel’s slab allocators, per-CPU buffers, and driver subsystems allocate and free kernel memory dynamically; these regions are globally shared and not partition-scoped.
C. Driver Contamination of Kernel Global State
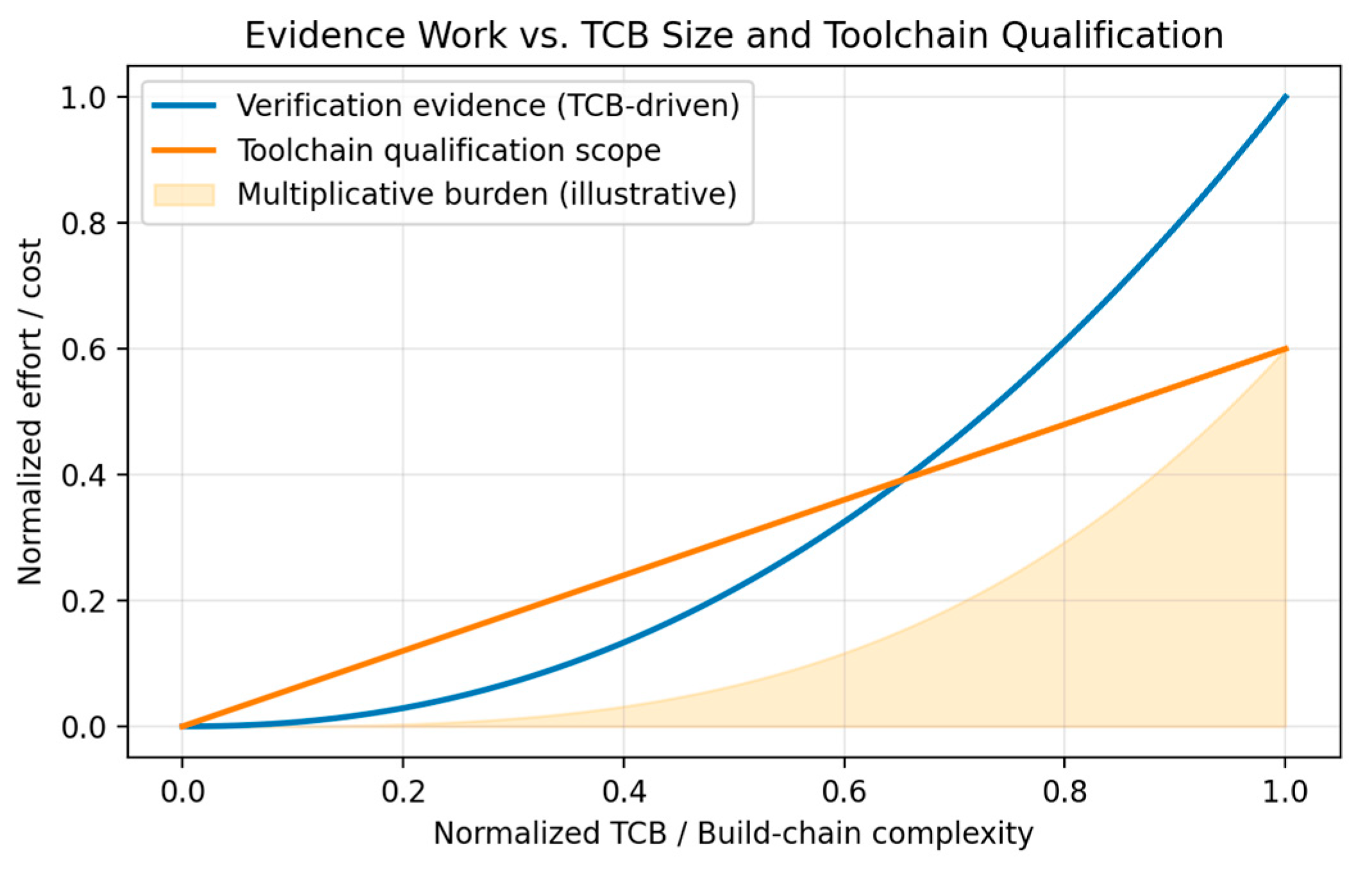
D. Overly Large Trusted Computing Base (TCB)
- Declaring all kernel subsystems, all bundled drivers, and all architecture-specific code paths as part of the certifiable airborne software item.
- Producing planning artifacts (PSAC, SDP, SVP, SCMP, SQAP) that must describe how each subsystem achieves determinism, verifiability, testability, and configuration stability.
- Defining an assurance strategy for kernel-wide concurrency, memory sharing, interrupt handling, scheduling, dynamic allocation, and toolchain behaviors.
- The kernel contains vast quantities of implementation-driven code, developed incrementally without DAL-style requirements decomposition.
- Core subsystems (scheduler, MM, VFS, network stack, timers, softirq) lack formalized HLR/LLR specifications, making traceability impossible.
- Architectural behavior depends on dynamic global state, hardware-dependent heuristics, and runtime conditions, violating DO-178C expectations of predictable and reviewable design behavior.
- Many kernel paths have implicit behavior (e.g., locking, RCU semantics, memory reclaim conditions) that cannot be fully captured in DAL-style requirements.
- Structural coverage analysis up to MC/DC at the source level
- Verification of all exception paths, error handlers, corner cases, and architecture-specific branches
- Robustness testing against abnormal inputs and worst-case conditions
- Review of all interfaces, data flows, and shared states
- Linux’s scale makes these obligations infeasible:
- The kernel’s millions of lines of code require astronomical verification effort.
- Many kernel paths depend on hardware behavior, timing, interrupts, speculative execution, and concurrency, making complete test coverage impossible.
- Dynamic subsystems (e.g., memory reclaim, workqueues, softirq, RCU) make it impractical to achieve deterministic coverage closure, because behavior varies with load, timing, and configuration.
- MC/DC on the kernel would require analyzing tens of thousands of complex decision points, many interacting across subsystems.
- Every version, file, requirement, and tool must be baselined and traceable.
- Any change requires impact analysis, regression evidence, and re-verification for affected DAL objectives.
- Linux’s characteristics conflict sharply with these requirements:
- The kernel evolves at a rapid pace with constant patch churn across all subsystems.
- Security fixes, driver updates, and architectural changes modify the kernel’s global behavior, invalidating prior baselines.
- Maintaining a stable, frozen Linux baseline contradicts the upstream model and imposes massive regression testing costs.
- The Linux toolchain (kbuild, gcc/llvm, binutils, scripts) forms a complex, multi-tool configuration that must itself be DO-330 qualified for use in DAL A/B—effectively infeasible.
- Its development is distributed across thousands of contributors with no DAL-style independence.
- No QA organization can audit or ensure compliance of upstream kernel changes.
- The kernel’s enormous TCB size makes independent reviews impractical, as QA must assess the entire lifecycle—from requirements to design to code—for millions of lines and hundreds of contributors.
- The separation kernel is purpose-designed to be extremely small, static, and analyzable.
- Device drivers and applications run outside the certified kernel, in isolated partitions.
- The separation kernel’s TCB is on the order of tens of thousands of lines, not millions, making DO-178C planning, verification, configuration control, and QA processes achievable at DAL A.
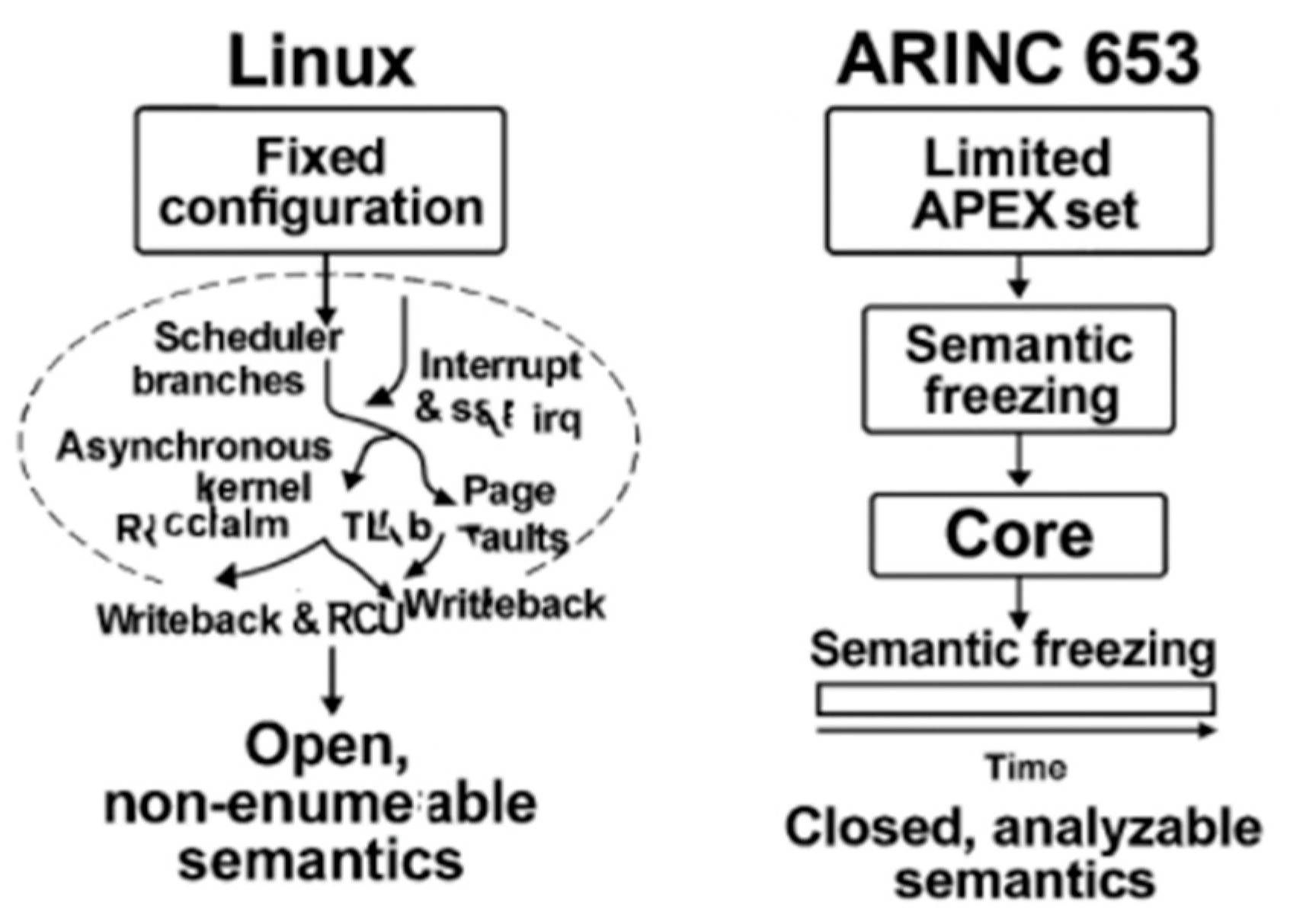
E. Open System Semantics with Unpredictable Behavior
- Fix all partition schedules,
- Allocate static memory regions,
- Define deterministic inter-partition communication,
- Prohibit dynamic creation of execution paths,
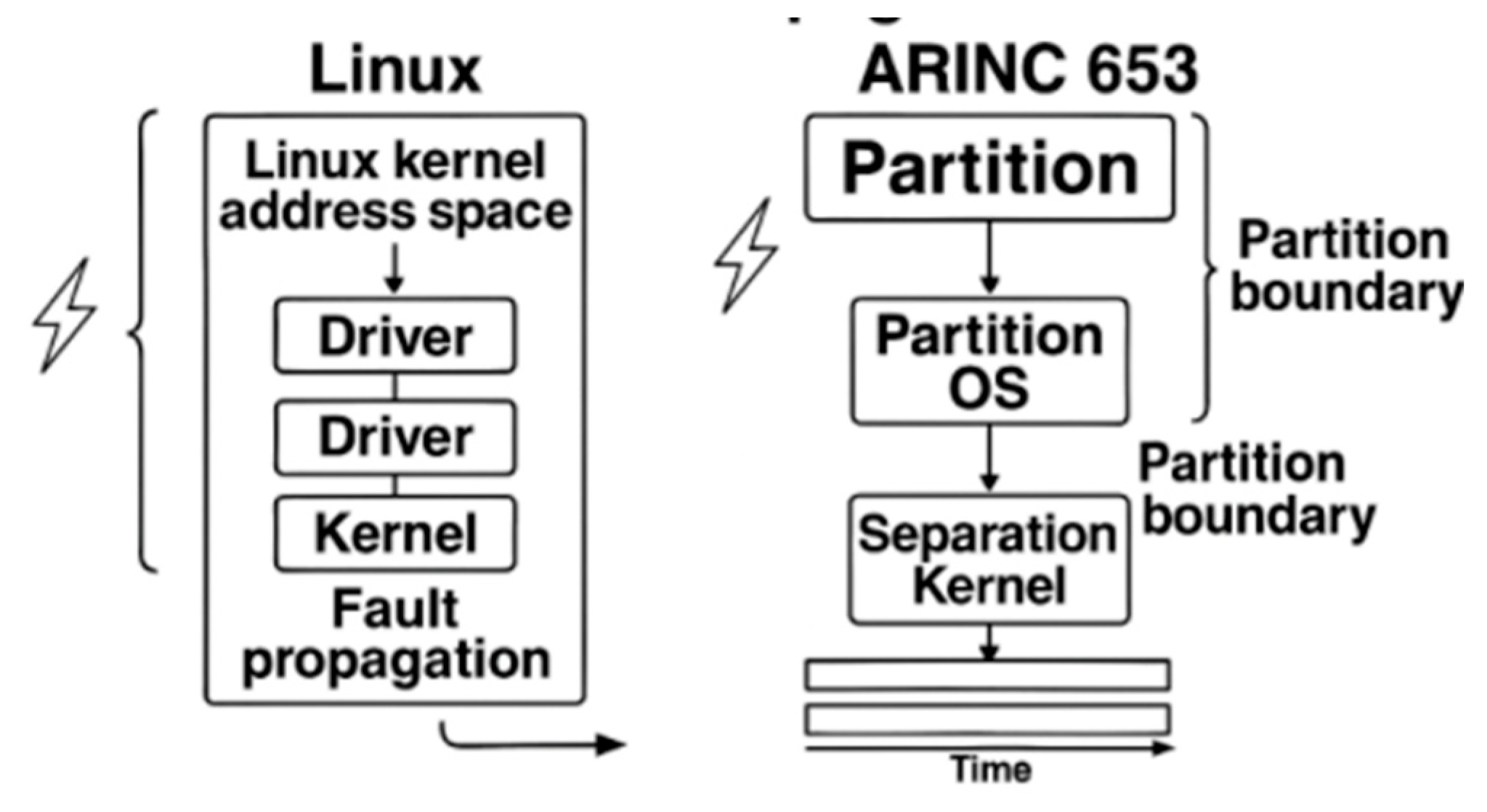
F. Lack of Fault Isolation
- shared kernel memory regions used by subsystems such as the scheduler, VFS, networking, and memory management;
- global locks and synchronization primitives that serialize access across unrelated components;
- reference counters and object life-cycle structures (e.g., file descriptors, network buffers, slab objects);
- interrupt-handling and softirq pathways, whose execution contexts are shared across all processes regardless of their criticality.
- hardware Memory Management Unit (MMU) isolation with statically defined, non-overlapping physical memory regions;
- a minimal, rigorously verified separation kernel responsible only for scheduling partitions and mediating controlled IPC;
- complete disallowance of shared kernel-writable global state between partitions;
- fault-containment boundaries that ensure a failure inside one partition cannot corrupt the separation kernel or any other partition.
G. Continuous Patch Stream Destabilizes Certified Baselines
- locking primitives
- interrupt and softirq threading
- scheduling heuristics
- preemption and concurrency models
H. Complex Toolchain Imposes Prohibitive DO-330 Qualification Burden
V. Common Misunderstandings and Why They Fail
A. Linux + RT Patches Provide Temporal Isolation
- Improves average latency but leaves asynchronous kernel activity and non-enumerable paths intact
- Cannot provide closed-form worst-case guarantees for ARINC 653 time windows
- Define WCET evidence for all critical threads without masking effects from interrupts/softirq/RCU
- Demonstrate absence of unbounded preemption points during the assigned time window
B. Open Source Reduces Cost
- Certification scope scales with TCB size and evidence depth, not license fees
- Large, evolving kernel inflates verification and configuration control
- Bound the TCB and evidence items; provide stable, freeze-able baselines
- Quantify toolchain qualification scope (DO-330) with fixed versions
C. Cgroups Provide Partition–Equivalent Isolation
- Resource shaping ≠ hardware-enforced isolation
- Shared kernel domain permits cross-component interference
- Show hardware-enforced memory exclusivity per partition
- Prove fault confinement boundaries with no cross-partition propagation
D. Using Mlock() and Disabling Swap
- Residency ≠ fixed physical mapping; mappings can remain mutable
- Kernel activities (reclaim/compaction) can relocate pages
- Allocate static, non-overlapping physical regions; verify immutability at runtime
- Disable mechanisms that mutate page tables for DAL partitions
- reserve a guaranteed amount of memory for an application,
- ensure that locked pages come from a specific physical memory range,
- prevent the kernel from compacting, migrating, or remapping those pages,
- isolate the locked pages from interference caused by other processes,
- protect the physical region with MMU hardware boundaries.
- Linux may still:
- migrate mlocked pages during compaction,
- modify their page-table entries,
- trigger TLB shootdowns,
- reclaim adjacent pages and cause cache/TLB side effects,
- allocate kernel memory into nearby physical ranges.
E. Static Configuration Can Make Linux Deterministic
F. Abundant Linux Ecosystem
- the number of tools involved in the build pipeline,
- the number of transformations applied to source artifacts,
- the number of scripts and generators that must be controlled or assessed, and
- the number of potential interactions requiring justification or qualification under DO-330.
VI. Recommendations
- Partitioning Kernels/Type-1 Hypervisors: XtratuM + LithOS, POK, JetOS
- Separation Kernels + User-Space ARINC Services: seL4 (MCS), Muen SK
- Commercial Certifiable Platforms: VxWorks 653, INTEGRITY-178B, LynxOS-178, PikeOS, DeOS
VII. Conclusions
References
- ARINC Industry Activities. ARINC Specification 653P1-3: Avionics Application Software Standard Interface, Part 1; ARINC: Annapolis, MD, USA, 2015. [Google Scholar]
- ARINC Industry Activities. ARINC Specification 653P3-2: Avionics Application Software Standard Interface, Part 3; ARINC: Annapolis, MD, USA, 2014. [Google Scholar]
- RTCA Inc. DO-178C: Software Considerations in Airborne Systems and Equipment Certification. RTCA: Washington, DC, USA, 2011.
- EUROCAE. ED-12C: Software Considerations in Airborne Systems and Equipment Certification; EUROCAE: Paris, France, 2011. [Google Scholar]
- RTCA Inc. DO-297: Integrated Modular Avionics (IMA) Design Guidance and Certification Considerations. RTCA: Washington, DC, USA, 2005.
- RTCA Inc. DO-330: Software Tool Qualification Considerations. RTCA: Washington, DC, USA, 2011.
- Wang, P.; Li, Q.; Xiong, & H. Time and space partitioning technology for integrated modular avionics systems. J. Beijing Univ. Aeronaut. Astronaut. (in Chinese). 2012, vol. 38(no. 6), 721–726. [Google Scholar]
- He, F.; Xiong, H.; Zhou, X. Overview of key technologies for ARINC 653 partitioned operating systems. Acta Aeronaut. Astronaut. Sin. (in Chinese). 2014, vol. 35(no. 7), 1777–1796. [Google Scholar]
- Li, Y.; Zhou, T.; Li, J. Research and implementation of airborne ARINC 653 partition operating system. Comput. Eng. Appl. (in Chinese). 2015, vol. 51(no. 20), 235–240. [Google Scholar]
- Chen, L. Research on deterministic scheduling of avionics partition operating systems. Ph.D. dissertation, (in Chinese). Coll. Aeronaut. Eng., Nanjing Univ. Aeronaut. Astronaut., Nanjing, China, 2018. [Google Scholar]
- Huang, R. Research on ARINC 653 partition isolation mechanism for IMA. Ph.D. dissertation, (in Chinese). Sch. Electr. Eng., Northwestern Polytech. Univ., Xi’an, China, 2020. [Google Scholar]
- Lopez, I.; Parra, P.; Urueña, M. XtratuM: a hypervisor for partitioned embedded real-time systems. Proc. 18th Int. Conf. Real-Time Netw. Syst. (RTNS), Paris, France, 2010; ACM; pp. 1–6. [Google Scholar]
- Crespo, A.; Metge, P.; Lopez, I. LithOS: A Guest OS for ARINC 653 on XtratuM Hypervisor; Univ. Politèc. Valencia: Valencia, Spain, 2012. [Google Scholar]
- Delange, J.; Pautet, L.; Faucou, S. POK: an ARINC 653 compliant operating system for high-integrity systems. In Reliable Software Technologies—Ada-Europe 2010; Springer: Berlin, Germany, 2010; pp. 172–185. [Google Scholar]
- Huber, B.; Lackorzynski, A.; Warg, A. seL4: formal verification of a high-assurance microkernel. Commun. ACM 2014, vol. 57(no. 3), 107–115. [Google Scholar]
- Kuz, I.; Elphinstone, K.; Heiser, G. MCS: temporal isolation in the seL4 microkernel. Proc. 11th Oper. Syst. Platforms Embedded Real-Time Appl. (OSPERT), New York, NY, USA, 2015; IEEE; pp. 1–6. [Google Scholar]
- Härtig, H.; Lackorzynski, A.; Warg, A. The Muen Separation Kernel: Design and Formal Verification; Tech. Univ. Dresden: Dresden, Germany, 2018. [Google Scholar]
- Rushby, J. Design and Verification of Secure Systems; SRI Int.: Menlo Park, CA, USA, 1981. [Google Scholar]
- Rushby, J. A kernelized architecture for safety-critical systems. Proc. IFIP Congr., Vienna, Austria, 1999; pp. 1–6. [Google Scholar]
- Wind River Systems Inc., VxWorks 653 Platform Datasheet. 2022. Available online: https://www.windriver.com.
- Green Hills Software Inc., INTEGRITY-178B RTOS for Avionics. 2021. Available online: https://www.ghs.com.
- SYSGO, AG. PikeOS Safety-Certifiable RTOS and Hypervisor. 2024. Available online: https://www.sysgo.com.
- DDC-I Inc. DeOS Safety-Critical RTOS. 2024. Available online: https://www.ddci.com.
- Bovet, D.; Cesati, M. Understanding the Linux Kernel; O’Reilly Media: Sebastopol, CA, USA, 2005. [Google Scholar]
- R. Love, Linux Kernel Development; Addison-Wesley: Upper Saddle River, NJ, USA, 2010.
- Gorman, M. Understanding the Linux Virtual Memory Manager; Prentice Hall: Upper Saddle River, NJ, USA, 2004. [Google Scholar]
- The Linux Kernel Organization, Linux Scheduler Documentation. 2024. Available online: https://docs.kernel.org/scheduler/.
- The Linux Kernel Organization, Linux Memory Management Documentation. 2024. Available online: https://docs.kernel.org/mm/.
- Gleixner, T. PREEMPT_RT Patch Overview and Design Philosophy; Linux Foundation: San Francisco, CA, USA, 2019; Available online: https://wiki.linuxfoundation.org/realtime/start.
- The Linux Kernel Organization, kbuild: The Linux Kernel Build System. 2024. Available online: https://docs.kernel.org/kbuild/.
- The Yocto Project, Yocto Project Mega-Manual. 2024. Available online: https://www.yoctoproject.org.
- Device Tree Working Group, Device Tree Specification. 2024. Available online: https://www.devicetree.org.
- Zhao, H.; Gao, S.; Yang, & Y. Applicability analysis of airborne software based on Linux real-time extension. Comput. Eng. 2017, vol. 43(no. S1), 311–315. [Google Scholar]
- a653rs Contributors, a653rs-linux: ARINC 653 Emulation on Linux. 2024. Available online: https://github.com/a653rs.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).