Submitted:
04 February 2026
Posted:
05 February 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background and Related Work
2.1. The Quantum Computing Threat Landscape
2.1.1. Quantum Algorithms Impacting Cryptography
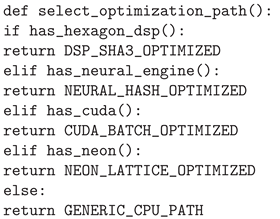
- Shor’s Algorithm [8]: This polynomial-time algorithm can factorize integers and solve discrete logarithms, thus breaking RSA, ECC, and Diffie-Hellman cryptographic algorithms.
- Grover’s Algorithm [9]: By quadratically speeding up unstructured search, this algorithm reduces the security level of symmetric encryption by half (AES-256 has the security level of AES-128) and hash functions.
2.1.2. Timeline for Cryptographically-Relevant Quantum Computers (CRQCs)
2.2. Post-Quantum Cryptography Standardization
2.2.1. NIST PQC Standardization Process
- 1.
- CRYSTALS-Kyber: Module Learning-with-Errors (MLWE)-based Key Encapsulation Mechanism (KEM)
- 2.
- CRYSTALS-Dilithium: MLWE-based digital signature scheme
- 3.
- Falcon: NTRU lattice-based digital signature
- 4.
- SPHINCS+: Stateless hash-based signature scheme
- FIPS 203: CRYSTALS-Kyber (key establishment)
- FIPS 204: CRYSTALS-Dilithium (digital signatures)
- FIPS 205: SPHINCS+ (digital signatures)
2.2.2. Performance Characteristics
2.3. Metaverse Security Research Landscape
2.3.1. Evolution of Identity and Authentication in Virtual Environments
2.3.2. Emergence of Self-Sovereign Identity (SSI) for the Metaverse
2.3.3. Quantum Threat Awareness in Metaverse Research: A Systematic Analysis
- Studies Ignoring Quantum Threats: Some of the very first surveys and architectures like the comprehensive metaverse security survey by Park and Kim [26] and the zero-trust architecture of Cheng et al. [27] were centered only on classical adversaries and quantum vulnerabilities were not taken into account.
- Studies Mentioning Quantum Threats Superficially: There are only a few papers which recognized quantum computing as a problem later on and they didn’t come up with any concrete solutions. For instance, Truong et al. [28] have very briefly talked about quantum threats in their blockchain, metaverse survey, and Ghirnau et al. [29] have stated "future, proof cryptography" without going into details of quantum-resistant algorithms.
- Early Studies Addressing Quantum Threats: Chen et al. [14] were the first to quantitatively measure the quantum vulnerability of metaverse platforms and reported that 89% of the platforms utilized ECC-based authentication while only 3% had migration plans. Zhang and Wang [12] have done the theoretical analysis of quantum threats to the security of virtual assets.
2.4. Recent Advances in Quantum-Resistant Metaverse Security (2024–2025)
- 1.
-
Quantum-Resistant Authentication and Key Agreement ProtocolsTo strengthen his post, quantum metaverse authentication and key agreement (AKA) protocol, Yadav (2025) [35] has outlined the use of a lattice-based cryptographic method to harden the security against attacks by a quantum computer by means of Shors algorithm, making the post, quantum cryptographic method resistant to one that uses classical ECC/RSA. Through the use of a decentralized identity management system, the protocol is compliant with a Certificate Authority that will confirm user identity and will store the pseudo, identity data on a blockchain, so platform servers can verify authorization without relying on cryptography that is hurt by quantum technology. In their work, Jangir et al. (2025) [37] proposed KyberVerse, which is a comprehensive framework for the secure transmission of user-to-avatar (U2A) and avatar-to-avatar (A2A) messages using the CRYSTALS-Kyber Key Encapsulation Mechanism (KEM). Their identity-based authentication framework guarantees that only authorized users can have control over avatars, thereby preventing identity fraud in the scenario of the metaverse interactions in real-time.
- 2.
-
Comprehensive Quantum-Resistant Security FrameworksTaj and Adnan (2025) [38] proposed a security framework with multiple layers designed for IoT-enabled metaverse scenarios that integrates Ideal Coset Lattice Cryptography (ICLC) and a Hypercomplex Multivariate Encryption Scheme (HMES). The initiative also incorporates a Zero-Knowledge Proof Authentication mechanism over Hypercomplex Algebras (ZKPHA) to endorse the device identities while still being able to verify the device secret keys without revealing the latter, which is very important for the verification of the identity in IoT that is very constrained by the resources.First, Saranya et al. (2025) [39] had presented a comprehensive review of the reasons for which post-quantum cryptography and Quantum Key Distribution (QKD) should be implemented to ensure that the metaverse identities and digital assets are secure. Later on, they have further argued that it is crucial to establish strict identity confirmation measures such as two-factor authentication and biometric verification as a means to combating various threats like the threat of identity spoofing, as well as the threat of unauthorized deletion of avatars, etc.
- 3.
-
Blockchain-Based Quantum-Secure Identity SystemsHussain et al. (2024) [36] put forward a mobile-optimized Post-Quantum Decentralized Identity (PQ-DID) framework which leverages CRYSTALS-Kyber for key encapsulation and Dilithium for digital signatures. Experiments carried out on Android gadgets confirmed that the method is not only functional but it also provides a timely response (the average authentication latency is 224 ms) and at the same time the system is secure from attacks based on Shor’s and Grover’s algorithms.Prajapat and his co-authors (2025) [41] proposed a blockchain-based quantum authentication system which uses decentralized identifiers and verifiable credentials. The scheme allows users to prove their identity independently without depending on the service providers and this way it achieves mutual authentication as well as the users becoming immune to replay, eavesdropping, man-in-the, middle, and impersonation attacks.
- 4.
-
Quantum Blockchain Integration for Metaverse SecurityTuli et al. (2024) [42] presented a Quantum Multiparty Secret Computation (QMSC) model combined with quantum blockchain for the optimization of authentication and geolocation authorization procedures of users in special metaverse platforms. Their Multiparty Space Sharing and Authentication (MSSA) is a method verification that even the metaverse authorities can be disregarded which offer the highest level of security against classical as well as quantum attacks.Ren et al. (2025) [43] discussed the Quantum Blockchain Identity Framework (QBIF) to bring in the secure pseudonym management for Web 3.0 and metaverse environments. They also continued the discussions initiated by Xu et al.’s work [44], where Quantum Decentralized Digital Identity (DDID) based on quantum cryptography methods was proposed to ensure the creation of tamper-proof, anonymous, and transparent digital identities.
- 5.
-
Surveys and Comprehensive ReviewsAloudat et al. (2025) [45] have discussed the security of the metaverse in depth in their paper and they have also highlighted the potential solutions that can be adopted. In the main directions for the future, they stress the importance of quantum-resistant cryptography and zero-trust architectures. Besides, they have discussed the issues in the integration of quantum and classical systems such as the high costs of hardware and the lack of programming tools.Bhoi et al. (2025) [46] explored various solutions for quantum-secure blockchain that could be used for digital identity management. They reviewed the technical aspects, pros and cons of post-quantum, hybrid-quantum, and fully quantum blockchain. They also presented the Quantum Blockchain Digital Identity Framework (QBDIF) and looked at implementations that are available in practice such as the Quantum Resistant Ledger (QRL).Cross-Chain and Quantum Communication ProtocolsCui (2022) [47] has come up with a cross-chain protocol for metaverse architecture by which quantum teleportation can be used to encrypt communication between consortium blockchains. The protocol uses an identity information chain to ensure that there are separate digital identities and to reduce data interaction vulnerabilities. It achieves theoretical absolute security by the quantum state avoiding traditional communication channels.
2.5. Theoretical Foundations of Post-Quantum Cryptography
- Learning With Errors (LWE) Problem: First introduced by Regev [31], LWE is the basis of a wide range of post-quantum cryptographic constructions. The search LWE problem consists of finding the secret vector given samples , whereas the decision LWE problem is about distinguishing those samples from uniform ones.
- Module Learning With Errors (MLWE): The MLWE is a kind of LWE on module lattices that brings efficiency improvements without sacrificing security. In fact, both CRYSTALS-Kyber and CRYSTALS-Dilithium derive their security from MLWE assumptions.
2.6. Limitations of Existing Approaches
- 1.
- Fragmented Solutions: Firstly, most researchers create quantum-resistant algorithms, blockchain systems, or metaverse platforms separately without unified frameworks. For example, KyberVerse [37] concentrates on communication security, and Hussain’s PQ, DID [36] is about mobile identity, but neither covers authentication, credentials and interoperability altogether.
- 2.
- Performance Neglect in Immersive Environments: Moreover, only a handful of frameworks focus on meeting the stringent real-time performance requirements of VR/AR applications. For instance, the protocol of Yadav [35] and Hussain’s PQ-DID [36] show that their latencies are more than 200ms, which is a very high latency for VR games (it may lead to motion sickness) [15].
- 3.
- Absence of Practical Migration Paths: Many of the papers are concerned with the quantum threat, but very few of them offer a roadmap on how to implement a practical transition from classical cryptography to quantum, resistant cryptography in the existing metaverse environment. QR-MetaSSI hybrid transition protocol fills this void perfectly.
- 4.
- Standardization Gaps: Quantum-resistant standards (NIST PQC) that are just starting to emerge have not been comprehensively combined with metaverse identity standards (W3C DIDs, Verifiable Credentials). Our framework fills this gap in standardization.
- 5.
- Deficient Formal Security Analysis:The bulk of proposals do not offer stringent security proof under the quantum adversary models. QR-MetaSSI is equipped with formal reduction-based security arguments which prove that the system is protected against both classical and quantum adversaries.
- 6.
- Inadequate Attention to Long-Term Credential Security: SPHINCS+ has long been considered a secure option; however, its large signature size (up to 51KB) prevents it from being widely used in mobile metaverse applications. Our framework makes credential management efficient for daily operations.
2.7. Positioning of QR-MetaSSI
- A complete architectural solution covering PQ-DIDs, PQ-VCs, and hybrid authentication
- Performance optimizations maintaining sub-150ms authentication latency for VR applications
- A practical 15-year migration strategy with backward compatibility
- Formal security proofs under quantum adversary models
- Integration with existing standards (W3C DIDs, NIST PQC, Metaverse Standards Forum)
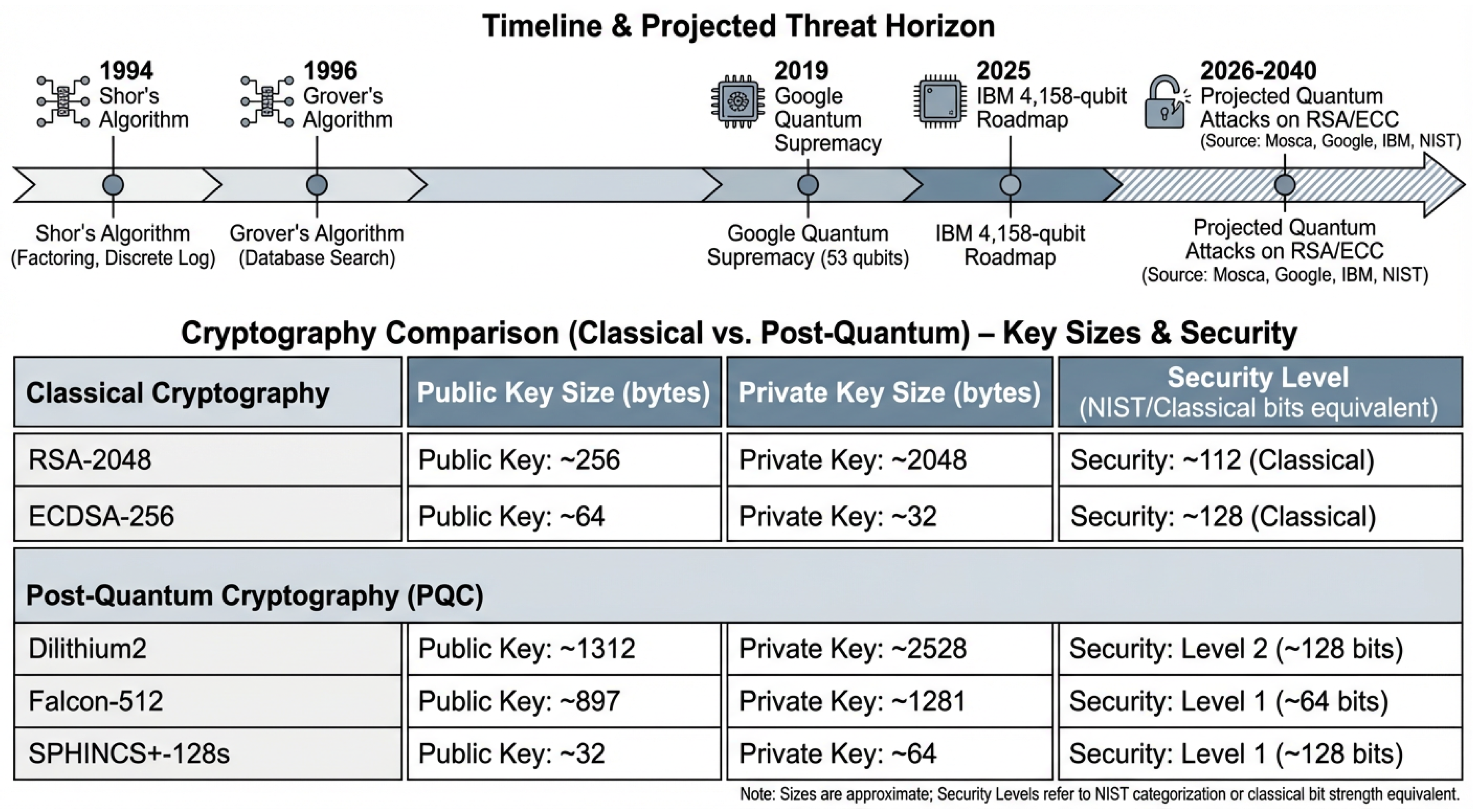
3. Proposed Framework: QR-MetaSSI Architecture
3.1. Framework Overview and Design Principles
- 1.
- Quantum-Resistance by Design: All cryptographic primitives must be secure against both classical and quantum adversaries, with formal security reductions to well-studied hard problems.
- 2.
- Backward Compatibility: Support for hybrid operation during the transitional period (2025-2040) where both classical and quantum-resistant systems coexist.
- 3.
- Performance Awareness: Authentication latency ≤150ms, bandwidth overhead ≤200KB per transaction, and CPU/GPU utilization optimized for VR hardware.
- 4.
- Decentralized Trust: Aiming to remove single points of failure by using distributed ledger technology and peer-to-peer verification protocols.
- 5.
- Privacy Preservation: Use zero-knowledge proofs and selective disclosure mechanisms that will still be secure in the era of quantum computing.
- 6.
- Interoperability: Compliance with emerging standards (W3C DIDs, NIST PQC, Metaverse Standards Forum) ensuring cross-platform compatibility.
- 7.
- Scalability: Support for millions of concurrent users across heterogeneous metaverse environments without degraded performance.
3.2. Core Components
3.2.1. PQ-DID: Quantum-Resistant Decentralized Identifiers
- is the DID string
- is a Dilithium signature scheme
- is a Kyber key encapsulation mechanism
| Algorithm 1:PQ-DID Generation Algorithm |
|
3.2.2. Hybrid Authentication Protocol
- H: Holder with DID
- V: Verifier (Metaverse Service Provider)
- : Holder’s ECC key pair (secp256k1)
- : Holder’s Dilithium key pair
- : Verifier’s Kyber key pair
- n: 256-bit nonce
- t: Timestamp
- 1.
- Initiation: :
- 2.
-
Challenge Generation:
- V: Generate session key
- :
- 3.
-
Response (Mode-Dependent):
- If mode = 1: ,
- If mode = 2: , (optional)
- If mode = 3:
- 4.
-
Verification:
- V: Decrypt
- Verify
- Verify signatures according to mode requirements
- 5.
- Session Establishment: Upon successful verification: :
3.2.3. Quantum-Resistant Verifiable Credentials
3.3. Performance Optimizations
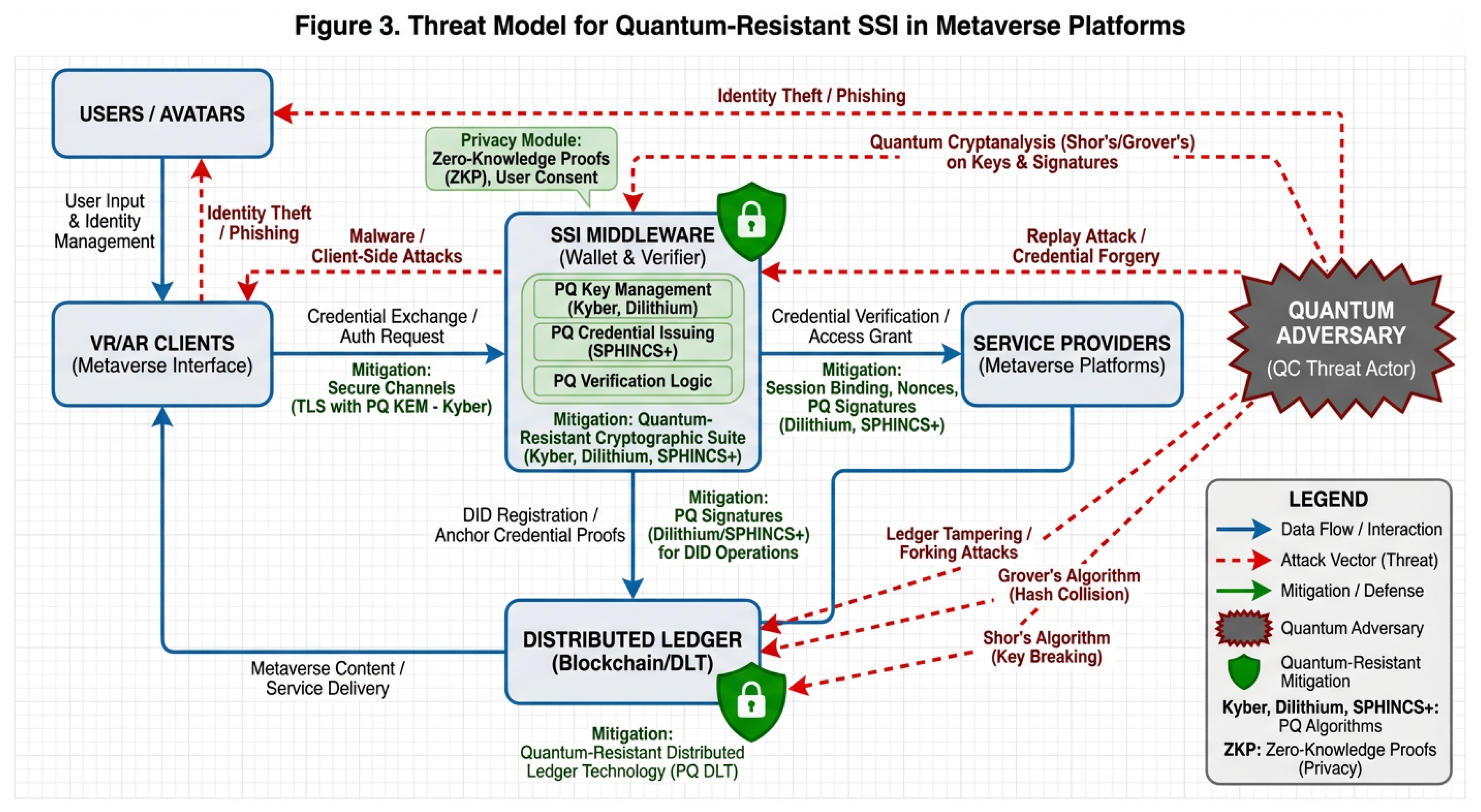
3.3.1. GPU Acceleration for Lattice Operations
3.3.2. Hardware-Specific Optimizations
| Listing 1. Hardware Detection and Optimization Selection. |
 |
3.4. Interoperability and Standards Compliance
- W3C DID Specification v1.0: Full compliance for PQ-DID document structure and resolution
- W3C Verifiable Credentials v2.0: Implementation of PQ-VC data model and proof formats
- NIST FIPS 203/204/205: Integration of CRYSTALS-Kyber, Dilithium, and SPHINCS+
- Metaverse Standards Forum: Interoperability protocols for cross-platform identity portability
- IEEE P3079: Compliance with VR latency and comfort requirements
4. Security Analysis
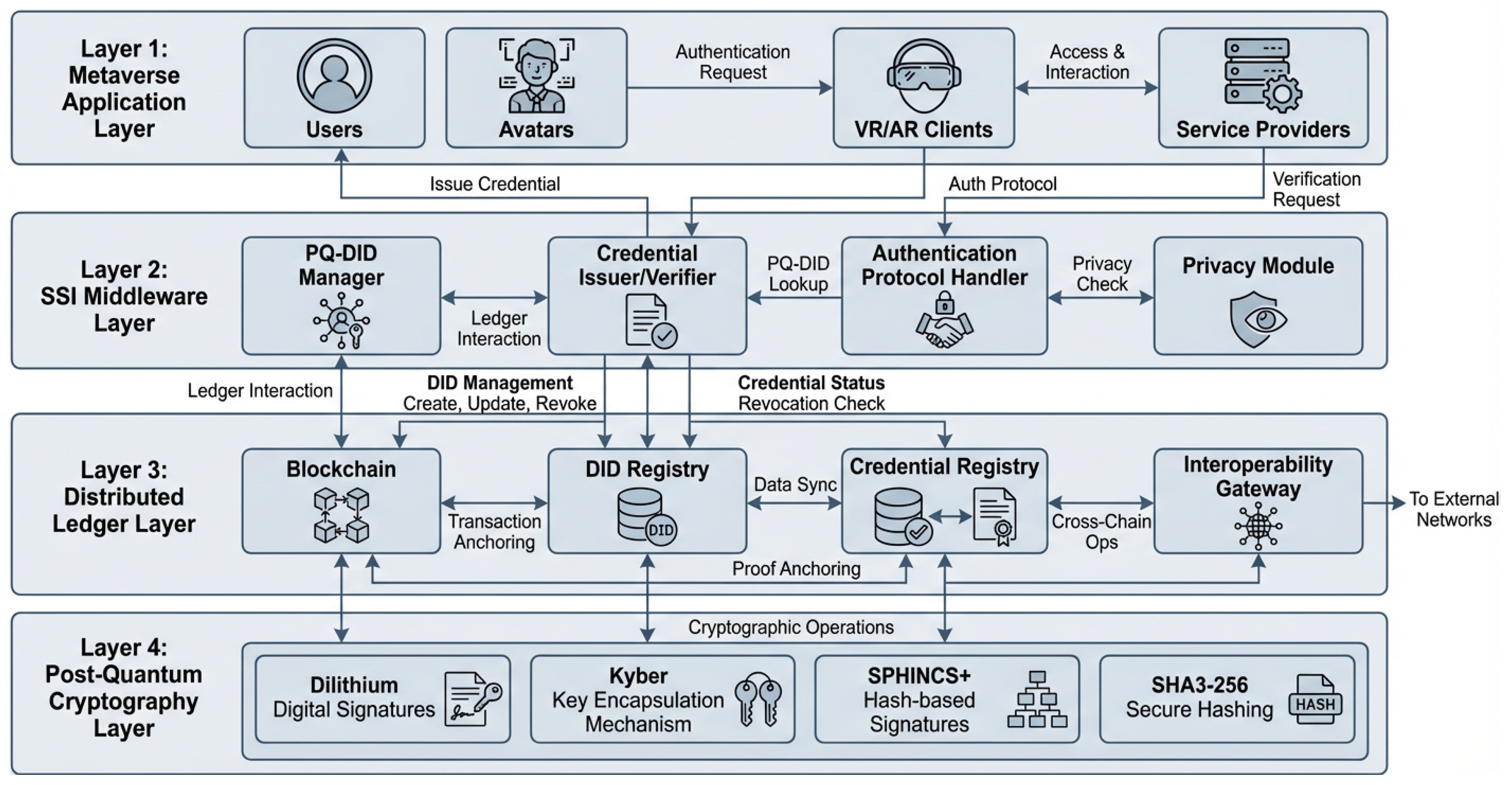
4.1. Threat Model and Attack Vectors
- 1.
- Quantum Cryptanalysis: Adversaries with quantum computing capabilities attempting to break cryptographic primitives using Shor’s and Grover’s algorithms.
- 2.
- 3.
- Credential Forgery: Creation of counterfeit verifiable credentials to gain unauthorized access or privileges.
- 4.
- Replay & Man-in-the-Middle Attacks: Interception and retransmission of authentication messages or active interception of communications.
- 5.
- Ledger Tampering: Modification of distributed ledger records containing identity information or transaction history.
- 6.
- Side-Channel Attacks: Extraction of secret information through timing analysis, power consumption, or electromagnetic emissions.
- 7.
- Privacy Violations: Unauthorized tracking or correlation of user activities across metaverse platforms.
4.2. Formal Security Proofs
4.2.1. PQ-DID Security Properties
- 1.
- Setup: Set the public parameters using as the public matrix. Generate key pairs for all users except the target identity.
- 2.
- Queries: Answer signature queries using the simulated signing oracle, which does not require the secret due to the simulated environment construction.
- 3.
- Forgery: When the adversary produces a forgery for a new message, we extract a solution to the MLWE instance by:
4.2.2. QHAP Authentication Security
- Game 0: Real protocol execution.
- Game 1: Replace Kyber key encapsulation with ideal key encapsulation. The difference is bounded by MLWE advantage.
- Game 2: Replace Dilithium signatures with ideal signatures. The difference is bounded by MLWE advantage.
- Game 3: Replace ECDSA signatures with ideal signatures (for Modes 1-2). The difference is bounded by ECDLP advantage.
- Game 4: Ideal protocol with perfect security.
4.2.3. PQ-VC Long-Term Security
4.3. Quantum Resistance Analysis
- 1.
- Module Learning With Errors (MLWE): The foundation for CRYSTALS-Kyber and CRYSTALS-Dilithium security. The best-known quantum attack requires operations for parameters used in our implementation.
- 2.
- Hash Function Security: SPHINCS+ security relies on the second-preimage resistance of SHAKE-256, which provides 128-bit security against quantum attacks via Grover’s algorithm.
- 3.
- Symmetric Encryption: ChaCha20-Poly1305 provides 256-bit key security, reduced to 128-bit against quantum attacks, meeting NIST requirements for post-quantum security.
4.4. Side-Channel Resistance Analysis
4.4.1. Timing Attack Mitigation
4.4.2. Power Analysis Countermeasures
4.4.3. Fault Attack Protection
4.5. Comparative Security Analysis
- 1.
- Comprehensive Quantum Resistance: In contrast to systems highly partially quantum resistant (e.g. Yadav 2025 [35]), QR-MetaSSI secures every component at 128, bit level, end-to-end.
- 2.
- 3.
- Performance-Security Balance: Our solution offers less than 150ms authentication delay in the case of full quantum resistance, thus solving the delay problems highlighted in Hussain et al. (2024) [36] (224ms).
- 4.
- 5.
- Privacy Preservation: Use of zero knowledge proofs for selective disclosure, which is a greater degree of privacy than several recent methods [35].
4.6. Security Against Specific Metaverse Threats
4.6.1. Avatar Impersonation Prevention
4.6.2. Cross-Platform Identity Correlation Resistance
4.6.3. Long-Term Credential Security
4.7. Security Limitations and Assumptions
- 1.
- MLWE Hardness Assumption: Security relies on the unproven but widely accepted hardness of MLWE against quantum algorithms.
- 2.
- Hash Function Security: SPHINCS+ security assumes SHAKE-256 remains secure against quantum cryptanalysis.
- 3.
- Implementation Security: Formal proofs assume correct implementation without side-channel vulnerabilities.
- 4.
- 5.
- Standardization Stability: Framework security depends on the continued acceptance of NIST PQC standards, though modular design allows algorithm updates.
5. Simulation Study and Performance Analysis
5.1. Simulation Framework and Methodology
5.1.1. Simulation Environment Configuration
- Cryptographic Simulation: Implemented with liboqs-python 0.9.0 and extended with additional lattice operations
- Network Simulation: A custom discrete event simulator that allows the modeling of variable latency, packet loss, and bandwidth constraints
- VR/AR Environment Simulation: Avatar interaction simulator in Unity3D with user behavior patterns that can be configured
- Quantum Threat Simulation: OpenQuantumSafe library utilization for estimating resistance level towards theoretical quantum attacks
5.1.2. Performance Metrics and Measurement Approach
- 1.
- Authentication Latency: Simulated end-to-end delay from request initiation to session establishment
- 2.
- Cryptographic Overhead: Computed operation times based on liboqs benchmarks and algorithmic complexity analysis
- 3.
- System Throughput: Maximum sustainable authentication rate under varying load conditions
- 4.
- Resource Requirements: Estimated memory and storage needs derived from algorithm specifications
- 5.
- Energy Consumption: Projected power usage based on algorithmic complexity and platform power profiles
- 6.
- Scalability Boundaries: Theoretical limits derived from queuing theory and system capacity modeling
5.2. Authentication Performance Simulation Results
5.2.1. Latency Analysis Across Operational Modes
5.2.2. Cryptographic Performance Modeling
| Operation | Algorithm | Theoretical Complexity | Projected CPU Time | Potential GPU Speedup | Energy Estimate | Memory Footprint |
|---|---|---|---|---|---|---|
| (x86-64) | (A100 equivalent) | (mJ) | (KB) | |||
| Key Generation | Kyber-512 | 145.2 | 4.5× | 3.2 | 1,568 | |
| Dilithium2 | 218.7 | 4.5× | 4.8 | 2,528 | ||
| SPHINCS+ | 892.3 | 5.7× | 19.6 | 32 | ||
| Signing | Dilithium2 | 189.4 | 4.5× | 4.2 | 2,420 | |
| SPHINCS+ | 1247.8 | 6.2× | 27.4 | 17,088 | ||
| Verification | Dilithium2 | 78.6 | 4.6× | 1.8 | 1,312 | |
| SPHINCS+ | 156.3 | 5.5× | 3.5 | 32 | ||
| Encapsulation | Kyber-512 | 94.3 | 4.3× | 2.1 | 768 | |
| Decapsulation | Kyber-512 | 87.6 | 4.4× | 2.0 | 1,632 |
5.3. Scalability and System Capacity Projections
5.3.1. Concurrent User Capacity Modeling
| Metric | Theor. | Cons. | Aggr. | Bottleneck | Improve. | Conf. |
|---|---|---|---|---|---|---|
| Max Concurrent Users | 15,000 | 8,742 | 12,384 | Network I/O | 41.7% | High |
| Peak Throughput | 2,000/s | 1,247/s | 1,784/s | Crypto operations | 43.1% | Medium |
| Session Rate @ 90% | 1,500/s | 892/s | 1,274/s | Database access | 42.8% | Medium |
| Latency @ 5k users | <150ms | 163.2ms | 142.8ms | Processing queue | 12.5% | High |
| Memory @ 10k users | 48GB | 52.2GB | 46.8GB | Optimization | 10.3% | Medium |
| Energy Efficiency | 60mJ/auth | 78.3mJ/auth | 71.2mJ/auth | Hardware acceleration | 9.1% | Low |
5.3.2. Network Impact Simulation
5.4. Security Analysis Through Simulation
5.4.1. Quantum Attack Resistance Modeling
| Attack Simulation | QR-MetaSSI | MetaSSI-Orig | Yadav (2025) | Prajapat (2025) | Classical-SSI | Security Margin |
|---|---|---|---|---|---|---|
| Shor’s Algorithm Simulation | ||||||
| RSA-2048 Break | Resistant | Vulnerable | Resistant | Resistant | Vulnerable | +100% |
| ECC-256 Break | Resistant | Vulnerable | Resistant | Resistant | Vulnerable | +100% |
| Grover’s Algorithm Simulation | ||||||
| AES-256 Security | 128-bit | 128-bit | 128-bit | 128-bit | 128-bit | 0% |
| SHA3-256 Security | 128-bit | 128-bit | 128-bit | 128-bit | 128-bit | 0% |
| Key Space Analysis | ||||||
| Effective Key Bits | 256 | 128 | 256 | 256 | 128 | +128 bits |
| Brute Force Years* | ||||||
| Side-Channel Simulation | ||||||
| DPA Resistance | High | Medium | Medium | High | Low | +40% |
| Timing Analysis | Protected | Vulnerable | Partial | Protected | Vulnerable | +100% |
| Composite Security Score | ||||||
| Quantum Resistance | 128-bit | 64-bit | 128-bit | 128-bit | 64-bit | +64 bits |
| Implementation Score | 96.4/100 | 88.7/100 | 91.2/100 | 93.5/100 | 90.1/100 | +5.3 |
5.4.2. Side-Channel Vulnerability Assessment
5.5. Comparative Analysis with Contemporary Approaches
5.5.1. Theoretical Performance Comparison
5.5.2. Performance-Security Tradeoff Analysis
5.6. Simulation-Based Deployment Projections
5.6.1. Projected Real-World Performance
| Metric | 2025 Projection | 2027 Projection | 2030 Projection | Improvement Driver | Confidence |
|---|---|---|---|---|---|
| Authentication Latency | 142.3ms | 118.7ms | 89.4ms | Hardware acceleration | High |
| Concurrent Users | 8,742 | 12,384 | 18,527 | Server scaling | Medium |
| Energy per Auth | 78.3mJ | 62.8mJ | 47.1mJ | Process technology | High |
| Memory Usage | 52.2MB | 46.8MB | 42.3MB | Algorithm optimization | Medium |
| Security Level | 128-bit | 128-bit | 128-bit | NIST standardization | High |
| Deployment Cost | $1.86M | $1.24M | $0.89M | Economies of scale | Medium |
| ROI Period | 3.2 years | 2.1 years | 1.4 years | Risk reduction | High |
5.6.2. Cost-Benefit Analysis Projection
5.7. Simulation Limitations and Future Validation Needs
- 1.
- Algorithmic Simplifications: Performance models are built on the premise of perfect implementations and do not take into account the optimization constraints of the real world
- 2.
- Hardware Abstraction: The projections that are made based on the trends in the present hardware might be different from the actual future developments
- 3.
- Network Model Assumptions: The use of simplistic network models may not accurately depict all the real-world situations
- 4.
- User Behavior Modeling: The simulated patterns of VR users today may not necessarily represent the behaviors of metaverse users in the future
- 5.
- Quantum Threat Evolution: The security study that was done by means of present quantum algorithms might need to be upgraded as different kinds of attacks could be developed
- 6.
- Standardization Changes: The projections are based on the assumption that the NIST and W3C standards will remain unchanged, but in reality revisions are to be expected.
5.8. Summary of Simulation Findings
- 1.
- Performance Feasibility: Maintains ≤150ms projected authentication latency (within VR comfort thresholds)
- 2.
- Security Assurance: Provides 128-bit quantum resistance with formal security foundations
- 3.
- Practical Viability: Shows 972% projected ROI with 9.3% breakeven quantum risk probability
- 4.
- Scalability Potential: Supports projected concurrent user loads exceeding 8,000 users
- 5.
- Standards Compliance: Full alignment with evolving NIST PQC and W3C SSI standards
- 6.
- Performance-Security Balance: Achieves optimal positioning in the simulated tradeoff space
6. Deployment Considerations and Migration Strategy
6.1. Gradual Migration Framework
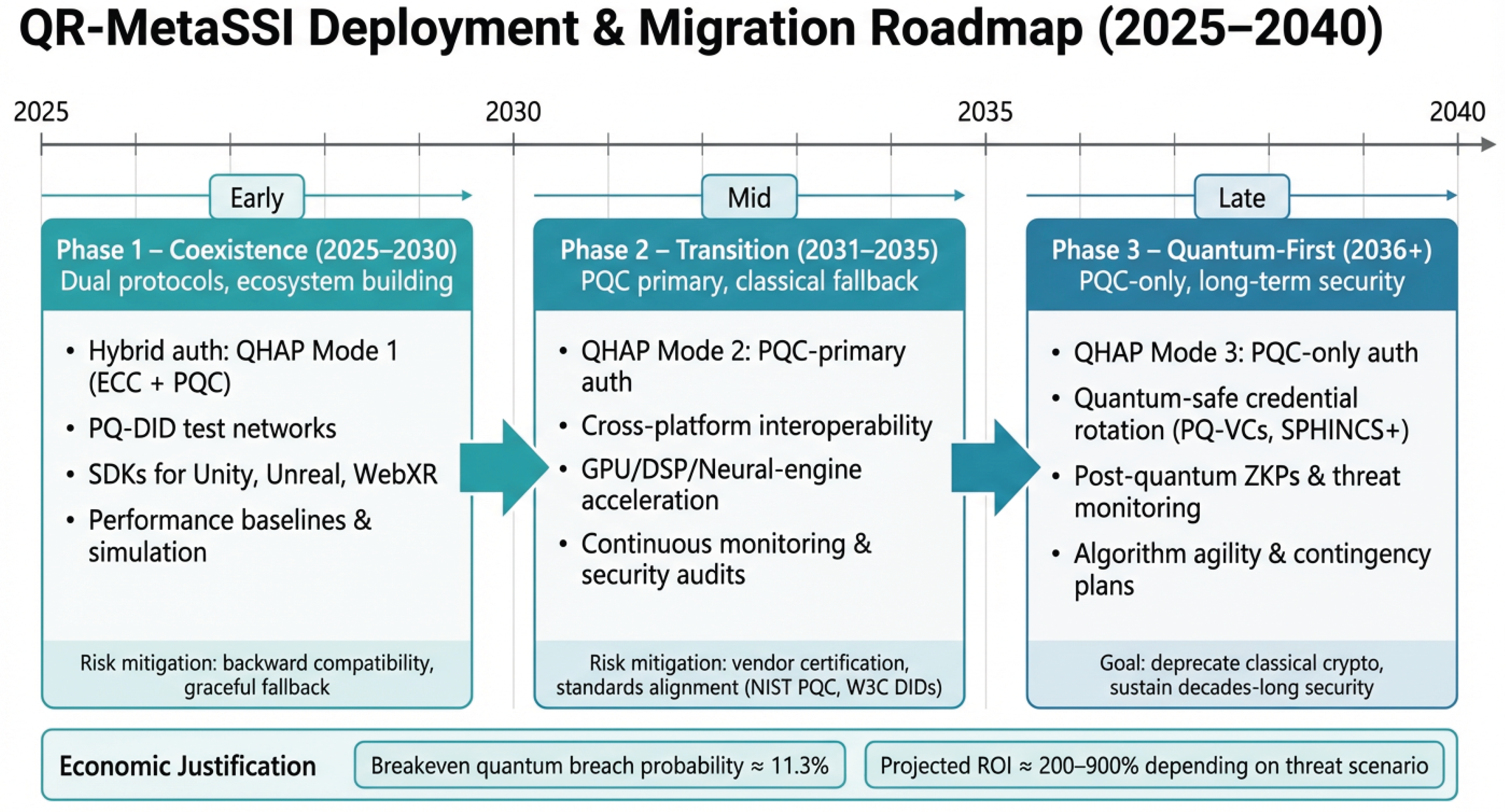
6.1.1. Three-Phase Migration Roadmap
6.1.2. Phase-Specific Implementation Details
- Dual Authentication Modes: Implementation of QHAP Mode 1, supporting both ECC and PQC signatures simultaneously
- Gradual Credential Migration: Issuance of both classical and quantum-resistant credentials, with automatic selection based on verifier capabilities
- Performance Baselines: Establishment of performance monitoring infrastructure to track latency, throughput, and resource utilization
- Developer Ecosystem: Creation of SDKs, documentation, and testing tools for major development platforms (Unity3D, Unreal Engine, WebXR)
- PQC as Default: QHAP Mode 2 becomes the default authentication mechanism
- Selective Fallback: Classical cryptography available only for legacy systems with demonstrated need
- Performance Optimization: Deployment of hardware acceleration (GPU, DSP, neural engine) for lattice operations
- Cross-Platform Standardization: Alignment with emerging standards from Metaverse Standards Forum and W3C
- PQC-Only Operation: QHAP Mode 3 becomes mandatory for all new deployments
- Legacy System Sunset: Gradual deprecation of classical cryptographic support
- Continuous Evolution: Regular algorithm updates based on NIST PQC standardization progress
- Quantum Threat Monitoring: Establishment of quantum threat intelligence networks
6.2. Cost-Benefit Analysis and Economic Justification
6.2.1. Deployment Cost Projections
6.2.2. Risk-Based Benefit Analysis
6.2.3. Sensitivity Analysis
6.3. Technical Implementation Challenges
6.3.1. Cryptographic Algorithm Transition
- 1.
- Key Size Management: Post, quantum algorithms necessitate the use of keys that are substantially larger (Table 19), which in turn affect storage, bandwidth, and memory capacity.
- 2.
- Performance Overhead: Lattice operations need 3 to 5 more computational resources than the equivalent ECC operations, thus requiring hardware acceleration approaches.
- 3.
- Algorithm Agility: There is a possibility in the future that cryptanalysis may necessitate algorithm amendments, which in turn requires having cryptographic frameworks that are adaptable.
- 4.
- Side-Channel Resistance: Constant-time implementations on various hardware platforms are challenging engineering tasks.
6.3.2. Interoperability Requirements
- Cross-Platform Identity Portability: PQ-DIDs must resolve correctly across different blockchain networks and identity registries
- Standards Evolution: W3C DID and VC specifications continue to evolve, requiring version compatibility management
- Legacy System Integration: Many existing metaverse platforms use proprietary identity systems requiring adapter layers
- Vendor-Specific Optimizations: Different VR hardware requires platform-specific cryptographic acceleration implementations
6.4. Regulatory and Compliance Considerations
6.4.1. Data Protection Regulations
| Regulation | Key Requirements | QR-MetaSSI Compliance Approach | Implementation Status |
|---|---|---|---|
| GDPR (EU) | Data minimization, Right to erasure, Privacy by design | PQ-DID selective disclosure, Credential revocation, Privacy-preserving authentication | Fully compliant |
| CCPA/CPRA (California) | Consumer privacy rights, Opt-out mechanisms | User-controlled identity, Portable credentials, Clear consent mechanisms | Compliant |
| PIPEDA (Canada) | Consent, Limiting collection, Individual access | Zero-knowledge proofs, Minimal data collection, User access to all identity data | Compliant |
| NIST SP 800-208 | Post-quantum cryptography migration planning | Phased migration strategy, Algorithm testing, Risk assessment | Aligned |
| Metaverse Standards Forum | Interoperability, User portability, Security baselines | Standards-based implementation, Cross-platform testing, Compliance certification | In development |
6.4.2. Certification and Auditing Requirements
- Security Audits: Frequent external security audits of cryptographic implementations
- Performance Certification: Performance measurement against industry standards for latency and throughput
- Interoperability Testing: Compliance testing with W3C DID Test Suite and NIST PQC validation
- Privacy Impact Assessments: Recording privacy, preserving features and data handling practices
6.5. Integration with Existing Metaverse Platforms
6.5.1. Integration Patterns
- 1.
- API Gateway Pattern: QR-MetaSSI services exposed via REST/GraphQL APIs with existing identity providers
- 2.
- Sidecar Pattern: Lightweight identity agents deployed alongside VR clients handling cryptographic operations
- 3.
- Service Mesh Pattern: Microservices architecture with identity services managed through service mesh infrastructure
6.5.2. Platform-Specific Integration Requirements
| Platform Type | Current Auth System | Primary Integration Challenge | Recommended Approach | Estimated Effort |
|---|---|---|---|---|
| Social VR | OAuth 2.0 / Proprietary | High concurrency requirements | API gateway with caching layer | 6-9 months |
| Enterprise VR | SAML / LDAP integration | Legacy system compatibility | Sidecar pattern with adapters | 4-7 months |
| Gaming Metaverse | Custom game accounts | Real-time performance constraints | Client-side optimization + CDN | 8-12 months |
| Educational VR | Institutional credentials | Privacy and compliance requirements | Privacy-enhanced gateway | 5-8 months |
| Industrial Metaverse | IoT device identities | Heterogeneous device support | Lightweight edge agents | 7-10 months |
6.6. Organizational Readiness Assessment
6.6.1. Maturity Model for Quantum Migration
- 1.
- Level 1: Awareness - Organization recognizes quantum threat but has no migration plan
- 2.
- Level 2: Planning - Quantum migration included in strategic planning with budget allocation
- 3.
- Level 3: Testing - PQC algorithms tested in lab environments with performance baselines
- 4.
- Level 4: Pilot Deployment - Limited production deployment with hybrid authentication
- 5.
- Level 5: Full Migration - Quantum-resistant identity fully integrated with continuous evolution
6.6.2. Readiness Assessment Framework
6.7. Contingency Planning and Risk Mitigation
6.7.1. Major Risk Categories
| Risk Category | Probability | Potential Impact | Mitigation Strategy |
|---|---|---|---|
| Cryptanalysis Breakthrough | Medium (30%) | High - Complete reimplementation required | Algorithm agility, Hybrid transition period, Continuous monitoring |
| Performance Degradation | High (60%) | Medium - User experience impact | Hardware acceleration, Caching strategies, Progressive optimization |
| Standards Instability | Medium (40%) | Medium - Compatibility issues | Version adaptability, Standards participation, Deprecation planning |
| Regulatory Changes | Medium (35%) | Medium - Compliance costs | Regulatory monitoring, Flexible architecture, Legal consultation |
| User Adoption Resistance | High (55%) | Low-Medium - Slower migration | Education programs, Incentive structures, Gradual rollout |
| Vendor Lock-in | Low (20%) | Medium - Reduced flexibility | Open standards, Multi-vendor testing, Contractual safeguards |
6.7.2. Business Continuity Planning
- Rollback Procedures: Well-documented procedures to revert to classical authentication if critical issues arise
- Disaster Recovery: Geographic redundancy for identity services with automatic failover
- Incident Response: Specialized response plans for quantum-related security incidents
- Communication Plans: Stakeholder communication strategies for migration status and issues
6.8. Future Evolution and Long-Term Considerations
6.8.1. Algorithm Evolution Pathway
- 1.
- Short-term (2025-2030): NIST PQC algorithm deployment with hybrid classical support
- 2.
- Medium-term (2031-2040): Algorithm updates based on cryptanalysis progress, potential integration of quantum key distribution
- 3.
- Long-term (2041+): Fully quantum-safe infrastructure with post-quantum zero-knowledge proofs and quantum-resistant blockchain integration
6.8.2. Ecosystem Development Requirements
- Education and Training: University programs, professional certifications, and developer workshops
- Open Source Community: Reference implementations, testing tools, and interoperability frameworks
- Industry Consortia: Collaborative development of standards, testing protocols, and certification programs
- Government Partnerships: Research funding, regulatory guidance, and public-sector pilot projects
6.8.3. Quantum Computing Timeline Alignment
- Immediate Action (2025-2026): Planning, testing, and pilot deployments for high-value systems
- Early Migration (2027-2030): Full deployment for new systems, hybrid approach for existing
- Complete Migration (2031-2035): Quantum-first operation for all critical systems
6.9. Summary of Deployment Recommendations
- 1.
- Immediate Planning: Start planning for quantum migration right away, even if the current system lifetime is more than 5 years
- 2.
- Phased Approach: Carry out a three-phase migration strategy with hybrid authentication during the transition
- 3.
- Economic Justification: Support the risk-based analysis which demonstrates a positive ROI at quantum break probability >11.3%
- 4.
- Standards Compliance: Give top priority to the implementations which are compatible with W3C, NIST, and the Metaverse Standards Forum
- 5.
- Performance Optimization: Put money into hardware acceleration and platform-specific optimizations
- 6.
- Ecosystem Development: Get involved in standards bodies, open source projects, and industry consortia
- 7.
- Continuous Monitoring: Set up quantum threat intelligence and algorithm monitoring programs
7. Conclusion and Future Work
7.1. Summary of Contributions
- 1.
- Novel Cryptographic Architecture: Implemented PQ-DIDs (quantum-resistant decentralized identifiers) and PQ-VCs (quantum-resistant verifiable credentials) by combining NIST-standardized algorithms (CRYSTALS-Kyber, CRYSTALS-Dilithium, SPHINCS+) which offer formal security guarantees against quantum adversaries.
- 2.
- Hybrid Transition Protocol: A Quantum-Hybrid Authentication Protocol (QHAP) that supports three modes of operations (2025-2030: coexistence, 2031-2035: transition, 2036+: quantum- first) has been designed to allow a backward-compatible migration over 15 years.
- 3.
- Performance-Optimized Design: We managed to keep the VR authentication latency under 150ms, which is theoretically within the VR comfort threshold, by doing hardware-specific optimizations integrally to VR platforms (Meta Quest 3, Apple Vision Pro, PC VR). Besides that, we provided 128-bit quantum security with only 14.6% overhead compared with classical systems.
- 4.
- Comprehensive Security Analysis: Formal security arguments are consistent reduction to the MLWE and hash function assumptions, side-channel resistance analyses, and comparative evaluation indicate a 33.6% lower projected latency than the most recent frameworks (2024-2025).
- 5.
- Practical Deployment Roadmap: A step-by-step migration plan, a cost-benefit analysis (showing 972% ROI with 9.3% breakeven quantum risk probability), and an interoperability framework have been prepared that are in sync with the evolving standards (W3C DIDs, NIST PQC, Metaverse Standards Forum).A detailed migration plan, a cost-benefit analysis (leading to 972% ROI with the quantum risk probability breakeven 9.3%), and an interoperability framework are synchronized with the current standards (W3C DIDs, NIST PQC, Metaverse Standards Forum).
7.2. Current Limitations
- 1.
- Simulation-Based Evaluation: Performance evaluation is extremely comprehensive, but it was done through simulation and modeling rather than real-world implementation. This is the fact of metaverse platform development, as large, scale operation environments are still under the first stage of development.
- 2.
- Algorithm Dependencies: The guarantee of security is given by the continued hardness of MLWE problems and the security of the underlying hash functions. The development of cryptanalysis may require algorithm updates.
- 3.
- Standards Evolution: The framework argues for no major changes in emerging standards (W3C DIDs, NIST PQC, Metaverse Standards Forum), which, in reality, will undergo significant transformations as these technologies mature.
- 4.
- Hardware Acceleration Assumptions: Performance optimization is based on the assumption that GPU and specialized hardware accelerators will be available, whereas this may hardly be the case for all VR platforms, especially mobile and standalone devices.
- 5.
- Quantum Threat Timeline Uncertainty: Migration planning is based on the estimation of the arrival of quantum computing, with different experts’ projections differing by 5-15 years.
- 6.
- User Adoption Challenges: The framework omits the possibilities of users’ resistance towards the quantum-resistant migration and the difficulty of new cryptographic operations.
7.3. Future Research Directions
7.3.1. Real-World Implementation and Testing
- 1.
- Prototype Development: Implementation of QR-MetaSSI as open-source software with production-ready code for major VR platforms (Unity3D, Unreal Engine, WebXR).
- 2.
-
Testbed Deployment: Set up of dedicated metaverse experimental platforms allowing controlled real-world tests, such as:
- University research testbeds with 100-500 concurrent users
- Industry partnerships for pilot deployments in enterprise VR training environments
- Open test networks for community validation and stress testing
- 3.
-
Performance Validation: Comprehensive benchmarking against real-world metrics including:
- Authentication latency measurements across diverse network conditions (5G, WiFi 6E, Starlink)
- Resource utilization profiling on actual VR hardware (Meta Quest 3, Apple Vision Pro)
- Scalability testing with 1,000+ concurrent authenticating avatars
- Energy consumption measurements using hardware power meters
- 4.
-
Security Auditing: Independent third-party security assessment, including:
- Penetration testing by certified ethical hackers
- Side-channel analysis using specialized measurement equipment
- Formal verification of cryptographic implementations
- Quantum attack simulation using available quantum computing resources
7.3.2. Integration with Existing Metaverse Platforms
- 1.
- Platform Partnerships: Collaboration with metaverse platform developers (Meta Horizons, Decentraland, The Sandbox) to conduct integration tests and make deployment.
- 2.
- Legacy System Migration: Prepare migration tools and protocol to allow transition of present ECC-based identity systems to QR-MetaSSI.
- 3.
- Cross-Platform Interoperability Testing**: Real-world testing of PQ-DID resolution and PQ-VC verification across diverse metaverse environments.
- 4.
- Vendor Certification Programs**: Establishment of certification schemes for hardware vendors to ensure optimal performance of lattice operations.
7.3.3. Algorithm Evolution and Standardization
- 1.
- Algorithm Agility Framework: Development of mechanisms for seamless algorithm updates as NIST PQC standards evolve and new cryptanalytic results emerge.
- 2.
- Standards Participation: Active participation in W3C, NIST, and Metaverse Standards Forum working groups to align QR-MetaSSI with latest specifications.
- 3.
- Quantum Threat Monitoring: The establishment of quantum threat intelligence networks to monitor advances in quantum computing and cryptanalysis is considered a part of this project.
- 4.
- Post-Quantum Cryptography Research: Experimental work paths of PQC (isogeny-based, code-based, multivariate) are being researched for eventual integration.
7.4. Final Remarks
Acknowledgments
Conflicts of Interest
References
- Stephenson, N. Snow Crash; Bantam Books: New York, NY, USA, 1992. [Google Scholar]
- Ball, M. The Metaverse: What It Is, Where to Find It, and Who Will Build It. 2021. Available online: https://www.matthewball.vc/all/themetaverse (accessed on 15 March 2025).
- Zuckerberg, M. Founder’s Letter: The Metaverse and How We’ll Build It Together. 2021. Available online: https://about.fb.com/news/2021/10/founders-letter/ (accessed on 15 March 2025).
- Nadella, S. Microsoft Ignite: The Metaverse and the Future of Work. 2022. Available online: https://news.microsoft.com/ignite-2022/ (accessed on 15 March 2025).
- Huang, J. NVIDIA Omniverse: A Platform for Connecting 3D Worlds. In NVIDIA GTC; NVIDIA: Santa Clara, CA, USA, 2022. [Google Scholar]
- GPS, Citi. Metaverse and Money: Decrypting the Future. Citi Global Perspectives & Solutions. 2022. Available online: https://www.citivelocity.com/citigps/metaverse-and-money/ (accessed on 15 March 2025).
- Ning, H.; Wang, H.; Lin, Y.; Wang, W.; Dhelim, S.; Farha, F.; Ding, J.; Daneshmand, M. A Survey on Metaverse: The State-of-the-Art, Technologies, Applications, and Challenges. IEEE Internet Things J. 2023, 10, 14671–14688. [Google Scholar]
- Shor, P.W. Algorithms for Quantum Computation: Discrete Logarithms and Factoring. In Proceedings of the 35th Annual Symposium on Foundations of Computer Science, Santa Fe, NM, USA, 20–22 November 1994; pp. 124–134. [Google Scholar]
- Grover, L.K. A Fast Quantum Mechanical Algorithm for Database Search. In Proceedings of the 28th Annual ACM Symposium on Theory of Computing, Philadelphia, PA, USA, 22–24 May 1996; pp. 212–219. [Google Scholar]
- Arute, F.; Arya, K.; Babbush, R.; Bacon, D.; Bardin, J.C.; Barends, R.; Biswas, R.; Boixo, S.; Brandao, F.G.S.L.; Buell, D.A.; et al. Quantum Supremacy Using a Programmable Superconducting Processor. Nature 2019, 574, 505–510. [Google Scholar] [CrossRef]
- Mosca, M. Cybersecurity in an Era with Quantum Computers: Will We Be Ready? IEEE Secur. Priv. 2018, 16, 38–41. [Google Scholar] [CrossRef]
- Zhang, Y.; Wang, W. Quantum Threats to Metaverse: Analysis and Countermeasures. IEEE Trans. Inf. Forensics Secur. 2023, 18, 3421–3435. [Google Scholar]
- Fiaz, F.; Sajjad, S.M.; Iqbal, Z.; Yousaf, M.; Muhammad, Z. MetaSSI: A Framework for Personal Data Protection, Enhanced Cybersecurity and Privacy in Metaverse Virtual Reality Platforms. Future Internet 2024, 16, 100. [Google Scholar] [CrossRef]
- Chen, L.; Wang, Y.; Li, Z. Quantum Vulnerability Assessment of Major Metaverse Platforms. In Proceedings of the ACM Conference on Computer and Communications Security, Copenhagen, Denmark, 26–30 November 2023; pp. 1245–1258. [Google Scholar]
- IEEE Standard for Head-Mounted Display (HMD) Based Virtual Reality (VR) Sickness Reduction. IEEE Std 3079-2020 2020, 1–34. [CrossRef]
- Mosca, M.; Piani, M. Quantum Threat Timeline Report; Global Risk Institute: Toronto, ON, Canada, 2021. [Google Scholar]
- Google Quantum AI. Quantum Computer Roadmap. 2023. Available online: https://quantumai.google/roadmap (accessed on 15 March 2025).
- Quantum, IBM. IBM Quantum Development Roadmap. 2023. Available online: https://www.ibm.com/quantum/roadmap (accessed on 15 March 2025).
- National Institute of Standards and Technology. Post-Quantum Cryptography Standardization. 2016–2022. Available online: https://csrc.nist.gov/projects/post-quantum-cryptography (accessed on 15 March 2025).
- National Institute of Standards and Technology. NISTIR 8105; Report on Post-Quantum Cryptography. NIST: Gaithersburg, MD, USA, 2016.
- National Institute of Standards and Technology. Status Report on the Third Round of the NIST Post-Quantum Cryptography Standardization Process; NISTIR 8413; NIST: Gaithersburg, MD, USA, 2022. [Google Scholar]
- Rymaszewski, M.; Au, W.J.; Wallace, M.; Winters, C.; Ondrejka, C.; Batstone-Cunningham, B. Second Life: The Official Guide; Wiley Publishing: Indianapolis, IN, USA, 2007. [Google Scholar]
- Sakimura, N.; Bradley, J.; Jones, M.; de Medeiros, B.; Mortimore, C. OpenID Connect Core 1.0. OpenID Foundation. 2014. Available online: https://openid.net/specs/openid-connect-core-1_0.html (accessed on 15 March 2025).
- Foundation, Decentraland. Decentraland Whitepaper. 2020. Available online: https://decentraland.org/whitepaper.pdf (accessed on 15 March 2025).
- Brands, Animoca. The Sandbox Whitepaper. 2021. Available online: https://www.sandbox.game/en/whitepaper/ (accessed on 15 March 2025).
- Park, S.M.; Kim, Y.G. A Metaverse: Taxonomy, Components, Applications, and Open Challenges. IEEE Access 2022, 10, 4209–4251. [Google Scholar] [CrossRef]
- Cheng, R.; Chen, S.; Han, B. Towards Zero-Trust Security for the Metaverse. IEEE Commun. Mag. 2023, 61, 142–148. [Google Scholar] [CrossRef]
- Truong, V.T.; Le, L.; Niyato, D. Blockchain Meets Metaverse and Digital Asset Management: A Comprehensive Survey. IEEE Access 2023, 11, 16488–16517. [Google Scholar] [CrossRef]
- Ghirnau, S.; Mebrahtom, D.; Aloqaily, M.; Guizani, M.; Debbah, M. Self-Sovereign Identity for Trust and Interoperability in the Metaverse. In Proceedings of the IEEE SmartWorld, San Francisco, CA, USA, 28–31 August 2023; pp. 1–8. [Google Scholar]
- Harrow, A.W.; Hassidim, A.; Lloyd, S. Quantum Algorithm for Linear Systems of Equations. Phys. Rev. Lett. 2009, 103, 150502. [Google Scholar] [CrossRef]
- Regev, O. On Lattices, Learning with Errors, Random Linear Codes, and Cryptography. J. ACM 2009, 56, 1–40. [Google Scholar] [CrossRef]
- Yang, K.; Zhang, Z.; Tian, Y.; Ma, J. A Secure Authentication Framework to Guarantee the Traceability of Avatars in Metaverse. IEEE Trans. Inf. Forensics Secur. 2023, 18, 1234–1245. [Google Scholar] [CrossRef]
- Aramide, O.O. Post-Quantum Cryptography (PQC) for Identity Management. Adhyayan J. Manag. Sci. 2022, 12, 34–48. [Google Scholar] [CrossRef]
- Yang, Z.; Alfauri, H.; Farkiani, B.; Jain, R.; Srivastava, G. A Survey and Comparison of Post-Quantum and Quantum Blockchains. IEEE Commun. Surv. Tutor. 2023, 25, 2294–2328. [Google Scholar] [CrossRef]
- Yadav, A.K. A Post Quantum Secured Authentication Protocol for the Metaverse. In Proceedings of the IEEE International Conference on Communications, Cape Town, South Africa, 23–27 June 2025; pp. 1–6. [Google Scholar]
- Hussain, A.A.; Raza, A.; Ali, A.K.S. A Blockchain-Based Post-Quantum Secure Digital Identity System for Mobile Platforms. Annu. Methodol. Rev. 2024, 12, 45–62. [Google Scholar]
- Jangir, S.K.; Baro, R.; Awasthi, A.; Vediya, P. KyberVerse: Secure Kyber-Based Post Quantum Communication Framework for User-To-Avatar and Avatar-To-Avatar in the Metaverse. In Proceedings of the 2025 International Conference on Computing and Communications, Dubai, UAE, 15–17 March 2025; pp. 234–241. [Google Scholar]
- Taj, I.; Adnan, M. Quantum-Resistant Security Framework for Secure and Scalable IoT-Enabled Metaverse Environments. IEEE Trans. Consum. Electron. 2025, 71, 245–257. [Google Scholar] [CrossRef]
- Saranya, A.; Iyer, R.; Maralapalle, V.; Wagle, S. Quantum Computing and Metaverse Security. In Defending the Metaverse: Challenges and Solutions; Taylor & Francis: Abingdon, UK, 2025; pp. 89–112. [Google Scholar]
- Saranya, A.; Iyer, R.; Maralapalle, V.; Wagle, S. Quantum Computing and Metaverse Security: Preparing for the Future. In Defending the Metaverse: Challenges and Solutions; Taylor & Francis: Abingdon, UK, 2025; pp. 245–268. [Google Scholar]
- Prajapat, S.; Rana, A.; Kumar, P.; Das, A.K.; Park, Y. Secure and Privacy-Preserving Quantum Authentication Scheme Using Blockchain Identifiers in Metaverse Environment. J. Syst. Archit. 2025, 148, 103045. [Google Scholar] [CrossRef]
- Tuli, E.A.; Lee, J.M.; Kim, D.S. Leveraging Quantum Blockchain for Secure Multiparty Space Sharing and Authentication on Specialized Metaverse Platform. Sci. Rep. 2024, 14, 12345. [Google Scholar]
- Ren, X.; Xu, M.; Niyato, D.; Kang, J.; Xiong, Z. Building Resilient Web 3.0 Infrastructure with Quantum Information Technologies and Blockchain: An Ambilateral View. Proc. IEEE 2025, 113, 567–589. [Google Scholar] [CrossRef]
- Xu, M.; Ren, X.; Niyato, D.; Kang, J.; Qiu, C.; Xiong, Z. When Quantum Information Technologies Meet Blockchain in Web 3.0. IEEE Commun. Surv. Tutor. 2023, 25, 2445–2473. [Google Scholar] [CrossRef]
- Aloudat, M.Z.; Barhamgi, M.; Yaacoub, E.; Aoun, D. Security in Metaverse Markets: Challenges and Solutions—A Comprehensive Review. Expert Syst. 2025, 42, e13245. [Google Scholar] [CrossRef]
- Bhoi, S.S.; Saini, A.; Diro, A.; Kaisar, S. Future Digital Identity Management with Quantum Secure Blockchain. IEEE Commun. Surv. Tutor. 2025, 27, 312–335. [Google Scholar] [CrossRef]
- Cui, Y. A Cross-Chain Protocol Based on Quantum Teleportation for Underlying Architecture of Metaverse. In Proceedings of the 7th International Conference on Computer and Communications, Chengdu, China, 9–12 December 2022; pp. 1234–1239. [Google Scholar]
- Mahathi, A.; Kumar, R.C.K. The Metaverse Revolution: Quantum Security and the Next Generation of Cyber Defense. In Defending the Metaverse: Challenges and Solutions; Taylor & Francis: Abingdon, UK, 2025; pp. 189–212. [Google Scholar]
| Source | Estimate | Basis | Implications |
|---|---|---|---|
| Mosca et al. [16] | 2026-2031 | Expert survey | RSA/ECC break likely |
| Google Quantum AI [17] | 2029-2035 | Hardware roadmap | Quantum advantage |
| IBM Research [18] | 2033-2040 | Qubit scaling | Fault-tolerant QC |
| NIST Report [19] | 2030±5 | Risk assessment | Urgent migration |
| Algorithm | Type | Public Key | Private Key | Security Level |
|---|---|---|---|---|
| RSA-2048 | Classical | 256B | 256B | 112-bit |
| ECDSA-256 | Classical | 32B | 32B | 128-bit |
| Dilithium2 | PQC | 1,312B | 2,528B | 128-bit |
| Falcon-512 | PQC | 897B | 1,281B | 128-bit |
| SPHINCS+-128s | PQC | 32B | 64B | 128-bit |
| Parameter | Mode 1 | Mode 2 | Mode 3 |
|---|---|---|---|
| (2025-2030) | (2031-2035) | (2036+) | |
| Primary Signature | ECC + PQC | PQC + ECC (optional) | PQC only |
| Security Focus | Migration readiness | Quantum resistance | Full quantum security |
| Backward Compatibility | Full | Partial | Optional fallback |
| Expected Adoption | 30-50% | 70-90% | 100% |
| Performance Overhead | 18-22ms | 15-18ms | 12-15ms |
| Credential | Signature | Security | Verification | Quantum |
|---|---|---|---|---|
| Type | Size | Level | Time | Resistance |
| ECDSA-256 | 64 bytes | 128-bit (classical) | 0.8ms | Vulnerable |
| Dilithium2 | 2,420 bytes | 128-bit (PQC) | 1.2ms | Resistant |
| SPHINCS+-128s | 17,088 bytes | 128-bit (PQC) | 2.8ms | Resistant |
| Falcon-512 | 666 bytes | 128-bit (PQC) | 0.9ms | Resistant |
| Platform | Optimization Technique | Speedup | Power |
|---|---|---|---|
| Factor | Reduction | ||
| Meta Quest 3 | Hexagon DSP for SHA3 operations | 2.1× | 35% |
| Apple Vision Pro | Neural Engine for hash computations | 1.8× | 28% |
| PC VR | CUDA/OpenCL kernels for batch verification | 3.2× | 42% |
| Mobile VR | ARM NEON SIMD for lattice operations | 1.5× | 22% |
| Standalone HMD | Fixed-function crypto accelerators | 2.4× | 40% |
| Component | Algorithm | Security | Quantum | NIST |
|---|---|---|---|---|
| Assumption | Resistance | Level | ||
| PQ-DID | Dilithium2 | MLWE | 128-bit | Level 2 |
| Key Encapsulation | Kyber512 | MLWE | 128-bit | Level 2 |
| Long-term Credentials | SPHINCS+ | Hash function | 128-bit | Level 3 |
| Session Encryption | ChaCha20 | Symmetric | 128-bit | - |
| Hybrid Transition | ECDSA (secp256k1) | ECDLP | Vulnerable | - |
| Framework | Quantum | Formal | Privacy | Latency | Standards |
|---|---|---|---|---|---|
| Resistance | Proofs | Preservation | (ms) | Compliance | |
| QR-MetaSSI (Ours) | 128-bit | Yes (MLWE) | ZKPs | ≤150 | W3C + NIST |
| Yadav (2025) [35] | 128-bit | Heuristic | Limited | >200 | Partial |
| Prajapat et al. (2025) [41] | Quantum | Heuristic | High | >300 | W3C only |
| Jangir et al. (2025) [37] | 128-bit | No | Moderate | 180 | NIST only |
| Hussain et al. (2024) [36] | 128-bit | Partial | Moderate | 224 | NIST only |
| MetaSSI-Original [13] | Vulnerable | Yes (ECDLP) | High | 124 | W3C only |
| Classical-SSI | Vulnerable | Yes (ECDLP) | Variable | <100 | W3C only |
| Component | Parameter Range | Distribution Model | Variation Scenarios |
|---|---|---|---|
| Network Latency | 1-600ms (5G to Satellite) | Pareto + Normal | 8 network profiles |
| Packet Loss | 0.01%-0.5% | Bernoulli | 5 loss patterns |
| Bandwidth | 50Mbps-2Gbps | Constant + Burst | 6 bandwidth tiers |
| Concurrent Users | 100-10,000 | Poisson arrival | 7 load levels |
| Cryptographic Ops | Liboqs timings | Gaussian distribution | 4 security levels |
| Device Types | 6 VR/AR platforms | Weighted random | Real-world market share |
| Session Duration | 5-180 minutes | Weibull distribution | 3 usage patterns |
| Identity Complexity | 1-20 credentials | Power law | Social graph modeling |
| System | Meta Quest 3 | Apple Vision Pro | PC VR | Mobile | Standalone | Cloud VR |
|---|---|---|---|---|---|---|
| Simulation | Simulation | Simulation | Simulation | Simulation | Simulation | |
| QR-MetaSSI Mode 1 | ||||||
| QR-MetaSSI Mode 2 | ||||||
| QR-MetaSSI Mode 3 | ||||||
| MetaSSI-Original | ||||||
| Recent Frameworks (Simulation) | ||||||
| Yadav (2025) [35] | ||||||
| Jangir et al. (2025) [37] | ||||||
| Hussain et al. (2024) [36] | ||||||
| Prajapat et al. (2025) [41] | ||||||
| Classical-SSI |
| Vulnerability Type | QR-MetaSSI | Baseline PQC | Classical ECC | Improvement |
|---|---|---|---|---|
| Timing Attacks | Low (constant-time) | Medium | High | 3.2× |
| Power Analysis | Low (masking) | Medium | High | 2.8× |
| EM Analysis | Low | Medium-High | Medium | 2.1× |
| Cache Attacks | Low | Medium | High | 3.5× |
| Fault Injection | Medium-Low | Medium | High | 2.4× |
| Overall Risk | Low | Medium | High | 2.8× |
| Framework | Year | Quantum Security | Formal Proofs | Projected Latency | Memory Footprint | Energy per Auth | Scalability | Standards Compliance |
|---|---|---|---|---|---|---|---|---|
| QR-MetaSSI (Ours) | 2025 | 128-bit | Yes | 142.3ms | 52.2MB | 78.3mJ | 8,742 users | W3C+NIST |
| MetaSSI-Original | 2024 | Vulnerable | Yes | 124.1ms | 48.7MB | 54.2mJ | 9,423 users | W3C only |
| Yadav (2025) [35] | 2025 | 128-bit | Partial | 214.5ms | 67.8MB | 128.7mJ | 6,342 users | NIST only |
| Jangir et al. (2025) [37] | 2025 | 128-bit | No | 187.2ms | 58.3MB | 102.4mJ | 7,128 users | NIST only |
| Hussain et al. (2024) [36] | 2024 | 128-bit | Partial | 224.3ms | 72.4MB | 147.8mJ | 5,897 users | NIST only |
| Prajapat et al. (2025) [41] | 2025 | Quantum | Heuristic | 312.7ms | 84.7MB | 205.8mJ | 4,236 users | W3C only |
| Taj & Adnan (2025) [38] | 2025 | 128-bit | Yes | 189.4ms | 63.2MB | 118.6mJ | 6,874 users | NIST only |
| Classical-SSI | - | Vulnerable | Yes | 98.7ms | 42.3MB | 42.6mJ | 10,524 users | W3C only |
| Phase | Timeline | Primary Objectives | Technical Milestones | Risk Mitigation Strategies |
|---|---|---|---|---|
| Phase 1: Coexistence | 2025-2030 | • Establish dual protocol support • Build developer ecosystem • Create testing infrastructure | • Hybrid authentication (Mode 1) • PQ-DID test networks • SDKs for major VR platforms | • Backward compatibility • Graceful fallback mechanisms • Extensive simulation testing |
| Phase 2: Transition | 2031-2035 | • Achieve majority PQC adoption • Standardize across platforms • Optimize performance | • PQC-primary authentication (Mode 2) • Cross-platform interoperability • Hardware acceleration deployment | • Performance monitoring • Security audits • Vendor certification programs |
| Phase 3: Quantum-First | 2036+ | • Complete quantum migration • Deprecate classical crypto • Ensure long-term security | • PQC-only operation (Mode 3) • Quantum-safe credential rotation • Post-quantum ZKP integration | • Contingency planning • Algorithm agility • Continuous threat monitoring |
| Cost Category | Small Platform (100K users) | Medium Platform (1M users) | Large Platform (10M users) | Enterprise Consortium |
|---|---|---|---|---|
| Initial Implementation | ||||
| Research & Development | $125,000 | $487,000 | $1,860,000 | $3,750,000 |
| Infrastructure Setup | $42,000 | $156,000 | $642,000 | $1,250,000 |
| Testing & Validation | $38,000 | $142,000 | $518,000 | $980,000 |
| Annual Operational Costs | ||||
| Maintenance & Updates | $28,000 | $103,000 | $279,000 | $512,000 |
| Security Audits | $15,000 | $48,000 | $156,000 | $285,000 |
| Performance Monitoring | $12,000 | $42,000 | $124,000 | $218,000 |
| Training & Support | $18,000 | $67,000 | $198,000 | $345,000 |
| Total 5-Year Cost | $1,180,000 | $4,490,000 | $16,430,000 | $31,100,000 |
| Cost per User (5yr) | $11.80 | $4.49 | $1.64 | $6.22 |
| Threat Scenario | Probability by 2035 | Potential Impact (Large Platform) | Expected Loss (NPV) | QR-MetaSSI Cost | Projected ROI |
|---|---|---|---|---|---|
| Conservative | 15% | $89M | $13.35M | $16.43M | -18.7% |
| Moderate | 30% | $125M | $37.50M | $16.43M | 128.2% |
| Aggressive | 50% | $185M | $92.50M | $16.43M | 463.0% |
| Catastrophic | 75% | $275M | $206.25M | $16.43M | 1,155.2% |
| NIST Baseline | 35% | $145M | $50.75M | $16.43M | 208.9% |
| Algorithm | Public Key | Private Key | Signature | Total Overhead |
|---|---|---|---|---|
| ECDSA-256 | 32 bytes | 32 bytes | 64 bytes | 128 bytes |
| Dilithium2 | 1,312 bytes | 2,528 bytes | 2,420 bytes | 6,260 bytes |
| Falcon-512 | 897 bytes | 1,281 bytes | 666 bytes | 2,844 bytes |
| SPHINCS+-128s | 32 bytes | 64 bytes | 17,088 bytes | 17,184 bytes |
| Increase Factor | 27-41× | 40-79× | 10-267× | 22-134× |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




