Submitted:
27 March 2026
Posted:
27 March 2026
Read the latest preprint version here
Abstract
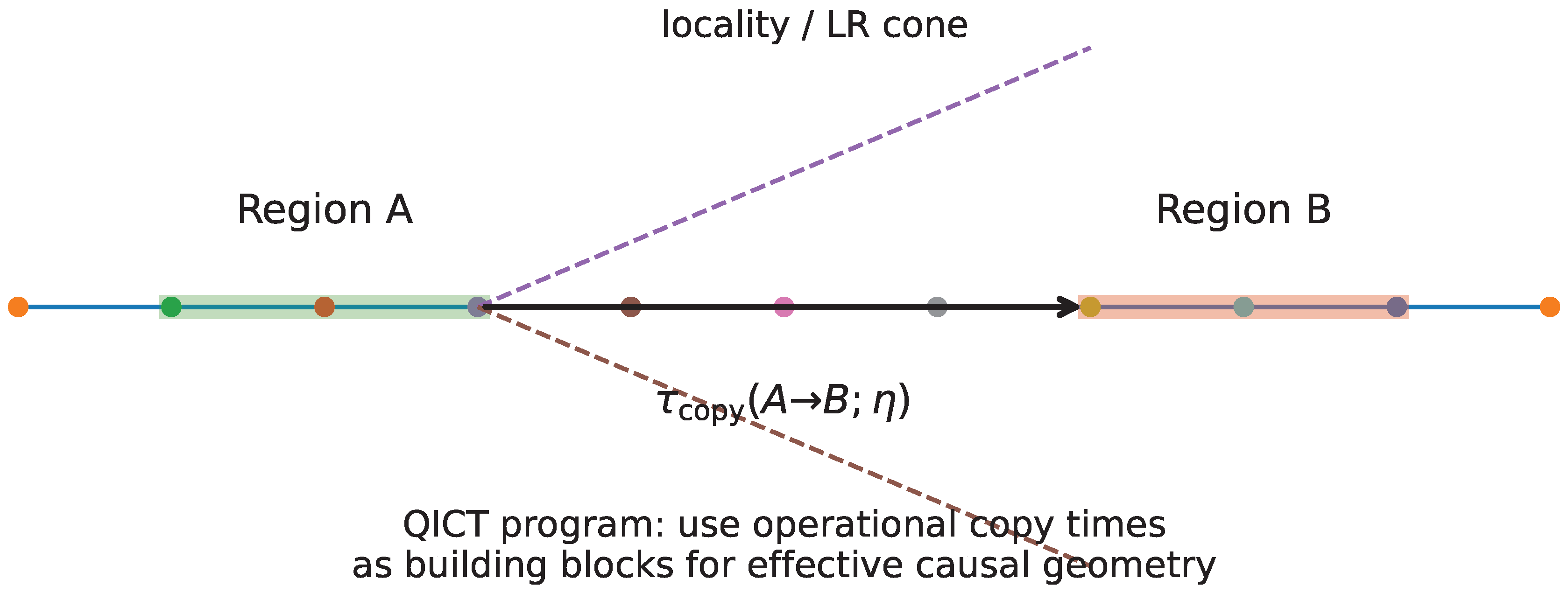
We introduce an operational transport latency, quantum information copy time: the earliesttime at which a receiver confined to a region B can certify, with prescribed advantage, whichof two global hypotheses was prepared by local operations in a distant sender region A. The benchmark quantity is information-theoretic—the Helstrom advantage on B, namely the tracedistance between the reduced states—and it also admits receiver-restricted refinements that makemeasurement constraints explicit, including few-body and moment-channel receivers. We derivethe corresponding kinematic locality constraints for Hamiltonian and Lindbladian dynamicswith Lieb–Robinson tails, as well as for circuits and quantum cellular automata with strictlight cones. We then establish the theorem-level anchor of the manuscript in the quantumsymmetric simple exclusion process (Q-SSEP): for locally prepared charge-biased hypotheses,the Helstrom copy time obeys an unconditional diffusion-limited lower bound expressed in termsof the diffusion constant D and the static susceptibility χ. For closed Hamiltonian systems,we formulate a projection-based reduction in which the operational scaling statement is made conditional on explicit, diagnostically checkable hypotheses, thereby separating what is provedmicroscopically from what is inferred in a controlled hydrodynamic window. We complement the analytical framework with exact-diagonalization diagnostics in the XXZ chain and with abundled TEBD/MPS reference protocol plus validation suite (Supplementary S2 and Code SC1),explicitly cross-validated against exact evolution at small sizes. In the strengthened submissionwe add three robustness layers beyond the original ED figures: an eight-size common-windowtransport sweep for the nonintegrable XXZ structure-factor diagnostic, an extractor-robustness check comparing first-crossing and sustained-crossing copy-time rules on the same Helstrom dataset, and a receiver-side validation dataset showing when a simple block-charge measurement saturates the Helstrom advantage in a controlled conserving reference model. Finally, we comparecopy time with scrambling diagnostics based on out-of-time-ordered correlators and show how conservation laws can delay certifiability well beyond the ballistic operator-growth front without any contradiction with locality.
Keywords:
1. Introduction
Main contributions.
- C1.
- Operational framework. We define receiver advantage and copy time as a task-defined latency, and we provide a receiver-class refinement that makes measurement restrictions explicit (Section 2.1).
- C2.
- Minimal locality constraints. For Hamiltonian/Lindbladian dynamics with Lieb–Robinson tails and for circuits/QCAs with strict light cones, we derive a kinematic lower bound on copy time that isolates the threshold dependence and constants (Section 3).
- C3.
- A rigorous diffusive benchmark (Q-SSEP). In the controlled, locality-preserving quantum symmetric simple exclusion process (Q-SSEP), we prove an unconditional lower bound of the formwhere , D is the diffusion constant of the conserved density, and is the associated static susceptibility. This furnishes a theorem-level instance in which diffusion-limited Helstrom copying is established directly from microscopic dynamics (Section 6; Supplementary S3).
- C4.
- Hydrodynamic reduction for unitary systems. For closed Hamiltonian dynamics we formulate a projection-based route from charge bias to receiver advantage and identify the concrete hypotheses under which a single slow transport pole controls the operational signal (Section 4 and Section 5). The resulting statement is organized so that each required ingredient admits a direct diagnostic proxy.
- C5.
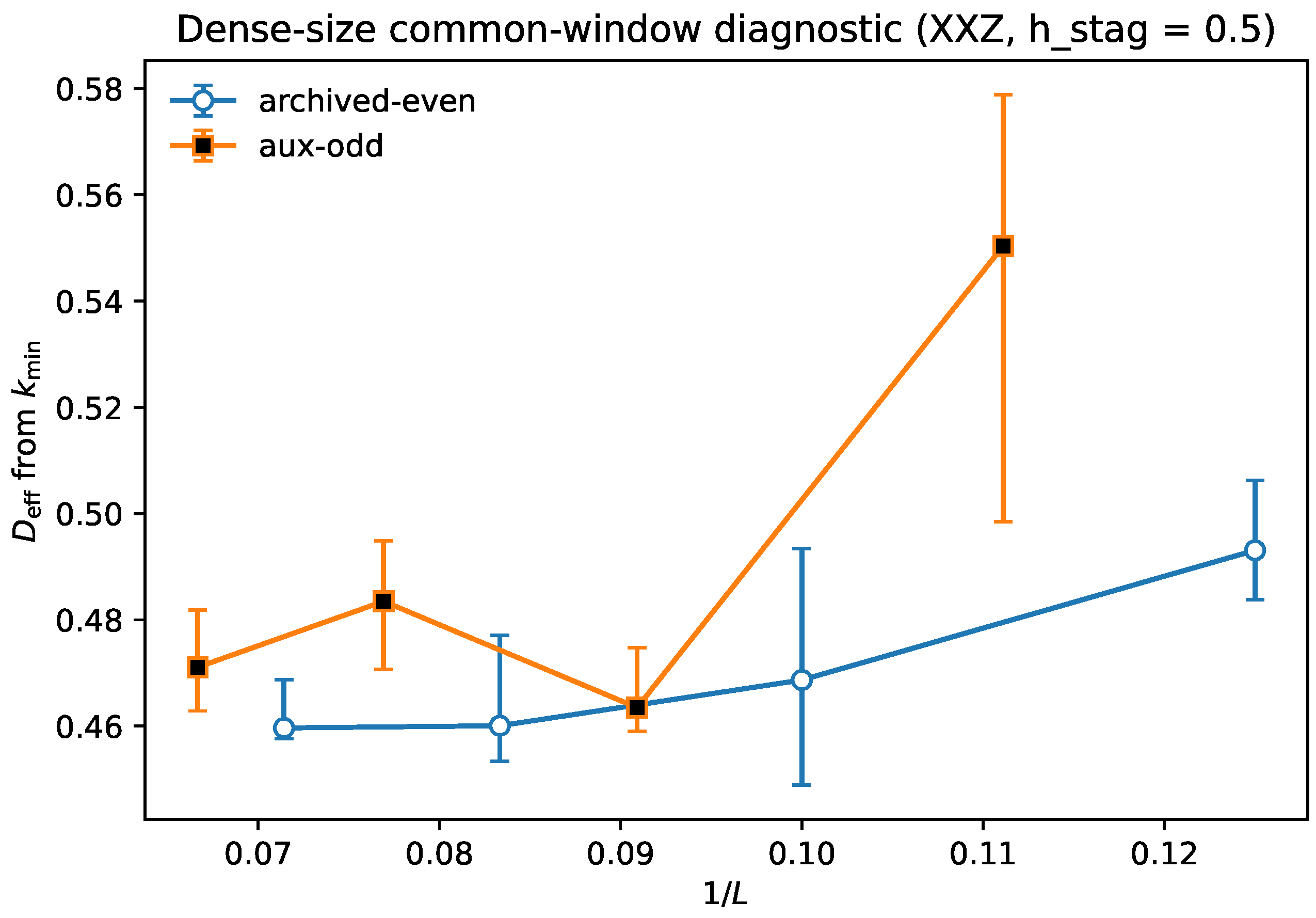
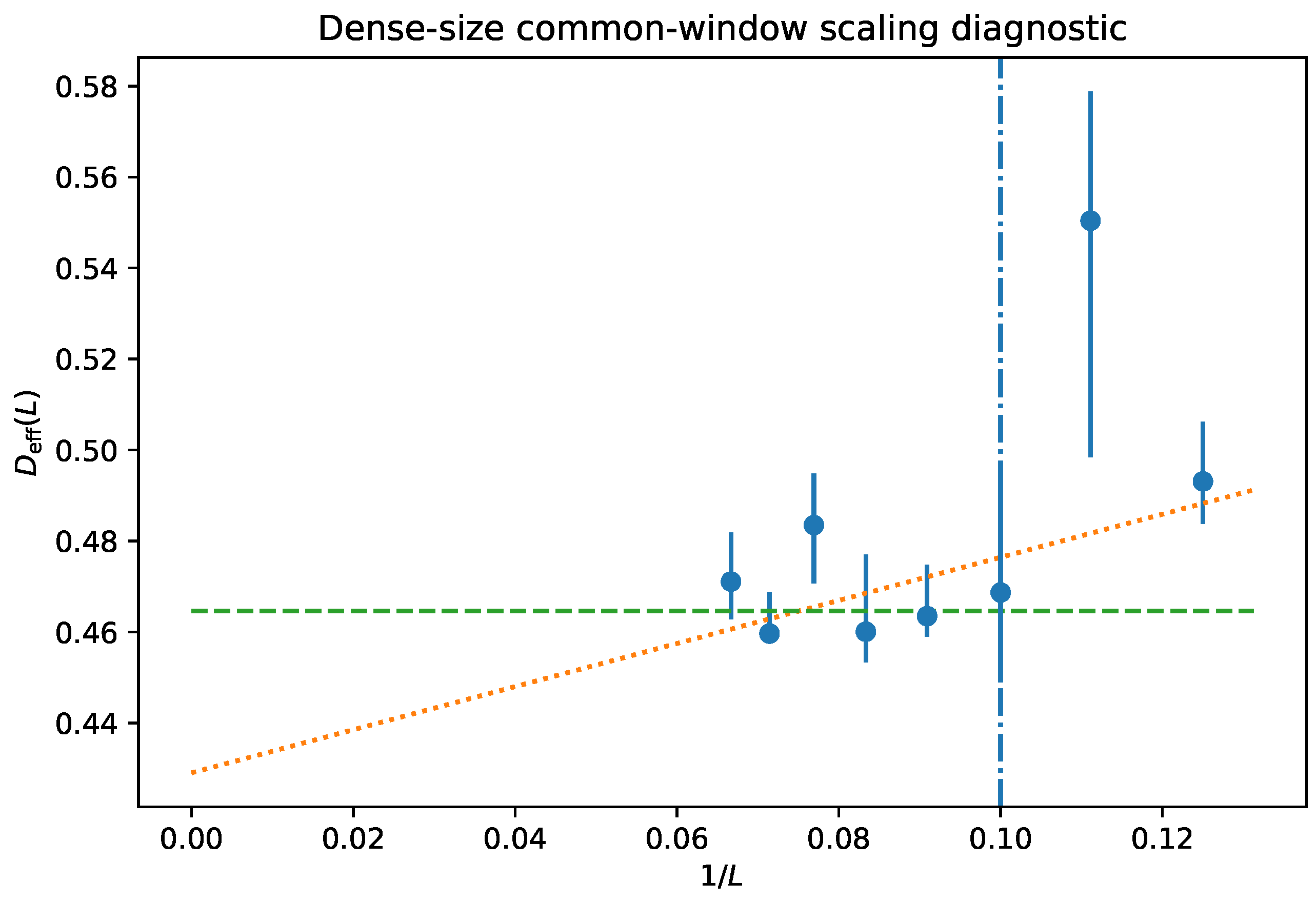
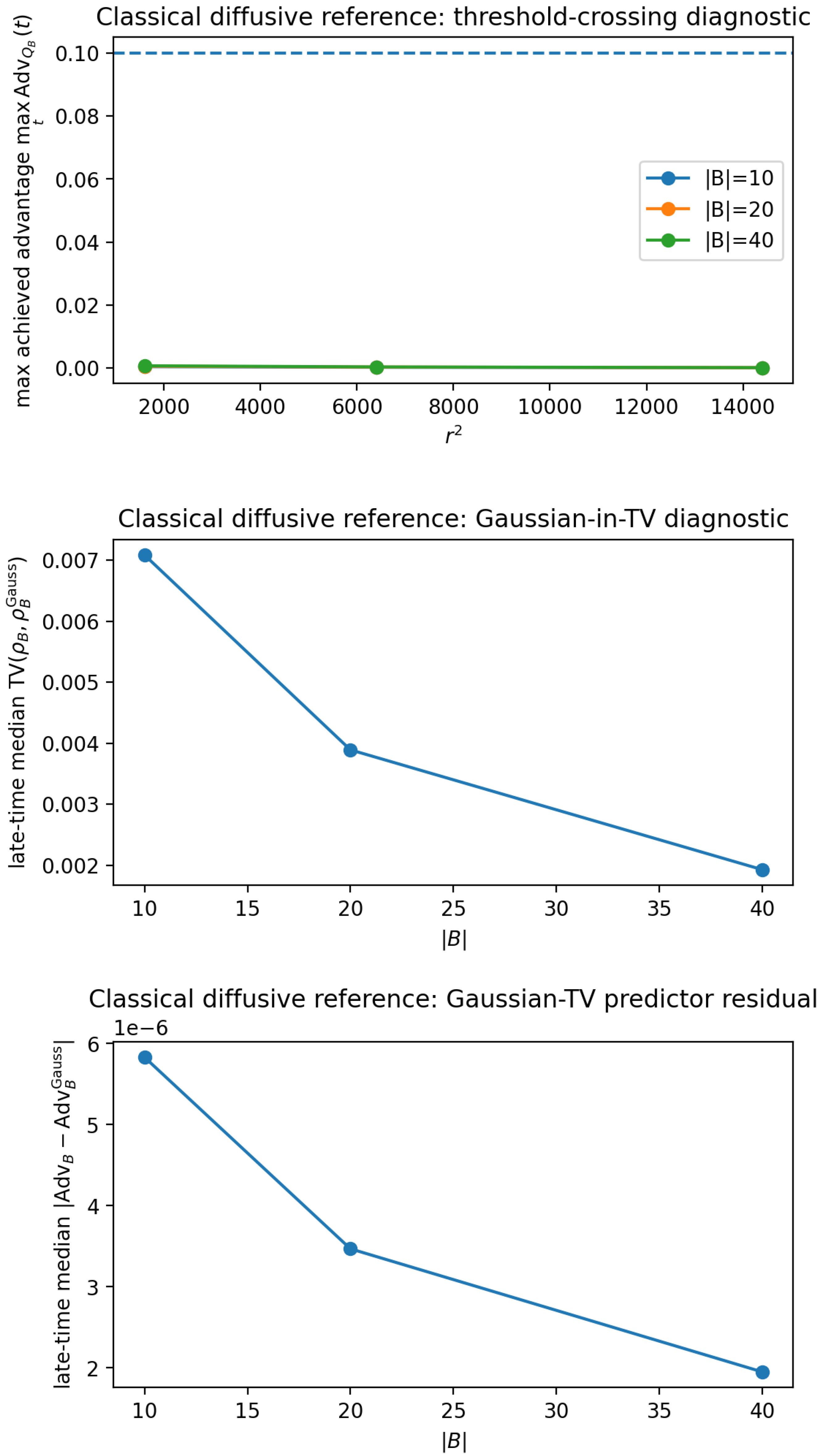
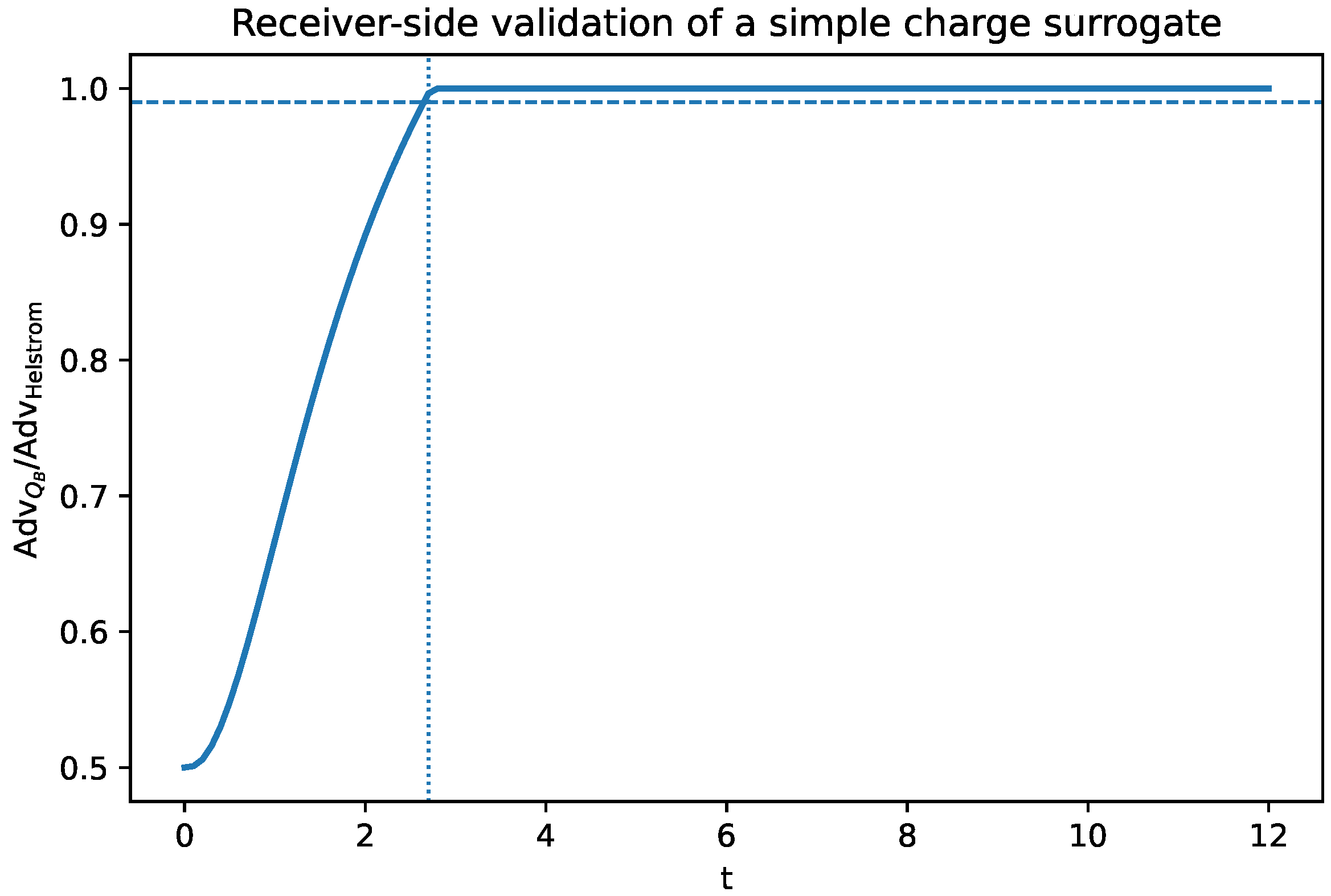
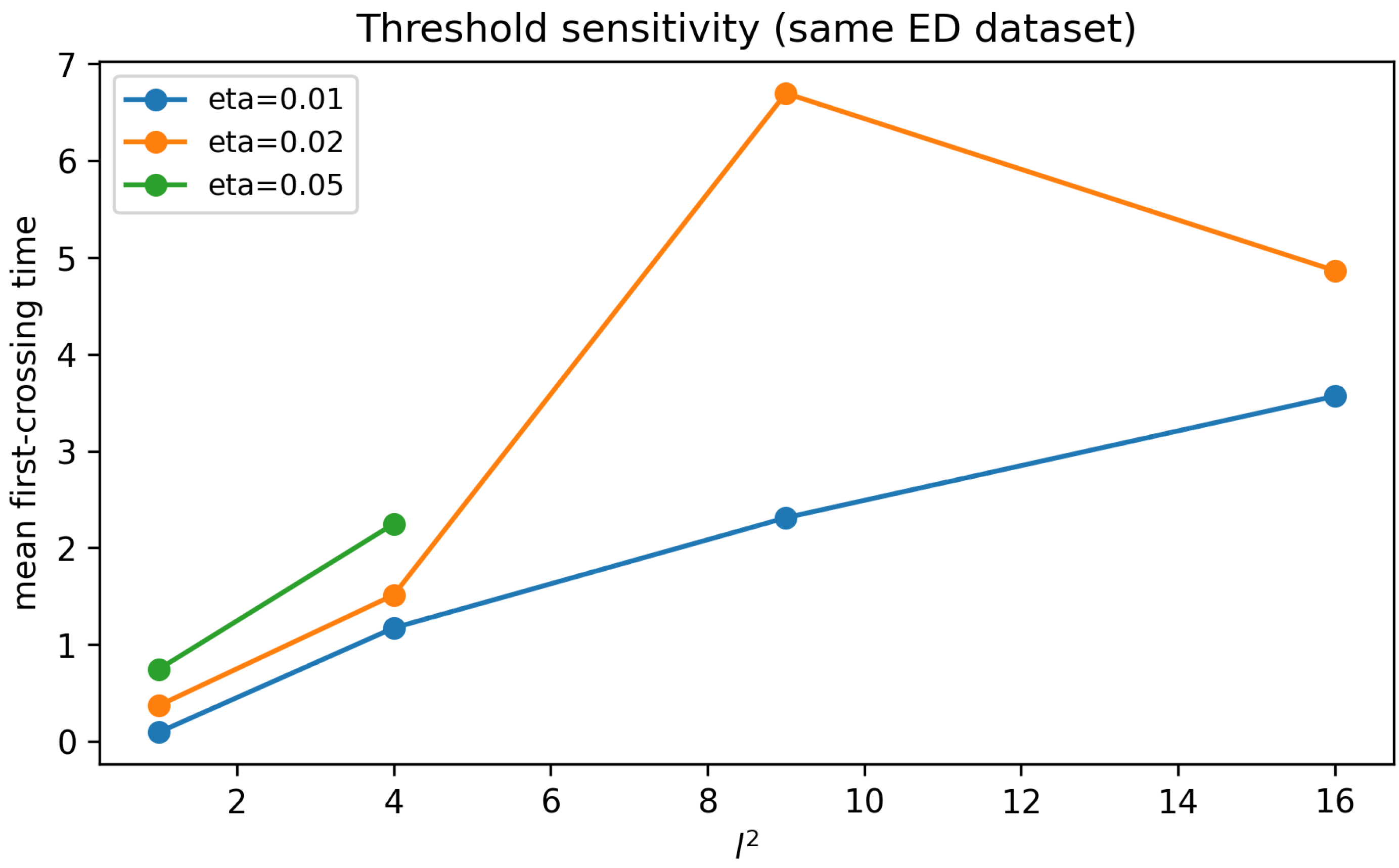
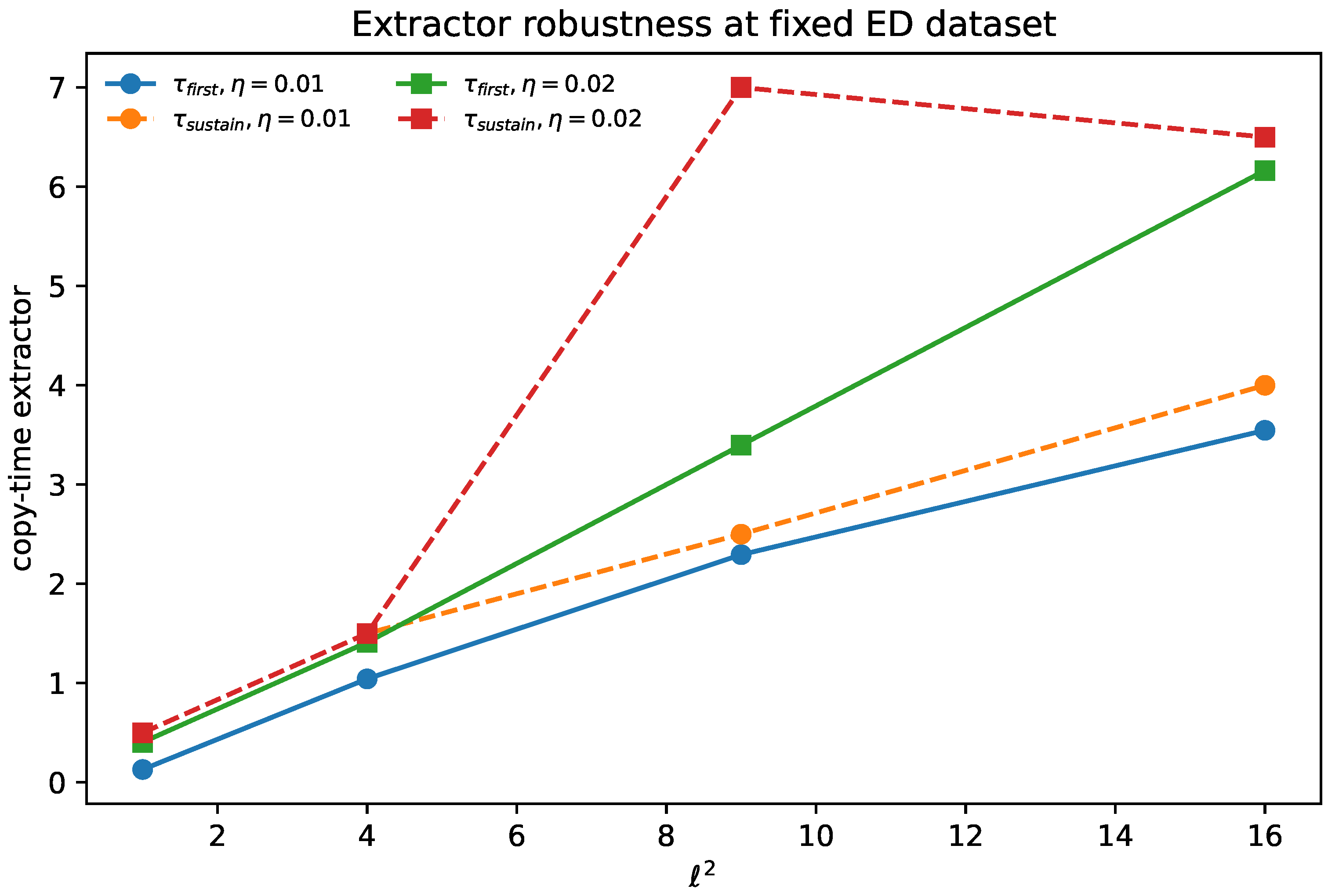
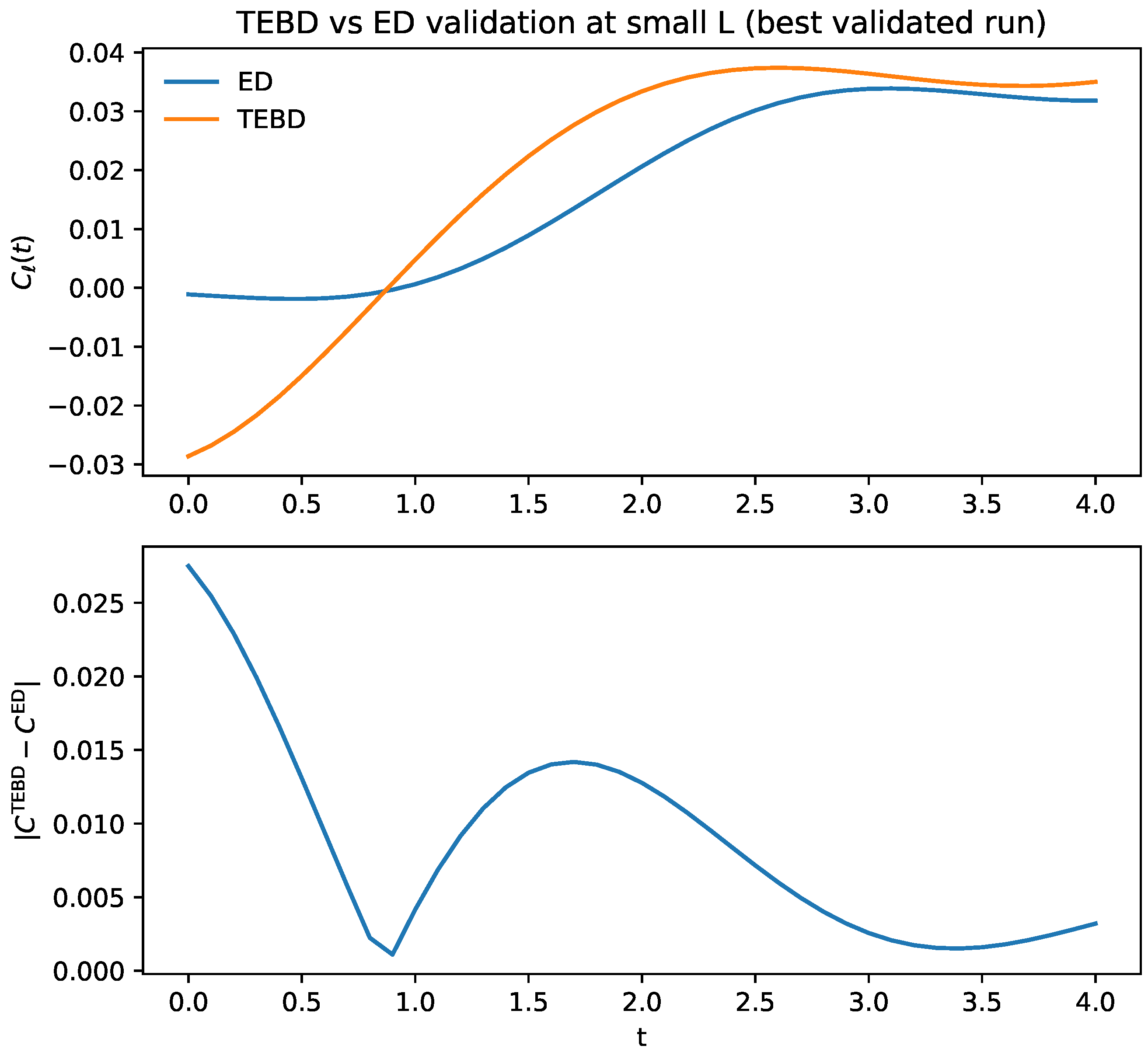
- Benchmarking and protocols. We provide finite-size transport diagnostics in the XXZ chain with explicit uncertainty controls, together with a detailed TEBD/MPS protocol outline and a bundled small-system TEBD-vs-ED validation suite (Section 10; Supplementary S2). The strengthened package adds an eight-size common-window transport sweep (including odd sizes), an explicit extractor-robustness diagnostic for copy-time extraction, and a receiver-side validation benchmark for a charge-measurement surrogate.
- C6.
- Comparison to scrambling diagnostics and extensions. We show, in a sharp operational sense, why a ballistic OTOC front can coexist with diffusion-limited certifiability under conservation laws (Section 8), and we outline how copy time can act as an operational microscope for non-diffusive regimes such as KPZ superdiffusion, Griffiths subdiffusion, and MBL (Supplementary S4).
Logical status of the results.
Positioning.
2. Operational Definition and Preliminaries
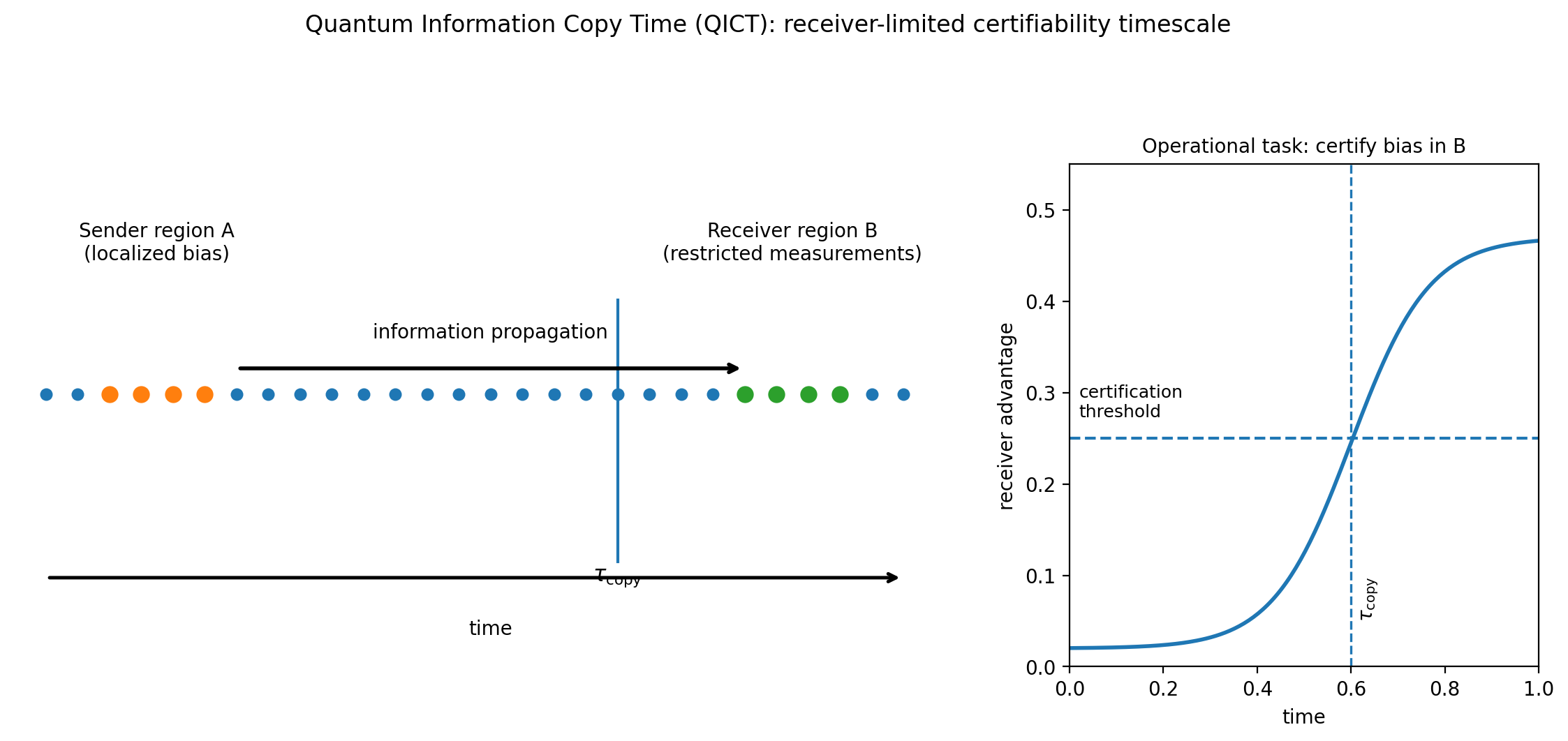
2.1. Copy Time as Receiver-Limited Hypothesis Testing
- (a)
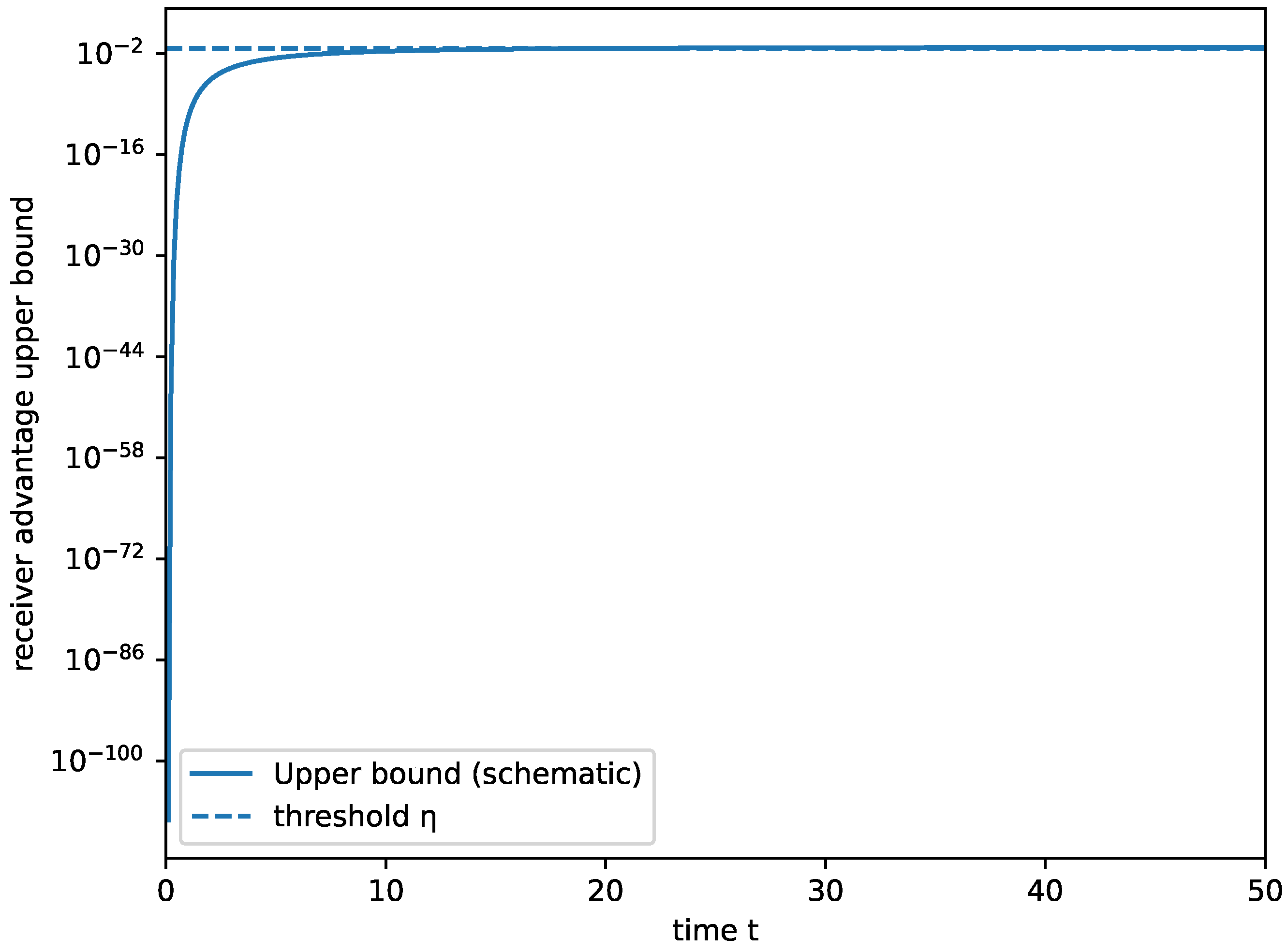
- Helstrom (unrestricted) advantage. The optimal receiver advantage isequivalently the Helstrom bias for discriminating vs. with equal priors. The associated copy time is
- (b)
- Restricted advantage. Let be an admissible observable class on B with for all (few-body algebras, moment channels, coarse-grained charge observables,etc.). Define the restricted advantageand the corresponding restricted copy time by the same hitting-time rule as in (3). Equivalently, if denotes a CPTP “measurement compression” channel whose dual maps the unit ball into , then .
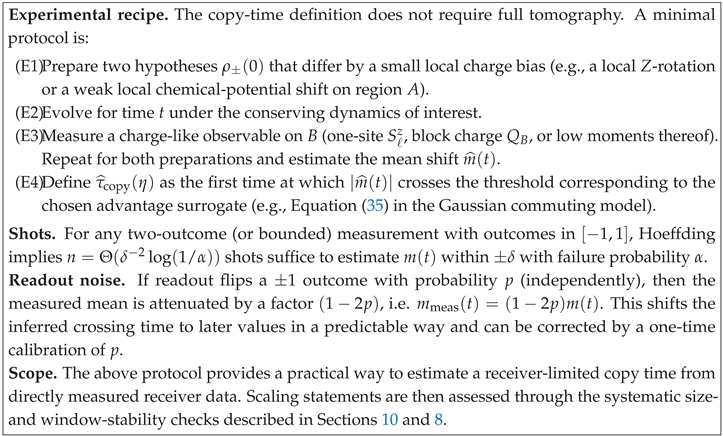
Operational sampling complexity (how many shots?).
Remark on “chemical potential tilts”.
2.2. Elementary Bounds and Remarks
3. Minimal Locality Bounds and What Is Genuinely nontrivial
3.1. Locality-Preserving Dynamics and Lieb–Robinson Constraints
- (H) Continuous-time Hamiltonian/Lindbladian (Lieb–Robinson tails). There exist constants such that for any observables supported on a finite region X and supported on Y,
- (C) Discrete-time range-R circuits / reversible QCAs (strict light cone). For each integer time , the Heisenberg image of a local algebra satisfies
- (H) For local Hamiltonian evolution satisfying a Lieb–Robinson bound, the receiver advantage is bounded by (A4) outside the effective cone.
- (C) For range-R circuits or reversible QCAs, the strict light cone implies whenever .
3.2. Conservation Laws and an Explicit Receiver Class
4. Hydrodynamic Closure: From Charge Bias to Spectral Susceptibility
4.1. Setup: Local Equilibrium Manifold and Linearization
| Symbol | Meaning |
| Liouvillian superoperator ( for closed systems) | |
| Mori projection onto the slow manifold and its complement | |
| Kubo–Mori inner product induced by the reference state | |
| Markovianized effective slow-sector generator (Equation (13)) | |
| Second-moment spectral susceptibility (Definition 2) | |
| Receiver observable restricted to the slow sector | |
| Fast-sector mixing gap controlling memory decay (assumption) |
4.2. A Principled Definition of the Second-Moment Susceptibility
Controlled hydrodynamic regime.
| Assumption | Operational/diagnostic proxy | Typical failure modes |
|---|---|---|
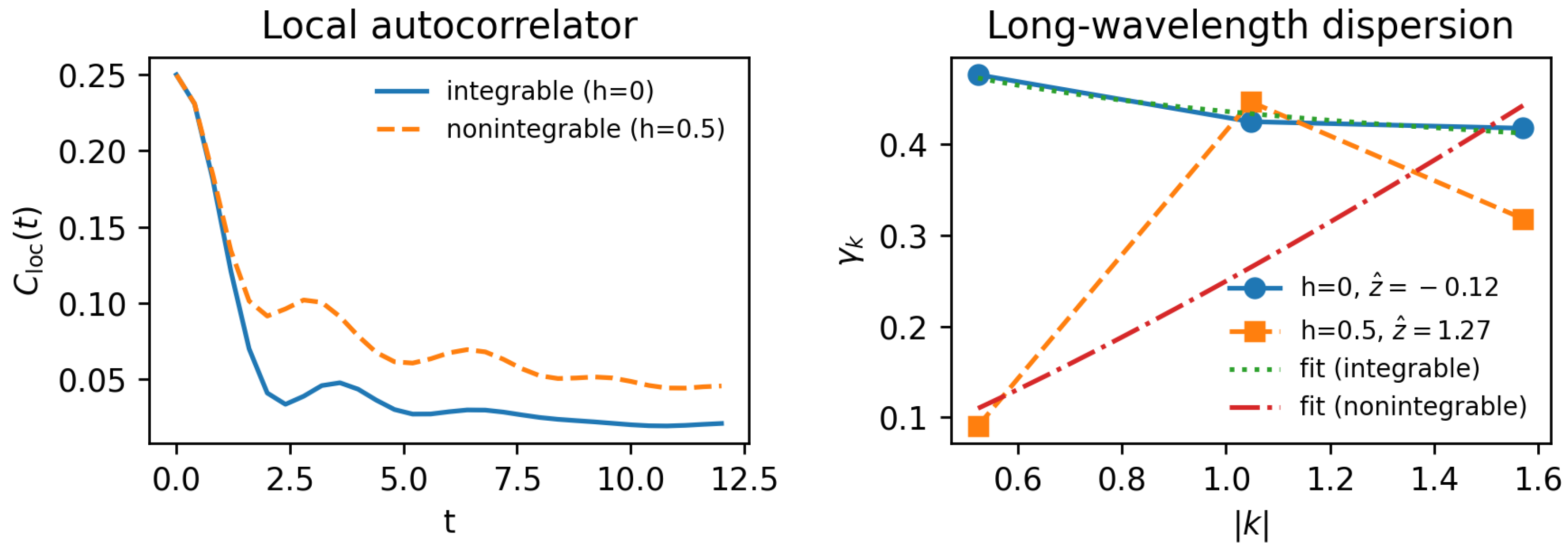
| Fast-sector mixing (“gap” in ) | Rapid decay of generic local autocorrelations to their hydrodynamic tail; absence of long-lived nonconserved operators in the accessible ED window (finite-size diagnostic) (Supplementary diagnostics) | Integrability, quasi-conservation (prethermal plateaus), MBL |
| Single isolated slow pole | approximately linear in over a time window; window-to-window stability; no competing ballistic/Drude channel (Section 9, Supplementary S2) | Multiple slow modes, long-time tails, Drude weight/nonzero stiffness |
| Nonzero receiver overlap | Choose with provable overlap (e.g., coarse- grained charge in B); verify signal is nonzero at accessible times | Symmetry mismatch; receiver observable orthogonal to slow mode |
| Linear-response regime | Small tilt; check odd-in- scaling and absence of saturation artifacts in numerics | Large perturbations, finite-size saturation, edge effects |
4.3. Two Theorems: Minimal and Single-Mode
- (S1)
- Single slow pole: on a wavelength band the slow spectrum on consists of a single nonzero mode with decay rate and a gap to the next slow mode on that band;
- (S2)
- Receiver overlap: the projected receiver observable has nonzero overlap with that mode, quantified by the form factor entering (A13);
- (S3)
- Fast mixing: the fast-sector leakage is controlled by Proposition 1 with rate on the window of interest.
5. Worked Hydrodynamic Example: One-Dimensional Diffusion Kernel
5.1. Linear-Response form of the Reduced-State Difference
5.2. Diffusion Equation for the Conserved Density
5.3. Receiver Signal and a Concrete Threshold-to-Time Relation
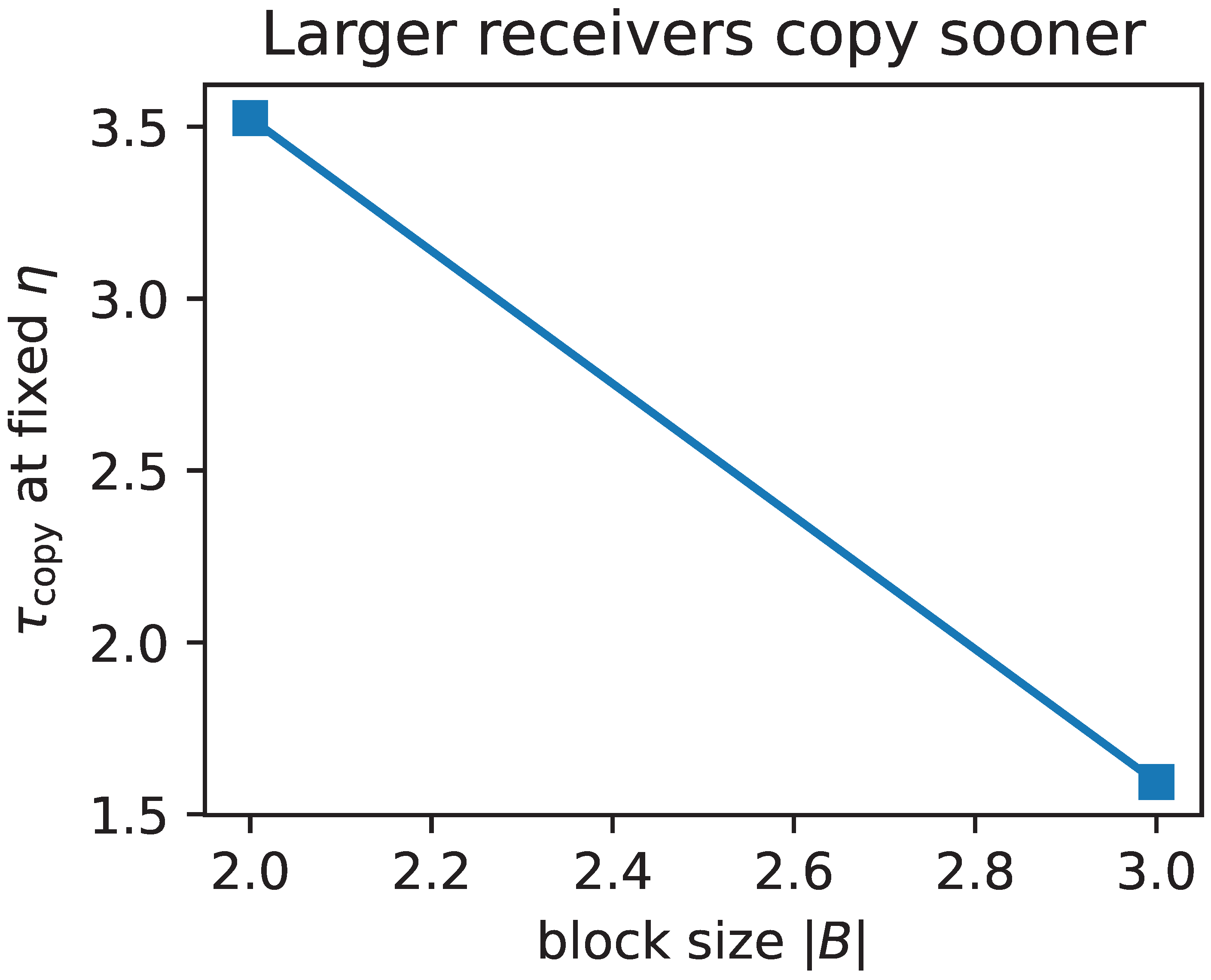
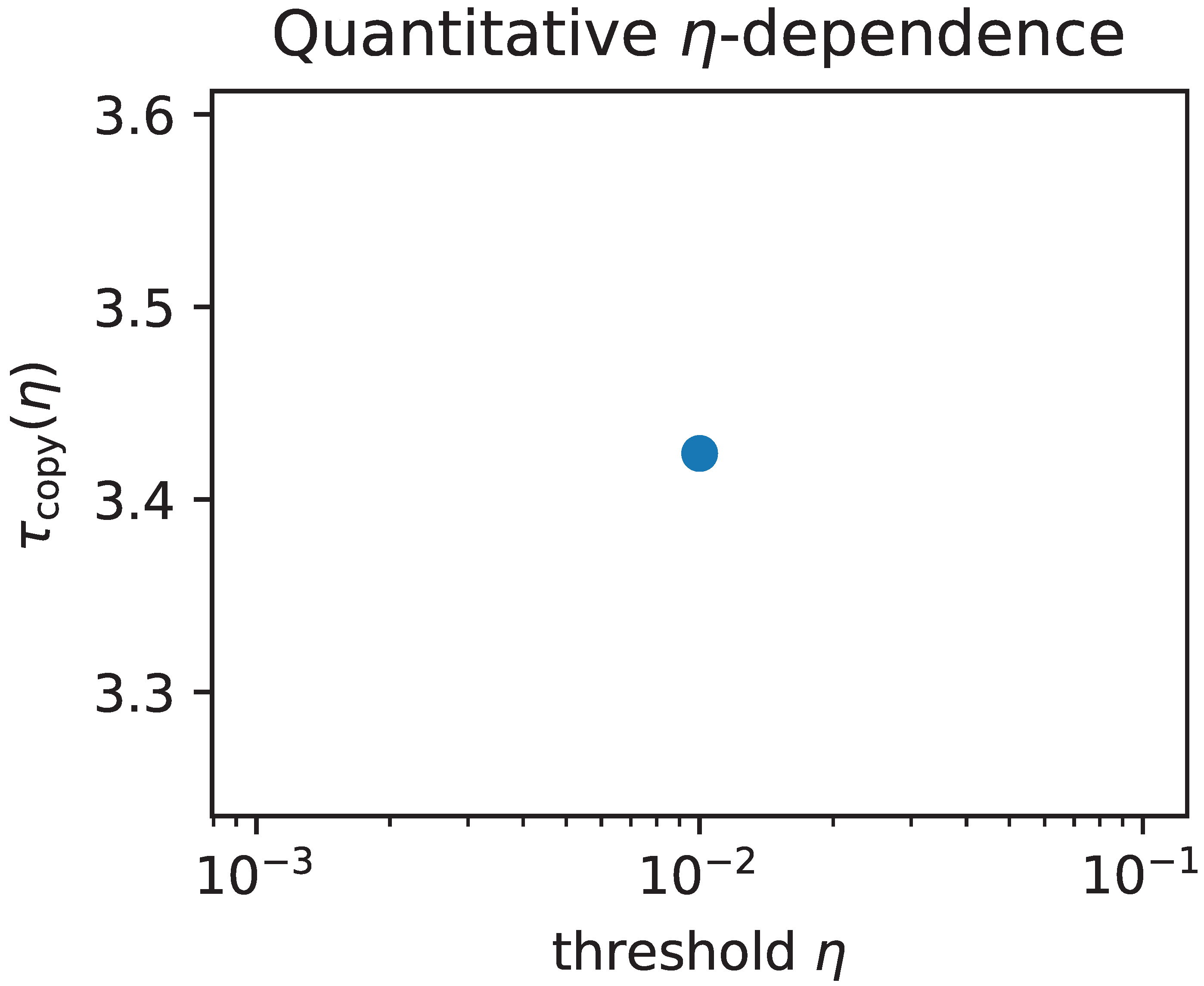
A quantitative – and –dependence (Gaussian-kernel inversion).
5.4. An Exactly Solvable Gaussian Diffusion Toy Model (Fully Analytic)
6. A Rigorous Diffusive Benchmark: Helstrom Copy Time in Q-SSEP
6.1. Model and Hypotheses
6.2. Main Inequality
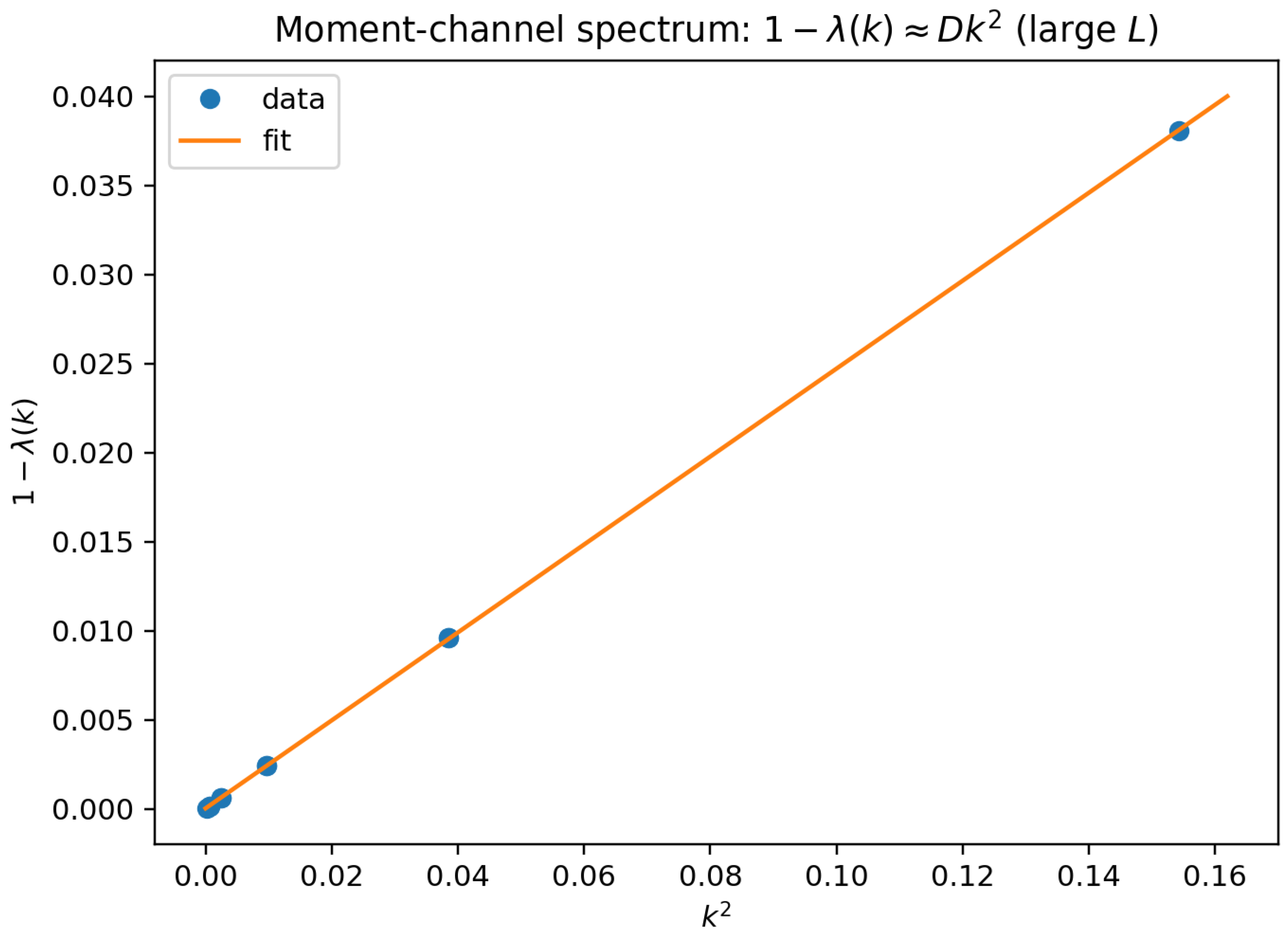
7. Moment-Channel Approximation and Operational Accessibility
7.1. Definition of the Moment Channel
7.2. When Moment Restriction Is Asymptotically Optimal
8. Copy Time Versus OTOCs and Lieb–Robinson Bounds: A Sharp Separation
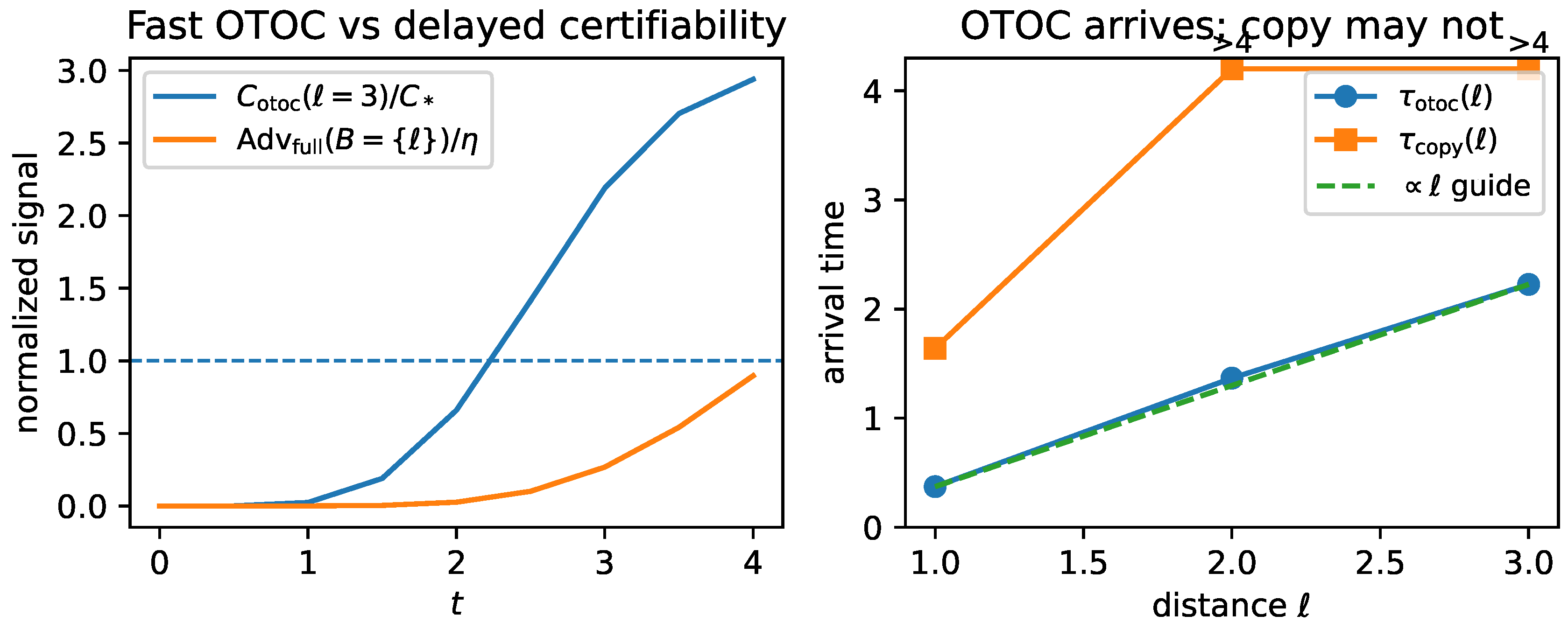
8.1. Ballistic Operator Growth Does Not Imply Fast Copying Under Conservation
Proof sketch.
8.2. Relation to LR Bounds
9. Failure Modes and Boundaries of Validity
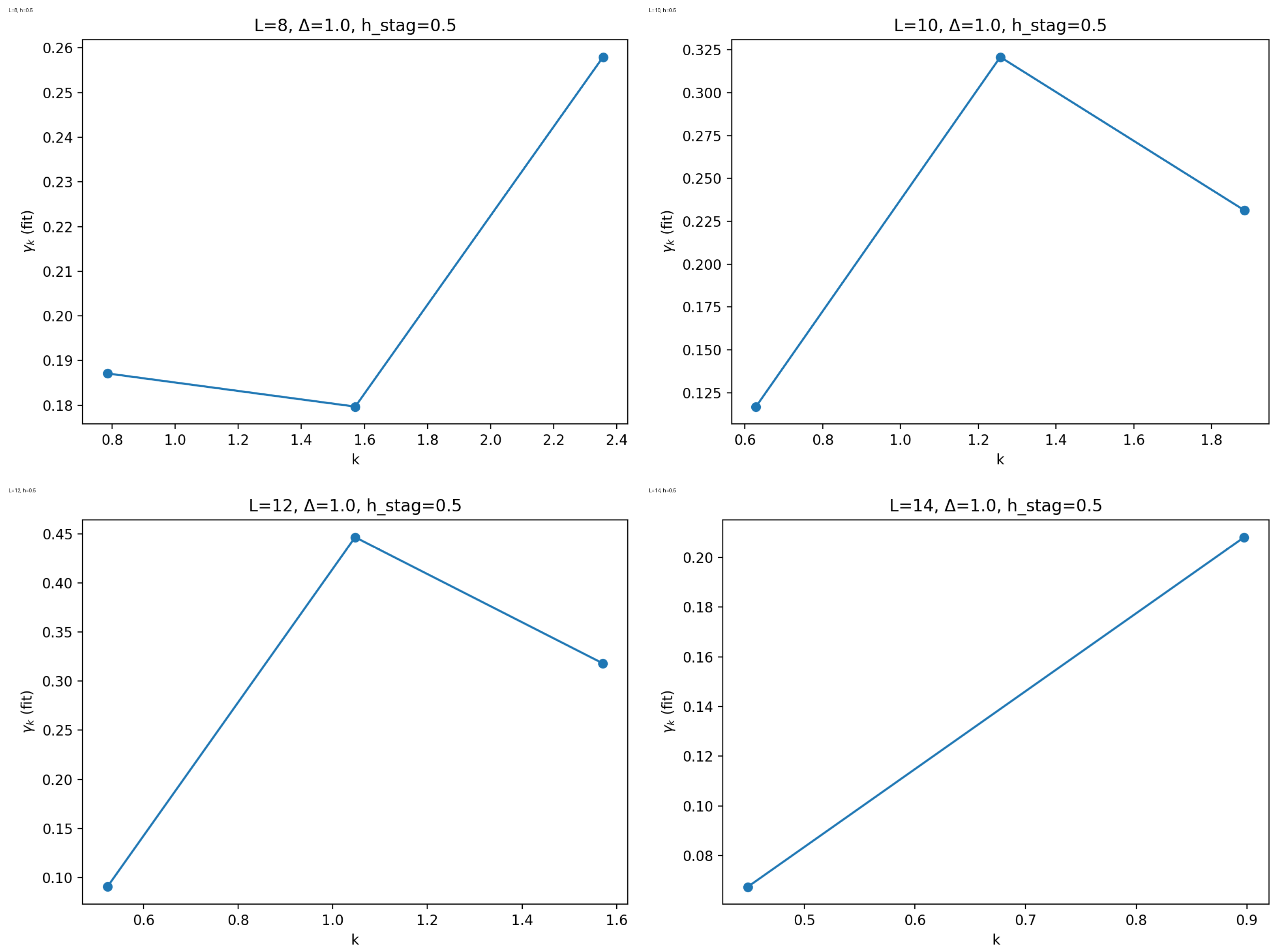
- Integrable / near-integrable dynamics. Ballistic channels and stable quasi-particles yield or coexistence of ballistic and diffusive channels; single-mode diffusion fails. The “effective exponent” extracted from small-k finite-size data can drift and even become negative when the estimator is outside its validity window (Appendix H).
- MBL or quasi-MBL. Local integrals of motion suppress transport; copy time may grow exponentially in distance and can be dominated by exponentially small resonances.
- Floquet without conservation. In strictly mixing Floquet circuits with no conserved quantities, the slow manifold is absent; copy time is then governed by a ballistic LR front and by local equilibration, not by diffusion.
- Quasi-conservation / prethermalization. Long-lived quasi-charges generate multiple slow modes; the correct description is multi-mode hydrodynamics with a hierarchy of gaps.
10. Numerical Benchmarks: ED with Explicit Uncertainty Quantification
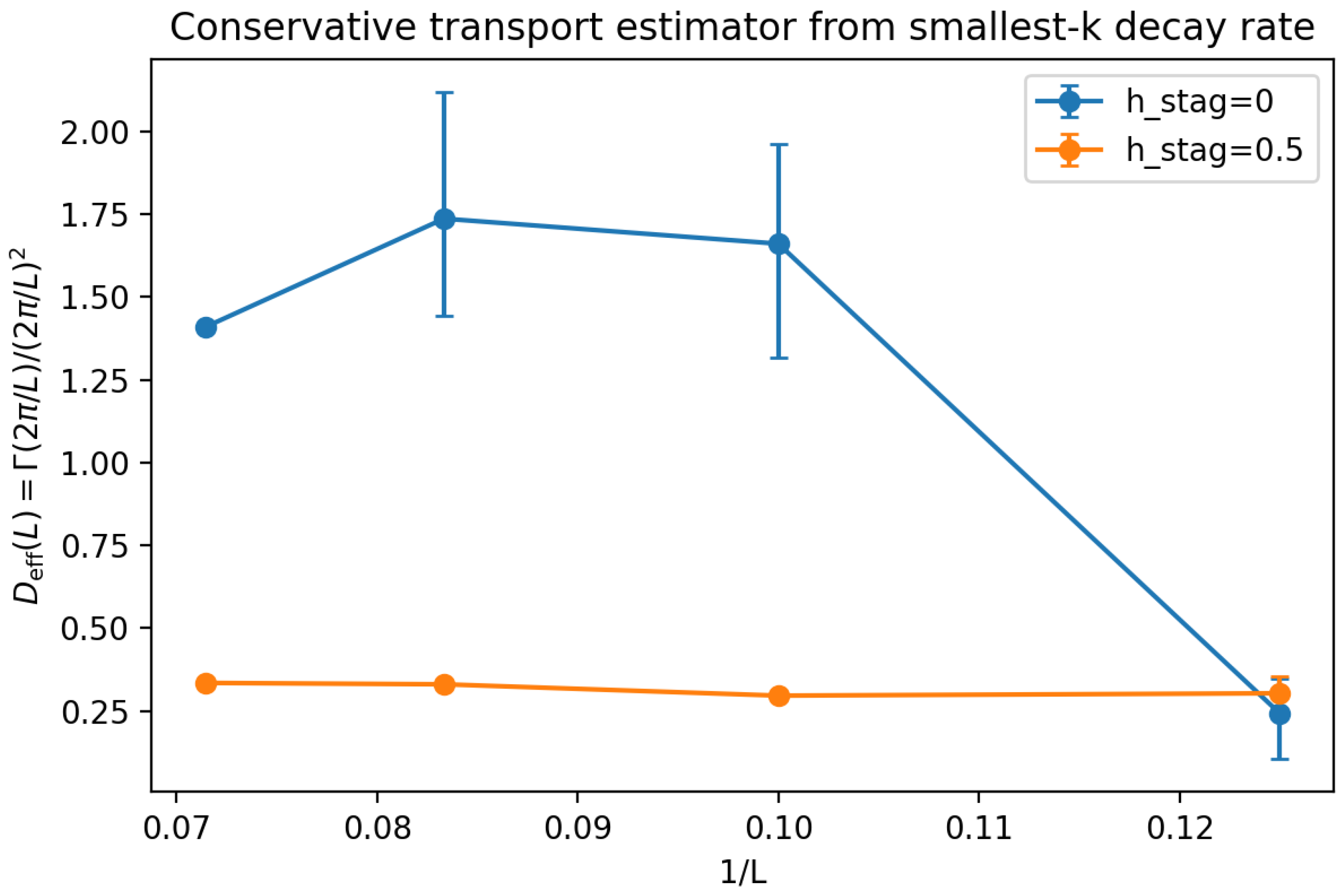
10.1. Exact Diagonalization Transport Extraction
Conservative finite-size protocol.
| L | 95% CI | ||
| 8 | 0.0 | 0.242 | [0.106, 0.348] |
| 10 | 0.0 | 1.661 | [1.316, 1.962] |
| 12 | 0.0 | 1.736 | [1.443, 2.118] |
| 14 | 0.0 | 1.409 | [1.409, 1.409] |
| 8 | 0.5 | 0.303 | [0.252, 0.354] |
| 10 | 0.5 | 0.296 | [0.294, 0.298] |
| 12 | 0.5 | 0.330 | [0.326, 0.334] |
| 14 | 0.5 | 0.335 | [0.335, 0.335] |
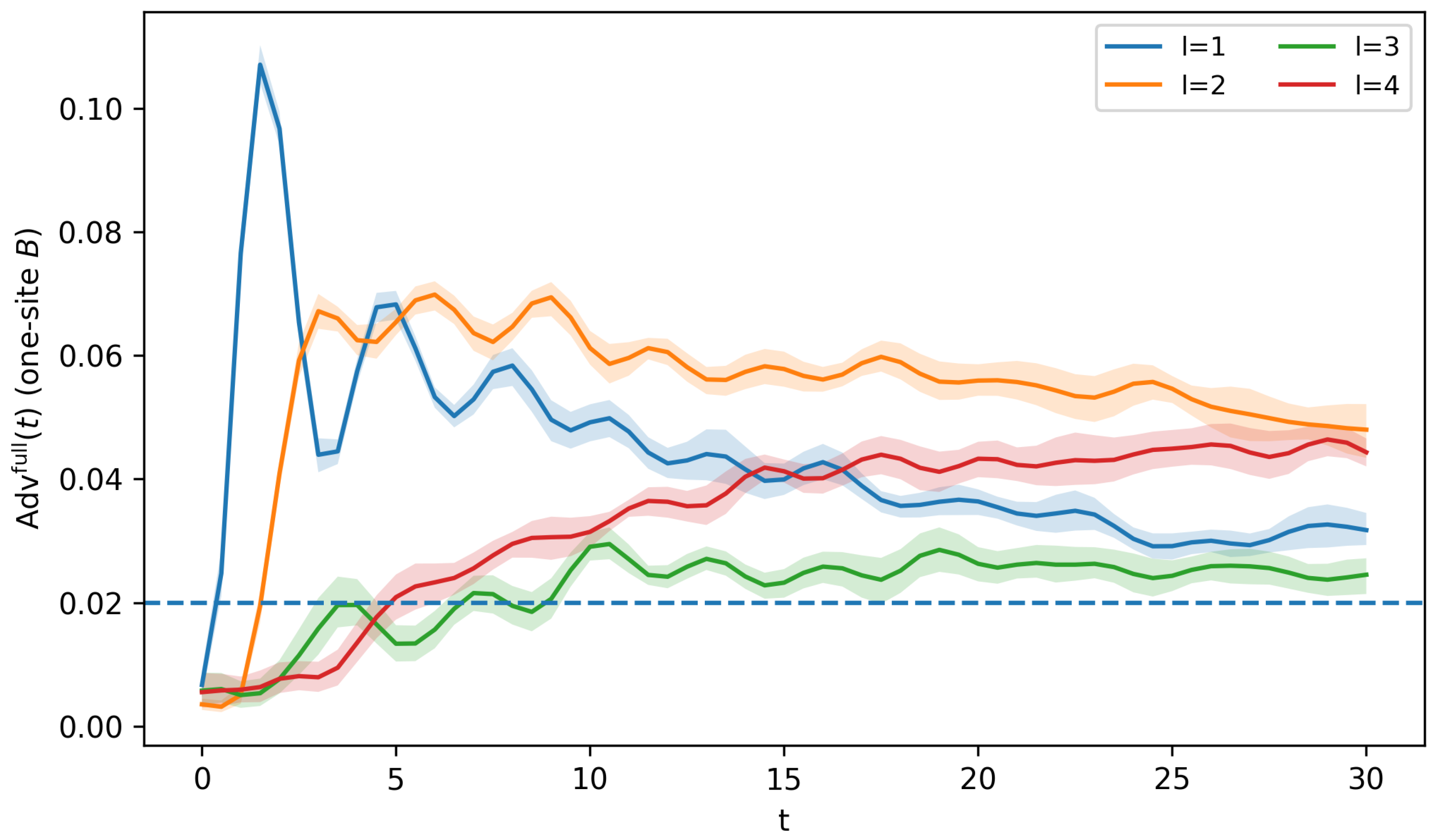
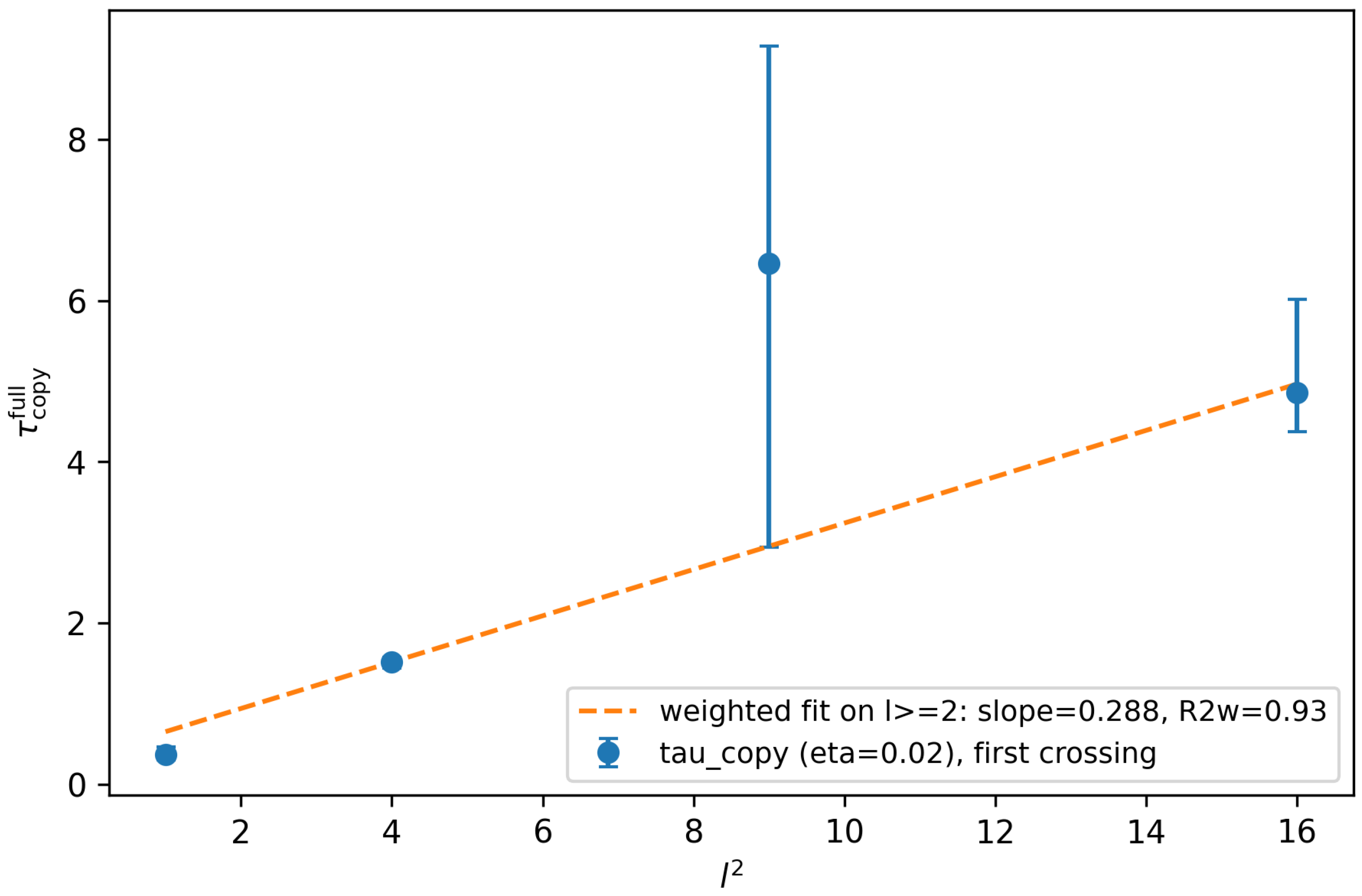
10.2. Direct Computation of the Helstrom Advantage and (XXZ, B One Site)
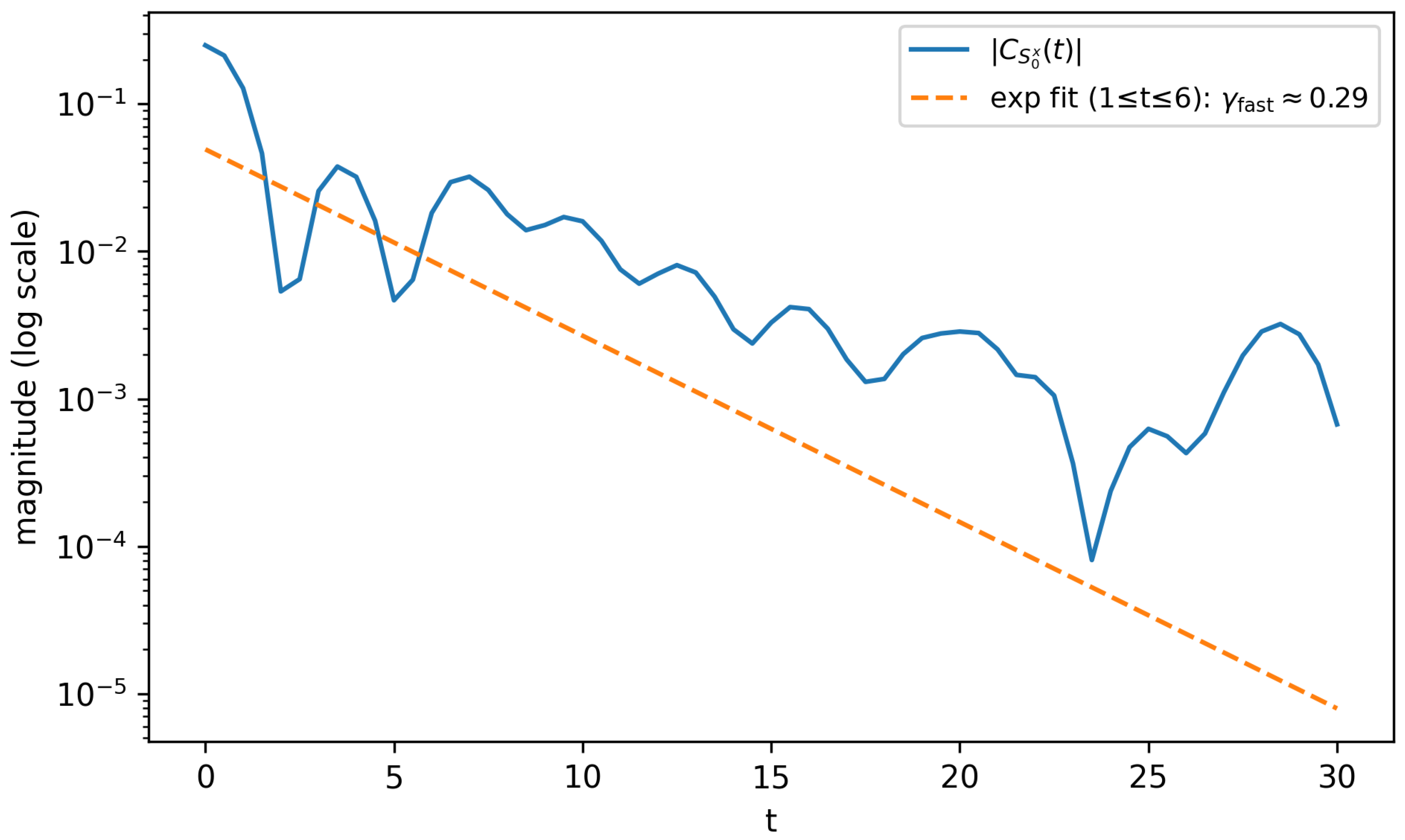
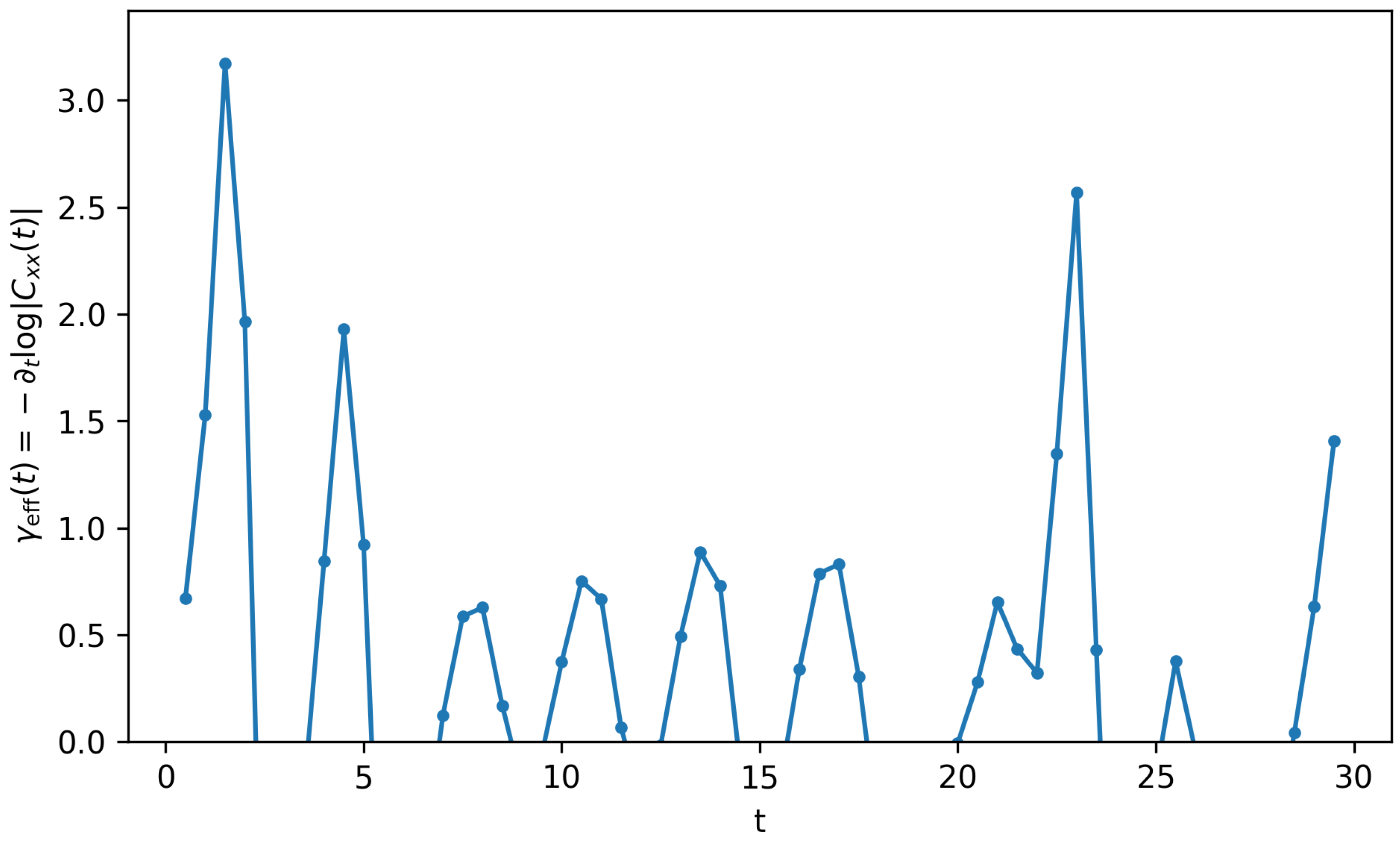
Numerical diagnostic for fast mixing.
10.3. Finite-Size Drift Diagnostics and the “Negative Exponent” Issue
10.4. TEBD/MPS Validation and Convergence Controls
10.5. One-Page Synthesis of Regimes, Scalings, and Uncertainties
11. Supplementary Discussion: Quantum Cellular Automata and Operational Copy-Time Distances
11.1. Locality-Preserving QCA as a Clean Microscopic Substrate
11.2. Copy-time distances and an operational geometry
| Microscopic structure | Dominant control of | Geometric interpretation of |
|---|---|---|
| Range-R QCA (strict cone) | Hard causal delay | Operational causal cone; metricity requires extra mixing |
| Local Hamiltonian (LR tails) | Exponential tail outside cone | Approximate causal cone with exponentially small leakage |
| Conservation + diffusion | Slowest mode (Theorem 3) | Transport geometry; distances can scale as in a diffusive window |
| Integrable / ballistic channels | Coexisting modes, Drude weight | Breakdown of single-mode geometry; is model dependent |
| Code-subspace restriction | Admissible perturbations/observables | Geometry depends on code constraints and decoding locality |
12. Conclusions
Supplementary Materials
Data Availability Statement
Conflicts of Interest
Appendix A. Proof Details and Technical Lemmas
Appendix A.1. Proof of Theorem 1
Appendix A.2. Proof of Theorem 2 and Corollary 1
Appendix B. Hydrodynamic Single-Mode Derivation
Appendix B.1. A Resolvent Criterion for Semigroup Reduction
Appendix B.2. From Projected Dynamics to a Diffusion Pole
Appendix B.3. Threshold Inversion and ℓ 2 Scaling
Appendix C. Moment-Channel Optimality in Gaussian Fluctuation Algebras
Appendix D. QCA Locality Versus LR Tails and Index Sensitivity
Appendix D.1. From Strict Causal Cones to Operational Zero Advantage
Appendix D.2. Why Copy-Time Data Might “See” the Index
Appendix E. Finite-Size Corrections for Diffusion-Kernel Inversion
Appendix F. Small-System ED Illustration: Threshold and Receiver- Size Dependence
Appendix G. Gaussian Discrimination and Moment Sufficiency: An Explicit Bound
Appendix H. Additional Numerical Tables and Metadata
Appendix H.1. Receiver-Side Calibration of a Simple Charge Surrogate
Appendix H.2. TEBD Validation and Convergence Summary
| RMSE | max abs. error | ||
| 0.1 | 32 | 0.01110 | 0.02749 |
| 0.1 | 64 | 0.01110 | 0.02749 |
| 0.1 | 128 | 0.01110 | 0.02749 |
| 0.2 | 64 | 0.01139 | 0.02749 |
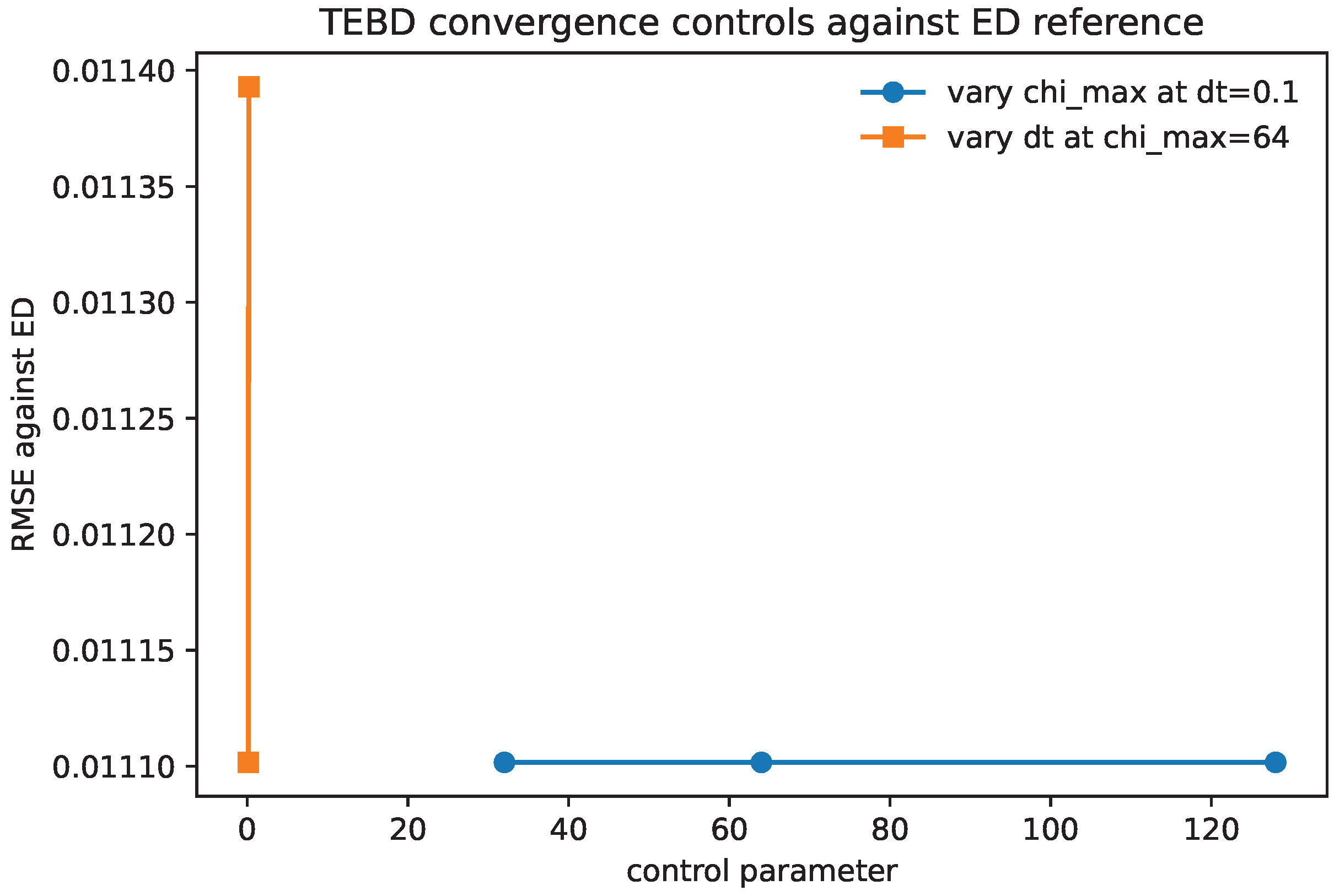
Appendix I. Reproducibility: Run Manifest and Code Pointers
- definitions, locality bounds, and technical lemmas supporting the operational setup (Supplementary File S1);
- a detailed TEBD/MPS protocol and convergence checklist for future thermodynamic-limit copy-time tests, together with a bundled small-system TEBD-vs-ED validation suite used only for implementation auditing (Supplementary File S2 and SC1);
- the rigorous Q-SSEP benchmark and supporting derivations for the diffusive lower bound (Supplementary File S3);
- conceptual positioning relative to OTOCs and toy examples separating receiver-limited certifiability from operator-growth diagnostics (Supplementary File S4);
- the code, parameter registries, integrity checks, fit-window scans, and the minimal data bundle used to generate the reported ED diagnostics and Helstrom-advantage figure suite (Supplementary Code Archive SC1 together with the accompanying data archive).
Appendix I.1. Reproducibility Pointers (ED Extraction and Post-Processing)
Appendix I.2. TEBD/MPS Protocol and Bundled Validation Code
References
- Helstrom, C.W. Quantum Detection and Estimation Theory; Academic Press, 1976. [Google Scholar]
- Holevo, A.S. Statistical decision theory for quantum systems. Journal of Multivariate Analysis 1973, 3, 337–394. [Google Scholar] [CrossRef]
- Kubo, R. Statistical-Mechanical Theory of Irreversible Processes. I. General Theory and Simple Applications to Magnetic and Conduction Problems. Journal of the Physical Society of Japan 1957, 12, 570–586. [Google Scholar] [CrossRef]
- Mori, H. Transport, Collective Motion, and Brownian Motion. Progress of Theoretical Physics 1965, 33, 423–455. [Google Scholar] [CrossRef]
- Zwanzig, R. Memory Effects in Irreversible Thermodynamics. Physical Review 1961, 124, 983–992. [Google Scholar] [CrossRef]
- Forster, D. Hydrodynamic Fluctuations, Broken Symmetry, and Correlation Functions; Benjamin, 1975. [Google Scholar]
- Nahum, A.; von Keyserlingk, C.W.; Rakovszky, T.; Pollmann, F.; Sondhi, S.L. Operator hydrodynamics, OTOCs, and entanglement growth in systems with conservation laws. Physical Review X 2018, 8, 021014. [Google Scholar] [CrossRef]
- Khemani, V.; Vishwanath, A.; Huse, D.A. Operator spreading and the emergence of dissipative hydrodynamics under unitary dynamics with conservation laws. Physical Review X 2018, 8, 031057. [Google Scholar] [CrossRef]
- Bernard, D.; Jin, T. Anomalous scaling and diffusion in the quantum symmetric simple exclusion process. Communications in Mathematical Physics 2021, 383, 659–712. [Google Scholar] [CrossRef]
- Nahum, A.; Vijay, S.; Haah, J. Operator Spreading in Random Unitary Circuits. Physical Review X 2018, 8, 021014. [Google Scholar] [CrossRef]
- von Keyserlingk, C.W.; Rakovszky, T.; Pollmann, F.; Sondhi, S.L. Operator Hydrodynamics, OTOCs, and Entanglement Growth in Systems without Conservation Laws. Physical Review X 2018, arXiv:cond8, 021013. [Google Scholar] [CrossRef]
- Xu, S.; Swingle, B. Scrambling Dynamics and Out-of-Time-Ordered Correlators in Quantum Many-Body Systems. PRX Quantum 2024, arXiv:quant5, 010201. [Google Scholar] [CrossRef]
- Khemani, V.; Vishwanath, A.; Huse, D.A. Operator Spreading and the Emergence of Dissipative Hydrodynamics under Unitary Evolution with Conservation Laws. Physical Review X 2018, 8, 031057. [Google Scholar] [CrossRef]
- Rakovszky, T.; Pollmann, F.; von Keyserlingk, C.W. Diffusive Hydrodynamics of Out-of-Time-Ordered Correlators with Charge Conservation. Physical Review X 2018, 8, 031058, [arXiv:cond-mat.str-el/1710.09827]. [Google Scholar] [CrossRef]
- Schumacher, B.; Werner, R.F. Reversible quantum cellular automata. arXiv:quant-ph/0405174, 2004. Preprint.
- Gross, D.; Nesme, V.; Vogts, H.; Werner, R.F. Index Theory of One Dimensional Quantum Walks and Quantum Cellular Automata. Communications in Mathematical Physics 2012, 310, 419–454. [Google Scholar] [CrossRef]
- Arrighi, P.; Nesme, V.; Werner, R. Unitarity plus causality implies localizability. Journal of Computer and System Sciences 2019, 101, 26–40. [Google Scholar] [CrossRef]
| Model / dynamics | Regime / structure | Diagnostic | scaling | Supported by |
|---|---|---|---|---|
| Gaussian charge field (commuting) | Diffusive kernel, Gaussian fluctuations | Exact TV distance (35) | (log- corr.) | Appendix G |
| Chaotic dynamics (generic) | Ballistic operator growth + diffusive charge | Separation Prop. 2 | , | Prop. 2 |
| XXZ chain () | Nonintegrable, candidate diffusive window | (bootstrap CI) | Consistent with window; no asymptotic claim | Table 3, Figure 4 |
| XXZ chain () | Integrable / multimode | Drift/nonmonotone | Single-mode diffusion fails | Figure 4, Section 10 |
| Range-R QCA | Strict light cone | Hard causal delay | Prop. 3 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).