Submitted:
31 December 2025
Posted:
02 January 2026
Read the latest preprint version here
Abstract
Keywords:
1. Introduction
2. Theoretical Background
3. Methods
3.1. Data and Sample
3.2. Variables and Analytical Strategy
4. Results
4.1. Descriptive Patterns and User Types
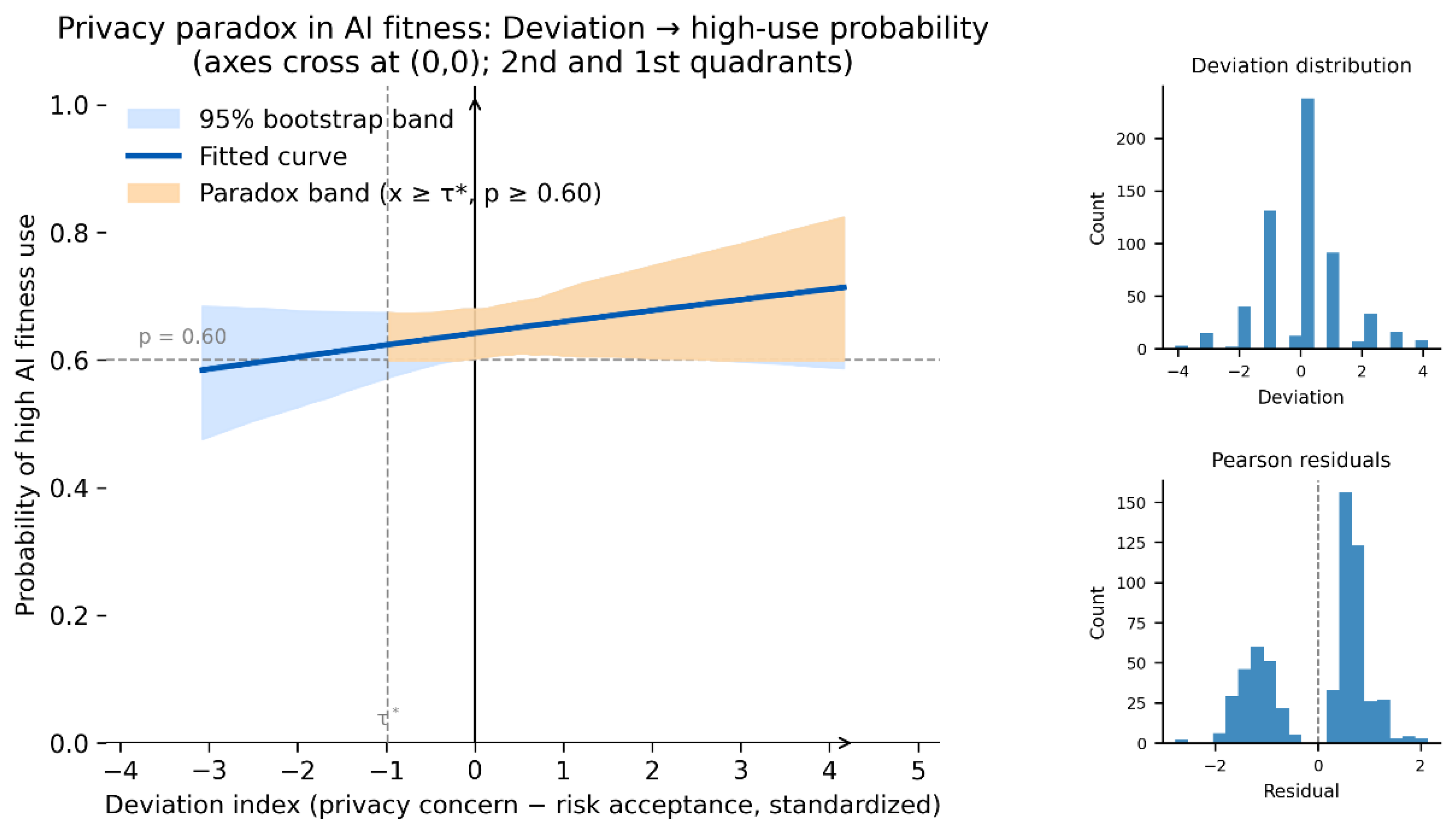
4.2. Logistic Regression and the Gradual Privacy Paradox
5. Discussion and Conclusion
5.1. Gradual Privacy Paradox as Privacy Satisficing
5.2. Implications and Limitations
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- P. F. Wu, “The privacy paradox in the context of online social networking: A self-identity perspective,” Journal of the Association for Information Science and Technology, Vol. 70, No. 3, pp. 207–217, 2019. [CrossRef]
- T. Dinev and P. Hart, “An extended privacy calculus model for e-commerce transactions,” Information Systems Research, Vol. 17, No. 1, pp. 61–80, 2006. [CrossRef]
- R. S. Hirschprung, “Is the privacy paradox a domain-specific phenomenon?,” Computers, Vol. 12, Article No. 156, 2023. [CrossRef]
- E. Arzoglou, Y. Kortesniemi, S. Ruutu, and T. Elo, “The Role of Privacy Obstacles in Privacy Paradox: A System Dynamics Analysis,” Systems, Vol. 11, No. 4, Article No. 205, 2023. [CrossRef]
- M. Abdelhamid, “Fitness tracker information and privacy management: Empirical study,” Journal of Medical Internet Research, Vol. 23, No. 11, Article No. e23059, 2021. [CrossRef]
- H. Kang and E. H. Jung, “The smart wearables–privacy paradox: A cluster analysis of smartwatch users,” Behaviour & Information Technology, Vol. 40, No. 16, pp. 1755–1768, 2021. [CrossRef]
- P. Zhang, M. N. K. Boulos et al., “Privacy-by-design environments for large-scale health research and federated learning from data,” International Journal of Environmental Research and Public Health, Vol. 19, Article No. 11876, 2022. [CrossRef]
- G. So, “A study on scenario-based web application security education method,” The International Journal of Internet, Broadcasting and Communication, Vol. 15, No. 3, pp. 149–159, 2023. [CrossRef]
- H. Su and G. So, “Platform disconnection in rural revitalization: A multi-level analysis with reference to East Asia,” The International Journal of Internet, Broadcasting and Communication, Vol. 17, No. 3, pp. 183–196, 2025. [CrossRef]
- H. Su, J. Liao, and G. So, “Satisficing equilibrium and multi-actor trust in AI-enabled smart tourism: Nonlinear evidence from digital governance dynamics,” Preprints, 2025. [CrossRef]
- J. Y. Cho, D. Ko, and B. G. Lee, “Strategic approach to privacy calculus of wearable device user regarding information disclosure and continuance intention,” KSII Transactions on Internet and Information Systems, Vol. 12, No. 7, pp. 3356–3374, 2018. [CrossRef]
- R. Reith, C. Buck, B. Lis, and T. Eymann, “Integrating privacy concerns into the unified theory of acceptance and use of technology to explain the adoption of fitness trackers,” International Journal of Innovation and Technology Management, Vol. 17, No. 7, Article No. 2050049, 2020. [CrossRef]
- B. Lebek, J. Uffen, M. Neumann, B. Hohler, and M. H. Breitner, “Information security awareness and behavior: A theory-based literature review,” Management Research Review, Vol. 37, No. 12, pp. 1049–1092, 2014. [CrossRef]
- H. A. Simon, “A behavioral model of rational choice,” The Quarterly Journal of Economics, Vol. 69, No. 1, pp. 99–118, 1955. [CrossRef]
- G. Lilly, “Bounded rationality: A Simon-like explication,” Journal of Economic Dynamics and Control, Vol. 18, No. 1, pp. 205–230, 1994. [CrossRef]
- G. J. S. Wilde, “The Theory of Risk Homeostasis: Implications for Safety and Health,” Risk Analysis, Vol. 2, No. 4, pp. 209–225, 1982. [CrossRef]
- F. Bu and L. Ji, “Research on privacy-by-design behavioural decision-making of information engineers considering perceived work risk,” Systems, Vol. 12, Article No. 250, 2024. [CrossRef]
- J. D. Lee and K. A. See, “Trust in Automation: Designing for Appropriate Reliance,” Human Factors, Vol. 46, No. 1, pp. 50–80, 2004. [CrossRef]
- D. W. Hosmer, S. Lemeshow, and R. X. Sturdivant, Applied Logistic Regression, 3rd ed. Hoboken, NJ, USA: Wiley, 2013. [CrossRef]
- T. D. Mize, “Best practices for estimating, interpreting, and presenting average marginal effects,” Sociological Science, Vol. 6, pp. 81–117, 2019. [CrossRef]
- M. Nardo, M. Saisana, A. Saltelli, S. Tarantola, A. Hoffmann, and E. Giovannini, Handbook on Constructing Composite Indicators: Methodology and User Guide. Paris, France: OECD Publishing, 2008. [CrossRef]
- L. Aquilino, C. Di Dio, F. Manzi, D. Massaro, P. Bisconti, and A. Marchetti, “Decoding trust in artificial intelligence: A systematic review of quantitative measures and related variables,” Informatics, Vol. 12, Article No. 70, 2025. [CrossRef]
- L. A. Gordon and M. P. Loeb, “The economics of information security investment,” ACM Transactions on Information and System Security, Vol. 5, pp. 438–457, 2002. [CrossRef]
| Variable | Mean | SD |
|---|---|---|
| High willingness to use AI fitness (1 = high-use) | 0.63 | 0.48 |
| Deviation (z-privacy concern − z-risk acceptance) | 0.00 | 1.34 |
| ICL (perceived transparency index, 1–5) | 3.37 | 0.79 |
| Privacy trade-off (1–5) | 3.86 | 0.79 |
| Gender (1 = female) | 0.32 | 0.47 |
| Age group (ordinal, 1–4) | 1.89 | 0.79 |
| App-use experience (1 = experienced user) | 0.93 | 0.26 |
| Variable | Coefficient | Std. Error |
|---|---|---|
| Deviation | 0.18 | 0.08 |
| ICL (perceived transparency) | 0.78 | 0.13 |
| Privacy trade-off | 0.47 | 0.14 |
| Constant | –3.87 | 0.61 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




