Submitted:
03 December 2025
Posted:
05 December 2025
You are already at the latest version
Abstract
Keywords:
I. Introduction
II. Background: The Evolving AI Technology Stack
A. Components of Modern AI Stacks
B. Global Competitive Landscape
C. Emerging Technologies and Trends
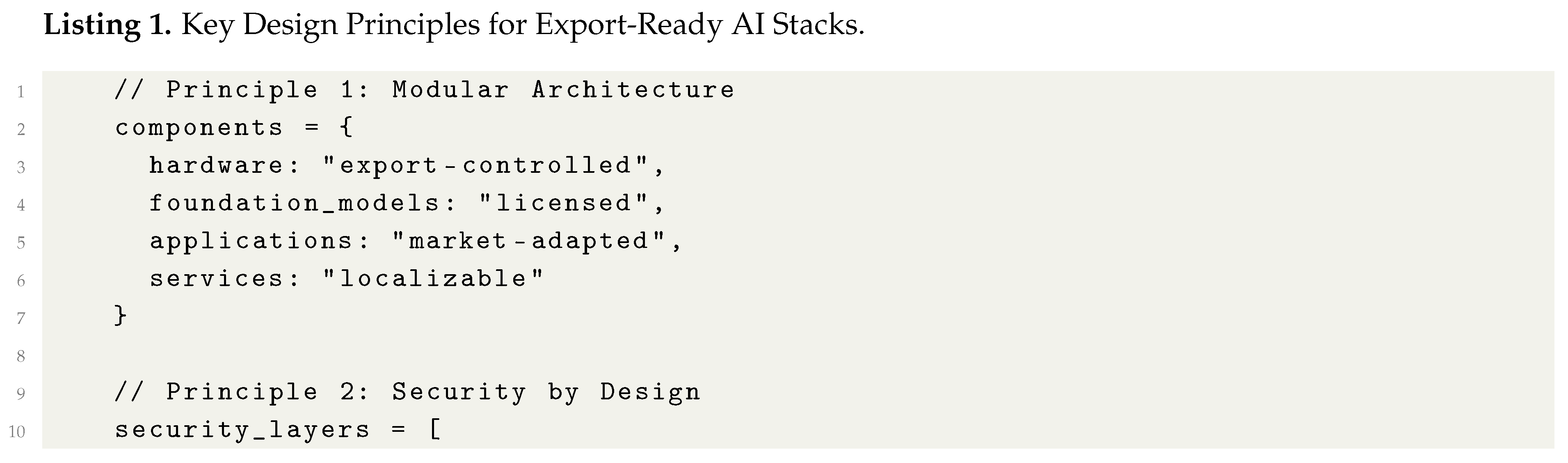
- AI Agent Interoperability: Protocols like A2A and MCP enable seamless agent collaboration but introduce security complexities [16]
- Federated Learning: Enables privacy-preserving distributed model training across jurisdictions [17]
- Edge AI: Supports localized processing while maintaining central coherence [18]
- Automated Compliance: Emerging tools for dynamic export control enforcement [19]
III. Comprehensive Framework Analysis and Visualization
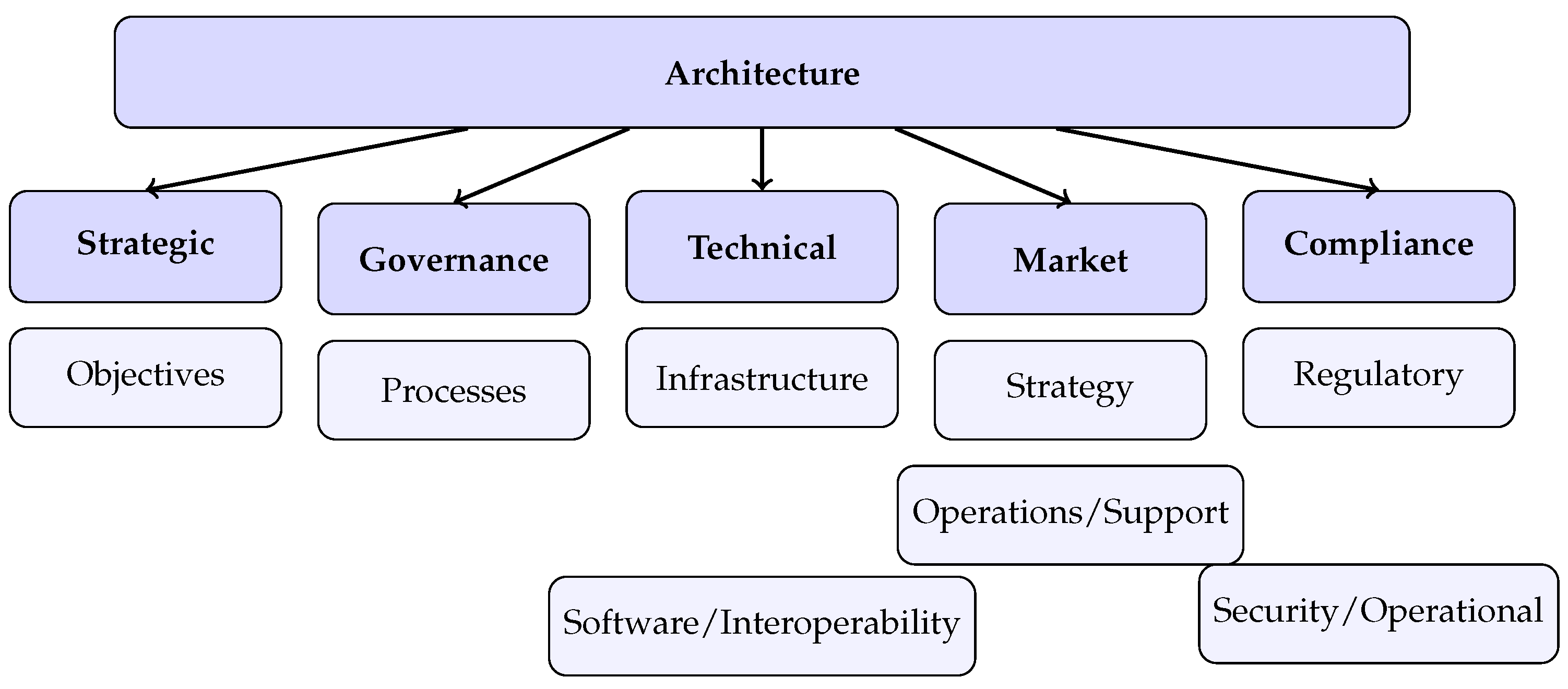
A. Architecture Diagrams and Visual Representations
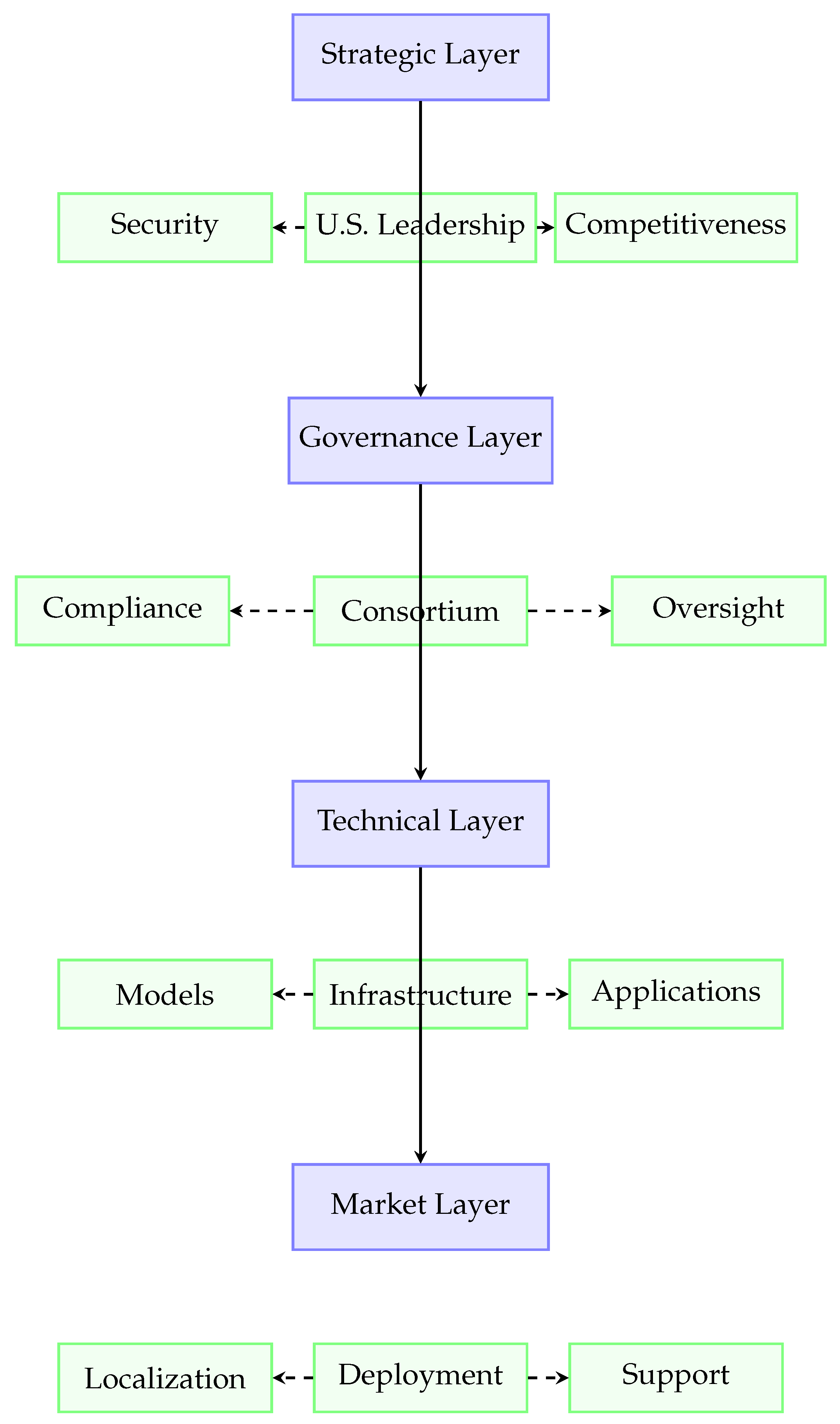
1) Complete Framework Architecture
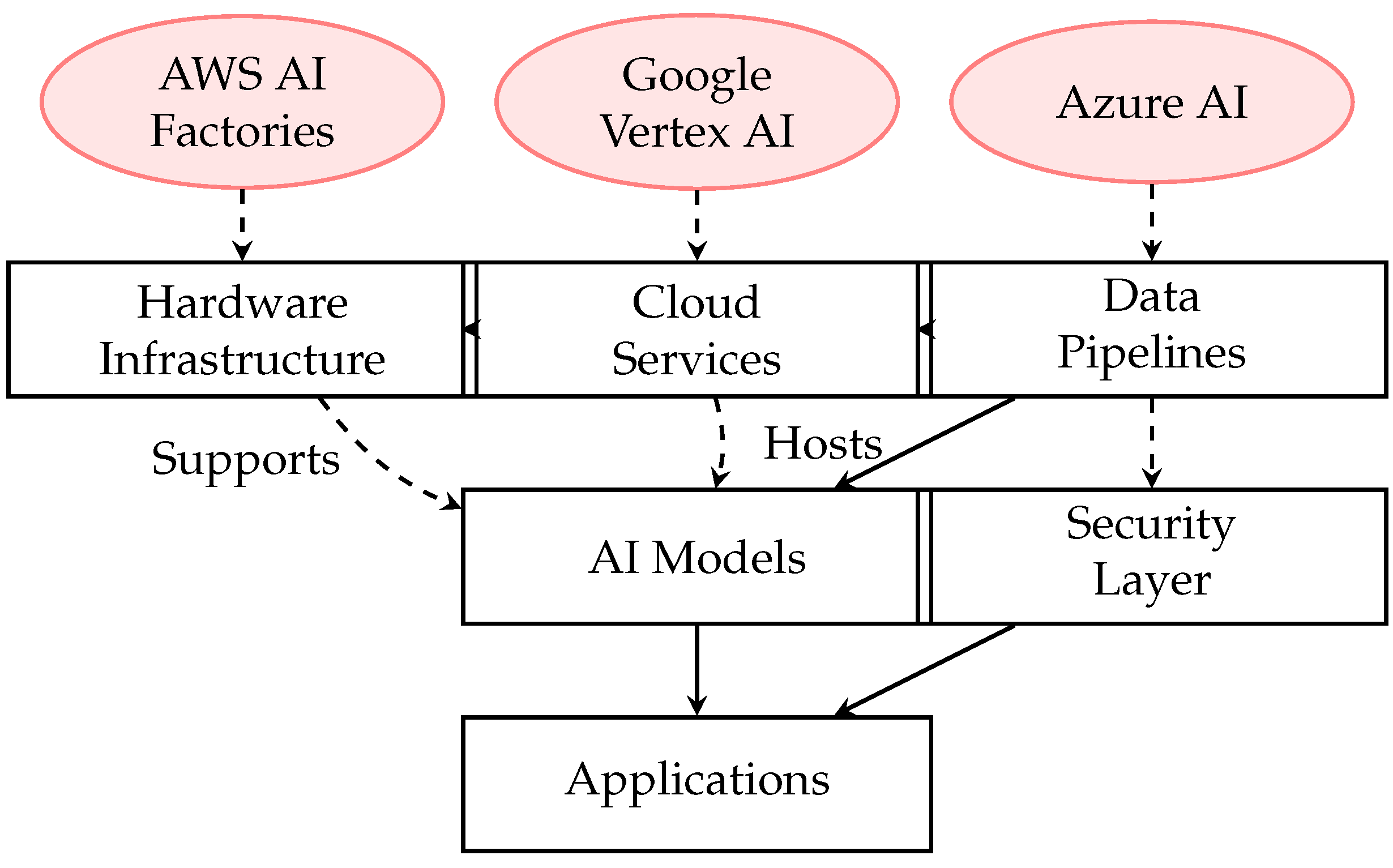
2) Technical Stack Components
B. Strategic Matrices and Decision Frameworks
1) Market Prioritization Matrix
2) Risk Assessment Matrix
C. Implementation Roadmap Visualization
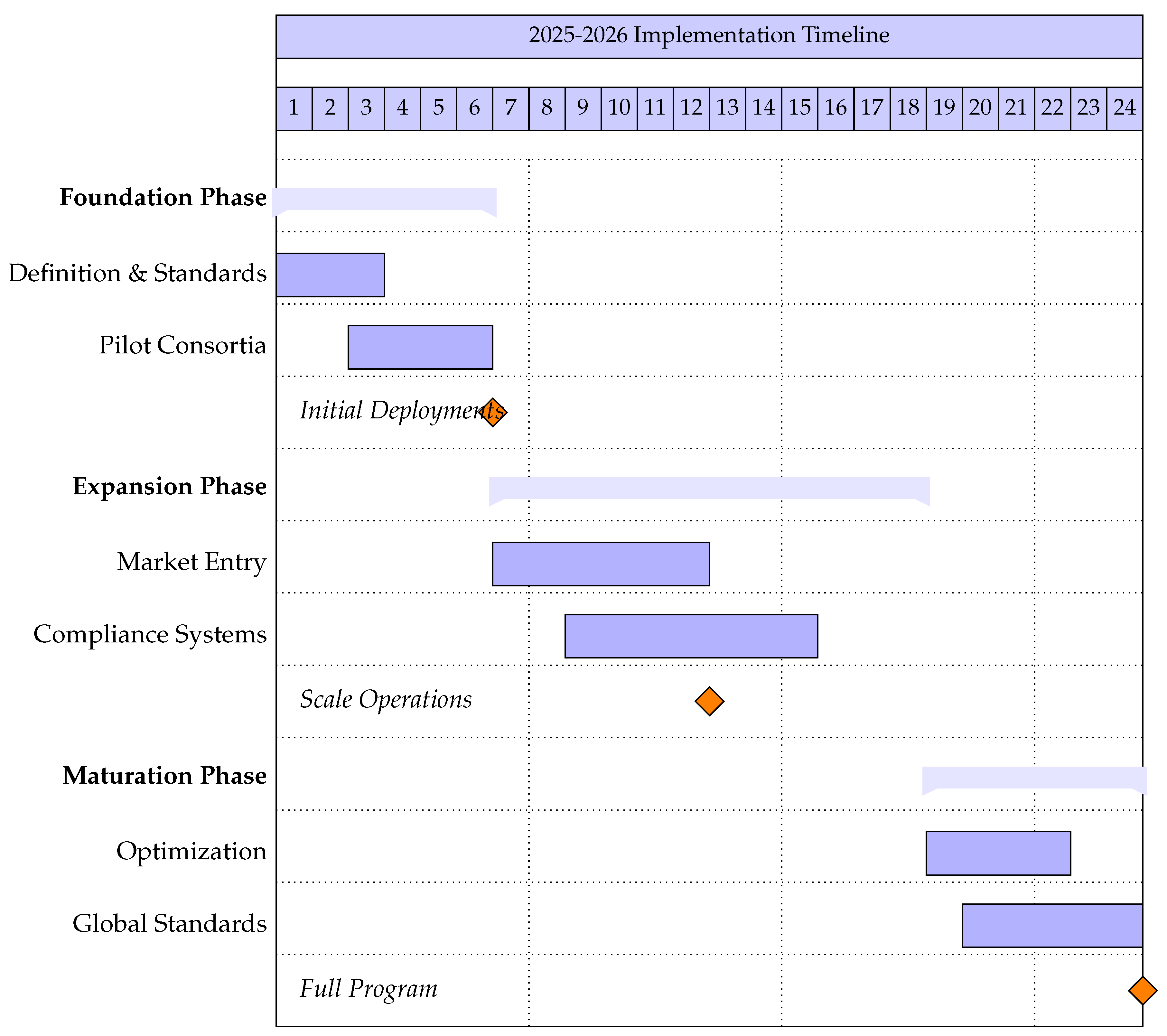
1) Phased Implementation Timeline
2) Stakeholder Engagement Matrix
D. Technical Architecture Diagrams
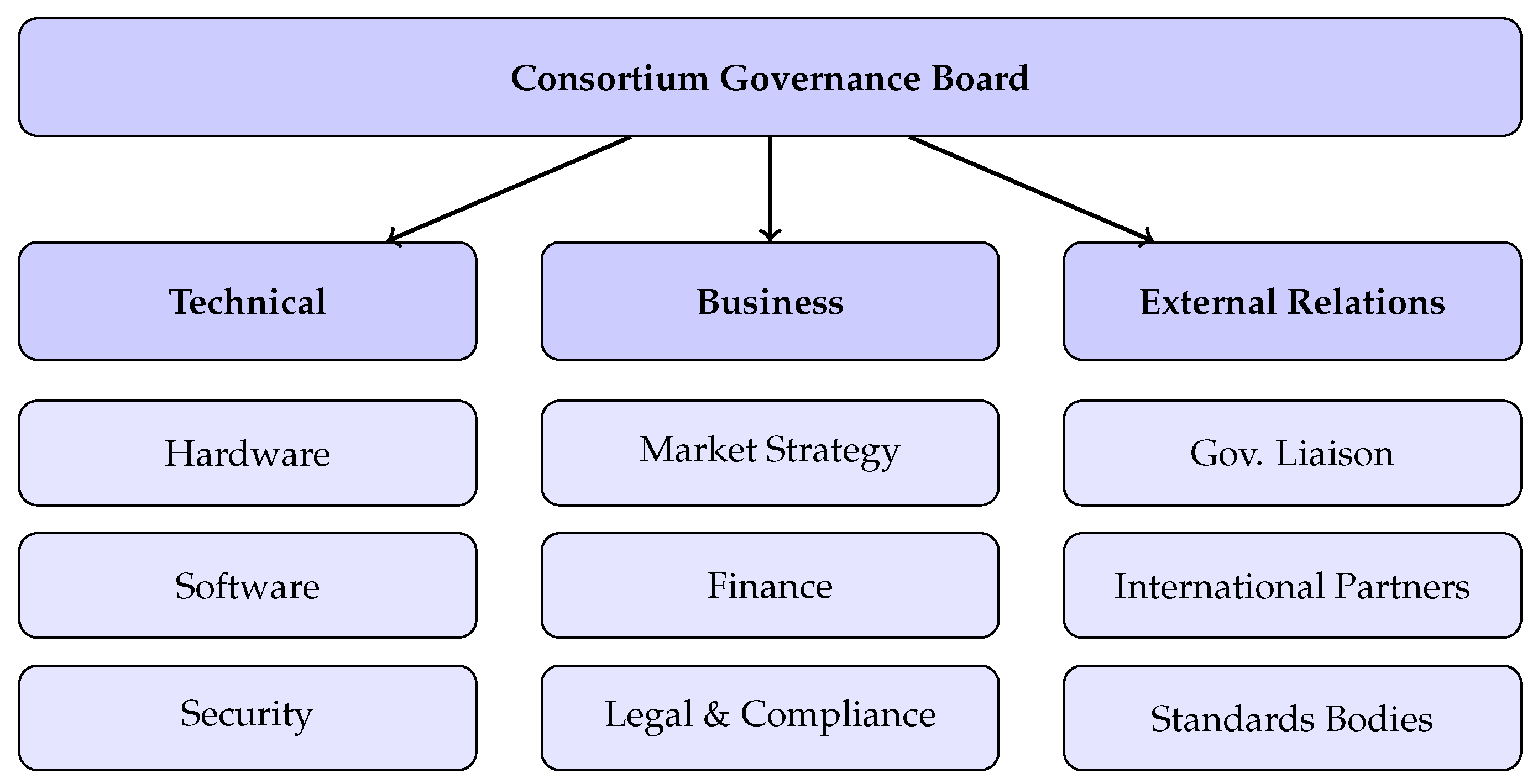
1) Consortium Governance Structure
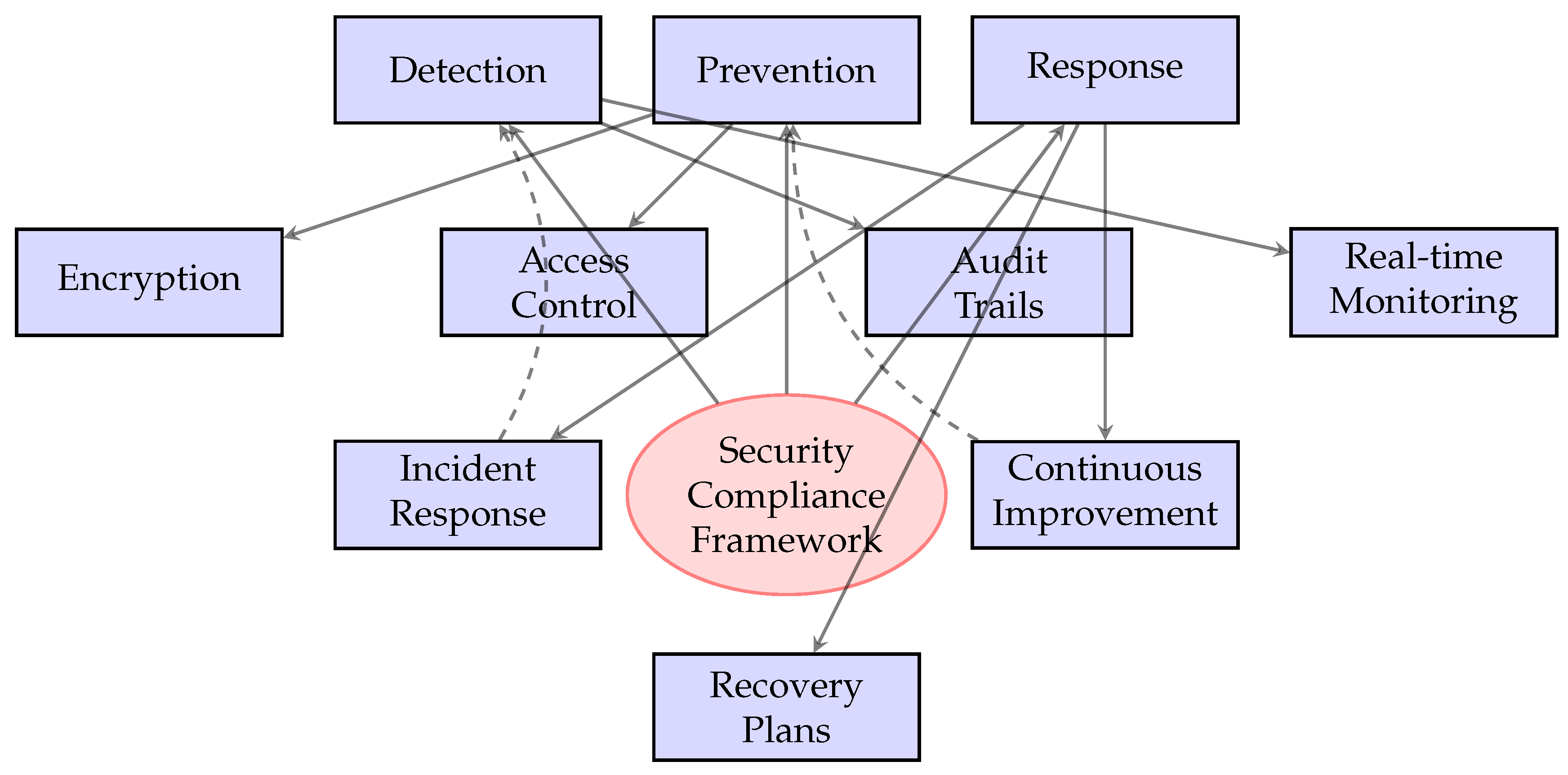
2) Security Compliance Framework
E. Performance Metrics Dashboard
1) Key Performance Indicators Matrix
2) Decision Support Matrix
F. Summary of Architecture Components (Tree Diagram Version)
- Financial Metrics: Revenue, ROI, Cost efficiency
- Technical Metrics: Uptime, Performance, Reliability
- Security Metrics: Compliance, Incident response
- Strategic Metrics: Market position, Innovation rate
| Country/Region | Strategic Alignment | Market Readiness | ||
|---|---|---|---|---|
| Alliance | Economic | Infrastructure | Regulatory | |
| United Kingdom | High | High | High | High |
| Japan | High | High | High | Medium |
| Germany | High | High | High | High |
| Singapore | Medium | High | High | High |
| United Arab Emirates | Medium | High | High | Medium |
| India | Medium | High | Medium | Medium |
| Brazil | Medium | High | Medium | Low |
| Vietnam | Low | Medium | Low | Low |
| Risk Category | Probability | Impact | Mitigation Strategy | Owner |
|---|---|---|---|---|
| Technology Diversion | High | Critical | Automated compliance monitoring | Security Team |
| IP Theft | Medium | High | Encryption & licensing controls | Legal Department |
| Market Competition | High | High | Strategic pricing & partnerships | Business Development |
| Regulatory Changes | Medium | Medium | Agile compliance frameworks | Compliance Office |
| Supply Chain Disruption | Low | High | Multi-source procurement | Operations |
| Cybersecurity Breach | Medium | Critical | Layered security protocols | CISO |
| Stakeholder Group | Phase 1 (0-6 mo) | Phase 2 (7-12 mo) | Phase 3 (13-18 mo) | Phase 4 (19-24 mo) | Success Metrics |
|---|---|---|---|---|---|
| AI Technology Providers | Consultation & Requirements | Pilot Participation | Full Deployment | Optimization & Feedback | Export Revenue, Market Share |
| Government Agencies | Policy Development | Regulatory Alignment | Diplomatic Support | International Standards | Trade Agreements, Compliance |
| Foreign Partners | Market Assessment | Localization Planning | Joint Operations | Capacity Building | Local Jobs, Technology Transfer |
| Security Experts | Framework Development | Compliance Testing | Ongoing Monitoring | Threat Intelligence | Security Incidents, Audit Results |
| Content Industry | IP Framework | Licensing Agreements | Royalty Management | Copyright Protection | Licensing Revenue, Infringement Cases |
| KPI Category | Metric | Target | Measurement Method |
|---|---|---|---|
| Market Performance | Export Revenue | $10B Year 3 | Quarterly Financial Reports |
| Market Share | 40% in Priority Markets | Market Analysis Surveys | |
| Customer Satisfaction | 90%+ | NPS Surveys | |
| Security Compliance | Security Incidents | < 0.1% | Security Monitoring Systems |
| Compliance Audit Score | 95%+ | Independent Audits | |
| Response Time | < 1 hour | Incident Response Logs | |
| Technical Performance | System Uptime | 99.9% | Monitoring Systems |
| Data Processing Speed | < 100ms | Performance Testing | |
| Interoperability Score | 95%+ | Integration Testing | |
| Strategic Impact | Technology Leadership Index | Top 3 Global | Gartner/IDC Rankings |
| IP Protection Score | 90%+ | Legal Compliance Audits | |
| Partner Satisfaction | 85%+ | Partner Surveys |
| Decision Scenario | Data Required | Analysis Method | Stakeholders | Timeframe | Success Criteria |
|---|---|---|---|---|---|
| Market Entry | Market size, Competition, Regulations | SWOT Analysis, PESTLE | Business Dev, Legal | 30-60 days | Profitability > 20% ROI |
| Technology Selection | Technical specs, Cost, Compatibility | TCO Analysis, Scoring Matrix | CTO, Engineering | 60-90 days | Performance > SLAs |
| Partner Selection | Capabilities, Reputation, Alignment | Due Diligence, Reference Checks | Partnerships, Legal | 45-60 days | Strategic Fit > 80% |
| Security Implementation | Threat Models, Compliance Regs | Risk Assessment, Gap Analysis | CISO, Compliance | Ongoing | Zero Critical Breaches |
| Scale Decision | Demand Forecast, Capacity, Costs | ROI Analysis, Capacity Planning | Operations, Finance | Quarterly | Efficiency Gains > 15% |
G. Implementation Recommendations
- 1)
- Phase 1 (0-6 months): Establish governance structures and technical foundations
- 2)
- Phase 2 (7-18 months): Deploy pilot programs in priority markets
- 3)
- Phase 3 (19-36 months): Scale operations and optimize performance
- 4)
- Phase 4 (37+ months): Lead global standards and innovation
IV. Research Methodology
A. Data Collection and Analysis
B. Analytical Framework
- 1)
- Technical Infrastructure: Hardware, software, and platform considerations
- 2)
- Governance Structures: Consortium formation, compliance mechanisms, oversight frameworks
- 3)
- Market Dynamics: Competitive positioning, customer requirements, partner ecosystems
- 4)
- Policy Environment: Regulatory frameworks, trade agreements, diplomatic considerations
V. Stakeholder Analysis and Perspectives
A. Technology Providers: Infrastructure and Implementation
- Stack Integration: Requirements for seamless interoperability across technology layers [23]
- Deployment Models: Varied approaches including Build-Own-Operate and managed services
- Security Integration: Built-in compliance mechanisms for international deployments [24]
- Localization Requirements: Adaptation needs for diverse international markets
B. Content Industry: Intellectual Property Framework
- Licensing Frameworks: Standardized approaches for training data usage [25]
- Compliance Verification: Mechanisms for ensuring proper data sourcing
- Market Access Conditions: Requirements for recipient country IP protection levels
- Dispute Resolution: Processes for addressing copyright concerns internationally
C. Security and Compliance Experts: Risk Management
- Automated Monitoring: Real-time compliance verification systems [19]
- Layered Security: Multi-level protection for different technology components
- Audit Capabilities: Comprehensive logging and reporting mechanisms
- Incident Response: Protocols for addressing security breaches
D. Policy Analysts: Strategic Considerations
- Competitive Positioning: Response to state-subsidized alternatives
- Diplomatic Coordination: Integration with broader foreign policy objectives
- Capacity Building: Development of partner country capabilities
- Long-term Sustainability: Creation of self-sustaining market ecosystems
VI. Technical Implementation Framework
A. Architecture Design Principles
B. Compliance Automation System
- Dynamic Classification: Automated Export Control Classification Number (ECCN) determination based on technical specifications
- Real-time Monitoring: Continuous verification of deployment parameters against regulatory requirements
- Reporting Automation: Generation of compliance documentation and audit trails
- Alert Mechanisms: Immediate notification of potential compliance issues
C. Security Implementation
- Model Protection: Techniques for securing AI model weights and architectures
- Data Security: Encryption and access control for training and operational data
- Infrastructure Security: Protection of underlying hardware and software platforms
- Operational Security: Safeguards for deployment and maintenance processes
VII. Governance and Compliance Framework
A. Consortium Governance Structure
| Component | Requirements | Implementation Guidelines |
|---|---|---|
| Legal Structure | Incorporated entity with defined governance | Establish clear articles of incorporation and bylaws |
| Membership | Clear eligibility criteria and vetting processes | Implement tiered membership with graduated privileges |
| Decision-Making | Transparent processes with documented procedures | Create technical and business review committees |
| IP Management | Defined ownership and licensing frameworks | Establish standard IP agreements and dispute resolution |
| Compliance | Integrated compliance monitoring and reporting | Deploy automated systems with manual oversight |
B. Regulatory Compliance Architecture
- Export Controls: ITAR, EAR, and dual-use regulations
- Data Protection: GDPR, CCPA, and other privacy regulations
- Intellectual Property: Copyright, patent, and trade secret protections
- Industry Standards: Sector-specific regulations and certifications
C. Risk Management System
- Risk Assessment: Systematic evaluation of technical, commercial, and policy risks
- Mitigation Strategies: Proactive measures to address identified risks
- Monitoring: Continuous tracking of risk indicators and compliance status
- Response Protocols: Documented procedures for addressing incidents
VIII. Market Strategy and Implementation
A. Market Segmentation and Prioritization
| Tier | Strategic Alignment | Market Readiness | Example Markets |
|---|---|---|---|
| Tier 1 | High (Alliance members) | High (Infrastructure, regulation) | UK, Canada, Japan, Australia |
| Tier 2 | Medium (Partners) | Medium (Growing capabilities) | India, UAE, Singapore, Brazil |
| Tier 3 | Developing (Emerging) | Low (Building foundations) | Vietnam, Indonesia, Colombia |
B. Deployment Models
- Direct Export: Complete technology stack delivery
- Licensing: Technology transfer with local adaptation
- Joint Venture: Collaborative development and deployment
- Managed Services: Ongoing operation and maintenance support
C. Capacity Building Programs
- Technical Training: Development of local AI expertise
- Regulatory Alignment: Support for developing appropriate frameworks
- Ecosystem Development: Fostering local innovation communities
- Standards Participation: Engagement in international standards development
IX. Policy Recommendations and Implementation Roadmap
A. Immediate Actions (0-6 Months)
- 1)
- Establish clear definitions for consortium structures and full-stack components
- 2)
- Develop standardized compliance frameworks based on NIST and ISO standards
- 3)
- Create pilot programs for automated export control implementation
- 4)
- Initiate interagency coordination for financing and diplomatic support
0.1. Medium-Term Initiatives (6-18 Months)
- 1)
- Launch targeted consortia in priority markets with balanced representation
- 2)
- Implement comprehensive monitoring and reporting systems
- 3)
- Develop bilateral agreements for technology sharing and cooperation
- 4)
- Establish certification programs for export-ready AI solutions
B. Long-Term Strategy (18+ Months)
- 1)
- Create sustainable financing mechanisms for international AI infrastructure
- 2)
- Build global coalitions for responsible AI development and deployment
- 3)
- Establish feedback loops for continuous program improvement
- 4)
- Develop metrics for measuring program effectiveness and impact
X. Case Studies and Best Practices
A. Successful AI Export Initiatives
- Clear Value Proposition: Demonstrable benefits for recipient countries
- Robust Governance: Effective oversight and compliance mechanisms
- Local Adaptation: Customization to specific market needs and conditions
- Sustainable Partnerships: Long-term collaborative relationships
B. Lessons Learned from Previous Programs
- Importance of phased implementation and iterative improvement
- Need for flexible adaptation to changing market conditions
- Value of comprehensive risk assessment and management
- Benefits of transparent communication and stakeholder engagement
XI. The American AI Exports Program Analysis
A. Key Requirements Analysis
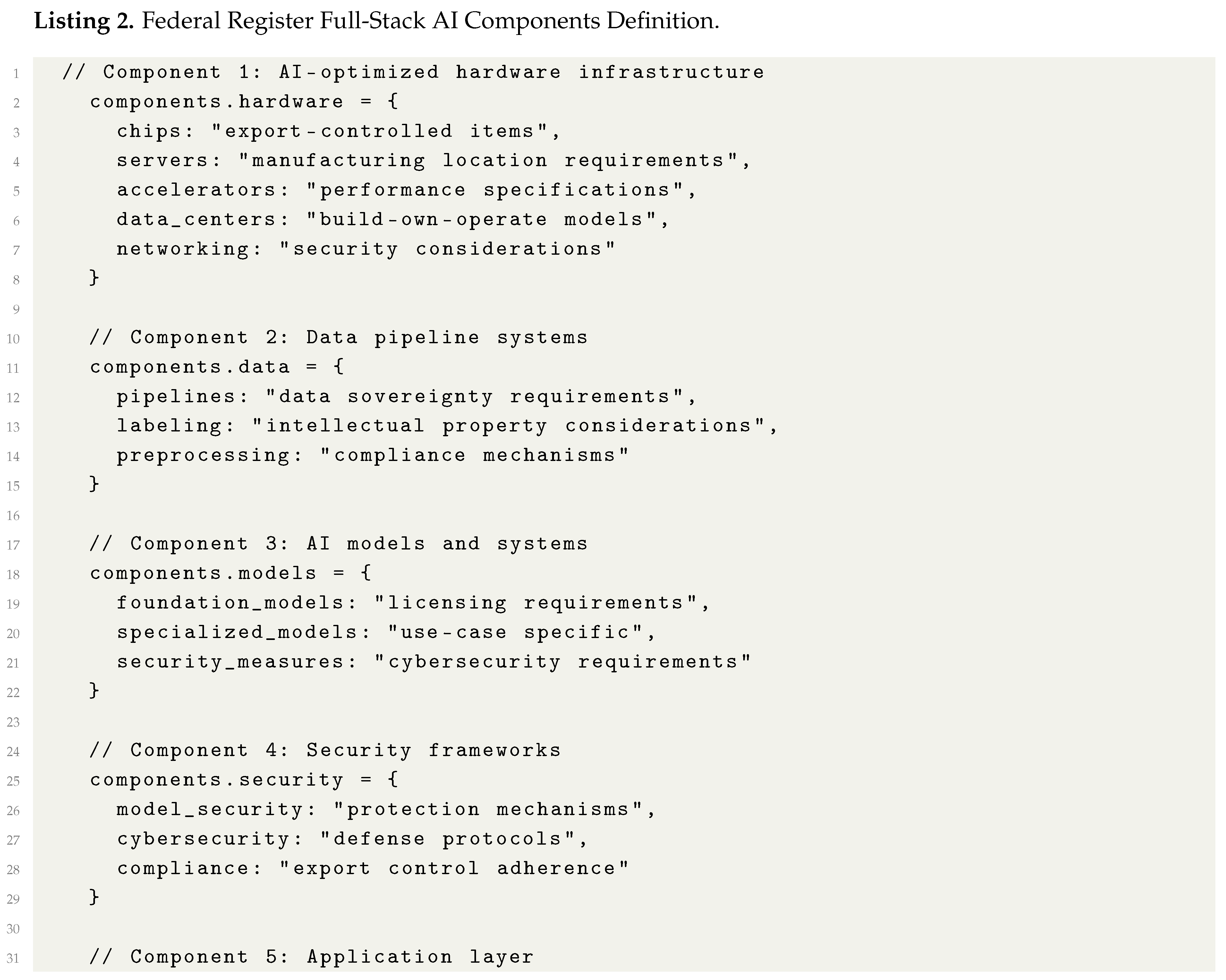
1) Full-Stack AI Technology Package Definition
2) Consortium Formation Requirements
| Aspect | RFI Requirement | Industry Implications |
|---|---|---|
| Eligibility | U.S.-based leadership with export capacity | Potential exclusion of smaller enterprises |
| Foreign Participation | Limited with security vetting | Need for trusted partner frameworks |
| Modularity | Encouraged but not required | Flexibility in technology integration |
| Governance | Transparent decision-making structures | Alignment with corporate governance standards |
| Lead Entity | Designated leadership with integration experience | Concentration of power in large tech firms |
B. Security and Compliance Framework
- Export Controls: Full adherence to Bureau of Industry and Security regulations
- Outbound Investment: Compliance with CFIUS and related frameworks
- End-User Policies: Strict vetting of technology recipients
- Cybersecurity: Implementation of NIST-aligned security measures
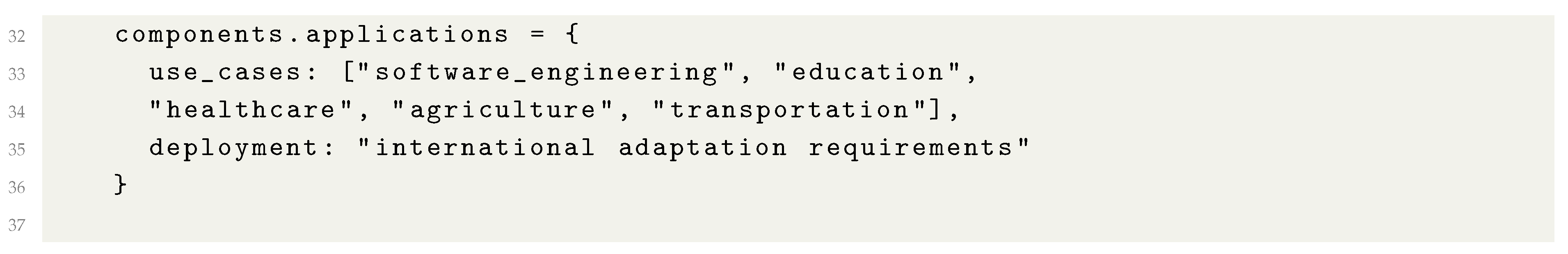
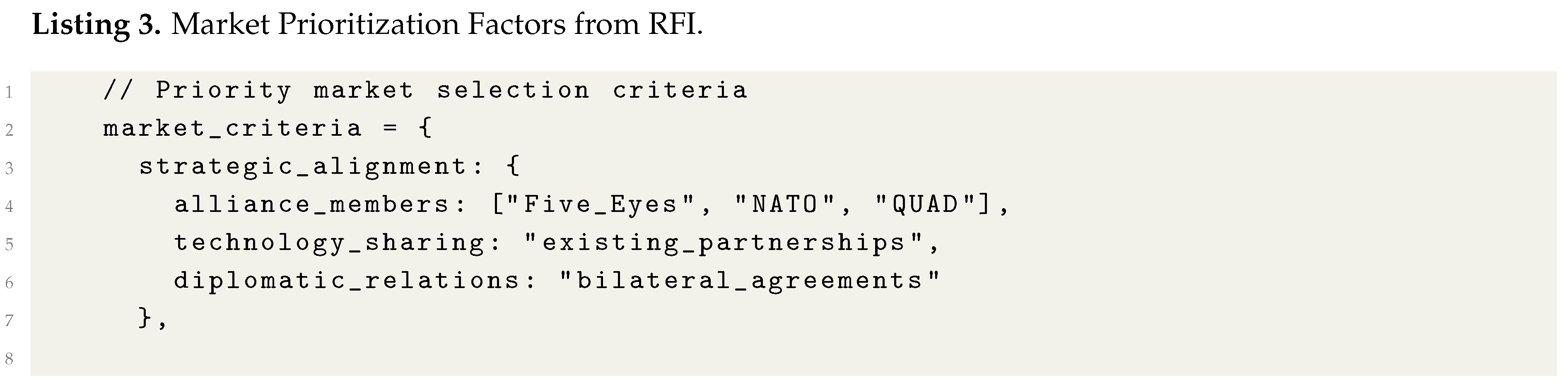
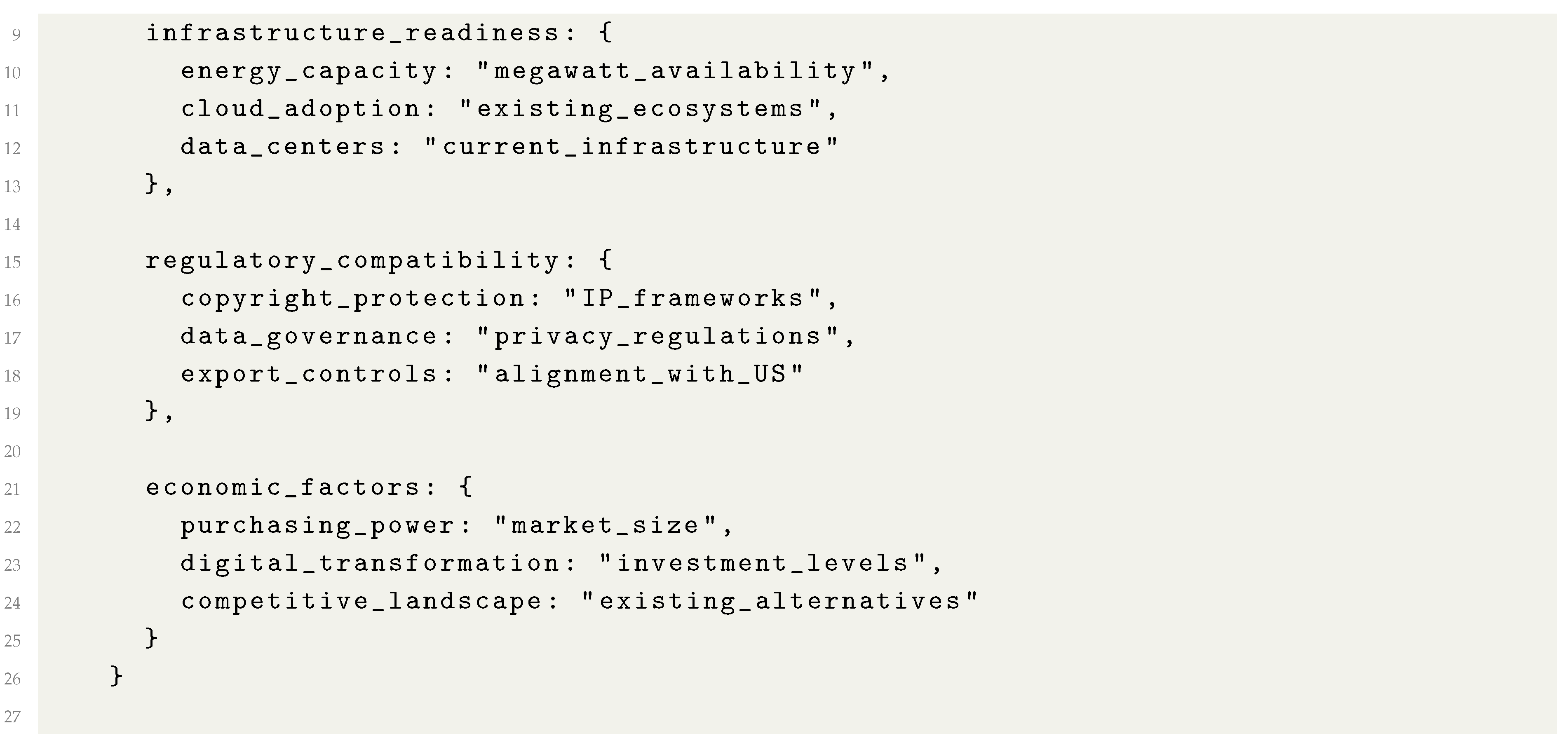
C. Market Strategy Implications
D. Federal Support Mechanisms
| Support Type | Legal Authority | Industry Relevance |
|---|---|---|
| Direct Loans | 12 U.S.C. 635 | Infrastructure financing |
| Loan Guarantees | 12 U.S.C. 635 | Risk mitigation |
| Equity Investments | 22 U.S.C. 9621 | Consortium capitalization |
| Political Risk Insurance | 22 U.S.C. 9621 | International deployment |
| Technical Assistance | 22 U.S.C. 2421(b) | Implementation support |
| Feasibility Studies | 22 U.S.C. 2421(b) | Market assessment |
| Regulatory Guidance | Agency discretion | Compliance navigation |
| Diplomatic Support | State Department | Market access |
E. Implementation Challenges Identified
1) Definitional Ambiguity
- "Consortium" formation and governance structures
- "Full-stack" technology package boundaries
- "Industry-led" versus government-involved participation
- "Trusted partner" criteria for foreign participation
2) Security-Competitiveness Balance
- Export control compliance versus technology accessibility
- End-user vetting versus market expansion
- Security frameworks versus implementation flexibility
- Compliance costs versus price competitiveness
3) Intellectual Property Considerations
- Technology transfer controls
- Licensing requirements for AI models
- Copyright protection for training data
- Patent considerations for AI innovations
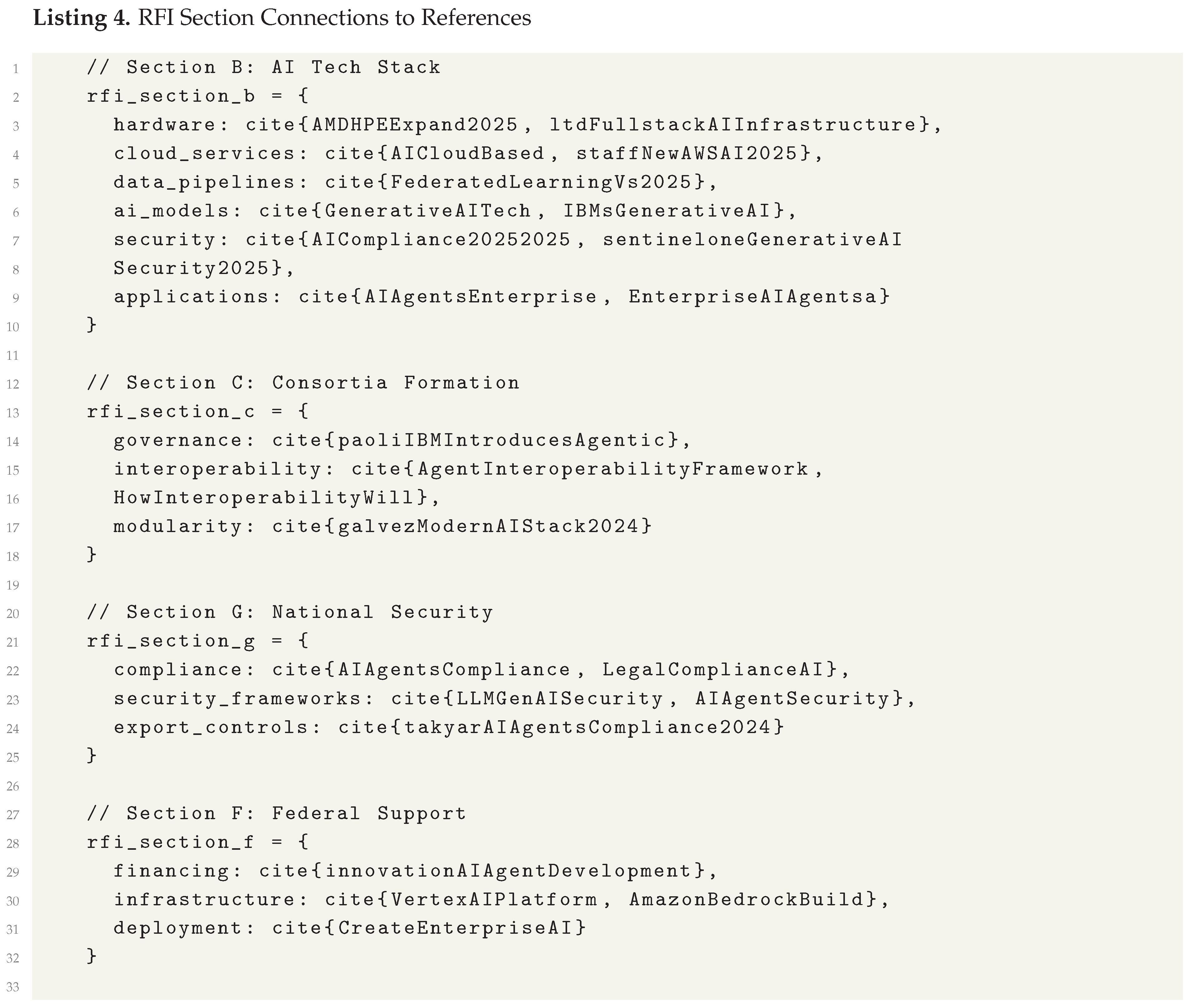
F. Connections to Industry References
G. Strategic Implications and Recommendations
1) Implementation Priority Areas
- 1)
- Clarity in Definitions: Immediate need for precise definitions of consortium structures and technology stack components
- 2)
- Security Frameworks: Development of standardized compliance mechanisms that balance security with competitiveness
- 3)
- Market Strategy: Systematic approach to market prioritization based on multiple criteria
- 4)
- Support Coordination: Integrated approach to federal support mechanisms across agencies
2) Policy Recommendations
- Establish clear consortium governance templates with standardized IP management frameworks
- Develop graduated security compliance levels based on destination country risk assessments
- Create flexible participation models that accommodate both large consortia and specialized providers
- Implement phased market entry strategies with pilot programs in priority markets
- Establish feedback mechanisms for continuous program improvement based on implementation experience
3) Research Opportunities
- Impact of consortium models on innovation ecosystems and market competition
- Effectiveness of different security-compliance frameworks in international deployments
- Comparative analysis of federal support mechanisms across technology sectors
- Longitudinal studies of AI export program impacts on U.S. competitiveness
XII. Figures and Tables Reference
A. Figures Reference
| Figure | Description | Section |
|---|---|---|
| Figure 1 | Multi-Layer Framework Architecture for AI Exports Program showing strategic, governance, technical, and market layers with their components | |
| Figure 2 | Technical Stack Component Architecture illustrating hardware infrastructure, cloud services, data pipelines, AI models, security layer, and applications | |
| Figure 3 | Three-Phase Implementation Roadmap using Gantt chart to visualize Foundation, Expansion, and Maturation phases over 24 months | |
| Figure 4 | Consortium Governance Organizational Structure showing hierarchical relationship between Governance Board, Technical Committee, Business Committee, and External Relations | |
| Figure 5 | Layered Security Compliance Framework illustrating prevention, detection, response mechanisms with their subcomponents and feedback loops | |
| Figure 6 | Visual Representation of Architecture Components as tree diagram showing Strategic, Governance, Technical, Market, and Compliance layers |
B. Tables Reference
| Table | Description | Section |
|---|---|---|
| Table 1 | Market Prioritization Matrix with Strategic Scoring for 8 countries/regions across Strategic Alignment and Market Readiness dimensions | |
| Table 2 | Comprehensive Risk Assessment Matrix covering 6 risk categories with Probability, Impact, Mitigation Strategy, and Owner columns | |
| Table 3 | Stakeholder Engagement and Responsibility Matrix showing engagement activities across 4 phases for 5 stakeholder groups | |
| Table 4 | Comprehensive Performance Metrics Dashboard with 4 KPI categories (Market Performance, Security Compliance, Technical Performance, Strategic Impact) | |
| Table 5 | Decision Support Matrix for Program Management covering 5 decision scenarios with Data Required, Analysis Method, Stakeholders, Timeframe, and Success Criteria | |
| Table 6 | Consortium Governance Framework Components table showing 5 components with Requirements and Implementation Guidelines | |
| Table 7 | Market Prioritization Matrix with 3 tiers (Tier 1, 2, 3) showing Strategic Alignment, Market Readiness, and Example Markets | |
| Table 8 | Federal Register Consortium Requirements Analysis table comparing RFI Requirements with Industry Implications across 5 aspects | 0.1 |
| Table 9 | Federal Support Mechanisms Analysis table showing 8 support types with Legal Authority and Industry Relevance | 0.1 |
| Table 10 | List of Figures in the Paper (this table) - Reference table for all figures | 0.1 |
| Table 11 | List of Tables in the Paper (this table) - Reference table for all tables | 0.1 |
| Table 12 | List of Code Listings in the Paper (this table) - Reference table for all code listings | 0.1 |
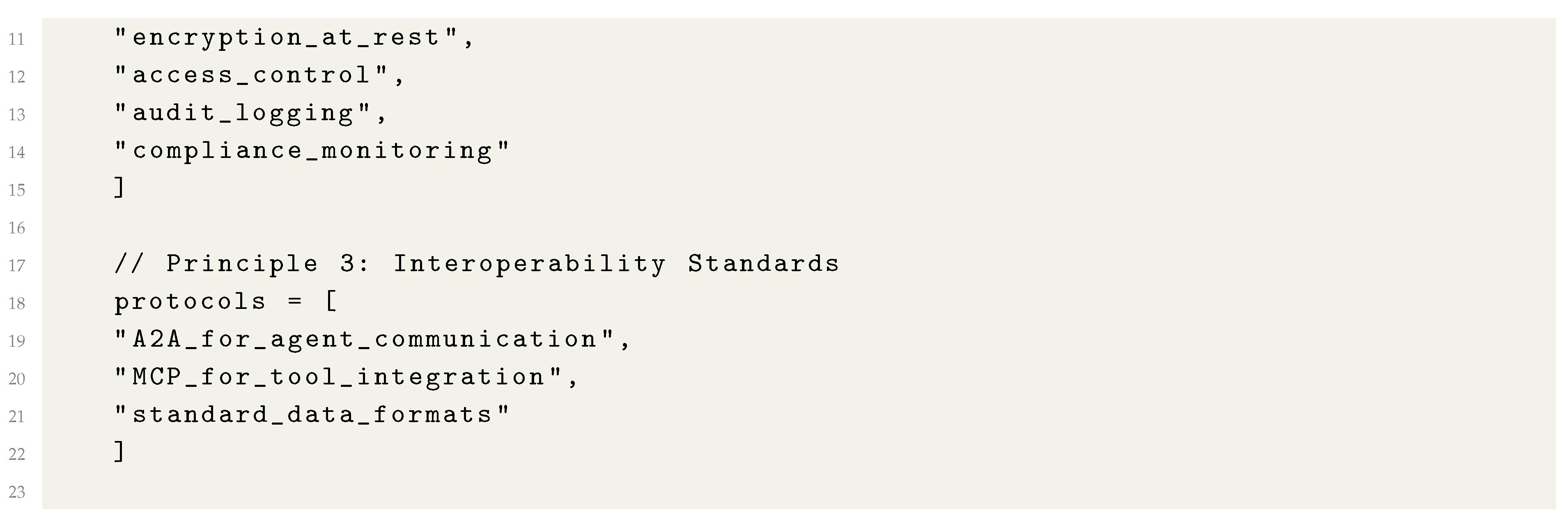
C. Code Listings Reference
| Listing | Description | Section |
|---|---|---|
| 1 | Key Design Principles for Export-Ready AI Stacks showing modular architecture, security by design, and interoperability standards in pseudocode format | |
| 2 | Federal Register Full-Stack AI Components Definition showing 5 components (hardware, data, models, security, applications) with their properties in pseudocode | 0.1 |
| 3 | Market Prioritization Factors from RFI showing selection criteria (strategic alignment, infrastructure readiness, regulatory compatibility, economic factors) in pseudocode | 0.1 |
| 4 | RFI Section Connections to References showing how different RFI sections connect to bibliography references in pseudocode format | 0.1 |
D. Visualization Summary
- 6 Figures: 2 architectural diagrams, 1 Gantt chart, 2 organizational charts, and 1 tree diagram
- 12 Tables: 7 analytical matrices, 3 reference tables, and 2 governance/implementation tables
- 4 Code Listings: All in pseudocode format illustrating implementation concepts
- 1)
- 2)
- Process Visualization:Figure 3 shows temporal implementation planning
- 3)
- 4)
- 5)
- Technical Specifications: Listings through document implementation details
XIII. Conclusion and Future Research Directions
Declaration
References
- D. W. Ball. Don’t Overthink "The AI Stack". [Online]. Available online: https://www.hyperdimensional.co/p/dont-overthink-the-ai-stack.
- Artificial Intelligence Market worth $2,407.02 billion by 2032. [Online]. Available online: https://www.marketsandmarkets.com/PressReleases/artificial-intelligence.asp.
- K. Chan, G. Smith, J. Goodrich, G. DiPippo, and K. F. Pilz, “Full Stack: China’s Evolving Industrial Policy for AI.” [Online]. Available online: https://www.rand.org/pubs/perspectives/PEA4012-1.html.
- What is an AI Stack? | IBM. [Online]. Available online: https://www.ibm.com/think/topics/ai-stack.
- AI Compliance in 2025: Definition, Standards, and Frameworks | Wiz. wiz.io. [Online]. Available online: https://www.wiz.io/academy/ai-compliance.
- A. Staff. New AWS AI Factories transform customers’ existing infrastructure into high-performance AI environments. [Online]. Available online: https://www.aboutamazon.com/news/aws/aws-data-centers-ai-factories.
- Agent interoperability framework | Designing an Agent Interoperability Framework for Next-Gen AI Collaboration. [Online]. Available online: https://www.llumo.ai/blog/designing-an-agent-interoperability-framework-for-next-gen-ai-collaboration.
- AI Tech Stack: A Complete Guide to Data, Frameworks, MLOps. [Online]. Available online: https://www.coherentsolutions.com/insights/overview-of-ai-tech-stack-components-ai-frameworks-mlops-and-ides.
- AMD and HPE Expand Collaboration to Advance Open Rack-Scale AI Infrastructure. Advanced Micro Devices, Inc. [Online]. Available online: https://ir.amd.com/news-events/press-releases/detail/1269/amd-and-hpe-expand-collaboration-to-advance-open-rack-scale-ai-infrastructure.
- Vertex AI Platform. Google Cloud. [Online]. Available online: https://cloud.google.com/vertex-ai.
- Edge AI vs Federated Learning | Complete Overview. [Online]. Available online: https://www.xenonstack.com/blog/edge-ai-vs-federated-learning.
- N. kaufman. The Rise of the Full-Stack AI Engineer. Israeli Tech Radar. [Online]. Available online: https://medium.com/israeli-tech-radar/the-rise-of-the-full-stack-ai-engineer-0f31fed4e1f0.
- Generative AI Tech Stack: A Comprehensive Guide for Developers. Requestum. [Online]. Available online: https://requestum.com/blog/generative-ai-tech-stack.
- AI Agents for the Enterprise | StackAI. [Online]. Available online: https://www.stack-ai.com/.
- G. A. Li, Yoko. The Trillion Dollar AI Software Development Stack. Andreessen Horowitz. [Online]. Available online: https://a16z.com/the-trillion-dollar-ai-software-development-stack/.
- M. Clark. Agents Today #15 - AI Agent Interoperability: Head-to-Head with MCP and A2A. AgentsToday. [Online]. Available online: https://agentstoday.substack.com/p/agents-today-15-ai-agent-interoperability.
- Federated Learning vs. Edge AI: Preserving Privacy. [Online]. Available online: https://dialzara.com/blog/federated-learning-vs-edge-ai-preserving-privacy.
- I. G. Wambui. The Magical World of Edge AI and Federated Learning: Unleashing the Power of Smart Devices and Protecting Data Privacy. Comet. [Online]. Available online: https://www.comet.com/site/blog/the-magical-world-of-edge-ai-and-federated-learning-unleashing-the-power-of-smart-devices-and-protecting-data-privacy.
- AI Agents’ Compliance | Automate Governance & Stay Audit-Ready. Zenity | Secure AI Agents Everywhere. [Online]. Available online: https://zenity.io/use-cases/business-needs/ai-agents-compliance.
- Modern AI Tech Stack in 2025: The Ultimate Guide. 5ly.co. [Online]. Available online: https://5ly.co/blog/ai-tech-stack/.
- A Comprehensive Guide to AI Tech Stack. Sparx IT Solutions. [Online]. Available online: https://www.sparxitsolutions.com/blog/ai-tech-stack/.
- SentinelOne. Generative AI Security Policy Templates and Best Practices. SentinelOne. [Online]. Available online: https://www.sentinelone.com/cybersecurity-101/data-and-ai/generative-ai-security-policy/.
- Intel. AI Tech Stack Solutions. Intel. [Online]. Available online: https://www.intel.com/content/www/us/en/learn/ai-tech-stack.html.
- LLM & GenAI Security with Our Platform: PlainID. [Online]. Available online: https://www.plainid.com/llm-genai-security/.
- Generative AI Licensing Agreement Tracker. Ithaka S+R. [Online]. Available online: https://sr.ithaka.org/our-work/generative-ai-licensing-agreement-tracker/.
- S. Chatterjee. Why Interoperability Is the Next Big Test for Enterprise AI Agents. RTInsights. [Online]. Available online: https://www.rtinsights.com/why-interoperability-is-the-next-big-test-for-enterprise-ai-agents/.
- AI Agent Security & Data Privacy: Complete Compliance Guide (2025) | P0STMAN. [Online]. Available online: https://p0stman.com/guides/ai-agent-security-data-privacy-guide-2025.html.
- R. Innovation. AI Agent Development Costs: Comprehensive Guide for Businesses. [Online]. Available online: https://www.rapidinnovation.io/post/what-is-the-cost-of-building-ai-agents.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




