Submitted:
06 March 2025
Posted:
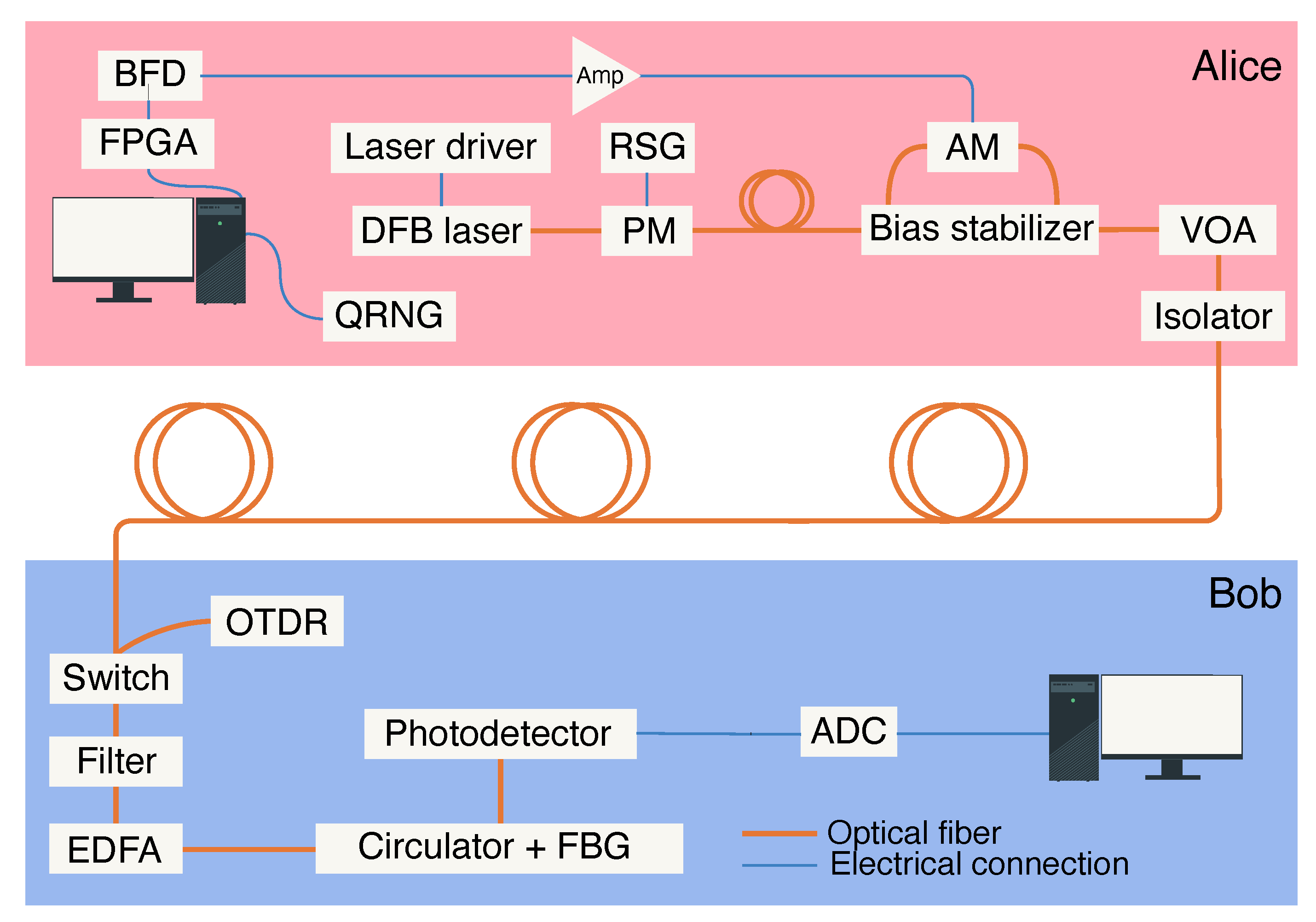
07 March 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Protocol Description
3. Experimental Setup
4. System Configuration
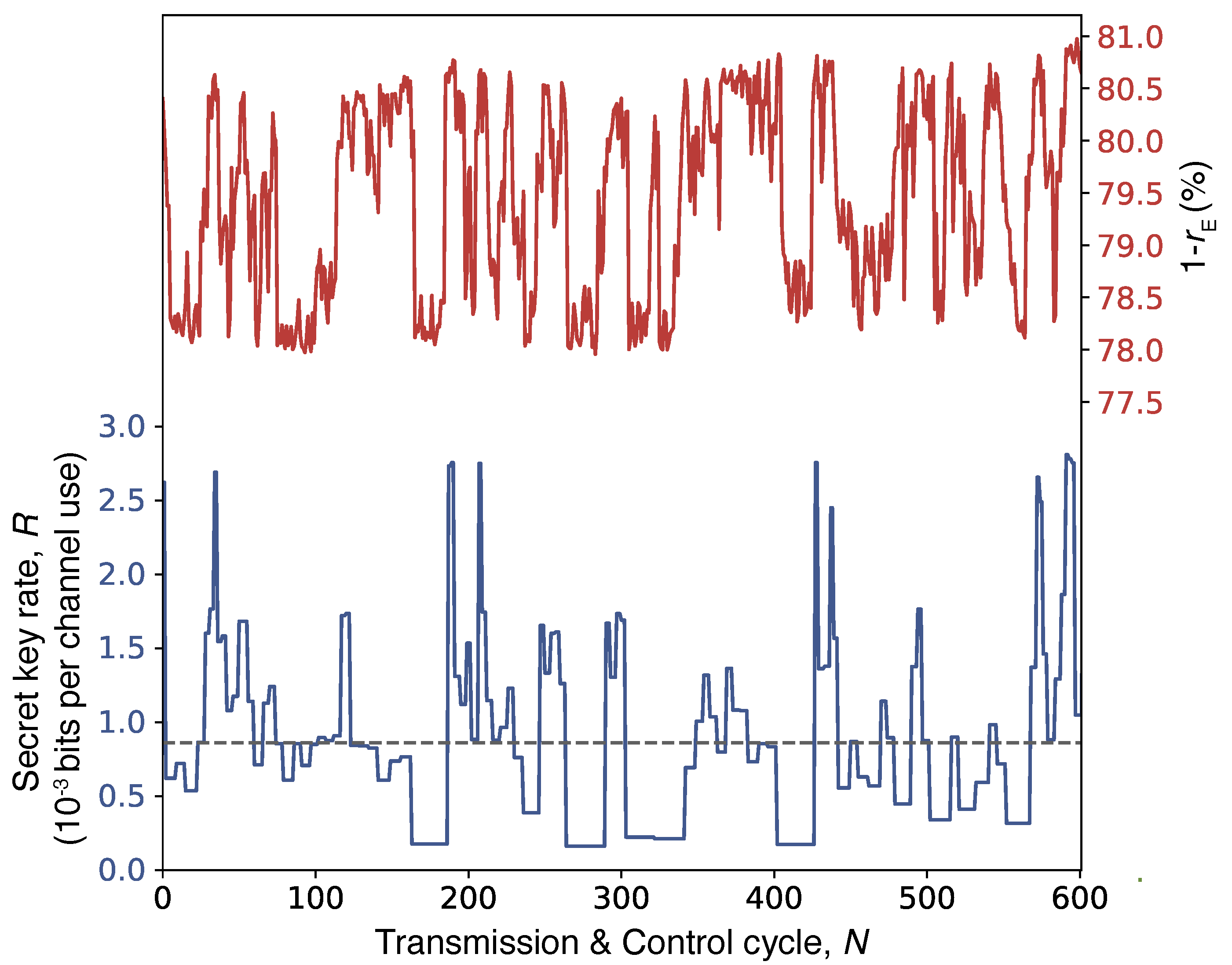
5. Results
6. Discussion
7. Methods
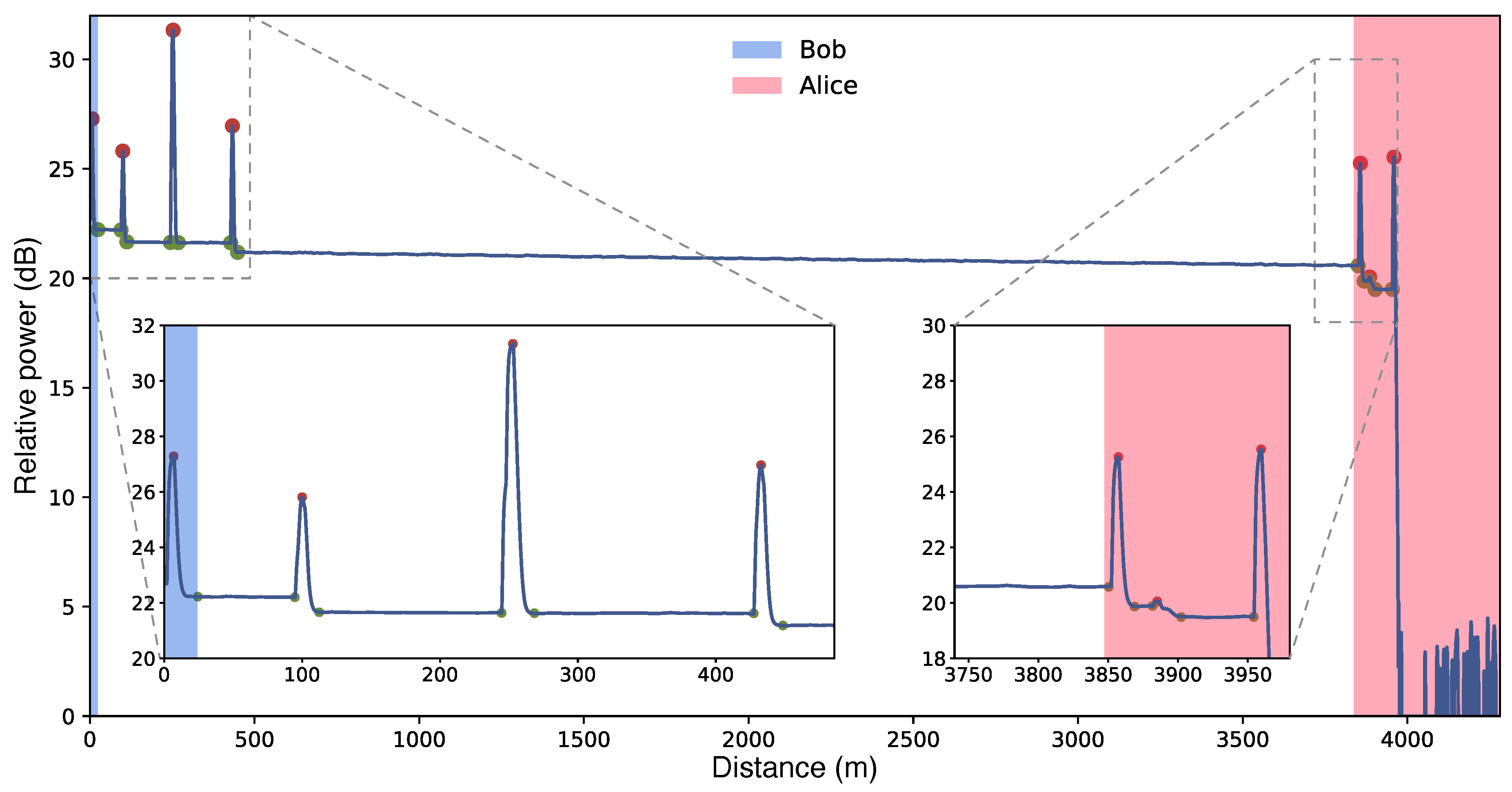
7.1. OTDR and Transmittometry
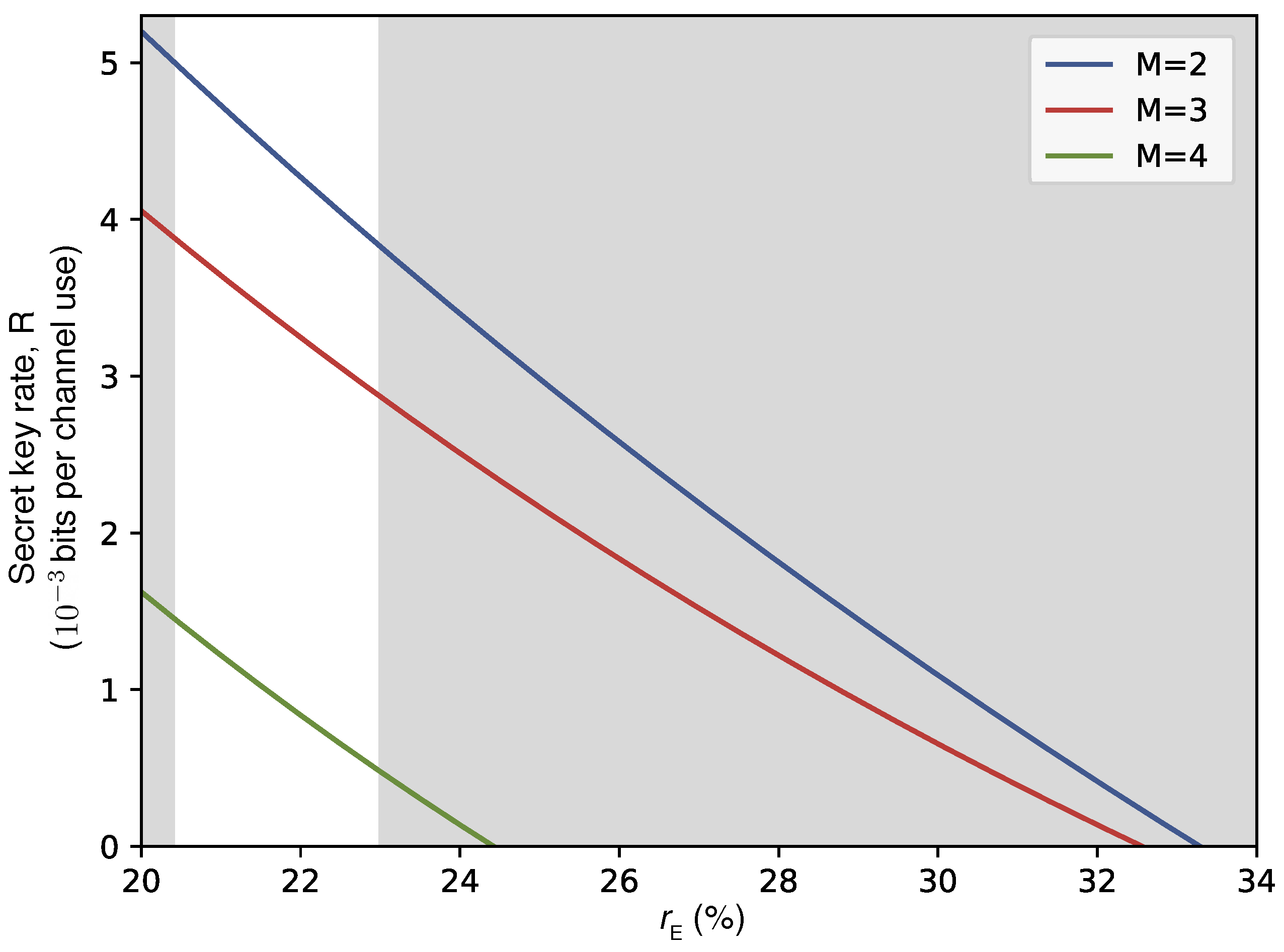
7.2. Eve’s Information
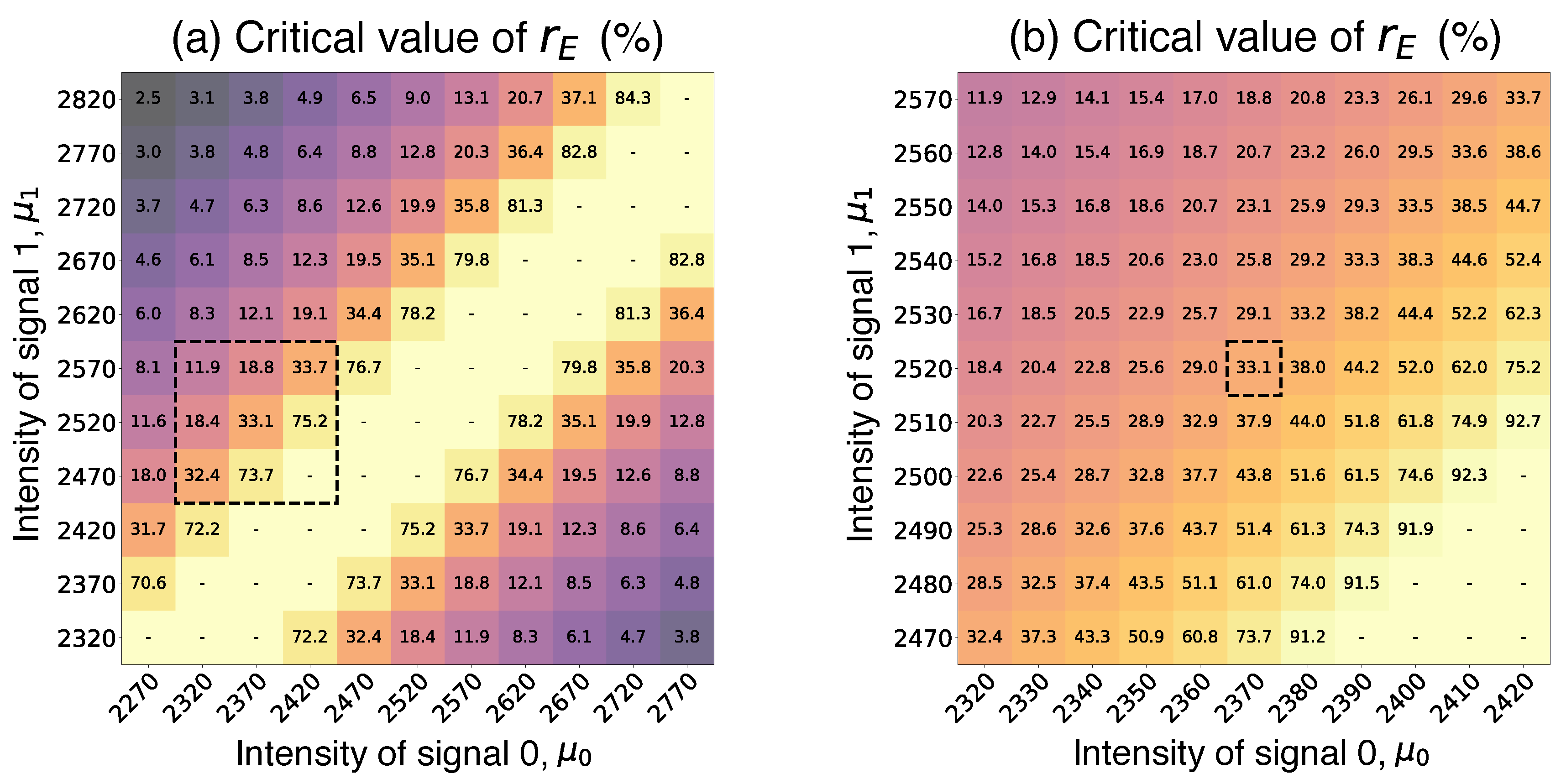
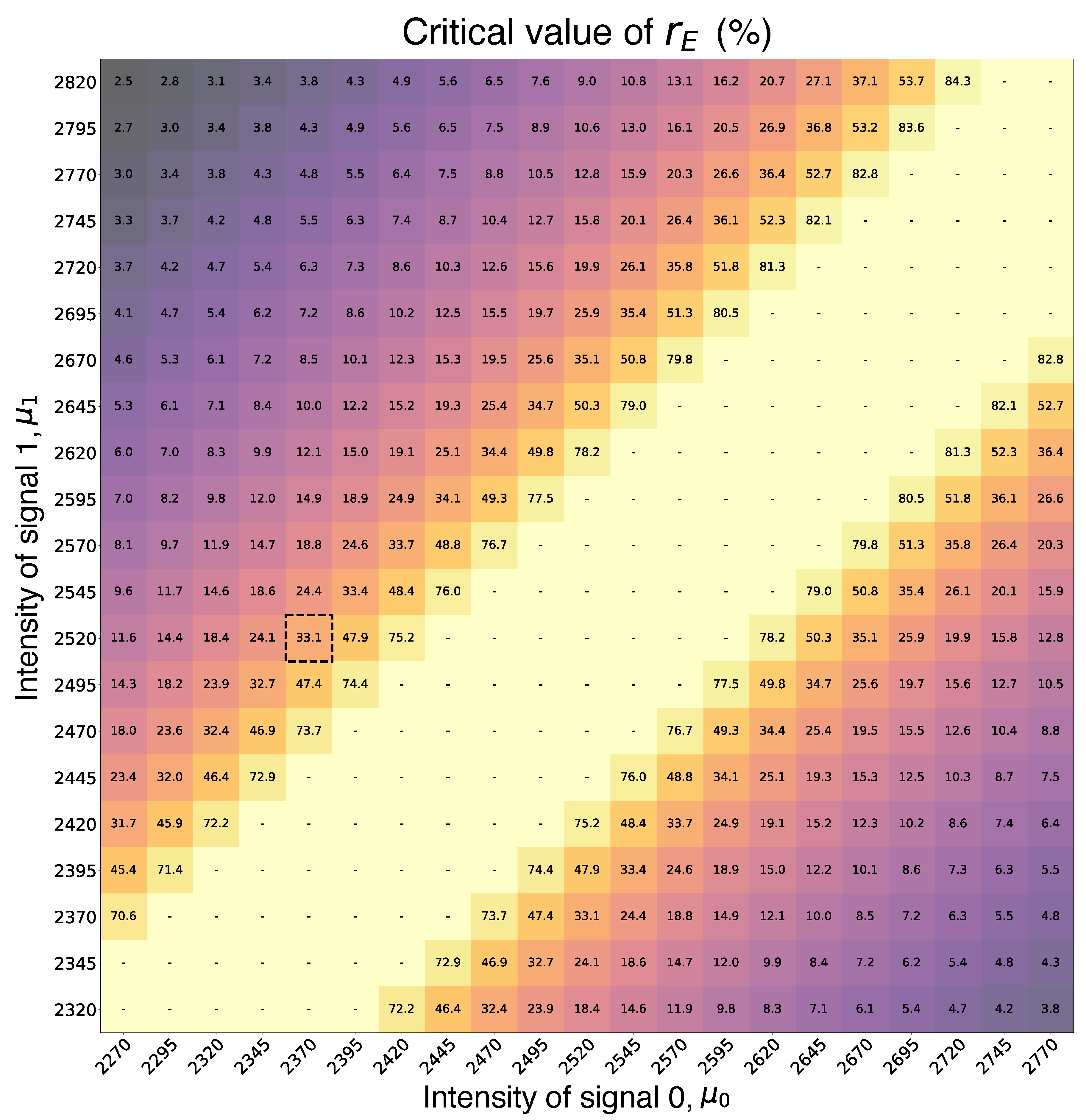
7.3. Critical Leakage Data
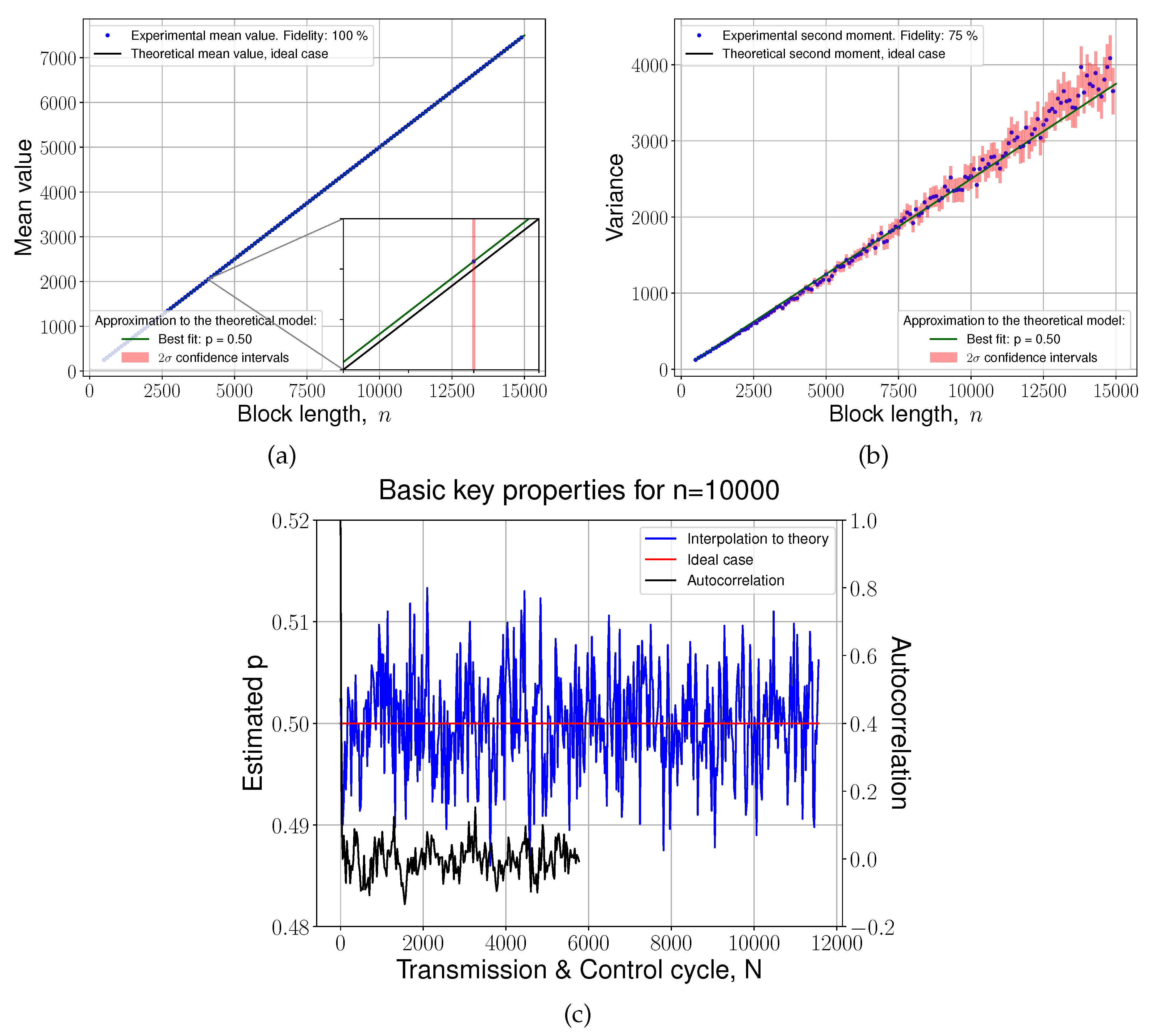
7.4. Statistical Analysis
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| ADC | Analog-to-digital converter |
| AM | Amplitude modulator |
| BER | Bit error ratio |
| BLR | Bit loss ratio |
| DFB | Distributed-feedback |
| DSA | Digital Signature Algorithm |
| ECC | Elliptic-curve cryptography |
| EDFA | Erbium-doped fiber amplifier |
| FBG | Fiber Bragg grating |
| FPGA | Field-programmable gate array |
| LDPC | Low-density parity-check |
| OTDR | Optical time-domain reflectometry |
| PM | Phase modulator |
| QCKD | Quantum-protected Control-based Key Distribution |
| QRNG | Quantum random number generator |
| RSG | Random signal generator |
| VOA | Variable optical attenuator |
References
- Rivest, R.L.; Shamir, A.; Adleman, L. A method for obtaining digital signatures and public-key cryptosystems. Commun. ACM 1978, 21, 120–126. [Google Scholar] [CrossRef]
- Koblitz, N. Elliptic curve cryptosystems. Mathematics of Computation 1987, 48, 203–209. [Google Scholar]
- Kravitz, D.W. Digital Signature Algorithm. US Patent No. US5231668A 1993. [Google Scholar]
- Shor, P. Algorithms for quantum computation: discrete logarithms and factoring. In Proceedings of the Proceedings 35th Annual Symposium on Foundations of Computer Science; 1994; pp. 124–134. [Google Scholar] [CrossRef]
- Bennett, C.H.; Brassard, G. Quantum cryptography: Public key distribution and coin tossing. Theoretical Computer Science 2014, 560, 7–11. [Google Scholar] [CrossRef]
- Ekert, A.K. Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 1991, 67, 661–663. [Google Scholar]
- Bennett, C.H. Quantum cryptography using any two nonorthogonal states. Phys. Rev. Lett. 1992, 68, 3121–3124. [Google Scholar] [CrossRef]
- Bruß, D. Optimal Eavesdropping in Quantum Cryptography with Six States. Phys. Rev. Lett. 1998, 81, 3018–3021. [Google Scholar] [CrossRef]
- Pirandola, S.; Andersen, U.L.; Banchi, L.; Berta, M.; Bunandar, D.; Colbeck, R.; Englund, D.; Gehring, T.; Lupo, C.; Ottaviani, C.; et al. Advances in quantum cryptography. Advances in Optics and Photonics 2020, 12, 1012. [Google Scholar] [CrossRef]
- Gu, J.; Cao, X.Y.; Fu, Y.; He, Z.W.; Yin, Z.J.; Yin, H.L.; Chen, Z.B. Experimental measurement-device-independent type quantum key distribution with flawed and correlated sources. Science Bulletin 2022, 67, 2167–2175. [Google Scholar] [CrossRef]
- Xie, Y.M.; Lu, Y.S.; Weng, C.X.; Cao, X.Y.; Jia, Z.Y.; Bao, Y.; Wang, Y.; Fu, Y.; Yin, H.L.; Chen, Z.B. Breaking the Rate-Loss Bound of Quantum Key Distribution with Asynchronous Two-Photon Interference. PRX Quantum 2022, 3, 020315. [Google Scholar] [CrossRef]
- Hu, J.Y.; Yu, B.; Jing, M.Y.; Xiao, L.T.; Jia, S.T.; Qin, G.Q.; Long, G.L. Experimental quantum secure direct communication with single photons. Light Sci. Appl. 2016, 5, e16144. [Google Scholar] [CrossRef] [PubMed]
- Lucamarini, M.; Yuan, Z.L.; Dynes, J.F.; Shields, A.J.; All, A. Overcoming the rate–distance limit of quantum key distribution without quantum repeaters. Nature 2018, 557, 400–403. [Google Scholar] [CrossRef]
- Qi, Z.; Li, Y.; Huang, Y.; Feng, J.; Zheng, Y.; Chen, X. A 15-user quantum secure direct communication network. Light Sci. Appl. 2021, 10, 183. [Google Scholar] [CrossRef] [PubMed]
- Ma, X.; Qi, B.; Zhao, Y.; Lo, H.K. Practical decoy state for quantum key distribution. Physical Review A—Atomic, Molecular, and Optical Physics 2005, 72, 012326. [Google Scholar] [CrossRef]
- Scarani, V.; Acin, A.; Ribordy, G.; Gisin, N. Quantum Cryptography Protocols Robust against Photon Number Splitting Attacks for Weak Laser Pulse Implementations. Physical review letters 2004, 92, 057901. [Google Scholar] [CrossRef]
- Zhang, H.; Sun, Z.; Qi, R.; Yin, L.; Long, G.L.; Lu, J. Realization of quantum secure direct communication over 100 km fiber with time-bin and phase quantum states. Light Sci. Appl. 2022, 11, 83. [Google Scholar] [CrossRef]
- Long, G.L.; Pan, D.; Sheng, Y.B.; Xue, Q.; Lu, J.; Hanzo, L. An Evolutionary Pathway for the Quantum Internet Relying on Secure Classical Repeaters. IEEE Network 2022, 36, 82–88. [Google Scholar] [CrossRef]
- Kirsanov, N.S.; Pastushenko, V.A.; Kodukhov, A.D.; Yarovikov, M.V.; Sagingalieva, A.B.; Kronberg, D.A.; Pflitsch, M.; Vinokur, V.M. Forty thousand kilometers under quantum protection. Scientific Reports 2023, 13, 8756. [Google Scholar] [CrossRef]
- Smirnov, A.; Yarovikov, M.; Zhdanova, E.; Gutor, A.; Vyatkin, M. An Optical-Fiber-Based Key for Remote Authentication of Users and Optical Fiber Lines. Sensors 2023, 23, 6390. [Google Scholar] [CrossRef]
- Kodukhov, A.D.; Pastushenko, V.A.; Kirsanov, N.S.; Kronberg, D.A.; Pflitsch, M.; Vinokur, V.M. Boosting Quantum Key Distribution via the End-to-End Loss Control. Cryptography 2023, 7, 38. [Google Scholar] [CrossRef]
- Kirsanov, N.; Pastushenko, V.; Kodukhov, A.; Aliev, A.; Yarovikov, M.; Strizhak, D.; Zarubin, I.; Smirnov, A.; Pflitsch, M.; Vinokur, V. Loss Control-Based Key Distribution under Quantum Protection. Entropy 2024, 26. [Google Scholar] [CrossRef]
- Maurer, U. Secret key agreement by public discussion from common information. IEEE Transactions on Information Theory 1993, 39, 733–742. [Google Scholar] [CrossRef]
- Bennett, C.H.; Brassard, G.; Robert, J.M. Privacy Amplification by Public Discussion. SIAM Journal on Computing 1988, 17, 210–229. [Google Scholar] [CrossRef]
- McKay, K.G. Avalanche Breakdown in Silicon. Phys. Rev. 1954, 94, 877–884. [Google Scholar] [CrossRef]
- Lampert, B.; Wahby, R.S.; Leonard, S.; Levis, P.; All, A. Robust, low-cost, auditable random number generation for embedded system security. In Proceedings of the Proceedings of the 14th ACM Conference on Embedded Network Sensor Systems CD-ROM. [CrossRef]
- Mølmer, K. Optical coherence: A convenient fiction. Phys. Rev. A 1997, 55, 3195–3203. [Google Scholar] [CrossRef]
- Lütkenhaus, N. Security against individual attacks for realistic quantum key distribution. Phys. Rev. A 2000, 61, 052304. [Google Scholar] [CrossRef]
- van Enk, S.J.; Fuchs, C.A. Quantum State of an Ideal Propagating Laser Field. Phys. Rev. Lett. 2001, 88, 027902. [Google Scholar] [CrossRef]
- Zhao, Y.; Qi, B.; Lo, H.K. Experimental quantum key distribution with active phase randomization. Applied Physics Letters 2007, 90, 044106. [Google Scholar] [CrossRef]
- Preskill, J.; Lo, H. Phase randomization improves the security of quantum key distribution. arXiv preprint quant-ph/0504209.
- Sun, S.; He, M.; Xu, M.; Gao, S.; Chen, Z.; Zhang, X.; Ruan, Z.; Wu, X.; Zhou, L.; Liu, L.; et al. Bias-drift-free Mach–Zehnder modulators based on a heterogeneous silicon and lithium niobate platform. Photon. Res. 2020, 8, 1958–1963. [Google Scholar] [CrossRef]
- Hill, K.O.; Fujii, Y.; Johnson, D.C.; Kawasaki, B.S.; All, A. Photosensitivity in optical fiber waveguides: Application to reflection filter fabrication. Applied Physics Letters 1978, 32, 647–649. [Google Scholar] [CrossRef]
- Smirnov, A.; Yarovikov, M.; Zhdanova, E.; Gutor, A.; Vyatkin, M. An optical-fiber-based key for remote authentication of users and optical fiber lines. Sensors 2023, 23, 6390. [Google Scholar] [CrossRef] [PubMed]
- Devetak, I.; Winter, A. Distillation of secret key and entanglement from quantum states. Proceedings of the Royal Society A: Mathematical, Physical and engineering sciences 2005, 461, 207–235. [Google Scholar]
- Holevo, A.S. Bounds for the quantity of information transmitted by a quantum communication channel. Problems Inform. Transmission 1973, 9, 177–183. [Google Scholar]
| Statistical Test | P-value | Proportion | Result |
|---|---|---|---|
| Frequency | 0.64 | 1.0 | SUCCESS |
| Block Frequency | 0.83 | 1.0 | SUCCESS |
| Cumulative Sums | 0.16 | 1.0 | SUCCESS |
| Runs | 0.44 | 1.0 | SUCCESS |
| Longest Run | 0.28 | 0.9 | SUCCESS |
| Rank | 0.83 | 1.0 | SUCCESS |
| FFT | 0.44 | 1.0 | SUCCESS |
| Non Overlapping Template | 0.06 ÷ 0.98 | 0.9 ÷ 1.0 | SUCCESS |
| Overlapping Template | 0.28 | 0.9 | SUCCESS |
| Universal | 0.16 | 1.0 | SUCCESS |
| Approximate Entropy | 0.16 | 1.0 | SUCCESS |
| Random Excursions | 0.14 ÷ 0.99 | 1.0 | SUCCESS |
| Random Excursions Variant | 0.06 ÷ 0.98 | 1.0 | SUCCESS |
| Serial | 0.83 ÷ 0.96 | 1.0 | SUCCESS |
| Linear Complexity | 0.96 | 1.0 | SUCCESS |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




