Submitted:
11 October 2024
Posted:
16 October 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
- (1). A short symmetric key is set, and it is mathematically extended.
- (2). Private randomization techniques is useful.
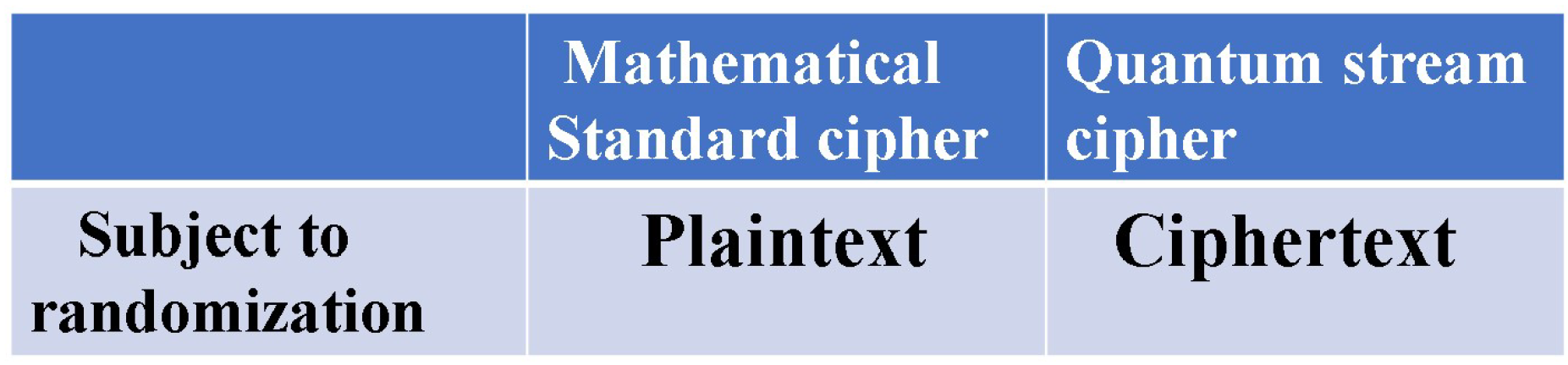
- (3). Randomization for plaintext is a candidate of private randomization.
- (1). A short symmetric key is set and it is mathematically extended.
- (2). Randomization techniques for ciphertext are adopted.).
- (3). The randomization is implemented as private randomization.
2. Review of Shannon-Massey Theory of Cryptography
2.1. Historical View
2.2. Conventional Definition of Information Theoretics Security for Symmetric Key Cipher
2.2.1. Non-Randam Cipher
2.2.2. Shannon Random Cipher
2.3. Unicity Distance Theory
2.3.1. Summary
2.3.2. Shannon Random Cipher and Its Unicity Distance
2.4. Known Plaintext Attack against Conventional Cipher
2.4.1. Non-Random Cipher
2.4.2. Random Cipher
3. Conceptual Generalized Random Cipher and Its Fundamental Properties
3.1. Conceptual Mechanism
3.2. Generalized Unicity Distance
3.2.1. Ciphertext Only Attack
3.2.2. Known Plaintext Attack
3.2.3. Secret Key Leakage Attack in COA
4. Concrete Evaluation Method of Generalized Shannon Random Cipher
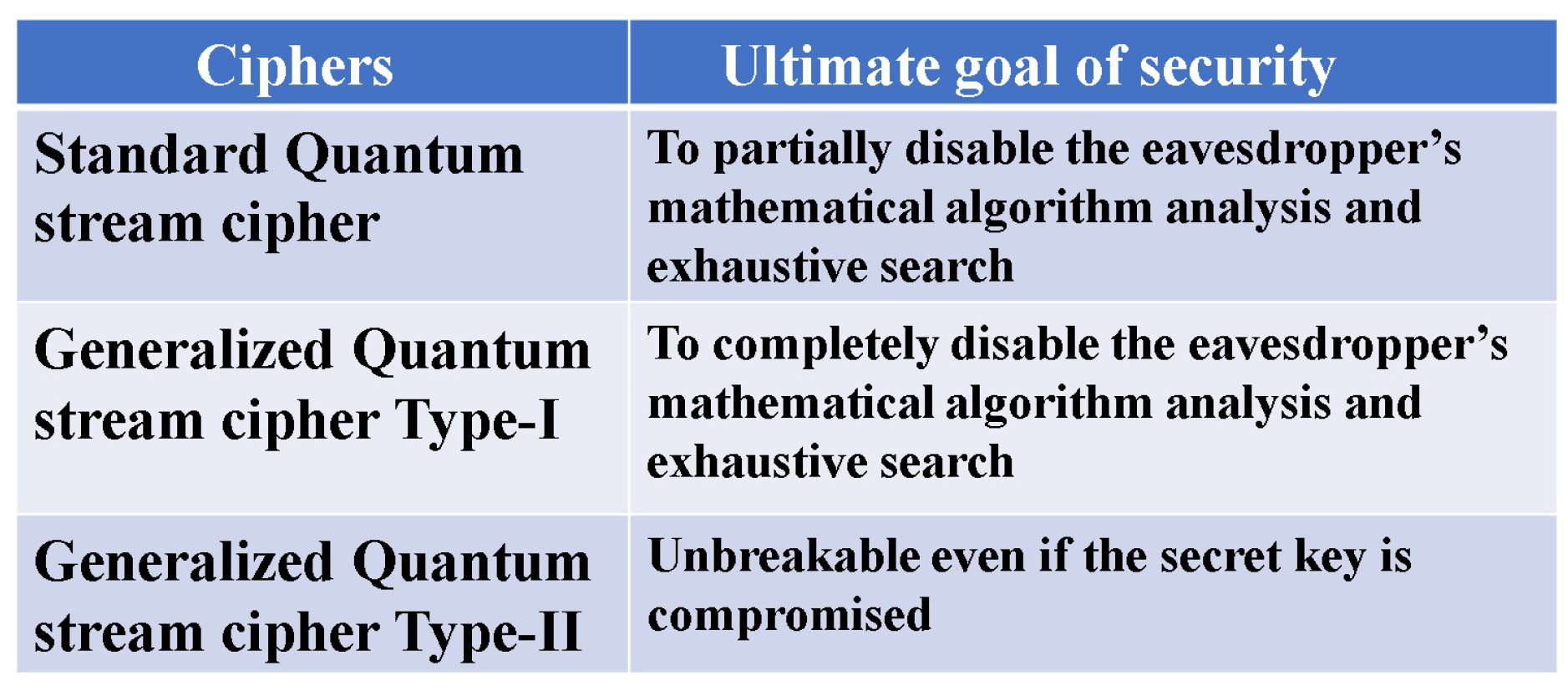
5. Structure of Standard Quantum Stream Cipher
6. Quantum Communication Theory for Cryptanalysis
6.1. Fundamental Formulae
6.2. Advantage Creation by Differenciation of Quantum Detection Performance by Secret Key
6.3. Physical Processes for Cryptanalysis against PRNG
6.3.1. Individual Quantum Measurement-Collective Procedure
6.3.2. Collective Quantum Measurement-Collective Procedure
7. Cryptological Attack for Quantum Stream Cipher and Its Performance
7.1. The Main Attack Scheme
7.1.1. Legitimate Receiver Simulation Attack
7.1.2. Fast Correlation Attack
7.1.3. Secret Key Leakage Attack
7.2. Role of Additional Randomization Techinique
8. Randomizations Towards Generalized Quantum Stream Cipher
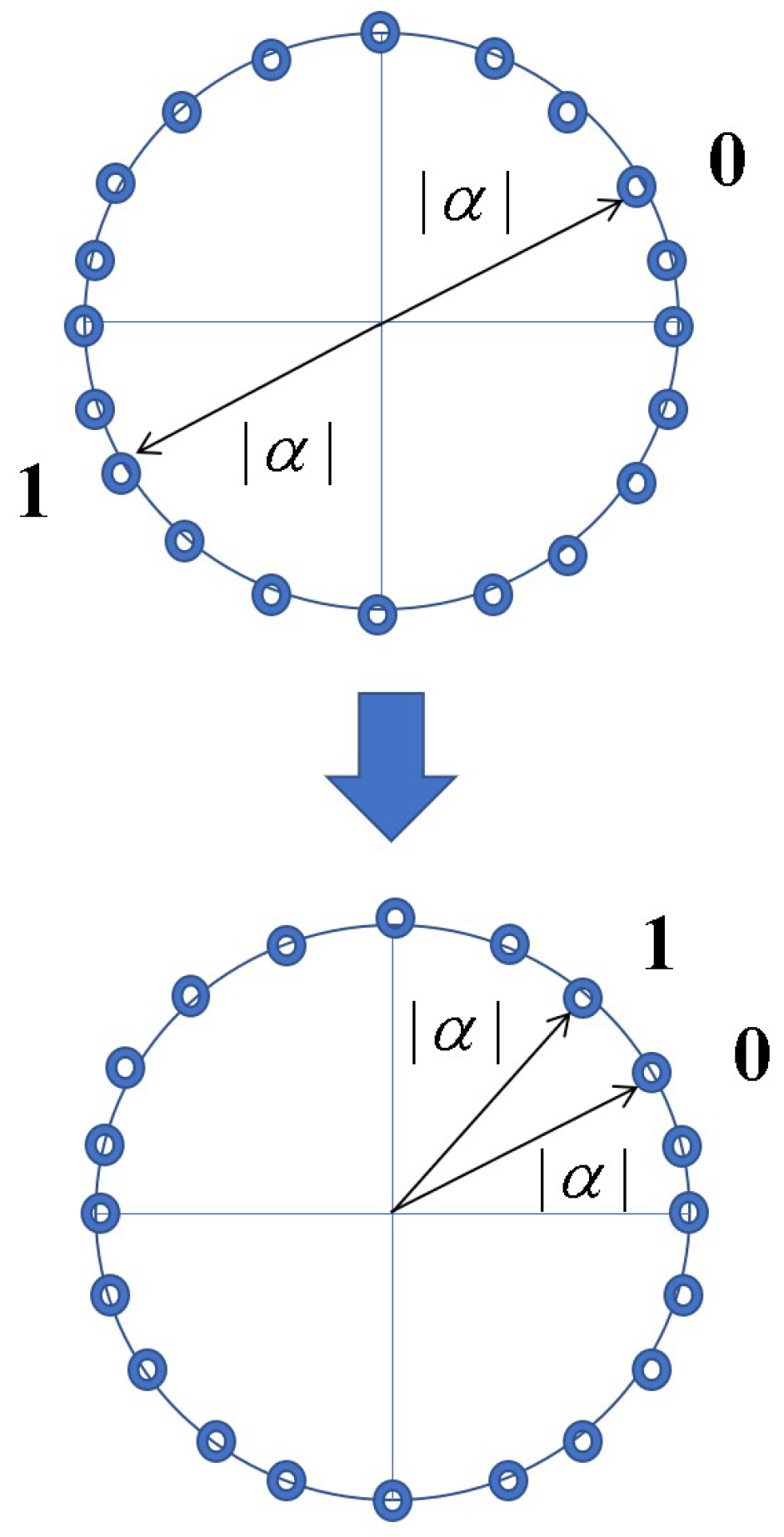
8.1. Overlap Selection Keying (OSK)
8.2. Deliberate Signal Randomization (DSR)
8.3. Quantum Noise-Diffusion Mapping
8.4. Phase Masking by Symplectic Matrix
9. Generalized Quantum Stream Cipher of Type-I and Its Performance
9.1. Communication Scheme
9.2. Unicity Distance of Known Plaintext Attack
9.3. Coherent Pulse Position Modulation Method
10. Generalized Quantum Stream Cipher of Type-Ii and Its Performance
10.1. Communication Scheme
10.2. Secret Key Leakage Attack
11. Generalized Quantum Stream Cipher of Type-Iii and Its Performance
11.1. Communication Scheme 1
11.2. Communication Scheme 2
11.2.1. Secret Capacity
11.2.2. Coding Problem
12. Conclusion
References
- Shannon, E. Communication theory of secrecy systems. BSTJ 1949, 26, 656. [Google Scholar] [CrossRef]
- Massey, J. Contemporary Cryptology-An Introduction-. Edited by G.J.Simmons, IEEE Press, 1992.
- Borbosa, G.A.; Corndolf, E.; Kumar, P.; Yuen,H.P. Secure communication using coherent state. Proceedings of QCMC-2002, Edited by Shapiro.J.H, and Hirota.O, Rinton Press, 2002.
- Sohma, M.; Hirota, O. Quantum stream cipher based on Holevo-Yuen theory. Entropy 2022, 24, 667. [Google Scholar] [CrossRef] [PubMed]
- Welsh, D. Codes and Cryptography. Oxford U Press, 1988. [Google Scholar]
- Blahut, R.E. Cryptography and Secure Communication. Cambridge University Press, 2014. [Google Scholar]
- Imai, H. Theory of information, codes, and Cryptography. Lecture series of IEICE of Japan, Corona Pablising Co. LTD, 2004. [Google Scholar]
- Tsuchiya, H. A study of attack against Vernum cipher. Report of graduation research at Tamagawa University, 2002. [Google Scholar]
- Hirota, O.; Sohma, M.; Kawanishi, K. Quantum noise randamized stream cipher:Y-00. Jpn. J. Opt. 2010, 39, 17. [Google Scholar]
- Sohma, M.; Hirota, O. Generalized unicity distance and its application to Y-00 quantum stream cipher, IEICE of Japan, Technical Report,2023 March, IT2022-128.
- Siegenthaler, T. Decrypting a class of stream ciphers using ciphertext only. IEEE Trans. Comput., 1985, C-34, 81.
- Chepyzhov, V.V.; Johansson, T.; Smeets, B. A simple algorithm for fast correlation attacks on stream cipher. FSE 2000, LNCS 1978, 2001, 2001, p181. [Google Scholar]
- Nair, R.; Yuen, H.P.; Corndolf, E.; Kumar, P. Quantum noise randomized ciphers. Phys. Rev. A 2006, 74, 052309. [Google Scholar] [CrossRef]
- Yuen,H.P. Key Generation: Foundations and a New Quantum Approach. IEEE. J. Selected topics in Quantum Electronics, 209, 15, 1630–1645. Yuen, H.P. KCQ : Keyed communication in quantum noise. arXiv 2003, arXiv:0311061.
- Helstrom, C.W. Quantum Detection and Estimation Theory", Academic Press, 1976.
- Holevo, A.S. Statistical decision theory for quantum systems. J. Multivar. Anal. 1973, 3, 337. [Google Scholar] [CrossRef]
- Yuen, H.P.; Kennedy, R.S.; Lax, M. Optimum testing of multiple hypotheses in quantum detection theory. IEEE Trans. Inf. Theory 1975, 21, 125–134. [Google Scholar] [CrossRef]
- Holevo, A.S. Quantum systems, channels, information. De Gruyter 2012. [Google Scholar]
- Hirota, O.; Ikehara, S. Minimax strategy in the quantum detection theory and its application to optical communications. Trans. IEICE Jpn. 1982, 65E, 627. [Google Scholar]
- Middleton, D. An introduction to statistical communication theory. McGRAW-HILL, 1960. [Google Scholar]
- Ban, M.; Kurokawa, K.; Momose, R.; Hirota, O. Quantum measurements for discrimination among symmetric quantum states and parameter estimation. International Theoretical Physics, 1997, 36, 1269. [Google Scholar] [CrossRef]
- Osaki, M.; Usuda, T.S.; Hirota, O. Group covariant detection for a three phase shift keyed signal. Physics Letters A, 1998, 245, 189–196. [Google Scholar] [CrossRef]
- Kato, K.; Osaki, M.; Hirota, O. Quantum detection and mutual information for QAM and PSK signals. IEEE Transactions on communications, 1999, 47, 248–254. [Google Scholar] [CrossRef]
- Osaki, M.; Ban, M.; Hirota, O. Derivation and physical interpretation of the optimum detection operators For coherent state signals. Phys. Rev. A 1996, 54, 1691. [Google Scholar] [CrossRef] [PubMed]
- Kato, K.; Hirota, O. Square Root Measurement for Quantum Symmetric Mixed State Signals. IEEE, Trans. on Information Theory 2003, 49, 3312–3317. [Google Scholar] [CrossRef]
- Sohma, M.; Hirota, O.; Kato, K. Japan Patent Number 4451085, 2003,June.
- Hirota, O.; Kurosawa, K. Immunity against correlation attack on quantum stream cipher by Yuen 2000 protocol. Quantum Inf. Process. 2007, 6, 81–91. [Google Scholar] [CrossRef]
- Hirota, O. Practical security analysis of quantum stream cipher by Yuen protocol. Phys. Rev. A 2007, 76, 032307. [Google Scholar] [CrossRef]
- Sohma, M.; Hirota, O. Coherent Pulse Position Modulation Quantum Cipher Supported by Secret Key. Bulletin of Quantum ICT Research Institute, Tamagawa University 2011, 1, 15–19. [Google Scholar]
- Sohma, M.; Hirota, O. Masking property of quantum random cipher with phase mask encryption. Quantum Info. Process. 2014, 13, 2221–2240. [Google Scholar] [CrossRef]
- Osaki, M.; Ban, M.; Hirota, O. The maximum mutual information without coding for binary quantum state signals. Journal of Modern Optics 1998, 45, 269–282. [Google Scholar] [CrossRef]
- Fuchs, C.A.; Peres, A. Quantum-state disturbance versus information gain: Uncertainty relations for quantum information. Phys. Rev. A 1996, 53, 2038. [Google Scholar] [CrossRef]
- Yuen, H.P.; Lax, M. Multiple-parameter quantum estimation and measurement of non-self adjoint observables. IEEE Trans. on Inform Theory, -19.
- Usuda, T.; Takumi, i. Group covariant signals in quantum information theory. Proc. of Quantum Commun. and Measurement 2, Ed by Kumar.P,D’Ariano.Hirota.O, Prenum Press (Kluwer/Plenum), 2000.
- Nakahira, K. Minimum error probability of asymmetric 3PSK coherent state signal. Private communication 2015. [Google Scholar]
- Hirota, O. Towards Quantum Enigma Cipher -A protocol for G bit/sec encryption based on discrimination property of non-orthogonal quantum states. Bulletin of Quantum ICT Research Institute,Tamagawa University 2015, 5–10.
- Holevo, A.S.; Sohma, M.; Hirota, O. Capacity of quantum Gaussian channels. Phys. Rev. 1820; A-59, 1820. [Google Scholar]
- Hirota, O.; Iwakoshi, T.; Sohma, M.; Futami, F. Quantum stream cipher beyond the Shannon limit of symmetric cipher and the possibility of experimental demonstration. Proceedings of SPIE on Quantum communication and quantum imaging 2010, 7815. [Google Scholar]
- Hirota, O. Importance and Applications of Infinite Dimensional Non-Orthogonal Quantum State. J Laser Opt Photonics 2016, 3. [Google Scholar] [CrossRef]
- Sasaki, M.; Kato, K.; Izutsu, M.; Hirota, O. Quantum channels showing superadditivity in classical capacity. Phys. Rev. A 1998, 58, 146–158. [Google Scholar] [CrossRef]
- Hirota, O. A foundation of quantum channels with super additiveness for Shannon information. Applicable Algebra in Eng. Communication and Computing 2000, 10, 401–423. [Google Scholar] [CrossRef]
- Borbosa, G.A.; Corndorf, E.; Kumar, P.; Yuen, H.P. Secure communication using mesoscopic coherent states. Phys. Rev. Lett. 2003, 90, 227901. [Google Scholar] [CrossRef]
- Kanter, G.S.; Reillly, D.; Smith, N. Practical physical layer encryption: The marriage of optical noise with traditional cryptography. IEEE Commun. Mag. 2009, 47, 74–81. [Google Scholar] [CrossRef]
- Hirota, O.; Sohma, M.; Fuse, M.; Kato, K. Quantum stream cipher by Yuen 2000 protocol: Design and experiment by intensity modulation scheme. Phys. Rev. A 2005, 72, 022335. [Google Scholar] [CrossRef]
- Nakazawa, M.; Yosida, M.; Hirooka, T.; Kasai, K. QAM quantum stream cipher using digital coherent optical transmission", Opt. Express 2014, 22, 4098. [Google Scholar] [CrossRef]
- Futami, F.; Guan, K.; Gripp, J.; Kato, K.; Tanizawa, K.; Chandrasekhar, S.; Winzer, P.J. Y-00 quantum stream cipher overlay in a coherent 256-Gbit/s polarization multiplexed 16-QAM WDM. Opt. Express 2017, 25, 33338. [Google Scholar] [CrossRef]
- Tanizawa, K.; Futami, F. Ultra-long-haul digital coherent PSK Y-00 quantum stream cipher transmission system. Opt. Express 2021, 29, 10451–10464. [Google Scholar] [CrossRef] [PubMed]
- Yu, Q.; Wang, Y.; Li, D.; Song, H.; Fu, Y.; Jiang, X.; Huang, L.; Cheng, M.; Liu, D.; Deng, L. Secure 100 Gb/s IMDD Transmission Over 100 km SSMF Enabled by Quantum Noise Stream Cipher and Sparse RLS-Volterra Equalizer. IEEE Access 2020, 8, 63585. [Google Scholar] [CrossRef]
- Luo, H.; Zhang, Z.; Dai, L.; Zhong, Y.Q.; Deng, L.; Liu, D.; Dai, X.; Gao, X.; Cheng, M. Device-compatible ultra-high-order quantum noise stream cipher based on delta-sigma modulator and optical chaos. Nature, communication engineering 2024, 3, 1–10. [Google Scholar] [CrossRef]
- Futami, F.; Tanizawa, K.; Kato, K. Transmission of Y-00 Quantum Noise Stream Cipher with Quantum Deliberate Signal Randomization over Field-Installed Fiber. Bulletin of Quantum ICT Research Institute,Tamagawa University 2023, 23–25. https://www.tamagawa.jp/research/quantum/bulletin/pdf/Tamagawa.Vol.12-3.pdf.
- Shapiro, J.H.; Boroson, D.N.; Dixon, P.B.; Green, M.E.; Hamilton, S.A. Quantum low probability of intercept. JOSA-B Optical Physics 2019, 36, B41. [Google Scholar] [CrossRef]
- Guha, S.; Hayden, P.; Krovi, H.L.; Lloyd, S.; Shapiro, J.H. Quantum enigma machines and the locking capacity of a quantum channel. Phys.Rev 2014, X-4011016. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



