Submitted:
03 April 2026
Posted:
07 April 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
- Development of a real-time cyber-physical smart grid testbed integrated with a SCADA monitoring system
- Implementation of protocol-based cyberattack scenarios using SSH
- Integration of Wireshark for packet-level network monitoring and analysis
- Evaluation of system performance using communication metrics and controllability/observability analysis
- Experimental analysis of the interaction between cyberattacks and power system stability
2. Related Works
2.1. Smart Grid Cybersecurity
2.2. SCADA System Vulnerabilities
2.3. Cyberattacks on Smart Grid Communication Networks
2.4. Protocol-Based Attacks and Federated Learning Approaches
2.5. Impact of Cyberattacks on System Stability, Monitoring, and Control
2.6. Research Gap and Contribution of This Work
3. Methodology
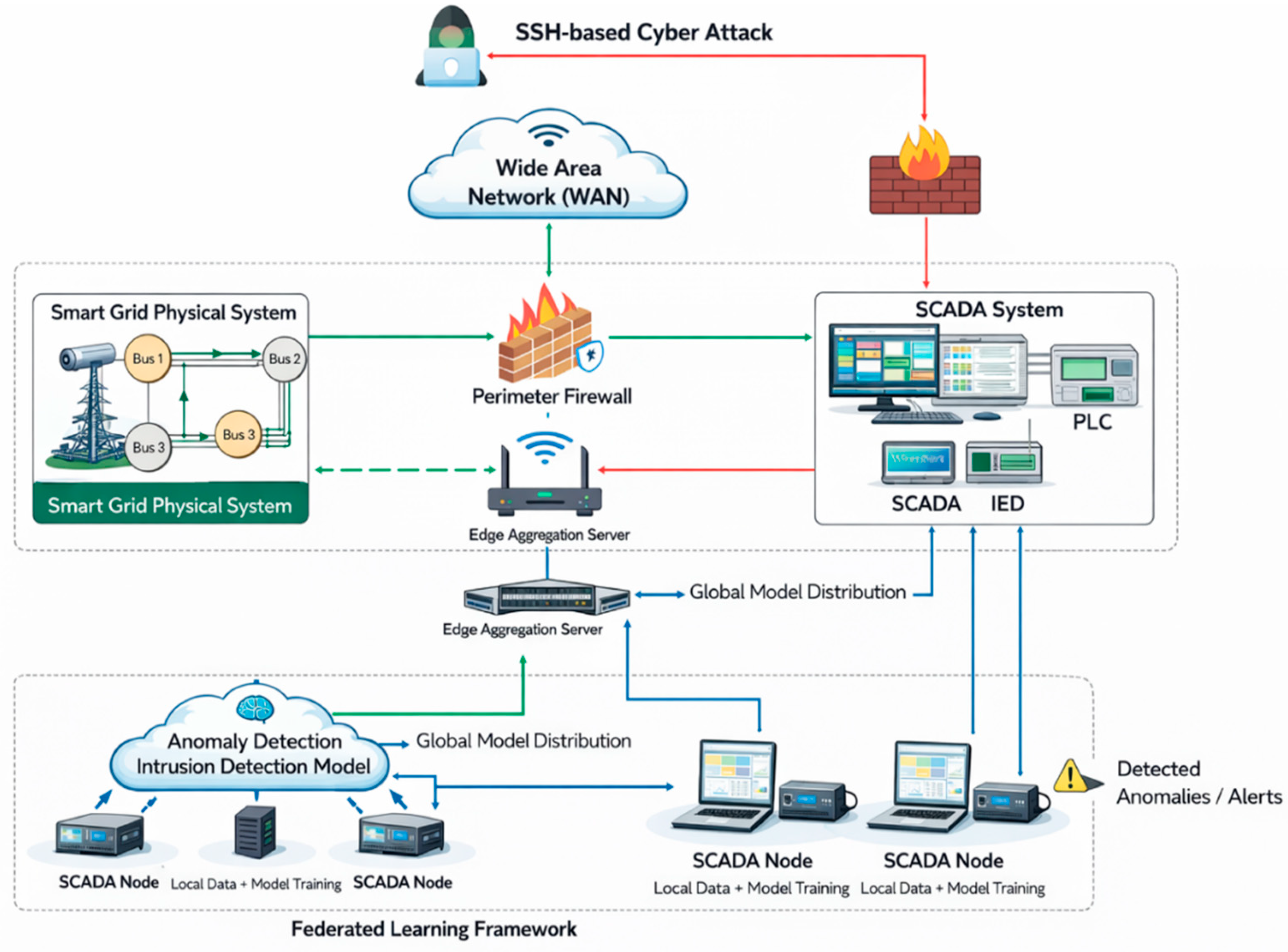
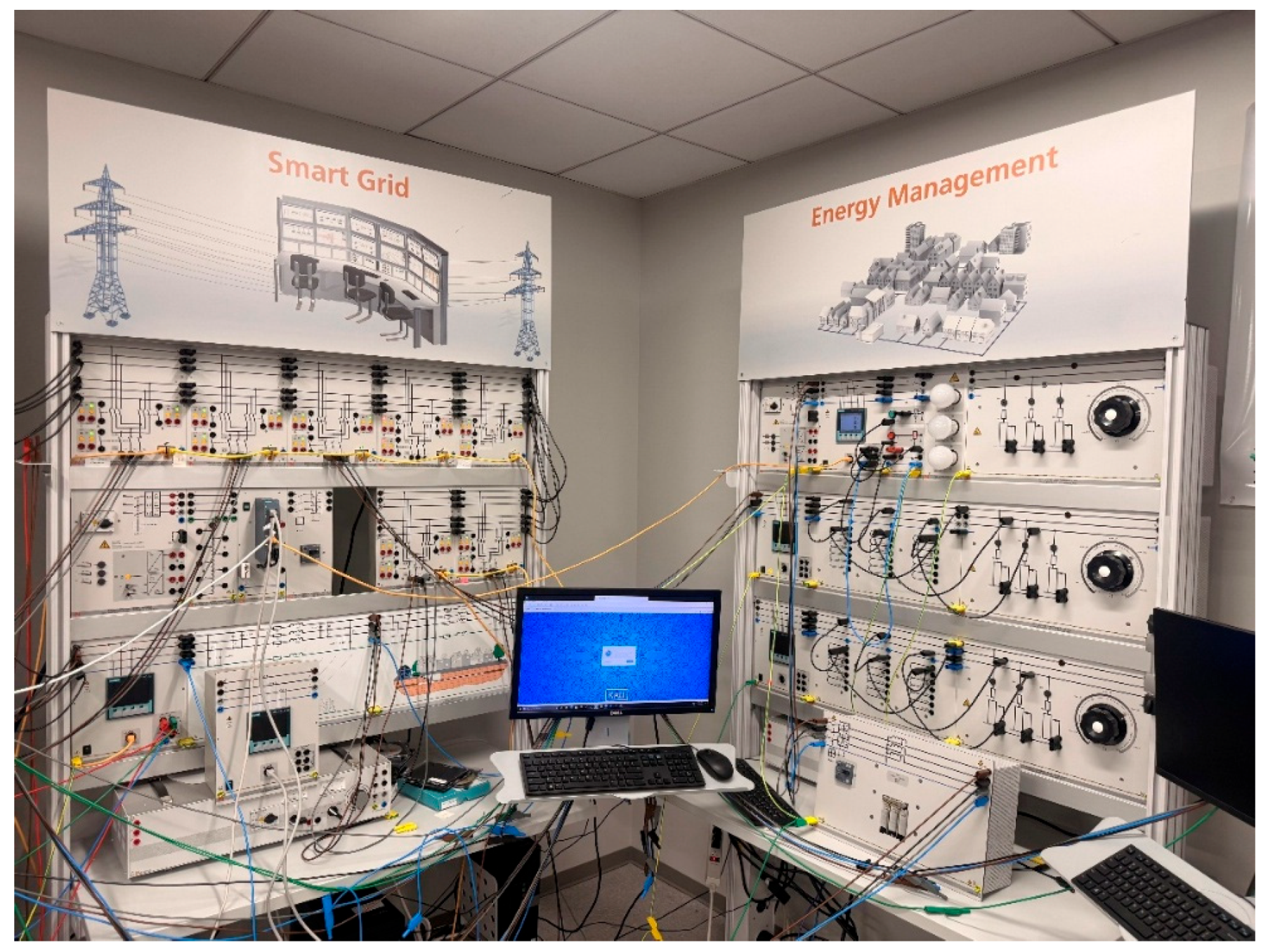
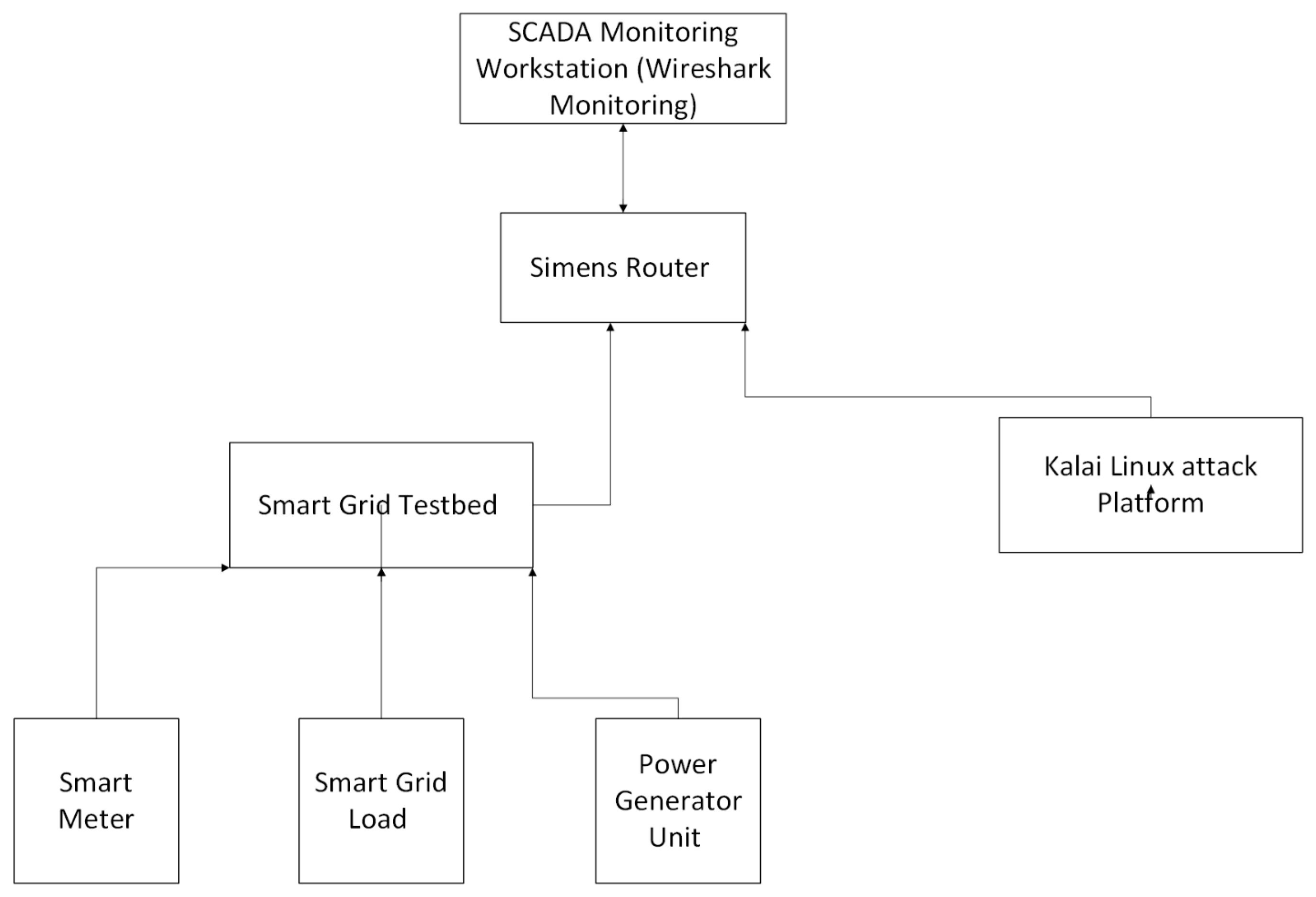
3.1. Smart Grid Cyber-Physical Testbed
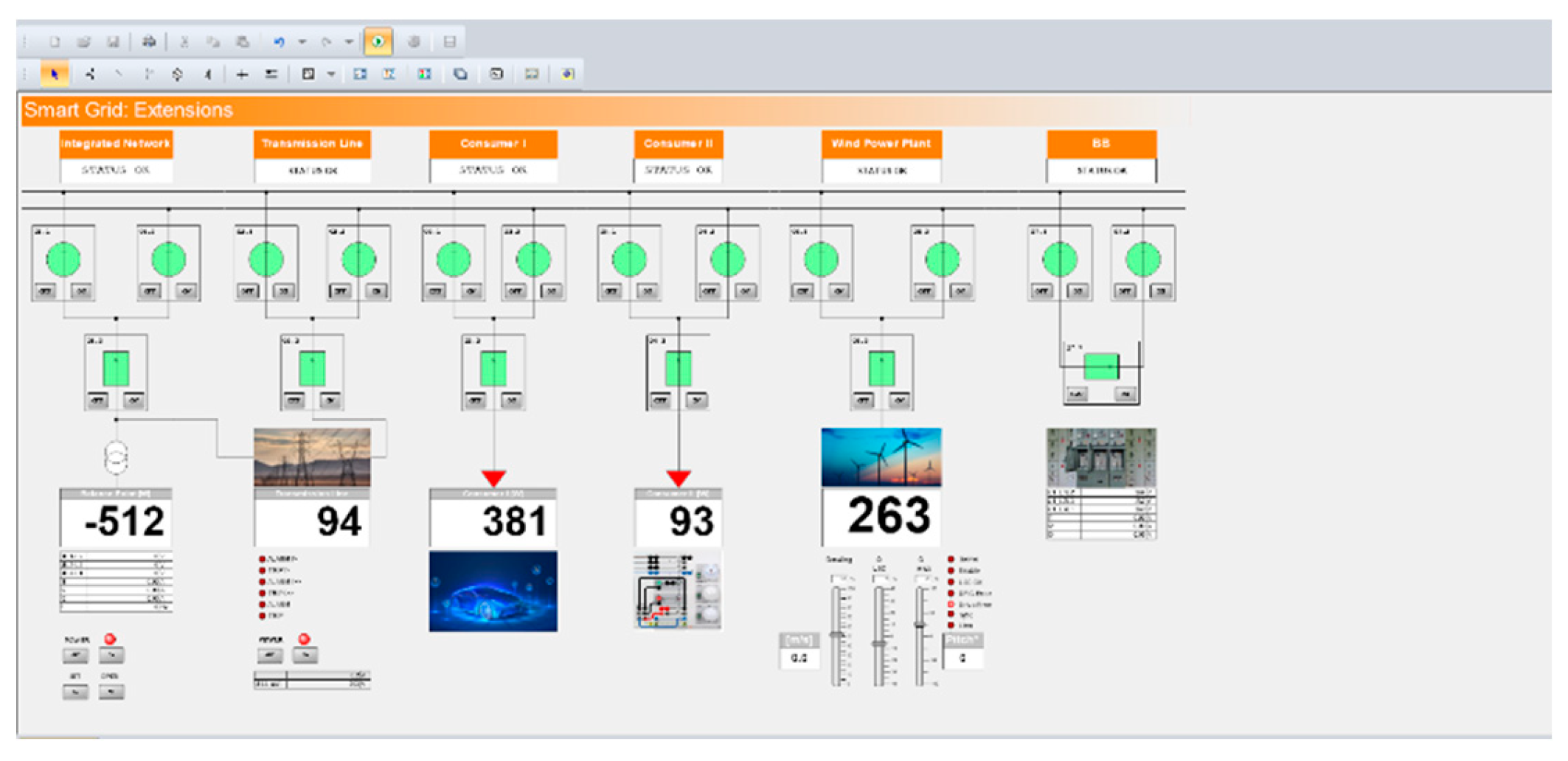
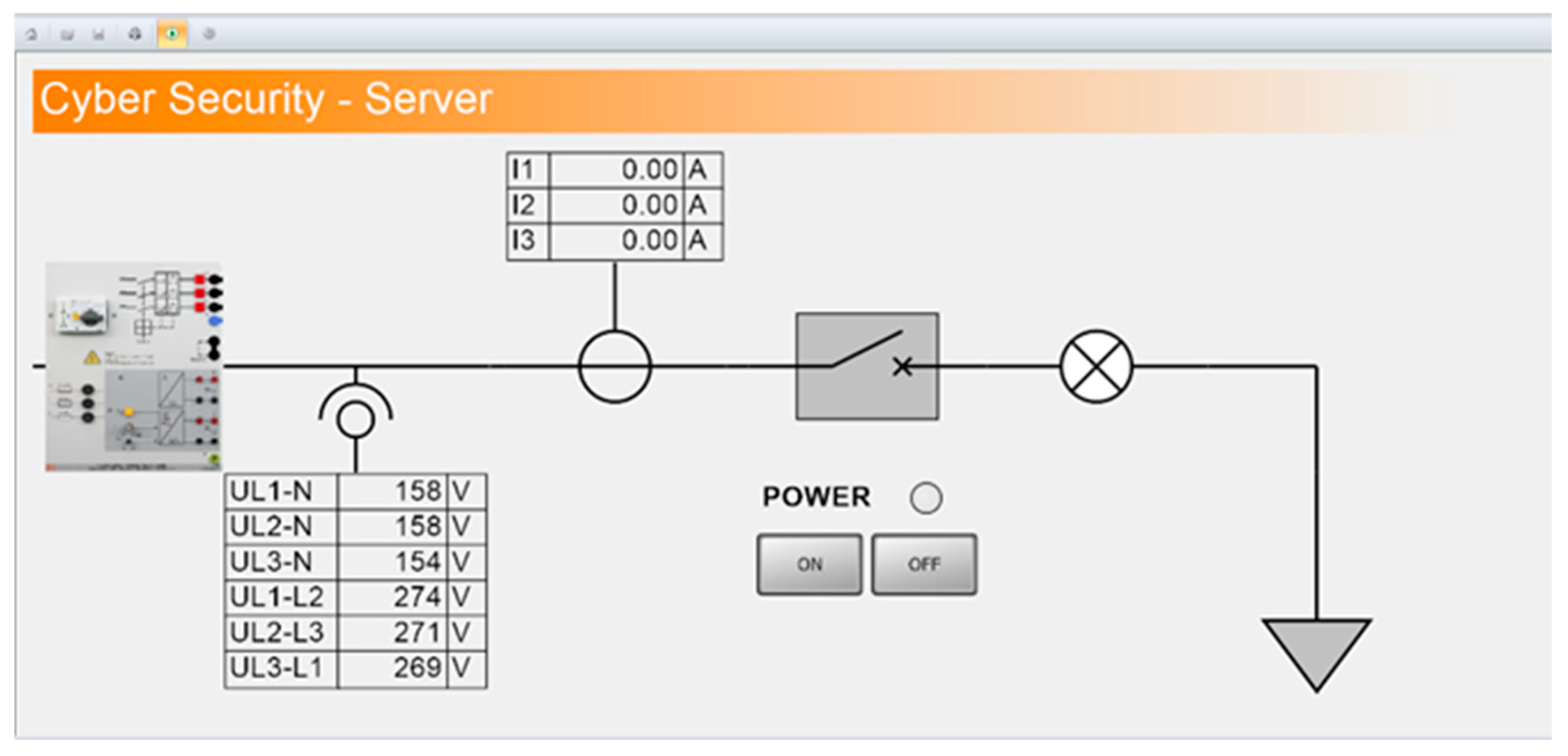
3.2. SCADA Server Monitoring Interface
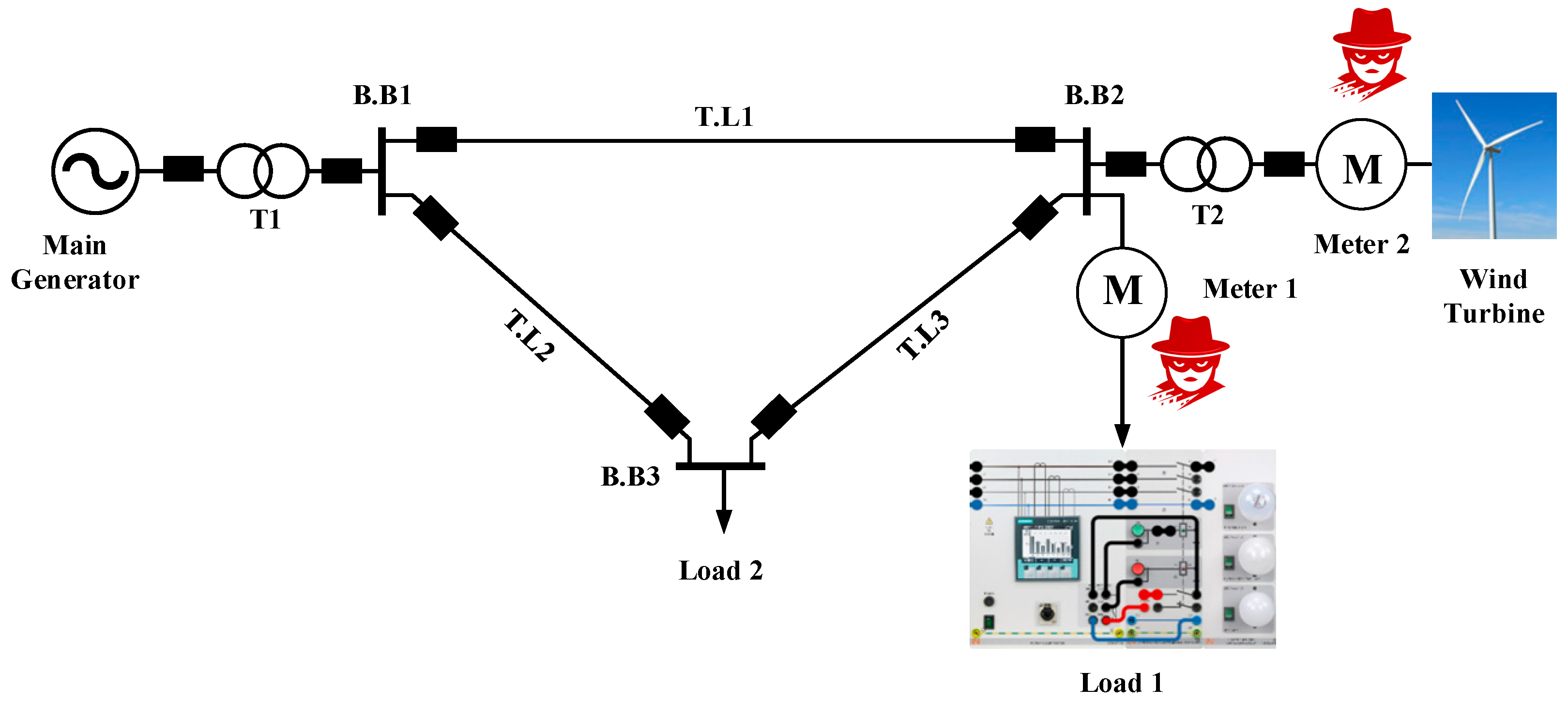
3.3. Proposed Power System
3.4. Physical Smart Grid Laboratory Testbed
3.5. Communication Network and Cyberattack Implementation
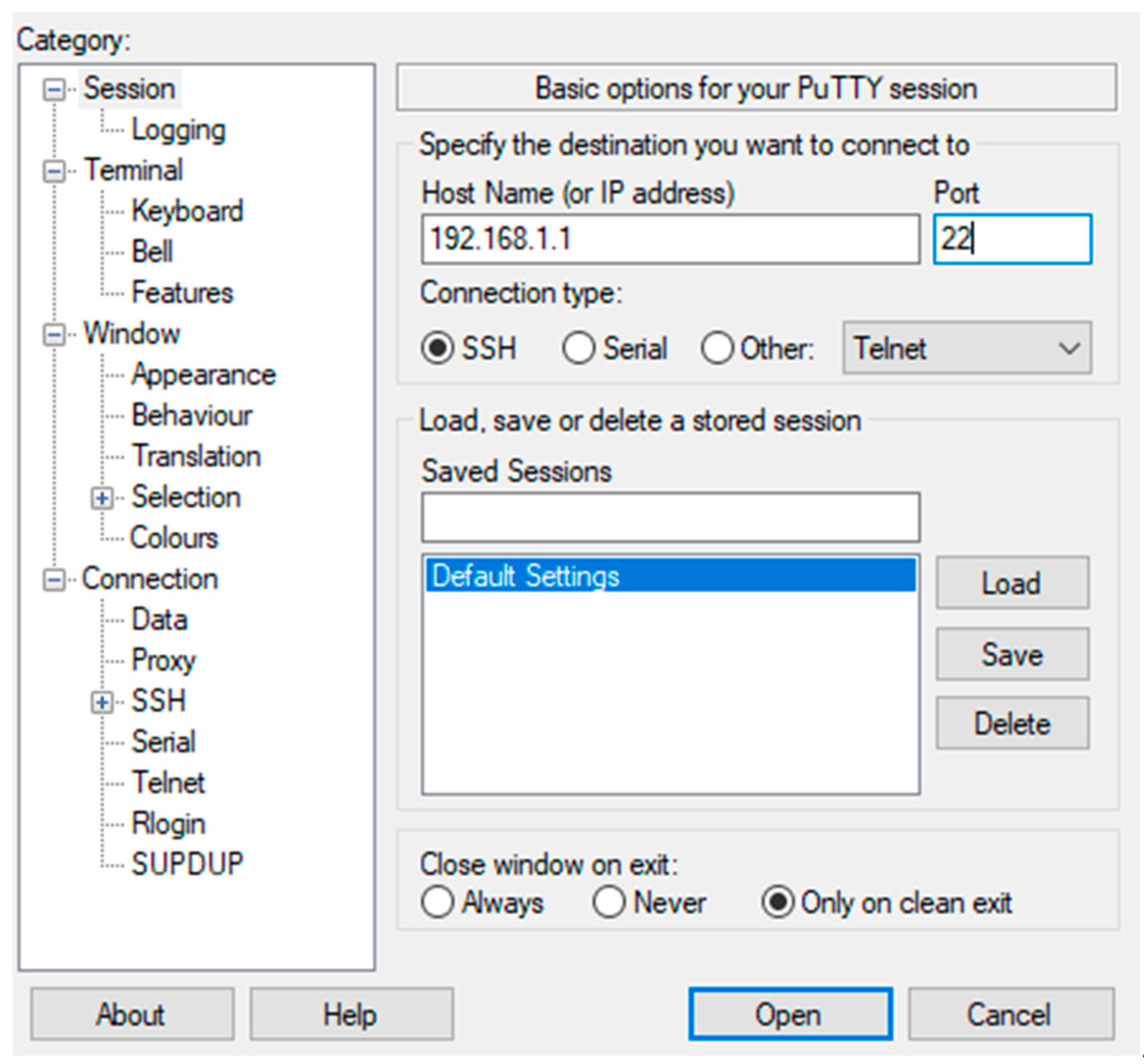
3.6. Cyberattack Implementation
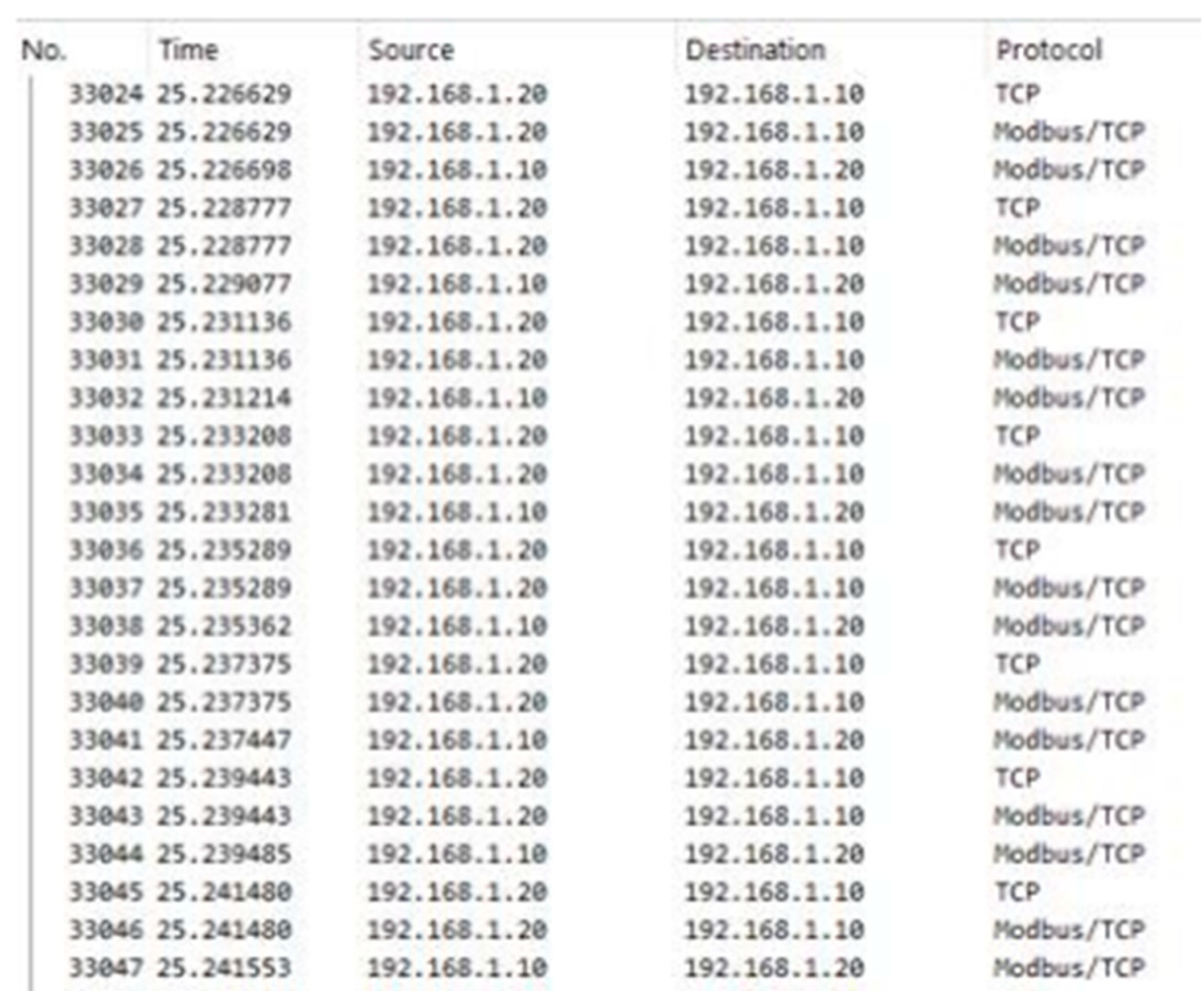
3.7. System Monitoring and Data Collection
3.8. Mathematical Modeling and Controllability/Observability Analysis
3.8.1. Controllability Analysis
3.8.2. Observability Analysis
3.9. Federated Cybersecurity Modeling
4. Experimental Results and Analysis
4.1. Normal System Operation
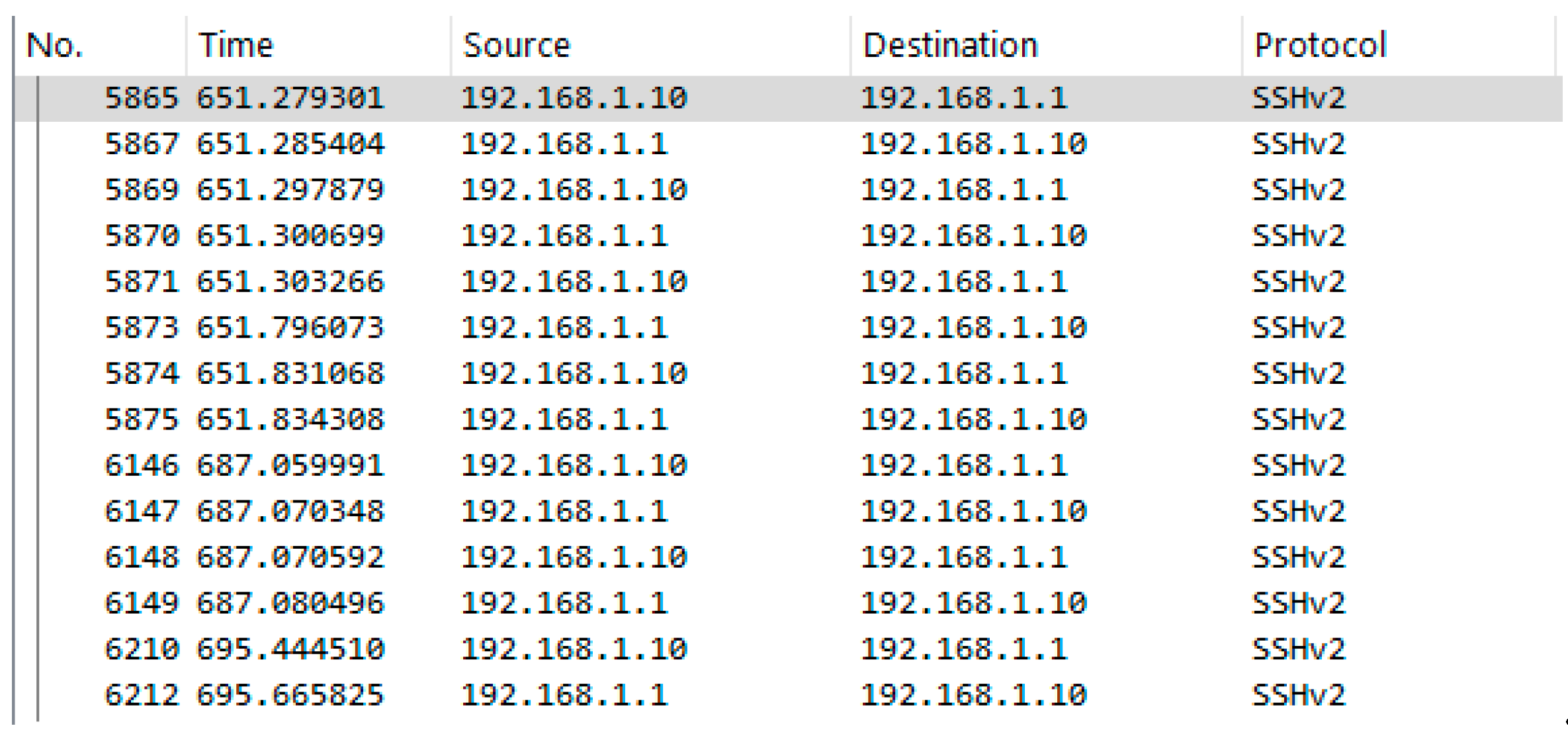
4.2. SSH-Based Attack
4.3. Comparative Performance and Power Flow Analysis
| Parameter | Meter 1 (192.168.1.20) | Meter 2 (192.168.168.31) |
| V_PH(V) | 114 – 114 – 114 | 114 – 114 – 114 |
| V_Line(V) | 198 – 198 – 198 | 198 – 198 – 198 |
| I (A) | 0.19 | 0.34 |
| P (W) | 14 | -14 |
| Q (var) | -1 | -116 |
| S (VA) | 21 | 116 |
| F (Hz) | 60.00 | 60.00 |
| Power Factor | 0.68 | 0.12 |
| Parameter | Meter 1 (192.168.1.20) | Meter 2 (192.168.168.31) |
| V_PH(V) | 108-115-113 | 110-112-113 |
| V_Line(V) | 191-197-194 | 191-197-194 |
| I (A) | 0.19-0.00-0.00-0.19 | 0.34-0.35-0.35-0.00 |
| P (W) | 14 | -14 |
| Q (var) | -1 | -115 |
| S (VA) | 21 | 116 |
| F (Hz) | 59.99 | 59.98 |
| Power Factor | 0.68 | 0.12 |
| Parameter | Meter 1 (192.168.1.20) | Meter 2 (192.168.168.31) |
|---|---|---|
| V_PH(V) | 108-114-113 | 108-111-112 |
| V_Line(V) | 192-197-194 | 190-196-193 |
| I (A) | 0.2-0.00-0.00-0.19 | 0.34-0.34-0.34-0.00 |
| P (W) | 14 | -14 |
| Q (var) | -1 | -115 |
| S (VA) | 21 | 116 |
| F (Hz) | 59.99 | 59.98 |
| Power Factor | 0.68 | 0.12 |
| Parameter | Meter | Normal | Attack | Deviation (%) |
|---|---|---|---|---|
| Vph avg (V) | Meter 1 | 114 | 112 | -1.75% |
| Vph avg (V) | Meter 2 | 114 | 111.67 | -2.05% |
| Frequency (Hz) | Meter 1 | 60.00 | 59.99 | -0.017% |
| Frequency (Hz) | Meter 2 | 60.00 | 59.98 | -0.033% |
| Reactive Power (var) | Meter 2 | -116 | -115 | +0.86% |
4.4. Cyberattack Scenarios Definition
4.4.1. Scenarios
4.4.2. Metrics
4.4.3. Controllability & Observability
4.4.4. Performance Under Cyberattacks
4.4.5. Voltage and Frequency Deviations
4.4.6. Federated Learning
5. Conclusions
References
- Adeleke, O.J.; Jovanovich, K.; Ogunbunmi, S.; Samuel, O.; Kehinde, T.O. Comprehensive exploration of smart cities: A systematic review of benefits, challenges, and future directions in telecommunications and urban development. IEEE Sensors Reviews 2025. [Google Scholar] [CrossRef]
- Zhang, H.; Liu, B.; Wu, H. Smart grid cyber-physical attack and defense: A review. IEEe Access 2021, 9, 29641–29659. [Google Scholar] [CrossRef]
- Ali, R.F.; Muneer, A.; Dominic, P.D.D.; Ghaleb, E.A.A.; Al-Ashmori, A. Survey on Cyber Security for Industrial Control Systems. In Proceedings of the 2021 International Conference on Data Analytics for Business and Industry (ICDABI), 2021. [Google Scholar] [CrossRef]
- Sujatha, M.S.; Banu, S.S.; Sriyesh, V.; Sreenivasan, G.; Kuruba, M.; Reddy, M.G.M. Cyber Security for Power System. In Proceedings of the 2024 International Conference on Electrical Energy Systems (ICEES), 2024. [Google Scholar] [CrossRef]
- Zhang, K.; Pan, S.; Zhang, S.; Lin, J. The Intrusion Detection Method for Power Grid Industrial Control Systems Based on Improved Triplet Neural Network. In Proceedings of the 2025 International Conference on Electrical Automation and Artificial Intelligence (ICEAAI), 2025. [Google Scholar] [CrossRef]
- Chakraborty, S.; Kar, S. Hierarchical Control of Networked Microgrid with Intelligent Management of TCLs: A Case Study Approach. Electric Power Systems Research 2023, 224, 109787. [Google Scholar] [CrossRef]
- Ran, X.; Ma, L. An Extended False Data Injection Attack via Deep Reinforcement Learning: Attack Model and Countermeasures in Cyber-Physical Power Systems. IEEE Transactions on Automation Science and Engineering 2025. [Google Scholar] [CrossRef]
- Sridhar, S.; Hahn, A.; Govindarasu, M. Cyber-physical system security for the electric power grid. Proceedings of the IEEE 2012, 100, 210–224. [Google Scholar] [CrossRef]
- Liu, Y.; Ning, P.; Reiter, M.K. False data injection attacks against state estimation in electric power grids. IEEE Transactions on Smart Grid 2011, 1, 13–25. [Google Scholar] [CrossRef]
- Karanfil, M.; Rebbah, D.E.; Debbabi, M.; Kassouf, M.; Ghafouri, M.; Youssef, E.-N.S.; Hanna, A. Detection of Microgrid Cyberattacks Using Network and System Management. IEEE Transactions on Smart Grid 2023, 14(3), 2390–2405. [Google Scholar] [CrossRef]
- McMahan, B.; Moore, E.; Ramage, D.; Hampson, S.; Aguera y Arcas, B. Communication-efficient learning of deep networks from decentralized data. In Proceedings of the 20th International Conference on Artificial Intelligence and Statistics (AISTATS), Fort Lauderdale, FL, USA, 20–22 April 2017; pp. 1273–1282. [Google Scholar]
- Bhol, S.G.; Swain, S.; Pattnaik, P.K.; Mohanty, S. Federated Learning and Blockchain Integrated Framework for Energy Management. In Proceedings of the 2025 2nd International Conference on Intelligent Systems for Cybersecurity (ISCS), 2025. [Google Scholar] [CrossRef]
- Li, Y. Detection of False Data Injection Attacks in Smart Grid: A Secure Federated Deep Learning Approach. In Proceedings of the 2024 IEEE Power & Energy Society General Meeting (PESGM), 2024. [Google Scholar] [CrossRef]
- Haridas, R.; Sharma, S.; Bhakar, R.; Mathuria, P. Evolution of Load Redistribution Attack in Cyber Physical Power System. In Proceedings of the 2023 IEEE PES Innovative Smart Grid Technologies – Middle East (ISGT Middle East), 2023. [Google Scholar] [CrossRef]
- Maliha, M.; Oluyomi, A.; Booge, M.; Bhattacharjee, S.; Braasch, N.; Gomez, P.; Das, S.K. Real-Time Testbed for Studying Cyberattacks and Defense in DER-integrated Smart Inverter Systems. In Proceedings of the 2025 IEEE International Conference on Communications, Control, and Computing Technologies for Smart Grids (SmartGridComm), 2025. [Google Scholar] [CrossRef]
- Jørgensen, J.; et al. Cybersecurity and resilience of smart grids: Threat landscape, incidents, and emerging solutions. Renewable and Sustainable Energy Reviews 2026, 182, 113456. [Google Scholar] [CrossRef]
- Khare, U.; Malviya, A.; Gawre, S.K.; Arya, A. Cyber Physical Security of a Smart Grid: A Review. In Proceedings of the 2023 IEEE International Students’ Conference on Electrical, Electronics and Computer Science (SCEECS), 2023. [Google Scholar] [CrossRef]
- Sanjalawe, Y.; Al-E’mari, S.; Fraihat, S.; Makhadmeh, S.N.; Alzubi, E. AI-Powered Smart Grids in the 6G Era: A Comprehensive Survey on Security and Intelligent Energy Systems. IEEE Open Journal of the Communications Society 2025, Vol. 6, 7677–7680+. [Google Scholar] [CrossRef]
- Rajesh, M.; Ramachandran, S.; Vengatesan, K.; Dhanabalan, S.S.; Nataraj, S.K. Federated Learning for Personalized Recommendation in Securing Power Traces in Smart Grid Systems. IEEE Transactions on Consumer Electronics 2024, Vol. 70(No. 1), 88–95. [Google Scholar] [CrossRef]
- Cintuglu, M.H.; Mohammed, O.A.; Akkaya, K.; Uluagac, A.S. A Survey on Smart Grid Cyber-Physical System Testbeds. IEEE Communications Surveys & Tutorials 2017, Vol. 19(No. 1), 446–464. [Google Scholar] [CrossRef]
- Athamnih, A.S.; Annamalai, A.; Abood, S.; Woodard, C.; Chouikha, M.; Al-zuhairi, H. AI-Driven Cybersecurity for SCADA-Integrated Microgrids: A Real-Time Detection Framework. In Proceedings of the 2026 IEEE 5th International Conference on AI in Cybersecurity (ICAIC), Houston, TX, USA, 18–20 February 2026; IEEE: Piscataway, NJ, USA, 2026. [Google Scholar] [CrossRef]
- Abood, S.I.; Islam, N.; Chouikha, M.F.; Annamalai, A.; Khalid, I. Controllability and Observability of Real-Time Implementation of Smart Grid Cyber-Physical Systems under Adversarial Attacks. IEEE Access 2026, 14, 11902–11920. [Google Scholar] [CrossRef]
- Abood, S.; Khalid, I.; Chouikha, M.; Annamalai, A.; Obiomon, P.; Butler-Purry, K.L. AI-Based Cybersecurity Assessment for Renewable-Integrated Smart Grid SCADA Systems. In Proceedings of the 4th International Scientific Conference of Engineering Sciences (ISCES 2025), Baquba, Iraq, 10–11 December 2025; IET; p. 2025. [Google Scholar] [CrossRef]
- Zhang, Z.; Peng, H.; Li, L.; Bao, S. Adaptive Asynchronous Federated Learning for Digital Twin Driven Smart Grid. IEEE Trans. Smart Grid 2025, 16, 4167–4182. [Google Scholar] [CrossRef]
- Deng, X.; Pan, Y.; Fang, H. Anomaly Detection in Smart Grid Behavior Monitoring via Federated Learning: A Privacy-Preserving Defense Against Cyber-Physical Attacks. J. Cyber Secur. Mobil. 2025, 14, 1151–1172. [Google Scholar] [CrossRef]
- Abood, S.; Ibrahim, Z.; Annamalai, A.; Khalid, I.; Chouikha, M.; Adeloye, A. SCADA Watch: Cybersecurity Mitigation in Smart Electric Microgrids. In Proceedings of the 2025 IEEE International Communications Energy Conference (INTELEC); IEEE: Piscataway, NJ, USA, 2025. [Google Scholar] [CrossRef]
- Xu, B.; Zhou, Y.; Li, M.; Ding, B.; Tan, G. A Digital Power Grid Information Security Protection Method Based on Federated Learning and Deep Learning. In Proceedings of the 2025 10th Asia Conference on Power and Electrical Engineering (ACPEE); IEEE: Piscataway, NJ, USA, 2025. [Google Scholar] [CrossRef]
- Li, X.; Wen, M.; He, S.; Lu, R.; Wang, L. A Privacy-Preserving Federated Learning Scheme against Poisoning Attacks in Smart Grid. IEEE Internet Things J. 2024, 11, 16805–16816. [Google Scholar] [CrossRef]
- Zheng, R.; Sumper, A.; Aragüés-Peñalba, M.; Galceran-Arellano, S. Advancing Power System Services with Privacy-Preserving Federated Learning Techniques: A Review. IEEE Access 2024, 12, 76753–76779. [Google Scholar] [CrossRef]
- Bhatia, K.; Ojha, S.S. Federated Learning Framework for Early Detection of Reconnaissance Attacks in Smart Grid Environments. In Proceedings of the 2024 2nd International Conference on Device Intelligence, Computing and Communication Technologies (DICCT); IEEE: Piscataway, NJ, USA, 2024. [Google Scholar] [CrossRef]
- Moniruzzaman, M.; Yassine, A.; Benlamri, R. Blockchain and Federated Reinforcement Learning for Vehicle-to-Everything Energy Trading in Smart Grids. IEEE Trans. Artif. Intell. 2024, 5, 839–855. [Google Scholar] [CrossRef]
- Li, Q.; Tang, W. An Anomaly Detection Method for Smart Power Grid: A Federated Learning Framework; 2024. [Google Scholar]
- Blika, A.; Palmos, S.; Doukas, G.; Lamprou, V.; Pelekis, S.; Kontoulis, M.; Ntanos, C.; Askounis, D. Federated Learning for Enhanced Cybersecurity and Trustworthiness in 5G and 6G Networks: A Comprehensive Survey. IEEE Open J. Commun. Soc. 2024, 6, 3094–3124. [Google Scholar] [CrossRef]
- Kapoor, A.; Kumar, D. Federated Learning for Urban Sensing Systems: A Comprehensive Survey on Attacks, Defenses, Incentive Mechanisms, and Applications. IEEE Commun. Surv. Tutor. 2024, 27, 1293–1325. [Google Scholar] [CrossRef]
| Ref. | Year | Main Focus | Attack / Threat Type | Methodology | Evaluation Environment | Controllability / Observability Consideration | Position relative to this work |
|---|---|---|---|---|---|---|---|
| [21] | 2026 | AI-driven cybersecurity framework for SCADA-integrated microgrids | DoS, ARP injection, plus broader discussion of FDI/replay | AI-based detection using SCADA and network features | Testbed / realistic scenarios | Not explicit | Strong real-time AI detection, but it does not directly formalize controllability/observability as the core evaluation lens. |
| [22] | 2026 | Maintaining smart-grid CPS controllability and observability under adversarial attacks | Telnet DoS, Modbus TCP flood, ICMP flood | SCADA-based real-time CPS + matrix-rank controllability/observability analysis | Real-time CPS + simulation (3-, 9-, 14-bus) | Explicitly addressed | Closest to the current manuscript, your new work extends toward privacy-preserving federated cybersecurity analytics and coordinated monitoring logic. |
| [23] | 2025 | AI-based cybersecurity assessment for renewable-integrated smart-grid SCADA systems | Telnet, DoS, Modbus/TCP, ICMP; protocol comparison across SSH/Telnet/HTTP/HTTPS | RNN–LSTM IDS + Wireshark + SCADA logs + protocol performance comparison | Real-world CPS testbed | Not explicit | Valuable for protocol/security benchmarking, but less centered on formal controllability/observability preservation. |
| [24] | 2025 | Digital-twin-driven smart grid with asynchronous federated learning and blockchain | Malicious station behavior, poisoning robustness, stale/non-IID updates | Blockchain + asynchronous FL + digital twin | Comparative experiments on heterogeneous devices and real power-grid datasets | Not addressed | Strong distributed learning architecture but not targeted to SCADA protocol attacks or operator visibility/control. |
| [25] | 2025 | Privacy-preserving anomaly detection for smart-grid behavior monitoring | Cyber-physical / privacy attacks | K-means + LSTM + FL | Experimental evaluation on smart-grid behavior data | Not addressed | Strong privacy/anomaly results, but no direct analysis of SCADA testbed controllability/observability. |
| [26] | 2025 | Cybersecurity mitigation in smart electric microgrids | DoS, Telnet, Modbus-based intrusion scenarios | SCADA-based mitigation, protocol analysis, testbed monitoring | Real-time CPS microgrid testbed | Partial / indirect | Practical mitigation paper, but the present work is stronger in control-theoretic interpretation and federated perspective. |
| [27] | 2025 | Information security protection for digital power grids | Network intrusion/cyberattack classification | Improved BiLSTM-DNN + multi-head attention + FL | NSL-KDD-based experimental study | Not addressed | Strong FL+DL classifier, but dataset-driven and not validated on a real SCADA/CPS control platform. |
| [28] | 2024 | Privacy-preserving FL against poisoning attacks in smart grid | Model poisoning / malicious gradients | Homomorphic encryption + hierarchical aggregation + adaptive defense | FL experiments on MNIST/CIFAR-10 under malicious participants | Not addressed | Strong privacy and robustness at the FL layer, but not a SCADA power-system operational study. |
| [29] | 2024 | Holistic review of FL applications across energy services | Broad privacy/security/data-silo concerns | Review/taxonomy of FL methods in energy systems | Conceptual / literature review | Not addressed | Useful background on FL in energy, but not focused on protocol-level SCADA attacks or control visibility. |
| [30] | 2024 | Early detection of reconnaissance attacks in smart-grid environments | Reconnaissance attack | FSGD-based federated learning | Kaggle IoT-security dataset; client/server validation | Not addressed | Important for attack-stage detection, but dataset-based and not experimentally tied to SCADA control performance. |
| [31] | 2024 | Secure V2X energy trading in smart grids | Trust, privacy, spoofing/SPOF-related platform threats, rather than SCADA intrusion detection | Blockchain + federated reinforcement learning | Simulation using a real-world dataset + Avalanche implementation | Not addressed | Relevant to secure smart-grid transactions, but outside SCADA attack monitoring and control-resilience scope. |
| [32] | 2024* | Federated anomaly detection in smart power grids | Abnormal events/anomalies | FL-based anomaly detection with weighted monitoring indicators | Simulation/analysis for grid monitoring categories | Not addressed | Useful anomaly-detection baseline but lacks real-time cyber-physical experimentation and explicit control-theoretic treatment. |
| [33] | 2024 | FL for cybersecurity and trustworthiness in 5G/6G networks | Inference, poisoning, insider/outsider FL attacks | Comprehensive survey | Review | Not addressed | Broader-domain FL security survey; indirectly useful for threat/defense framing, not for smart-grid SCADA validation. |
| [34] | 2024 | FL in urban sensing systems with attacks, defenses, and incentives | Inference attacks, poisoning attacks | Comprehensive survey | Review | Not addressed | Provides a broader FL attack/defense context but is only indirectly relevant to smart-grid SCADA cybersecurity. |
| This work | - | Privacy-preserving federated cybersecurity analytics for SCADA-based smart grids under coordinated attacks | SSH, Modbus/TCP flooding, ICMP-based attacks | Real-time SCADA/CPS testbed + federated-learning perspective + controllability/observability matrix analysis + Wireshark-assisted monitoring | Real-time laboratory smart-grid/SCADA testbed | Explicitly addressed | Distinguishes itself by jointly studying protocol attacks, SCADA monitoring, and control-theoretic resilience in one real-time framework. |
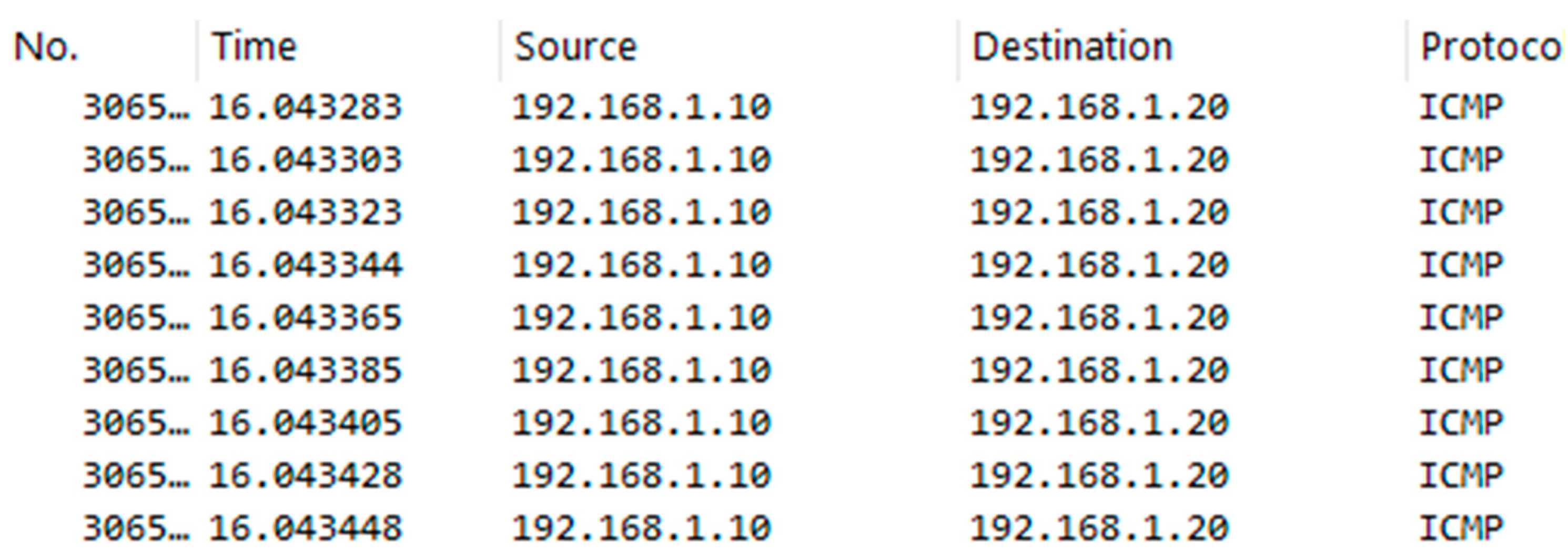
| Scenario | Type of Attack | Protocol | Tool Used | Duration (s) | Packet Rate (pkt/s) |
|---|---|---|---|---|---|
| S1 | Normal | Modbus/TCP | — | 60 | 120 |
| S2 | SSH | SSH | PuTTY | 60 | 350 |
| S3 | ICMP Flood | ICMP | hping3 | 60 | 1200 |
| S4 | Coordinated Attack | SSH + ICMP | PuTTY + hping3 | 60 | 1800 |
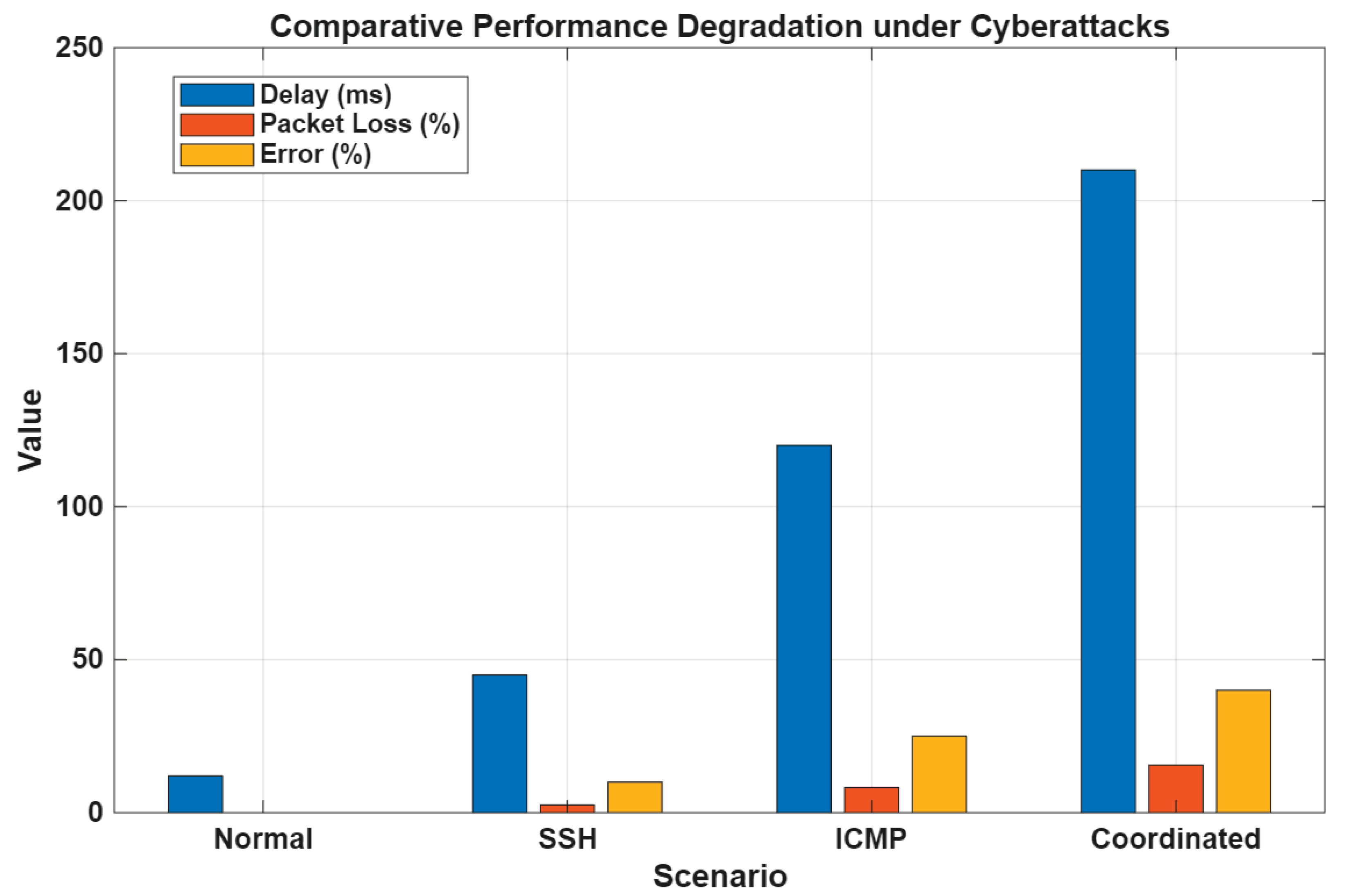
| Scenario | Avg. Delay (ms) | Packet Loss (%) | Command Error (%) | Response Time (ms) |
|---|---|---|---|---|
| Normal | 12 | 0 | 0 | 15 |
| SSH | 45 | 2.5 | 10 | 60 |
| ICMP | 120 | 8.2 | 25 | 140 |
| Coordinated | 210 | 15.5 | 40 | 260 |
| Scenario | Rank (Controllability) | Rank (Observability) | System States (n) | Status |
|---|---|---|---|---|
| Normal | 4 | 4 | 4 | Fully Controllable & Observable |
| SSH | 4 | 3 | 4 | Partial Observability Loss |
| ICMP | 3 | 3 | 4 | Degraded System |
| Coordinated | 2 | 2 | 4 | Critical Loss |
| Parameter | Normal | Attack | Deviation (%) |
|---|---|---|---|
| Voltage (V) | 115 | 113 | -1.7% |
| Frequency (Hz) | 60.01 | 59.98 | -0.05% |
| Metric | Value (%) |
|---|---|
| Accuracy | 96.4 |
| Precision | 95.8 |
| Recall | 95.2 |
| F1-Score | 95.5 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




