1. Introduction
Classical circuit theory offers multiple notions of equivalence (Thevenin/Norton, port models, driving-point and transfer descriptions), typically expressed at accessible terminals. In parallel, modified nodal analysis (MNA) is a standard framework for systematic modeling and simulation.
Question. Given a static linear circuit and a chosen set of accessible boundary nodes, can one compute and synthesize a canonical equivalent circuit that reproduces exactly the same boundary behavior?
This paper answers the question in a constructive and deliberately modest way: we formalize an equivalence relation based on boundary behavior, prove that the boundary relation is necessarily affine under standard well-posedness assumptions, and provide a boundary-only normal form that uses only independent current sources and VCCS elements. The goal is not to “invent a new circuit theorem”, but to package standard elimination ideas into a clean, boundary-centric statement with an explicit canonical realization and classification.
Contributions.
(i) A boundary behavioral equivalence relation is defined for static linear circuits.
(ii) Under mild MNA well-posedness assumptions, the boundary map is affine.
(iii) A canonical boundary normal form is given and can be synthesized with only independent current sources and VCCS.
(iv) The transformation is deterministic, idempotent, and yields a classification via (constraint-aware).
(v) A worked numeric case study includes a dependent source, an explicit VCCS list, and an exact spot-check verification.
Positioning with respect to Kron reduction.
Kron reduction is commonly presented as a Schur complement operation on passive nodal conductance matrices. The present paper retains the same linear-algebraic core but reframes it as a boundary behavioral equivalence statement for general static linear circuits, including dependent sources. In addition, we provide an explicit boundary-only realization using only current sources and VCCS elements, and we state a classification result in terms of .
2. Scope, Sign Conventions, and Modeling Assumptions
We restrict attention to static linear lumped circuits: conductances, independent sources, and linear dependent sources (VCCS/CCCS/VCVS/CCVS realizable in MNA), with no capacitors or inductors and no nonlinearities. The circuit admits an algebraic description.
Boundary sign convention.
Boundary current is defined as net current injected from the exterior into the circuit at the boundary nodes; positive injection means current enters the circuit at the boundary node.
3. Behavioral Equivalence on the Boundary
Definition 1 (Boundary behavior).
Fix a ground node and choose a set B of n boundary nodes. Let denote boundary node voltages (w.r.t. ground). Let denote the vector of net currents injected from the exterior into the circuit at the boundary nodes. Theboundary behavior
of a circuit C is the set
of all pairs consistent with internal circuit laws (KCL/KVL and element relations) and ideal-source constraints.
3.1. Admissible Boundary Voltages
Ideal voltage sources (independent or dependent) impose algebraic constraints among node voltages (supernodes). If such constraints touch the boundary, boundary voltages cannot always be assigned arbitrarily.
Definition 2 (Admissible boundary voltage set). Let be the set of boundary voltage vectors consistent with all ideal voltage-source constraints that involve boundary node voltages. A boundary voltage isadmissibleif .
Assumption A1 (Affine constraint structure).
The admissible set is affine:
for some matrix F and vector f (possibly , in which case ).
Definition 3 (Behavioral boundary equivalence).
Two circuits C and sharing the same boundary node set B arebehaviorally equivalent on the boundary
, written , if they induce the same boundary behavior:
4. Affine Boundary Law via MNA Elimination
We connect boundary behavior with elimination in modified nodal analysis (MNA). See, e.g., [
1,
2] for MNA background.
4.1. A Minimal MNA Partition Viewpoint
An MNA formulation yields a linear descriptor system of the form
where
x collects node voltages and (for ideal voltage sources and certain dependent sources) additional currents/auxiliary variables. Reorder unknowns as
so that boundary-related coordinates
include
explicitly and
collects internal variables. Partition (
1) accordingly:
Assumption A2 (Well-posed internal elimination).
For each admissible boundary voltage , the internal block in (2) is nonsingular, so internal variables can be uniquely eliminated (in exact arithmetic).
Remark 1 (How is read). In standard nodal sign conventions, the boundary KCL residual can be interpreted as netexternal injection. Equivalently, one may define as the vector of currents flowing from the exterior into the circuit at boundary nodes so that, after eliminating internal variables, the reduced boundary equations can be written in the conjugate pair . The present paper uses this interpretation, consistent with Definition 1.
Theorem 1 (Affine boundary law).
Under Assumptions A1 and A2, there exist a matrix and a vector such that
Moreover, can be obtained by a Schur-complement reduction of (2) (without explicit matrix inversion) followed by a consistent identification of from the reduced boundary equations.
Remark 2 (No symmetry or passivity is assumed). With dependent sources, need not be symmetric nor positive semidefinite. It should be interpreted as a boundary input–output operator on , not necessarily as the admittance matrix of a passive resistive network.
4.2. Uniqueness and Constraints: What Is Actually Identifiable
When
, the affine law (
3) determines
uniquely. When
is constrained, only the restriction of the affine law to the admissible directions is identifiable.
Lemma 1 (Uniqueness on the admissible subspace).
Let be nonempty. Choose any particular , and let have columns forming a basis of , so every admissible boundary voltage can be written as . If
then the induced affine law on free coordinates is unique:
In particular, if (so ), then and .
Remark 3 (A convenient “canonical” representation under constraints). If is constrained, one may treat as the canonical parameters on the free coordinate w. This eliminates the non-identifiable directions orthogonal to .
5. Canonical Boundary Normal Form
(Norton-type)).
Definition 4 (Boundary normal form Given n boundary nodes and parameters , define as theboundary-only
circuit that realizes (3) on using only:
Independent current sourcesinjecting the components of at boundary nodes, and
VCCS elementsimplementing the linear map .
Concretely, for each pair , a VCCS injects into boundary node i a current , where the control voltage is measured from node j to ground, and the output is a current source from node i to ground.
Theorem 2 (Synthesis and correctness).
Under Assumptions A1 and A2, every static linear circuit C is behaviorally equivalent on B to its boundary normal form:
where are the parameters of the boundary affine law (3).
Corollary 1 (Idempotence). Applying the construction to the normal form returns the same boundary law parameters (on ), i.e., the transformation is idempotent.
Corollary 2 (Classification (constraint-aware)).
Let C and be static linear circuits sharing the same boundary set B and satisfying Assumptions A1 and A2. Then if and only if their induced affine laws agree on . Equivalently, in the parametrization of Lemma 1, one has
In particular, if then iff .
6. Deterministic Construction Recipe
This section summarizes the transformation in an implementation-oriented form.
Remark 4 (Numerical note). In floating-point arithmetic, Step 5 should use sparse-aware factorizations (e.g. LU with pivoting) rather than explicit inversion. The transformation is exact in exact arithmetic; practical discrepancies arise only from numerical conditioning (e.g. ).
7. Interpretation and Relation to Kron/Norton/Thevenin
7.1. Reduction to Classical Kron Reduction in the Passive Resistive Case
When the network is purely resistive and passive (no dependent sources and no active elements), the elimination of internal nodes coincides with classical Kron (Schur) reduction of the nodal conductance matrix. Then
is symmetric and positive semidefinite, and
captures the effect of independent current injections mapped to the boundary through elimination [
3,
4].
7.2. Dependent Sources: Asymmetry and Non-Passivity
With dependent sources, the reduced operator
need not be symmetric nor passive. This is not a pathology: controlled sources encode directed gain, and
is best interpreted as a boundary input–output operator in the behavioral sense [
5,
6].
|
Algorithm 1:Boundary normal form for a static linear circuit (MNA-based) |
-
Require:
Static linear circuit C, boundary node set B (size n), a consistent MNA formulation. -
Ensure:
Parameters such that holds on . - 1:
Choose ground and identify boundary nodes B and internal nodes I. - 2:
Assemble the MNA linear system and reorder unknowns so boundary voltages appear explicitly. - 3:
Encode boundary voltage constraints induced by ideal voltage sources as . - 4:
Partition the MNA system into boundary-related and internal blocks (Schur setting):
- 5:
Eliminate internal unknowns by solving linear systems (avoid explicit inverses):
- 6:
Form reduced (Schur) quantities:
- 7:
Interpret the reduced boundary equations in the conjugate pair to extract the affine law on . - 8:
Constraint-aware note: if constrains the boundary, select with and a basis N for ; compute canonical parameters on free coordinates w via . - 9:
Synthesize with: (i) n current sources injecting into boundary nodes, and (ii) VCCS sources injecting into node i for all . |
7.3. Norton Viewpoint on n Boundary Nodes
Equation (
3) is a multi-node Norton-type representation: the boundary currents are the sum of (i) an operator term
and (ii) an offset
. For a single port this reduces to the classical Norton form; here it generalizes to an
n-node boundary.
7.4. Dual (Thevenin-Type) Remark
A dual formulation expresses boundary voltages affinely in boundary currents,
on an appropriate admissible current set. When
is invertible on the admissible subspace (or after restriction to free coordinates), one may take
and
. We do not pursue the dual synthesis here; the current-source/VCCS realization aligns directly with MNA elimination.
8. Case Study
8.1. Original Circuit (One Internal Node and a Dependent Source)
8.2. Elimination and Explicit Affine Parameters
Write KCL at internal node 3 (sum of currents leaving node 3 equals zero). Using the boundary convention that
are injected from the exterior into nodes 1,2, we obtain:
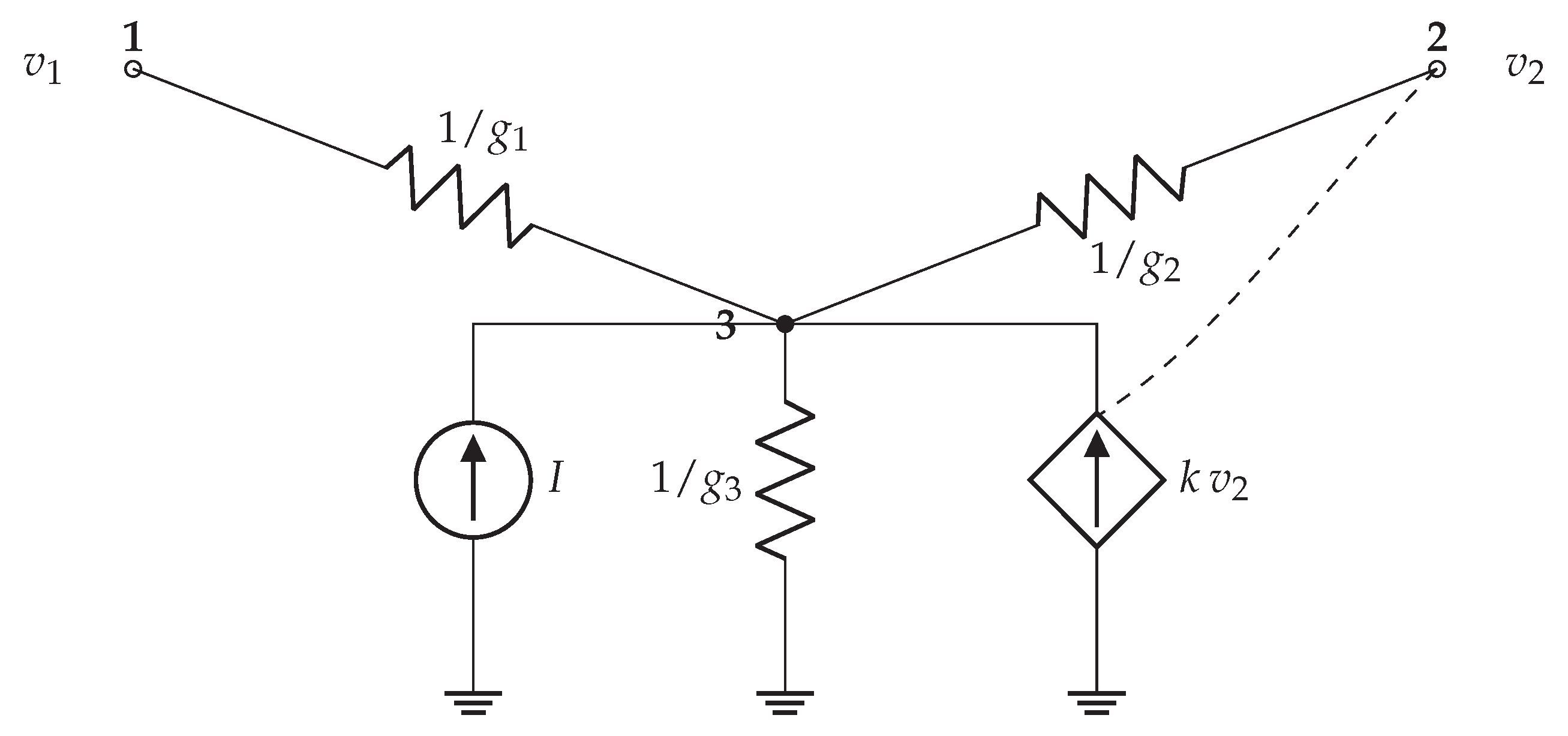
Figure 1.
Case-study circuit with boundary nodes 1,2 and internal node 3.
Figure 1.
Case-study circuit with boundary nodes 1,2 and internal node 3.
Boundary injected currents follow from the resistors connected to node 3:
Substituting (
4) yields an affine law
.
For the numerical instance
, one obtains
8.3. Normal-Form Realization for (Explicit Source List)
This corresponds to the sources in
Table 1.
8.4. Numerical Consistency Check (Spot Test)
Choose
. The normal form predicts
Evaluating the original circuit via (
4) gives
hence
and
, matching exactly.
9. Conclusions
A boundary-centric, behavior-preserving transformation for static linear circuits has been presented. Under standard MNA well-posedness assumptions, boundary behavior is captured completely by an affine law on an admissible affine set , and a canonical boundary-only realization using independent current sources and VCCS elements provides a normal form. The construction is deterministic, idempotent, and yields a complete classification (constraint-aware): two circuits are behaviorally equivalent on a given boundary if and only if their induced affine laws agree on .
9.0.0.4. Future work (concrete directions).
(i) Dynamics: extend to circuits with storage by deriving reduced transfer operators (or ) via descriptor MNA and structured elimination.
(ii) Interconnection: develop algebraic composition rules for normal forms under boundary interconnection.
(iii) Numerics: characterize stability and error in terms of and sparse fill-in, and implement robust solvers that avoid inverses.
References
- C.-W. Ho, A. E. Ruehli, and P. A. Brennan, “The Modified Nodal Approach to Network Analysis,” IEEE Transactions on Circuits and Systems, vol. 22, no. 6, pp. 504–509, June 1975.
- L. W. Nagel, SPICE2: A Computer Program to Simulate Semiconductor Circuits, Technical Report UCB/ERL M520, EECS Department, University of California, Berkeley, May 1975.
- F. Dörfler and F. Bullo, “Kron Reduction of Graphs With Applications to Electrical Networks,” IEEE Transactions on Circuits and Systems I: Regular Papers, vol. 60, no. 1, pp. 150–163, Jan. 2013.
- G. Kron, Tensor Analysis of Networks, Wiley, New York, 1939.
- J. C. Willems, “Paradigms and Puzzles in the Theory of Dynamical Systems,” IEEE Transactions on Automatic Control, vol. 36, no. 3, pp. 259–294, Mar. 1991.
- J. C. Willems, “The Behavioral Approach to Open and Interconnected Systems,” IEEE Control Systems Magazine, vol. 27, no. 6, pp. 46–99, Dec. 2007.
Table 1.
Explicit source list for the normal form when . Each VCCS is understood as: control voltage measured from node j to ground; output is a current source from node i to ground of value .
Table 1.
Explicit source list for the normal form when . Each VCCS is understood as: control voltage measured from node j to ground; output is a current source from node i to ground of value .
| Element |
Injected at node |
Value (control) |
| Independent current source |
1 |
|
| Independent current source |
2 |
|
| VCCS (self) |
1 |
|
| VCCS (cross) |
1 |
|
| VCCS (cross) |
2 |
|
| VCCS (self) |
2 |
|
|
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).