Submitted:
16 February 2026
Posted:
28 February 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
II. Background
- A.
- Machine Learning and Deep Learning:

 |
 |
III. Systematic Evaluation Framework of AI-Based Ransomware Detection
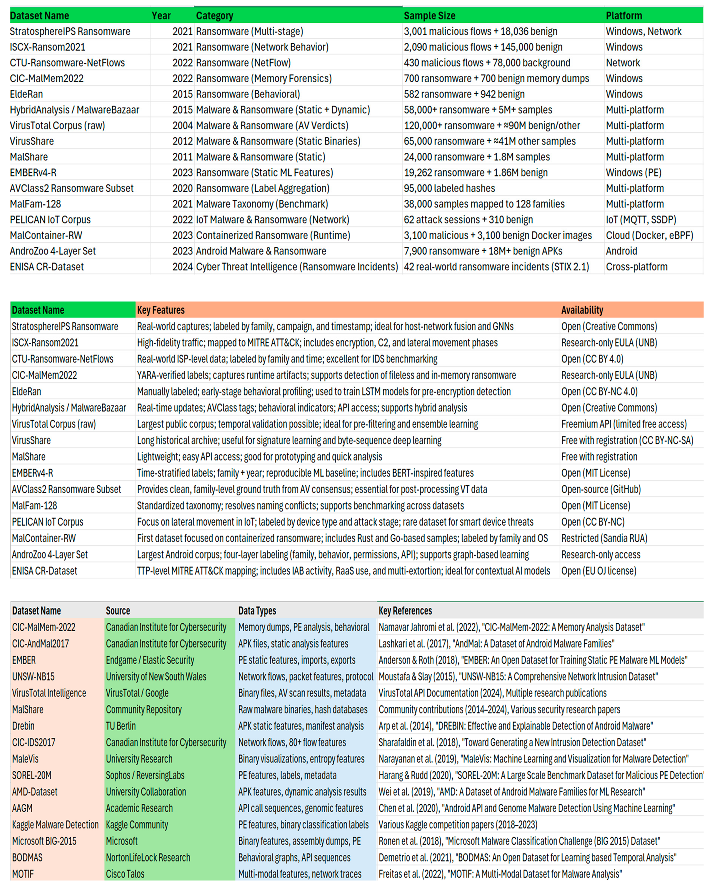
| CIC-MalMem-2022 | Datasets | Research | Canadian Institute for Cybersecurity | UNB |
| CIC-AndMal2017 | Datasets | Research | Canadian Institute for Cybersecurity | UNB |
| EMBER | GitHub - elastic/ember: Elastic Malware Benchmark for Empowering Researchers |
| UNSW | The UNSW-NB15 Dataset | UNSW Research |
| VirusTotal Intelligence | VirusTotal - Home |
| MalShare | MalShare |
| IEEE DataPort | Dataset for Android Malware Detection | IEEE DataPort |
| Android-Malware-Datasets | traceflight/Android-Malware-Datasets: Popular Android malware datasets |
| CIC-IDS2017 | Datasets | Research | Canadian Institute for Cybersecurity | UNB |
| MaleVis University Research | https://vision.ece.ucsb.edu/ |
| SOREL-20M | GitHub - sophos/SOREL-20M: Sophos-ReversingLabs 20 million sample dataset |
| IMPACT Cyber-Trust | IMPACT - Android Malware Dataset (Argus Lab) |
| AAGM | |
| Kaggle Malware Detection | Benign & Malicious PE Files |
| Microsoft BIG-2015 | Microsoft Malware Classification Challenge (BIG 2015) | Kaggle |
| BODMAS | whyisyoung/BODMAS: Code for our DLS'21 paper - BODMAS: An Open Dataset for Learning based Temporal Analysis of PE Malware. BODMAS is short for Blue Hexagon Open Dataset for Malware AnalysiS. BODMAS Malware Dataset |
| CIC-AAGM -2017 | Android Adware 2017| Datasets | Research | Canadian Institute for Cybersecurity | UNB |
| Ransomware-DB | Static + dynamic analysis, encryption behaviour |
| RanDroid | APK analysis, encryption patterns, UI blocking |
| CryptoLocker Analysis Set | Behavioural logs, encryption analysis, network traces |
| Locky Behaviour Datasets | API calls, file operations, registry modifications |
| WannaCry Lab Collections | Network propagation, vulnerability exploitation, encryption |
| Ryuk Analysis Suite | Enterprise attack chains, lateral movement, privilege escalation |
| Maze double-extortion set | Data exfiltration patterns, encryption behaviour, C2 communication |
| RaaS Lab collection | RaaS platform analysis, affiliate samples, payment mechanisms |
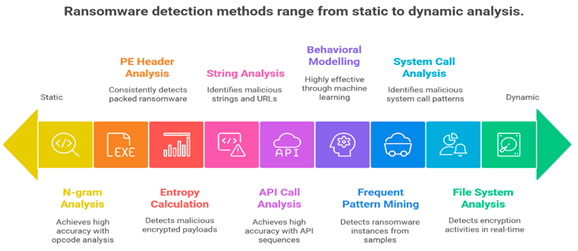
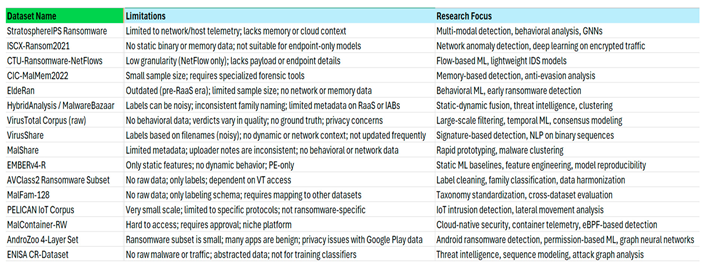
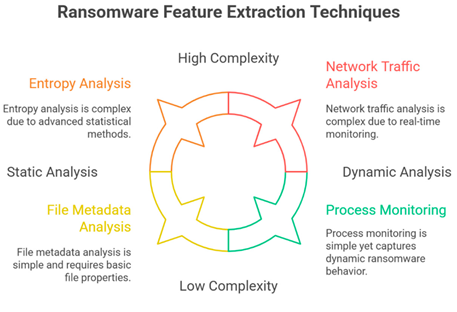
| Description of static analysis | Detects structural and syntactic features such as headers, opcodes, and imported libraries in ransomware binaries without executing them |
| Key techniques and approaches | Disassembly using IDA Pro, Ghidra, radare2, OllyDump Opcode sequence extraction PE header analysis (e.g., section entropy, imports) N-gram analysis of opcodes TF-IDF for feature weighting Use of pefile, DIE, Distorm3 librarie |
| Tools & Frameworks | IDA Pro, Ghidra, radare2, OllyDump, pefile, DIE, Distorm3 |
| Relevant findings & applications | Extracts features like strings and API calls pre-execution Vulnerable to packing/obfuscation Effective for initial triage but limited against advanced evasion techniques |
| Description of statistical analysis | Applies statistical methods to quantify and interpret patterns in ransomware data, often used in preprocessing and feature evaluation. |
| Key techniques and approaches | Handling missing values (mean/median imputation, removal) Noise reduction (binning, regression) Data discretization and generalization Dimensionality reduction (PCA, LDA, GDA) Outlier detection and duplication removal |
| Tools & Frameworks | Python (Pandas, Scikit-learn), R, WEKA |
| Relevant findings & applications | Improves data quality and model performance Mutual Information (MI), Chi-Square, and RFE used for feature selection in MLRan Balances class distributions and reduces false positives through preprocessing |
| Description of dynamic analysis | Involves executing ransomware in a controlled environment (e.g., sandbox) to observe runtime behaviour such as file operations, API calls, and registry changes. |
| Key techniques and approaches | Behavioural monitoring in sandboxes Logging system calls, file/directory operations, registry modifications, network activity API call sequence analysis Execution on multiple OS versions Repetitive execution for consistency |
| Tools & Frameworks | Cuckoo Sandbox, BitVisor, IRP Logger, ANY.RUN, Hybrid Analysis, VirusTotal |
| Relevant findings & applications | Captures real-time behaviours: encryption patterns, persistence mechanisms MLRan dataset uses Cuckoo Sandbox with 4,880 samples (2,330 ransomware, 2,550 goodware) Most widely used method in public datasets (e.g., ISOT, MarauderMap, MIRAD) |
| Description of hybrid analysis | Combines static and dynamic analysis to improve detection accuracy by leveraging both structural and behavioural features. |
| Key techniques and approaches | - Integration of static features (e.g., PE attributes) with dynamic behaviours (e.g., API calls) - Multi-level profiling - Feature fusion from multiple sources - Sequential or parallel model integration |
| Tools & Frameworks | Custom pipelines combining static and dynamic tools |
| Relevant findings & applications | Achieves higher F1-scores and accuracy than single-method approaches Used in studies combining 72 static and 45 dynamic features selected via Information Gain Enhances robustness against obfuscated samples Recommended for comprehensive ransomware characterization |
| Description of anomaly detection | Identifies deviations from normal system behaviour to detect previously unseen (zero-day) ransomware. |
| Key techniques and approaches | Unsupervised/semi-supervised learning (e.g., autoencoders) Reconstruction error analysis Behavioural baselining Threshold-based alerting Real-time monitoring |
| Tools & Frameworks | Convolutional Autoencoders (CAE), Isolation Forest, One-Class SVM |
| Relevant findings & applications | Effective for detecting novel ransomware strains High sensitivity but prone to false positives SHAP and LIME used to explain anomalies and validate detections |
| Description of pattern recognition | Identifies recurring behavioural or structural patterns associated with ransomware families or attack stages. |
| Key techniques and approaches | N-gram modelling of opcodes or API calls Sequence modelling (e.g., Markov chains, FSMs) Frequent pattern mining Clustering of similar behaviours Signature generation from common traits |
| Tools & Frameworks | TF-IDF, NLP techniques, clustering algorithms (K-means, DBSCAN) |
| Relevant findings & applications | Enables ransomware family classification TF-IDF preserves uniqueness of critical n-grams Frequent pattern mining helps in automated labelling and taxonomy construction |
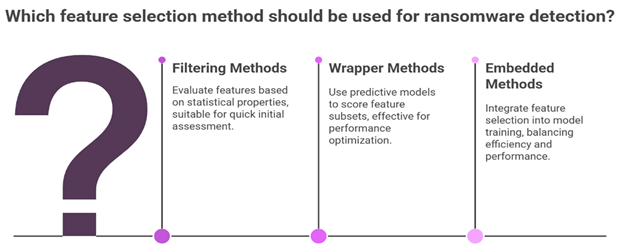
| Description of feature selection | Identifies recurring behavioural or structural patterns associated with ransomware families or attack stages. |
| Key techniques and approaches | N-gram modelling of opcodes or API calls Sequence modelling (e.g., Markov chains, FSMs) Frequent pattern mining Clustering of similar behaviours Signature generation from common traits |
| Tools & Frameworks | TF-IDF, NLP techniques, clustering algorithms (K-means, DBSCAN) |
| Relevant findings & applications | Enables ransomware family classification Uses patch-based CNN and self-attention on opcode n-grams TF-IDF preserves uniqueness of critical n-grams Frequent pattern mining helps in automated labelling and taxonomy construction |
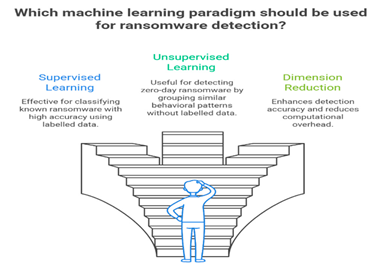
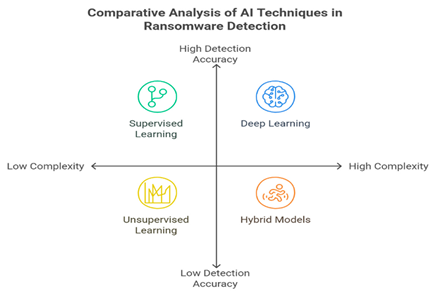
| Description of Machine Learning | Applies supervised and unsupervised algorithms to classify and detect ransomware based on extracted features. |
| Key techniques and approaches | Supervised: Random Forest (RF), SVM, Decision Trees (DT), XGBoost, Logistic Regression, Gradient Boosting Unsupervised: Clustering, Autoencoders, Ensemble methods (e.g., AdaBoost, CSPE-R) |
| Tools & Frameworks | Scikit-learn, XGBoost, TensorFlow, PyTorch |
| Relevant findings & applications | RF, XGBoost, Logistic Regression (achieve >98% accuracy in MLRan) CSPE-R framework detects novel ransomware with cost-sensitive learning Multiple classifiers (DT, SVM, RF, AdaBoost) combined for improved F1-score Models trained on balanced, up-to-date datasets perform better in real-world scenarios |
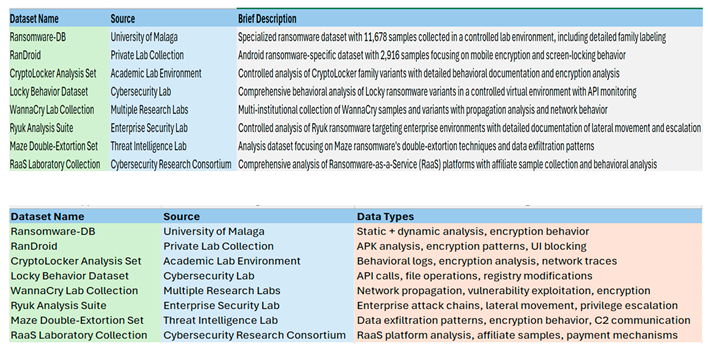
| Algorithm | Purpose | Implementation details | Advantage | Limitations | Best use cases |
| Isolation Forest | Outlier detection and removal | Unsupervised anomaly detection using random forests | Effective for high-dimensional data, no assumptions about data | May remove legitimate rare behaviours | Identifying corrupted sandbox logs |
| Local Outlier Factor (LOF) | Anomaly detection based on local density | Compare local density of samples with neighbours | Good for detecting local anomalies | Computationally expensive for large datasets | Finding execution anomalies in behavioural data |
| One-Class SVM | Novelty detection for data validation | Learns boundary around normal data points | Robust to outliers, works well in high dimensions | Sensitive to hyperparameters selection | Validating sandbox execution quality |
| DBSCAN | Clustering-based outlier removal | Density-based clustering to identify noise points | About cluster shape, automatic outlier detection | Sensitive to hyperparameters, struggles with varying densities | Grouping similar behavioural patterns |
| Z-Score Filtering | Statistical outlier removal | Removes samples beyond standards | Simple implementation, interpretable | Assumes normal distribution | Filtering extreme feature values |
|
Table summary for Missing Value Imputation | |||||
| Algorithm | Purpose | Implementation Details | Advantage | Limitations | Best Use Cases |
| K-Nearest Neighbors (KNN) | Imputation based on similar samples | Uses k most similar samples to impute missing values | Preserves local patterns, handles mixed data types | Computationally expensive, sensitive to distance metric | API call sequences with gaps |
| Random Forest Imputation | Tree-based missing value prediction | Uses RF to predict missing values from other features | Handles non-linear relationships, robust to outliers | Can be biased toward frequent categories | Complex behavioural feature imputation |
| Iterative Imputer | Multivariate imputation using regression | Models each feature with missing values as function of others | Captures feature interaction, flexible model choice | Computationally intensive, may not coverage | Registry operations with dependencies |
| Matrix Factorization | Low-rank approximation for imputation | Decomposes feature matrix to fill missing entries | Effective for high-dimensional sparse data | Assumes low-rank structure | Sparse behavioural matrices |
| Autoencoders | Neural network-based reconstruction | Learns compressed representation to reconstruct missing data | Can capture complex patterns, end-to-end learning | Requires large datasets, block box approach | Complex multi-model behavioural data |
| Algorithm | Purpose | Implementation Details | Advantage | Limitation | Best Use Cases |
| Min-Max Normalization | Scale features to fixed range [0,1] | Preserves original distribution shape, bounded output | Sensitive to outliers, not robust to new data | Entropy values, percentage features | |
| Z-Score Standardization | Centre data around mean with unit variance | Handles different scales, centres data | Assumes normal distribution, unbounded | API call counts, memory usage | |
| Robust Scaler | Scale using median and IQR | Robust to outliers, stable statistics | Less sensitive to distribution tails | Network packet size with outliers | |
| Quantile Normalization | Transform to uniform distribution | Maps values to quantile ranks | Distribution reduces skewness | Loses original distribution information | Highly skewed behavioural metrics |
| Unit Vector Scaling (L2 Normalization) | Scale to unit norm | Preserves direction of data (useful for angle-based similarity) and useful for sparse data | Distorts relative magnitudes and not suitable for features requiring absolute scale | Opcode frequency vectors, behavioural sequence embeddings, and in cosine similarity-based models |
| Algorithm | Purpose | Implementation Details | Advantages | Limitations | Best Use Cases |
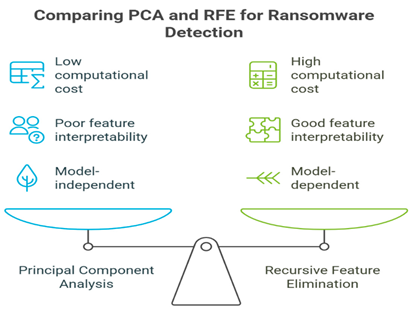
| Principle Component Analysis (PCA) | Linear dimensionality reduction | Finds orthogonal components maximizing | Reduces dimensionality removes correlation | Linear assumptions, interpretability loss | High-dimensional API call features |
| Independent Component Analysis (ICA) | Blind source separation | Finds statistically independent components | Reveals hidden factors, reduces redundancy | Assumes independence, sensitive to pre-processing | Separating malware from benign activities |
| t-SNE | Non-linear dimensionality reduction | Preserves local neighbourhood structure in low dimensions | Good for visualization, capture non-linear patterns | Computationally expensive, stochastic results | Visualizing ransomware family clusters |
| UMAP | Uniform manifold approximation | Preserves both local and global structure | Fater than t-SNE, better global structure preservation | Hyperparameter sensitive | High-dimensional behavioural embeddings |
| Autoencoders | Neural dimensionality reduction | Learns compressed representation through | Non-linear, end-to-end learning flexible architecture | Requires large datasets, overfitting risk | Complex behavioural pattern compression |
| Algorithm | Purpose | Implementation Details | Advantage | Limitation | Best Use Case |
| One-Hot Encoding | Binary representation of categories | Creates binary column for each category | Simple, interpretable, no ordinality assumptions | High dimensionality, sparse matrices | API function names, file extensions |
| Label encoding | Map categories to integers | Assigns unique integer to each category | Memory efficient, simple implementation | Implies false ordinality | Ordinal categorical features |
| Target encoding | Encode based on target statistics | Replaces categories with target-related statistics | Captures category-target relationship | Prone to overfitting, requires regularization | Malware family encoding |
| Hash encoding | Map categories to hash values | Uses hash function to map to fixed-size space | Handles high cardinality, memory efficient | Hash collisions, information loss | Registry keys, file paths |
| Embedding layers | Neural categorical representation | Learns dense vector representation for categories | Captures semantic relationships, trainable | Requires neural network, needs training data | Similar API functions, malware variants |
| Algorithm | Purpose | Implementation Details | Advantage | Limitations | Best Use Case |
| Padding/Truncation | Standardize sequence lengths | Pad short sequences, truncate long ones | Simple implementation, fixed input size | Information loss, introduces bias | API call sequences, system events |
| Sliding window | Extract fixed size subsequence | Creates overlapping windows from sequences | Preserves temporal information, increase samples | Correlated samples, memory overhead | Time-series behavioural analysis |
| Sequence aggregation | Statistical summaries of sequences | Compute statistics (mean, max, etc) over sequences | Reduces dimensionality, stable features | Loses sequential information | Converting dynamic traces to features |
| Recurrent Preprocessing | Prepare for RNN/LSTM input | Format sequences for recurrent neural networks | Maintains temporal dependencies, flexible length | Requires sequential models | Temporal behavioural modelling |
| N-gram Extraction | Extract subsequence patterns | Creates features from sequence n-gram | Captures local patterns, interpretable | Exponential feature growth, sparse | System call patterns, API sequences |
| Algorithm | Purpose | Implementation Details | Advantages | Limitations | Best Use Case |
| Box-Cox Transform | Stabilize variance and normalise | Handles skewed data, stabilises variance | Requires positive data, parameter selection | Execution times, memory allocations | |
| Yeo-Johnson Transform | Handle positive and negative data | Extended Box-Cox for any real numbers | Works with negative values, flexible | More complex than Box-Cox | Network traffic volumes |
| Log Transform | Reduce right skewness | Simple, interpretable, reduces skewness | Only for positive data, zero handling | File size, API call frequencies | |
| Square Root Transform | Mild variance stabilisation | Less aggressive than log, handles zeros | Limited effectiveness for high skewness | Count-based features | |
| Polynomial Features | Create interaction terms | Generate polynomial combinations of features | Captures feature interactions. Simple | Exponential feature growth, overfitting | Non-linear relationships in behaviour |
| Algorithm | Purpose | Implementation Details | Advantages | Limitations | Best Case Use |
| Gaussian Filter | Smooth continuous signals | Convolves with Gaussian Kernel | Smooth results, parameter control | May blur important details | Time-series smoothing |
| Median Filter | Remove impulse noise | Replaces values with local median | Preserves edges, robust to outliers | May remove sharp legitimate changes | Filtering execution spikes |
| Kalman Filter | Optimal state estimation | Recursive estimation with uncertainty modelling | Optimal for linear systems, and handles uncertainty | Requires system model, linear assumptions | Tracking system state changes |
| Savitzky-Golay Filter | Polynomial smoothing | Fits local polynomials for smoothing | Preserves features, flexible | Requires parameter tuning | Smoothing behavioural time series |
| Wavelet Denoising | Multi-scale noise removal | Decomposes signal, removes noise components | Multi-resolution, adaptive | Complex implementation, parameter selection | Complex behavioural signals |
| Algorithm | Purpose | Implementation Details | Advantages | Limitations | Best of Use |
| Mutual Information | Information-theoretic selection | Measures information shared between feature and target | Non-parametric, captures non-linear relationships | Computationally expensive, discrete approximation | Selecting predictive behavioural features |
| Chi-Square Test | Statistical independence test | Tests independency between categorial features and target | Simple interpretable, and fast | Only for categorial features | Binary behavioural indicators |
| Recursive Feature Elimination | Iterative feature removal | Removes features based on model importance | Model-agnostic considers feature interactions | Computationally expensive, wrapper method | Optimizing feature subset size |
| LASSO regularization | L1 penalty for sparsity | Adds penalty to force feature weights to zero | Automatic feature selection, regularization | May select arbitrary features from correlated groups | Sparse model requirements |
| Variance Threshold | Remove low-variance features | Eliminate features below variance threshold | Simple, fast, removes constants | Ignores relationship with target | Removing constant behavioural indicators |
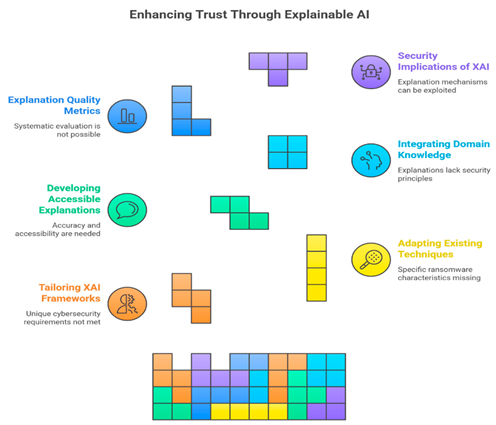
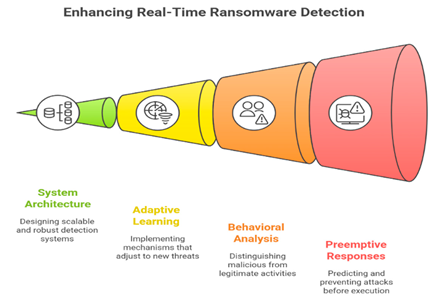
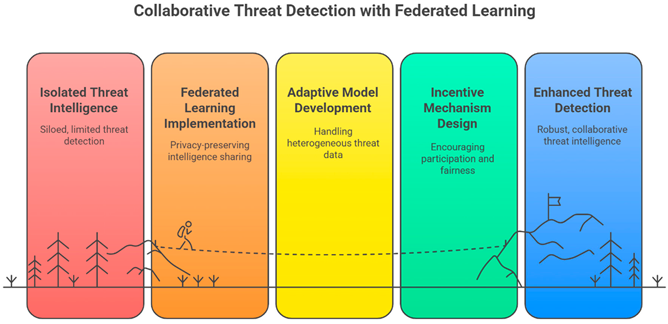
IV. Challenges and Limitations in Existing Literature and Future Research Directions
V. Conclusion
Author Contributions
Funding
Conflicts of Interest
References
- Alzahrani, B.; Alshamrani, S.; Alghamdi, A. AI-Based Ransomware Detection: A Comprehensive Review. Charles Sturt University Research Output. 2023. Available online: https://researchoutput.csu.edu.au/files/544062743/532572193_Published_article.pdf.
- Kim, J.; Park, S.; Lee, H. Ransomware Detection with Machine Learning: Techniques, Challenges, and Future Directions. Journal of Information Security and Intelligent Systems 2025, 1, 17. Available online: https://jisis.org/wp-content/uploads/2025/04/2025.I1.017.pdf.
- Singh, A.; Sharma, R.; Kumar, V. Ransomware Detection Using Machine Learning: A Review, Research Challenges and Future Directions. IEEE Xplore. 2024. Available online: https://ieeexplore.ieee.org/document/10521643.
- Alraizza, A.; Algarni, A. Ransomware Detection Using Machine Learning: A Survey. Big Data Cogn Comput. 2023, 7, 143. Available online: https://www.mdpi.com/2504-2289/7/3/143. [CrossRef]
- Patel, H.; Mehta, P. Machine Learning Approaches to Ransomware Detection: A Comprehensive Review. International Information and Engineering Technology Association. 2023. Available online: https://iieta.org/download/file/fid/153100.
- Vinayakumar, R.; Alazab, M.; Soman, K.P.; Poornachandran, P.; Al-Nemrat, A.; Venkatraman, S. Deep learning approach for intelligent intrusion detection system. IEEE Access. 2019, 7, 41525–50. Available online: https://ieeexplore.ieee.org/document/8681044. [CrossRef]
- Harzie, R.E.; Selamat, A.; Fujita, H.; Krejcar, O.; Do, N.Q. Enhancing Ransomware Detection Using Deep Learning Models. In Advances and Trends in Artificial Intelligence. Theory and Applications. Lecture Notes in Computer Science; Springer, 2025; pp. 403–414. Available online: https://link.springer.com/chapter/10.1007/978-981-96-8892-0_34.
- Ransomware Detection: Challenges and Techniques. In Proceedings of the 2025 IEEE Conference on Computing, Informatics, and Cybersecurity Technologies (CCICT), 2025; IEEE; pp. 319–324. Available online: https://www.computer.org/csdl/proceedings-article/ccict/2025/113500a319/28KfgQ6t5a8.
- Alzahrani, B.; Alshamrani, S.; Alghamdi, A. Understanding and Mitigating Ransomware Threats: Trends, Techniques, and Countermeasures. 2025 IEEE International Conference on Cybersecurity and Resilience (CyberRes); Available online: https://ieeexplore.ieee.org/document/10585140.
- Gómez Hernández, J.A.; García Teodoro, P.; Magán Carrión, R.; Rodríguez Gómez, R. Crypto-Ransomware: A Revision of the State of the Art, Advances and Challenges. Electronics 2023, 12, 4494. Available online: https://www.mdpi.com/2079-9292/12/21/4494. [CrossRef]
- Arnone, G.; Scire’, G.; Bivona, E. The (mis)use of cryptocurrencies by criminal organizations: a systematic literature review. Digital Finance. 2025. Available online: https://link.springer.com/article/10.1007/s42521-025-00148-1.
- Rawindaran, N.; Jayal, A.; Prakash, E. Exploration of the Impact of Cybersecurity Awareness on Small and Medium Enterprises (SMEs) in Wales Using Intelligent Software to Combat Cybercrime. Computers 2022, 11, 174. Available online: https://www.mdpi.com/2073-431X/11/12/174. [CrossRef]
- Gómez Hernández, J.A.; García Teodoro, P.; Magán Carrión, R.; Rodríguez Gómez, R. Ransomware Anti-Analysis and Evasion Techniques: A Survey and Research Directions. 2021 IEEE International Conference on Cyber Security and Protection of Digital Services (Cyber Security); Available online: https://ieeexplore.ieee.org/document/9392529.
- Alzahrani, B.; Alshamrani, S.; Alghamdi, A. A Survey of Ransomware as a Service (RaaS) and Methods to Mitigate the Threat. 2022 IEEE International Conference on Cybersecurity and Resilience (CyberRes); Available online: https://ieeexplore.ieee.org/document/9719456.
- Maratsi, M.I.; Popov, O.; Alexopoulos, C.; Charalabidis, Y. Ethical and Legal Aspects of Digital Forensics Algorithms: The Case of Digital Evidence Acquisition. In ICEGOV 2022: 15th International Conference on Theory and Practice of Electronic Governance; ACM, 2022; Available online: https://dl.acm.org/doi/fullHtml/10.1145/3560107.3560114.
- Enomoto, S.; Kuzuno, H.; Yamada, H.; Shiraishi, Y.; Morii, M. Early mitigation of CPU-optimized ransomware using monitoring encryption instructions. Int J Inf Secur. 2024, 23, 3393–3413. Available online: https://link.springer.com/article/10.1007/s10207-024-00892-2. [CrossRef]
- Butt, U.; Dauda, Y.; Shaheer, B. Ransomware Attack on the Educational Sector. In AI, Blockchain and Self-Sovereign Identity in Higher Education; Springer, 2023; pp. 279–313. Available online: https://link.springer.com/chapter/10.1007/978-3-031-33627-0_11.
- Iwasaki, M. Banning ransomware payments: unintended effects on cybersecurity investment and incident reporting. Int Cybersecurity Law Rev. 2025, 6, 17–27. Available online: https://link.springer.com/article/10.1365/s43439-025-00137-5. [CrossRef]
- Halikias, H. Business Impacts of Ransomware. In Digital Shakedown; Springer, 2024; pp. 25–47. Available online: https://link.springer.com/chapter/10.1007/978-3-031-65438-1_3.
- Warren, D.F.; Komninos, N.; Chen, T. A Study on the Evolution of Ransomware Detection Using Machine Learning and Deep Learning Techniques. IoT 2020, 1, 551–604. Available online: https://www.mdpi.com/2624-831X/1/2/30. [CrossRef]
- Ciaramella, G.; Iadarola, G.; Martinelli, F.; Mercaldo, F.; Santone, A. Explainable Ransomware Detection with Deep Learning Techniques. J Comput Virol Hack Tech. 2024, 20, 317–330. Available online: https://link.springer.com/article/10.1007/s11416-023-00501-1. [CrossRef]
- Urooj, U.; Al-rimy, B.A.S.; Zainal, A.; Ghaleb, F.A.; Rassam, M.A. Ransomware Detection Using the Dynamic Analysis and Machine Learning: A Survey and Research Directions. Appl Sci. 2022, 12, 172. Available online: https://www.mdpi.com/2076-3417/12/1/172. [CrossRef]
- Singh, A.; Mushtaq, Z.; Abosaq, H.A.; Mursal, S.N.F.; Irfan, M.; Nowakowski, G. Enhancing Ransomware Attack Detection Using Transfer Learning and Deep Learning Ensemble Models on Cloud-Encrypted Data. Electronics 2023, 12, 3899. Available online: https://www.mdpi.com/2079-9292/12/18/3899. [CrossRef]
- Pelekis, S.; Koutroubas, T.; Blika, A.; Berdelis, A.; Karakolis, E.; Ntanos, C.; Spiliotis, E.; Askounis, D. Adversarial Machine Learning: A Review of Methods, Tools, and Critical Industry Sectors. Artif Intell Rev. 2025, 58, 226. Available online: https://link.springer.com/article/10.1007/s10462-025-11147-4. [CrossRef]
- McCarthy, A.; Ghadafi, E.; Andriotis, P.; Legg, P. Functionality-Preserving Adversarial Machine Learning for Robust Classification in Cybersecurity and Intrusion Detection Domains: A Survey. J Cybersecur Priv. 2022, 2, 154–190. Available online: https://www.mdpi.com/2624-800X/2/1/10. [CrossRef]
- Fernando, D.; Komninos, N.; Chen, T. Comparative Study of CNN and RNN for Deep Learning Based Intrusion Detection System. In Cloud Computing and Security; Springer, 2018; pp. 159–170. Available online: https://link.springer.com/chapter/10.1007/978-3-030-00018-9_15.
- Sharmeen, N.; Islam, S.; Rahman, M.M.; Hossain, M.S. Comparative Analysis of Machine Learning and Deep Learning Models for Ransomware Detection. In Proceedings of Fifth International Conference on Computer and Communication Technologies (IC3T 2023); Springer, 2024; pp. 253–266. Available online: https://link.springer.com/chapter/10.1007/978-981-99-9707-7_24.
- Rhode, M.; Burnap, P.; Jones, K. Early-stage malware prediction using recurrent neural networks Early-stage malware prediction using recurrent neural networks - ScienceDirect. Comput Secur. Available from. 2018, 77, 578–94. [Google Scholar] [CrossRef]
- Homayoun, S.; Dehghantanha, A.; Ahmadzadeh, M.; Hashemi, S.; Khayami, R.; Homayoun, S.; Dehghantanha, A.; Ahmadzadeh, M.; Hashemi, S.; Khayami, R.; Know abnormal; find evil: frequent pattern mining for ransomware threat hunting and intelligence. IEEE Trans Emerg Topics Comput. 2020;8(2):341-51. Available from: Homayoun, S., Dehghantanha, A., Ahmadzadeh, M., Hashemi, S. and Khayami, R. (2020). Know Abnormal, Find Evil Frequent Pattern Mining for Ransomware Threat Hunting and Intelligence. IEEE;IEEE Transactions on Emerging Topics in Computting Available from. 2020, 8, 341–51 341-351, - References - Scientific Research Publishing. [Google Scholar] [CrossRef]
- Zhang, Y.; Zhang, Y.; Li, Y.; Wang, Y. Ransomware Detection Using Machine Learning Algorithms. 2025 IEEE International Conference on Cybersecurity and Resilience (CyberRes); Available online: https://xplorestaging.ieee.org/document/10652659.
- Baldwin, J.; Dehghantanha, A. Leveraging Support Vector Machine for Opcode Density Based Detection of Crypto-Ransomware. In Cyber Threat Intelligence; Springer, 2018; pp. 107–136. Available online: https://link.springer.com/chapter/10.1007/978-3-319-73951-9_6.
- Panda, S.; Sahu, S.; Jena, P.; Chattopadhyay, S. Comparing Fuzzy-C Means and K-Means Clustering Techniques: A Comprehensive Study. In Advances in Computer Science, Engineering & Applications; Springer, 2012; pp. 451–460. Available online: https://link.springer.com/chapter/10.1007/978-3-642-30157-5_45.
- Hussain, I.; Sinaga, K.P.; Yang, M.S. Unsupervised Multiview Fuzzy C-Means Clustering Algorithm. Electronics 2023, 12, 4467. Available online: https://www.mdpi.com/2079-9292/12/21/4467. [CrossRef]
- Sharma, P.; Chaudhary, K. An Advanced Comparative Study of Ransomware Anomaly Detection Techniques Through Optimized Hyperparameters. In Artificial Intelligence and Sustainable Computing; Springer, 2024; pp. 379–393. Available online: https://link.springer.com/chapter/10.1007/978-981-97-0327-2_28.
- Sharmeen, N.; Islam, S.; Rahman, M.M.; Hossain, M.S. Deep Learning Approaches for Ransomware Detection: Assessing CNN and Traditional Classifiers. J Neural Inf Process Tech. 2020, 2, 112–124. Available online: https://ieeexplore.ieee.org/document/10760450.
- Roy, S.; Biswas, S.; Sinha, S.; Ghosh, S. DeepRan: Attention-based BiLSTM and CRF for Ransomware Early Detection. J Organ Comput Electron Commer. 2021, 31, 265–284. Available online: https://link.springer.com/article/10.1007/s10796-020-10017-4. [CrossRef]
- Almomani, A.; Alshamrani, S.; Alghamdi, A. Transfer Learning for Ransomware Detection Using Pre-trained CNN Architectures. Appl Sci. 2023, 13, 5167. Available online: https://www.mdpi.com/2076-3417/13/8/5167.
- Poudyal, S.; Dasgupta, D. Opcode Sequence Analysis for Ransomware Detection Using TF-IDF and SVM. J Cybersecurity and Privacy 2021, 1, 231–248. Available online: https://www.mdpi.com/2624-800X/1/2/14.
- Alqahtani, A.; Alshamrani, S.; Alghamdi, A. A Novel Approach for Ransomware Detection Based on PE Header Using Machine Learning. J Comput Virol Hack Tech. 2021, 17, 321–336. Available online: https://link.springer.com/article/10.1007/s11416-021-00414-x.
- Lee, K.; Lee, J.; Lee, S.-Y.; Yim, K. Effective Ransomware Detection Using Entropy Estimation of Files for Cloud Services. Sensors 2023, 23, 3023. Available online: https://www.mdpi.com/1424-8220/23/6/3023. [CrossRef] [PubMed]
- Davidian, M.; Kiperberg, M.; Vanetik, N. Early Ransomware Detection with Deep Learning Models. Future Internet 2024, 16, 291. Available online: https://www.mdpi.com/1999-5903/16/8/291. [CrossRef]
- Shifa, M.S.; Hasan, M.; Hossain, M.J.; Tasin, T.I.; Sarker, M.R.; Islam, M. Ransomware Attacks and Detection Mechanisms: A Systematic Literature Review. In Cyber Intelligence and Information Retrieval; Springer, 2025; pp. 65–71. Available online: https://link.springer.com/chapter/10.1007/978-981-97-7603-0_7.
- Abdallah, M.; Le Khac, N.A.; Jahromi, H.; Jurcut, A.D. A Hybrid CNN-LSTM Based Approach for Anomaly Detection Systems in SDNs. ARES 2021, 16th International Conference on Availability, Reliability and Security, 2021; ACM. Available online: https://dl.acm.org/doi/fullHtml/10.1145/3465481.3469190.
- Song, S.; Kim, J.; Kim, I.; Hong, J.; Kang, B.B. Detecting code reuse attacks in software defined networking. 2017 IEEE Conference on Dependable and Secure Computing, 2017; IEEE; pp. 256–63. Available online: https://ieeexplore.ieee.org/document/8073518.
- Sgandurra, D.; Muñoz-González, L.; Mohsen, R.; Lupu, E.C. Automated dynamic analysis of ransomware: benefits, limitations and use for detection. arXiv. 2016. Available online: https://arxiv.org/abs/1609.03020.
- Alserhani, F.; Aljared, A. Evaluating Ensemble Learning Mechanisms for Predicting Advanced Cyber Attacks. Appl Sci. 2023, 13, 13310. Available online: https://www.mdpi.com/2076-3417/13/24/13310. [CrossRef]
- Hasan, M.; Rahman, M.A. Hybrid Static and Dynamic Analysis for Ransomware Detection: A Case Study on WannaCry. In Proceedings of the 2017 International Conference on Cyber Security and Protection of Digital Services (Cyber Security); IEEE, 2017; pp. 1–6. Available online: https://ieeexplore.ieee.org/document/8005461.
- Mercaldo, F.; Milosevic, J.; Martinelli, F. Extinguishing Ransomware: A Hybrid Approach to Android Ransomware Detection. In Foundations and Practice of Security; Springer, 2018; pp. 242–258. Available online: https://link.springer.com/chapter/10.1007/978-3-319-75650-9_16.
- Mehnaz, S.; Mudgerikar, A.; Bertino, E. RWGuard: A Real-Time Detection System Against Cryptographic Ransomware. In Research in Attacks, Intrusions, and Defenses; Springer, 2018; pp. 114–136. Available online: https://link.springer.com/chapter/10.1007/978-3-030-00470-5_6.
- Zuhair, H.; Selamat, A.; Krejcar, O. A Multi-Tier Streaming Analytics Model of 0-Day Ransomware Detection Using Machine Learning. Appl Sci. 2020, 10, 3210. Available online: https://www.mdpi.com/2076-3417/10/9/3210. [CrossRef]
- Azmoodeh, A.; Dehghantanha, A.; Choo, K.K.R. Robust malware detection for internet of (battlefield) things devices using deep eigenspace learning. IEEE Trans Sustain Comput.;Robust Malware Detection for Internet of (Battlefield) Things Devices Using Deep Eigenspace Learning | IEEE Journals & Magazine | IEEE Xplore Available from. 2019, 4, 88–95. [Google Scholar]
- Vinayakumar, R.; Soman, K.P.; Poornachandran, P. Evaluation of recurrent neural network and its variants for intrusion detection system (IDS). Int J Inf Secur. 2017, 17, 43–63. [Google Scholar] [CrossRef]
- Nataraj, L.; Karthikeyan, S.; Jacob, G.; Manjunath, B.S. Malware images: visualization and automatic classification. In Proceedings of the 8th International Symposium on Visualization for Cyber Security, 2011; ACM; pp. 1–7. Available online: https://dl.acm.org/doi/10.1145/2016904.2016908.
- Ravi Kumar, P.; Ramlie, H.R.E. Anatomy of Ransomware: Attack Stages, Patterns and Handling Techniques. In Computational Intelligence in Information Systems; Springer, 2021; pp. 205–214. Available online: https://link.springer.com/chapter/10.1007/978-3-030-68133-3_20.
- Hampton, N.; Baig, Z.; Zeadally, S. Ransomware behavioural analysis on Windows platforms Ransomware behavioural analysis on windows platforms - ScienceDirect. J Inf Secur Appl. Available from. 2018, 40, 44–51. [Google Scholar]
- Rehman, M.; Akbar, R.; Omar, M.; Gilal, A.R. A Systematic Literature Review of Ransomware Detection Methods and Tools for Mitigating Potential Attacks. In Computing and Informatics (ICOCI 2023); Springer, 2024; pp. 80–95. Available online: https://link.springer.com/chapter/10.1007/978-981-99-9589-9_7.
- Ryan, M. Ransomware Revolution: The Rise of a Prodigious Cyber Threat. In Advances in Information Security; Springer, 2021; Available online: https://link.springer.com/book/10.1007/978-3-030-66583-8.
- Khammas, B.M. Ransomware detection using random forest technique. ICT Express Available from: Ransomware Detection using Random Forest Technique - ScienceDirect. 2020, 6, 325–31. [Google Scholar] [CrossRef]
- Afianian, A.; Niksefat, S.; Sadeghiyan, B.; Baptiste, D. Malware dynamic analysis evasion techniques: a survey. ACM Comput Surv. 2019, 52, 1–28. Available online: https://dl.acm.org/doi/10.1145/3365001. [CrossRef]
- Cabaj, K.; Gawkowski, P.; Grochowski, K.; Osojca, D. Network activity analysis of CryptoWall ransomware. Przeglad Elektrotechniczny Available from. 2015, 91, 201–4, (PDF) Network activity analysis of CryptoWall ransomware. [Google Scholar] [CrossRef]
- Chen, M.; Ji, T.; Li, S.; Zhang, Y.; Wang, T.; Mao, K.; Sun, Y. A Double-Shell Structured Ransomware Defense Method Tailored for the RaaS Model. In Cyberspace Simulation and Evaluation; Springer, 2025; pp. 361–376. Available online: https://link.springer.com/chapter/10.1007/978-981-96-4503-9_24.
- Djenna, A.; Belaoued, M.; Lifa, N. Top Cyber Threats: The Rise of Ransomware. In Information Security Theory and Practice; Springer, 2024; pp. 80–95. Available online: https://link.springer.com/chapter/10.1007/978-3-031-60391-4_6.
- Kerns, Q.; Payne, B.; Abegaz, T. Double-Extortion Ransomware: A Technical Analysis of Maze Ransomware. In Future Technologies Conference (FTC) 2021; Springer, 2021; Volume 3, pp. 82–94. Available online: https://link.springer.com/chapter/10.1007/978-3-030-89912-7_7.
- Algarni, S. Cybersecurity Attacks: Analysis of “WannaCry” Attack and Proposing Methods for Reducing or Preventing Such Attacks in Future. In ICT Systems and Sustainability; Springer, 2020; pp. 763–770. Available online: https://link.springer.com/chapter/10.1007/978-981-15-8289-9_73.
- MacRae, J.; Franqueira, V.N.L. On Locky Ransomware, Al Capone and Brexit. In Digital Forensics and Cyber Crime; Springer, 2018; pp. 33–45. Available online: https://link.springer.com/chapter/10.1007/978-3-319-73697-6_3.
- Ehrenfeld, J.M. WannaCry, Cybersecurity and Health Information Technology: A Time to Act. J Med Syst. 2017, 41(104). Available online: https://link.springer.com/article/10.1007/s10916-017-0752-1. [CrossRef] [PubMed]
- Pham, P.-H.; Dang, L.X.; Do, Q.N.; Hoang, C.N.; Nguyen, L.V. EternalBlue Exploit: Definitions and Working Mechanism. In Trends in Sustainable Computing and Machine Intelligence (ICTSM 2024); Springer, 2025; pp. 1–13. Available online: https://link.springer.com/chapter/10.1007/978-981-96-1452-3_1.
- Liu, Z.; Chen, C.; Zhang, L.Y.; Gao, S. Working Mechanism of EternalBlue and Its Application in Ransomworm. In Cyberspace Safety and Security (CSS 2022); Springer, 2022; pp. 178–191. Available online: https://link.springer.com/chapter/10.1007/978-3-031-18067-5_13.
- McDonald, G.; Papadopoulos, P.; Pitropakis, N.; Ahmad, J.; Buchanan, W.J. Ransomware: Analysing the Impact on Windows Active Directory Domain Services. Sensors 2022, 22, 953. Available online: https://www.mdpi.com/1424-8220/22/3/953. [CrossRef] [PubMed]
- Kharraz, A.; Robertson, W.; Balzarotti, D.; Bilge, L.; Kirda, E. Cutting the Gordian Knot: A Look Under the Hood of Ransomware Attacks. In Detection of Intrusions and Malware, and Vulnerability Assessment (DIMVA 2015); Springer, 2015; pp. 3–24. Available online: https://link.springer.com/chapter/10.1007/978-3-319-20550-2_1.
- Kok, S.H.; Abdullah, A.; Jhanjhi, N.Z.; Supramaniam, M. Prevention of Crypto-Ransomware Using a Pre-Encryption Detection Algorithm. Computers 2019, 8, 79. Available online: https://www.mdpi.com/2073-431X/8/4/79. [CrossRef]
- Yaqoub, S.A.F. What Petya/NotPetya Ransomware Is and What Its Remediations Are. In Information Technology - New Generations; Springer, 2018; pp. 93–100. Available online: https://link.springer.com/chapter/10.1007/978-3-319-77028-4_15.
- Continella, A.; Guagnelli, A.; Zingaro, G.; De Pasquale, G.; Barenghi, A.; Zanero, S.; Maggi, F. ShieldFS: a self-healing, ransomware-aware filesystem. In Proceedings of the 32nd Annual Conference on Computer Security Applications. ACM, 2016; pp. 336–47. Available online: https://dl.acm.org/doi/10.1145/2991079.2991110.
- Cabaj, K.; Mazurczyk, W. Using software-defined networking for ransomware mitigation: the case of CryptoWall. IEEE Netw.;Using Software-Defined Networking for Ransomware Mitigation: The Case of CryptoWall | IEEE Journals & Magazine | IEEE Xplore Available from. 2016, 30, 14–20. [Google Scholar]
- Kirubavathi, G.; Regis Anne, W.; Sridevi, U.K. A Recent Review of Ransomware Attacks on Healthcare Industries. Int J Syst Assur Eng Manag. 2024, 15, 5078–5096. Available online: https://link.springer.com/article/10.1007/s13198-024-02496-4. [CrossRef]
- Möller, D.P.F. Ransomware Attacks and Scenarios: Cost Factors and Loss of Reputation. In Guide to Cybersecurity in Digital Transformation; Springer, 2023; pp. 273–303. Available online: https://link.springer.com/chapter/10.1007/978-3-031-26845-8_6.
- Mbol, F.; Robert, J.M.; Sadighian, A. An efficient approach to detect torrent locker ransomware in computer systems. In Cryptology and Network Security; Springer, 2016; pp. 532–41. Available online: https://link.springer.com/chapter/10.1007/978-3-319-48965-0_32.
- Marion, J.Y. Ransomware: Extortion Is My Business. Commun ACM. 24 Apr 2025. Available online: https://cacm.acm.org/research/ransomware-extortion-is-my-business.
- Scaife, N.; Carter, H.; Traynor, P.; Butler, K.R.B. CryptoLock (and drop it): stopping ransomware attacks on user data. 2016 IEEE 36th International Conference on Distributed Computing Systems (ICDCS), 2016; IEEE; pp. 303–12. Available online: https://ieeexplore.ieee.org/document/7536540.
- Mercaldo, F. A Framework for Supporting Ransomware Detection and Prevention Based on Hybrid Analysis. J Comput Virol Hack Tech. 2021, 17, 221–227. Available online: https://link.springer.com/article/10.1007/s11416-021-00388-w. [CrossRef]
- Kharaz, A.; Arshad, S.; Mulliner, C.; Robertson, W.; Kirda, E. UNVEIL: a large-scale, automated approach to detecting ransomware. 25th USENIX Security Symposium. USENIX, 2016; pp. 757–72. Available online: https://www.usenix.org/conference/usenixsecurity16/technical-sessions/presentation/kharaz.
- Kolodenker, E.; Koch, W.; Stringhini, G.; Egele, M. PayBreak: defense against cryptographic ransomware. In Proceedings of the 2017 ACM on Asia Conference on Computer and Communications Security, 2017; ACM; pp. 599–611. Available online: https://dl.acm.org/doi/10.1145/3052973.3053035.
- Park, S.; Lee, M.; Na, S.; Lim, J. Destructive Malwares on MITRE ATT&CK Tactics for Cyber Warfare: A Brief Survey and Analysis. In Mobile Internet Security (MobiSec 2023); Springer, 2024; pp. 260–270. Available online: https://link.springer.com/chapter/10.1007/978-981-97-4465-7_19.
- Branescu, I.; Grigorescu, O.; Dascalu, M. Automated Mapping of Common Vulnerabilities and Exposures to MITRE ATT&CK Tactics. Information 2024, 15, 214. Available online: https://www.mdpi.com/2078-2489/15/4/214. [CrossRef]
- Kuppa, A.; Aouad, L.; Le-Khac, N.A. Linking CVEs to MITRE ATT&CK Techniques. In ARES 2021: 16th International Conference on Availability, Reliability and Security; ACM, 2021; Available online: https://dl.acm.org/doi/fullHtml/10.1145/3465481.3465758.
- Xiong, W.; Legrand, E.; Åberg, O.; Lagerström, R. Cybersecurity Threat Modeling Based on the MITRE Enterprise ATT&CK Matrix. Softw Syst Model. 2022, 21, 157–177. Available online: https://link.springer.com/article/10.1007/s10270-021-00898-7.
- Georgiadou, A.; Mouzakitis, S.; Askounis, D. Assessing MITRE ATT&CK Risk Using a Cyber-Security Culture Framework. Sensors 2021, 21, 3267. Available online: https://www.mdpi.com/1424-8220/21/9/3267.
- Moussaileb, R.; Cuppens, N.; Lanet, J.L.; Le Bouder, H. Ransomware Network Traffic Analysis for Pre-encryption Alert. In Foundations and Practice of Security (FPS 2019); Springer, 2020; pp. 20–38. Available online: https://link.springer.com/chapter/10.1007/978-3-030-45371-8_2.
- Cusack, G.; Michel, O.; Keller, E. Machine learning-based detection of ransomware using SDN. In Proceedings of the 2018 ACM International Workshop on Security in Software Defined Networks & Network Function Virtualization, 2018; ACM; pp. 1–6. Available online: https://dl.acm.org/doi/10.1145/3180465.3180467.
- Alqahtani, A.; Sheldon, F.T. A Survey of Crypto Ransomware Attack Detection Methodologies: An Evolving Outlook. Sensors 2022, 22, 1837. Available online: https://www.mdpi.com/1424-8220/22/5/1837. [CrossRef] [PubMed]
- Shuai, Y.; Zhang, Y.; Li, Y.; Li, J. Mitigation of Privilege Escalation Attack Using Kernel Data Relocation Mechanism. Int J Inf Secur 2024, 23. Available online: https://link.springer.com/content/pdf/10.1007/s10207-024-00890-4.pdf.
- Sheen, S.; Anitha, R.; Natarajan, V. Android based malware detection using a multifeature collaborative decision fusion approach Android based malware detection using a multifeature collaborative decision fusion approach - ScienceDirect. Neurocomputing Available from. 2018, 151, 905–12. [Google Scholar] [CrossRef]
- Mundt, M.; Baier, H. Enhancing Incident Management by an Improved Understanding of Data Exfiltration: Definition, Evaluation, Review. In Digital Forensics and Cyber Crime (ICDF2C 2023); Springer, 2024; pp. 33–57. Available online: https://link.springer.com/chapter/10.1007/978-3-031-56580-9_3.
- Monika, M.S.; Zavarsky, P.; Lindskog, D. Experimental study of ransomware on Windows and Android platforms. Procedia Comput Sci. 2018, 94, 465–72. Available online: https://www.sciencedirect.com/science/article/pii/S1877050916306032. [CrossRef]
- Fatima, S.; Rehman, T.; Fatima, M.; Khan, S.; Ali, M.A. Comparative Analysis of AES and RSA Algorithms for Data Security in Cloud Computing. Eng Proc. 2022, 20, 14. Available online: https://www.mdpi.com/2673-4591/20/1/14.
- Zimba, A.; Wang, Z.; Chen, H. Multi-stage crypto ransomware attacks: a new emerging cyber threat to critical infrastructure and industrial control systems Multi-stage crypto ransomware attacks: A new emerging cyber threat to critical infrastructure and industrial control systems - ScienceDirect. ICT Express Available from. 2018, 4, 14–18. [Google Scholar]
- Chen, Q.; Bridges, R.A. Automated behavioral analysis of malware: a case study of WannaCry ransomware. 2017 16th IEEE International Conference on Machine Learning and Applications (ICMLA), 2017; IEEE; pp. 454–60. Available online: https://ieeexplore.ieee.org/document/8260772.
- Morato, D.; Berrueta, E.; Magaña, E.; Izal, M. Ransomware early detection by the analysis of file sharing traffic Ransomware early detection by the analysis of file sharing traffic - ScienceDirect. J Netw Comput Appl. Available from. 2018, 124, 14–32. [Google Scholar] [CrossRef]
- Ahmed, Y.A.; Huda, S.; Al-rimy, B.A.S.; Alharbi, N.; Saeed, F.; Ghaleb, F.A.; Ali, I.M. A weighted minimum redundancy maximum relevance technique for ransomware early detection in industrial IoT. Sustainability 2022, 14, 1231. Available online: https://www.mdpi.com/2071-1050/14/3/1231. [CrossRef]
- Lee, Y.; Lee, J.; Ryu, D.; Park, H.; Shin, D. Clop Ransomware in Action: A Comprehensive Analysis of Its Multi-Stage Tactics. Electronics 2023, 13, 3689. Available online: https://www.mdpi.com/2079-9292/13/18/3689. [CrossRef]
- Hwang, J.; Kim, J.; Lee, S.; Kim, K. Two-stage ransomware detection using dynamic analysis and machine learning techniques. Wirel Pers Commun. 2020, 112, 2597–609. Available online: https://link.springer.com/article/10.1007/s11277-020-07166-9. [CrossRef]
- Alhawi, O.M.K.; Baldwin, J.; Dehghantanha, A. Leveraging machine learning techniques for Windows ransomware network traffic detection. In Cyber Threat Intelligence; Springer, 2018; pp. 93–106. Available online: https://link.springer.com/chapter/10.1007/978-3-319-73951-9_5.
- Australian Signals Directorate. ASD Cyber Threat Report 2022–23. Cyber.gov.au. 14 Nov 2023. Available online: https://www.cyber.gov.au/sites/default/files/2023-11/asd-cyber-threat-report-2023.pdf.
- Jiang, T.; Gradus, J.L.; Rosellini, A.J. Supervised Machine Learning: A Brief Primer. Behav Ther. Available from. 2020, 51, 675–687. [Google Scholar] [CrossRef] [PubMed] [PubMed Central]
- Greubel, A.; Andres, D.; Hennecke, M. Analyzing Reporting on Ransomware Incidents: A Case Study. Soc Sci. 2023, 12, 265. Available online: https://www.mdpi.com/2076-0760/12/5/265. [CrossRef]
- Dhiman, P.; Saini, N.; Gulzar, Y.; Turaev, S.; Kaur, A.; Nisa, K.U.; Hamid, Y. A Review and Comparative Analysis of Relevant Approaches of Zero Trust Network Model. Sensors 2024, 24, 1328. Available online: https://www.mdpi.com/1424-8220/24/4/1328. [CrossRef] [PubMed]
- Booshan, P.; Armoogum, S.; Li, X. An Adaptive Security Architecture for Detecting Ransomware Attack Using Open Source Software. In Advances in Information and Communication (FICC 2020); Springer, 2020; pp. 618–633. Available online: https://link.springer.com/chapter/10.1007/978-3-030-39445-5_45.
- Herrera-Silva, J.A.; Hernández-Álvarez, M. Dynamic Feature Dataset for Ransomware Detection Using Machine Learning Algorithms. Sensors 2023, 23, 1053. Available online: https://www.mdpi.com/1424-8220/23/3/1053. [CrossRef]
- Vinayakumar, R.; Alazab, M.; Jolfaei, A.; Soman, K.P.; Poornachandran, P. Ransomware triage using deep learning: Twitter as a case study. 2019 Cybersecurity and Cyberforensics Conference (CCC) Ransomware triage using deep learning: Twitter as a case study - Research @ Flinders, Available from. 2019; IEEE; pp. 67–73. [Google Scholar]
- Zhang, J.; Chen, B.; Zhao, Y.; Cheng, X.; Hu, F. Data Security and Privacy-Preserving in Edge Computing Paradigm: Survey and Open Issues. in IEEE Access;Data Security and Privacy-Preserving in Edge Computing Paradigm: Survey and Open Issues | IEEE Journals & Magazine | IEEE Xplore Available from. 2018, vol. 6, 18209–18237. [Google Scholar] [CrossRef]
- Ouerdi, N.; Mejjout, B.; Laaroussi, K.; Kasmi, M.A. Ransomware Detection and Classification Using Machine Learning and Deep Learning. In Advances in Smart Medical, IoT & Artificial Intelligence (ICSMAI 2024); Springer, 2024; pp. 195–202. Available online: https://link.springer.com/chapter/10.1007/978-3-031-66850-0_22.
- Maiorca, D.; Mercaldo, F.; Giacinto, G.; Visaggio, C.A.; Martinelli, F. R-PackDroid: API package-based characterization and detection of mobile ransomware. In Proceedings of the Symposium on Applied Computing. ACM, 2017; pp. 1718–23. Available online: https://dl.acm.org/doi/10.1145/3019612.3019793.
- Andronio, N.; Zanero, S.; Maggi, F. HELDROID: dissecting and detecting mobile ransomware. In Research in Attacks, Intrusions, and Defenses; Springer, 2015; pp. 382–404. Available online: https://link.springer.com/chapter/10.1007/978-3-319-26362-5_18.
- Hussain, M.Z.; Hasan, M.Z.; Baig, M.M.; Khan, T.; Nosheen, S.; Bhatti, A.M.; Qureshi, A.M.; Siddiqui, A.A.; Mubarak, Z.; Chuhan, S.H.; Bilal, A.; Yaqub, M.A. Malware/Ransomware Analysis and Detection Using CIC-MalMem2022 Dataset. In Intelligent Sustainable Systems (WorldS4 2023); Springer, 2024; pp. 339–352. Available online: https://link.springer.com/chapter/10.1007/978-981-99-8031-4_30.
- Coglio, F.; Lekssays, A.; Carminati, B.; Ferrari, E. Early-Stage Ransomware Detection Based on Pre-Attack Internal API Calls. In Advanced Information Networking and Applications (AINA 2023); Springer, 2023; pp. 417–429. Available online: https://link.springer.com/chapter/10.1007/978-3-031-28451-9_36.
- Homayoun, S.; Dehghantanha, A.; Ahmadzadeh, M.; Hashemi, S.; Khayami, R. DRTHIS: deep ransomware threat hunting and intelligence system at the fog layer. Future Gener Comput Syst. Available from. 2019, 90, 94–104, DRTHIS: Deep ransomware threat hunting and intelligence system at the fog layer - ScienceDirect. [Google Scholar] [CrossRef]
- Taşcı, B. Deep-Learning-Based Approach for IoT Attack and Malware Detection. Appl Sci. 2024, 14, 8505. Available online: https://www.mdpi.com/2076-3417/14/18/8505. [CrossRef]
- Almobaideen, W.; Abu Alghanam, O.; Abdullah, M.; Hussain, S.B.; Alam, U. Comprehensive Review on Machine Learning and Deep Learning Techniques for Malware Detection in Android and IoT Devices. Int J Inf Secur. 2025, 24, 110. Available online: https://link.springer.com/article/10.1007/s10207-025-01027-x. [CrossRef]
- Anand, P.M.; Charan, P.V.; Chunduri, H.; Shukla, S.K. RTR-Shield: Early Detection of Ransomware Using Registry and Trap Files. In Information Security Practice and Experience (ISPEC 2023); Springer, 2023; pp. 209–229. Available online: https://link.springer.com/chapter/10.1007/978-981-99-7032-2_13.
- Davies, S.R.; Macfarlane, R.; Buchanan, W.J. Comparison of Entropy Calculation Methods for Ransomware Encrypted File Identification. Entropy 2022, 24, 1503. Available online: https://www.mdpi.com/1099-4300/24/10/1503. [CrossRef]
- Hashwanth, S.; Kirthica, S. Effective Ransomware Detection Method Using PE Header and YARA Rules. In Network Security and Blockchain Technology (ICNSBT 2023); Springer, 2023; pp. 185–194. Available online: https://link.springer.com/chapter/10.1007/978-981-99-4433-0_16.
- Ayub, M.A.; Siraj, A.; Filar, B.; Gupta, M. RWArmor: A Static-Informed Dynamic Analysis Approach for Early Detection of Cryptographic Windows Ransomware. Int J Inf Secur. 2024, 23, 533–556. Available online: https://link.springer.com/article/10.1007/s10207-023-00758-z. [CrossRef]
- Hull, G.; John, H.; Arief, B. Ransomware deployment methods and analysis: views from a predictive model and human responses. Crime Sci. 2019, 8, 2. Available online: https://crimesciencejournal.biomedcentral.com/articles/10.1186/s40163-019-0097-9. [CrossRef]
- Wan, Y.L.; Chang, J.C.; Chen, R.J.; Wang, S.J. Feature-selection-based ransomware detection with machine learning of data analysis. In Proceedings of the 2018 3rd International Conference on Computer and Communication Systems (ICCCS), Available from. 2018; IEEE; Feature-Selection-Based Ransomware Detection with Machine Learning of Data Analysis - National Yang Ming Chiao Tung University Academic Hub; pp. 392–6. [Google Scholar]
- Umara, U.; Zainal, A.; Al-Rimy, B.A.S.; Ghaleb, F.A.; Rassam, M.A. Static and Dynamic Analysis of Ransomware: Challenges and Future Directions. In Recent Advances in Cybersecurity; Springer, 2023; pp. 45–62. Available online: https://link.springer.com/chapter/10.1007/978-981-99-7032-2_4.
- Berrueta, E.; Morato, D.; Magaña, E.; Izal, M. A survey on detection techniques for cryptographic ransomware. IEEE Access. Available from: A Survey on Detection Techniques for Cryptographic Ransomware | IEEE Journals & Magazine | IEEE Xplore. 2019, 7, 144925–44. [Google Scholar] [CrossRef]
- Nieuwenhuizen, D. A behavioural-based approach to ransomware detection. In MWR Labs Whitepaper; Available from: [PDF] A behavioural-based approach to ransomware detection | Semantic Scholar; 2017. [Google Scholar]
- Moussaileb, R.; Bouget, B.; Palisse, A.; Le Bouder, H.; Cuppens, N.; Lanet, J.L. Ransomware's early mitigation mechanisms. In Proceedings of the 13th International Conference on Availability, Reliability and Security. ACM Ransomware's Early Mitigation Mechanisms | Proceedings of the 13th International Conference on Availability, Reliability and Security, Available from. 2018; pp. 1–10. [Google Scholar]
- Song, S.; Kim, B.; Lee, S. The effective ransomware prevention technique using process monitoring on Android platform. Mobile Inf Syst. 2016, 2016, 2946735. Available online: https://www.hindawi.com/journals/misy/2016/2946735/. [CrossRef]
- Shijo, P.V.; Salim, A. Integrated static and dynamic analysis for malware detection. Procedia Comput Sci. Available from. 2015, 46, 804–11, Integrated Static and Dynamic Analysis for Malware Detection - ScienceDirect. [Google Scholar] [CrossRef]
- Singla, A.; Bertino, E.; Verma, D. Preparing network intrusion detection deep learning models with minimal data using adversarial domain adaptation. In Proceedings of the 15th ACM Asia Conference on Computer and Communications Security. ACM, 2020; pp. 127–40. Available online: https://dl.acm.org/doi/10.1145/3320269.3384718.
- UUrooj, B.A.S.; Al-Rimy; Zainal, A. B.; Saeed, F.; Abdelmaboud, A.; Nagmeldin, W. Addressing Behavioral Drift in Ransomware Early Detection Through Weighted Generative Adversarial Networks. IEEE Access;Addressing Behavioral Drift in Ransomware Early Detection Through Weighted Generative Adversarial Networks | IEEE Journals & Magazine | IEEE Xplore Available from. 2024, vol. 12, 3910–3925. [Google Scholar] [CrossRef]
- Aboaoja, F.A.; Zainal, A.; Ghaleb, F.A.; Al-rimy, B.A.S.; Eisa, T.A.E.; Elnour, A.A.A. Malware detection issues, challenges, and future directions: a survey. Appl Sci. 2022, 12, 8482. Available online: https://www.mdpi.com/2076-3417/12/17/8482. [CrossRef]
- Maniath, S.; Ashok, A.; Poornachandran, P.; Sujadevi, V.G.; Sankar, A.U.P.; Jan, S. Deep learning LSTM based ransomware detection. In 2017 Recent Developments in Control, Automation & Power Engineering (RDCAPE); IEEE, 2017; pp. 442–6. Available online: https://ieeexplore.ieee.org/document/8358312.
- Zhang, H.; Xiao, X.; Mercaldo, F.; Ni, S.; Martinelli, F.; Sangaiah, A.K. Classification of ransomware families with machine learning based on N-gram of opcodes Classification of ransomware families with machine learning based onN-gram of opcodes - ScienceDirect. Future Gener Comput Syst. Available from. 2019, 90, 211–21. [Google Scholar] [CrossRef]
- Sivasubramanian, A.; Devisetty, M.; Bhavukam, P. Feature Extraction and Anomaly Detection Using Different Autoencoders for Modeling Intrusion Detection Systems. Arab J Sci Eng. 2024, 49, 13061–13073. Available online: https://link.springer.com/article/10.1007/s13369-024-08951-5. [CrossRef]
- Shaik, A.S.; Shaik, A. AI Enhanced Cyber Security Methods for Anomaly Detection. In Machine Intelligence, Tools, and Applications (ICMITA 2024); Springer, 2024; pp. 348–359. Available online: https://link.springer.com/chapter/10.1007/978-3-031-65392-6_30.
- Kok, S.; Azween, A.; Jhanjhi, N.Z. Evaluation metric for crypto-ransomware detection using machine learning Evaluation metric for crypto-ransomware detection using machine learning - ScienceDirect. J Inf Secur Appl. Available from. 2020, 55, 102646. [Google Scholar]
- Alhashmi, A.A.; Darem, A.A.; Alashjaee, A.M.; Alanazi, S.M.; Alkhaldi, T.M.; Ebad, S.A.; Ghaleb, F.A.; Almadani, A.M. Similarity-Based Hybrid Malware Detection Model Using API Calls. Mathematics Available from. 2023, 11, 2944. [Google Scholar] [CrossRef]
- Hwang, R.H.; Peng, M.C.; Nguyen, V.L.; Chang, Y.L. An LSTM-based deep learning approach for classifying malicious traffic at the packet level. Appl Sci. 2019, 9, 3414. Available online: https://www.mdpi.com/2076-3417/9/16/3414. [CrossRef]
- Al-Hawawreh, M.; Moustafa, N.; Garg, S.; Hossain, M.S. Deep learning-enabled threat intelligence scheme in the Internet of Things networks. IEEE Trans Netw Sci Eng.;Deep Learning-Enabled Threat Intelligence Scheme in the Internet of Things Networks | IEEE Journals & Magazine | IEEE Xplore Available from. 2021, 8, 2968–81. [Google Scholar]
- Al-rimy, B.A.S.; Maarof, M.A.; Shaid, S.Z.M. A 0-day aware crypto-ransomware early behavioral detection framework. In Advances in Information and Communication Networks. Lecture Notes in Networks and Systems; Available from: A 0-Day Aware Crypto-Ransomware Early Behavioral Detection Framework | Springer Nature Link; Springer, 2019; pp. 758–77. [Google Scholar]
- Nissim, N.; Cohen, A.; Glezer, C.; Elovici, Y. Detection of malicious PDF files and directions for enhancements: a state-of-the art survey Detection of malicious PDF files and directions for enhancements: A state-of-the art survey - ScienceDirect. Comput Secur. Available from. 2015, 48, 246–66. [Google Scholar] [CrossRef]
- Azmoodeh, A.; Dehghantanha, A.; Conti, M.; Choo, K.K.R. Detecting crypto-ransomware in IoT networks based on energy consumption footprint. J Ambient Intell Humaniz Comput. 2018, 9, 1141–52. Available online: https://link.springer.com/article/10.1007/s12652-017-0558-5. [CrossRef]
- Richardson, R.; North, M.M. Ransomware: Evolution, mitigation and prevention. Int Manag Rev. Available from: Ransomware: Evolution, Mitigation and Prevention. 2017, 13, 10–21. [Google Scholar]
- Chen, Z.; Kang, H.S.; Yin, S.N.; Kim, S.R. Automatic ransomware detection and analysis based on dynamic API calls flow graph. In Proceedings of the International Conference on Research in Adaptive and Convergent Systems, 2017; ACM; pp. 196–201. Available online: https://dl.acm.org/doi/10.1145/3129676.3129704.
- Ahmadian, M.M.; Shahriari, H.R.; Ghaffarian, S.M. Connection-monitor & connection-breaker: a novel approach for prevention and detection of high survivable ransomwares. 2015 12th International Iranian Society of Cryptology Conference on Information Security and Cryptology (ISCISC) Connection-monitor & connection-breaker: A novel approach for prevention and detection of high survivable ransomwares | IEEE Conference Publication | IEEE Xplore, Available from. 2015; IEEE; pp. 79–84. [Google Scholar]
- Oliveira Lima, Td; Colaço, M.; Prado, K. H. de J.; Dias de J., I.; de Oliveira, F. R. A Big Data Experiment to Evaluate the Effectiveness of Traditional Machine Learning Techniques Against LSTM Neural Networks in the Hotels Clients Opinion Mining. 2021 IEEE International Conference on Big Data (Big Data), Orlando, FL, USA, 2021; pp. 5199–5208. [Google Scholar] [CrossRef]
- Al-Hawawreh, M.; Sitnikova, E.; Aboutorab, N. X-IIoTID: a connectivity-agnostic and device-agnostic intrusion dataset for industrial Internet of Things. IEEE Internet Things J.;X-IIoTID: A Connectivity-Agnostic and Device-Agnostic Intrusion Data Set for Industrial Internet of Things | IEEE Journals & Magazine | IEEE Xplore Available from. 2022, 9, 3962–77. [Google Scholar]
- Khammas, B.M.; Monemi, A.; Basurra, S.; De Santis, E.; Iadarola, G.; Martinelli, F. Ransomware detection using random forest technique: a survey and a case study. In Proceedings of the 7th International Conference on Information Systems Security and Privacy (ICISSP 2021), Available from. 2021; SciTePress; pp. 534–41, Ransomware Detection using Random Forest Technique - ScienceDirect. [Google Scholar]
- Cabaj, K.; Gregorczyk, M.; Mazurczyk, W. Software-defined networking-based crypto ransomware detection using HTTP traffic characteristics Software-defined networking-based crypto ransomware detection using HTTP traffic characteristics - ScienceDirect. Comput Electr Eng. Available from. 2018, 66, 353–68. [Google Scholar] [CrossRef]
- Arivudainambi, D.; KAVD; Visu, P. Malware traffic classification using principal component analysis and artificial neural network for extreme surveillance Malware traffic classification using principal component analysis and artificial neural network for extreme surveillance - ScienceDirect. Comput Commun. Available from. 2019, 147, 50–7. [Google Scholar]
- Darem, A.; Abawajy, J.H.; Makkar, A.; Alanazi, A.; Alanazi, S.; Alshahrani, H.; Almotairi, K.H.; Ghaleb, F.A.; Alqarni, M.A. Visualization and deep-learning-based malware variant detection using OpCode-level features Visualization and deep-learning-based malware variant detection using OpCode-level features - ScienceDirect. Future Gener Comput Syst. Available from. 2021, 125, 314–23. [Google Scholar] [CrossRef]
- Naeem, H.; Guo, B.; Naeem, M.R.; Ullah, F.; Aldabbas, H.; Javed, M.S. Identification of malicious code variants based on image visualization Identification of malicious code variants based on image visualization - ScienceDirect. Comput Electr Eng. Available from. 2020, 76, 225–37. [Google Scholar] [CrossRef]
- Al-Rimy, B.A.S.; Maarof, M.A.; Shaid, S.Z.M. Ransomware threat success factors, taxonomy, and countermeasures: a survey and research directions. Comput Secur. Available from: Ransomware threat success factors, taxonomy, and countermeasures: A survey and research directions - ScienceDirect. 2018, 74, 144–66. [Google Scholar] [CrossRef]
- Abaid, Z.; Kaafar, M.A.; Jha, S. Early detection of in-the-wild botnet attacks by exploiting network communication uniformity: an empirical study. 2016 IEEE Conference on Communications and Network Security (CNS), Available from. 2016; IEEE; pp. 270–8, Early detection of in-the-wild botnet attacks by exploiting network communication uniformity: an empirical study - Macquarie University. [Google Scholar]
- Alzaylaee, M.K.; Yerima, S.Y.; Sezer, S. DynaLog: An automated dynamic analysis framework for characterizing Android applications. 2016 International Conference on Cyber Security and Protection of Digital Services (Cyber Security) 1607.08166] DynaLog: An automated dynamic analysis framework for characterizing Android applications, Available from. 2016; IEEE; pp. 1–8. [Google Scholar]
- Kara, I.; Aydos, M. The rise of ransomware: forensic analysis for windows based ransomware attacks. 2019 1st International Informatics and Software Engineering Conference (UBMYK) The rise of ransomware: Forensic analysis for windows based ransomware attacks - ScienceDirect, Available from. 2019; IEEE; pp. 1–6. [Google Scholar]
- Ahmed, M.E.; Kim, H.; Park, M. Mitigating DNS query-based DDoS attacks with machine learning on software-defined networking. 2017 IEEE Military Communications Conference (MILCOM) Mitigating DNS query-based DDoS attacks with machine learning on software-defined networking | IEEE Conference Publication | IEEE Xplore, Available from. 2017; IEEE; pp. 11–16. [Google Scholar]
- Razaulla, S. The Age of Ransomware: A Survey on the Evolution, Taxonomy, and Research Directions. IEEE Access 2023, vol. 11, 40698–40723. [Google Scholar] [CrossRef]
- Mercaldo, F. Automated Ransomware Behavior Analysis: Pattern Extraction and Early Detection. In Cybersecurity and Privacy in Cyber Physical Systems; Springer, 2020; pp. 251–267. Available online: https://link.springer.com/chapter/10.1007/978-3-030-34637-9_15.
- De Gaspari, F.; Hitaj, D.; Pagnotta, G.; De Carli, L.; Mancini, L.V. Evading Behavioral Classifiers: A Comprehensive Analysis on Evading Ransomware Detection Techniques. Neural Comput Appl. 2022, 34, 12077–12096. Available online: https://link.springer.com/article/10.1007/s00521-022-07096-6. [CrossRef]
- Alqahtani, A.; Gazzan, M.; Sheldon, F.T. Ransomware detection and prevention based on artificial intelligence: a systematic review. Secur Priv. 2022, 5, e256. Available online: https://onlinelibrary.wiley.com/doi/full/10.1002/spy2.256.
- Akbanov, M.; Vassilakis, V.G.; Logothetis, M.D. Ransomware detection and mitigation using software-defined networking: the case of WannaCry Ransomware detection and mitigation using software-defined networking: The case of WannaCry - ScienceDirect. Comput Electr Eng. Available from. 2019, 76, 111–21. [Google Scholar] [CrossRef]
- Cohen, A.; Nissim, N. Trusted detection of ransomware in a private cloud using machine learning methods leveraging meta-features from volatile memory Trusted detection of ransomware in a private cloud using machine learning methods leveraging meta-features from volatile memory - ScienceDirect. Expert Syst Appl. Available from. 2018, 102, 158–78. [Google Scholar]
- Shaukat, K.; Luo, S.; Varadharajan, V.; Hameed, I.A.; Xu, M. Ransomware classification and detection with machine learning algorithms. 2022 IEEE 46th Annual Computers, Software, and Applications Conference (COMPSAC), 2022; pp. 1154–63. [Google Scholar] [CrossRef]
- Barua, R.; Reza, M.S.U.; Tonmoy, T.I. Is iterative feature selection technique efficient enough? A comparative performance analysis of RFECV feature selection technique in ransomware classification using SHAP. Discov Internet Things 2023, 3, 25. [Google Scholar] [CrossRef]
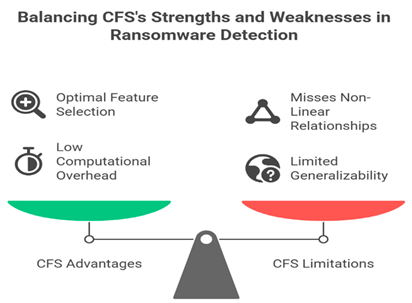
- Sharma, M.; Sharma, T.; Singla, A.K.; Rattan, D. CFSBFDroid: Android malware detection using CFS + best first search-based feature selection. Mob Inf Syst. 2022, 2022, 6425583. [Google Scholar] [CrossRef]
- Padmavathi, G.; Shanmugapriya, D. Evaluation of principal component analysis variants to assess their suitability for mobile malware detection. In Intelligent Computing. Lecture Notes in Networks and Systems; Arai, K, Ed.; Springer: Cham, 2022; pp. 269–90. Available online: https://www.intechopen.com/chapters/82166.
- Meidan, Y.; Bohadana, M.; Mathov, Y.; Mirsky, Y.; Shabtai, A.; Breitenbacher, D.; Elovici, Y. N-BaIoT—network-based detection of IoT botnet attacks using deep autoencoders. IEEE Pervasive Comput. 2018, 17, 12–22. Available online: https://ieeexplore.ieee.org/document/8490192. [CrossRef]
- Kshirsagar, D.; Kumar, S. Intrusion detection system using PCA with random forest approach. 2020 International Conference on Electronics and Sustainable Communication Systems (ICESC), Coimbatore, India, 2020 Jul 2-4; IEEE; pp. 803–8. Available online: https://ieeexplore.ieee.org/document/9155656/. [CrossRef]
- Takeuchi, Y.; Sakai, K.; Fukumoto, S. Detecting ransomware using support vector machines. In Proceedings of the 47th International Conference on Parallel Processing Companion, Eugene, OR, USA, 2018 Aug 13-16; ACM: New York; pp. 1–6. Available online: https://dl.acm.org/doi/10.1145/3229710.3229726. [CrossRef]
- Al-Syouf, R.; Aljarrah, O.Y.; Bani-Hani, R.; Alma’aitah, A. Ensemble Machine Learning Models Utilizing a Hybrid Recursive Feature Elimination (RFE) Technique for Detecting GPS Spoofing Attacks Against Unmanned Aerial Vehicles. Sensors (Basel) 2025, 25, 2388. Available online: https://www.mdpi.com/1424-8220/25/8/2388. [CrossRef]
- Madhavi, S.; Jyothi, V.E.; Chilukuri, L.S.Y.; Yadav, N.P.; Sri, J.B.; Bhargavi, K. Intrusion Detection System Using a Hybrid of SVM and RFE. In Advances in Information Communication Technology and Computing. Lecture Notes in Networks and Systems; Springer: Singapore, 2024; pp. 703–11. Available online: https://link.springer.com/chapter/10.1007/978-981-97-6103-6_44.
- Awad, M.; Fraihat, S. Recursive Feature Elimination with Cross-Validation with Decision Tree: Feature Selection Method for Machine Learning-Based Intrusion Detection Systems. J Sens Actuator Netw. 2023, 12, 67. Available online: https://www.mdpi.com/2224-2708/12/5/67. [CrossRef]
- Alshamrani, S.; Alzahrani, A.; Alzahrani, B.; Alzahrani, A. SRFE: A Stepwise Recursive Feature Elimination Approach for Network Intrusion Detection. Pers Ubiquit Comput. 2024. Available online: https://link.springer.com/article/10.1007/s12083-024-01763-2.
- AAlzahrani, H. Alshahrani; Alshehri, A.; Fu, H. An Intelligent Behavior-Based Ransomware Detection System For Android Platform. 2019 First IEEE International Conference on Trust, Privacy and Security in Intelligent Systems and Applications (TPS-ISA), Los Angeles, CA, USA, 2019; pp. 28–35. [Google Scholar] [CrossRef]
- Ba’abbad, I.; Batarfi, O. Proactive Ransomware Detection Using Extremely Fast Decision Tree (EFDT) Algorithm: A Case Study. Computers (Basel) 2023, 12, 121. Available online: https://www.mdpi.com/2073-431X/12/6/121. [CrossRef]
- Alshamrani, S.; Alzahrani, A.; Alzahrani, B.; Alzahrani, A. A Multi-level Correlation-Based Feature Selection for Intrusion Detection. Arab J Sci Eng. 2022, 47, 13369–83. Available online: https://link.springer.com/article/10.1007/s13369-022-06760-2.
- Arabo, A.; Dijoux, R.; Poulain, T.; Chevalier, G. Detecting ransomware using process behavior analysis. Procedia Comput Sci. Available from. 2020, 168, 289–96, Detecting Ransomware Using Process Behavior Analysis - ScienceDirect. [Google Scholar] [CrossRef]
- Darabian, H.; Homayounoot, S.; Dehghantanha, A.; et al. Detecting Cryptomining Malware: a Deep Learning Approach for Static and Dynamic Analysis. J Grid Computing Available from. 2020, 18, 293–303. [Google Scholar] [CrossRef]
- Albshaier, L.; Almarri, S.; Rahman, M.M. Earlier Decision on Detection of Ransomware Identification: A Comprehensive Systematic Literature Review. Information (Basel) 2024, 15, 484. Available online: https://www.mdpi.com/2078-2489/15/8/484. [CrossRef]
- Sheen, S.; Yadav, S. Ransomware detection by mining API call usage. 2018 International Conference on Advances in Computing, Communications and Informatics (ICACCI) Ransomware detection by mining API call usage | IEEE Conference Publication | IEEE Xplore, Available from. 2018; IEEE; pp. 983–7. [Google Scholar]
- Baek, S.; Jung, Y.; Mohaisen, A.; Lee, S.; Nyang, D. SSD-assisted ransomware detection and data recovery techniques. IEEE Trans Comput.;SSD-Assisted Ransomware Detection and Data Recovery Techniques | IEEE Journals & Magazine | IEEE Xplore Available from. 2021, 70, 1332–44. [Google Scholar]
- Tahsien, S.M.; Karimipour, H.; Spachos, P. Machine learning based solutions for security of Internet of Things (IoT): a survey. J Netw Comput Appl. Available from: Machine learning based solutions for security of Internet of Things (IoT): A survey - ScienceDirect. 2020, 161, 102630. [Google Scholar] [CrossRef]
- Abbasi, M.; Shahraki, A.; Taherkordi, A. Deep learning for network traffic monitoring and analysis (NTMA): a survey. Comput Commun. Available from: Deep Learning for Network Traffic Monitoring and Analysis (NTMA): A Survey - ScienceDirect. 2021, 170, 19–41. [Google Scholar] [CrossRef]
- Ramilli, M.; Bishop, M.; Sun, S. Multiprocess malware. 2011 6th International Conference on Malicious and Unwanted Software Multiprocess malware | IEEE Conference Publication | IEEE Xplore, Available from. 2011; IEEE; pp. 8–13. [Google Scholar]
- RKumar; Zhang, X.; Wang, W.; Khan, R. U.; Kumar, J.; Sharif, A. A Multimodal Malware Detection Technique for Android IoT Devices Using Various Features. IEEE Access;IEEE Journals & Magazine | IEEE Xplore Available from. 2019, vol. 7, 64411–64430. [Google Scholar] [CrossRef]
- Al-Hawawreh, M.; Sitnikova, E. Ransomware detection using random forest technique. ICT Express 2022, 8, 218–23. Available online: https://www.sciencedirect.com/science/article/pii/S2405959520304756.
- Urooj, U.; Maarof, M.A.; Al-rimy, B.A.S. Ransomware detection using deep learning based unsupervised feature extraction and a cost sensitive Pareto Ensemble classifier. Sci Rep. 2022, 12, 15647. Available online: https://www.nature.com/articles/s41598-022-19443-7.
- Zahra, A.; Shah, M.A. Android ransomware detection using supervised machine learning techniques based on traffic analysis. Sensors 2024, 24, 189. Available online: https://www.mdpi.com/1424-8220/24/1/189.
- Ahmed, Y.A.; Kocer, B.; Al-rimy, B.A.S. Automated analysis and detection of ransomware using machine learning: a survey. Appl Sci. 2022, 12, 172. Available online: https://www.mdpi.com/2076-3417/12/1/172.
- Sihag, V.; Vardhan, M.; Singh, P. A survey of android application and malware hardening A survey of android application and malware hardening - ScienceDirect. J Comput Sci Review Available from. 2021, 12, 10001–29. [Google Scholar]
- Manavi, F.; Hamzeh, A. A new method for ransomware detection based on PE header using convolutional neural networks. 2020 17th International ISC Conference on Information Security and Cryptology (ISCISC) A New Method for Ransomware Detection Based on PE Header Using Convolutional Neural Networks | IEEE Conference Publication | IEEE Xplore, Available from. 2020; IEEE; pp. 82–7. [Google Scholar]
- Iqbal, M.S.; Javed, Y. Digital forensics as advanced ransomware pre-attack detection algorithm for endpoint data protection. Secur Commun Netw. 2022, 2022, 1424638. Available online: https://www.hindawi.com/journals/scn/2022/1424638/.
- Şahin, D.Ö.; Akleylek, S. Permission-based Android malware analysis by using dimension reduction with PCA and LDA. J Inf Secur Appl. 2021, 63, 102995. Available online: https://www.sciencedirect.com/science/article/abs/pii/S2214212621002039. [CrossRef]
- Mahdavifar, S.; Kadir, A.F.A.; Fatemi, R.; Alhadidi, D.; Ghorbani, A.A. Dynamic Android malware category classification using semi-supervised deep learning. 2020 IEEE Intl Conf on Dependable, Autonomic and Secure Computing, 2020; IEEE; pp. 515–22. Available online: https://pmc.ncbi.nlm.nih.gov/articles/PMC9890381/.
- Beaman, C.; Barkworth, A.; Akande, T.D.; Hakak, S.; Khan, M.K. Ransomware: recent advances, analysis, challenges and future research directions. Comput Secur. 2021, 111, 102490. Available online: https://www.researchgate.net/publication/365734823_A_review_of_machine_learning-based_zero-day_attack_detection_Challenges_and_future_directions. [CrossRef]
- Sharmeen, S.; Ahmed, Y.A.; Huda, S.; Koçer, B.Ş.; Hassan, M.M. Avoiding future digital extortion through robust protection against ransomware threats using deep learning based adaptive approaches. IEEE Access. 2020, 8, 24522–34. Available online: https://doaj.org/article/a7d20b3936484cd4b16785d00c69ad5c. [CrossRef]
- Or-Meir, O.; Nissim, N.; Elovici, Y.; Rokach, L. Dynamic malware analysis in the modern era—a state of the art survey. ACM Comput Surv. 2019, 52, 1–48. Available online: https://dl.acm.org/doi/10.1145/3329786. [CrossRef]
- Almomani, I.; Alkhayer, A.; El-Shafai, W. E2E-RDS: Efficient end-to-end ransomware detection system based on static-based ML and vision-based DL approaches. Sensors 2023, 23, 4467. Available online: https://www.mdpi.com/1424-8220/23/9/4467. [CrossRef] [PubMed]
- Oz, H.; Aris, A.; Levi, A.; Uluagac, A.S. A survey on ransomware: evolution, taxonomy, and defense solutions. ACM Comput Surv. 2022, 54(11s), Article 238. Available online: https://dl.acm.org/doi/10.1145/3514229. [CrossRef]
- Gopinath, M.; Sethuraman, S.C. A comprehensive survey on deep learning based malware detection techniques. Comput Sci Rev. 2023, 47, 100529. Available online: https://www.sciencedirect.com/science/article/abs/pii/S1574013722000636.
- Sharmeen, S.; Huda, S.; Koçer, B.; Abawajy, J.H. A holistic analysis of ransomware detection techniques for IoT ecosystems: challenges, solutions and future directions. Procedia Comput Sci. Available from. 2021, 191, 320–7, A Holistic Approach to Ransomware Classification: Leveraging Static and Dynamic Analysis with Visualization | MDPI. [Google Scholar]
- Mohamed, N. Artificial Intelligence and Machine Learning in Cybersecurity: A Deep Dive into State-of-the-Art Techniques and Future Paradigms. Knowl Inf Syst. 2025, 67, 6969–7055. Available online: https://link.springer.com/article/10.1007/s10115-025-02429-y. [CrossRef]
- Karbab, E.M.B.; Debbabi, M.; Derhab, A. SwiftR: Cross-platform ransomware fingerprinting using hierarchical neural networks on hybrid features. Expert Syst Appl. 2023, 225, 120017. Available online: https://www.sciencedirect.com/science/article/abs/pii/S0957417423005195. [CrossRef]
- Hasan, M.M.; Rahman, M.M. RansHunt: A support vector machines based ransomware analysis framework with integrated feature set. 2017 20th International Conference of Computer and Information Technology (ICCIT), 2017; IEEE; pp. 1–7. Available online: https://ieeexplore.ieee.org/document/8281838.
- Alshammari, A.B.; Darem, L.A.; Sheatah, H.K. Ransomware early detection techniques. Eng Technol Appl Sci Res. 2024, 14, 14497–503. Available online: https://www.etasr.com/index.php/ETASR/article/view/6915.
- Yewale, A.; Singh, M. Malware detection based on opcode frequency using machine learning. 2016 International Conference on Advanced Communication Control and Computing Technologies (ICACCCT) Malware detection based on opcode frequency | IEEE Conference Publication | IEEE Xplore, Available from. 2016; IEEE; pp. 646–9. [Google Scholar]
- Chourasiya, L.; Khatri, S.; Lilhore, U.K.; et al. Advanced system log analyzer for anomaly detection and cyber forensic investigations using LSTM and transformer networks. J Cloud Comp Available from. 2025, 14, 60. [Google Scholar] [CrossRef]
- Goutte, C.; Gaussier, E. A Probabilistic Interpretation of Precision, Recall and F-Score, with Implication for Evaluation. In Advances in Information Retrieval. Lecture Notes in Computer Science; Springer: Berlin, 2005; pp. 345–59. Available online: https://link.springer.com/chapter/10.1007/978-3-540-31865-1_25.
- Orozco-Arias, S.; Piña, J.S.; Tabares-Soto, R.; Castillo-Ossa, L.F.; Guyot, R.; Isaza, G. Measuring Performance Metrics of Machine Learning Algorithms for Detecting and Classifying Transposable Elements. Processes 2020, 8, 638. Available online: https://www.mdpi.com/2227-9717/8/6/638. [CrossRef]
- Ferdous, J.; Islam, R.; Mahboubi, A.; Islam, M.Z. AI-based ransomware detection: A comprehensive review. IEEE Access. Available from. 2024, 12, 136666–136695. [Google Scholar] [CrossRef]
- Gazet, A. Comparative analysis of various ransomware virii. J Comput Virol Available from. 2010, 6, 77–90. [Google Scholar] [CrossRef]
- Ashwini, K.; Nagasundara, K.B. An intelligent ransomware attack detection and classification using dual vision transformer with Mantis Search Split Attention Network. Comput Electr Eng. Available from. 2024, 119, 109509. [Google Scholar] [CrossRef]
- Saito, T.; Rehmsmeier, M. The precision-recall plot is more informative than the ROC plot when evaluating binary classifiers on imbalanced datasets. PLoS One Available from. 2015, 10, e0118432. [Google Scholar] [CrossRef] [PubMed]
- Richardson, E.; Trevizani, R.; Greenbaum, J.A.; Carter, H.; Nielsen, M.; Peters, B. The receiver operating characteristic curve accurately assesses imbalanced datasets. Patterns Available from. 2024, 5, 100994. [Google Scholar] [CrossRef]
- Dhawan, S.; Narwal, B. Unfolding the Mystery of Ransomware. In International Conference on Innovative Computing and Communications. Lecture Notes in Networks and Systems; Available from; Bhattacharyya, S., Hassanien, A., Gupta, D., Khanna, A., Pan, I., Eds.; Springer: Singapore, 2019; vol 55. [Google Scholar] [CrossRef]
- Teichmann, F. Ransomware attacks in the context of generative artificial intelligence—an experimental study. Int Cybersecurity Law Rev. 2023, 4, 399–414. Available online: https://link.springer.com/article/10.1365/s43439-023-00094-x. [CrossRef]
- Ferrante, A.; Medvet, E.; Mercaldo, F.; Visaggio, C.A.; Fornaia, A. Spotting the malicious moment: characterizing malware behavior using dynamic features. 2016 11th International Conference on Availability, Reliability and Security (ARES), Available from: [PDF] Spotting the Malicious Moment: Characterizing Malware Behavior Using Dynamic Features | Semantic Scholar. 2016; IEEE; pp. 372–81. [Google Scholar]
- Iqbal, A.; Hussain, M.; Riaz, Q.; Khalid, M.; Mumtaz, R.; Jung, K. Enhancing ransomware detection with machine learning techniques and effective API integration. Comput Mater Contin. Available from. 2025, 85, 1693–1714. [Google Scholar] [CrossRef]
- Jeong, H.; Lee, K. A machine learning-based ransomware detection method for attackers' neutralization techniques using format-preserving encryption. Sensors Available from. 2025, 25, 2406. [Google Scholar] [CrossRef]
- Brodersen, K.H.; Ong, C.S.; Stephan, K.E.; Buhmann, J.M. Class imbalance should not throw you off balance: Choosing the right classifiers and performance metrics for brain decoding with imbalanced data. NeuroImage Available from. 2023, 171, 437–452. [Google Scholar] [CrossRef]
- Bergmeir, C.; Hyndman, R.J.; Koo, B. A note on the validity of cross-validation for evaluating autoregressive time series prediction. Comput Stat Data Anal. Available from. 2018, 120, 70–83. [Google Scholar] [CrossRef]
- Cawley, G.C.; Talbot, N.L.C. On over-fitting in model selection and subsequent selection bias in performance evaluation. J Mach Learn Res. 2010, 11, 2079–2107. Available online: http://jmlr.org/papers/v11/cawley10a.html.
- Shaukat, K.; Luo, S.; Varadharajan, V.; Hameed, I.A.; Xu, M. A novel method for improving the robustness of deep learning-based malware detectors against adversarial attacks. Eng Appl Artif Intell. Available from. 2022, 116, 105461. [Google Scholar] [CrossRef]
- Demetrio, L.; Coull, S.E.; Biggio, B.; Lagorio, G.; Armando, A.; Roli, F. Adversarial examples: A survey and experimental evaluation of practical defenses. Digit Threat Res Pract. Available from. 2022, 3, 1–31. [Google Scholar] [CrossRef]
- Al-banaa, A.; Sahana, S.; Ali, J.; Das, S. Ransomware Taxonomy and Detection Techniques Based on Machine Learning: A Review. In Advanced Communication and Intelligent Systems. ICACIS 2023. Communications in Computer and Information Science; Available from; Shaw, R.N., Paprzycki, M., Ghosh, A., Eds.; Springer: Cham, 2023; vol 1921. [Google Scholar] [CrossRef]
- Suciu, O.; Coull, S.E.; Johns, J. Exploring adversarial examples in malware detection. 2019 IEEE Security and Privacy Workshops (SPW), Available from. San Francisco, CA, USA, 2019 May 19-23; IEEE; pp. 8–14. [Google Scholar] [CrossRef]
- Sihwail, R.; Omar, K.; Ariffin, K.A.Z. A survey on malware detection using data mining techniques. Symmetry 2019, 11, 1193. Available online: https://www.mdpi.com/2073-8994/11/10/1193.
- Alshamrani, A.; Myneni, S.; Chowdhary, A.; Huang, D. A survey on advanced persistent threats: techniques, solutions, challenges, and research opportunities. IEEE Commun Surv Tutor. 2019, 21, 1851–77. Available online: https://ieeexplore.ieee.org/document/8656877. [CrossRef]
- Salem, A.H.; Azzam, S.M.; Emam, O.E.; Abohany, A.A. Advancing cybersecurity: a comprehensive review of AI-driven detection techniques. J Big Data 2024, 11, 105. Available online: https://journalofbigdata.springeropen.com/articles/10.1186/s40537-024-00957-y. [CrossRef]
- Agrawal, R.; Stokes, J.W.; Selvaraj, K.; Marinescu, M. Neural sequential malware detection with parameters. 2019 IEEE International Conference on Big Data Neural Sequential Malware Detection with Parameters | IEEE Conference Publication | IEEE Xplore, Available from. 2019; IEEE; pp. 1066–73. [Google Scholar]
- Ahmed, M.; Alasad, Q.; Yuan, J.S.; Alawad, M. Re-evaluating deep learning attacks and defenses in cybersecurity systems. Big Data Cogn Comput. 2024, 8, 191. Available online: https://www.mdpi.com/2504-2289/8/12/191. [CrossRef]
- Li, J.; Yang, G.; Shao, Y. Ransomware detection model based on adaptive graph neural network learning. Appl Sci. 2024, 14, 4579. Available online: https://www.mdpi.com/2076-3417/14/11/4579. [CrossRef]
- Joyce, R.J.; Miller, G.; Roth, P.; Zak, R.; Zaresky-Williams, E.; Anderson, H.; et al. EMBER2024, a benchmark dataset for holistic evaluation of malware classifiers. arXiv. 5 Jun 2025. Available online: https://arxiv.org/abs/2506.05074.
- Wang, P.; Lin, H.C.; Chen, J.H.; Lin, W.H.; Li, H.C. Improving cyber defense against ransomware: a generative adversarial networks-based adversarial training approach for long short-term memory network classifier. Electronics 2025, 14, 810. Available online: https://www.mdpi.com/2079-9292/14/4/810. [CrossRef]
- Kaushik, K.; Khan, A.; Kumari, A.; Sharma, I.; Dubey, R. Ethical considerations in AI-based cybersecurity. In Next-Generation Cybersecurity; Springer: Singapore, 2024; pp. 437–70. Available online: https://link.springer.com/chapter/10.1007/978-981-97-1249-6_19.
- Bruschi, D.; Diomede, N. A framework for assessing AI ethics with applications to cybersecurity. AI and Ethics 2023, 3, 65–72. Available online: https://link.springer.com/article/10.1007/s43681-022-00162-8. [CrossRef]
- Owen-Jackson, C. Navigating the ethics of AI in cybersecurity. IBM Think Insights. 16 Oct 2024. Available online: https://www.ibm.com/think/insights/navigating-ethics-ai-cybersecurity.
- Tuhin, M. The dark side of AI: cybersecurity threats and privacy concerns. Science News Today. 27 Mar 2025. Available online: https://www.sciencenewstoday.org/the-dark-side-of-ai-cybersecurity-threats-and-privacy-concerns.
- KPMG The ethical use of AI in cybersecurity: balancing security and privacy in the digital age. KPMG Insights. 2025. Available online: https://kpmg.com/us/en/articles/2025/ethical-ai-cybersecurity-balancing-security-privacy-digital-age.html.
- Meti, S.; Sidramayyanmath, V.; Patil, S.; Patil, P. Ransomware detection using machine learning and explainable AI. In Artificial Intelligence: Theory and Applications (AITA 2024); Springer: Singapore, 2025; pp. 31–46. Available online: https://link.springer.com/chapter/10.1007/978-981-96-1918-4_3.
- Preuveneers, D.; Joosen, W. An ontology-based cybersecurity framework for AI-enabled systems and applications. Future Internet 2024, 16, 69. Available online: https://www.mdpi.com/1999-5903/16/3/69. [CrossRef]
- Galwaduge, V.; Samarabandu, J. Novel actionable counterfactual explanations for intrusion detection using diffusion models. J Cybersecur Priv. 2025, 5, 68. Available online: https://www.mdpi.com/2624-800X/5/3/68. [CrossRef]
- Nazim, S.; Alam, M.M.; Rizvi, S.S.; Mustapha, J.C.; Hussain, S.S.; Suud, M.M. Advancing malware imagery classification with explainable deep learning: a state-of-the-art approach using SHAP, LIME and Grad-CAM. PLoS One 2025, 20, e0318542. Available online: https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0318542. [CrossRef] [PubMed]
- Spartalis, C.N.; Semertzidis, T.; Daras, P. Balancing XAI with privacy and security considerations. In Computer Security. ESORICS 2023 International Workshops; Springer: Cham, 2024; pp. 111–24. Available online: https://link.springer.com/chapter/10.1007/978-3-031-54129-2_7.
- Yousefi, N.; Georgiopoulos, M.; Anagnostopoulos, G.C. Multi-Task Learning with Group-Specific Feature Space Sharing. In Machine Learning and Knowledge Discovery in Databases. ECML PKDD 2015. Lecture Notes in Computer Science(); Available from; Appice, A., Rodrigues, P., Costa, Santos, Gama, V., Jorge, J., Soares, A.C., Eds.; Springer: Cham, 2015; vol 9285. [Google Scholar] [CrossRef]
- Ispahany, J.; Islam, M.R.; Khan, M.A.; Islam, M.Z. A Sysmon incremental learning system for ransomware analysis and detection. arXiv. 2 Jan 2025. Available online: https://arxiv.org/html/2501.01089v1.
- Shiring, B.; Stanhope, C.; Devito, H.; Brigham, R.; Tschernov, L. Adaptive ransomware detection using dynamic encryption pattern analysis. TechRxiv. 2025. Available online: https://www.techrxiv.org/articles/1235439.
- Chambers, L.; Gaber, M.M.; Ghomeshi, H. Deepstreamensemble: streaming adaptation to concept drift in deep neural networks. Int J Mach Learn Cybern. 2025, 16, 3955–76. Available online: https://link.springer.com/article/10.1007/s13042-024-02492-x. [CrossRef]
- Almasri, Y.; Islam, M.S.; Elnour, M.; Shinwari, M.W.; Binbeshr, F.; Mahmoud, A.; Imam, M. Ransomware detection on IoT edge using optimized deep representation learning. TechRxiv. 2025. Available online: https://www.techrxiv.org/articles/1267873.
- Rahmati, M.; Pagano, A. Federated learning-driven cybersecurity framework for IoT networks with privacy-preserving and real-time threat detection capabilities. Informatics 2025, 12, 62. Available online: https://www.mdpi.com/2227-9709/12/3/62. [CrossRef]
- Jemili, F.; Jouini, K.; Korbaa, O. Intrusion detection based on concept drift detection and online incremental learning. Int J Pervasive Comput Commun 2025, 21(1). Available online: https://www.emerald.com/insight/content/doi/10.1108/ijpcc-12-2023-0358/full/html. [CrossRef]
- Timofte, E.M.; Dimian, M.; Graur, A.; Potorac, A.D.; Balan, D.; Croitoru, I.; et al. Federated learning for cybersecurity: a privacy-preserving approach. Appl Sci. 2025, 15, 6878. Available online: https://www.mdpi.com/2076-3417/15/12/6878. [CrossRef]
- Peng, H.; Wu, C.; Xiao, Y. FD-IDS: federated learning with knowledge distillation for intrusion detection in non-IID IoT environments. Sensors 2025, 25, 4309. Available online: https://www.mdpi.com/1424-8220/25/14/4309. [CrossRef]
- Alshamrani, A. Federated hierarchical MARL for zero-shot cyber defense. PLoS One 2025, 20, e0329969. Available online: https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0329969. [CrossRef]
- Piplai, A.; Mittal, S.; Joshi, A.; Finin, T.; Holt, J.; Zak, R. Creating cybersecurity knowledge graphs from malware after action reports. IEEE Access.;Creating Cybersecurity Knowledge Graphs From Malware After Action Reports | IEEE Journals & Magazine | IEEE Xplore Available from. 2020, 8, 211691–703. [Google Scholar]
- Jimenez, D.M.G.; Solans, D.; Heikkila, M.; Vitaletti, A.; Kourtellis, N.; Anagnostopoulos, A.; et al. Non-IID data in federated learning: a survey with taxonomy, metrics, methods, frameworks and future directions. arXiv. 19 Nov 2024. Available online: https://arxiv.org/abs/2411.12377.
- Cloud Optics. The legal framework surrounding threat intelligence sharing: what organizations need to know. Cloud Optics. 2025. Available online: https://cloudoptics.ai/the-legal-framework-surrounding-threat-intelligence-sharing-what-organizations-need-to-know/.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




