1. Introduction
A MANET is a collection of autonomous mobile nodes communicating with each other using wireless links and decentralized administration; there is no fixed net-work infrastructure. In this environment, nodes are involved in decision-making, performing maintenance duties and taking part in routing algorithms. In general, any proposal applicable to a MANET must consider the constraints imposed by the inherent characteristics of these networks. These characteristics are defined in [
1] and they are: dynamic topology, limited bandwidth links, energy constraints [
2], physical security constraints [
3], and processing capacity of the nodes. So far, research efforts have primarily focused on routing issues. Considering that routing is one of the most important mechanisms in MANETs, others like QoS provided or security and service discovery, cannot be executed if there is no optimal communication link [
3]. The increasing usage of new applications has enabled more people to use and take advantage of smart devices o smartphone [
4] but configuring more challenging scenarios. A scenario is composed of a particular number of nodes, topography, and a mobility algorithm, which includes direction, speed and pauses of those nodes. In real-world scenarios, the topography tends to be irregular due to the presence of numerous obstacles resulting from unexpected events, which alter typical mobility paths. Consequently, the motion algorithm is defined based on the terrain’s characteristics and the corresponding nodes that must adjust their movement according to these obstacles. On the other hand, it is also important to mention that there is a novel node routing strategy that, because nodes lose energy, they become selfish after being classified as reliable by everyone. This strategy can be used by various types of routing protocols where nodes are not considered malicious, so they are allowed to provide information about their current energy level. Knowledge about the energy status of neighbors helps a node avoid those nodes with very little energy, in order to prevent these nodes from discarding the packets presented to them for forwarding in a selfish manner in order to save energy [
5]. The number of nodes depends on the MANET network and of course [
6], if it is in an urban or in a rural area. When there is a non-planned event, normal mobility routes change, and new rescue and evacuation routes are recalculated. The main objective of this work is to determine which of the Ad Hoc strategies reviewed, has a better performance. For the comparative analysis on QoS parameters [
7], we chose one routing protocol from each of the following groups: proactive, reactive and hybrid [
8,
9]. The simulation was performed for any urban area, under the Random Obstacle Mobility Model, for twenty-four scenarios, and with help of the NS2 (Network Simulator version 2.35) tool [
10].
2. Related Work
2.1. Routing Protocols
Proactive routing protocols maintain information on all routes throughout the network, even if they are not required, so each node can have them registered [
11]. Generally, these protocols exchange control information between nodes to keep updated routing tables in the entire network [
12]. They also react when a new node appears or when another node is no longer within the network topology. The most known proactive protocols are Destination-Sequence Distance-Vector (DSDV) [
13] and Optimized Link State Routing (OLSR) [
14].
Currently, several types of research have been carried out on reactive and proactive routing protocols in MANET. Among the results, studies show that routing protocols have good quality of service performance, but this depends on the context in which it is linked in the analysis. On the other hand, it is also important to clarify that these protocols are developed from link-state or distance-vector routing algorithms, which represent the techniques that allow them to extract information related to the network topology [
15]
The DSDV protocol [
13] solves the major problem associated with distance vector routing of wired networks i.e., Count-to-infinity, by using destination sequence number. The DSDV protocol requires each mobile station to advertise to each of its current neighbors. However, this protocol also requires each node to maintain routing tables. These routing tables may cause a significant amount of memory overhead at each node as the size of the network increases.
Optimized Link State Routing (OLSR) [
14] is a point-to-point protocol based on the traditional link state algorithm. In this protocol, topology information is periodically exchanged by using link state messages. The advantage of OLSR is that it minimizes the size of each protocol message and the number of rebroadcasting nodes during each route update by employing a multipoint replying strategy.
As mentioned above, when a change occurs, updates are propagated through the network to keep routing tables on day. It is an ongoing assessment of the routes between nodes. However, these events can cause serious overloading in the network, affecting the utilization of bandwidth, performance and energy [
2]. In static topologies, this routing scheme can adapt and work properly, but for highly dynamic topologies, the network may not perform in terms of scalability [
16].
Reactive routing protocols only allow on-demand updating of the tables. For example, when a unique node wants to exchange information in the network, an on-demand routing protocol typically includes two components:
Route Discovery: If the source does not have the route towards the destination in its current routing table, it broadcasts a route discovery packet throughout the network. Once the route between the source and destination has been established, the data could be transmitted through the selected route.
Route Maintenance: Due to the dynamic nature of MANETs, failure of the links through the route may happen. Route maintenance is a mechanism to handle the route breaks. A node can confirm if a packet is correctly received on its downstream node (backward Route), by using any of the three types of acknowledgments: link-level, passive (listening to the forwarding by next-hop node), and network-layer.
Among the most known reactive protocols are: Dynamic Source Routing (DSR) [
17] and Ad Hoc Demand Distance Vector (AODV) [
8,
18]. The Ad hoc on Demand Distance Vector (AODV) [
19] routing protocol is based on the DSDV and DSR [
17,
20,
21] protocols. It provides unicast, multicast, and broadcast communication. It uses the periodic beaconing and sequence numbering procedure of DSDV, and a similar route discovery procedure as used in DSR. However, there are major differences between DSR and AODV. The most distinguishing is that in DSR each packet carries full routing information whereas in AODV the packets only carry the destination address, meaning that AODV has potentially fewer routing overheads than DSR [
20]. DSR protocol requires each transmitted packet to carry the full address from the source to the destination likewise the mechanism used in AODV. This mechanism in DSR makes it not to perform effectively in large networks, since the amount of overhead carried in these packets is increased dramatically as the size of network grows [
16,
22]. Hence, in highly dynamic and large networks the overhead may consume a large amount of bandwidth. However, this protocol has several advantages over routing protocols such as AODV and TORA (Temporally Ordered Routing Algorithm) [
23] and in small to moderately size networks, this protocol performs better.
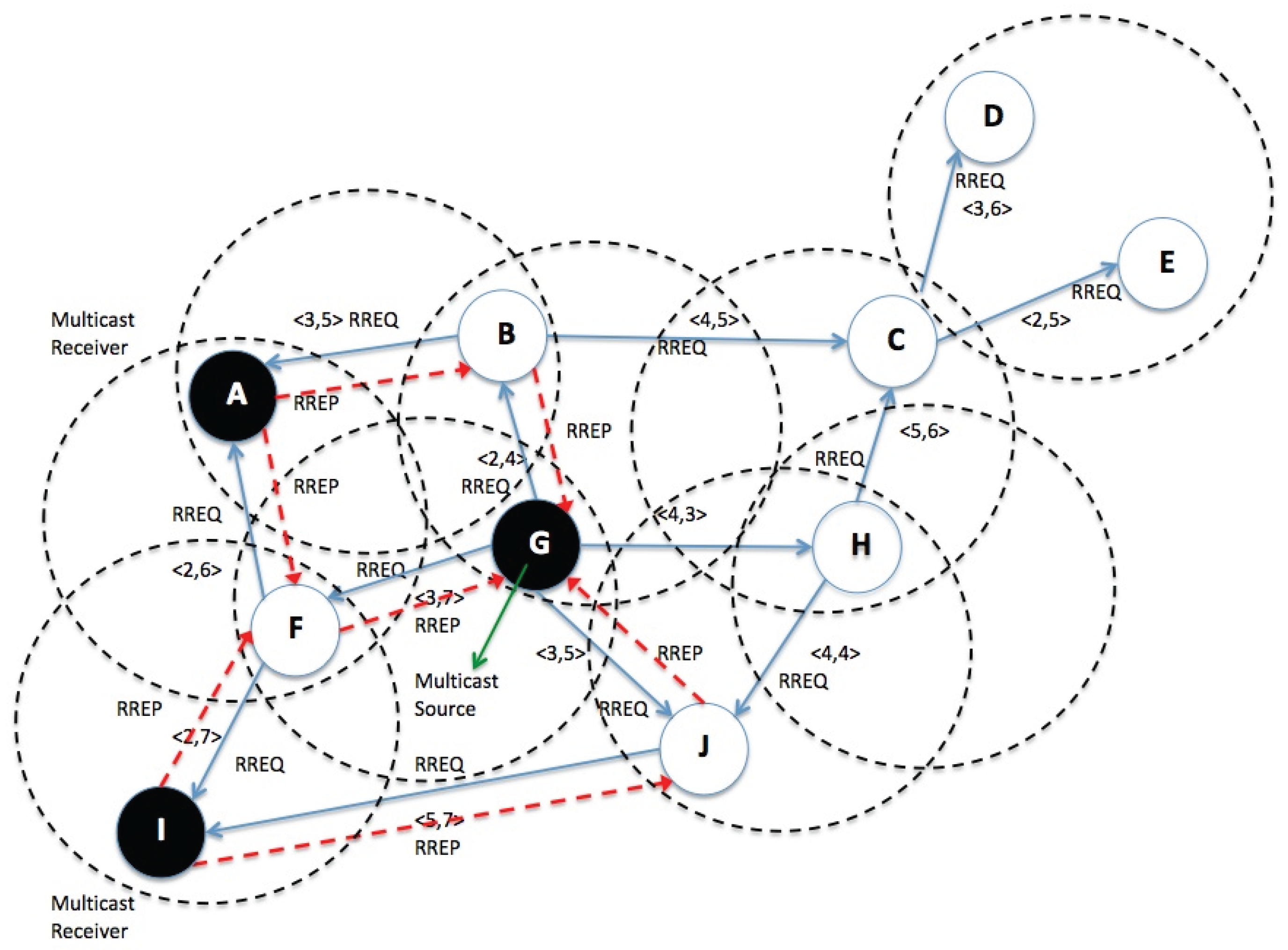
Hybrid routing. This sort of routing combines reactive and proactive features. For our specific case, within this classification we find the AOMDV routing protocol, an AODV extension, which allows calculating several disjoint paths without loops and without links. AOMDV [
24] can be used to find node-disjoints or link-disjoint routes. To find node-disjoint paths, each node does not reject duplicate RREQs immediately. Each Route Request (RREQ), which arrives via a neighbor different from the source, defines a path of node-disjoints. This is because the nodes cannot broadcast duplicated RREQs, so any RREQ arriving at an intermediate node through a neighbor, could not have passed through the same node. In an attempt to get multiple link-disjoint paths, the destination responds duplicating RREQs. After the first jump, Route Replies (RREPs) traverse the return paths that are node-disjoints and therefore link-disjoints. The trajectories of each RREP can be cut at an intermediate node, but each one of them has a different return path to the source for ensuring link disjunction [
24,
25]. In general terms, the advantage of using AOMDV is that it concedes intermediate nodes to respond to RREQs, while disjoint paths are still being screened. Of course, always considering that AOMDV has more overhead messages during the route discovery, since it is a multipath protocol, and it suffers increased flooding.
Figure 1 shows components and communications processes of a hybrid AOMDV routing protocol.
2.2. Mobility Model
In the context of networks, solutions are needed for efficient and effective information management in order to solve problems related to resource scarcity, such as energy, storage, bandwidth, and connectivity of communication devices [
26]. It is believed that when algorithms self-organize and cooperate, they are more likely to overcome constraints, which would lead them to better comply with service quality parameters. That is why mobile ad hoc networks (MANETs) are considered to use multicasting as a way to optimize the use of available bandwidth. This multicasting feature saves resources because it sends a single set of data to many receivers at once, reducing the cost of communication in a network.
One of the most used methods for evaluating the characteristics of Ad Hoc routing protocols is through simulation. With a simulation we obtain a number of significant benefits including repeatable scenarios, removal or changes of parameters, and exploration of a variety of metrics.
Once the nodes are set in a certain area, the mobility model governs the displacement of the nodes within the network [
27,
28,
29].
In general, the mobility model can be categorized either as a synthetic mobility model or as a based-on-traces mobility model [
30]. In the synthetic mobility model, nodes move according to certain rules and equations. Moreover, the nodes in the based-on-trace mobility model are sustained on information of real trace files. These files are obtained by tracking the mobility of nodes in real scenarios. The synthetic mobility model has attracted much attention in recent decades because of its simplicity. Taking this particular type of mobility model, the Ad Hoc network’s performance has been evaluated under different patterns [
30]. So far, the Random Waypoint Mobility Model is the most used one in Ad Hoc networks. However, it may not be accurate for real-life scenarios. The nodes do not follow a uniform density, as the central positions are heavier than others. That’s why for the simulation of the analyzed routing AOMDV, DSDV and AODV protocols, we used the Random Obstacle Mobility Model, which applies for a broader range of movement possibilities in urban areas.
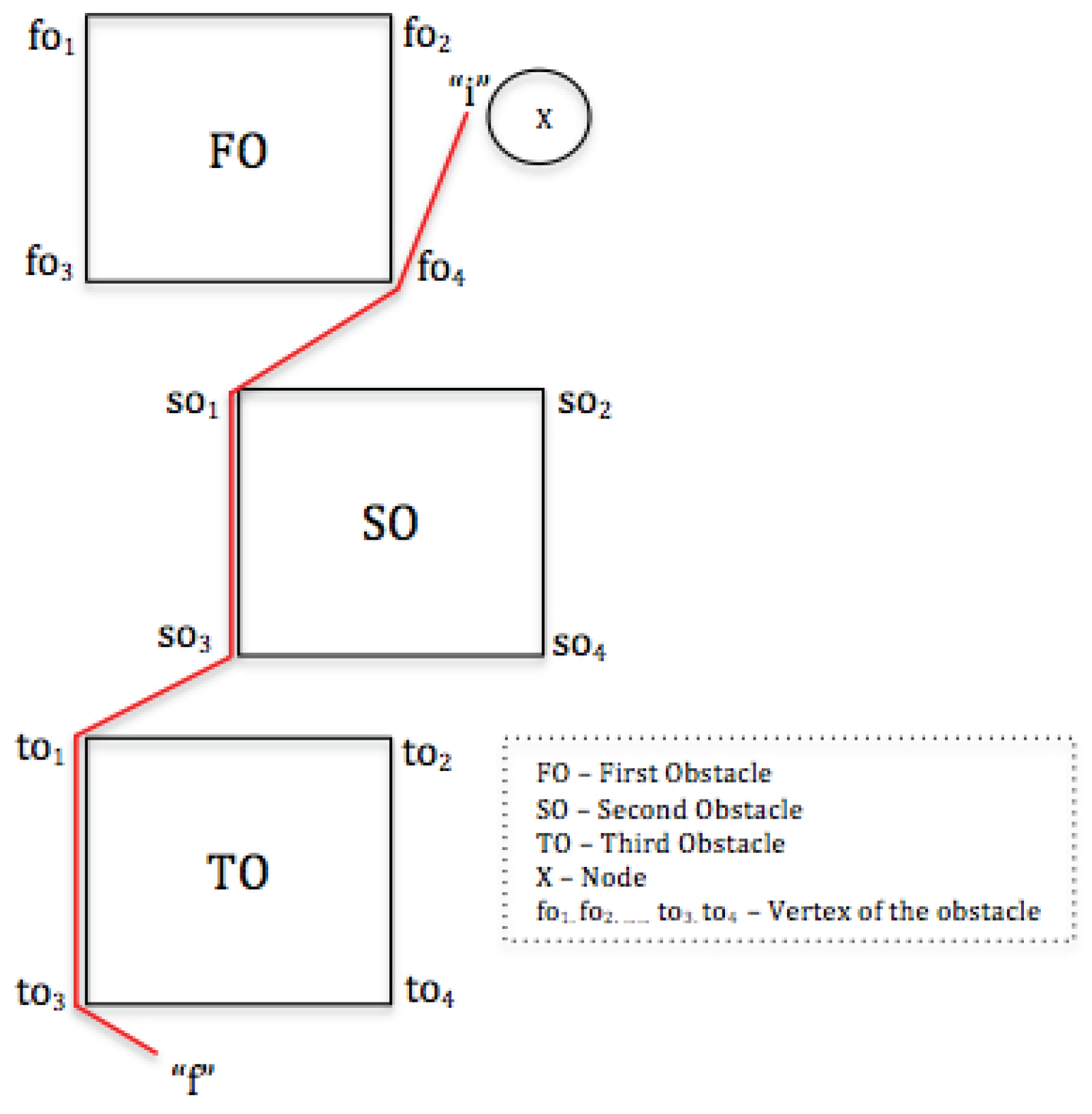
The purpose of this approach is to also consider the applications in various emergency scenarios or disaster areas, where, for instance, rescue teams such as doctors, firefighters, police and more, operators, are facing a stage full of obstacles. The X node first sets i as the start point of mobility and f as the destination, then it analyzes the vertex so
1 and so
2 from the nearest obstacle from f node, which is SO. In case this vertex is inaccessible due to a SO obstacle, the node selects a vertex fo
4, nearest to obstacle FO and to the so
1 vertex from SO. This is done until reaching your destination f, as shown in
Figure 2.
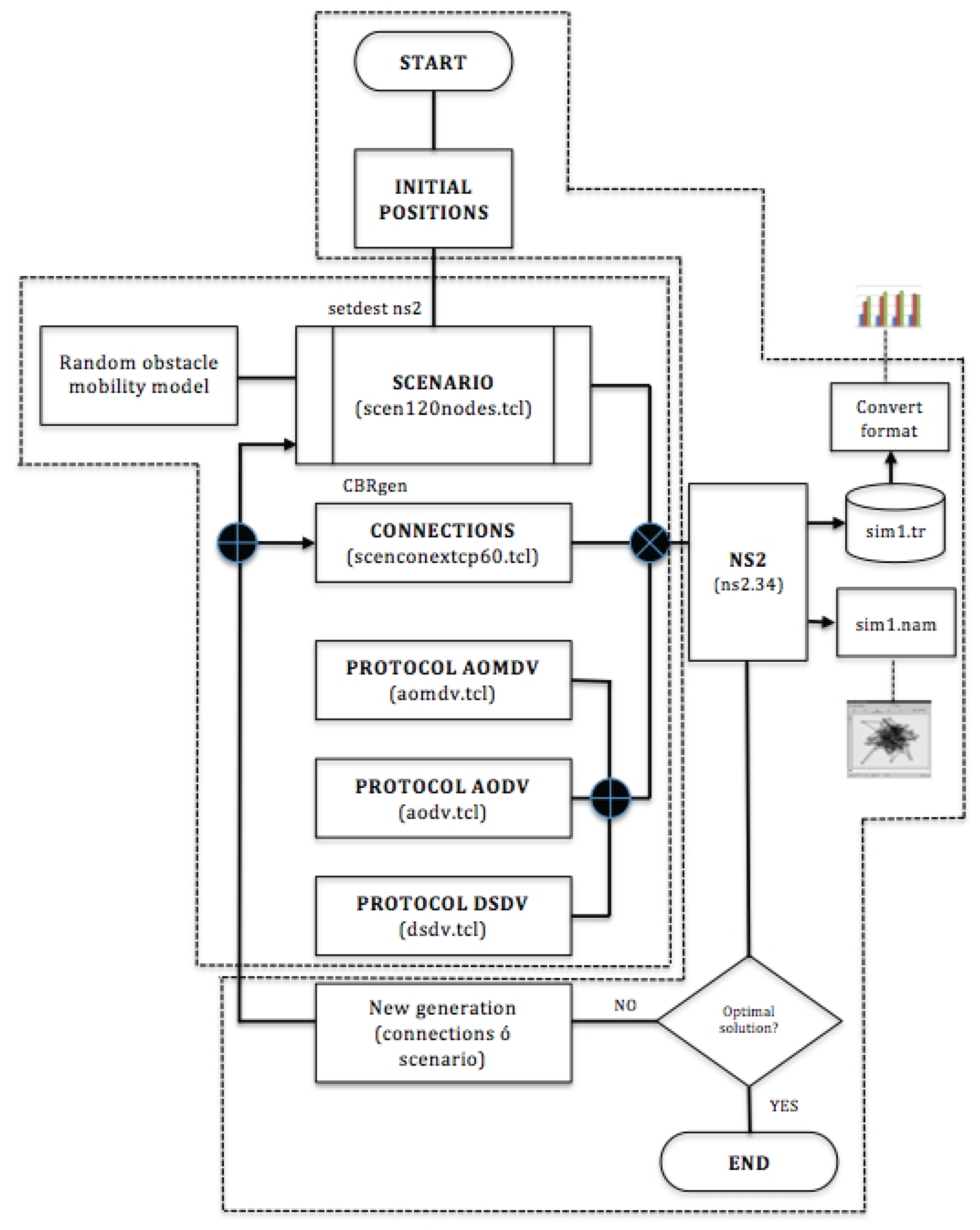
Our design sets a mobility model that reflects a realistic behavior of people around obstacles. When a person moves to a particular point, it is reasonable to assume that he will try to go dodging the obstacles in the way, to reach the desired destination, even if at the end, this is not the most optimal path in terms of the total distance. In most cases, obstacles are presumably unknown for a person moving in those areas and cases. Below is the architecture process considering all components from the beginning of the simulation to the general results here discussed (
Figure 3).
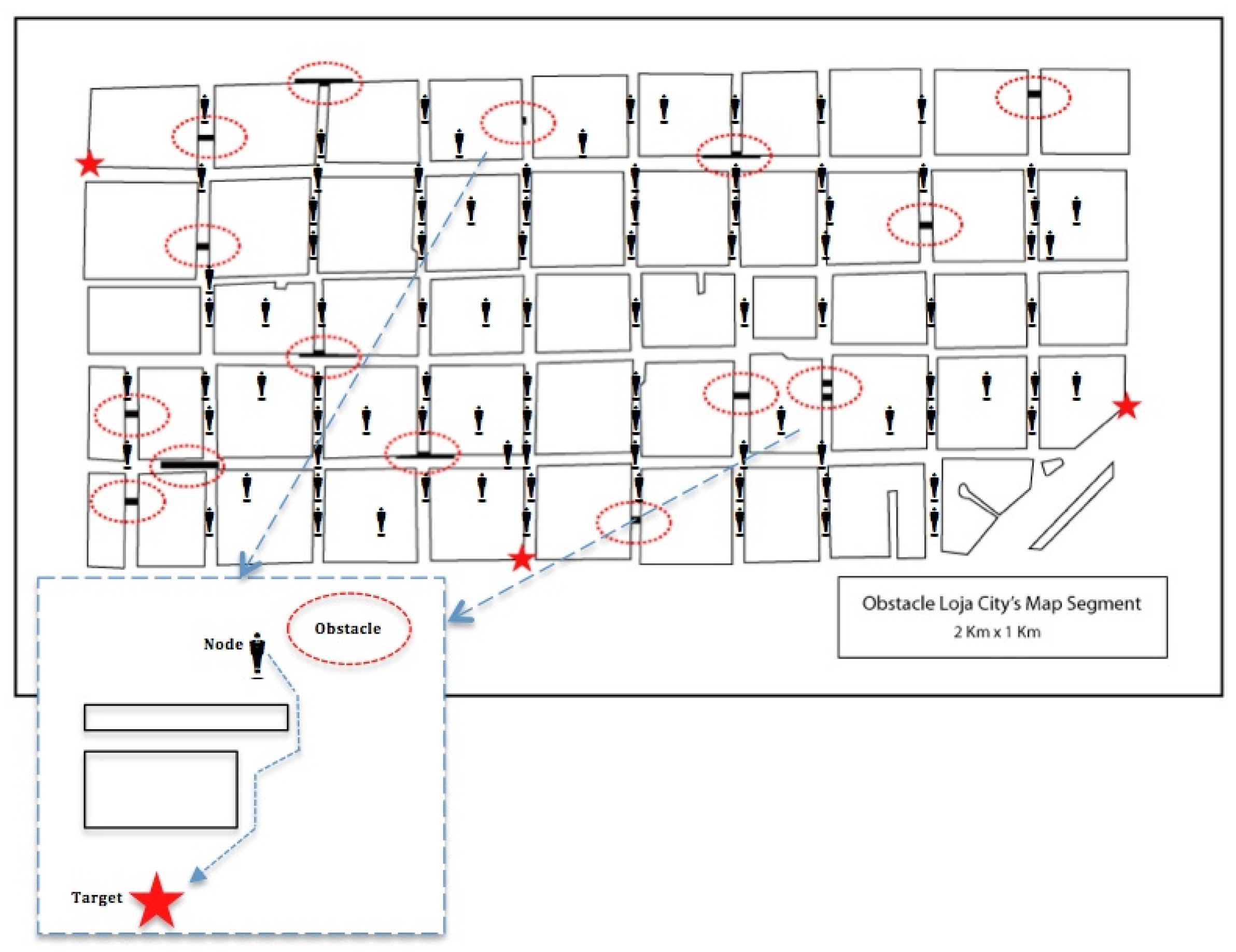
Next, we will set the variables to simulate scenarios, starting with the calculation of the node densities in an area of 1000m x 2000m (
Figure 4).
3. Materials and Methods
3.1. Simulation process of Real scenario chosen and node density calculation
The calculation of the node density P
nodes
is supported by information obtained from the Ecuadorian census in 2010. An important factor for the calculation of the node density is the percentage of the Economically Active Population (PEA). To calculate the density of nodes the following equation has been proposed [
7,
31].
- Number of people in the urban areas
- Urban smartphone factor
- Loja - PEA is 62% for urban area
- Urban factor specified for the simulation area
- Urban area
- Chosen area for simulation
We found that Pnodes1, Pnodes2 and Pnodes3 are 90, 120 and 150, respectively. The node densities for simulation are: Pnodes0 = 90, Pnodes1 = 97, Pnodes2 = 120 and Pnodes3 = 150.
3.2. Creating Scenarios
Using a terminal, we entered the following directory: ns-allinone, then we ac- cessed ns2.35/indeputils/cmugen/setdest/setdest, in order to create a scenario of 120 nodes with the following command /set- dest-v 120-2-n-m 2 s 1 m 6-t- 150-P-1-p 2 x 2000-and 1000. The sample was successfully created and named Scenario1. This should be replicated to the other scenarios we need to create. In the command shown: run-v 2, which is the scenario generator version; we identify: n, which means the number of nodes; s, is the kind of speed (1 = Uniform); minspeed, represented with lowercase m, is the minimum speed in m/s; maxspeed, represented with uppercase m, is the maximum speed in m/s; -t, indicating the simulation time in seconds; -P is the pause time simulation in seconds; maxX, the size in meters for the X dimension; maxY, the size in meters for the Y dimension; and finally [outdir = file], Filename motion itself scenario name. The directory should be reopened to verify the creation of all scenarios.
3.3. Creating Connections
First, we entered ns-allinone, then, the next route is ns2.35/indeputils/cmugen/setdest/. In this direction, the cbrgen.tcl file is located, this file functions as a basis to create the connections, it should be emphasized that for this scenario we created two types of connections 30 and 60 for 90, 97, 120 and 150 nodes. To generate the connections, we accessed via a terminal ns2.35 and executed the following command: ns cbrgen.tcl-type tcp-nn 120 seed-mc 60-rate rate 2 > scenconextcp60. Where: tcp -, is the type of traffic; nn -, indicates the number of nodes in the simulation; seed, random seed; mc -, connections number of connections; - rate, indicates the baud rate in pkts/sec; and finally [outdir=file] that becomes the file name connections.
3.4. Characteristics and Performance Metrics of Routing Protocols in MANETs
Commonly, there are four main metrics presented in [
32] as parameters of QoS which are dropped packet (or packet delivery ratio), delay (route latency), jitter (delay variance), and bandwidth.
Table 1 provides a list of popular qualitative and quantitative properties and characteristics of MANET routing protocols as well [
33,
34]. Some of the metrics in [
34] are applied to compare proactive and reactive routing protocols in terms of overhead, scalability, and loop-freedom. The purpose of referring to performance metrics in this paper is to correlate proactive, reactive and hybrid protocols according to these metrics. Considering that some publications have contrasted routing protocols using the packet delivery ratio, control overhead, hop count, and end-to-end delay, the performance of routing protocols in this paper is mostly evaluated in terms of delay, jitter and dropped packets with random obstacle mobility model. To define the simulation scenarios, we used the same basis as in [
39,
40]. Some of these values are shown in the
Table 2.
In order to analyze results and measure behavior of protocols, we selected some indicators from [
33,
41]. These indicators are performance, protocol overhead, packet dropped, average delay and the variation of the delay or jitter. They are all compared with those of the following protocols: AOMDV, AODV and DSDV.
4. Results
The NS2 simulator [
10] is used to determine protocols behaviour with the data shown in
Table 1. In order to determine which is the best protocol, we considered the following indicators:
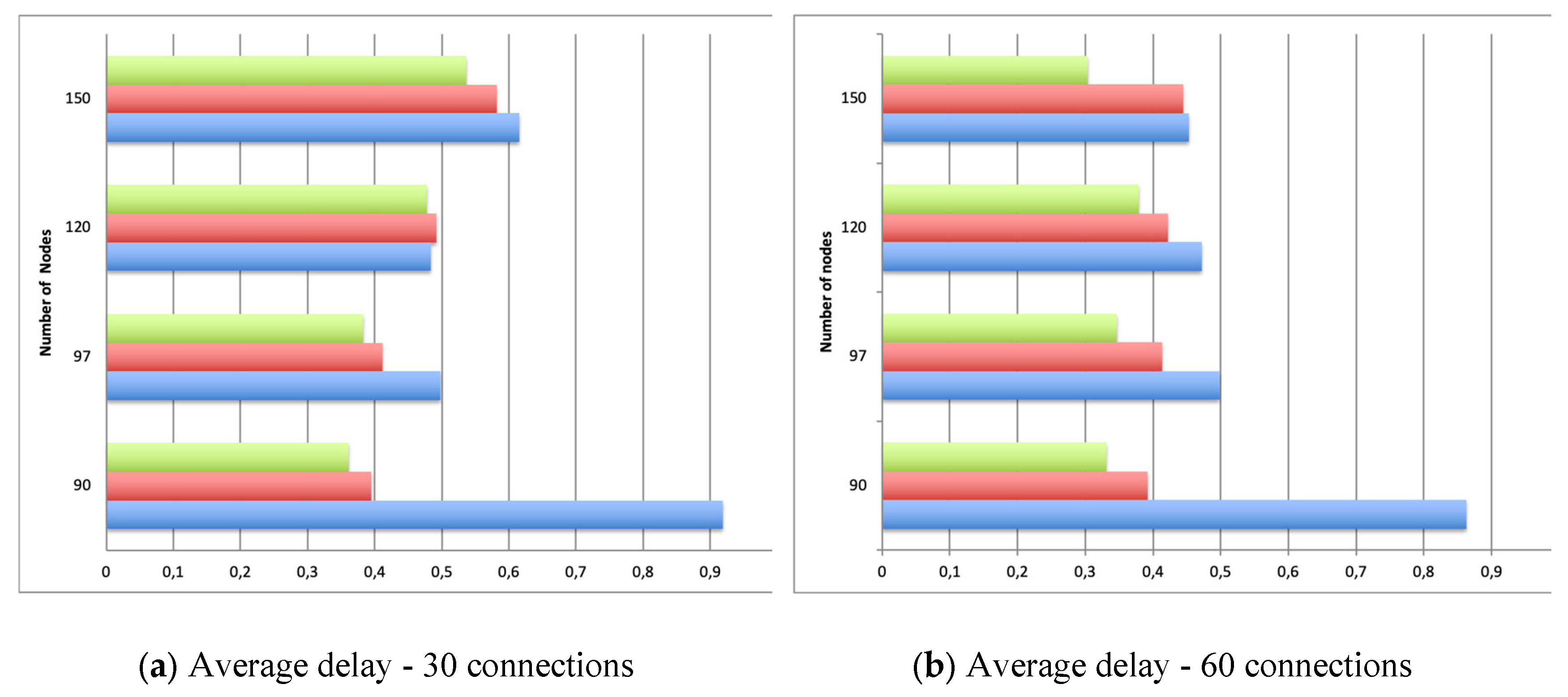
– Average Delay. This is very significant to measure for our purpose, because there is a need to send and receive network management information as soon as possible. With 30 connections, and with 120 and 150 nodes, AOMDV protocol yields little delays. Instead, with 60 connections, the panorama changes to demonstrate a great advantage in AOMDV usage over AODV and DSDV. Collected data is shown in
Table 3,
Table 4,
Figure 5 (a), and
Figure 5 (b).
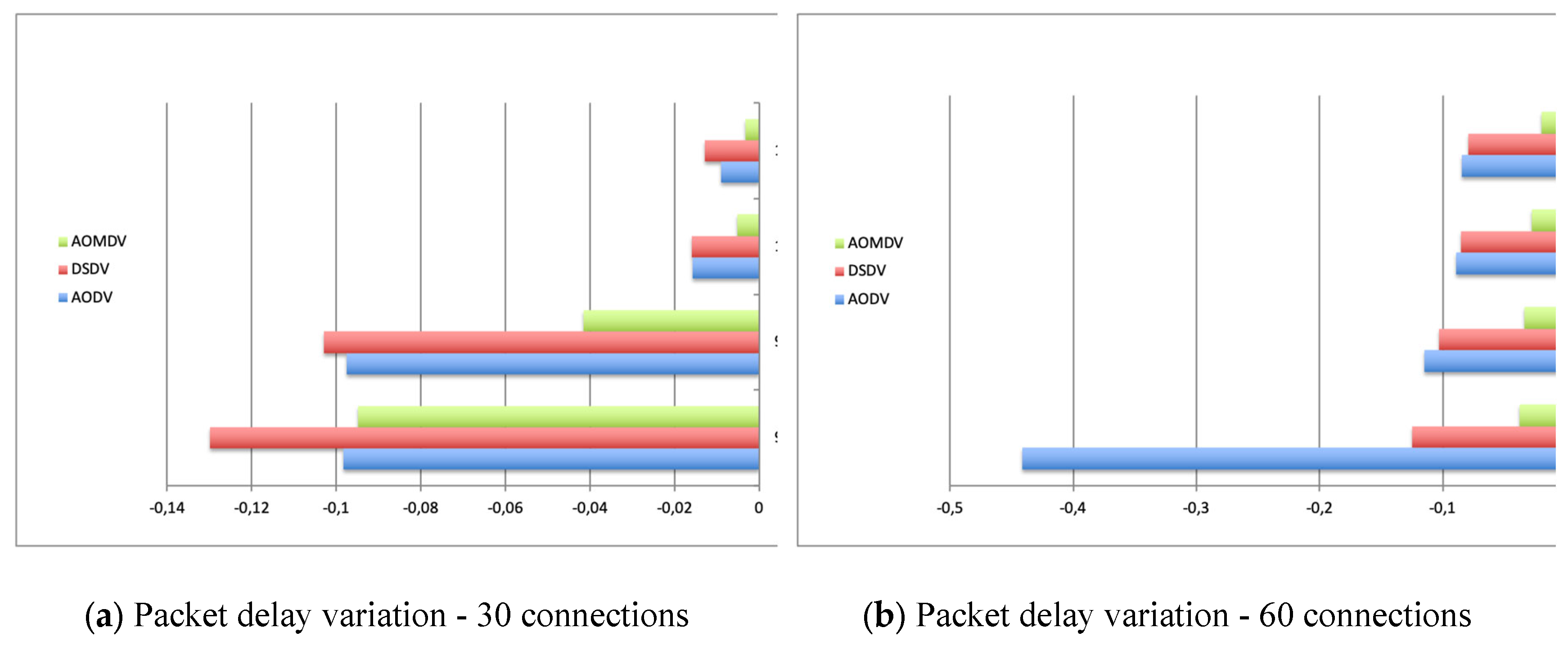
– Packet delay variation. It is the difference or delay between end-to-end communication selected packets. In MANETs, it allows to measure convergence and network stability.
This parameter is related to the mean fluctuation and helps us to determine which one of the three protocols would be the most appropriate. The protocol with the lower jitter is the best, and it is the AOMDV. The simulation results are shown in
Table 5,
Table 6,
Figure 6 (a) and
Figure 6 (b).
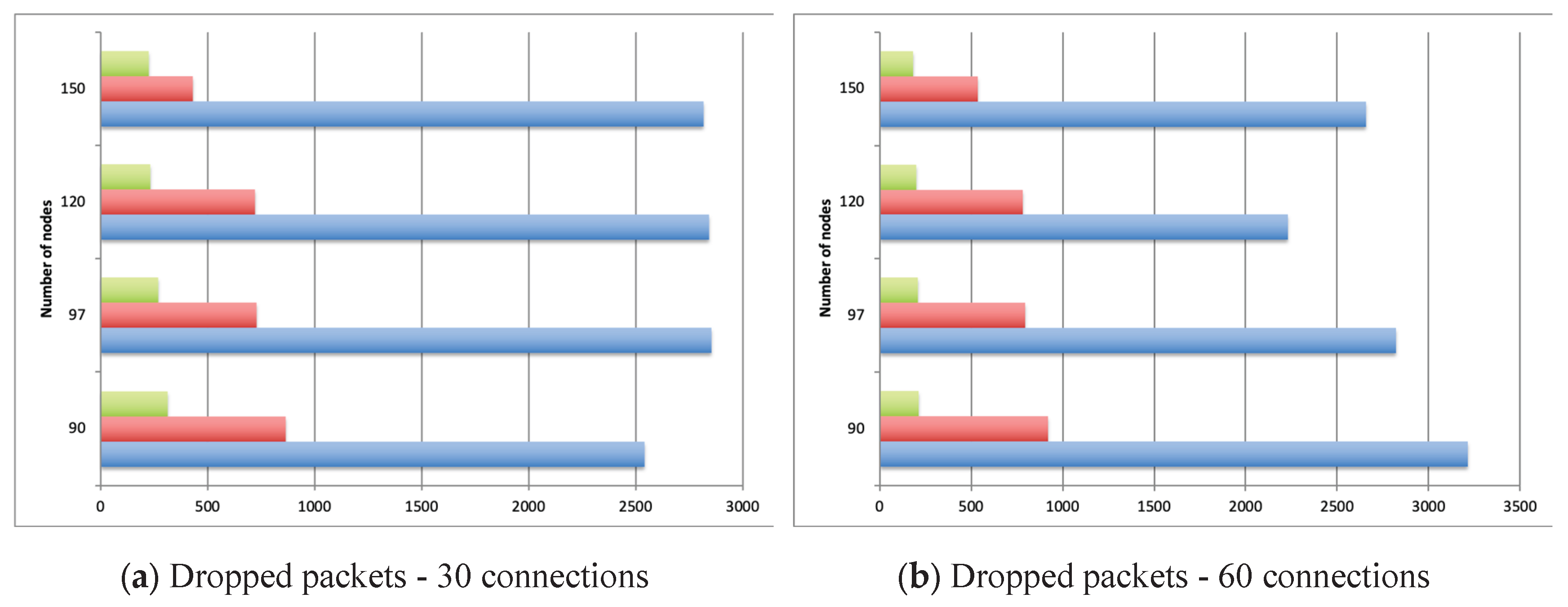
– Dropped Packet. This is the number of packets dropped by intermediate nodes due to the effects produced by its own continuous mobility, timer expiration, and unreachable destinations by Address Resolution Protocol (ARP).
The purpose of this simulation is to set up which of the three routing protocols developed shows better QoS characteristics. According to the analysis, the protocol that removes fewer packets during transmission is the AOMDV protocol, both with 30 and with 60 connections. Data is shown in
Table 7 y
Table 8,
Figure 7 (a) and
Figure 7 (b).
5. Conclusions
Mobility models are representations of human behavior that require prior analysis and should be analyzed in all their dimensions. In this article they were implemented on a defined and simulated urban area, considering random obstacles, and governed by various parameters such as time of simulation, number of nodes, and others.
The Random Obstacle Mobility Model grants QoS parameters to be analyzed reliably in routing protocols simulations to adapt for more unpredictable cases in this research.
Finally, of the twenty-four simulated scenarios under AODV, DSDV and AOMDV routing protocols, the one that has greater compatibility with the Random Obstacle Mobility Model, and best QoS characteristics at the communication time between nodes is the AOMDV.
Author Contributions
Conceptualization, L.E.; methodology, L.E.; software, L.E.; validation, L.E.; formal analysis, L.E.; investigation, L.E.; resources, L.E; data curation, L.E.; writing—original draft preparation, L.E.; writing—review and editing, L.E.; visualization, L.E.; supervision, L.E.; project administration, L.E.
Funding
This research received no external funding.
Institutional Review Board Statement
This study is exempt from IRB approval as it does not include personally identifiable data and is presented in a general manner.
Informed Consent Statement
Not applicable. The study did not involve human participants or identifiable personal data.
Data Availability Statement
The original contributions presented in this study are included in the article. Further inquiries can be directed to the corresponding authors.
Conflicts of Interest
The authors declare no conflict of interest.
Abbreviations
The following abbreviations are used in this manuscript:
| OLSR |
Optimized Link State Routing |
| DSR |
Dynamic Source Routing |
| AODV |
Ad Hoc On Demand Distance Vector |
| DSDV |
Destination Sequence Distance Vector |
| AOMDV |
Ad Hoc On Demand Multiple Distance Vector |
| RREQ |
Route Request |
| RREP |
Route Replies |
| NS2 |
Network Simulator Version 2 |
| MANET |
Mobile Ad Hoc Network |
References
- Padmavathy, N.; Chaturvedi, S. K. Evaluation of mobile ad hoc network reliability using propagation-based link reliability model. Reliability Engineering System Safety 2013, vol. 115(no. 0), 1–9. [Google Scholar] [CrossRef]
- Ahmed, S.; Javaid, N.; Yousaf, S.; Ahmad, A.; Sandhu, M.; Imran, M.; Khan, Z.; Alrajeh, N. Co-laeeba: Cooperative link aware and energy efficient protocol for wireless body area networks. Computers in Human Behavior 2015, vol. 51, 1205–1215. [Google Scholar] [CrossRef]
- Saleem, K.; Derhab, A.; Al-Muhtadi, J.; Shahzad, B.; Orgun, M. Secure transfer of environmental data to enhance human decision accuracy. Computers in Human Behavior 2015, vol. 51, 632–639. [Google Scholar] [CrossRef]
- Liu, N.; Yu, R. Identifying design feature factors critical to acceptance and usage behavior of smartphones. Computers in Human Behavior 2017, vol. 70, 131–142. [Google Scholar] [CrossRef]
- Chiejina, E.; Xiao, H.; Christianson, B. A Dynamic Reputation Management System for Mobile Ad Hoc Networks. Computers 2015, 4, 87–112. [Google Scholar] [CrossRef]
- Cho, J.-H.; Swami, A.; Chen, I.-R. A survey on trust management for mobile ad hoc networks. IEEE Communications Surveys and Tutorials 2011, vol. 13(no. 4), 562–583. [Google Scholar] [CrossRef]
- Quispe, L. E.; Galan, L. M. Assessment of Throughput Performance under NS2 in Mobile Ad Hoc Networks (MANETs). 2013 Fifth International Conference on Computational Intelligence, Communication Systems and Networks, Madrid, Spain, 2013; pp. 338–343. [Google Scholar] [CrossRef]
- Enciso, L.; Mengual, L. Analysis of qos parameter in aodv a dsr in mobile ad hoc networks; 2012; pp. 276–279. [Google Scholar] [CrossRef]
- Enciso, L.; Tandazo, R.; Mengual, L. Analysis of ad hoc routing protocols for emergency and rescue scenarios; 2012; pp. 781–786. ISBN 978-989-8565-08-2. [Google Scholar] [CrossRef]
- NS2. The Network Simulator NS-2. Available online: http://www.isi.edu/nsnam/ns/.
- R. Amin, S. Ashrafch, M. Akhtar, and A. Khan, “Analyzing performance of ad hoc network mobility models in a peer-to-peer network application over mobile ad hoc network,” in Electronics and Information Engineering (ICEIE), 2010 International
Conference On, vol. 2, aug. 2010, pp. V2–344 –V2–348.
- Boukerche, A.; Turgut, B.; Aydin, N.; Ahmad, M. Z.; Bo ̈lo ̈ni, L.; Turgut, D. Routing protocols in ad hoc networks: A survey. Computer Networks 2011, vol. 55(no. 13), 3032–3080. [Google Scholar] [CrossRef]
- Ansari, J.; Ishak, M.K.; Ammar, K. “Combined Architecture of Destination Sequence Distance Vector (DSDV) Routing with Software Defined Networking (SDN) and Blockchain in Cyber-Physical Systems”. Computers, Materials and Continua 2025, 82, 2311–2330. [Google Scholar] [CrossRef]
- Schweitzer, N.; Cohen, L.; Dvir, A.; Stulman, A. Persuasive: A node isolation attack variant for OLSR-based MANETs and its mitigation. Ad Hoc Networks 2023, Volume 148, 103192. [Google Scholar] [CrossRef]
- Priyambodo, T. K.; Wijayanto, D.; Gitakarma, M. S. Performance Optimization of MANET Networks through Routing Protocol Analysis. Computers 2021, 10(no. 1), 2. [Google Scholar] [CrossRef]
- P. Gupta and P. Saxena, “Energy consumption in wireless ad hoc network,” in
Emerging Trends in Engineering and Technology (ICETET), 2010 3rd International Conference on, nov. 2010, pp. 831 –835.
- Johnson, D.; Hu, Y.; Maltz, D. “The Dynamic Source Routing Protocol (DSR)
for Mobile Ad Hoc Networks for IPv4,” ser. Request for Comments, no. 4728, Internet Engineering Task Force. IETF. February 2007. Available online: http://www.ietf.org/rfc/rfc4728.txt.
- Dafhalla, A.K.Y.; Elobaid, M.E.; Tayfour Ahmed, A.E.; Filali, A.; SidAhmed, N.M.O.; Attia, T.A.; Mohajir, B.A.I.; Altamimi, J.S.; Adam, T. Computer-Aided Efficient Routing and Reliable Protocol Optimization for Autonomous Vehicle Communication Networks. Computers 2025, 14, 13. [Google Scholar] [CrossRef]
- Priyambodo, T.K.; Wijayanto, D.; Gitakarma, M.S. Performance Optimization of MANET Networks through Routing Protocol Analysis. Computers 2021, 10, 2. [Google Scholar] [CrossRef]
- Satveer, K.; Manjit, S.; Varinder, K.A.; Shashi Bhushan, R.; Himali, S.; Butta, S. Simulative investigation of network scalability over MANET routing protocols. Procedia Computer Science, Volume Volume 252(2025), Pages 500–509. [CrossRef]
- Radwan, A.; Mahmoud, T.; Houssein, E. Evaluation comparison of some ad hoc networks routing protocols. Egyptian Informatics Journal 2011, vol. 12(no. 2), 95–106. [Google Scholar] [CrossRef]
- Rango, F. D.; Cano, J.-C.; Fotino, M.; Calafate, C.; Manzoni, P.; Marano, S. OLSR vs DSR: A comparative analysis of proactive and reactive mechanisms from an energetic point of view in wireless ad hoc networks. Computer Communications 2008, vol. 31(no. 16), 3843–3854. [Google Scholar] [CrossRef]
- Layuan, L.; Chunlin, L.; Peiyan, Y. Performance evaluation and simulations of routing protocols in ad hoc networks. Computer Communications 2007, vol. 30(no. 8), 1890–1898. [Google Scholar] [CrossRef]
- Parmar, A.; Vaghela, V.B. Detection and Prevention of Wormhole Attack in Wireless Sensor Network using AOMDV Protocol. Procedia Computer Science 2016, Volume 79, 700–707. [Google Scholar] [CrossRef]
- Balachandra, M.; P. K., v; M, K. Article: Enhancing the efficiency of wireless ad hoc networks by improving the quality-of-service routing; Foundation of Computer Science: New York, USA, July 2012; vol. 3, no. 5, pp. 51–59. [Google Scholar]
- Latif, S.; Fang, X.; Mohsin, S.M.; Abrar Akber, S.M.; Aslam, S.; Mujlid, H.; Ullah, K. An Enhanced Virtual Cord Protocol Based Multi-Casting Strategy for the Effective and Efficient Management of Mobile Ad Hoc Networks. Computers 2023, 12(no. 1), 21. [Google Scholar] [CrossRef]
- Babaei, H.; Fathi, M.; Romoozi, M. Obstacle mobility model based on activity area in ad hoc networks; 2007; vol. 4706, pp. 804–817. [Google Scholar] [CrossRef]
- Abed, A. K.; Oz, G.; Aybay, I. Influence of mobility models on the performance of data dissemination and routing in wireless mobile ad hoc networks. Computers Electrical Engineering 2013, no. 0. [Google Scholar] [CrossRef]
- Niewiadomska-Szynkiewicz, E.; Sikora, A.; Koodziej, J. Modeling mobility in cooperative ad hoc networks. In Mobile Networks and Applications; 2013; pp. 1–12. [Google Scholar] [CrossRef]
- Appiah, M. The impact of mobility models on the performance of mobile ad hoc network (MANET). 2016 International Conference on Advances in Computing and Communication Engineering (ICACCE), Durban, South Africa, 2016; pp. 208–213. [Google Scholar] [CrossRef]
- Enciso, L.; Mengual, L. Behavior of ad hoc routing protocols, analyzed for emergency and rescue scenarios, on a real urban area. Expert Systems with Applications 2014, vol. 41(no. 5), 2565–2573. [Google Scholar] [CrossRef]
- Latif, S.; Fang, X.; Mohsin, S.M.; Akber, S.M.A.; Aslam, S.; Mujlid, H.; Ullah, K. An Enhanced Virtual Cord Protocol Based Multi-Casting Strategy for the Effective and Efficient Management of Mobile Ad Hoc Networks. Computers 2023, 12, 21. [Google Scholar] [CrossRef]
- Kour, S.; Anand, A.; Thankur, K.; Singh, M.; Sarangal, H.; Singh, B.; Dub, S. Evaluation of MANET Routing Protocols: Effects of Terrain Dimensions and Network Scalability. Procedia Computer Science 259(2025), 1479–1489. [CrossRef]
- Zehre, K.M; Dalay, M.F; Koca, M.; Alam, S.F; Yildiz, M. Enhancing Performance in Mobile Ad-Hoc Networks via Expanded View of Network Topology. 2024 8th International Artificial Intelligence and Data Processing Symposium (IDAP), Malatya, Turkiye, 2024; pp. 1–5. [Google Scholar] [CrossRef]
- Chenchen, Y.; Xiaohong, L.; Dafang, Z. An obstacle avoidance mobility model. Intelligent Computing and Intelligent Systems (ICIS), 2010 IEEE International Conference on 2010, vol. 3, 130–134. [Google Scholar]
- Sengar, H. S.; Venkatesha, G. G.; Chauhan, P.; Mallela, I. R.; Bhimanapati, V.; Goel, O. Modelling and Analysis of Network Protocols for Mobile Ad-hoc Networks with Non-Ideal Conditions. 2025 International Conference on Pervasive Computational Technologies (ICPCT), Greater Noida, India; 2025, pp. 229–233. [CrossRef]
- Munir, A. Cluster Based Routing Protocols: A Comparative Study. 2015 Fifth International Conference on Advanced Computing & Communication Technologies, Haryana, India, 2015; pp. 590–594. [Google Scholar] [CrossRef]
- Akkari Sallum, E. E.; dos Santos, G.; Alves, M.; Santos, M. M. Performance analysis and comparison of the DSDV, AODV and OLSR routing protocols under VANETs. 2018 16th International Conference on Intelligent Transportation Systems Telecommunications (ITST), Lisboa, Portugal, 2018; pp. 1–7. [Google Scholar] [CrossRef]
- Brys, R.; Kosmowski, K.; Suchański, M. Challenges in Improving Routing Protocols in Ad Hoc Mobile Networks. 2025 35th International Conference Radioelektronika (RADIOELEKTRONIKA), Czech Republic; 2025, pp. 1–5. [CrossRef]
- Chiejina, E.; Xiao, H.; Christianson, B.A. Dynamic Reputation Management System for Mobile Ad Hoc Networks. Computers 2015, 4, 87–112. [Google Scholar] [CrossRef]
- Isha, Y.K.; Malik, A. Performance Analysis of Hybrid routing protocol. 2021 2nd International Conference on Intelligent Engineering and Management (ICIEM), London, United Kingdom, 2021; pp. 400–405. [Google Scholar] [CrossRef]
Figure 1.
Communication routing protocol AOMDV in the Ad Hoc networks.
Figure 1.
Communication routing protocol AOMDV in the Ad Hoc networks.
Figure 2.
An example of the random obstacle mobility model.
Figure 2.
An example of the random obstacle mobility model.
Figure 3.
Process of simulation of protocols under Random Obstacle Mobility Model.
Figure 3.
Process of simulation of protocols under Random Obstacle Mobility Model.
Figure 4.
Random Obstacle Mobility Model in area 1000m x 2000m.
Figure 4.
Random Obstacle Mobility Model in area 1000m x 2000m.
Figure 5.
Average delay - 30 and 60 connections with 90, 97, 120 and 150 nodes.
Figure 5.
Average delay - 30 and 60 connections with 90, 97, 120 and 150 nodes.
Figure 6.
Packet delay variation - 30 and 60 connections with 90, 97, 120 and 150 nodes.
Figure 6.
Packet delay variation - 30 and 60 connections with 90, 97, 120 and 150 nodes.
Figure 7.
Dropped Packets - 30 and 60 connections with 90, 97, 120 and 150 nodes.
Figure 7.
Dropped Packets - 30 and 60 connections with 90, 97, 120 and 150 nodes.
Table 1.
General parameters and characteristics for the simulation of AODV, DSDV and AOMDV protocols.
Table 1.
General parameters and characteristics for the simulation of AODV, DSDV and AOMDV protocols.
| Parameter |
Value |
Observations and related works |
| Simulation area |
1000m x 2000m |
Area established within the center of the city of Loja |
| Mobility model |
Obstacle Models |
Obstacle models [35,36] |
| Number of nodes |
90, 97, 120 and 150 |
To determine the behavior of protocols for different node densities |
| Number of connections |
30, 60 |
random connections |
| Time of simulation |
150 |
seconds |
| Network layer protocols |
AOMDV [24,37], DSDV [38] and AODV [18] |
Proactive and reactive protocols |
Table 2.
Variables and parameters in the script for the simulation of protocols AODV, DSDV and AOMDV.
Table 2.
Variables and parameters in the script for the simulation of protocols AODV, DSDV and AOMDV.
| Variable |
Value |
Observations |
| set val(chan) |
Channel /Wireless- Channel |
Channel Type |
| set val(prop) |
Propagation /TwoRayGround |
radio- propagation model |
| set val(netif) |
Phy/WirelessPhy |
network interface type |
| set val(mac) |
Mac/802.11 |
MAC type |
| set val(ifq) |
Queue/DropTail /PriQueue |
interface queue type |
| set val(ll) |
LL |
link layer type |
| set val(ant) |
Antenna/ Omni- Antenna |
antenna model |
| set val(ifqlen) |
100 |
max packet in ifq |
| set val(nn) |
150 |
number of mobile nodes |
| set val(rp)
|
AODV |
routing protocol |
| *set val(rp)
|
AOMDV |
routing protocol |
| *set val(rp)
|
DSDV |
routing protocol |
| set val(x)
|
2000 |
area |
| set val(y)
|
1000 |
area |
| set val(connections)
|
”scenconextcp60” |
connections |
| set val(scenario) |
”scen120nodes” |
scenario |
| set val(stop) |
150 |
time simulation |
Table 3.
Average delay - 30 connections with 90, 97, 120 and 150 nodes.
Table 3.
Average delay - 30 connections with 90, 97, 120 and 150 nodes.
| Number of nodes |
AODV (30c) |
DSDV (30c) |
AOMDV (30c) |
| 90 |
0.918654 |
0.394391 |
0.361367 |
| 97 |
0.498009 |
0.411367 |
0.383271 |
| 120 |
0.483952 |
0.492132 |
0.477534 |
| 150 |
0.615480 |
0.582582 |
0.536986 |
Table 4.
Average delay - 60 connections with 90, 97, 120 and 150 nodes.
Table 4.
Average delay - 60 connections with 90, 97, 120 and 150 nodes.
| Number of nodes |
AODV (60c) |
DSDV (60c) |
AOMDV (60c) |
| 90 |
0.863285 |
0.392374 |
0.331367 |
| 97 |
0.498023 |
0.414231 |
0.346918 |
| 120 |
0.471993 |
0.421802 |
0.379617 |
| 150 |
0.452916 |
0.444208 |
0.303840 |
Table 5.
Packet delay variation or Average Jitter - 30 connections with 90, 97, 120 and 150 nodes.
Table 5.
Packet delay variation or Average Jitter - 30 connections with 90, 97, 120 and 150 nodes.
| Number of nodes |
AODV (30c) |
DSDV (30c) |
AOMDV (30c) |
| 90 |
-0.098328 |
-0.129873 |
-0.094765 |
| 97 |
-0.097499 |
-0.102874 |
-0.041516 |
| 120 |
-0.015795 |
-0.015821 |
-0.005149 |
| 150 |
-0.009072 |
-0.012745 |
-0.003136 |
Table 6.
Packet delay variation or Average Jitter - 60 connections with 90, 97, 120 and 150 nodes.
Table 6.
Packet delay variation or Average Jitter - 60 connections with 90, 97, 120 and 150 nodes.
| Number of nodes |
AODV (60c) |
DSDV (60c) |
AOMDV (60c) |
| 90 |
-0.441367 |
-0.124643 |
-0.037436 |
| 97 |
-0.114973 |
-0.102764 |
-0.033419 |
| 120 |
-0.088908 |
-0.085109 |
-0.027638 |
| 150 |
-0.084256 |
-0.079349 |
-0.019921 |
Table 7.
Dropped Packets - 30 connections with 90, 97, 120 and 150 nodes.
Table 7.
Dropped Packets - 30 connections with 90, 97, 120 and 150 nodes.
| Number of nodes |
AODV (30c) |
DSDV (30c) |
AOMDV (30c) |
| 90 |
2543 |
863 |
314
|
| 97 |
2820 |
799 |
269
|
| 120 |
3207 |
631 |
245 |
| 150 |
2819 |
429 |
224 |
Table 8.
Dropped Packets - 60 connections with 90, 97, 120 and 150 nodes.
Table 8.
Dropped Packets - 60 connections with 90, 97, 120 and 150 nodes.
| Number of nodes |
AODV (60c) |
DSDV (60c) |
AOMDV (60c) |
| 90 |
3214 |
921 |
211 |
| 97 |
2820 |
796 |
206 |
| 120 |
2206 |
751 |
198 |
| 150 |
2659 |
496 |
184 |
|
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).