Submitted:
26 January 2026
Posted:
05 February 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
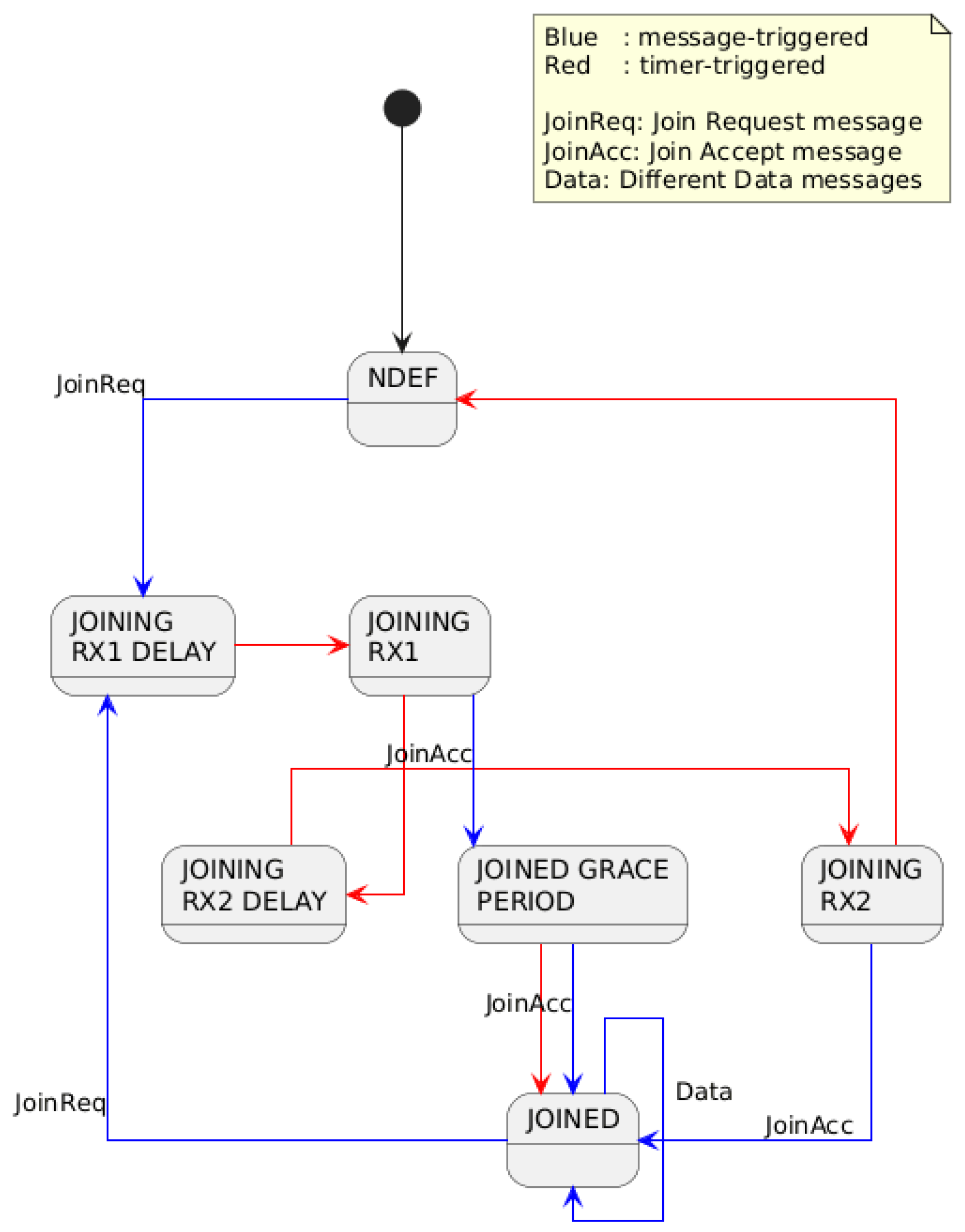
- Protocol-Aware Formalization of the OTAA Procedure. We present a finite state machine (FSM)–based formalization of the LoRaWAN Over-The-Air Activation (OTAA) procedure, explicitly modeling valid protocol states, message sequences, and timing constraints. Unlike packet-centric or statistical approaches, the proposed model captures the semantic correctness of protocol progression.
- State-Based Characterization of OTAA Security Weaknesses. We systematically reinterpret known OTAA weaknesses, such as DevNonce reuse, replay conditions, join flooding, and state desynchronization, such as violations of expected state transitions rather than isolated packet anomalies. This perspective enables structured and interpretable detection of protocol misuse.
- Integration with SOC-Oriented LoRaWAN Monitoring Pipelines. Building on our earlier work on SOC-compatible LoRaWAN telemetry ingestion, we position the FSM model as a logical validation layer operating on enriched protocol metadata. The proposed approach complements existing SIEM-based observability mechanisms by adding formal protocol semantics without assuming full payload visibility.
- Digital-Twin–Style Detection Model for Encrypted LoRaWAN Traffic. We demonstrate how a state-machine-based digital twin of the OTAA procedure enables intrusion detection even under constrained observability and encrypted communication, relying on protocol-level metadata and state consistency rather than deep packet inspection.
- Foundations for Extensible State-Aware IDS Design. While this work focuses on OTAA, the presented methodology is intentionally generic and can be extended to other phases of the LoRaWAN protocol or to similar low-power IoT systems where security-relevant behavior is inherently state-dependent.
2. Background
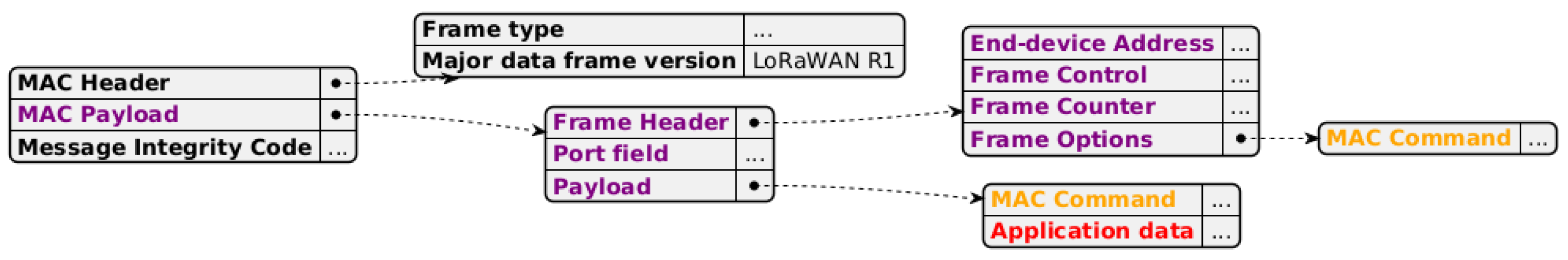
2.1. LoRa, LoRaWAN
2.2. OTAA
3. Related Work
3.1. Security Weaknesses and Attack Surfaces of OTAA
DevNonce Reuse and Replay Conditions
Join Requests Flooding and Activation Abuse
Join Accept Manipulation and Desynchronization Effects
Timing and State Transition Violations
3.2. Intrusion Detection Systems and Digital Twin Solutions in IoT Networks
State-Based IDS Approaches for LoRaWAN
Digital Twin–Based Anomaly Detection in IoT
Positioning of the Present Work
4. Methodology and Prior Work
4.1. Threat Model and Observability Assumptions
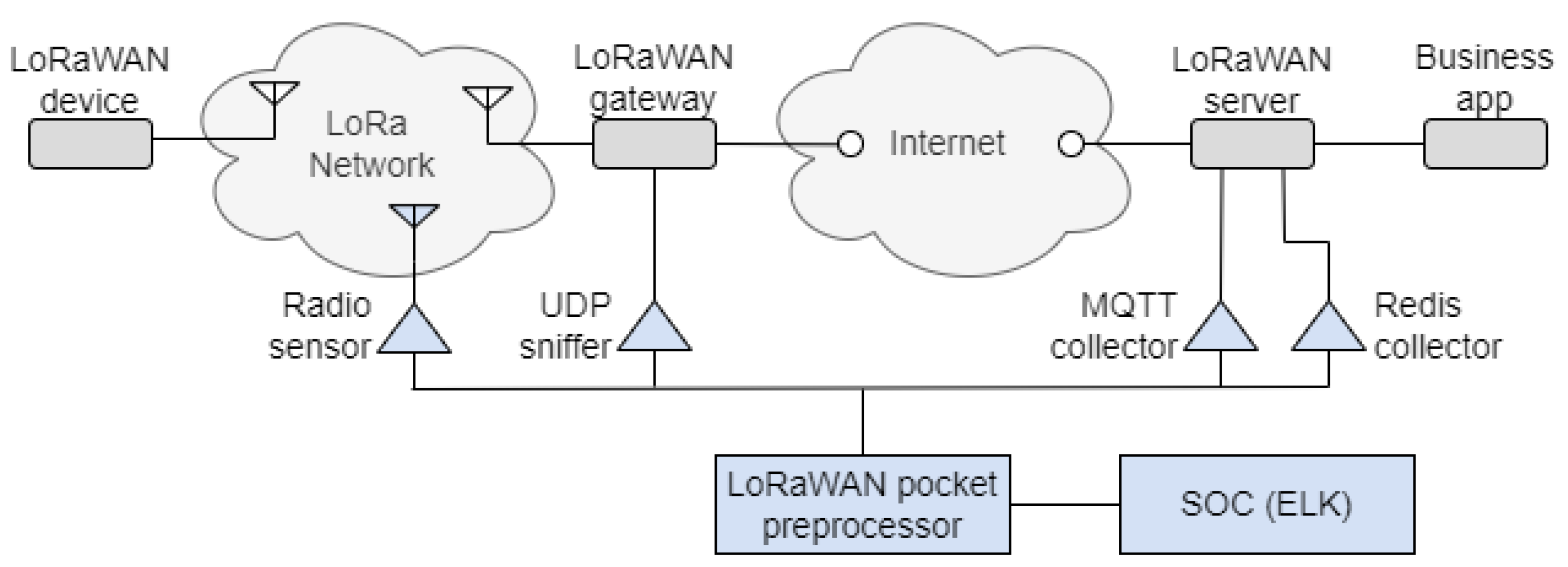
4.2. Prior Work: SOC-Compatible Telemetry Pipeline
4.3. Approach Overview: Protocol-Aware Digital Twin as Detection Core
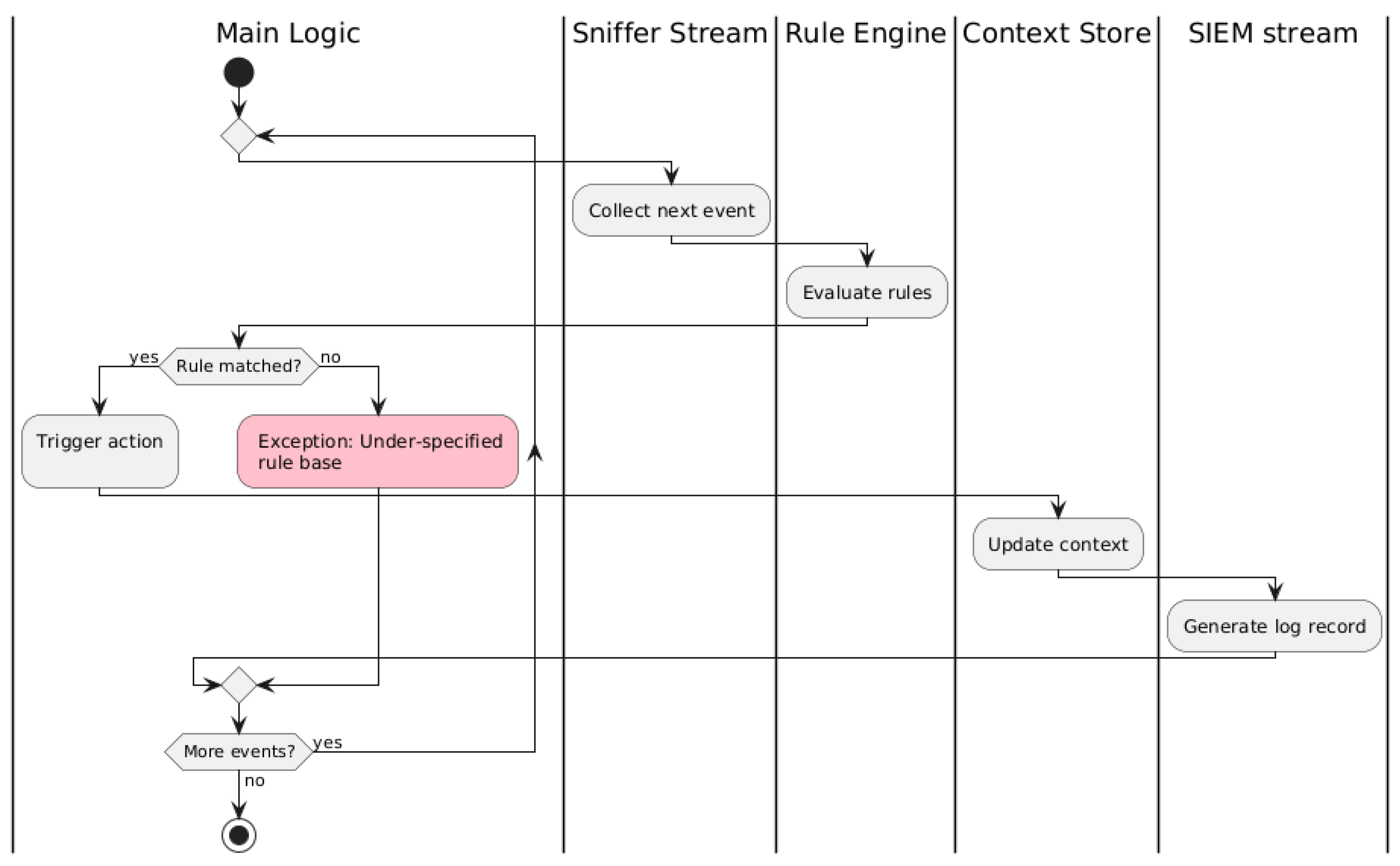
4.4. Finite State Machine–Based IDS
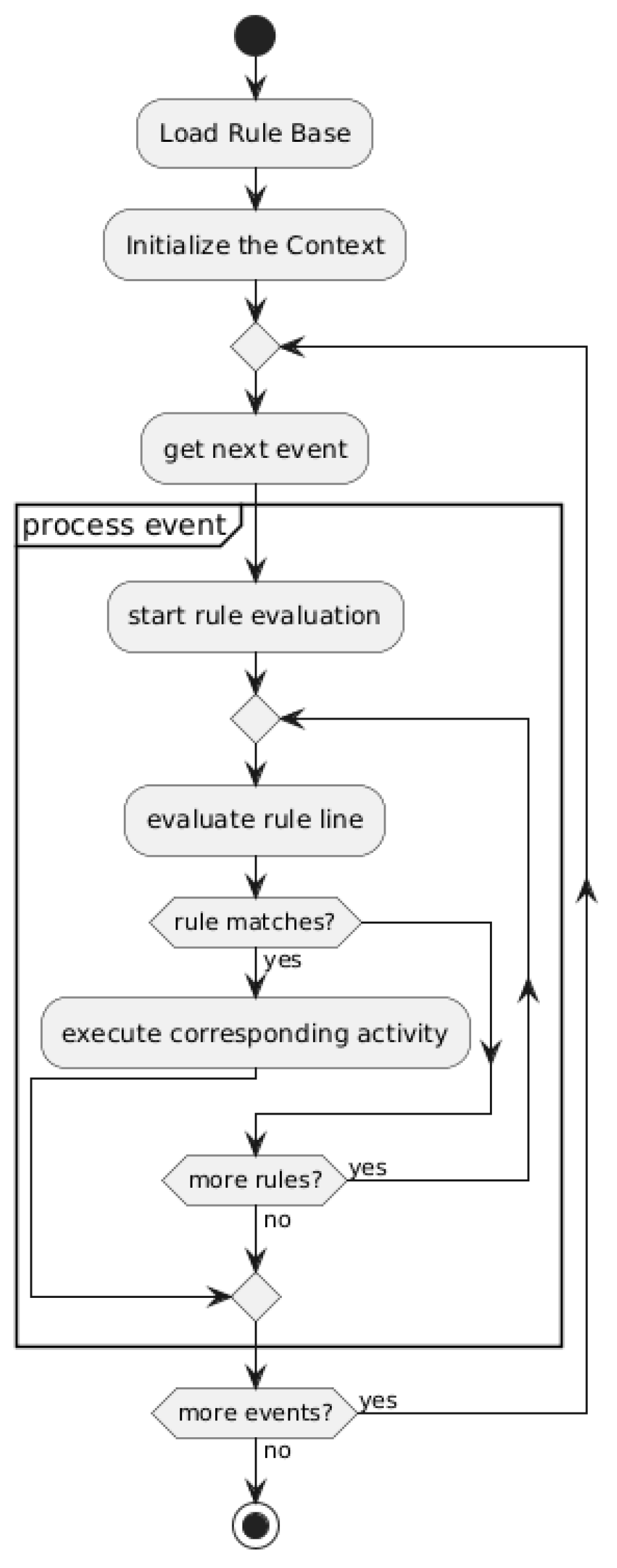
4.5. Formal Description of the Digital Twin Rule Engine
4.5.1. Notation and Semantics
4.5.2. States, Events, and Timers
4.5.3. Radio Layer Constraints (Level 0)
4.5.4. Flow Guard Constraints (Level 1)
4.5.5. Security Constraints (Level 2)
4.5.6. State Transition Flow (Level 3)
5. Experimental Setup and System Implementation
5.1. LoRaWAN Testbed Environment
5.2. Monitoring Points and Data Acquisition
- MQTT-based monitoring: decoded telemetry published by the gateway forwarders and network server is captured by subscribing to relevant MQTT topics. Messages encoded in Protobuf format are decoded and transformed into structured JSON records.
- Redis-based frame log access: internal frame logs maintained by the ChirpStack network server are retrieved from Redis streams using authenticated API access. These logs provide detailed protocol-level context, including message types, device identifiers, and session-related metadata.
5.3. Preprocessing Pipeline and FSM Integration
5.4. SIEM Integration and Visualization
6. Results
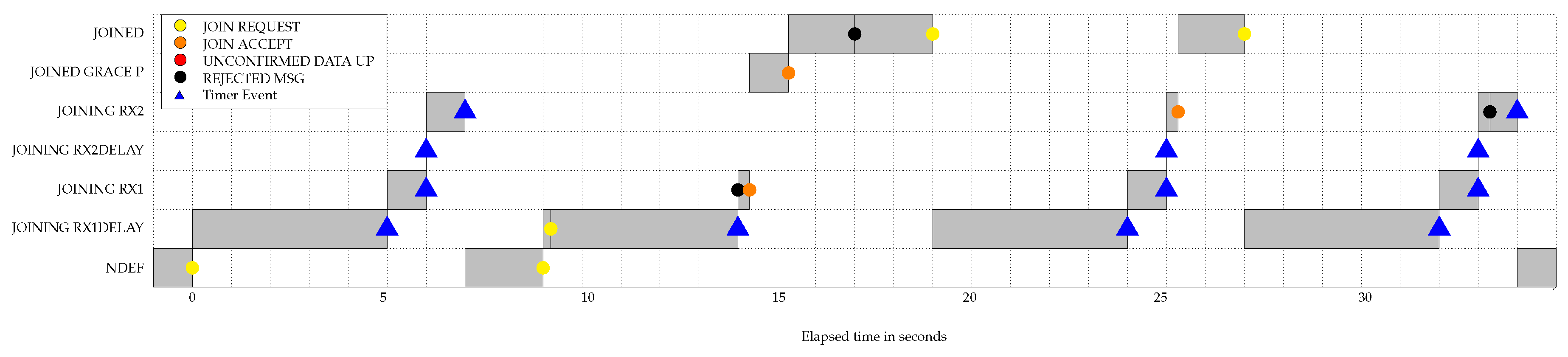
6.1. FSM State Evolution and Detection Outcomes
6.2. Handling of Benign Deviations and Recovery
6.3. Detection of Suspicious but Tolerated Behavior
6.4. Cryptographic and Protocol-Level Enforcement
6.5. SIEM-Level Interpretability
6.6. FSM-Based End-Device State Evolution
7. Discussion
7.1. What the Approach Adds Beyond Conventional LoRaWAN Monitoring
7.2. Relation to Our Prior Pipeline and to Existing Approaches
7.3. Limitations
7.4. Future Directions
8. Conclusions
Author Contributions
Acknowledgments
Code Availability
Conflicts of Interest
References
- Tolvaly-Roşca, F.; Fekete, G.; Bíró, I.; Fekete, A.Z.; Forgó, Z. Real-Time IoT Solution to Monitor and Control dMVHR Units in Real-Life Environment. Acta Polytechnica Hungarica 2024, 21. [CrossRef]
- Pekarčík, P.; Chovancová, E.; Chovanec, M.; Štancel, M. A Centralized Approach to Intrusion Detection System Management: Design, Implementation and Evaluation. Acta Polytechnica Hungarica 2025, 22, 7–26. [CrossRef]
- Bringye, Z.; Fleiner, R.; Umhauser, B.; Aradi, M.; Kail, E. Extending SOC Capabilities to LoRaWAN: A Cloud-Integrated Intrusion Detection Framework for IoT Networks. Acta Polytechnica Hungarica 2026, 23. [CrossRef]
- Alliance®, L. LoRaWan Specification 1.0.3.
- Semtech Corporation. LoRa Technology Overview. https://www.semtech.com/lora, n.d. Accessed: January 10, 2026.
- Alliance®, L. LoRaWan Specification 1.1.
- Butun, I.; Pereira, N.; Gidlund, M. Security Risk Analysis of LoRaWAN and Future Directions. Future Internet 2018, 11, 3. [CrossRef]
- Eldefrawy, M.; Butun, I.; Pereira, N.; Gidlund, M. Formal security analysis of LoRaWAN. Computer Networks 2019, 148, 328–339. [CrossRef]
- Hessel, F.; Almon, L.; Hollick, M. LoRaWAN Security: An Evolvable Survey on Vulnerabilities, Attacks and their Systematic Mitigation. ACM Transactions on Sensor Networks 2023, 18. [CrossRef]
- Loukil, S.; Fourati, L.; Nayyar, A.; Chee, K.W.A. Analysis of LoRaWAN 1.0 and 1.1 Protocols Security Mechanisms. Sensors 2022, 22. [CrossRef] [PubMed]
- Tomasin, S.; Zulian, S.; Vangelista, L. Security analysis of lorawan join procedure for internet of things networks. In Proceedings of the 2017 IEEE Wireless Communications and Networking Conference Workshops (WCNCW). IEEE, 2017, pp. 1–6.
- Spadaccino, P.; Cuomo, F. Intrusion Detection Systems for IoT: opportunities and challenges offered by Edge Computing and Machine Learning. arXiv preprint arXiv:2012.01174 2022. arXiv:2012.01174 [cs]. arXiv:2012.01174. [CrossRef]
- Verzegnassi, E.G.M.; Tountas, K.; Pados, D.A.; Cuomo, F. Data conformity evaluation: a novel approach for IoT security. In Proceedings of the 2019 IEEE 5th World Forum on Internet of Things (WF-IoT). IEEE, 2019, pp. 842–846.
- Liao, H.J.; Lin, C.H.R.; Lin, Y.C.; Tung, K.Y. Intrusion detection system: A comprehensive review. Journal of network and computer applications 2013, 36, 16–24. [CrossRef]
- Danish, S.M.; Nasir, A.; Qureshi, H.K.; Ashfaq, A.B.; Mumtaz, S.; Rodriguez, J. Network Intrusion Detection System for Jamming Attack in LoRaWAN Join Procedure. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), 2018, p. 1–6. [CrossRef]
- Horák, T.; Střelec, P.; Kováč, S.; Tanuška, P.; Nemlaha, E. Detection of IoT communication attacks on LoRaWAN gateway and server. In Proceedings of the Computer Science On-line Conference. Springer, 2023, pp. 489–497.
- Fu, Y.; Yan, Z.; Cao, J.; Koné, O.; Cao, X. An Automata Based Intrusion Detection Method for Internet of Things. Mobile Information Systems 2017, 2017, 1–13. [CrossRef]
- Le, A.; Loo, J.; Chai, K.; Aiash, M. A Specification-Based IDS for Detecting Attacks on RPL-Based Network Topology. Information 2016, 7, 25. [CrossRef]
- Fuller, A.; Fan, Z.; Day, C.; Barlow, C. Digital twin: enabling technologies, challenges and open research. IEEE access 2020, 8, 108952–108971. [CrossRef]
- Eckhart, M.; Ekelhart, A. Towards security-aware virtual environments for digital twins. In Proceedings of the Proceedings of the 4th ACM workshop on cyber-physical system security, 2018, pp. 61–72.
- Homaei, M.; Morales, V.G.; Gutierrez, O.M.; Gomez, R.M.; Caro, A. Smart Water Security with AI and Blockchain-Enhanced Digital Twins. arXiv preprint arXiv:2504.20275 2025. arXiv:2504.20275 [cs]. arXiv:2504.20275. [CrossRef]
- El-Hajj, M. Leveraging Digital Twins and Intrusion Detection Systems for Enhanced Security in IoT-Based Smart City Infrastructures. Electronics 2024, 13, 3941. [CrossRef]
- Schösser, A.; Khursheed, D.; Schulz, P.; Burmeister, F.; Fettweis, G. Digital Twin of the Radio Environment: A Novel Approach for Anomaly Detection in Wireless Networks; IEEE, 2023. [CrossRef]
- Bringye, Z. LoRa_FSM: Finite State Machine–Based Digital Twin for LoRaWAN OTAA. https://github.com/zsoltbringye/LoRa_FSM, 2025. Accessed: 2025-05-26.
- ChirpStack. ChirpStack Open-Source LoRaWAN Network Server. https://www.chirpstack.io/, 2025. Accessed: May 26, 2025.
- Elastic. Elastic Stack (ELK): Elasticsearch, Kibana & Logstash. https://www.elastic.co/elastic-stack, 2025. Accessed: May 26, 2025.

| State | Description |
|---|---|
| Idle or reset state, no active join procedure | |
| Waiting for the opening of the RX1 reception window | |
| RX1 reception window active | |
| Waiting for the opening of the RX2 reception window | |
| RX2 reception window active | |
| Device successfully activated and joined to the network |
| Composite State | Description |
|---|---|
| Set of states in which a Join Request message is admissible | |
| Set of states in which a Join Accept message may be processed |
| ID | Scenario description | Deviation type | FSM final state | Detection level | SIEM outcome |
|---|---|---|---|---|---|
| S1 | Join-Request → Join-Accept → Data | None (baseline) | JOINED | – | No alert |
| S2 | Join-Request with reused DevNonce observed from another gateway, followed by Join-Accept and Data | DevNonce reuse (multi-GW) | JOINED | L2 (Sec) | Notice |
| S3 | Join-Request with invalid MIC | MIC integrity violation | NDEF | L2 (Sec) | Reject |
| S4 | Join-Request transmitted on invalid frequency | Radio parameter violation | NDEF | L0 (Radio) | Reject |
| S5 | Join-Request → timeout → new Join-Request (new DevNonce) → Join-Accept → Data | Timing deviation with recovery | JOINED | L3 (Flow) | Notice |
| S6 | Join-Request → Join-Accept received only in RX2 window | RX1 window miss | JOINED | L3 (Timing) | Notice |
| S7 | Join-Request → Join-Accept received after RX2 window | RX window violation | NDEF | L3 (Timing) | Reject |
| S8 | Join-Request → timeout → repeated Join-Request with identical DevNonce | Replay after timeout | NDEF | L2 (Sec) | Reject |
| S9 | Join-Request → Join-Accept with invalid MIC | MIC integrity violation | NDEF | L2 (Sec) | Reject |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




