Submitted:
05 January 2026
Posted:
06 January 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Quantum Encryption Paradigms: From Key Distribution to Direct Encryption
1.2. Phase Space: The Arena for Optical Quantum Encryption
- Phase Operators (): Implementing rotations , these operators form the basis of the original Quantum Public Key Envelope (QPKE) protocol [10]. The same physical principle—randomizing the phase of a coherent state—was subsequently adapted for symmetric-key physical-layer encryption, leading to the QEPS-p scheme. This adaptation has been extensively studied via simulation [11,12,13] and experimental demonstrations [14,15] for the QPKE scheme and experimental demonstration for QEPS-p symmetric encryption [13]. However, pure phase encryption exhibits an inherent limitation: while effective for phase-encoded data (e.g., PSK), it becomes partially vulnerable for modulation formats that encode information in both amplitude and phase, such as quadrature amplitude modulation (QAM), as amplitude information remains partially exposed.
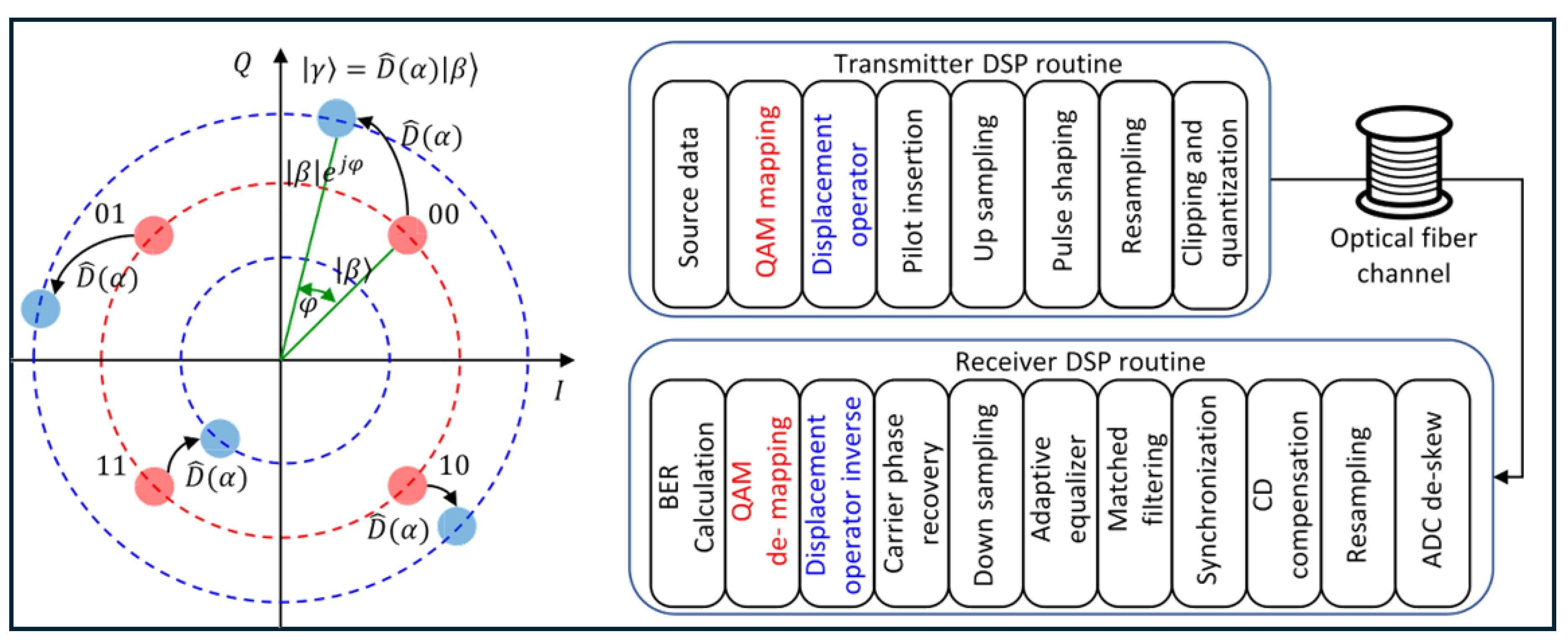
- Displacement Operators (): To address this limitation, QEPS-d schemes were developed, employing the reduced displacement operator (defined by its action ) that translates coherent states across the entire phase space. This approach overcomes the amplitude-sensitivity of pure phase encryption by randomizing both quadratures, thereby enabling the secure encryption of arbitrary QAM formats [16,17]. Crucially, these reduced operators commute (), making QEPS-d practically implementable with standard coherent optical hardware while expanding the cipher space to include the full two-dimensional constellation plane [18].
- Dynamic Displacement Operators (DDOs): Building upon both preceding approaches, the most recent advancement combines displacement and phase operations in time-varying sequences, , yielding QEPS-dd. This dynamic framework creates a highly randomized and expansive cipher space through the continuous evolution of encryption parameters and according to cryptographic algorithms. By introducing temporal variability alongside spatial obfuscation, QEPS-dd offers enhanced security against advanced cryptanalytic techniques and adapts more robustly to evolving threat models [19,20].
1.3. Quantum Public-Key Encryption in Phase Space
1.4. The Broader Landscape of Optical Physical-Layer Security
1.5. Chaos-Based Optical Encryption: A Comparative Perspective
- Security Foundation: Chaos security relies on computational hardness—the difficulty of reconstructing nonlinear dynamics from intercepted signals. While sensitive to parameter mismatches, this security is not information-theoretic and can be vulnerable to advanced system identification or machine-learning attacks with sufficient intercepted signal length [39,40].
- Synchronization Requirement: Most chaos schemes require active synchronization between transmitter and receiver, either through common drive signals, matched parameters, or digital post-processing. This introduces a potential point of failure and added complexity, especially in dynamic or impaired channels [41,42].
- Dual-Channel Architecture: Many chaos synchronization schemes (particularly drive-response configurations) inherently require two optical channels or signals: one for the chaotic carrier and another for the encrypted message, or dedicated synchronization preambles. This increases system complexity and reduces spectral efficiency compared to single-channel approaches.
- Implementation Complexity: High-bandwidth chaos generation often involves specialized laser configurations, optical feedback loops, or careful parameter tuning, which can increase cost and reduce compatibility with standard telecom hardware [29].
- Single-Channel Operation: QEPS operates over a single optical channel—the same channel used for standard coherent communication. No separate drive signals, synchronization channels, or pilot transmissions are required. Encryption and decryption are performed entirely within the standard modulation and demodulation process.
- DSP Phase Synchronization as Cryptographic Control: In QEPS, the essential DSP function of carrier phase recovery (CPR) becomes cryptographically controlled. Authorized receivers use the shared secret to apply the inverse transformation before CPR, restoring a stable constellation that enables standard DSP to succeed. Unauthorized receivers cannot establish a phase reference, causing their CPR algorithms to fail and resulting in BER near 50%. Thus, QEPS transforms a routine DSP requirement into a cryptographic barrier.
- No Continuous Synchronization Needed: Unlike chaos systems requiring continuous dynamical synchronization, QEPS decryption is a deterministic inversion of a unitary transformation using a shared key sequence.
- Hardware Compatibility: QEPS transformations (phase shifts, displacements) are natively implemented using standard IQ modulators and coherent transceivers, ensuring seamless integration into existing optical networks.
- Security Based on Physical Law: Security arises from the quantum noise of coherent states and the fundamental inability to establish a phase reference without the secret—a physical limitation rather than a computational assumption.
- Chaos Encryption: Embeds data within a complex, noise-like analog waveform; requires synchronization mechanisms; often uses dual channels; security based on computational hardness of dynamics reconstruction.
- QEPS: Denies signal recovery by cryptographically controlling phase synchronization; operates over a single channel; requires no additional synchronization; security based on physical impossibility of phase reference establishment without the secret key.
1.6. Scope and Contribution of This Review
2. Theoretical Foundations: Coherent States and Phase-Space Dynamics
2.1. Coherent States: Bridging Classical and Quantum Optics
- Minimum Uncertainty: Coherent states saturate the Heisenberg uncertainty principle with equal uncertainties in the two field quadratures ( in appropriate units). This makes them the closest quantum mechanical analogue to a stable classical electromagnetic wave.
- Poissonian Photon Statistics: The photon number distribution is Poissonian, , with mean photon number . This matches the statistical behavior of an ideal laser operating well above threshold and underpins the signal-to-noise characteristics in coherent optical systems.
- Overcompleteness: Coherent states form an overcomplete basis, satisfying the resolution of identity . This property allows any optical quantum state to be expressed as a superposition of coherent states, providing a powerful representation for calculations.
-
Displacement Property and its Simplification: The action of a displacement operator is given by . This reveals two distinct effects: a translation in phase space from to , and an overall global phase factor. Since global phases are unobservable in physical measurements, the core action can be captured by a reduced displacement operator defined by its action:This simplified operator retains the additive property and, critically, commutes: . As established in QEPS-d [16], this commutativity is a key enabler for practical implementation, allowing encryption and decryption sequences to be applied without concern for operator ordering, thus facilitating direct realization with standard in-phase/quadrature (IQ) modulators.
2.2. Phase-Space Formalism: Visualizing Quantum Encryption
2.3. Key Operator Transformations in Phase Space
2.3.1. Phase Operators: Phase-Space Rotations
2.3.2. Displacement Operators: Phase-Space Translations
2.3.3. Dynamic Displacement Operators: Combined Transformations
2.3.4. Non-Commutativity: The Quantum Mechanical Heart of Security
3. The QEPS Framework: Principles and Mechanisms
3.1. Core Encryption Protocol Architecture
- QEPS-p (Phase-based): Uses only phase shift operators, rotating constellation points around the origin:where is derived from the secret key.
- QEPS-d (Displacement-based): Uses only displacement operators, shifting the entire constellation in phase space:where is derived from the secret key.
- QEPS-dd (Dual Displacement Operator): Combines both operators in sequence:where both and are derived from the secret key. The dynamic nature arises because the combined transformation creates an effective displacement that depends on , making the encryption state-dependent and enhancing security.
3.2. Channel Normalization via Digital Signal Processing
- Source data undergoes QAM Mapping to generate complex symbols , which correspond mathematically to coherent states .
- The Encryption Operator (specific to the QEPS variant) applies the encryption. For QEPS-d: ; for QEPS-p: ; for QEPS-dd: .
- The encrypted complex waveform then enters the standard Transmitter DSP routine: pilot symbols are inserted for synchronization, the signal is up-sampled, pulse-shaped, re-sampled to the DAC rate, and finally undergoes clipping and quantization before optical modulation.
- Synchronization aligns the signal using inserted pilots.
- Matched filtering optimizes the signal-to-noise ratio.
- The Adaptive equalizer compensates for linear channel impairments (e.g., chromatic and polarization-mode dispersion).
- Down-sampling reduces the data to one sample per symbol.
- Carrier phase recovery corrects for laser phase noise and frequency offset.
- The Inverse Encryption Operator is applied using the shared key. This crucial decryption step restores the original constellation point .
- Finally, QAM de-mapping recovers the bit stream for BER calculation.
- Without the secret key, the Inverse Encryption Operator cannot be applied correctly. Any attempt at inversion (including skipping it entirely) leaves the signal in a scrambled state.
- When this scrambled signal reaches QAM de-mapping, it no longer corresponds to valid constellation points, preventing meaningful data recovery.
- The encryption’s effect is thus not to prevent initial DSP convergence, but to ensure that the signal presented to the decision circuitry remains indistinguishable from noise after all channel compensation has been applied.
- Even with brute-force key search, each trial would require complete QAM demapping and error evaluation, as the DSP chain up to carrier recovery may still execute on incorrectly decrypted signals without obvious failure cues.
3.3. Cipher Space and Key Space Characterization
3.4. Dynamical Evolution and Security Enhancement
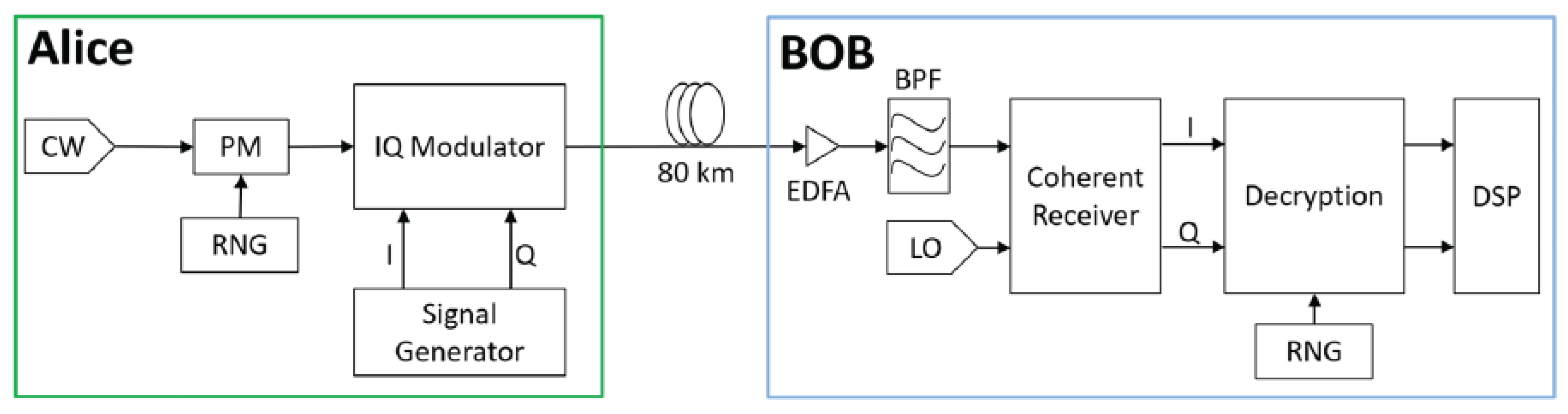
3.5. Practical Implementation and Experimental Validation
- Transmitter: Laser diode, IQ-MZM modulator driven by DACs, DSP for pulse shaping and pilot insertion, with QEPS encryption integrated into the modulation process.
- Receiver: Coherent detector with local oscillator, ADC, QEPS decryption module, followed by standard DSP for channel compensation.
4. Physical-Layer Security Principle: Phase Synchronization Barrier
4.1. The Phase Synchronization Imperative in Coherent Detection
- Active phase recovery (e.g., blind phase search, decision-directed phase-locked loops) estimates and compensates phase drift using known statistical or structural properties of the transmitted symbols.
- Passive phase mitigation (e.g., differential encoding, phase-diverse reception) reduces sensitivity to phase noise through signal design without explicit feedback.
4.2. The Phase Synchronization Barrier: Core Mechanism
4.3. Core Security Rationale: Basis Randomization and Restoration
- Scope: Operates at the physical waveform level rather than the digital bit level.
- Secret Nature: Utilizes a continuously evolving parameter stream rather than a fixed-length cryptographic key.
- Security Consequence: Creates physical undecodability rather than computational hardness.
4.4. Security Evolution Across QEPS Variants
4.4.1. QEPS-p: Phase-Only Encryption
4.4.2. QEPS-d: Displacement-Based Encryption
4.4.3. QEPS-dd: Dynamic Displacement Operator Encryption
4.5. Contrast with Classical Digital Encryption
4.6. The Nature of Secrecy and Attack Considerations
4.7. Assessment of Security Analysis in QEPS Literature
4.8. Summary: The Phase Synchronization Barrier in Perspective
- Physical rather than computational: Security stems from signal properties, not mathematical hardness.
- Operationally validated: Eavesdroppers’ BER approaches 50% in experimental demonstrations.
- Compatible with existing infrastructure: Implemented using standard coherent transceivers and DSP.
- Inherently quantum-resistant: Immune to attacks from both classical and quantum computers, as it does not rely on computational assumptions vulnerable to quantum algorithms.
5. Experimental Review
5.1. QPKE: Quantum Public Key Encryption via Round-Trip Architecture
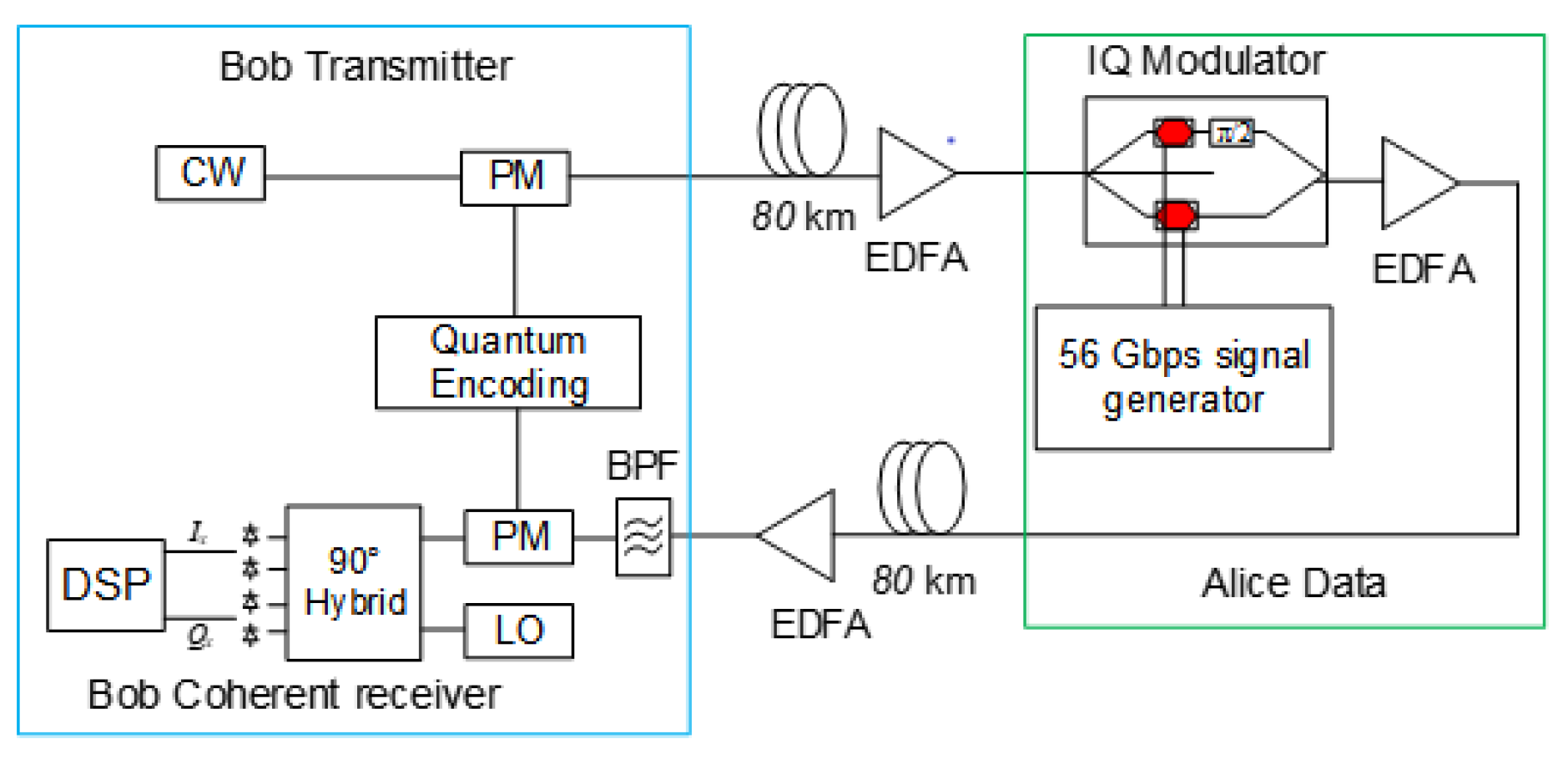
- Bob (initiator) generates a random phase sequence using a Quantum Permutation Pad (QPP) and applies it to a continuous-wave (CW) laser via a phase modulator (PM), creating an encrypted "envelope" signal.
- This phase-randomized carrier is transmitted to Alice over an 80 km standard single-mode fiber link with Erbium-Doped Fiber Amplifier (EDFA) compensation.
- Alice receives the scrambled carrier and modulates her secret data (at 56 Gbps) onto it using an IQ modulator, effectively "hiding" her information within Bob’s phase randomization without learning or storing the phase sequence.
- The doubly-modulated signal returns to Bob over another 80 km link. Bob possesses the original phase sequence and applies the inverse phase transformation via synchronized QPP before coherent detection using a 90° hybrid and local oscillator, followed by digital signal processing (DSP).
5.2. QEPS-p: Experimental Demonstration of Phase Mask Encryption
5.3. QEPS-d: Experimental Validation Using Displacement Operator Encryption
5.4. Summary of Experimental Performance and Achievements
- All QEPS variants successfully enforce a phase synchronization barrier at the physical layer, causing unauthorized receivers to experience a bit error rate (BER) near the theoretical maximum of 50%, equivalent to random guessing.
- Authorized receivers with the correct secret (or, in the case of QPKE, with the ability to apply the inverse transformation) achieve BER performance comparable to unencrypted coherent links, typically below the forward error correction (FEC) threshold ( for hard-decision FEC).
- The implementations support high-speed transmission (up to 200 Gb/s in experiments) over standard single-mode fiber spans of 80 km, confirming compatibility with existing optical infrastructure.
- Security does not depend on computational complexity but on the physical-layer denial of a stable phase reference, making it inherently resistant to advances in computing power, including quantum computing.
- The framework is versatile, supporting multiple cryptographic models: from public-key emulation (QPKE) that requires no pre-shared secret, to symmetric encryption (QEPS-p, QEPS-d) with enhanced randomness through displacement operators.
6. Conclusions
Acknowledgments
References
- Shor, P.W. Algorithms for quantum computation: discrete logarithms and factoring. Proceedings 35th Annual Symposium on Foundations of Computer Science; 1994; pp. 124–134. [Google Scholar]
- Bernstein, D.J. Introduction to post-quantum cryptography. Post-quantum cryptography 2009, 1–14. [Google Scholar]
- Deng, F.G.; Long, G.L. Secure direct communication with a quantum one-time pad. Phys. Rev. A 2004, 69, 052319. [Google Scholar] [CrossRef]
- Long, G.l.; Deng, F.g.; Wang, C.; Li, X.h.; Wen, K.; Wang, W.y. Quantum secure direct communication and deterministic secure quantum communication. Frontiers of Physics in China 2007, 2, 251–272. [Google Scholar] [CrossRef]
- Wang, C.; Deng, F.G.; Li, Y.S.; Liu, X.S.; Long, G.L. Quantum secure direct communication with high-dimension quantum superdense coding. Phys. Rev. A 2005, 71, 044305. [Google Scholar] [CrossRef]
- Sheng, Y.B.; Zhou, L.; Long, G.L. One-step quantum secure direct communication. Science Bulletin 2022, 67, 367–374. [Google Scholar] [CrossRef]
- Zhou, Z.; Sheng, Y.; Niu, P.; Yin, L.; Long, G.; Hanzo, L. Measurement-device-independent quantum secure direct communication. Science China Physics, Mechanics, and Astronomy 2020, arXiv:quant63, 230362. [Google Scholar] [CrossRef]
- Pan, D.; Liu, Y.C.; Niu, P.; Zhang, H.; Zhang, F.; Wang, M.; Song, X.T.; Chen, X.; Zheng, C.; Long, G.L. Simultaneous transmission of information and key exchange using the same photonic quantum states. Science Advances 2025, 11, eadt4627. [Google Scholar] [CrossRef]
- Glauber, R.J. Coherent and incoherent states of the radiation field. Physical Review 1963, 131, 2766–2788. [Google Scholar] [CrossRef]
- Kuang, R.; Bettenburg, N. Quantum Public Key Distribution using Randomized Glauber States. In Proceedings of the 2020 IEEE International Conference on Quantum Computing and Engineering (QCE), 2020; pp. 191–196. [Google Scholar] [CrossRef]
- Chan, A.; Khalil, M.; Shahriar, K.A.; Chen, L.R.; Plant, D.V.; Kuang, R. Security Analysis of a Next Generation TF-QKD for Secure Public Key Distribution with Coherent Detection over Classical Optical Fiber Networks. In Proceedings of the 2021 7th International Conference on Computer and Communications (ICCC), 2021; pp. 416–420. [Google Scholar] [CrossRef]
- Khalil, M.; Chan, A.; Shahriar, K.A.; Chen, L.R.; Plant, D.V.; Kuang, R. Security Performance of Public Key Distribution in Coherent Optical Communications Links. In Proceedings of the 2021 3rd International Conference on Computer Communication and the Internet (ICCCI), 2021; pp. 123–129. [Google Scholar] [CrossRef]
- Chan, A.; Khalil, M.; Shahriar, K.A.; Plant, D.V.; Chen, L.R.; Kuang, R. Encryption in Phase Space for Classical Coherent Optical Communications. Scientific Reports 2023, 13, 12965. [Google Scholar] [CrossRef]
- Shahriar, K.A.; Khalil, M.; Chan, A.; Chen, L.R.; Kuang, R.; Plant, D.V. Physical-Layer Secure Optical Communication Based on Randomized Phase Space in Pseudo-3-Party Infrastructure. In Proceedings of the Conference on Lasers and Electro-Optics, 2022; Optica Publishing Group; p. SF4L.3. [Google Scholar] [CrossRef]
- Shahriar, K.A.; Khalil, M.; Chan, A.; Chen, L.R.; Kuang, R.; Plant, D.V. Security Performance of Physical-Layer Encryption Based on Randomized Phase Space in Optical Fiber Communication. In Proceedings of the 2022 IEEE Photonics Conference (IPC), 2022; pp. 1–2. [Google Scholar] [CrossRef]
- Kuang, R.; Chan, A. Quantum encryption in phase space with displacement operators. EPJ Quantum Technology 2023, 10, 26. [Google Scholar] [CrossRef]
- Kuang, R. Quantum Encryption in Phase Space Uing Displacement Operator for QPSK Data Modulation. In Proceedings of the Proceedings of the 2023 8th International Conference on Systems, Control and Communications, New York, NY, USA, 2024; ICSCC ’23, pp. 35–40. [Google Scholar] [CrossRef]
- Khalil, M.; Chan, A.; Chen, L.R.; Plant, D.V.; Kuang, R. Quantum-Inspired Encryption Using Displacement Operators in Coherent Optical Communications. In Proceedings of the Advanced Photonics Congress 2024, 2024; Optica Publishing Group; p. SpW2H.6. [Google Scholar] [CrossRef]
- Zhang, C.; Kuang, R.; Wen, K.; et al. Toward Practical Quantum Encryption in Phase Space: Simulated QPSK and 16-QAM with Dynamic Displacement Operators. Research Square;Preprint 2025, 1. [Google Scholar] [CrossRef]
- Kuang, R. Quantum encryption in phase space with dynamic displacement operators and quantum permutation pad. Academia Quantum 2025, 2. [Google Scholar] [CrossRef]
- Wu, B.; Zhang, W.; Zhou, H.; Dong, J.; Wang, Y.; Zhang, X. Partially coherent optical chip enables physical-layer public-key encryption. Opto-Electron Adv 2025, 8, 250098. [Google Scholar] [CrossRef]
- Wu, Y.; Zhang, Z.; Luo, H.; Deng, L.; Yang, Q.; Dai, X.; Liu, D.; Gao, X.; Yu, Y.; Cheng, M. 100Gb/s coherent optical secure communication over 1000 km based on analog-digital hybrid chaos. Opt. Express 2023, 31, 33200–33211. [Google Scholar] [CrossRef]
- Tang, X.; Xu, Z.; Gao, C.; Xiao, Y.; Liu, L.; Zhang, X.; Xi, L.; Xu, H.; Bai, C. Physical layer encryption for coherent PDM system based on polarization perturbations using a digital optical polarization scrambler. Opt. Express 2023, 31, 26791–26806. [Google Scholar] [CrossRef]
- Li, R.; Gong, X.; Zhang, Q.; Qin, W.; Hou, W.; Guo, L. High-speed coherent optical encryption/decryption system based on cross-phase encoding. Opt. Express 2025, 33, 33021–33032. [Google Scholar] [CrossRef]
- Gao, X.; Gu, W.; Deng, Z.; Li, X.; Ye, J.; An, Y.; Bi, S.; Wang, A.; Wang, Y.; Qin, Y.; et al. 40 Gb/s Secure Coherent Optical Communication Based on Electro-Optic Phase Feedback Encryption. IEEE Photonics Technology Letters 2024, 36, 481–484. [Google Scholar] [CrossRef]
- Tan, S.H.; Ouyang, Y.; Rohde, P.P. Practical somewhat-secure quantum somewhat-homomorphic encryption with coherent states. Physical Review A 2018, 97. [Google Scholar] [CrossRef]
- Liu, Y.L.; Dong, Z.; Zhu, Y.M.; Peng, D.M.; Wang, Y.K.; Zhang, Y.; Wang, F.; Zhu, W.Q.; Li, D.Z.; Liu, X.L. Three-channel robust optical encryption via engineering coherence Stokes vector of partially coherent light. PhotoniX 2024, 5, 8. [Google Scholar] [CrossRef]
- Larger, L.; Goedgebuer, J.P. Encryption using chaotic dynamics for optical telecommunications. Comptes Rendus Physique 2004, 5, 609–611. [Google Scholar] [CrossRef]
- Chen, W.; Mao, X.; Wang, J.; Zhang, R.; Wang, L.; Jia, Z.; Li, P.; Wang, A.; Wang, Y. Optical Chaos Generation and Applications. Advanced Photonics Research 2025, 6, 2500055. [Google Scholar] [CrossRef]
- Yu, M.; Wang, H.; Ji, Y.; Zhang, Y. Ultra-wideband chaotic optical communication based on electro-optic differential feedback loop. Optics Communications 2023, 545, 129729. [Google Scholar] [CrossRef]
- Xie, Y.; Yang, Z.; Shi, M.; Zhuge, Q.; Hu, W.; Yi, L. 100 Gb/s coherent chaotic optical communication over 800 km fiber transmission via advanced digital signal processing. Advanced Photonics Nexus 2024, 3, 016003. [Google Scholar] [CrossRef]
- Jacobo, A.; Soriano, M.C.; Mirasso, C.R.; Colet, P. Chaos-Based Optical Communications: Encryption Versus Nonlinear Filtering. IEEE Journal of Quantum Electronics 2010, 46, 499–505. [Google Scholar] [CrossRef]
- Kanakidis, D.; Argyris, A.; Bogris, A.; Syvridis, D. Influence of the decoding process on the performance of chaos encrypted optical communication systems. Journal of Lightwave Technology 2006, 24, 335–341. [Google Scholar] [CrossRef]
- Ye, J.; Gao, X.; Li, X.; Yang, H.; An, Y.; Xu, P.; Wang, A.; Dong, X.; Wang, Y.; Qin, Y.; et al. Physical layer security–enhanced optical communication based on chaos masking and chaotic hardware encryption. Optics Express 2024, 32, 27734–27747. [Google Scholar] [CrossRef]
- Zhang, C.; Wang, H.; Yang, H.; Ji, Y. Chaotic optical communication decryption framework based on the conv-transformer model. Opt. Express 2025, 33, 44071–44086. [Google Scholar] [CrossRef]
- Fan, X.; Mao, X.; Wang, L.; Fu, S.; Wang, A.; Wang, Y. Improving decryption quality of optical chaos communication using neural networks. Opt. Lett. 2024, 49, 4445–4448. [Google Scholar] [CrossRef]
- Zaminga, S.; Martinez, A.; Huang, H.; Rontani, D.; Morichetti, F.; Melloni, A.; Grillot, F. Optical chaotic signal recovery in turbulent environments using a programmable optical processor. Light: Science & Applications 2025, 14, 131. [Google Scholar] [CrossRef]
- Zhang, Y.; Xu, M.; Pu, M.; Chen, Q.; Zhou, M.; Chen, S.; Qiu, K.; Jiang, N.; Luo, X. Experimental demonstration of an 8-Gbit/s free-space secure optical communication link using all-optical chaos modulation. Optics Letters 2023, 48, 1470–1473. [Google Scholar] [CrossRef]
- Liu, J.Y.; Zhou, X.F.; Li, Q.L.; Hu, M.; Li, H.Z. Secondary-encryption optical chaotic communication system based on one driving laser and two responding lasers. Chaos, Solitons & Fractals 2022, 163, 112554. [Google Scholar] [CrossRef]
- Xue, C.; Xia, Y.; Chen, W.; Gu, P.; Zhang, Z. Physical-layer security of optical communication based on chaotic optical encryption without an additional driving signal. Optics Letters 2023, 48, 2611. [Google Scholar] [CrossRef]
- Ashraf, M.W.A.; Singh, A.R.; Pandian, A.; Bajaj, M.; Zaitsev, I.; Rathore, R.S. Enhancing network security with hybrid feedback systems in chaotic optical communication. Scientific Reports 2024, 14, 24958. [Google Scholar] [CrossRef]
- Guo, R.; Song, L. Optical chaotic secure algorithm based on space laser communication. Discrete and Continuous Dynamical Systems - S 2019, 12, 1355–1369. [Google Scholar] [CrossRef]
- Kuang, R. Quantum Permutation Pad for Quantum Secure Symmetric and Asymmetric Cryptography. Academia Quantum 2025, 2. [Google Scholar] [CrossRef]
- Taylor, M.G. Coherent Detection for Fiber Optic Communications Using Digital Signal Processing. In Proceedings of the Optical Amplifiers and Their Applications/Coherent Optical Technologies and Applications; Optica Publishing Group, 2006; p. CThB1. [Google Scholar] [CrossRef]
- Zhou, X.; Yu, J. Digital signal processing for coherent optical communication. In Proceedings of the 2009 18th Annual Wireless and Optical Communications Conference, 2009; pp. 1–5. [Google Scholar] [CrossRef]
- Zhao, J.; Liu, Y.; Xu, T. Advanced DSP for Coherent Optical Fiber Communication. Applied Sciences 2019, 9. [Google Scholar] [CrossRef]
- Khalil, M.; Plant, D.V.; Chan, A.; Chen, L.R.; Kuang, R. Experimental demonstration of quantum encryption in phase space with displacement operator in coherent optical communications. EPJ Quantum Technology 2024, 11, 49. [Google Scholar] [CrossRef]
- Kuang, R.; Barbeau, M. Quantum Permutation Pad for Universal Quantum-Safe Cryptography. Quantum Information Processing 2022, 21, 211. [Google Scholar] [CrossRef]
| Variant | Architecture | Auth. BER | Unauth. BER |
|---|---|---|---|
| QPKE | Round-trip, PK-like | ||
| QEPS-p | Symmetric phase key | ||
| QEPS-d | Symmetric displacement key | 48–49% |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.




