Submitted:
01 January 2026
Posted:
02 January 2026
You are already at the latest version
Abstract
Keywords:
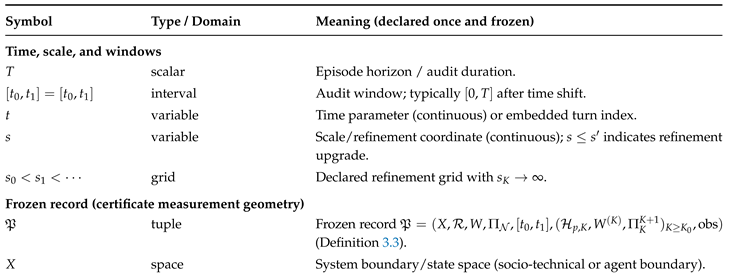
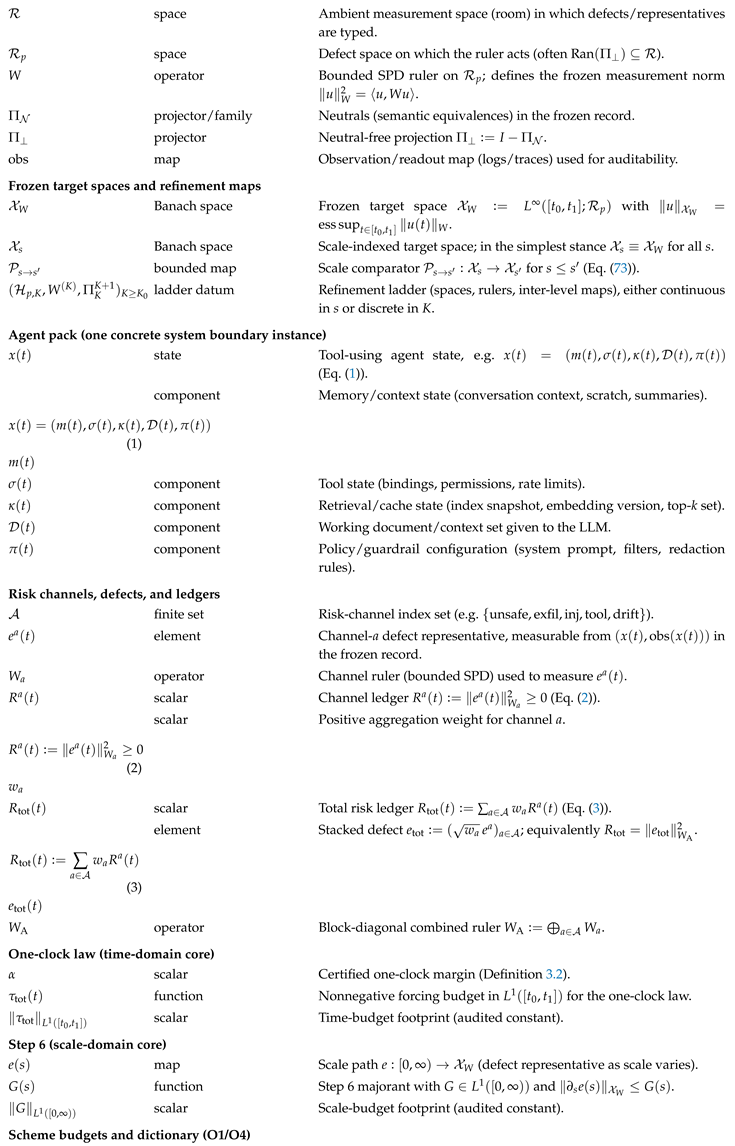
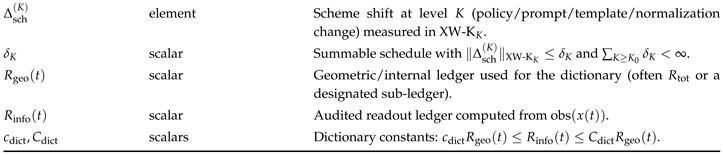
Notation
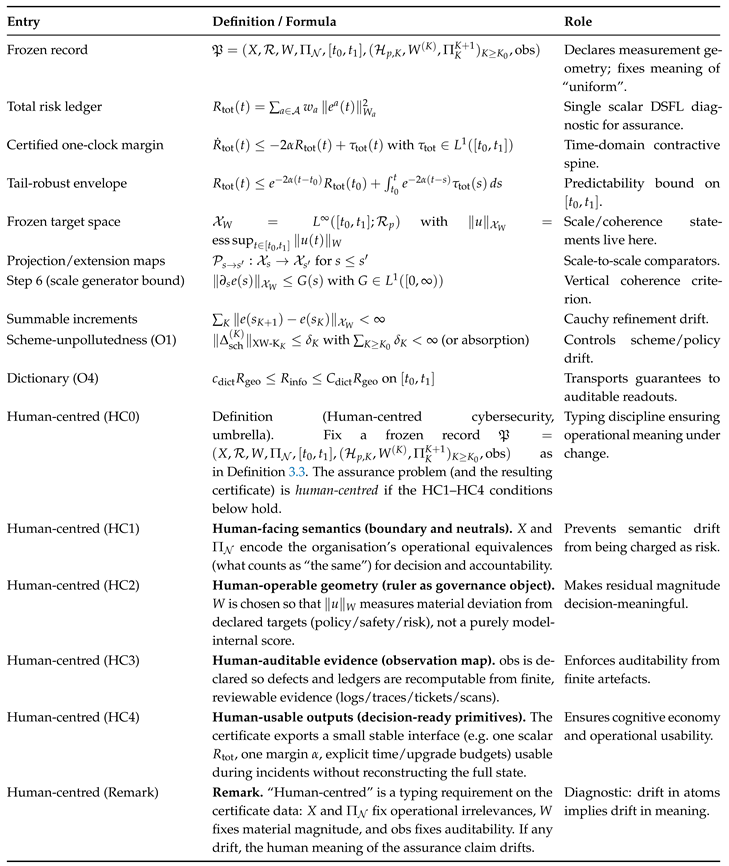
Master Definitions (Used Throughout)
1. Introduction
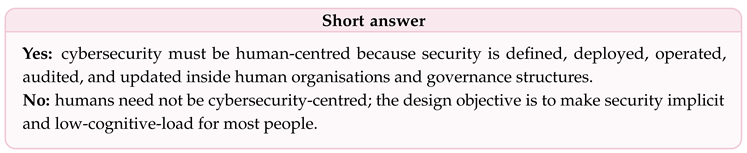
1.1. Why Cybersecurity Is Human-Centred by Construction
1.2. Problem Statement
Given a deployed system that evolves in time and across refinement scales (tool versions, policy revisions, monitoring pipelines, model and retrieval updates), can we produce a proof-carrying, refinement-invariant safety envelope that is (i) meaningful under upgrades, (ii) compositional across coupled risk channels, and (iii) auditable from a finite bundle?
1.3. Scope and Non-Claims
Scope
Non-Claims
1.4. Approach: Frozen Records, One-Clock Reduction, and Vertical Coherence
Time Axis (One-Clock Safety Envelope)
Scale Axis (Refinement Ladders and Step 6)
Proof-Carrying Posture (Bundle-and-Checker Semantics)
1.5. Two-Domain Positioning and Avatar-Chain Method
1.6. Main Contributions
- C1
- Frozen-record semantics for assurance under change. We formalise the typing data required to make cross-version claims invariant: a frozen defect room, a frozen SPD ruler, a neutral convention, an audit window, a refinement ladder, and an observation map. This prevents metric drift from being mistaken for safety improvement [3,4].
- C2
- A one-clock certificate for coupled risk channels. Under cooperative coupling and a Hurwitz margin condition, we prove a positive weighting reduces multiple ledgers to a single scalar residual obeying (4) with explicit budgets. The resulting envelope is tail-robust and mechanically checkable [16,17,18,19].
- C3
- A refinement-ladder coherence theorem (Step 6). We show that a summable refinement drift condition (or an scale-generator bound) implies vertical coherence in the frozen target norm: upgrade effects have finite total footprint, yielding a well-defined limiting representative and an honest meaning for “uniform across upgrades” [20].
- C4
- A Master Certificate with auditable obligations. We package the requirements as auditable obligations (scheme/dictionary control, uniform one-clock margin, vertical coherence, and dictionary transport). Passing these checks implies a refinement-invariant safety envelope on the declared audit window [1,2].
1.7. What This Paper Does Not Claim
1.8. Roadmap
2. Positioning and State of the Art
2.1. The Position: Cybersecurity Is Human-Centered, but Guarantees Must Be Typed
- design (interfaces, defaults, and affordances that shape operator and user behaviour),
- workflow integration (how precautions compete with productivity and latency constraints),
- governance (policy revision, compliance instruments, accountability, and audit evidence),
- adversarial and geopolitical context (crime, conflict, regulation, and standards).
2.2. State of the Art: Four Literatures That Do not yet Yield One upgrade-Stable Assurance Object
(i) Stability and Semigroups in Fixed norms (Typed Meaning)
(ii) Positive Systems, Small-Gain, and Compositional Closure (Coupled Channels)
(iii) Proof-Carrying and Runtime-Verifiable Assurance (Ship Evidence, Verify Cheaply)
(iv) Human-Centred Cybersecurity and Usable Security (Why Drift and Overload Are First-Order)
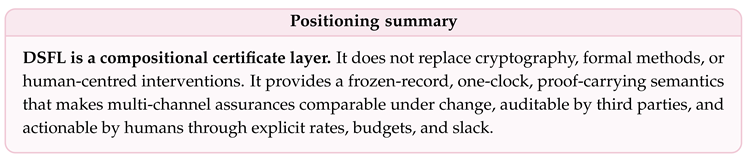
2.3. Why a Compositional Certificate Is Still Missing
- (i)
- (ii)
- (iii)
- separates global security state from what bounded observers can actually audit via an explicit observation map [1];
- (iv)
2.4. Implications: Three Interfaces That Make Guarantees Operational
2.4.1. Decision Interface: Cognitive Economy Under Metric Drift
Problem
DSFL Response
2.4.2. Governance Interface: Continuous Assurance as a Contract
Problem
DSFL Response
2.4.3. Engineering Interface: Non-Regression for Adaptive AI and Evolving Systems
Problem
DSFL Response
3. Problem Setting and Design Principles
3.1. Human-Centred Cybersecurity as a Dynamical System
3.1.1. System Boundary and State
- (i)
- interventions (training, patching, policy changes, access reviews, monitoring changes);
- (ii)
- disturbances (attacks, outages, user error, vendor changes, workload spikes);
- (iii)
- observations produced by an observation map (logs, telemetry, tickets, scans), declared precisely in subsec:frozen-geometry.
Why this Abstraction Is Necessary
3.1.2. Equilibria as Constraints and Residuals as Distances
Human-Centred Reading
3.1.3. Lyapunov Claims as Certificate Interfaces
Human-Centred Meaning
3.2. Frozen Measurement Geometry (“No Moving Goalposts”)
3.2.1. Definition of a Frozen Record
- (i)
- X is the system state space (human-centered boundary);
- (ii)
- is an ambient measurement space in which defect representatives are typed;
- (iii)
- is a bounded SPD ruler on a defect space , defining ;
- (iv)
- is theneutral convention(semantic equivalences), and is the neutral-free projection;
- (v)
- is the audit window;
- (vi)
- is a declared refinement ladder (tool versions, policy versions, monitoring pipelines);
- (vii)
- is an observation map that produces auditable readouts (logs/telemetry) from trajectories.
Why Each Component Is Necessary
3.2.2. A Formal “No Moving Goalposts” Impossibility Statement
Interpretation
3.2.3. Neutrals as Semantic Equivalence Classes
Design Principle
3.3. Residuals Versus Metrics
3.3.1. Residuals as Distances to Constraints
Why this Matters
3.3.2. Metrics as Scores and the Danger of Non-Transportability
3.3.3. Admissible Updates: Why Residuals Support Compositional Reasoning
Human-Centred Meaning
3.3.4. From Residuals to a Decision-Ready Scalar Ledger
4. Mathematical Framework
4.1. Residual Spaces and Rulers
4.1.1. Hilbert Defect Room and the Frozen Ruler
4.1.2. Neutral Directions and Semantic Equivalence
4.1.3. Norm Transfer and “No Moving Goalposts”
4.2. Multi-Ledger Systems
4.2.1. Ledger Vector and Nonnegativity
4.2.2. Couplings and Forcing Budgets
- (ii)
- is measurable andMetzlerfor a.e. t (off-diagonal entries );
- (ii)
- is a nonnegative forcing vector with .
4.3. One-Clock Reduction (Metzler Closure)
4.3.1. Metzler Matrices and the Hurwitz Margin
4.3.2. One-Clock Theorem
4.3.3. Certificate-Friendly Feasibility Condition
4.3.4. Two-Channel Closed Form (for Intuition)
5. The One-Residual, One-Clock Theorem
5.1. Assumptions (Certificate Layer)
5.1.1. Ledgers, Regularity, and Forcing Budgets
5.1.2. Metzler Comparison Inequality and Stability Margin
Interpretation of M
Why constant M Is Acceptable at the Certificate Layer
5.2. Main Theorem
5.2.1. Positivity and the Forced Comparison Formula
5.2.2. One-Clock Reduction
Security assurance interpretation
LP-checkable certificate interface
5.3. Tail-Robust Envelopes
5.3.1. Interpretation: Incidents as Budgets, Recovery as Rate
Transient Spikes
Recovery
Human-Facing Assurance
6. Compliance and Assurance as Imbalance
6.1. Policy–Practice Imbalance Operators
6.1.1. Typing: Blueprint Space, Practice Space, and Observation Map
6.1.2. Concrete Imbalance Operators by Channel
Identity and Access Management (IAM)
Configuration State (Hardening Posture)
Data Handling and Governance
Agent Tool Use and AI Governance
6.2. Compliance Residuals
6.2.1. Frozen Ruler and the Compliance Residual
6.2.2. Comparability Under Tool Changes
6.2.3. Multi-Channel Compliance as a Ledger Vector
6.3. Assurance as a Gap, not a Checklist
6.3.1. Assurance Means a Contraction Margin in the Frozen Ruler
6.3.2. Metzler Closure Yields Assurance from Coupled Channels
6.3.3. Slack Is the Audit Object
7. Empirical Coupling Budgets
7.1. Why Coupling Matters in Security
7.1.1. Coupling Is the Difference Between Local and Global Guarantees
7.1.2. Operational Meaning of Couplings
- Workload → misconfiguration: high alert load increases the probability of rushed changes and policy exceptions, inflating configuration residuals.
- Misconfiguration → workload: drifting configurations create more alerts and incidents, inflating workload.
- Identity sprawl ↔ policy violations: expanding entitlements increases both violation frequency and response overhead.
7.2. Model-Free Empirical Coupling Estimate
7.2.1. From Coupled Inequalities to an Observable Injection Trace
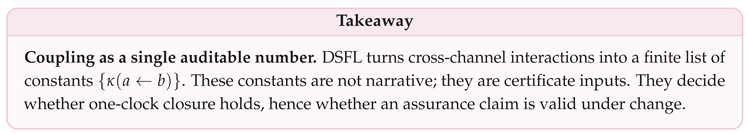
7.2.2. Definition of the Empirical Coupling Constant
7.2.3. Immediate Inequality (the Certificate-Ready Bound)
7.2.4. From to a Metzler Comparison Form
7.3. Interpretation as a Certificate Constant
7.3.1. Certificate Semantics: What Means
The worst-case observed rate (in the declared frozen record) at which channel b can inject mismatch into channel a, normalised by the geometric mean of the two residuals.
7.3.2. Robustness Under Protocol Variation and Resampling
7.3.3. How Appears in an Assurance Report
- each off-diagonal coupling is instantiated by a conservative bound such as ;
- diagonal terms include the certified gaps minus any diagonal penalties induced by coupling bounds;
- the report records the slack in the Hurwitz margin condition (LP-feasible and witness ), not just the raw couplings.
8. Floors and Feasibility Under Human Constraints
8.1. Why Security Improvement Has Floors
8.1.1. Human and Organisational Mechanisms That Generate Floors
(i) Attention and Throughput Bounds
(ii) Workflow Latency and Batching
(iii) Fatigue and Diminishing Returns
8.1.2. Formal Encoding at the Certificate Layer
- (i)
- is the effective improvement margin (how much dissipation we can sustain);
- (ii)
- is the disturbance/arrival footprint (how much risk is injected or how much work arrives).
8.2. Asymptotic Improvement Floors
8.2.1. Effective Rate and Average Exponent
Interpretation
8.2.2. Feasible Floors
8.2.3. A Capacity Model for Forcing
Interpretation
8.2.4. A Persistent Dissipation Hypothesis
8.2.5. The Floor Theorem and Its Consequences
- (i)
-
Uniform ultimate bound.For all ,In particular,
- (ii)
-
Floor interpretation.If (no sustained forcing), then decays exponentially with rate andIf , then the best possible long-run outcome is a neighbourhood of size , and the meaningful “floor” becomes afloor on the transient recovery rateback to this neighbourhood after spikes.
8.2.6. Governance Interpretation: Feasibility Tests and Planning
Feasibility test
How to improve the floor
- (i)
- increase sustainable dissipation (process improvement, automation, staffing, reduced latency);
- (ii)
- reduce disturbance density B (attack surface reduction, fewer incidents, better upstream quality control).
Connection to ISS thinking
9. Certificates Under Change
9.1. Refinement Ladders and Upgrades
9.1.1. What Counts as “Refinement” in Human-Centered Security
- a scanner upgrade that changes vulnerability definitions or severity scoring,
- a policy revision that changes what is counted as compliant,
- a new telemetry pipeline or log schema (instrumentation change),
- a model update in an AI-enabled system (weights, prompt templates, guardrails),
- a retrieval/index update in RAG systems (corpus snapshot changes).
9.1.2. Scale Comparators: Cocycle and Nonexpansivity
Interpretation
Concrete Realisation on a Discrete Ladder
Role in the Certificate Architecture
9.1.3. Frozen Target Space and Comparators
Why Is the Correct Choice
Interpretation
9.2. Summable Refinement Drift (Step–6)
9.2.1. Step–6 as an Scale-Generator Bound
Why Bochner Absolute Continuity
9.2.2. Step–6 Implies Summable Increments
Security Meaning
9.2.3. Projective-Limit Semantics Under Contractive Comparators
Operational Reading
9.3. Failure Modes When Step–6 Fails
9.3.1. Failure Mode 1: Metric Drift by Instrumentation
9.3.2. Failure Mode 2: Scheme Freedom not Controlled (Policy Semantics Drift)
9.3.3. Failure Mode 3: Noncontractive Comparators (Moving Goalposts)
9.3.4. Failure Mode 4: Non-Normal Transients Misdiagnosed as Regression
- (i)
- if is large or diverging, the upgrade path is not coherent in the frozen record;
- (ii)
- the tail bound (82) quantifies how far the current version may be from a stable limiting claim;
- (iii)
- the remedy is explicit: either refine comparators, freeze the observation map, or treat policy changes as scheme budgets.
10. Numerical Audit Architecture
10.1. Certificate Bundle Contents
10.1.1. Bundle as a Proof-Carrying Artifact
- (i)
- Metadata .Version identifiers for tools/policies/models, hashes of configuration files, and time-window descriptors.
- (ii)
- (iii)
- Ledger specification .Definitions of defect extractors, channel rulers, and aggregation weights producing .
- (iv)
- Constants and budgets .Numerical values for verified margins and budgets, e.g. α, , , .
- (v)
- Trace .Committed logs/telemetry sufficient to recompute audited ledgers; may include integrity commitments (hashes) if required.
- (vi)
- Witnesses .Auxiliary data that makes checking cheap: e.g. LP witnesses , gap fit summaries, block decomposition indices, and resampling robustness summaries.
Why this Is Minimal
10.1.2. Checker Interface and PASS/FAIL Semantics
Human-Centred Meaning
10.2. Block-Structured Operator Avatars
10.2.1. Why Block Structure Is the Scalable Verification Primitive
10.2.2. Formal Block Decomposition and Audit Reduction
10.2.3. Audit Reduction: Blockwise Constants with Coupling Schedules
- (i)
- Diagonal blocks: compute blockwise gaps and coercivity constants;
- (ii)
- Off-diagonal blocks: compute norm bounds that become coupling coefficients in the Metzler closure;
- (iii)
- Ladder upgrades: compute blockwise increments that must be summable (Step–6).
10.3. Spectrum, Gap, and Non-Normality Audits
10.3.1. Two Spectral Regimes: Symmetric Versus Non-Normal
Symmetric/Symmetrizable Case
Non-Normal Case
10.3.2. Audit Targets: What Is Computed
(A) Norm Matching Constants
(B) Gap Estimate
(C) Coupling Budgets
10.3.3. Certificate-Style Interpretation (Human Meaning)
- a gap estimate is accepted only as a conservative bound (e.g. lower quantile across trials);
- non-normality is treated explicitly by reporting transient amplification indicators (e.g. peak-to-tail ratios) rather than hiding it inside averages, consistent with pseudospectral warnings about eigenvalue-only diagnostics [26].
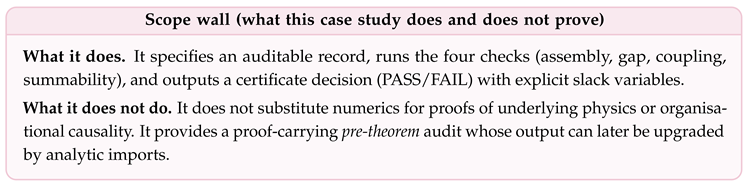
11. Case Study: Audit of a Large Block-Structured System
11.1. Assembly Audit
11.1.1. Frozen Record for the Avatar
11.1.2. Dimension Check (Block Accounting)
11.1.3. Sparsity Audit (Structural Sanity)
11.2. Gap Estimation
11.2.1. What a “Gap” Means in a Frozen Ruler
11.2.2. Time-Domain Ringdown Fit
11.2.3. A Conservative Matrix-Only Proxy (Symmetric-Part Bound)
11.3. Coupling and Summability
11.3.1. Coupling Audit: Empirical Constants
11.3.2. Summability Audit: Ladder Increments
11.4. Certificate Decision
11.4.1. Formal PASS/FAIL Rule
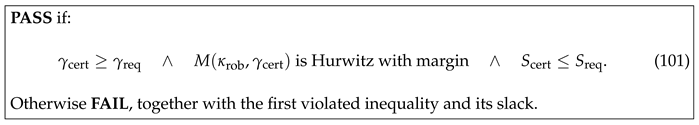
11.4.2. Slack Variables (What the Audit Reports)
12. Implications for Human-Centred Cybersecurity
12.1. Decision Support
12.1.1. Cognitive Load as a Formal Failure Mode
12.1.2. From Multi-Ledger Telemetry to One Decision-Ready Scalar
Human-Centred Interpretation
- a certified improvement margin (“how fast we recover when not being hit”),
- a disturbance footprint (“how hard we were hit on this window”),
- a starting residual (“how far we were from target at window start”).
12.1.3. Actionability: What Interventions Can Change
12.2. Governance and Compliance
12.2.1. From Snapshot Audits to Continuous Assurance
12.2.2. Compliance as a Residual and Remediation as a Margin
Governance Interpretation
12.2.3. Non-Regression Under Change as a Governance Requirement
12.3. AI Agents and Adaptive Systems
12.3.1. Why Tool-Using Agents Require Proof-Carrying Semantics
12.3.2. Agent Safety as a Ledger Vector
12.3.3. Proof-Carrying Guarantees Under Model and Tool Upgrades
Human-Centred Meaning
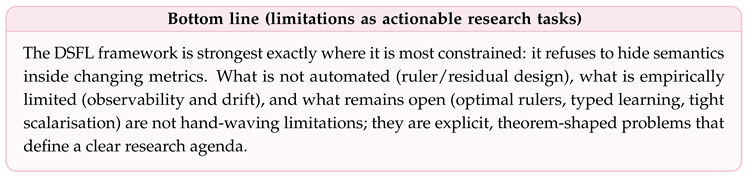
13. Limitations and Open Problems
13.1. What Is not Automated
13.1.1. Rulers Are Part of the Theorem Data
13.1.2. Residual Definitions Encode Semantics
13.2. Empirical Calibration Challenges
13.2.1. Observability Limits Are Structural, not Incidental
13.2.2. Calibration Drift and Dataset Shift
13.3. Open Theoretical Questions
13.3.1. Optimal Ruler Selection Under Composability Constraints
- (O1)
- Operationally meaningful: encodes the organisation’s notion of risk and neutrality;
- (O2)
- Stable under change: yields explicit norm-equivalence constants when tooling changes;
- (O3)
- Composable: admits tight coupling bounds and a large Hurwitz margin for the induced Metzler system.
13.3.2. Learning Residuals Without Losing Typing
- (i)
- the proposal is equivalent (with explicit constants) to the declared semantics in the frozen record, or else is declared as a new record;
- (ii)
- the induced coupling bounds remain Metzler-typed and preserve (or improve) the Hurwitz margin;
- (iii)
- the resulting certificate remains auditable by a third party.
13.3.3. Tightness of the Metzler Reduction
14. Conclusion
14.1. What Has Been Proved
14.1.1. One Residual and One Clock from Multi-Channel Ledgers
14.1.2. Tail-Robust Envelopes (Incident Spikes Become Budgets)
14.1.3. Non-Regression Under Upgrades via Summable Refinement Drift
14.2. What This Reframing Changes for Human-Centred Cybersecurity
Decision Support
Governance and Compliance
AI Agents and Adaptive Systems
14.3. Limits of the Present Work
14.4. A Research Agenda with Theorem-Shaped Milestones
- (i)
- Pack library (definitions). Publish a catalogue of frozen-record templates for common deployments (SOC pipeline, cloud posture management, tool-using agents), including standard neutral conventions and observation commitments.
- (ii)
- Coupling identification (empirical ). Develop robust, conservative estimation procedures for coupling coefficients (including resampling robustness and worst-case confidence bands) to populate certificate tables from operational data.
- (iii)
- Step–6 for real upgrades. Define refinement operators for tool and policy upgrades and prove (or conservatively bound) integrable scale-generator majorants , yielding summable drift and non-regression across versions.
- (iv)
- Non-normality-aware audits. Standardise audits that distinguish symmetric/selfadjoint from non-normal regimes and report transient growth indicators alongside decay/gap estimates [26].
- (v)
- Floor-aware governance. Operationalise feasibility floors by connecting resource constraints (staffing, latency, cadence) to certified dissipation margins and forcing densities, producing planning tools that detect infeasible improvement targets.
14.5. Final Positioning
Cybersecurity becomes auditable and comparable under change when it is expressed as a forced contraction inequality for a single residual in a frozen measurement geometry, with all unresolved effects routed into explicit budgets.
Funding
Data Availability Statement
Ethics Approval
Declaration of Generative AI and AI-Assisted Technologies in the Writing Process
Acknowledgments
Conflicts of Interest
References
- Bauer, A.; Leucker, M.; Schallhart, C. Runtime Verification for LTL and TLTL. ACM Transactions on Software Engineering and Methodology 2011, 20, 14:1–14:64. [Google Scholar] [CrossRef]
- Necula, G.C. Proof-Carrying Code. In Proceedings of the Proceedings of the 24th ACM SIGPLAN-SIGACT Symposium on Principles of Programming Languages (POPL ’97), New York, NY, USA, 1997; pp. 106–119. [Google Scholar] [CrossRef]
- Pazy, A. Semigroups of Linear Operators and Applications to Partial Differential Equations; Applied Mathematical Sciences; Springer: New York, 1983; Vol. 44. [Google Scholar] [CrossRef]
- Engel, K.J.; Nagel, R. One-Parameter Semigroups for Linear Evolution Equations; Graduate Texts in Mathematics; Springer: New York, 2000; Vol. 194. [Google Scholar]
- Anderson, R. Security Engineering: A Guide to Building Dependable Distributed Systems; John Wiley & Sons: New York, 2001. [Google Scholar]
- Sasse, M.A. “Technology Should Be Smarter Than This!”: A Vision for Overcoming the Great Authentication Fatigue, 2014. Position paper / invited talk manuscript (UCL Discovery).
- Adams, A.; Sasse, M.A. Users are not the enemy. In Proceedings of the Proceedings of the 1999 Workshop on New Security Paradigms (NSPW ’99), New York, NY, USA, 1999. [Google Scholar] [CrossRef]
- Beautement, A.; Sasse, M.A.; Wonham, M. The Compliance Budget: Managing Security Behaviour in Organisations. In Proceedings of the Proceedings of the 2008 Workshop on New Security Paradigms (NSPW ’08), New York, NY, USA, 2008; pp. 47–58. [Google Scholar] [CrossRef]
- Herley, C. More Is Not the Answer. IEEE Security & Privacy 2014, 12, 14–19. [Google Scholar]
- Nielsen, M.A.; Chuang, I.L. Quantum Computation and Quantum Information, 10th anniversary edition ed.; Cambridge University Press: Cambridge, 2010. [Google Scholar]
- Terhal, B.M. Quantum error correction for quantum memories. Reviews of Modern Physics 2015, 87, 307–346. [Google Scholar] [CrossRef]
- Preskill, J. Quantum Computing in the NISQ era and beyond. Quantum 2018, 2, 79. [Google Scholar] [CrossRef]
- Wald, R.M. General Relativity; The University of Chicago Press: Chicago, 1984. [Google Scholar]
- Wald, R.M. Quantum Field Theory in Curved Spacetime and Black Hole Thermodynamics; University of Chicago Press: Chicago, 1994. [Google Scholar]
- Fewster, C.J.; Verch, R. Algebraic Quantum Field Theory in Curved Spacetimes. In Advances in Algebraic Quantum Field Theory; Brunetti, R., Fredenhagen, K., Verch, R., Eds.; Springer: Cham, 2015; pp. 125–189. [Google Scholar] [CrossRef]
- Farina, L.; Rinaldi, S. Positive Linear Systems: Theory and Applications; John Wiley & Sons: New York, 2000. [Google Scholar]
- Briat, C. Linear Parameter-Varying and Time-Delay Systems: Analysis, Observation, Filtering & Control; Advances in Delays and Dynamics; Springer: Berlin, Heidelberg, 2015. [Google Scholar] [CrossRef]
- Khalil, H.K. Nonlinear Systems, 3 ed.; Prentice Hall: Upper Saddle River, NJ, 2002. [Google Scholar]
- Sontag, E.D. Input to State Stability: Basic Concepts and Results. In Nonlinear and Optimal Control Theory;Lecture Notes in Mathematics; Springer: Berlin, Heidelberg, 2008; Vol. 1932, pp. 163–220. [Google Scholar] [CrossRef]
- Diestel, J.; Uhl, J.J. Vector Measures; Mathematical Surveys; American Mathematical Society: Providence, RI, 1977; Vol. 15. [Google Scholar]
- Watrous, J. The Theory of Quantum Information; Cambridge University Press, 2018. [Google Scholar]
- Lyapunov, A.M. The General Problem of the Stability of Motion; Original work published in Russian; Taylor & Francis, 1992. [Google Scholar]
- Grönwall, T.H. Note on the Derivatives with Respect to a Parameter of the Solutions of a System of Differential Equations. Annals of Mathematics 1919, 20, 292–296. [Google Scholar] [CrossRef]
- Coddington, E.A.; Levinson, N. Theory of Ordinary Differential Equations; McGraw–Hill: New York, 1955. [Google Scholar]
- Berman, A.; Plemmons, R.J. Nonnegative Matrices in the Mathematical Sciences; Classics in Applied Mathematics; SIAM: Philadelphia, PA, 1994; Vol. 9. [Google Scholar]
- Trefethen, L.N.; Embree, M. Spectra and Pseudospectra: The Behavior of Nonnormal Matrices and Operators; Princeton University Press: Princeton, NJ, 2005. [Google Scholar]
- Farina, L.; Rinaldi, S. Positive Linear Systems: Theory and Applications; Pure and Applied Mathematics; Wiley–Interscience: New York, 2000; Vol. 255. [Google Scholar]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



