Submitted:
11 December 2025
Posted:
14 December 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background and Related Work
2.1. Post-Quantum Cryptography
2.2. Access Control in Cloud-Native Environments
2.3. Quantum-Resilient and Hybrid Security Approaches
3. System and Threat Model
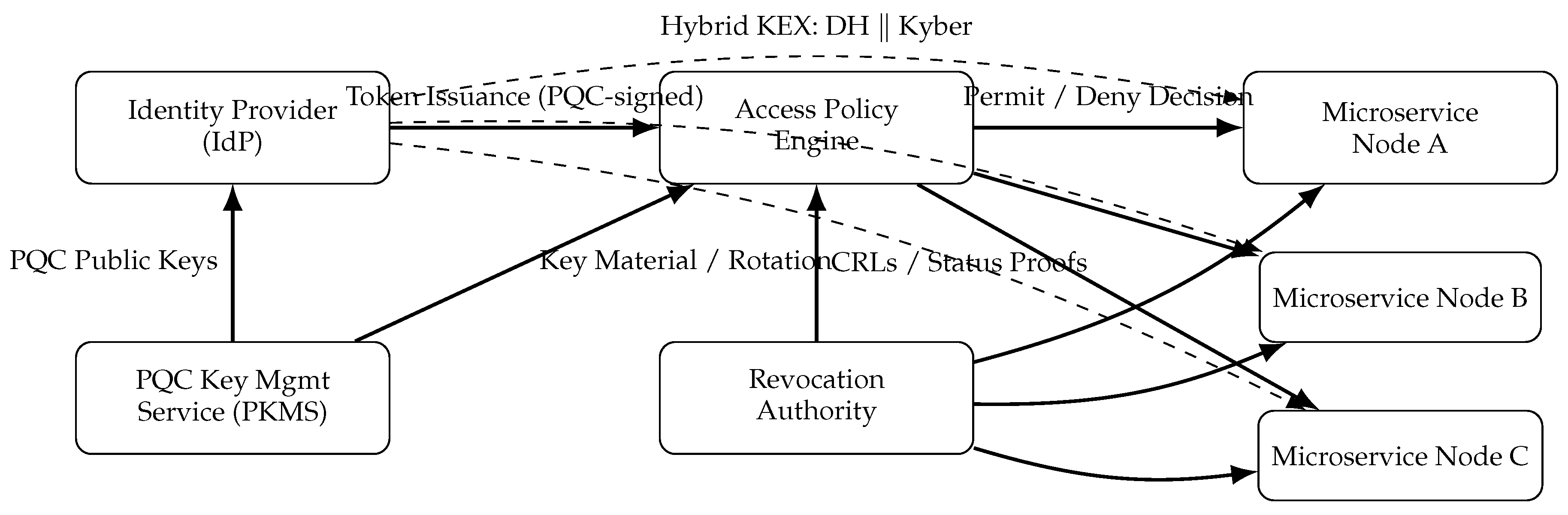
3.1. System Architecture
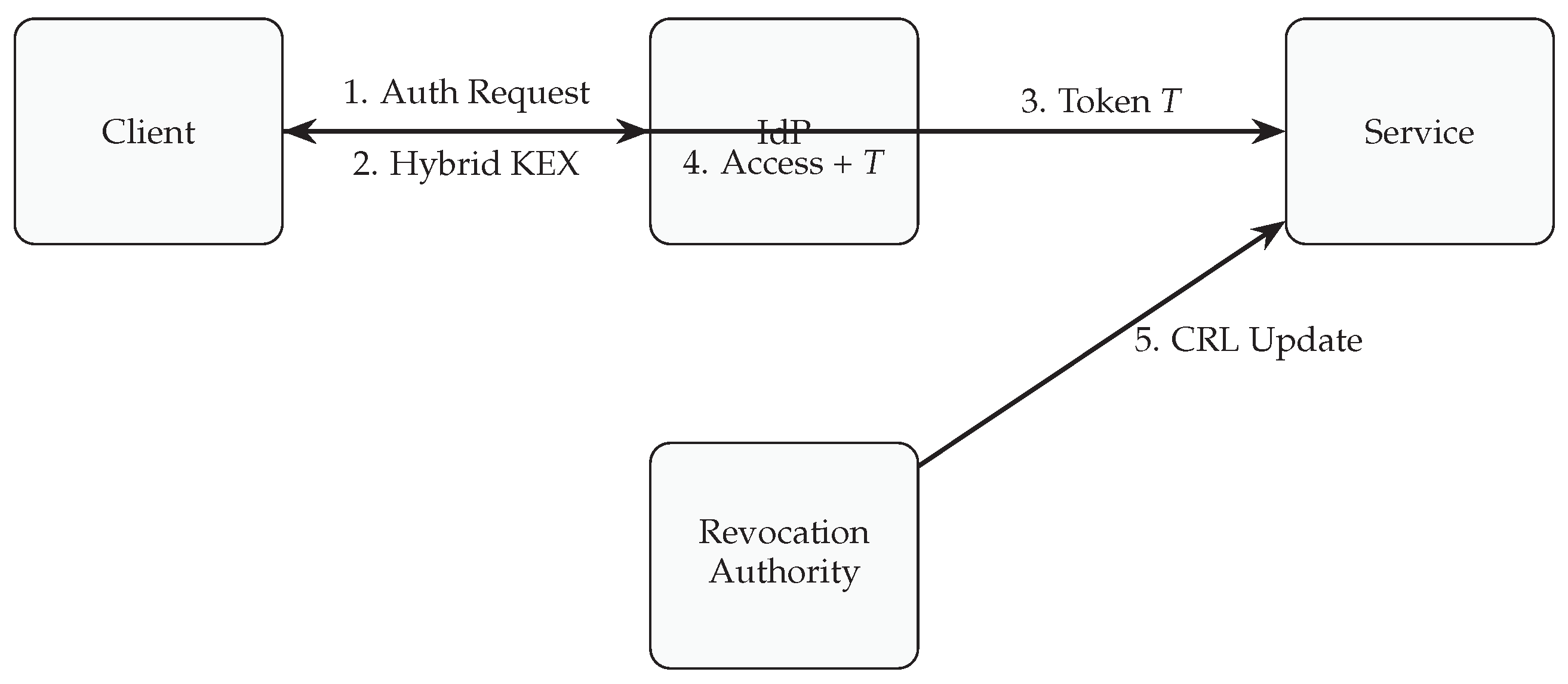
3.2. Operational Flow
3.3. Threat Model
- Intercept, replay, or modify network messages.
- Derive private keys from public parameters using quantum algorithms such as Shor’s.
- Attempt to forge digital signatures or counterfeit tokens.
- Compromise microservice nodes or gain unauthorized access through lateral movement.
- Post-quantum schemes (Kyber and Dilithium) remain computationally infeasible to break under the Learning With Errors (LWE) problem [12].
- The Identity Provider, PKMS, and Revocation Authority are trusted but may be semi-honest (honest-but-curious).
- Communication channels are authenticated via hybrid key exchanges combining classical and post-quantum primitives.
- Confidentiality: Session keys and token payloads are protected against both classical and quantum adversaries.
- Integrity and Authenticity: PQC signatures prevent message tampering and forgery.
- Forward Secrecy: Session compromise does not reveal past communications.
- Revocation Security: Expired or compromised tokens are effectively invalidated network-wide.
4. Proposed Protocol Design
4.1. Cryptographic Foundations
- Key Encapsulation Mechanism (KEM): The lattice-based Kyber algorithm is used for secure key exchange. It operates over the Learning With Errors (LWE) problem, providing IND-CCA2 security.
- Digital Signature Scheme: The Dilithium scheme, also based on LWE, ensures message authenticity and non-repudiation.
- Symmetric Encryption: AES-256-GCM provides authenticated encryption for token confidentiality under session keys.
4.2. Token Construction and Signing
4.3. Verification and Policy Enforcement
4.4. Revocation and Key Rotation
4.5. Security Properties
- Quantum Resistance: Security is based on the hardness of the LWE problem, providing protection against both classical and quantum adversaries.
- Forward Secrecy: Each session key is derived from ephemeral key pairs, isolating past sessions from future compromises.
- Token Integrity: Dilithium signatures ensure tamper-proof access tokens.
- Crypto-Agility: The hybrid composition allows modular substitution of PQC primitives as new standards emerge.
5. Security Analysis
5.1. Confidentiality of Sessions and Tokens
5.2. Integrity and Authenticity of Tokens
5.3. Forward Secrecy
5.4. Replay Protection and Freshness
5.5. Privacy and Unlinkability Considerations
5.6. Revocation Soundness
5.7. Resistance to Specific Attacks
5.8. Computational and Communication Overhead
5.9. Security Limitations
6. Performance Evaluation
6.1. Experimental Setup
6.2. Metrics and Parameters
- Key Exchange Time (): Average time to complete the hybrid key negotiation between client and IdP.
- Token Verification Time (): Time required to validate a PQC-signed token at microservice endpoints.
- Throughput (): Number of successful authentication and authorization requests processed per second.
- Latency Overhead (): Additional round-trip delay introduced by PQC operations compared to a classical baseline.
- Memory Footprint (M): Average memory consumption per microservice for storing PQC public keys, CRLs, and active sessions.
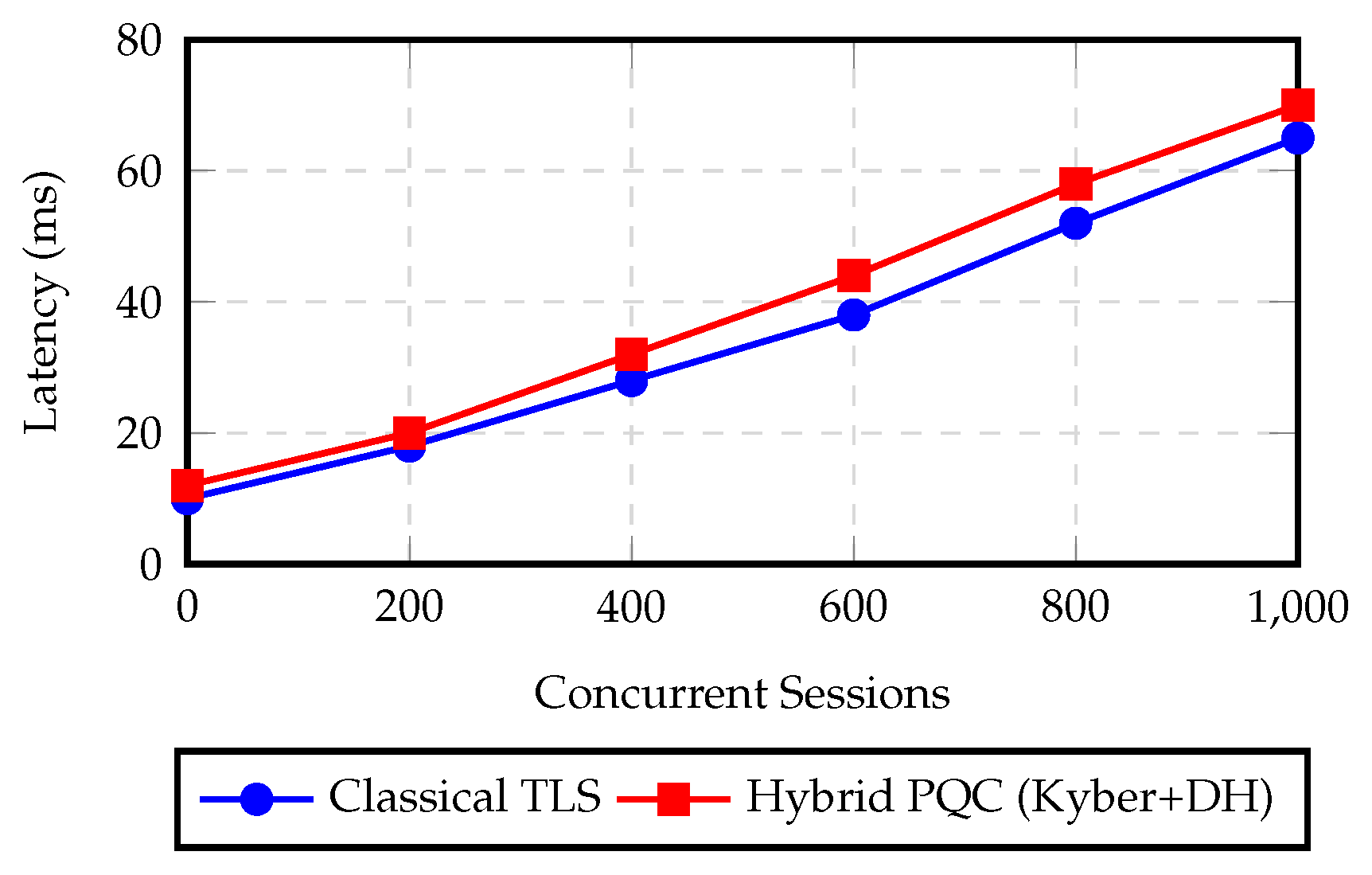
| Concurrent Sessions | Classical TLS (ms) | Hybrid PQC (ms) | Overhead (%) |
|---|---|---|---|
| 100 | 12 | 15 | 25.0 |
| 200 | 18 | 22 | 22.2 |
| 400 | 28 | 33 | 17.9 |
| 600 | 38 | 44 | 15.8 |
| 800 | 52 | 59 | 13.5 |
| 1000 | 65 | 72 | 10.7 |
6.3. Results and Observations
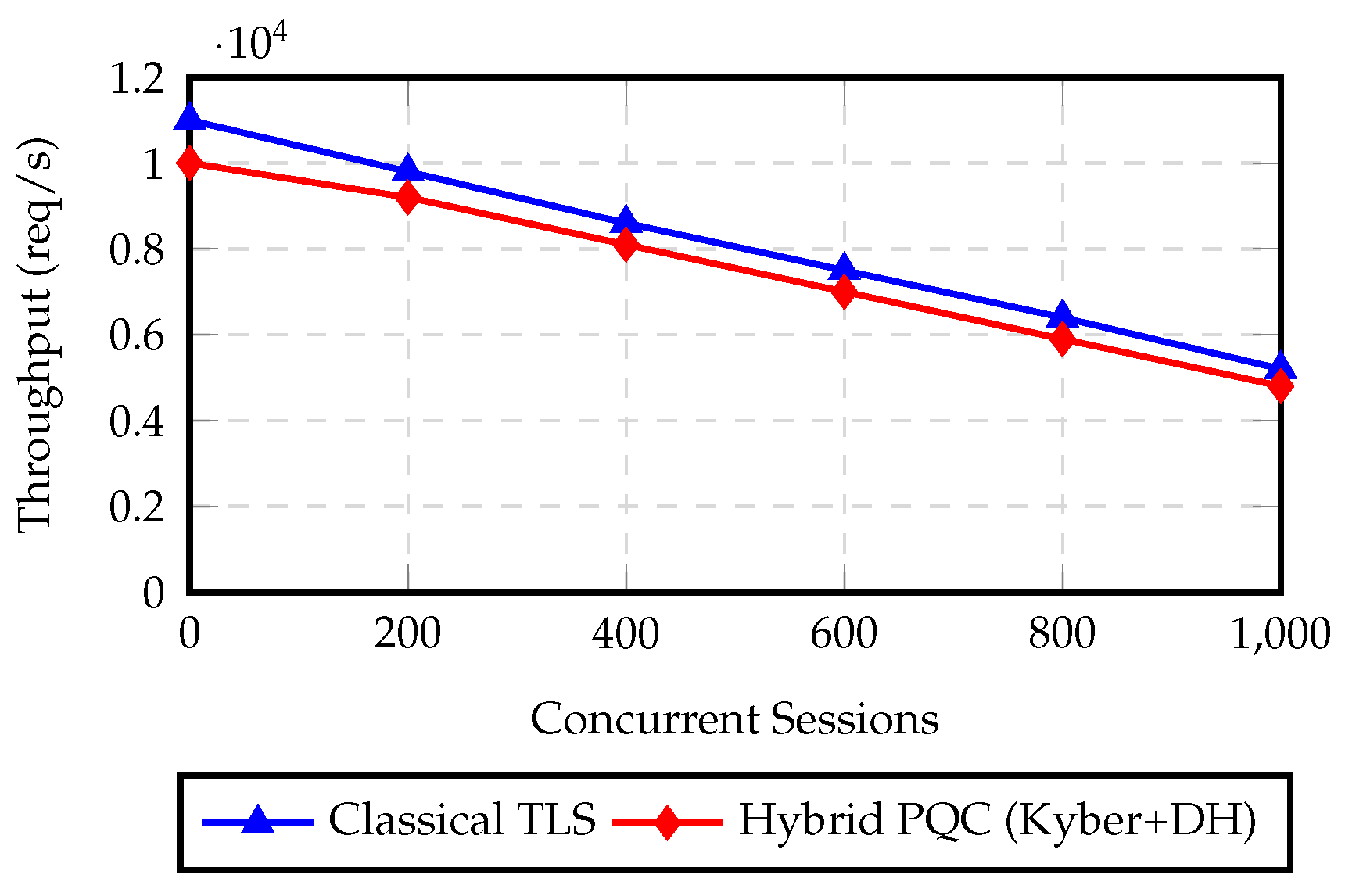
| Concurrent Sessions | Classical TLS) | Hybrid PQC (req/s) | Drop (%) |
|---|---|---|---|
| 100 | 11000 | 10000 | 9.1 |
| 200 | 9800 | 9200 | 6.1 |
| 400 | 8600 | 8100 | 5.8 |
| 600 | 7500 | 7000 | 6.7 |
| 800 | 6400 | 5900 | 7.8 |
| 1000 | 5200 | 4800 | 7.7 |
6.4. Discussion
7. Conclusion and Future Work
References
- Bavdekar, R.; Chopde, E.J.; Bhatia, A.; Tiwari, K.; Daniel, S.J.; Atul. Post Quantum Cryptography: Techniques, Challenges, Standardization, and Directions for Future Research. arXiv 2022, arXiv:2202.02826. [Google Scholar] [CrossRef]
- Shahane, R.; Prakash, S. UGC CARE II Journal of Validation Technology Quantum Machine Learning Opportunities for Scalable AI. Journal of Validation Technology 2022, 28. [Google Scholar] [CrossRef]
- Bos, J.W.; Ducas, L.; Kiltz, E.; Lepoint, T.; Lyubashevsky, V.; Schwabe, P.; Seiler, G.; Stehlé, D. CRYSTALS–Kyber: Algorithm Specifications and Supporting Documentation. In Proceedings of the National Institute of Standards and Technology, Post-Quantum Cryptography Project, 2021. [Google Scholar]
- Shor, P. Algorithms for quantum computation: discrete logarithms and factoring. In Proceedings of the Proceedings 35th Annual Symposium on Foundations of Computer Science, 1994; pp. 124–134. [Google Scholar] [CrossRef]
- Grover, L.K. A Fast Quantum Mechanical Algorithm for Database Search. In Proceedings of the 28th Annual ACM Symposium on Theory of Computing (STOC), 1996; pp. 212–219. [Google Scholar] [CrossRef]
- Devipriya, A.; Rosaline, R.A.; Prabhu, M.R.; Nancy, P.; Karthick, V.; Kadumbadi, V. Algorithmic Approaches to Securing Cloud Environments in the Realm of Cybersecurity. Proceedings of the 2024 10th International Conference on Communication and Signal Processing (ICCSP) 2024, 697–702. [Google Scholar] [CrossRef]
- Devaraju, P.; Devarapalli, S.; Tuniki, R.R.; Kamatala, S. Secure and Adaptive Federated Learning Pipelines: A Framework for Multi-Tenant Enterprise Data Systems. In Proceedings of the 2025 International Conference on Computing Technologies (ICOCT), 2025; pp. 1–7. [Google Scholar] [CrossRef]
- Irshad, R.R.; Hussain, S.; Hussain, I.; Nasir, J.A.; Zeb, A.; Alalayah, K.M.; Alattab, A.A.; Yousif, A.; Alwayle, I.M. IoT-Enabled Secure and Scalable Cloud Architecture for Multi-User Systems: A Hybrid Post-Quantum Cryptographic and Blockchain-Based Approach Toward a Trustworthy Cloud Computing. IEEE Access 2023, 11, 105479–105498. [Google Scholar] [CrossRef]
- Yang, J.; Govindarajan, V.; Xu, X.; Khan, M.A.; Shaikh, Z.A.; Ayouni, S.; Shabaz, M.; Gadekallu, T.R.; Por, L.Y. Enhancing Cryptographic Security in Smart Consumer Electronics with a Hybrid Classical–Post-Quantum Framework. IEEE Transactions on Consumer Electronics 2025, 1–1. [Google Scholar] [CrossRef]
- Tsui, E.; Cheong, R.K.; Sabetzadeh, F. Cloud-Based Personal Knowledge Management as a service (PKMaaS). In Proceedings of the 2011 International Conference on Computer Science and Service System (CSSS), 2011; pp. 2152–2155. [Google Scholar] [CrossRef]
- Sinha, A.R. Unified System Design: A Comprehensive Study on Scalability, Access Control, and Communication Protocols. IJSAT-International Journal on Science and Technology 2024, 15. [Google Scholar] [CrossRef]
- Ducas, L.; Kiltz, E.; Lepoint, T.; Lyubashevsky, V.; Schwabe, P.; Seiler, G.; Stehlé, D. CRYSTALS–Dilithium: Digital Signatures from Module-Lattices. In Proceedings of the National Institute of Standards and Technology, Post-Quantum Cryptography Project, 2021. [Google Scholar]
- Bollikonda, M. Federated Zero-Trust: Privacy-Preserving Analytics Across Multi-Cloud Environments. Preprints 2025. [Google Scholar] [CrossRef]
- Shirdi, A.; Peta, S.B.; Sajanraj, N.; Acharya, S. Federated Learning for Privacy-Preserving Big Data Analytics in Cloud Environments. In Proceedings of the 2025 Global Conference in Emerging Technology (GINOTECH), 2025; pp. 1–8. [Google Scholar] [CrossRef]
- Bollikonda, T. Design and Optimization of Cloud Native Homomorphic Encryption Workflows for Privacy-Preserving ML Inference. arXiv 2025, arXiv:2510.24498. [Google Scholar] [CrossRef]
- Pasam, V.R.; Devaraju, P.; Methuku, V.; Dharamshi, K.; Veerapaneni, S.M. Engineering Scalable AI Pipelines: A Cloud-Native Approach for Intelligent Transactional Systems. In Proceedings of the 2025 International Conference on Computing Technologies (ICOCT), 2025; pp. 1–8. [Google Scholar] [CrossRef]
- Shahane, R. Design Patterns for Scalable ML Workflows in Azure Data Lake and Synapse Analytics 2024. 12 11. [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




