Submitted:
04 December 2025
Posted:
05 December 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Challenges
1.2. Contributions
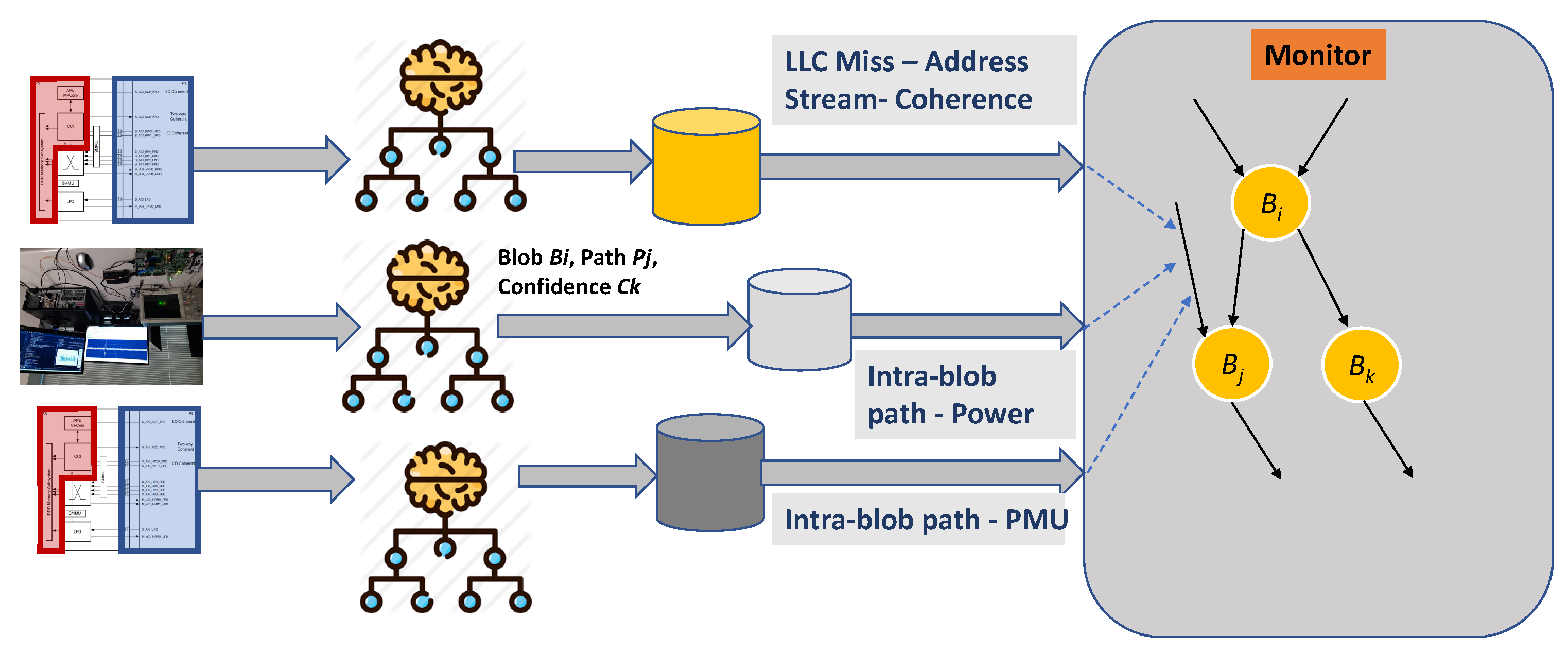
- Low-overhead program tapping for sensor streams without disrupting the program state. Syncing diverse sensor streams to maintain a coherent view of the program state.
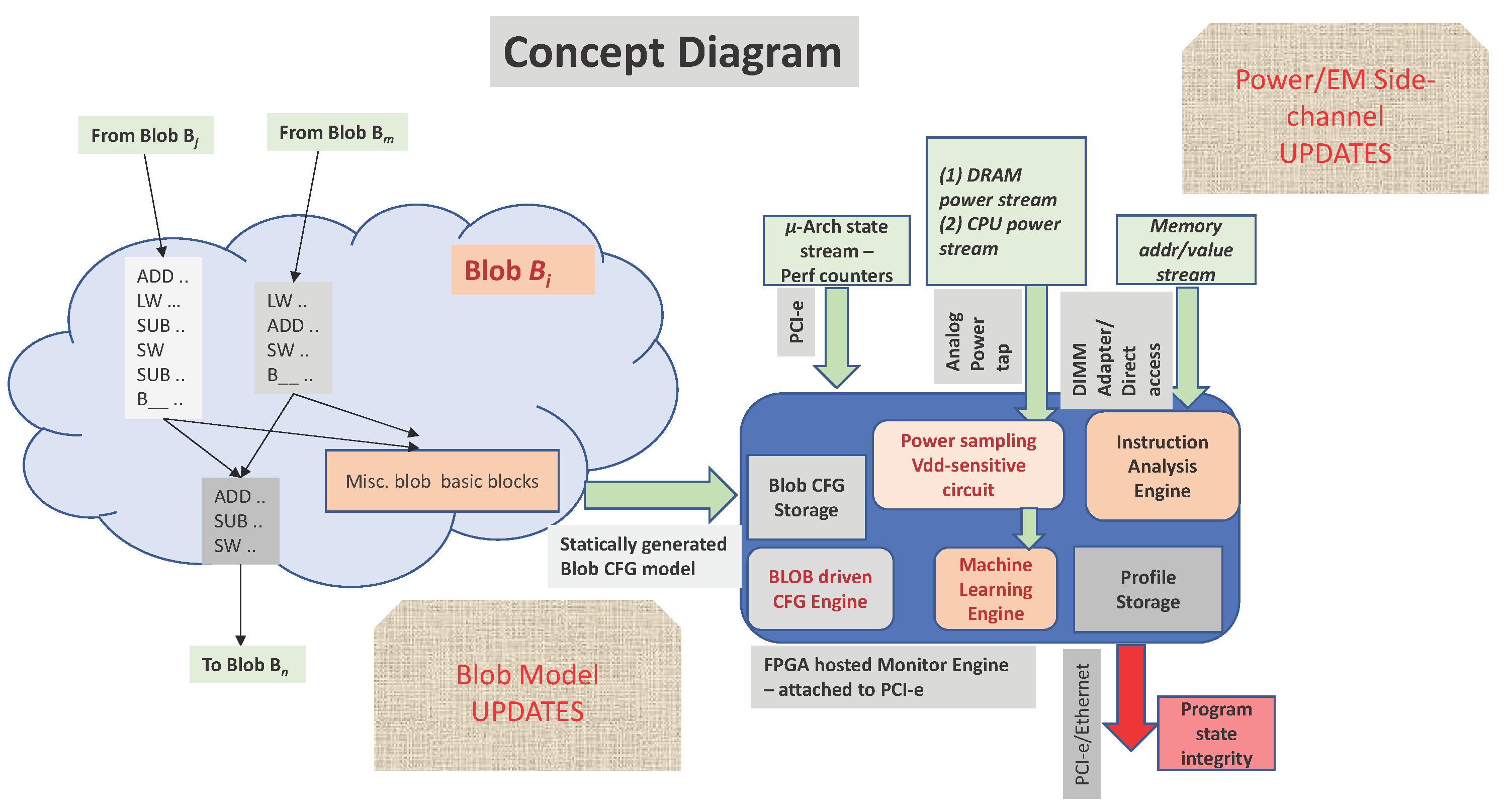
- A novel program execution model based on a blob, a coarser control flow graph, enables low overhead multi-modal sensor stream.
- Mapping/transformation of traditional control-flow integrity to parameterized blob-level CFG integrity driven by sensor stream characteristics.
- First prototype of a physical decoupled monitor. Evaluations demonstrate that individual side-channel sensor streams show over 80-90% accuracy in path localization, while the overall monitor accuracy for normal execution flow localization is 83.3%, and anomalous execution flow detection is 100%.
2. Related Work / Background
2.1. Performance Counter Anomaly Detection and CFI
2.2. Power and EM Side-Channels for Integrity/CFI
2.3. CFG Coarsening – Super and Hyper Blocks
2.4. Microarchitectural Side-Channels
3. Motivation or Vision
Problem:
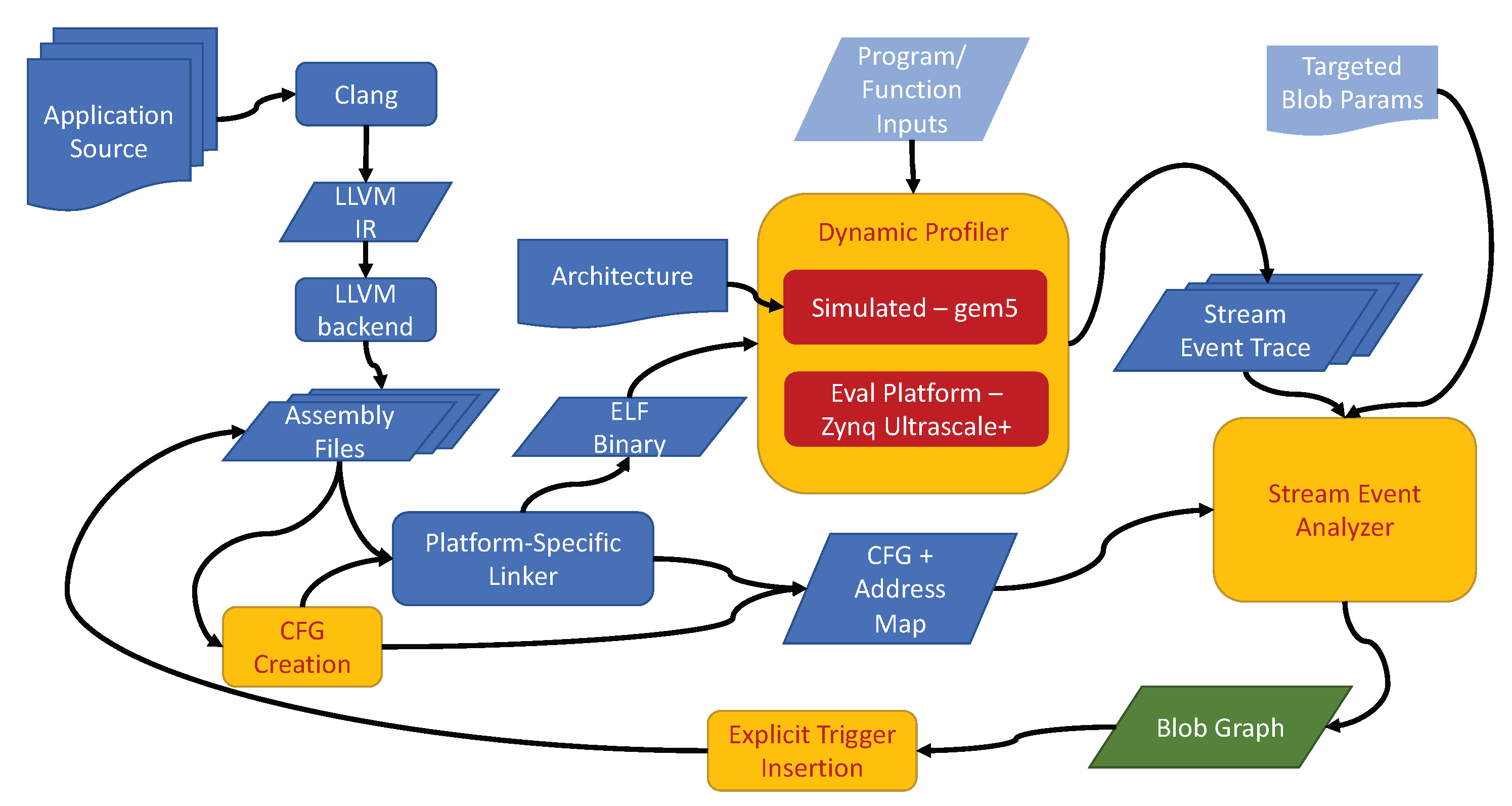
Solution Framework:
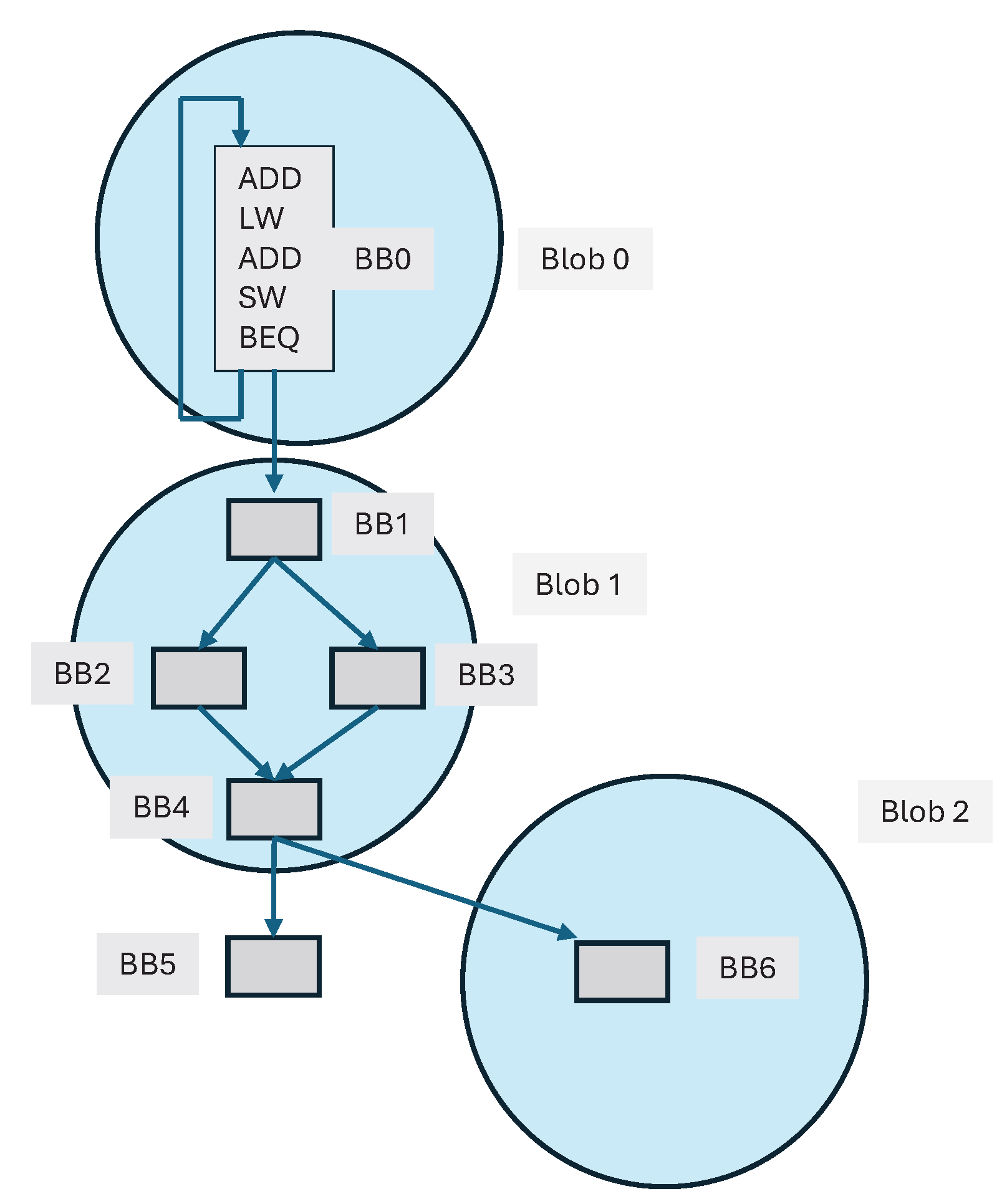
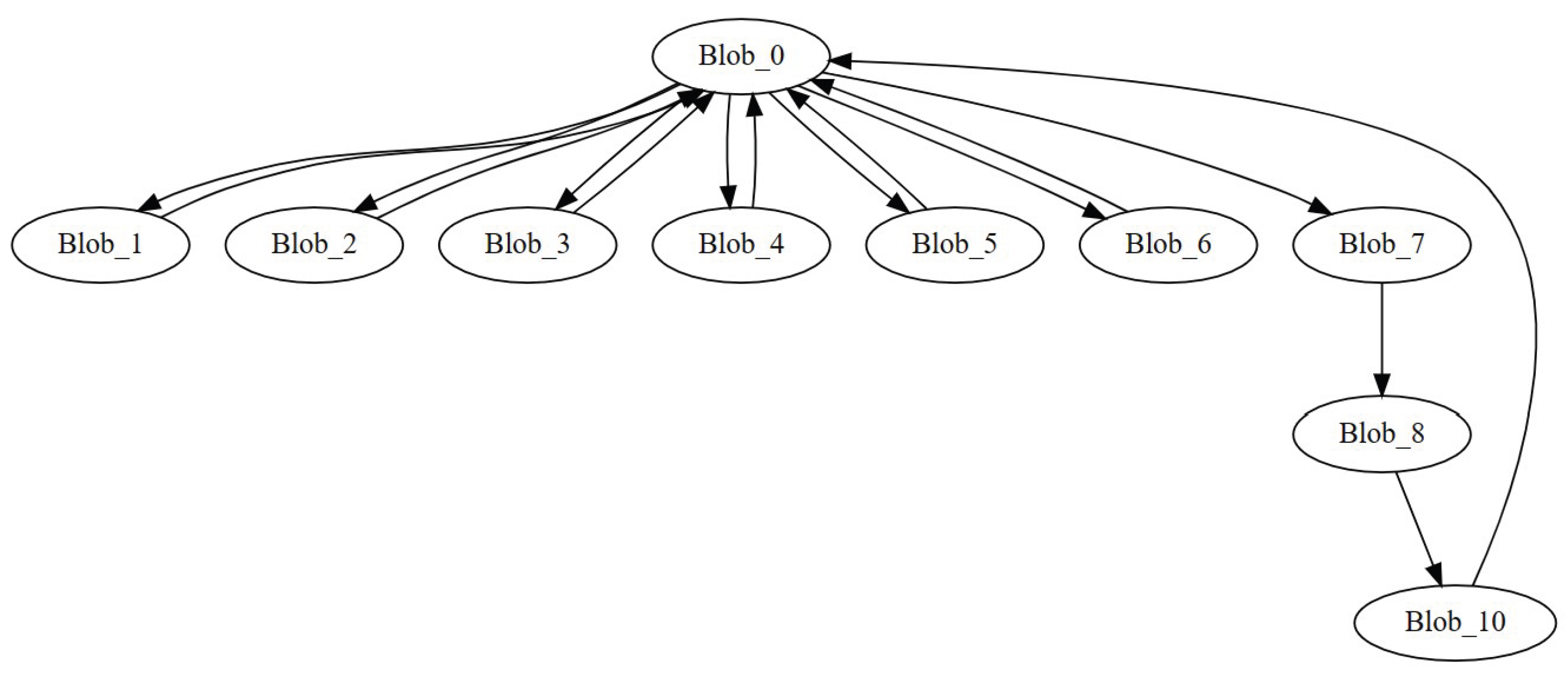
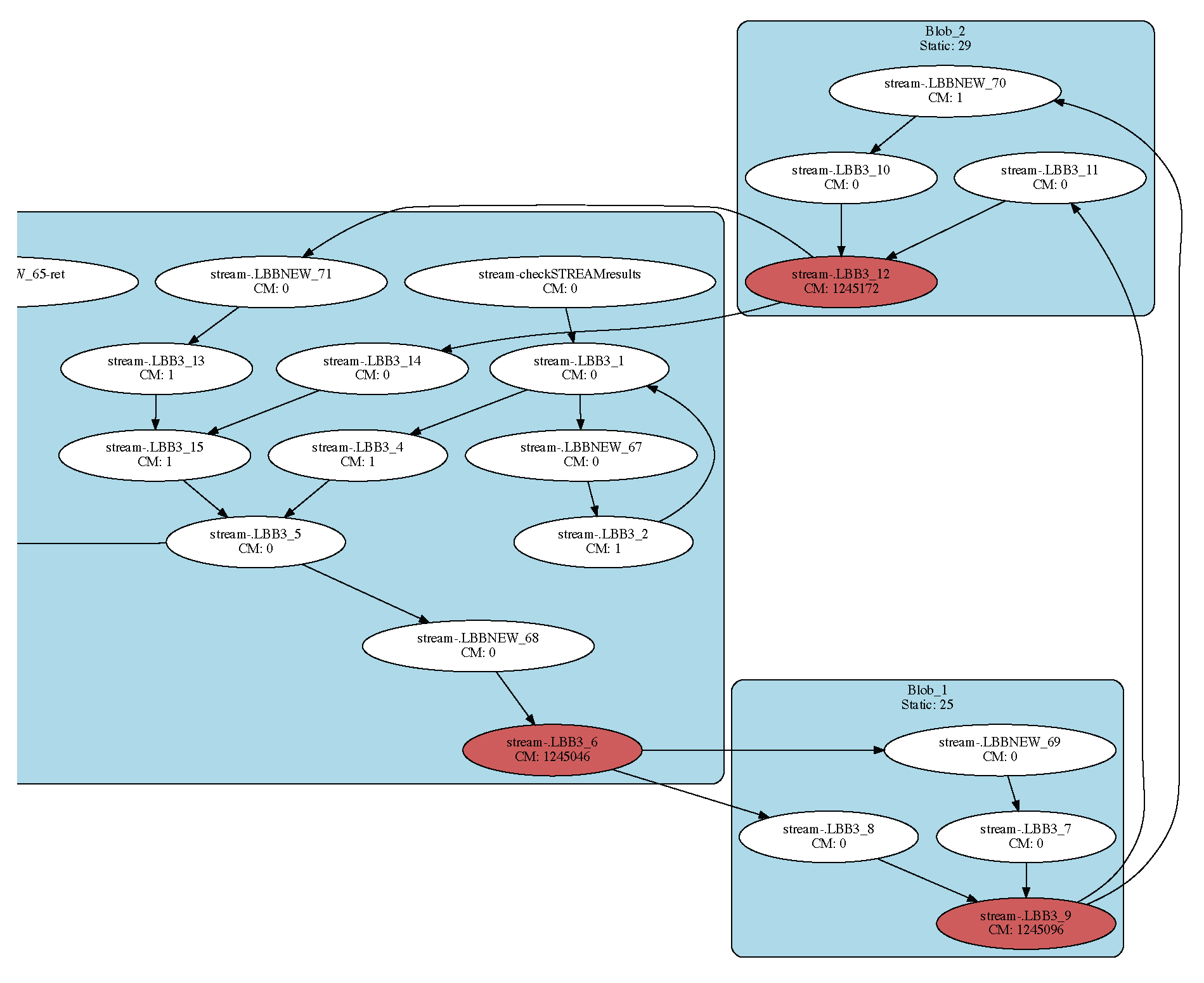
4. Control Flow Graphs Coarsening Blob Graphs
4.1. Blob Graph
4.2. Blob Creation
4.2.1. Strongly-Connected Component Approach
- First, some blobs would be overly large. For example, if multiple functions are called in a loop, those functions’ basic blocks and the loop are an SCC—since there is a way for each basic block in the loop to reach each basic block in a function and vice versa.
- Second, isolated basic blocks end up in their own SCC with limited or no externally visible signals. The execution of these blobs is likely to be invisible to a decoupled monitor.
4.2.2. SCC Approach with Dynamic Profiling
4.2.3. Naive Direct DFS Profiling Approach
| Algorithm 1: Naive DFS Profiling Blob Generation |
|
4.2.4. Natural Loops Approach
| Algorithm 2: Natural Loop Blob Generation |
|
5. Evaluation Platform & Methodology
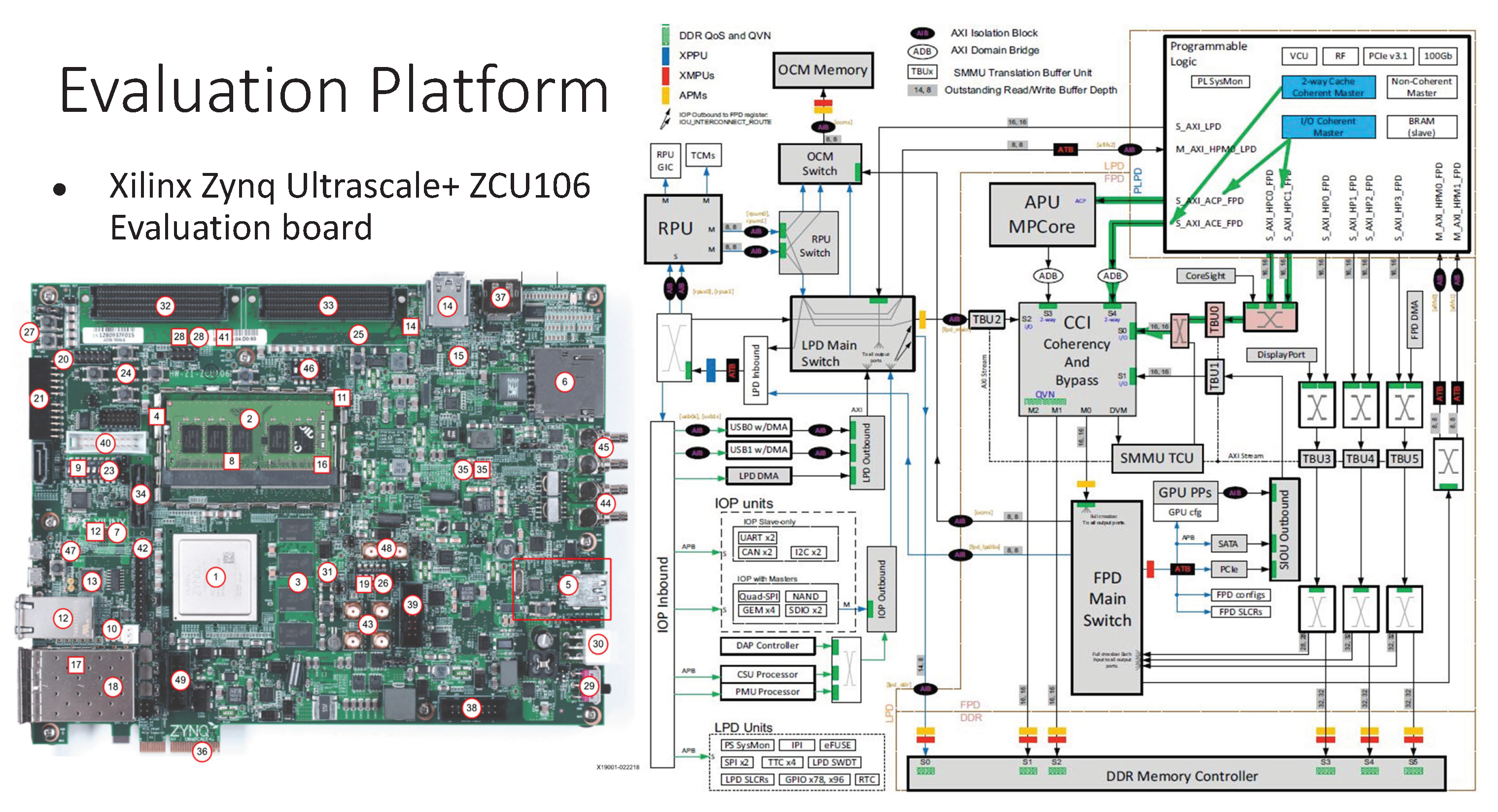
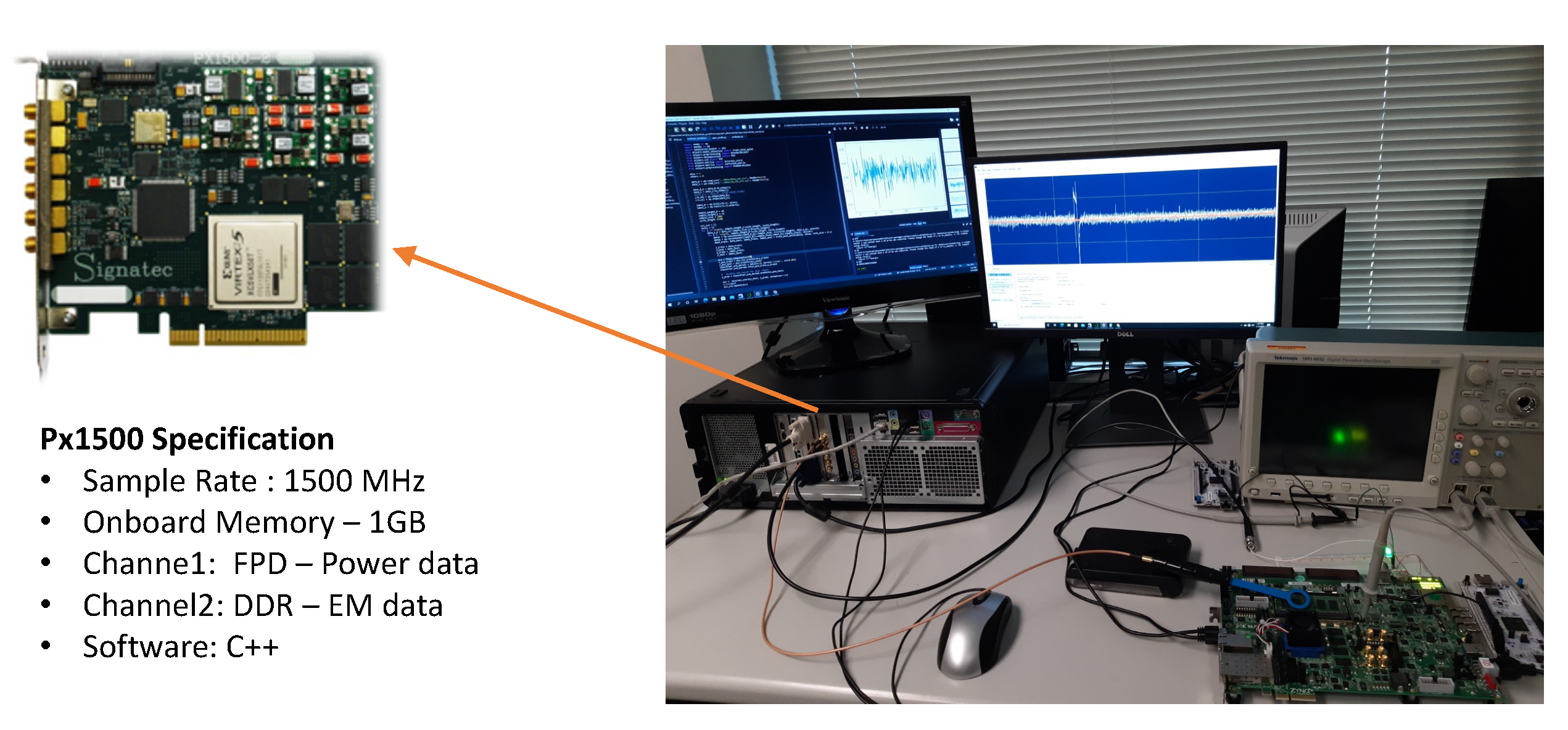
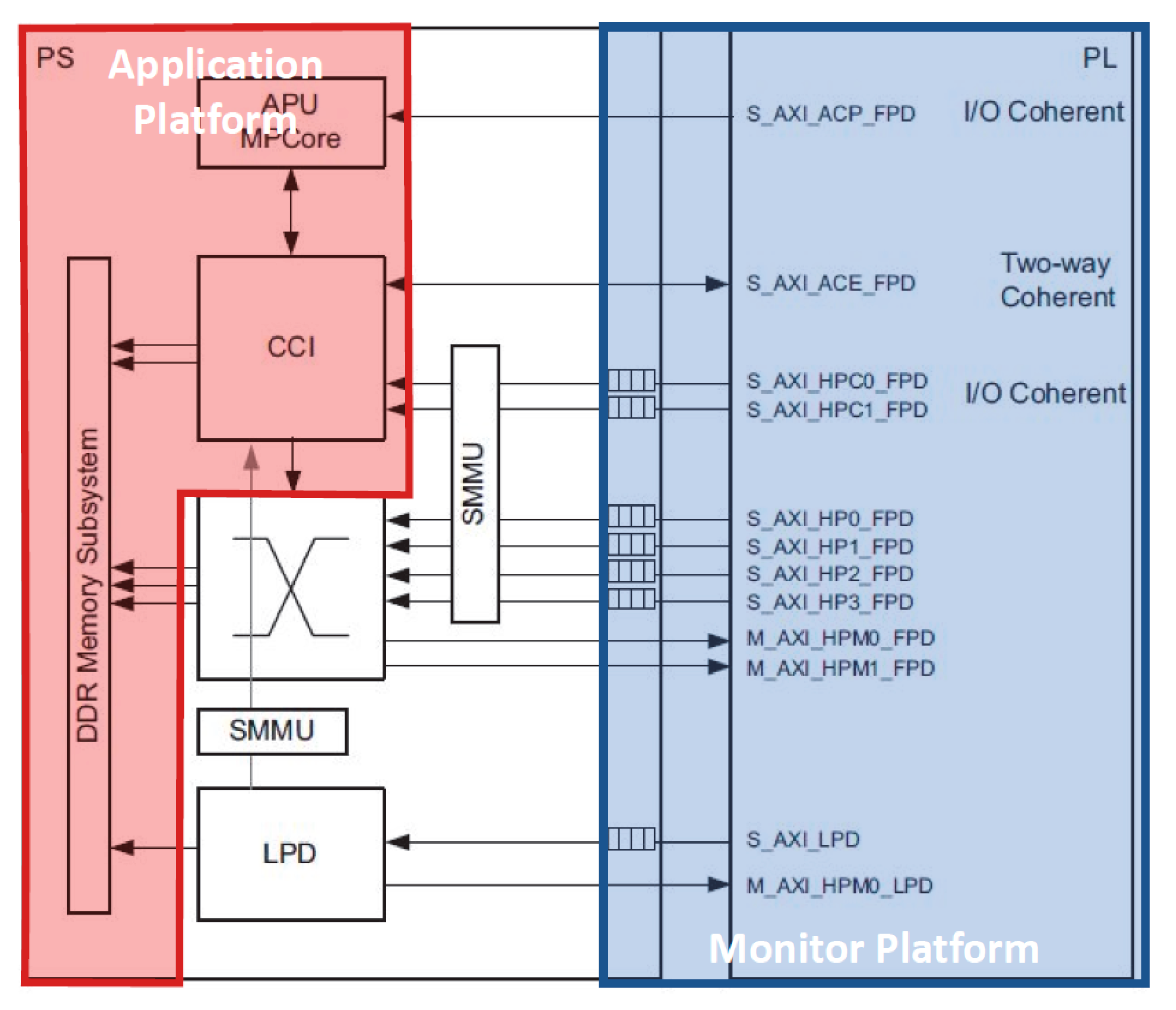
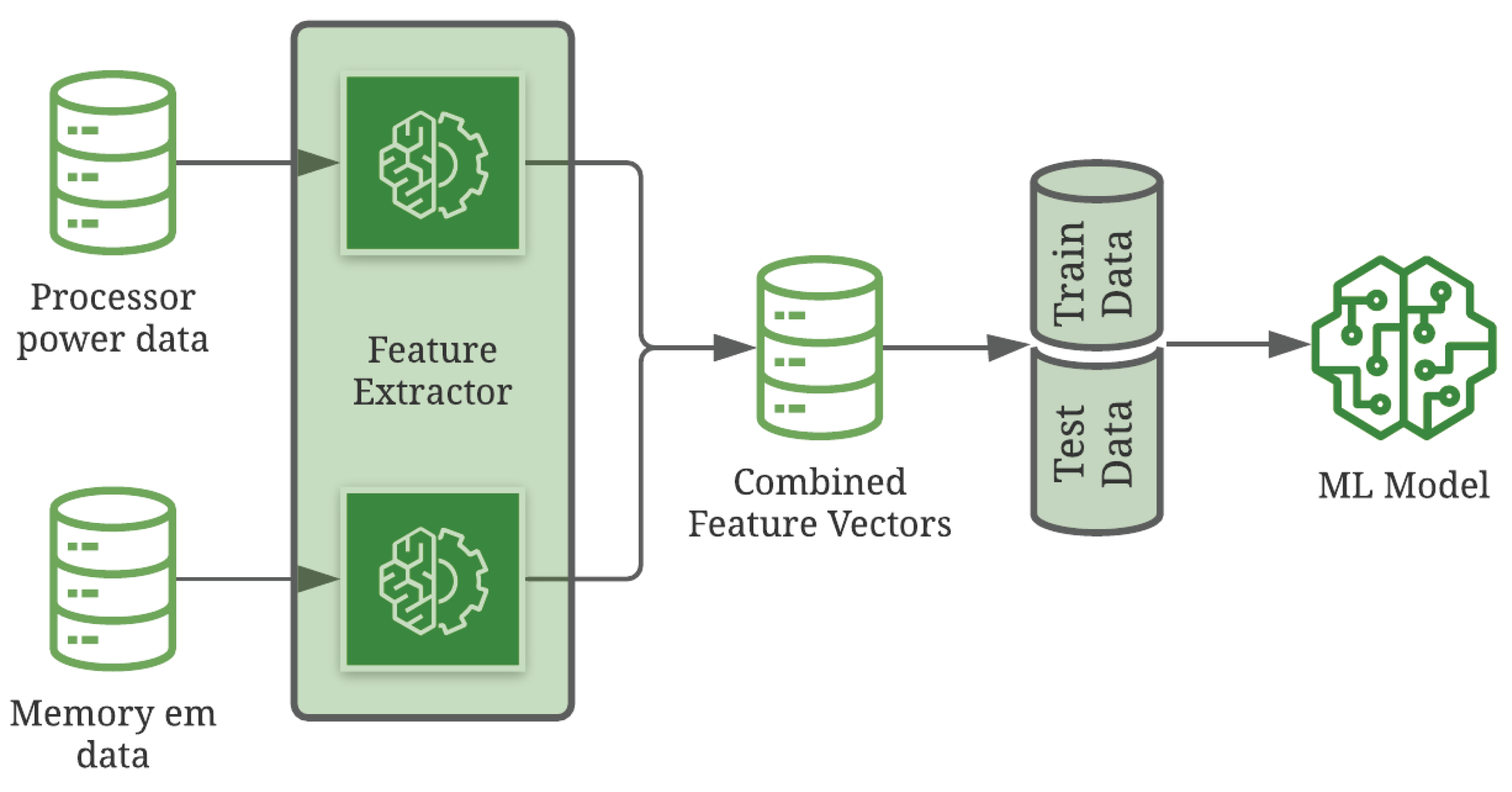
5.1. Evaluation Platform
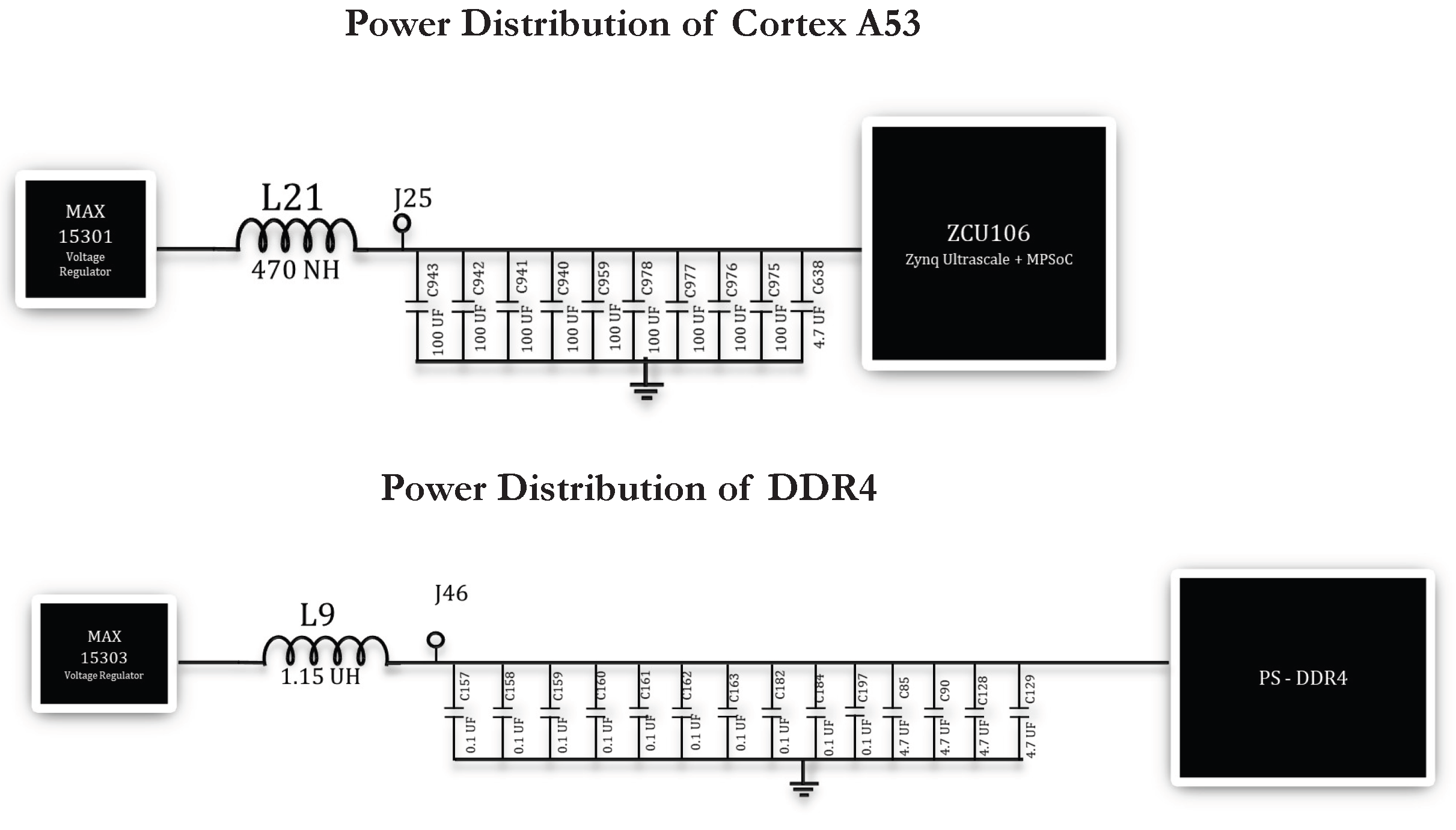
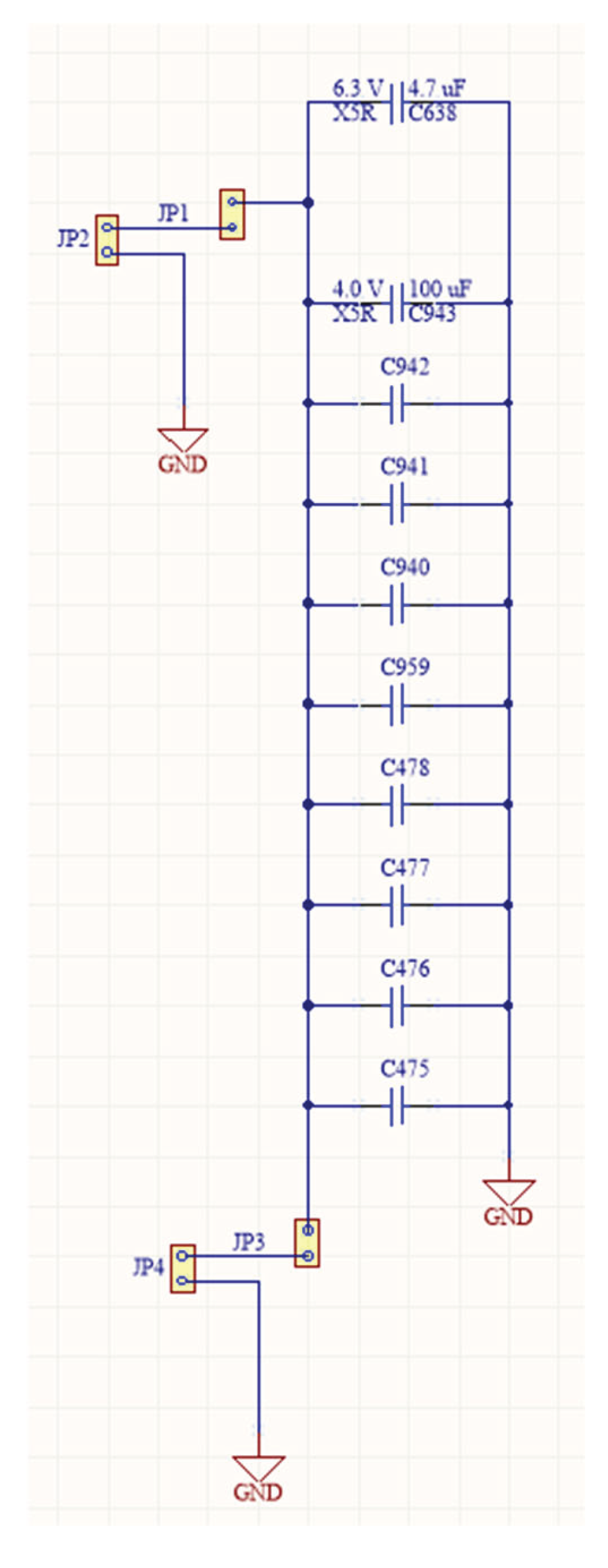
5.2. Characterization of Power Stream
5.2.1. Power Domains
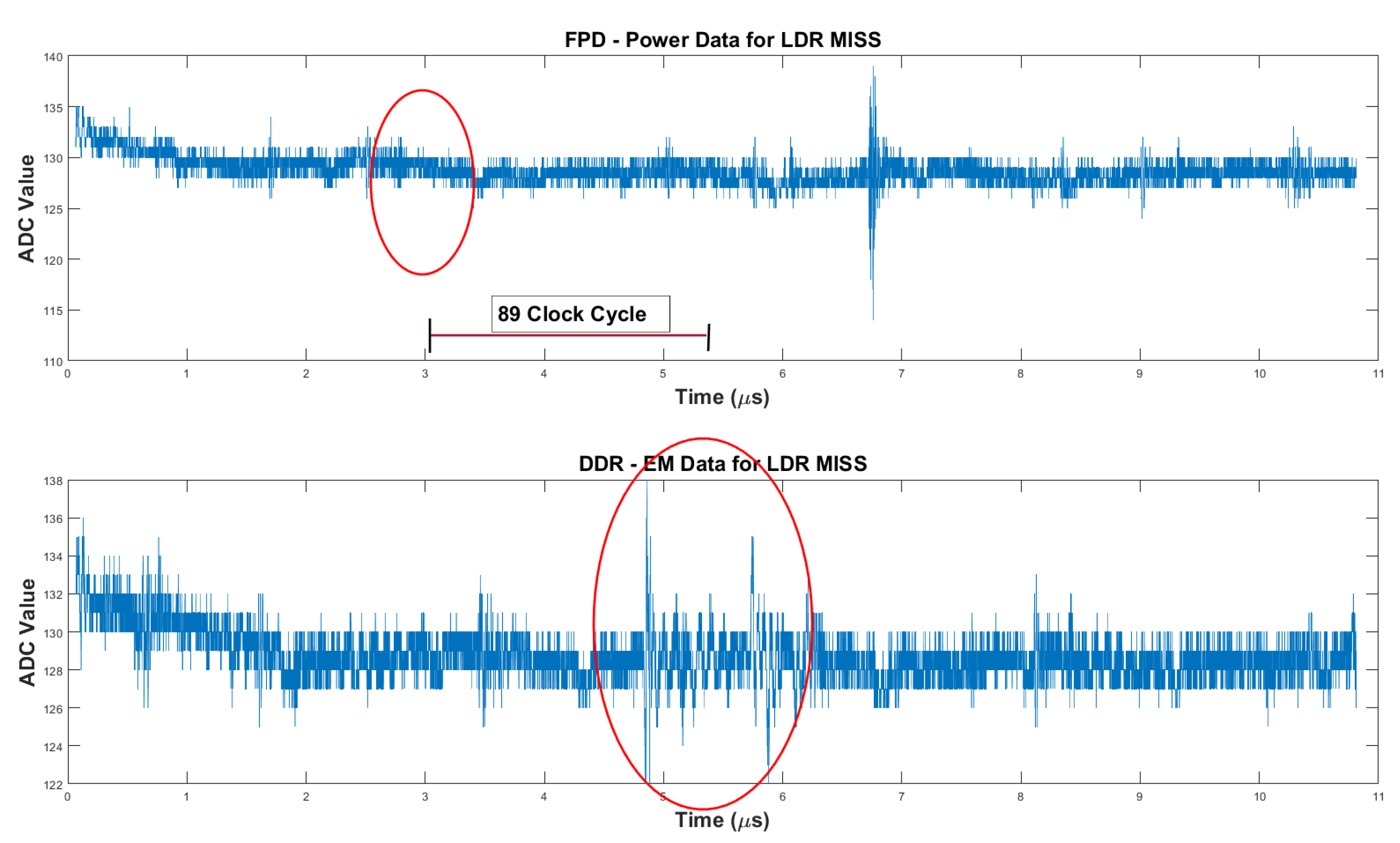
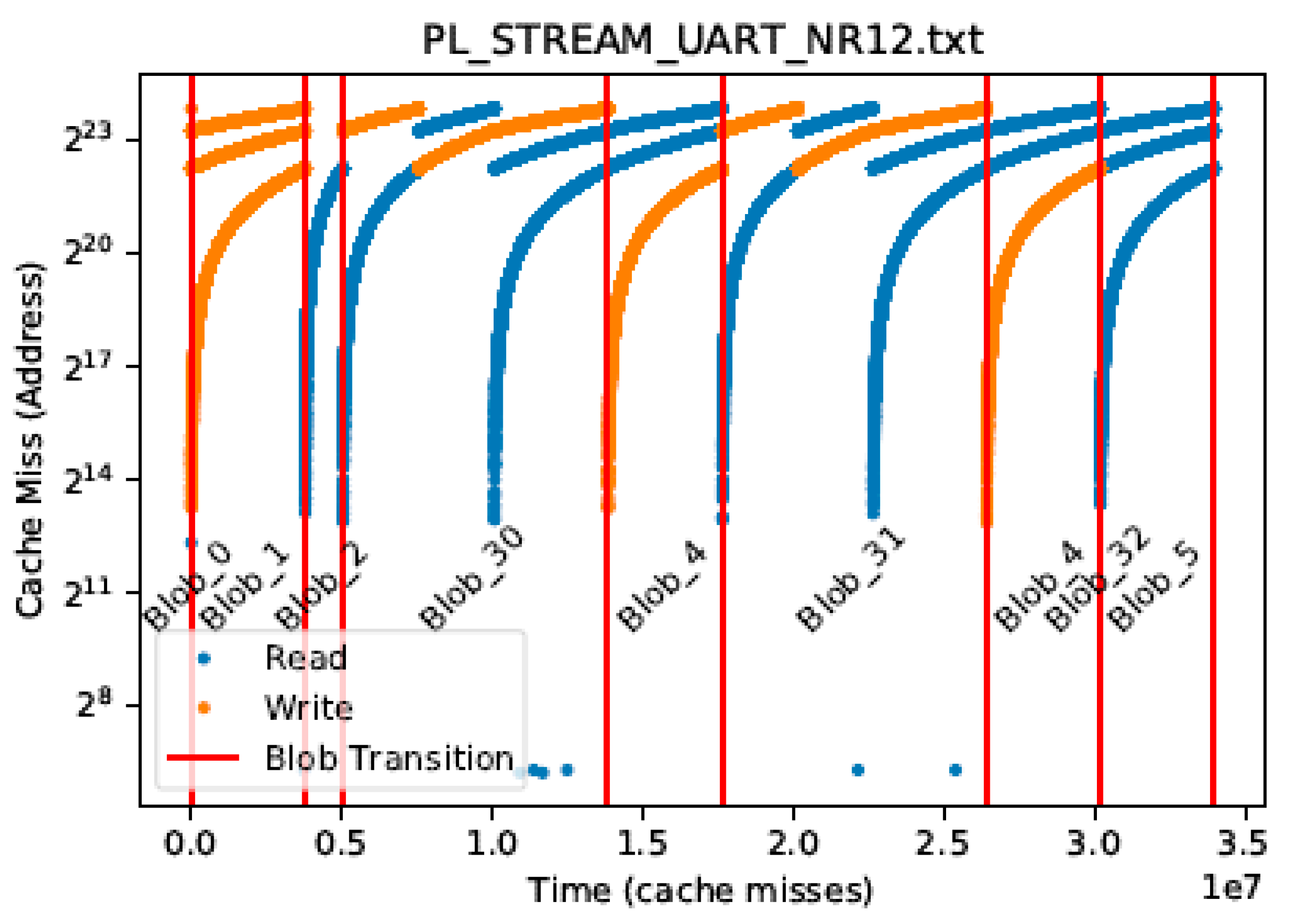
5.3. LLC Miss Address Stream
5.3.1. Explicit State Triggers
5.4. Performance Counter Stream
5.5. Assumptions for Current Evaluation
5.6. Monitor
6. Results
6.1. Benchmark
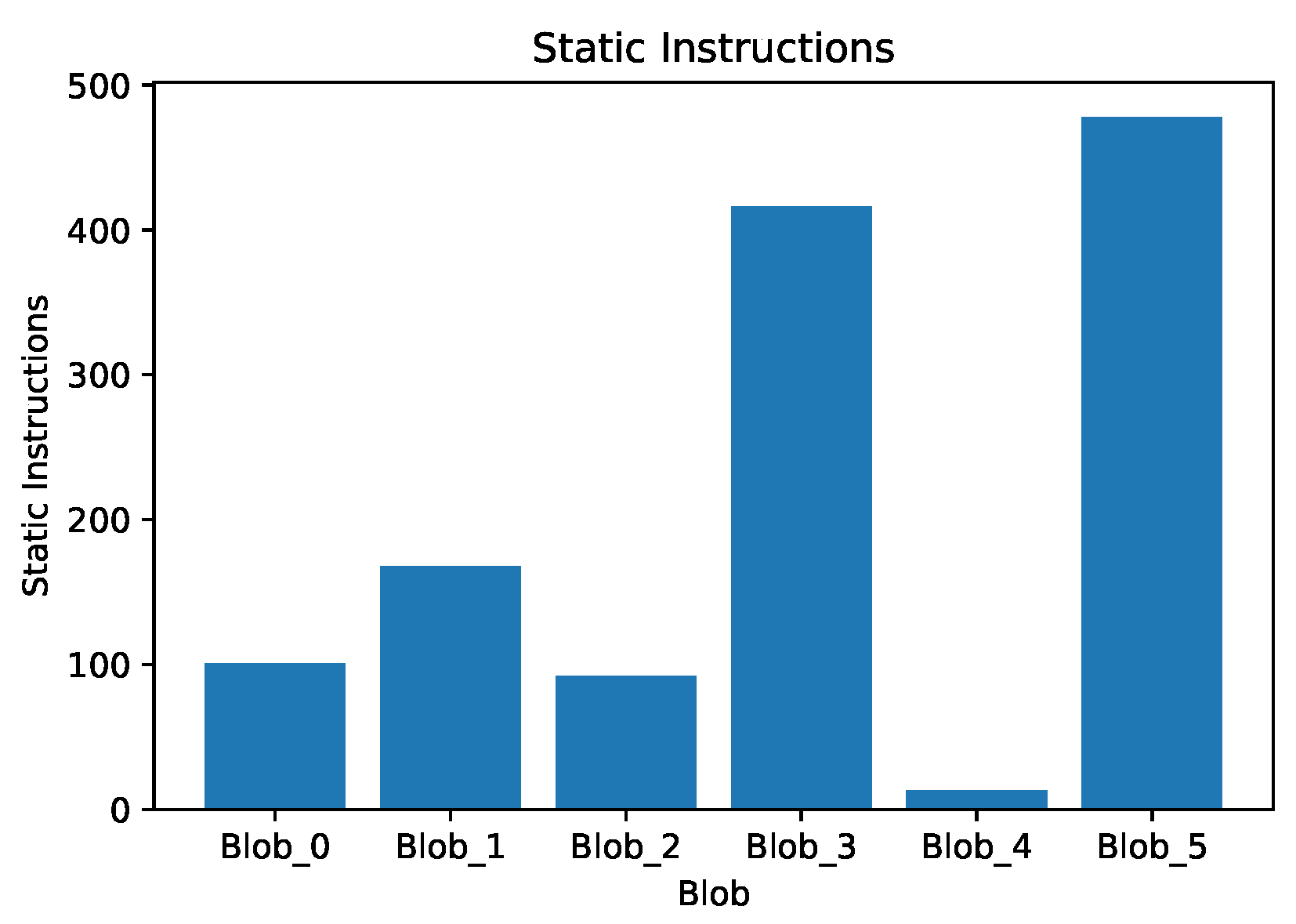
6.2. Blob Characteristics
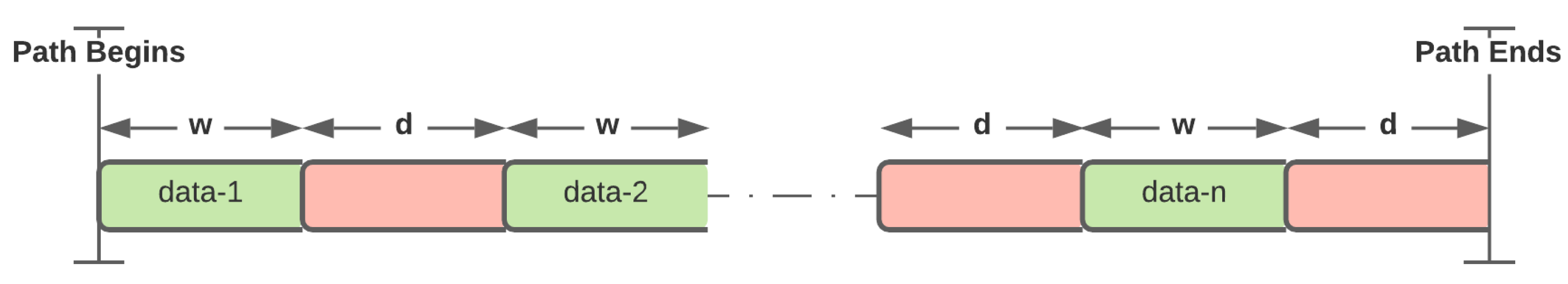
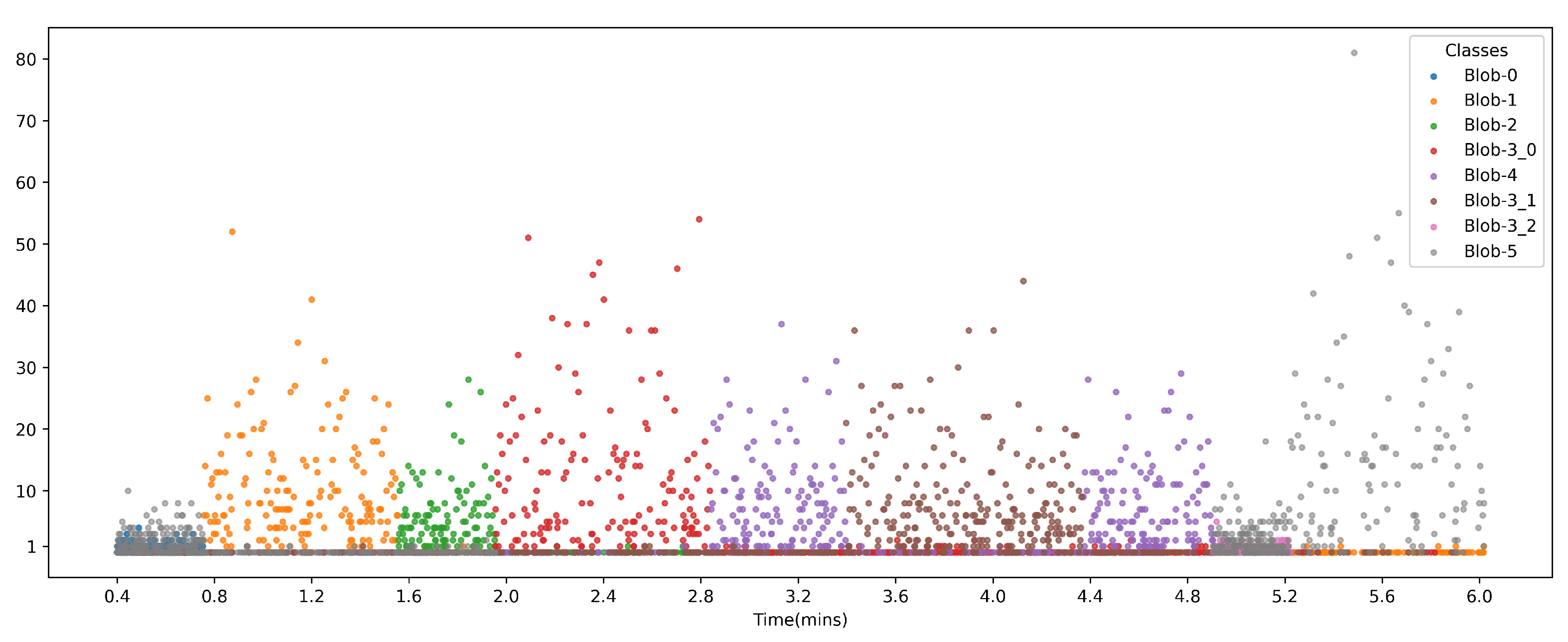
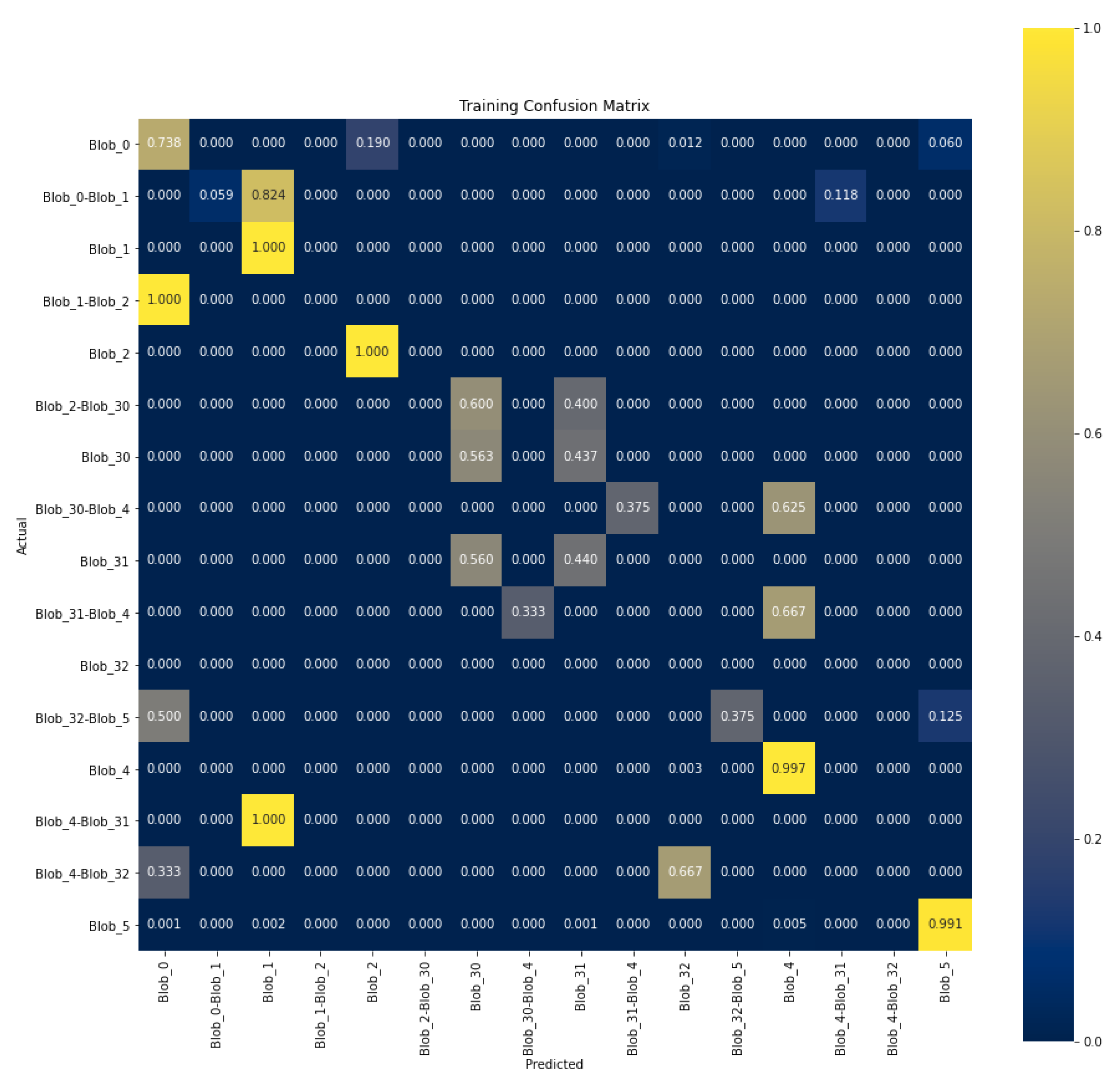
6.3. Power Stream Blob Path Identification
- Path-based Identification:
- The machine learning model is built to localize into a unique path through a blob that the benchmark executes.
- Blob-based Identification:
- The machine learning model is built to localize the execution into a blob in the benchmark.
Path-based Identification:
Blob-based Identification:
| Blob-ID | Success rate |
|---|---|
| Blob-0 | 85% |
| Blob-1 | 96% |
| Blob-2 | 95% |
| Blob-3 | 86% |
| Blob-4 | 85% |
| Blob-5 | 90% |
6.4. Address Stream Blob Path Identification
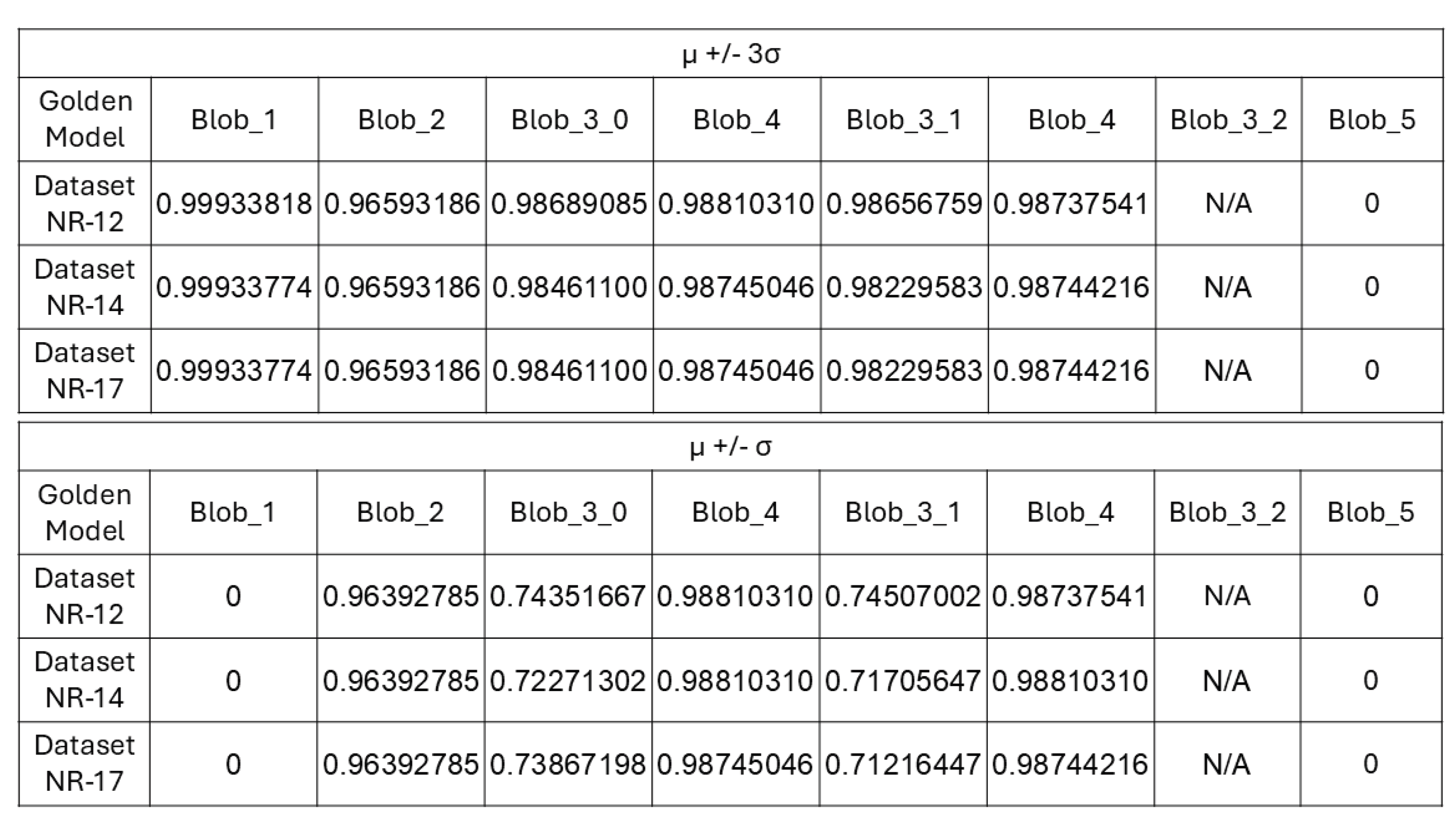
6.5. PMU Stream Blob Path Identification
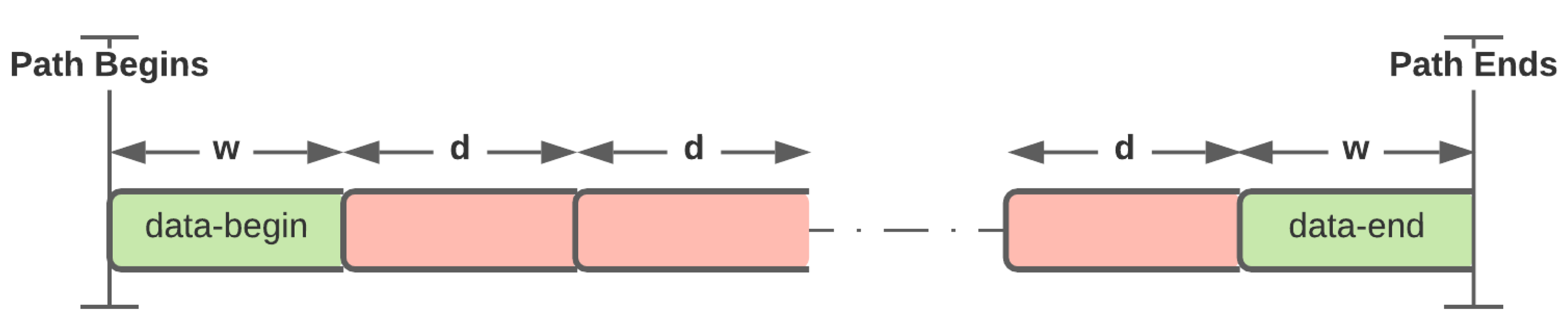
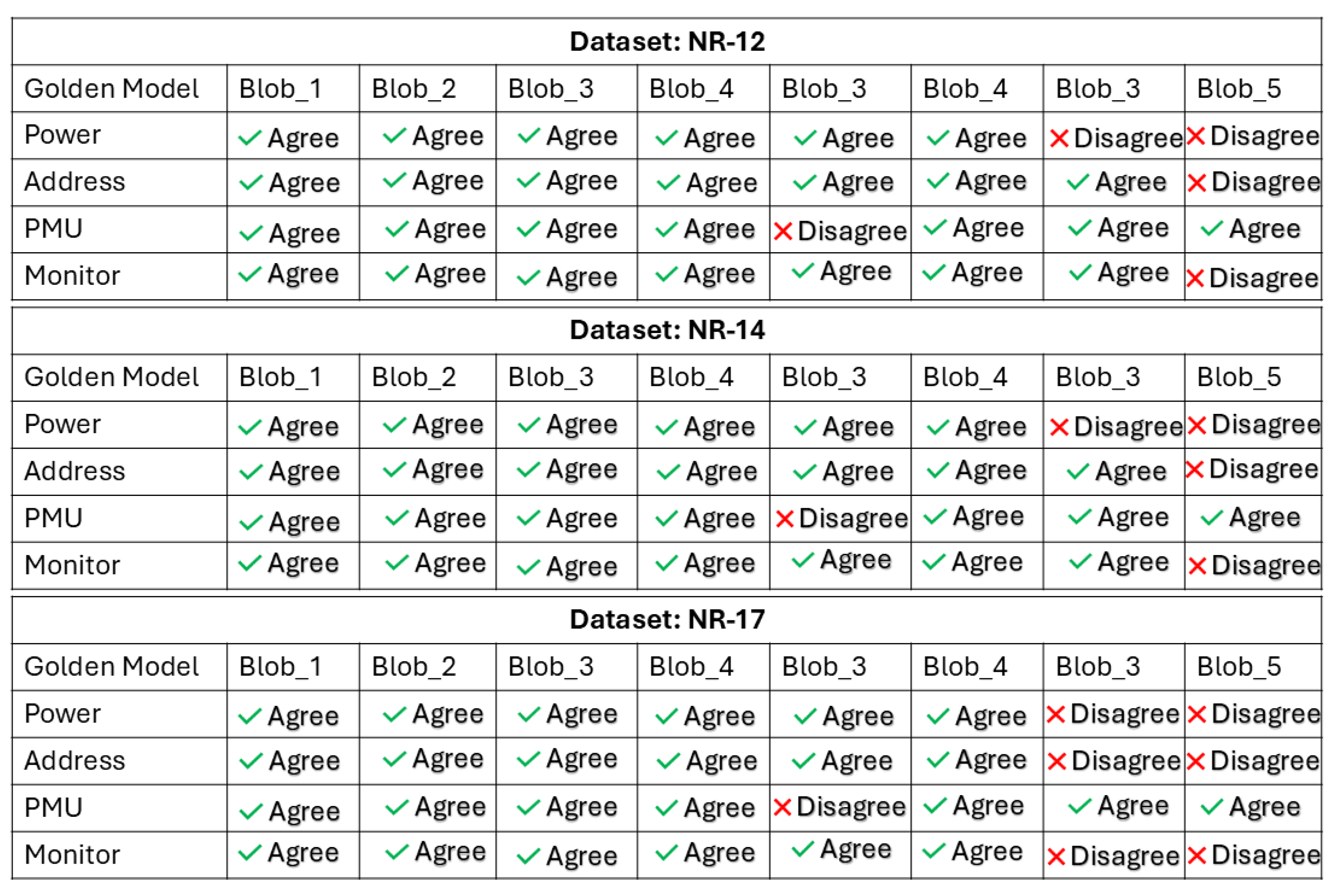
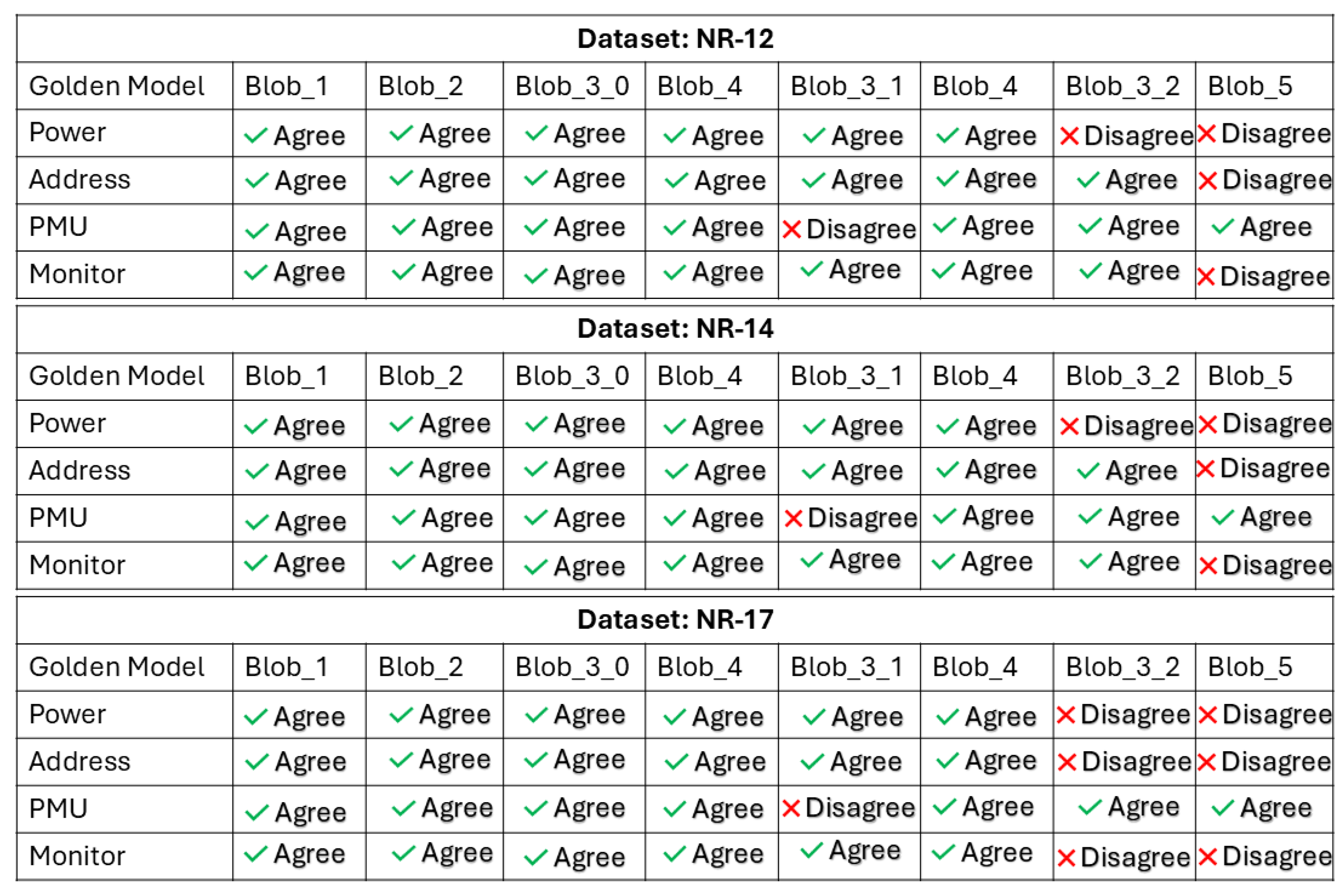
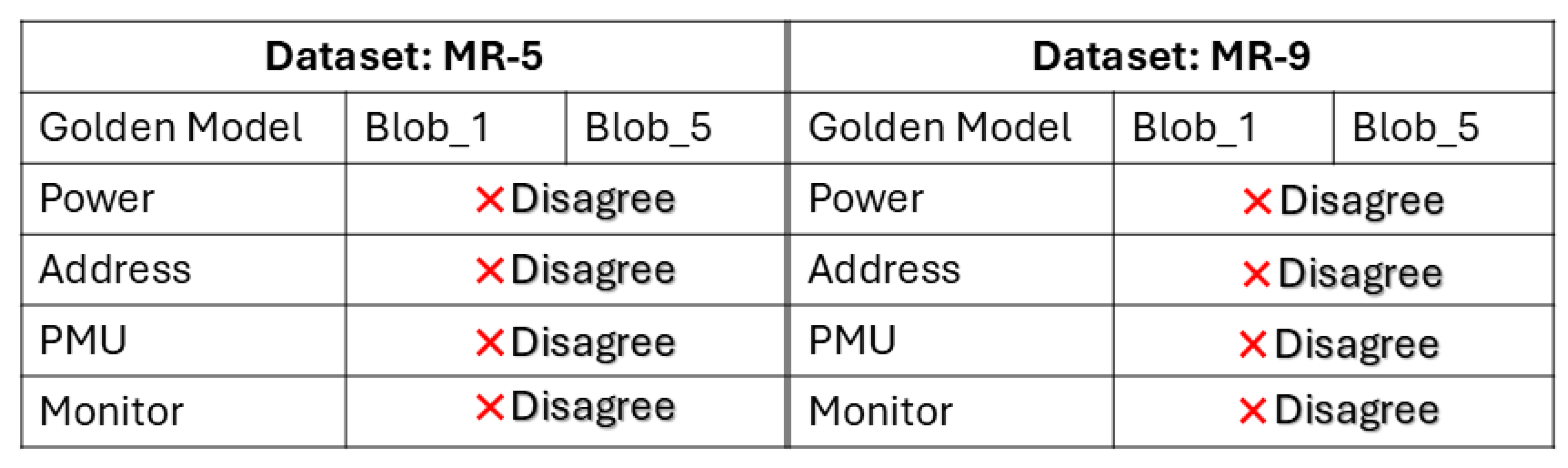
6.6. Monitor Blob Identification and Anomaly Detection
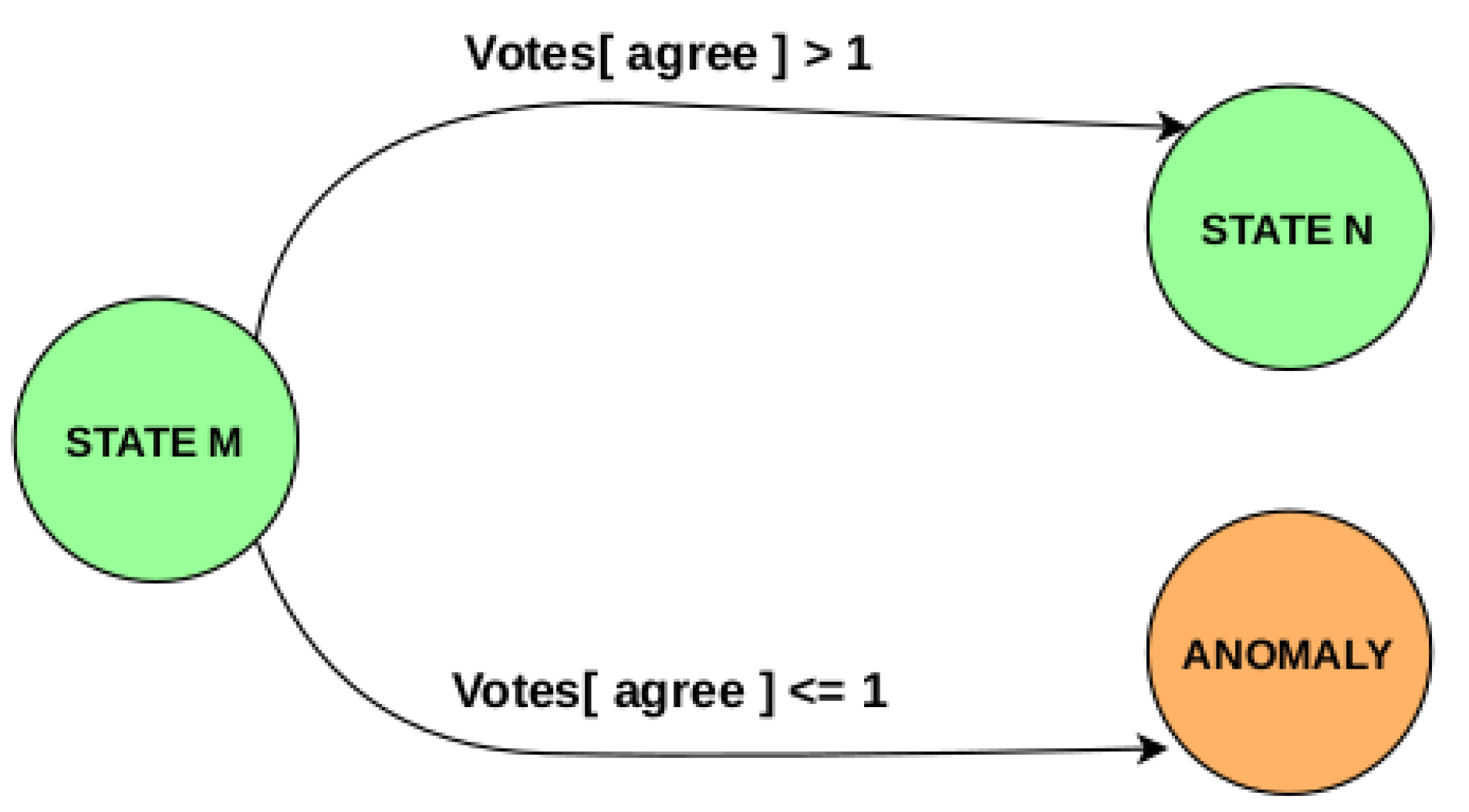
- At blob boundaries
- Along a path
7. Discussion
- The synchronization between streams becomes extremely challenging through this decomposition. In a real-time system, synchronization can be built in implicitly or explicitly despite its challenging nature. But in the decomposed system model, as in this work, explicit crutches in terms of timestamps and markers have to be created.
- Misaligned raw data has a huge impact on blob/path detection accuracy further highlighting need for good synchronization.
8. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Abbreviations
| PMU | Performance Monitoring Unit |
| CFI | Control Flow Integrity |
| LLC | Last Level Cache |
| DDR | Double Data Rate |
| FPGA | Field Programmable Gate Array |
| CFG | Control Flow Graph |
| BFG | Blob Flow Graph |
| LLVM | Low Level Virtual Machine |
| COTS | Commercial Off The Shelf |
| PL | Programmable Logic |
| CCI | Cache Coherence Interface |
| L1D | Level-1 Data Cache |
| L1I | Level-1 Instruction Cache |
| ML | Machine Learning |
| EM | Electromagnetic |
| PESI | Program Execution State Integrity |
| PCB | Printed Circuit Board |
| PCA | Principal Component Analysis |
| SCA | Side-Channel Attack |
References
- Wikipedia. Trusted Foundry Program. Available online: https://en.wikipedia.org/wiki/Trusted_Foundry_Program.
- Rajendran, J.; Sinanoglu, O.; Karri, R. Regaining Trust in VLSI Design: Design-for-Trust Techniques. Proceedings of the IEEE 2014, 102, 1266–1282. [Google Scholar] [CrossRef]
- Vaarandi, R.; Tsiopoulos, L.; Visky, G.; ur Rehman, M.; Bahsi, H. A Systematic Literature Review of Cyber Security Monitoring in Maritime. IEEE Access 2025, 13, 85307–85329. [Google Scholar] [CrossRef]
- Diana, L.; Dini, P.; Paolini, D. Overview on Intrusion Detection Systems for Computers Networking Security. Computers 2025, 14. [Google Scholar] [CrossRef]
- Park, J.; Xu, X.; Jin, Y.; Forte, D.; Tehranipoor, M. Power-based side-channel instruction-level disassembler. In Proceedings of the Proceedings of the 55th Annual Design Automation Conference, DAC ’18. New York, NY, USA, 2018. [Google Scholar] [CrossRef]
- Krishnankutty, D.; Li, Z.; Robucci, R.; Banerjee, N. Instruction Sequence Identification and Disassembly Using Power Supply Side-Channel Analysis. IEEE Transactions on Computers 2020, 69, 1639–1651. [Google Scholar] [CrossRef]
- Fendri, H.; Macchetti, M.; Perrine, J.; Stojilović, M. A deep-learning approach to side-channel based CPU disassembly at design time. In Proceedings of the Proceedings of the 2022 Conference & Exhibition on Design, Automation & Test in Europe, Leuven, BEL, 2022; DATE ’22, pp. 670–675. [Google Scholar]
- Glamočanin, O.; Shrivastava, S.; Yao, J.; Ardo, N.; Payer, M.; Stojilović, M. Instruction-Level Power Side-Channel Leakage Evaluation of Soft-Core CPUs on Shared FPGAs. In Proceedings of the Proceedings of the 32nd USENIX Security Symposium, 2023; pp. 2926–2944. [Google Scholar]
- Brisfors, M.; Moraitis, M.; Dubrova, E. Do Not Rely on Clock Randomization: A Side-Channel Attack on a Protected Hardware Implementation of AES. In Proceedings of the Foundations and Practice of Security: 15th International Symposium, FPS 2022, Ottawa, ON, Canada; Revised Selected Papers, Berlin, Heidelberg, December 12–14, 2022; pp. 38–53. [Google Scholar] [CrossRef]
- Uhsadel, L.; Georges, A.; Verbauwhede, I. Exploiting hardware performance counters. In Proceedings of the 2008 5th Workshop on Fault Diagnosis and Tolerance in Cryptography, 2008; IEEE; pp. 59–67. [Google Scholar]
- Biswas, A.; Li, Z.; Tyagi, A. Control Flow Integrity in IoT Devices with Performance Counters and DWT. In Proceedings of the 2020 IEEE International Symposium on Smart Electronic Systems (iSES) (Formerly iNiS), 2020; pp. 171–176. [Google Scholar] [CrossRef]
- Malone, C.; Zahran, M.; Karri, R. Are hardware performance counters a cost effective way for integrity checking of programs. In Proceedings of the Proceedings of the Sixth ACM Workshop on Scalable Trusted Computing, New York, NY, USA, 2011; STC ’11, pp. 71–76. [Google Scholar] [CrossRef]
- Xia, Y.; Liu, Y.; Chen, H.; Zang, B. CFIMon: Detecting violation of control flow integrity using performance counters. In Proceedings of the IEEE/IFIP International Conference on Dependable Systems and Networks (DSN 2012), 2012; pp. 1–12. [Google Scholar] [CrossRef]
- Kocher, P.C.; Jaffe, J.; Jun, B. Differential Power Analysis. In Proceedings of the Advances in Cryptology - CRYPTO ’99, 19th Annual International Cryptology Conference, Santa Barbara, California, USA; Proceedings, August 15-19, 1999; 1999; pp. 388–397. [Google Scholar] [CrossRef]
- Kocher, P.C. Timing Attacks on Implementations of Diffie-Hellman, RSA, DSS, and Other Systems. In Proceedings of the Advances in Cryptology — CRYPTO ’96; Berlin, Heidelberg, Koblitz, N., Ed.; 1996; pp. 104–113. [Google Scholar]
- Quisquater, J.J.; Samyde, D. Electromagnetic analysis (ema): Measures and counter-measures for smart cards. In Proceedings of the International Conference on Research in Smart Cards, 2001; Springer; pp. 200–210. [Google Scholar]
- Genkin, D.; Pipman, I.; Tromer, E. Get Your Hands Off My Laptop: Physical Side-Channel Key-Extraction Attacks on PCs. In Proceedings of the Cryptographic Hardware and Embedded Systems – CHES 2014; Berlin, Heidelberg, Batina, L., Robshaw, M., Eds.; 2014; pp. 242–260. [Google Scholar]
- Eisenbarth, T.; Paar, C.; Weghenkel, B. Building a side channel based disassembler. In Transactions on Computational Science X: Special Issue on Security in Computing, Part I; Springer-Verlag: Berlin, Heidelberg, 2010; pp. 78–99. [Google Scholar]
- Park, J.; Tyagi, A. Security Metrics for Power Based SCA Resistant Hardware Implementation. In Proceedings of the Proceedings of the 2016 29th International Conference on VLSI Design and 2016 15th International Conference on Embedded Systems (VLSID), USA, 2016; VLSID ’16, pp. 541–546. [Google Scholar] [CrossRef]
- Park, J.; Tyagi, A. Using Power Clues to Hack IoT Devices: The power side channel provides for instruction-level disassembly. IEEE Consumer Electronics Magazine 2017, 6, 92–102. [Google Scholar] [CrossRef]
- Robins, A.; Olguin, S.; Brown, J.; Carper, C.; Borowczak, M. Power-Based Side-Channel Attacks on Program Control Flow with Machine Learning Models. Journal of Cybersecurity and Privacy 2023, 3, 351–363. [Google Scholar] [CrossRef]
- Han, Y.; Chan, M.; Aref, Z.; Tippenhauer, N.O.; Zonouz, S. Hiding in Plain Sight? On the Efficacy of Power Side Channel-Based Control Flow Monitoring. In Proceedings of the 31st USENIX Security Symposium (USENIX Security 22), Boston, MA, 2022; pp. 661–678. [Google Scholar]
- Vaidyan, V.M.; Tyagi, A. Instruction Level Disassembly through Electromagnetic Side-Chanel: Machine Learning Classification Approach with Reduced Combinatorial Complexity. In Proceedings of the Proceedings of the 2020 3rd International Conference on Signal Processing and Machine Learning, New York, NY, USA, 2020; SPML ’20, pp. 124–130. [Google Scholar] [CrossRef]
- Arguello, C.N.; Searle, H.; Rampazzi, S.; Butler, K.R.B. A Practical Methodology for ML-Based EM Side Channel Disassemblers. arXiv 2022, arXiv:2206.10746. [Google Scholar] [CrossRef]
- Maillard, J.; Hiscock, T.; Lecomte, M.; Clavier, C. Towards Fine-grained Side-Channel Instruction Disassembly on a System-on-Chip. In Proceedings of the 2022 25th Euromicro Conference on Digital System Design (DSD), 2022; pp. 472–479. [Google Scholar] [CrossRef]
- van Geest, J.; Buhan, I. A Side-Channel Based Disassembler for the ARM-Cortex M0. In Proceedings of the Applied Cryptography and Network Security Workshops: ACNS 2022 Satellite Workshops, AIBlock, AIHWS, AIoTS, CIMSS, Cloud S&P, SCI, SecMT, SiMLA, Rome, Italy; Proceedings, Berlin, Heidelberg, June 20–23, 2022; pp. 183–199. [Google Scholar] [CrossRef]
- Iyer, V.V.; Thimmaiah, A.; Orshansky, M.; Gerstlauer, A.; Yilmaz, A.E. A Hierarchical Classification Method for High-accuracy Instruction Disassembly with Near-field EM Measurements. ACM Trans. Embed. Comput. Syst. 2024, 23. [Google Scholar] [CrossRef]
- Callan, R.; Behrang, F.; Zajic, A.; Prvulovic, M.; Orso, A. Zero-overhead profiling via EM emanations. In Proceedings of the Proceedings of the 25th International Symposium on Software Testing and Analysis, New York, NY, USA, 2016; ISSTA 2016, pp. 401–412. [Google Scholar] [CrossRef]
- Sayakkara, A.; Le-Khac, N.A.; Scanlon, M. A survey of electromagnetic side-channel attacks and discussion on their case-progressing potential for digital forensics. Digit. Investig. 2019, 29, 43–54. [Google Scholar] [CrossRef]
- Han, Y.; Christoudis, I.; Diamantaras, K.I.; Zonouz, S.; Petropulu, A. Side-Channel-Based Code-Execution Monitoring Systems: A Survey. IEEE Signal Processing Magazine 2019, 36, 22–35. [Google Scholar] [CrossRef]
- Aho, A.V.; Lam, M.S.; Sethi, R.; Ullman, J.D. Compilers: Principles, Techniques, and Tools (2nd Edition); Addison-Wesley Longman Publishing Co., Inc.: USA, 2006. [Google Scholar]
- Mahlke, S.; Lin, D.; Chen, W.; Hank, R.; Bringmann, R. Effective Compiler Support For Predicated Execution Using The Hyperblock. In Proceedings of the [1992] Proceedings the 25th Annual International Symposium on Microarchitecture MICRO 25, 1992; pp. 45–54. [Google Scholar] [CrossRef]
- Fisher, J.A. Trace Scheduling: A Technique for Global Microcode Compaction. IEEE Transactions on Computers 1981, C-30, 478–490. [Google Scholar] [CrossRef]
- Lokuciejewski, P.; Kelter, T.; Marwedel, P. Superblock-Based Source Code Optimizations for WCET Reduction. In Proceedings of the Proceedings of the 2010 10th IEEE International Conference on Computer and Information Technology, USA, 2010; CIT ’10, pp. 1918–1925. [Google Scholar] [CrossRef]
- Zhang, Y. Cache Side Channels: State of the Art and Research Opportunities. In Proceedings of the Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, New York, NY, USA, 2017; CCS ’17, pp. 2617–2619. [Google Scholar] [CrossRef]
- Aldaya, A.C.; Brumley, B.B.; ul Hassan, S.; Pereida García, C.; Tuveri, N. Port Contention for Fun and Profit. In Proceedings of the 2019 IEEE Symposium on Security and Privacy (SP), 2019; pp. 870–887. [Google Scholar] [CrossRef]
- Rokicki, T.; Maurice, C.; Botvinnik, M.; Oren, Y. Port Contention Goes Portable: Port Contention Side Channels in Web Browsers. In Proceedings of the Proceedings of the 2022 ACM on Asia Conference on Computer and Communications Security, New York, NY, USA, 2022; ASIA CCS ’22, pp. 1182–1194. [Google Scholar] [CrossRef]
- Li, X.; Tyagi, A. Multi-Line Prefetch Covert Channel with Huge Pages. Cryptography 2025, 9. [Google Scholar] [CrossRef]
- LLVM. The LLVM Compiler Infrastructure. Available online: https://llvm.org/.
- Gem5. Gem5: The Gem5 Simulator System. Available online: https://www.gem5.org/.
- Binkert, N.; Beckmann, B.; Black, G.; Reinhardt, S.K.; Saidi, A.; Basu, A.; Hestness, J.; Hower, D.R.; Krishna, T.; Sardashti, S.; et al. The gem5 simulator. SIGARCH Comput. Archit. News 2011, 39, 1–7. [Google Scholar] [CrossRef]
- Sharir, M. A strong-connectivity algorithm and its applications in data flow analysis. Computers & Mathematics with Applications 1981, 7, 67–72. [Google Scholar] [CrossRef]
- Xilinx. Xilinx ZCU 106 Evaluation Board User Guide. 23 October 2019, UG1244. Available online: https://www.xilinx.com/support/documentation/boards_and_kits/zcu106/ug1244-zcu106-eval-bd.pdf.
- ARM. Arm Cortex-A53 MPCore Processor Technical Reference Manual. Available online: https://developer.arm.com/documentation/ddi0500/latest/.
- McCalpin, J. STREAM Benchmark Git. Available online: https://www.cs.virginia.edu/stream/.
- Hammond, J. STREAM: Sustainable Memory Bandwidth in High Performance Computers. Available online: https://github.com/jeffhammond/STREAM.
| 1 | Note that this methodology fits in well with the plans of LLVM [39] to provide CFG information along with assembly program for the purpose of link-time assembly code optimizations. |
| 2 | Although the memory-access stream is directly collected on-chip, L2 misses are visible off-chip via the DDR bus. |
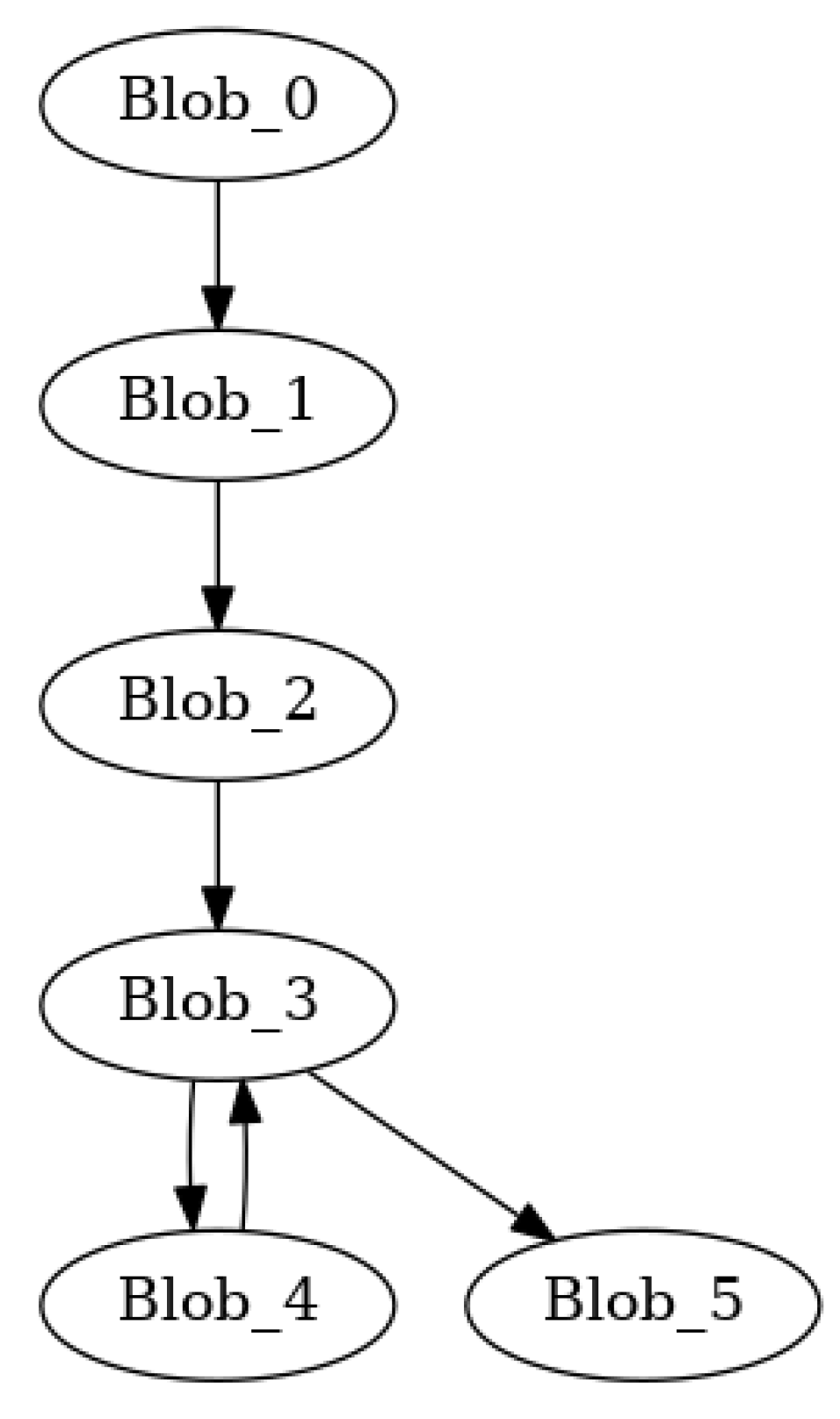
| blob | count | Dynamic Instructions | Inst. Before | Inst. After | |||
|---|---|---|---|---|---|---|---|
| mean | min | max | Miss (mean) | Exit (mean) | |||
| 0 | Blob_0 | 1 | 14241 | 14241 | 14241 | 0 | 11 |
| 1 | Blob_1 | 1 | 260400425 | 260400425 | 260400425 | 11 | 343634 |
| 2 | Blob_2 | 1 | 170002890 | 170002890 | 170002890 | 343634 | 6 |
| 3 | Blob_3 | 3 | 400284005 | 31757 | 600410146 | 102497 | 273254 |
| 4 | Blob_4 | 2 | 240153748 | 240000020 | 240307477 | 409879 | 153742 |
| 5 | Blob_5 | 1 | 740003339 | 740003339 | 740003339 | 5 | 0 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




