Submitted:
03 December 2025
Posted:
04 December 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
- What are the main multi-tenancy security threats in IoT-Cloud systems?
- What mitigation techniques have been proposed, and how do they perform?
- Which emerging technologies show promise for enabling secure, scalable, and future-proof multi-tenant IoT-cloud deployments?
2. Architecture Foundations of IoT-Cloud Integration
2.1. Internet of Things and Cloud Integration
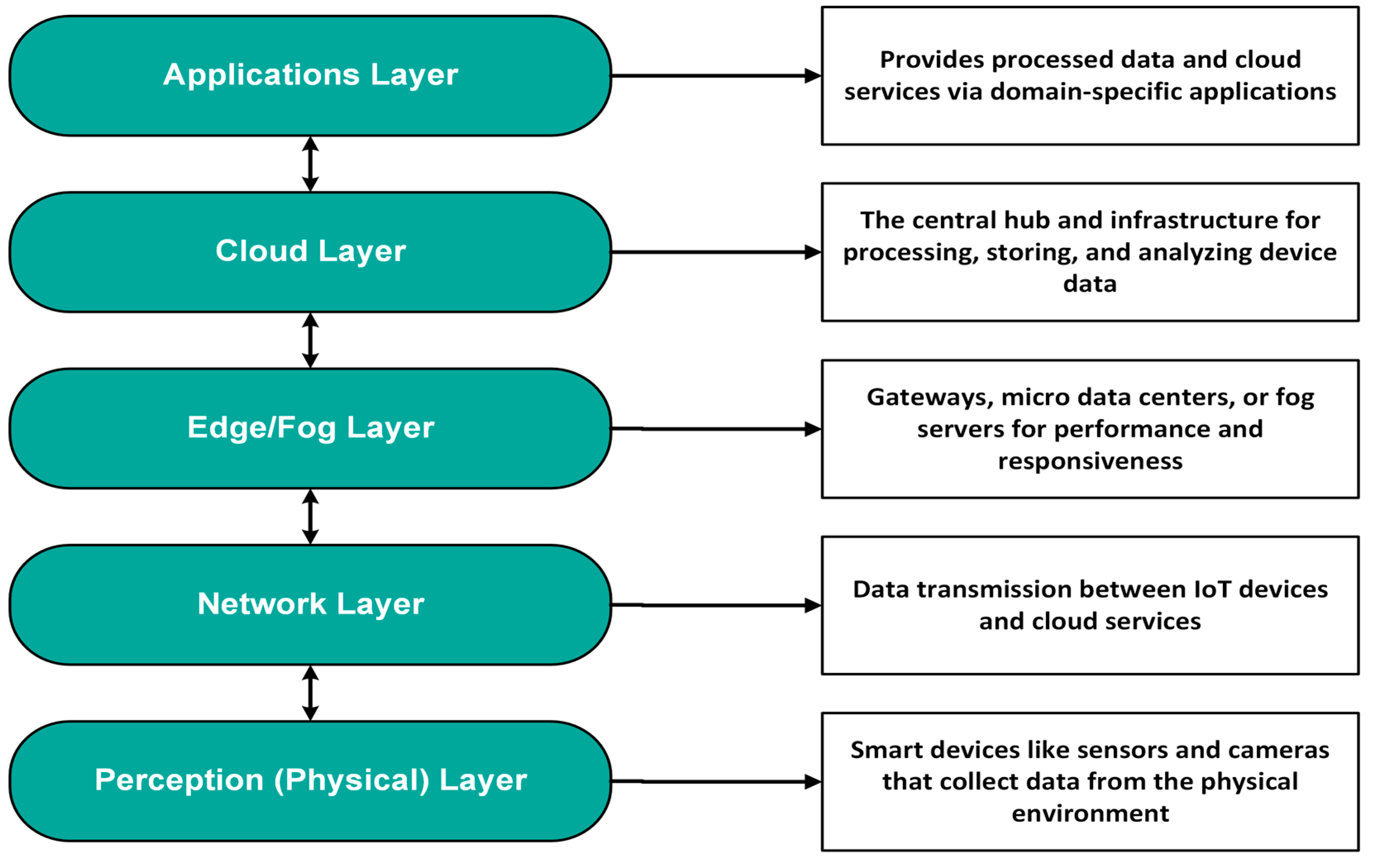
2.2. IoT-Cloud Systems Architecture
2.2.1. Perception (Physical) Layer
2.2.2. Network Layer
2.2.3. Edge/Fog Layer
2.2.4. Cloud Layer
2.2.4.1. Cloud System Components
- Compute Resources: Contemporary cloud infrastructures utilize a wide variety of computing resources to supply the processing power needed for modern applications and services. These core elements include virtualized servers like Amazon Elastic Compute Cloud (Amazon EC2) that operate independently on physical hardware; containers, offering lightweight and efficient virtualization at the OS level; and serverless computing, also known as Function as a Service (FaaS), that enables cost-effective, highly scalable applications without infrastructure management worries [13,14]. The combination of these paradigms has resulted in innovative solutions like serverless containers, such as AWS Fargate and the SCAR framework, which build on microservice architectures to make managing complex applications easier for users without system-level expertise [15,16]. However, the growing adoption of container-based virtualization has highlighted significant challenges in maintaining adequate isolation and security. This has led to the active development of innovative container runtimes and specialized security solutions aimed at mitigating these risks [13].
- Storage: Cloud storage solutions are fundamental to IoT architectures, as they must ingest and persistently store massive volumes of data at varying velocities and varieties. These solutions can be generally classified into three categories: object storage, including Amazon S3 and Azure Blob Storage, which are highly scalable and cost-efficient for unstructured data such as images, videos, and log files; block storage, providing high-performance virtual disks (volumes) for computing instances; and file storage, intended for shared access [17].
- Networking: Cloud networking components are integral to managing communication between cloud resources and external networks, enabling data ingress from IoT gateways. Key components include Virtual Private Clouds (VPCs), a fundamental aspect of this architecture that provides logically isolated virtual networks within a public cloud infrastructure [18]. Moreover, load balancers evenly allocate incoming traffic among multiple virtual machine instances to ensure high availability, reliability, and optimal performance, preventing the overloading or underutilization of networking nodes [19]. Content Delivery Networks (CDNs) mitigate latency by distributing content across geographically dispersed edge locations. Furthermore, these CDNs may be virtualized by utilizing cloud infrastructure, employing shared virtual machines within an Infrastructure as a Service (IaaS) model. This approach delivers tailored content-delivery services that dynamically scale resources to accommodate evolving demands while maintaining compliance with service-level agreements [20].
- Management and Monitoring: Cloud resource management and security rely on three primary categories of tools and services: monitoring, management, and automation. Monitoring tools such as Azure Monitor, Google Cloud Operations Suite, and AWS CloudWatch enable ongoing tracking of resource usage, system performance, and operational health. Management tools enable system administrators to efficiently provision, configure, and monitor cloud resources, often including features for policy enforcement and lifecycle management. Automation tools, including Azure Resource Manager, facilitate the deployment, scaling, and orchestration of resources via predefined templates and scripts. Collectively, these tools establish the technological foundation for advancing next-generation internet applications, expanding smart infrastructure markets, and optimizing business operations within cloud computing ecosystems [21].
- Cloud Security: Ensuring robust security is a paramount concern in cloud computing, necessitating a multifaceted approach to safeguard sensitive data and applications. At a fundamental level, security is established through both contractual agreements and technical controls. Service Level Agreements (SLAs) function as formal contracts to align data protection expectations between users and cloud service providers. Simultaneously, it is imperative to establish robust technical protections for data storage, transmission, and authorization [22]. These strategies usually involve encrypting data at rest and in transit, implementing protected authentication methods, enforcing strict access controls, employing data loss prevention techniques, and conducting regular security audits to ensure confidentiality, integrity, and availability [23].
2.2.4.2. Cloud Service Models
2.2.4.3. Cloud Deployment Models
2.2.5. Application Layer
- Access Control Attack: Access control prevents unauthorized users from accessing IoT data, ensuring it remains restricted to legitimate users. However, if that access is compromised, the entire IoT system is at risk.
- Malicious Code Injection Attacks: An attacker injects malicious code or scripts from an unknown source into the system, hacking authorized user data and stealing or manipulating important user information.
- Sniffing Attacks: An attacker can monitor network traffic using sniffer applications, which can reveal confidential user data.
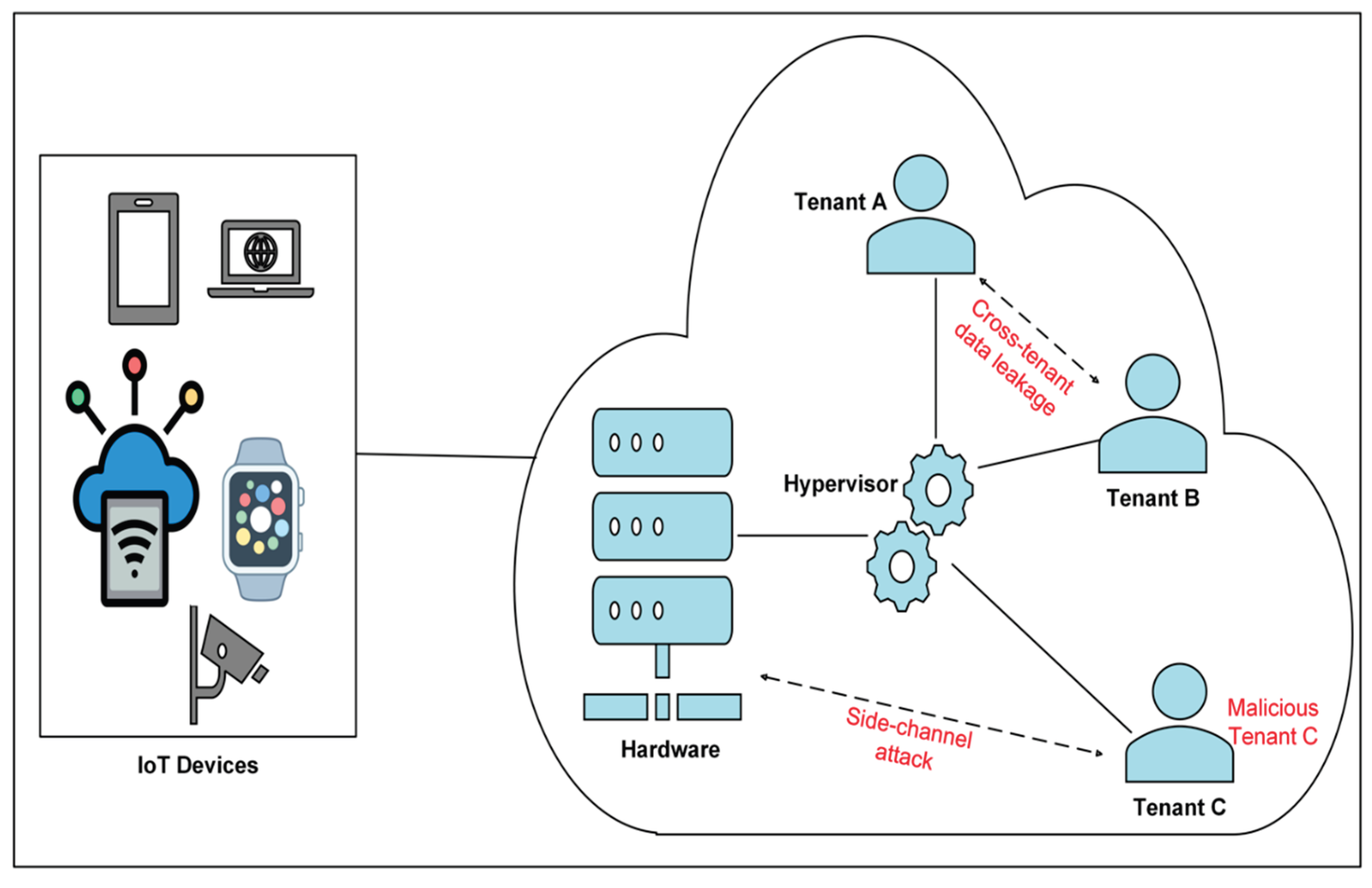
2.3. Multi-Tenancy Cloud Systems
- Single Database: Each tenant has a dedicated application and database instance.
- Shared Database, Isolated Schema: A single database instance is utilized; however, each tenant maintains a separate schema.
- Shared Database, Shared Schema: All tenants utilize the same database schema, with mechanisms implemented to distinguish their data.
2.3.1. Mechanisms of Tenant Isolation
2.3.1.1. Device and Connectivity Isolation
2.3.1.2. Network Isolation
- Physical Isolation
- 2.
- Logical Isolation
- Virtual LANs (VLANs) are logical clusters of network devices separated from devices on other VLANs, regardless of shared physical infrastructure. Each tenant is assigned a unique VLAN, providing network traffic isolation. VLANs are scalable, adaptable, and economical, although managing them becomes more complex as the tenant count grows.
- Virtual Private Networks (VPNs): A VPN establishes a secure, encrypted tunnel for a tenant’s data transmission over a shared network. Each tenant is allocated a distinct private virtual network within the shared infrastructure, ensuring all traffic is encrypted and isolated from other tenants. This mechanism offers robust security and privacy for tenant communications; however, it may also introduce latency and pose scalability challenges if not properly managed.
- Software-Defined Networking (SDN) facilitates dynamic and programmable control of network traffic. Through the utilization of SDN, tenants are able to isolate their network traffic via software configurations that establish virtualized networks on a shared physical infrastructure. SDN is characterized by its high flexibility and scalability; however, it necessitates sophisticated software-defined network infrastructure and management.
- Network policies and micro-segmentation: Micro-segmentation is a network security strategy that partitions a network into discrete, isolated segments. This methodology facilitates the granular isolation of tenants’ networks and applications by enforcing policies engineered to govern traffic flow and mandate separation. Implementation is commonly achieved via technologies such as network firewalls, access control lists (ACLs), and policy-driven routing. While this approach affords highly fine-grained control over network access, it introduces significant management complexity, particularly within large-scale, multi-tenant architectures [36].
2.3.1.3. Resource Isolation
2.3.1.4. Data Isolation
2.3.1.5. Application Isolation
2.3.1.6. Management and Governance Isolation
3. Critical Analysis of Multi-Tenancy Security
3.1. Classification of Multi-Tenancy Security Risks
3.2. Existing Mitigation Techniques
4. Discussion
4.1. Fragmentation of Security Architectures
4.2. The Security-Performance Trade-Off
4.3. Lack of Dynamic Adaptability
4.4. Long-Term Cryptographic Vulnerabilities
5. Emerging Trends and Future Directions
5.1. Zero Trust Architectures (ZTA)
5.2. AI-Driven Threat Detection
5.3. Blockchain Integration
5.4. Lightweight Post-Quantum Cryptography (PQC)
| Emerging Solution | Core Function | Primary Multi-Tenancy Benefit | Key IoT Implementation Challenge |
|---|---|---|---|
| Zero Trust Architecture (ZTA) | Continuous Authentication & Authorization | Granular Access Control, Minimized "Blast Radius" of Tenant Compromise | Lack of Visibility, Overhead of Continuous Monitoring, Legacy System Integration |
| Blockchain | Decentralized & Immutable Ledger | Tamper-Proof Audit Trails, Non-Repudiation for Compliance and Forensics | Scalability, High Latency/Throughput, Computational Cost of Consensus |
| Post-Quantum Cryptography (PQC) | Quantum-Resistant Encryption | Future-Proofing Long-Term Data Confidentiality and Integrity | Increased Memory/Processing Footprint, Resistance to Side-Channel Attacks |
| Adaptive AI Security | Real-Time Anomaly Detection and Intrusion Prevention | Proactive, Automated Threat Identification and Mitigation | Vulnerability to Adversarial Attacks (Poisoning, Evasion), High Computational Demand |
6. Conclusion
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Abbreviations
| IoT | Internet of Things | MQTT | Message Queuing Telemetry Transport |
| PQC | Post-Quantum Cryptography | SaaS | Software as a Service |
| ZTA | Zero Trust Architectures | IaaS | Infrastructure as a Service |
| CoAP | Constrained Application Protocol | AMQP | Advanced Message Queuing Protocol |
| LPWANs | Low-Power Wide Area Networks | ACLs | Access Control Lists |
| SSL | Secure Sockets Layer | Amazon EC2 | Amazon Elastic Compute Cloud |
| RBAC | Role-Based Access Control | PaaS | Platform as a Service |
| VM | virtual machine | SDN | Software-Defined Networking |
| QoS | Quality of Service | VPN | Virtual Private Networks |
| VPCs | Virtual Private Clouds | VLAN | Virtual Local Area Network |
| ABAC | Attribute-Based Access Control | DoS | Denial-of-Service |
| APIs | Application Programming Interfaces | SCA | side-channel attacks |
References
- Zoting, S.S.; Aditi. Multi-Tenant Data Centers Market Size, Share and Trends 2025 to 2034. 2025. Available online: https://www.precedenceresearch.com/multi-tenant-data-centers-market.
- Hashim, W.; Hussein, N.A.-H.K. Securing Cloud Computing Environments: An Analysis of Multi-Tenancy Vulnerabilities and Countermeasures . SHIFRA. 2024. [Google Scholar]
- Surianarayanan, C.; Chelliah, P.R. Integration of the Internet of Things and Cloud: Security Challenges and Solutions – A Review. International Journal of Cloud Applications and Computing (IJCAC) 2023, 13. [Google Scholar] [CrossRef]
- Almutairi, M. IoT–Cloud Integration Security: A Survey of Challenges, Solutions, and Directions. Electronics 2025, 14, 1394. [Google Scholar] [CrossRef]
- Kuchuk, H.; Malokhvii, E. INTEGRATION OF IOT WITH CLOUD, FOG, AND EDGE COMPUTING: A REVIEW. Advanced Information Systems 2024, 8. [Google Scholar] [CrossRef]
- Botta, A. Integration of Cloud computing and Internet of Things: A survey. Future Generation Computer Systems 2016, 56. [Google Scholar] [CrossRef]
- Gubbi, J. Internet of Things (IoT): A vision, architectural elements, and future directions. Future Generation Computer Systems 2013, 29. [Google Scholar] [CrossRef]
- Mrabet, H. A Survey of IoT Security Based on a Layered Architecture of Sensing and Data Analysis. Sensors 2020, 20, 3625. [Google Scholar] [CrossRef]
- Bello, O.; Zeadally, S.; Badra, M. Network layer inter-operation of Device-to-Device communication technologies in Internet of Things (IoT). Ad Hoc Networks 2017, 57. [Google Scholar] [CrossRef]
- Sharif. B.H.W.E.M.S., The Internet of Things Security Issues and Countermeasures in Network Layer: A Systematic Literature Review. 2022 International Conference on Data Analytics for Business and Industry (ICDABI), 2022.
- Dallaf, A.A.A. Edge Computing in IoT Networks: Enhancing Efficiency, Reducing Latency, and Improving Scalability. International Journal of Advanced Network, Monitoring and Controls 2025, 10. [Google Scholar] [CrossRef]
- Sarwar, K. Efficient privacy-preserving data replication in fog-enabled IoT. Future Generation Computer Systems 2022, 128. [Google Scholar] [CrossRef]
- Mavridis, I.; Karatza, H. Orchestrated sandboxed containers, unikernels, and virtual machines for isolation-enhanced multitenant workloads and serverless computing in cloud. In Concurrency and Computation: Practice and Experience; 2023; Volume 35. [Google Scholar]
- Emeakaroha, T. L.P.R.A.L.V., A Preliminary Review of Enterprise Serverless Cloud Computing (Function-as-a-Service) Platforms. 2017 IEEE International Conference on Cloud Computing Technology and Science (CloudCom), 2017.
- Jain, P. Performance Analysis of Various Server Hosting Techniques. Procedia Computer Science 2020, 173. [Google Scholar] [CrossRef]
- Toader. E.v.E.J.G.S.E.A.B.L.V.L., The SPEC-RG Reference Architecture for FaaS: From Microservices and Containers to Serverless Platforms. IEEE Internet Computing 2019, 23. [Google Scholar]
- Armoogum, S.; Khonje, P. Healthcare Data Storage Options Using Cloud. Internet of Things.
- Hu, Z. FDRA: Fully Distributed Routing Architecture for Private Virtual Netwo. Parallel Architectures, Algorithms and Programming . 2021. [Google Scholar]
- Moharana, S.S.; Ramesh, R.D.; Powar, D. Analysis of load balancers in cloud computing. International Journal of Computer Science and Engineering 2013, 2, 101–108. [Google Scholar]
- Um, T.-W. Dynamic Resource Allocation and Scheduling for Cloud-Based Virtual Content Delivery Networks. ETRI Journal 2014, 36. [Google Scholar] [CrossRef]
- Facca, T.Z.A.P.F.A.J.G.F.L.F. FIWARE Lab: Managing Resources and Services in a Cloud Federation Supporting Future Internet Applications. 2014 IEEE/ACM 7th International Conference on Utility and Cloud Computing, 2014.
- Zeng, X.Z.H.-t.D.J.-q.C.Y.L.L.-j. Ensure Data Security in Cloud Storage. 2011 International Conference on Network Computing and Information Security, 2011 .
- Waghchaude, K. A Review on Cloud Computing Security Issues, Applicable Solutions and Implementation. Int. J. Sci. Res. Eng. Manag 2024, 8, 1–3. [Google Scholar] [CrossRef]
- Sood, S.K. A combined approach to ensure data security in cloud computing. Journal of Network and Computer Applications 2012, 35. [Google Scholar] [CrossRef]
- Pal, S. A New Trusted and Collaborative Agent Based Approach for Ensuring Cloud Security 2011.
- Joel Gibson, R.R.; Eveleigh, Darren; Tan, Qing. Benefits and challenges of three cloud computing service models. 2012 Fourth International Conference on Computational Aspects of Social Networks (CASoN), 2021.
- Lagana, C.D.N.A.F.G.F.A.G.A.G.D. IoT-HC: A Novel IoT Architecture for the Hybrid Cloud. 2019 28th International Conference on Computer Communication and Networks (ICCCN), 2019.
- Muneer Bani Yassein, M.Q.S.; Al-zoubi, Dua'. Application layer protocols for the Internet of Things: A survey. 2016 International Conference on Engineering & MIS (ICEMIS), 2016.
- Elmedany, S.A.W. Security threats of application programming interface (API's) in internet of things (IoT) communications 2021.
- Jannatul Ferdows, S.T.M.; Delowar Hossain, A.S.M.; Abdullah Al Mamun Shamim, G.M. Rasiqul Islam Rasiq, A Comprehensive Study of IoT Application Layer Security Management. 2020 IEEE International Conference for Innovation in Technology (INOCON), 2020.
- Kaur, K. Frontiers | Unveiling the core of IoT: comprehensive review on data security challenges and mitigation strategies. Frontiers in Computer Science 2024, 6. [Google Scholar] [CrossRef]
- Khan, Y. Architectural Threats to Security and Privacy: A Challenge for Internet of Things (IoT) Applications. Electronics 2023, 12, 88. [Google Scholar] [CrossRef]
- Banerjee, S.; Parisa, S.K. Secure Multi-Tenancy in Cloud Computing: Challenges and Solutions 2025, Vol. 17(No. 17), TRIoT.
- Sharma, R.K. Multi-Tenant Architectures in Modern Cloud Computing: A Technical Deep Dive. International Journal of Scientific Research in Computer Science, Engineering and Information Technology 2025, 11. [Google Scholar] [CrossRef]
- Njeguš, A. Intelligent Software Systems for Multi-Tenant Cloud Environments: Challenges and Solutions. Sinteza 2025 - International Scientific Conference on Information Technology, Computer Science, and Data Science, 2025 .
- Paktiti, M. Tenant isolation in multi-tenant systems: What you need to know. 2025. Available online: https://workos.com/blog/tenant-isolation-in-multi-tenant-systems.
- Factor, M. Secure Logical Isolation for Multi-tenancy in cloud storage. IEEE Conference on Mass Storage Systems and Technologies, 2013.
- T.B., M. Enhancing Data Security under Multi-Tenancy within Open Stack. International Journal of Advanced Trends in Computer Science and Engineering 2020. [Google Scholar]
- 39. Kumar, R., Multi-Tenant SaaS Architectures: Design Principles and Security Considerations. Journal of Software Engineering and Simulation 2020, 6, 28–41. [CrossRef]
- Panguraj, A.R.R. Systematic Approach to Security Testing in Multi-Tenant Cloud Systems. International Journal of Multidisciplinary Research and Growth Evaluation 2025, 6. [Google Scholar] [CrossRef]
- Saxena, D. An AI-Driven VM Threat Prediction Model for Multi-Risks Analysis-Based Cloud Cybersecurity, 2023.
- Yadav, S. Enhancing Security in Multi-Tenant Cloud Environments: Threat Detection, Prevention, and Data Breach Mitigation. Journal of Information Systems Engineering and Management 2025, 10. [Google Scholar] [CrossRef]
- Pandit, A.; Pandit, R. Side-Channel Attacks in Multi-Tenant Cloud Environments: Prevention & Mitigation. International Journal of Innovations in Science, Engineering And Management 2025. [Google Scholar]
- Ghorbani, E.C.P.N.S.D.A.A. Collaborative DDoS Detection in Distributed Multi-Tenant IoT using Federated Learning. 2022 19th Annual International Conference on Privacy, Security & Trust (PST), 2022 . 2022.
- Malikireddy, S.K.R. Securing Multi-Tenant Cloud Environments with Graph-Based Models 2024.
- Hariharan, R. Zero Trust Security in Multi-Tenant Cloud Environments. Journal of Information Systems Engineering and Management 2025, 10. [Google Scholar] [CrossRef]
- Sebestyen, H. A Literature Review on Security in the Internet of Things: Identifying and Analysing Critical Categories. Computers 2025, 14, 61. [Google Scholar] [CrossRef]
- Dauda, A. A Survey on IoT Application Architectures. Sensors 2024, 24. [Google Scholar] [CrossRef]
- Kyriakidou, C.D.P.; Pittaras, A.M.; Fotiou, I.; Thomas, N.; Y. Polyzos, G. Attribute-Based Access Control Utilizing Verifiable Credentials for Multi-Tenant IoT Systems. 2024 IEEE 4th International Conference on Electronic Communications, Internet of Things and Big Data (ICEIB). 2024; Volume 800. [Google Scholar]
- Awasthi, A. Quantum-Resistant Security for IoT Systems Challenges and Implementation Strategies. International Journal of Scientific Research in Computer Science, Engineering and Information Technology 2025. Available online: https://independent.academia.edu/AmitAwasthi46.
- Mahdi, L.H.; Abdullah, A. A. Fortifying Future IoT Security: A Comprehensive Review on Lightweight Post-Quantum Cryptography. Engineering, Technology & Applied Science Research 2025, 15, 21812–21821. [Google Scholar]
- Oladimeji, G. A Critical Analysis of Foundations, Challenges and Directions for Zero Trust Security in Cloud Environments 2024.
- Peng, Y. An Improved Co-Resident Attack Defense Strategy Based on Multi-Level Tenant Classification in Public Cloud Platforms. Electronics 2024, 13, 3273. [Google Scholar] [CrossRef]
| Author(s) | Focus / Approach | Key Contribution | Remarks |
|---|---|---|---|
| Hashim et al., 2024 [2] | Tenant isolation & access control | Enhanced encryption reduced attacks ~5% | 12% overhead; limited scalability |
| Surianarayanan et al., 2023 [3] | Data confidentiality | Exposed leakage risks in shared setups | No mitigation modeling |
| Panguraj et al., 2025 [40] | Resource sharing | Identified inter-tenant leakage paths | No integrated isolation model |
| Kumar et al., 2020[39] | VM isolation | Simulated weak boundaries | Lacked IoT performance context |
| Kyriakidou et al., 2024 [41] | ABAC + Verifiable credentials | Tenant-level privacy authentication | Added computation overhead |
| Yadav et al., 2025 [42] | Zero Trust analytics | Continuous access validation | Not tested at scale |
| Pandit et al., 2025 [43] | AI anomaly detection | 97.3% accuracy for tenant attacks | Training bias; scalability issue |
| Neto et al., 2022 [44] | Federated DDoS detection | 84.2% accuracy; privacy preserved | Energy overhead |
| Almutairi et al., 2025 [4] | AI & PQC survey | Highlighted framework gaps | No unified integration |
| Malikireddy et al., 2024 [45] | Elasticity testing | Found inadequate dynamic security | No adaptive model proposed |
| Hariharan et al., 2025 [46] | Zero Trust | Continuous verification model | Conceptual; no IoT validation |
| Sebestyen et al., 2025 [47] | Blockchain audit | Immutable audit trails | Scalability constraints |
| Aspect | Previous Works | This Review |
|---|---|---|
| Scope | Prior studies analyzed IoT or cloud security separately, lacking focus on shared tenancy [2] [40]. | Provides an integrated review of IoT-Cloud multi-tenancy security. |
| Target Environment | Most works addressed single-tenant or hybrid edge models [39] [49]. | Focuses on multi-tenant resource sharing and isolation. |
| Depth of Threat Analysis | Broader surveys covered generic cloud threats with limited tenant-specific risks [4] [3]. | Categorizes tenant-level threats: data leakage, privilege escalation, and cross-VM attacks. |
| Mitigation Techniques | Emphasized traditional encryption and access control [42] [45]. | Introduces adaptive models integrating ZTA, AI-driven detection, blockchain, and PQC. |
| Evaluation Focus | Prior work offered qualitative insights only [44] [43]. | Provides comparative evaluation based on scalability, latency, and isolation effectiveness. |
| Gap Analysis | Often lacked systematic categorization [46]. | Delivers structured taxonomy of unresolved issues and testable metrics. |
| Post-Quantum Readiness | PQC rarely examined [2] [51]. | Positions PQC as a critical enabler for quantum-resilient multi-tenant communication. |
| Contribution Type | Mostly descriptive surveys [4] [3]. | Provides comparative synthesis and a roadmap for future research directions. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




