Submitted:
30 October 2025
Posted:
30 October 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Materials and Methods
2.1. Research Design
2.2. Participants and Sampling
2.3. Data Collection
- “How serious are cybersecurity threats in your current healthcare setting?”;
- “What barriers do you encounter when enforcing security policies among non-technical staff?”;
- “How confident are you in the effectiveness of your organization’s security training or compliance programs?”.
2.4. Data Analysis
- Data familiarization;
- Initial coding;
- Preliminary theme identification;
- Theme review and refinement;
- Final theme naming;
- Theme integration into reporting.
- Member checking: Participants reviewed their transcripts for accuracy [10];
- Triangulation: Themes were compared with practitioner reports and relevant literature;
- Reflexivity: The researcher kept a journal to note assumptions, decisions, and insights.
2.5. Ethical Considerations
3. Results
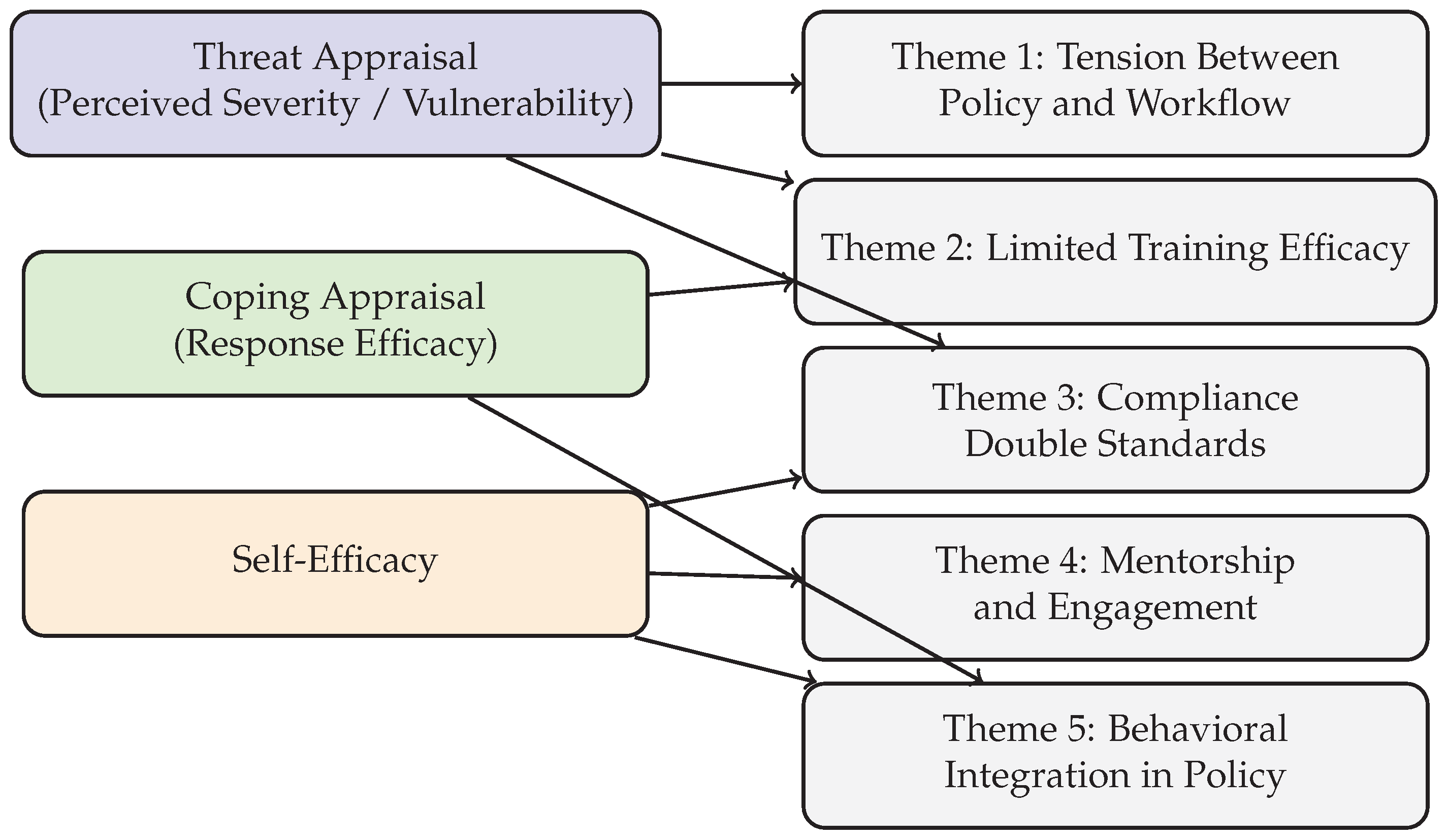
3.1. Tension Between Security Policies and Clinical Workflows
3.2. Limited Efficacy of Generic Training
- “Annual training feels like a checkbox. People click through slides without reading. It doesn’t stick.” — P9, Senior Cybersecurity Engineer;
- “We started using phishing simulations. That gets attention. When someone clicks, they’re more receptive to real conversations.” — P2, Director of Information Security.
3.3. Organizational Culture and Compliance Double Standards
- “When management ignores policies or overrides them, others notice. It sets a tone that security is optional.” — P10, Cybersecurity Engineer;
- “Doctors get frustrated with MFA. Sometimes IT disables it to avoid conflict.” — P5, Nurse on Cybersecurity Committee.
3.4. Value of Engagement, Visibility, and Mentorship
- “We have IT liaisons who rotate through departments. It builds trust. People are more likely to report something suspicious.” — P6, Associate Director, EMR Applications;
- “Pairing new nurses with experienced staff who understand cybersecurity helps normalize good behavior early on.” — P7, Nurse on Cybersecurity Committee.
3.5. Behavioral Integration in Policy and Technology
- “Security training should feel relevant. Pop-up reminders for MFA or phishing tips at login screens would be better than long lectures.” — P3, Product Manager with Nursing Background;
- “We need policies designed with clinicians, not just for them.” — P1, Help Desk Analyst,
3.6. Theme Frequency Summary
| Theme | Frequency (Mentions Across Participants) |
|---|---|
| Phishing Concerns | 10 |
| Training Ineffectiveness | 10 |
| Unit-Specific Training Recommendation | 9 |
| IT Staff Training Recommendation | 8 |
| Shared Credential Use | 8 |
| Workflow vs. Compliance Conflict | 8 |
| Inclusion in Policy Creation | 7 |
| Mentorship Value | 7 |
4. Discussion
- Design policies that align with clinical workflows and involve frontline staff in their development;
- Deliver tiered, interactive training tailored to specific roles and contexts;
- Improve IT visibility through embedded personnel or departmental liaisons to build trust;
- Implement mentorship programs during onboarding to model secure behaviors.
5. Conclusions
Institutional Review Board Statement
Informed Consent Statement
Conflicts of Interest
References
- Healthcare and Public Health Sector Coordinating Council. Health Industry Cybersecurity Practices: Managing Threats and Protecting Patients (2023 Edition), 2023.
- Ponemon Institute. Cost of a Data Breach Report 2023. https://www.ibm.com/reports/data-breach, 2023. Available online: https://www.ibm.com/reports/data-breach (accessed on 10 April 2025).
- National Institute of Standards and Technology. Cybersecurity: Challenges and Opportunities for Small Businesses, Field Hearing. Technical report, U.S. Department of Commerce, 2023.
- Kannelønning, K.; Katsikas, S.K. A systematic literature review of how cybersecurity-related behavior has been assessed. Information & Computer Security 2023, 31, 463–477. [Google Scholar] [CrossRef]
- Maddux, J.E.; Rogers, R.W. Protection motivation and self-efficacy: A revised theory of fear appeals and attitude change. Journal of Experimental Social Psychology 1983, 19, 469–479. [Google Scholar] [CrossRef]
- Dodge, C.E.; Fisk, N.; Burruss, G.W.; Moule, R.K.; Jaynes, C.M. What motivates users to adopt cybersecurity practices? A survey experiment assessing protection motivation theory. Criminology & Public Policy 2023, 22, 849–868. [Google Scholar] [CrossRef]
- Caelli, K.; Ray, L.; Mill, J. “Clear as Mud”: Toward greater clarity in generic qualitative research. International Journal of Qualitative Methods 2003, 2, 1–13. [Google Scholar] [CrossRef]
- Braun, V.; Clarke, V. Using thematic analysis in psychology. Qualitative Research in Psychology 2006, 3, 77–101. [Google Scholar] [CrossRef]
- Guest, G.; Bunce, A.; Johnson, L. How many interviews are enough? An experiment with data saturation and variability. Field Methods 2006, 18, 59–82. [Google Scholar] [CrossRef]
- Birt, L.; Scott, S.; Cavers, D.; Campbell, C.; Walter, F. Member checking: A tool to enhance trustworthiness or merely a nod to validation? Qualitative Health Research 2016, 26, 1802–1811. [Google Scholar] [CrossRef] [PubMed]
- National Commission for the Protection of Human Subjects of Biomedical and Behavioral Research. The Belmont Report: Ethical Principles and Guidelines for the Protection of Human Subjects of Research, 1979.
- Nowell, L.; Norris, J.; White, D.; Moules, N. Thematic analysis: Striving to meet the trustworthiness criteria. International Journal of Qualitative Methods 2017, 16, 1–13. [Google Scholar] [CrossRef]
- Floyd, D.; Prentice-Dunn, S.; Rogers, R. A meta-analysis of research on protection motivation theory. Journal of Applied Social Psychology 2006, 30, 407–429. [Google Scholar] [CrossRef]
- Sulaiman, N.S.; Fauzi, M.A.; Hussain, S.; Wider, W. Cybersecurity behavior among government employees: The role of protection motivation theory and responsibility in mitigating cyberattacks. Information 2022, 13, 413. [Google Scholar] [CrossRef]
- Abouelmehdi, K.; Beni-Hessane, A.; Khaloufi, H. Cybersecurity Training in Healthcare: A Systematic Review of Trends and Effectiveness. Health Informatics Journal 2024, 30, 95–112. [Google Scholar] [CrossRef]
- Renaud, K.; Flowerday, S.; Smith, M. Embedding Behavioral Science into Cybersecurity Governance: A Holistic Framework. Journal of Cybersecurity and Privacy 2023, 3, 450–468. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




