Submitted:
30 June 2025
Posted:
02 July 2025
Read the latest preprint version here
Abstract
Keywords:
1. Introduction
- High-fidelity physical process simulation
- Real-time monitoring,
- Adversarial attack emulation and Hybrid anomaly detection using both physics-based and machine learning techniques.
2. Related Work
3. Core Components
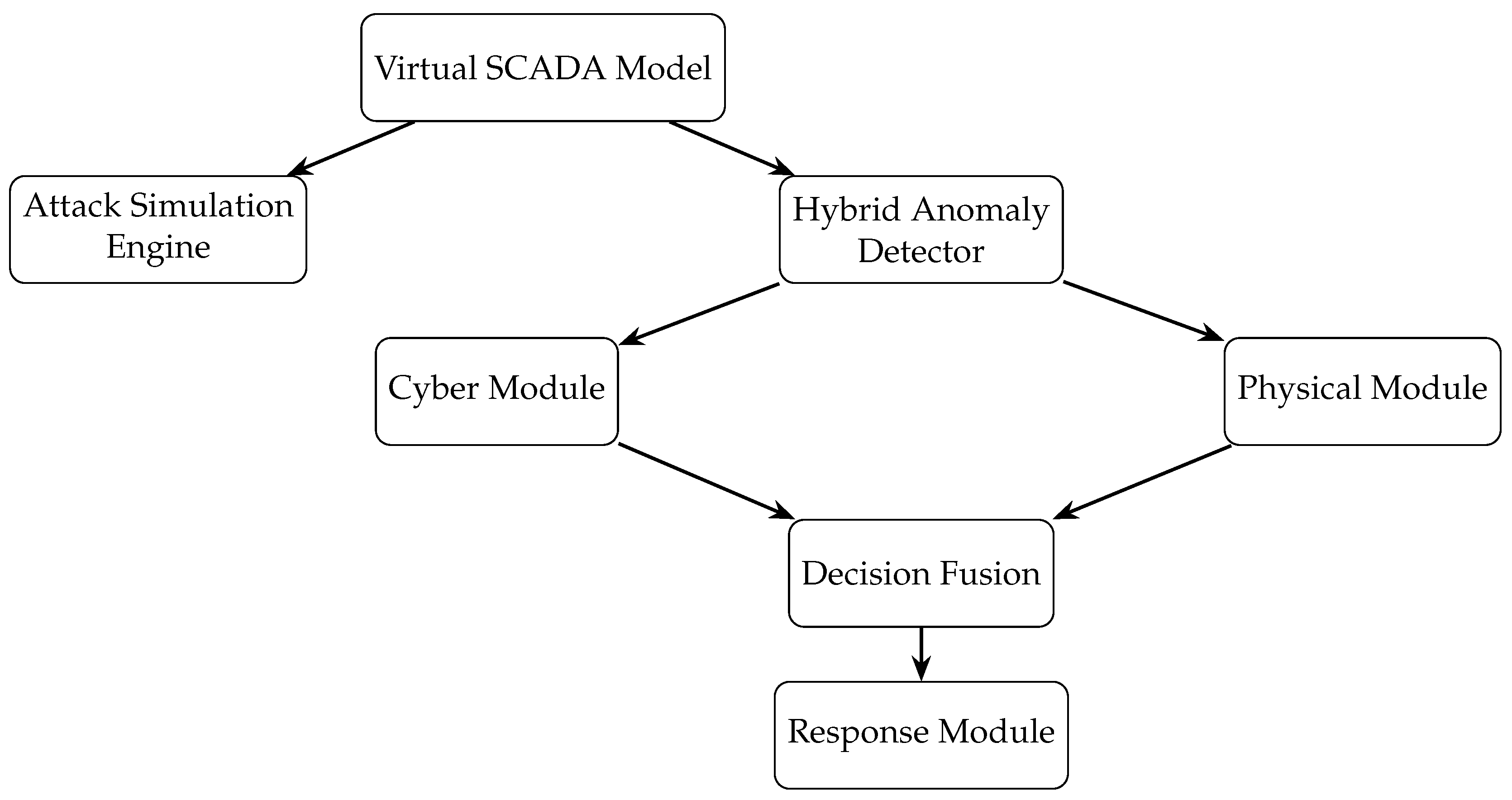
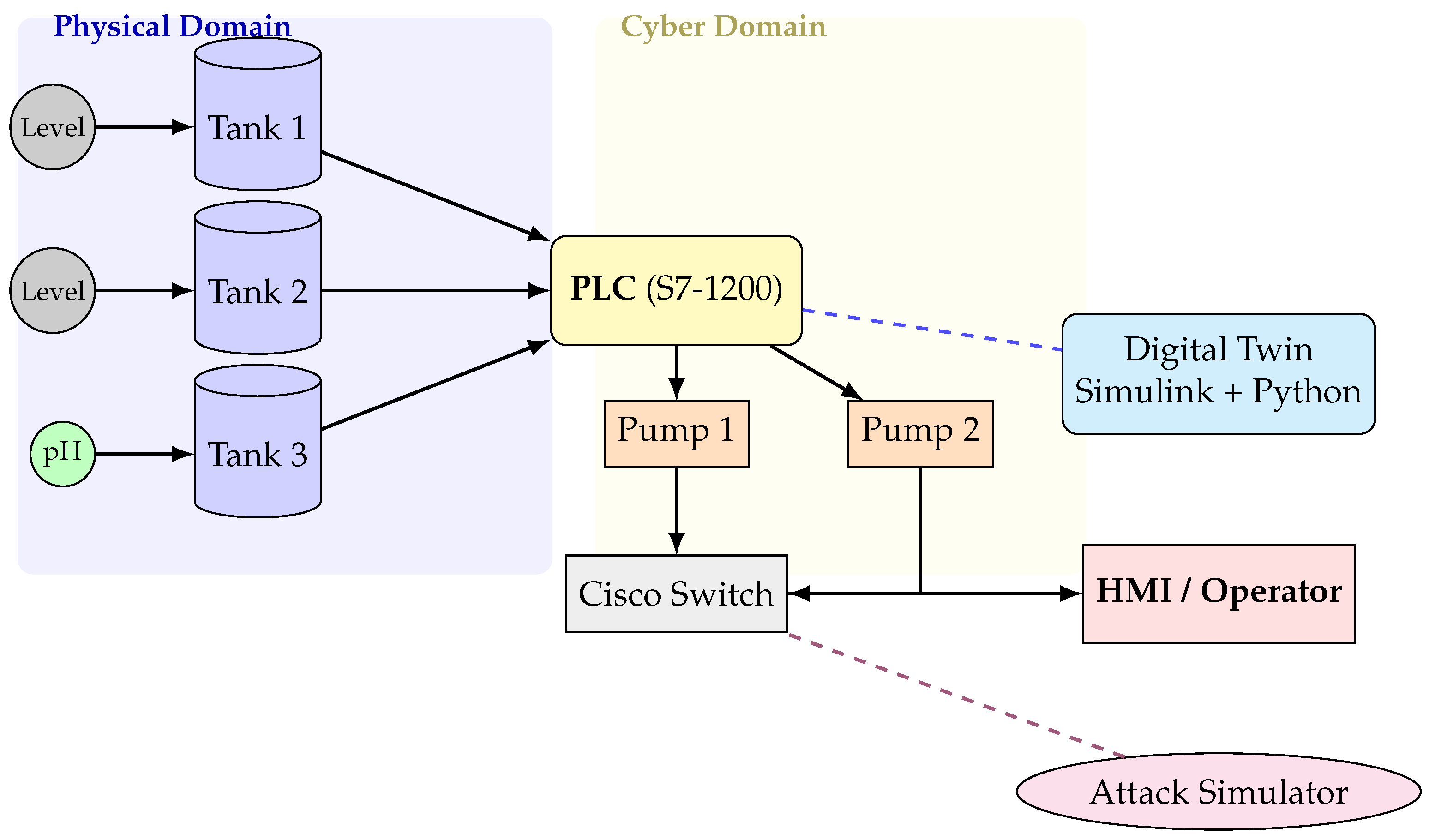
3.1. Virtual SCADA Model
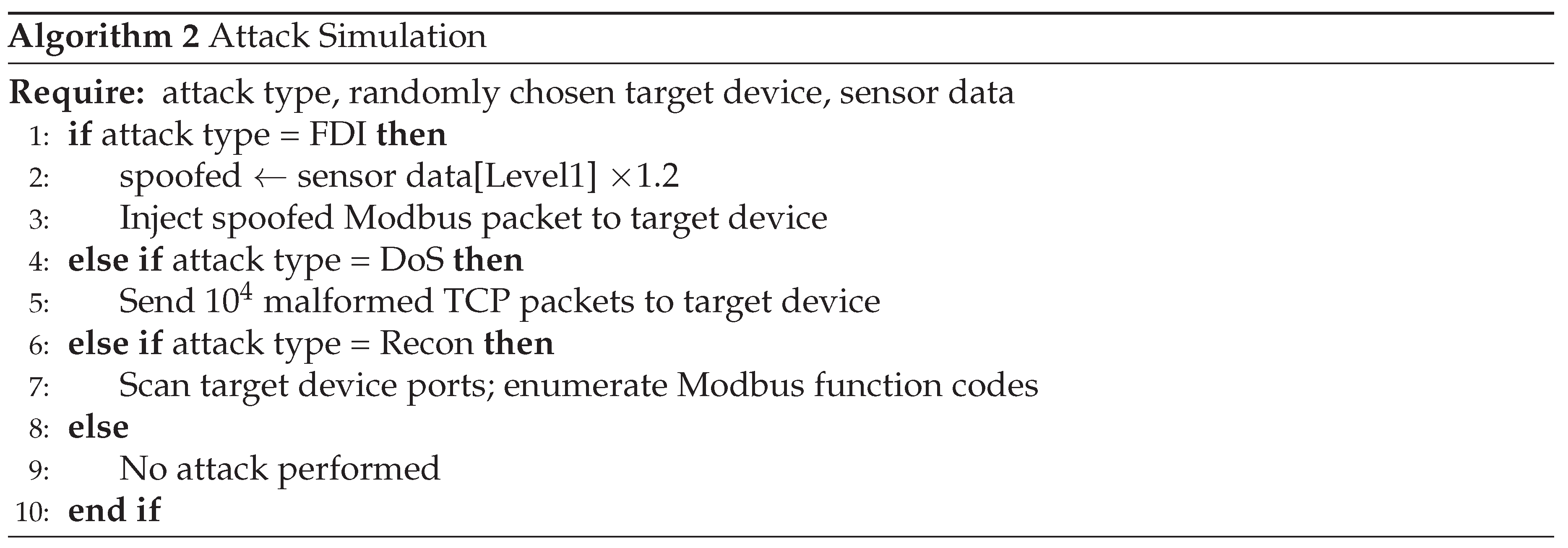
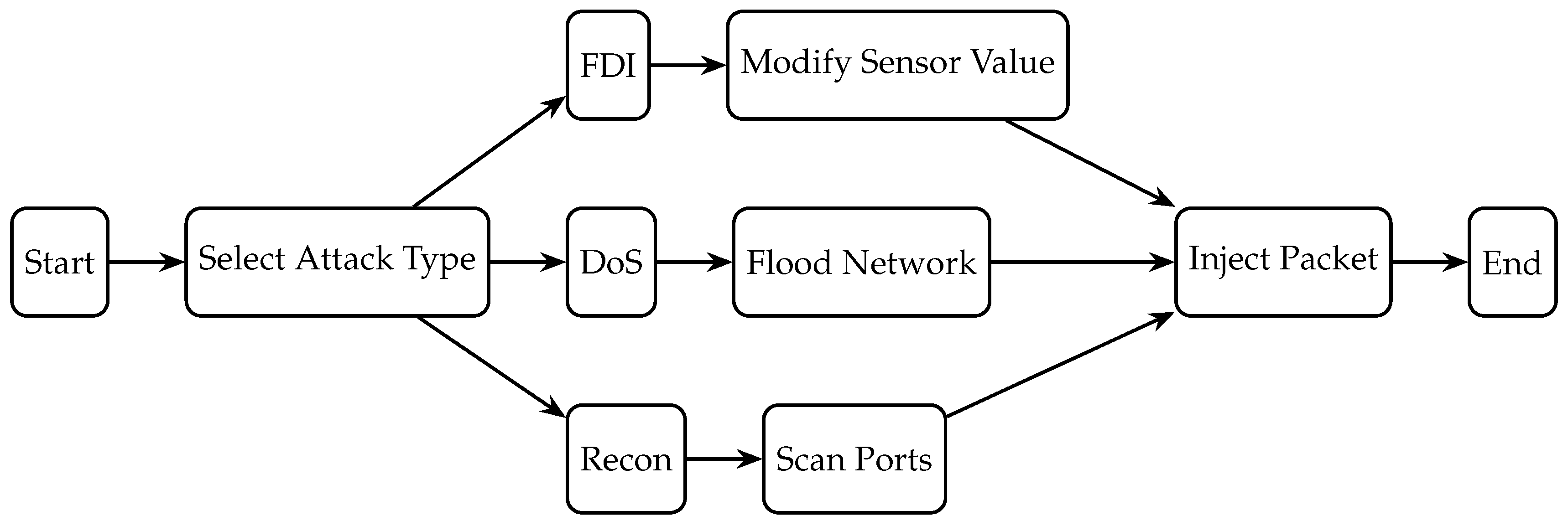
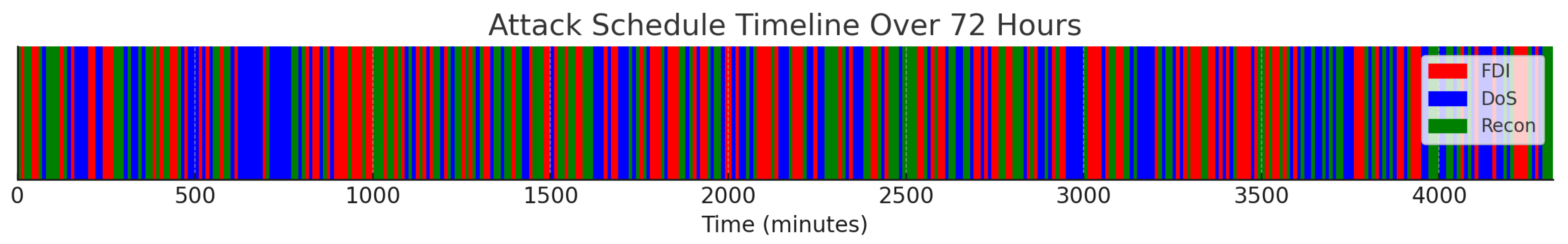
3.2. Attack Simulation Engine
- False Data Injection (FDI): Introduces up to ±20% sensor bias or ramps in tank level and pH readings.
- Denial of Service (DoS): Floods the PLC-HMI channel with malformed Modbus packets per second.
- Reconnaissance/Command Injection: Performs automated port scans and injects unauthorized commands, e.g., remote actuator manipulation.
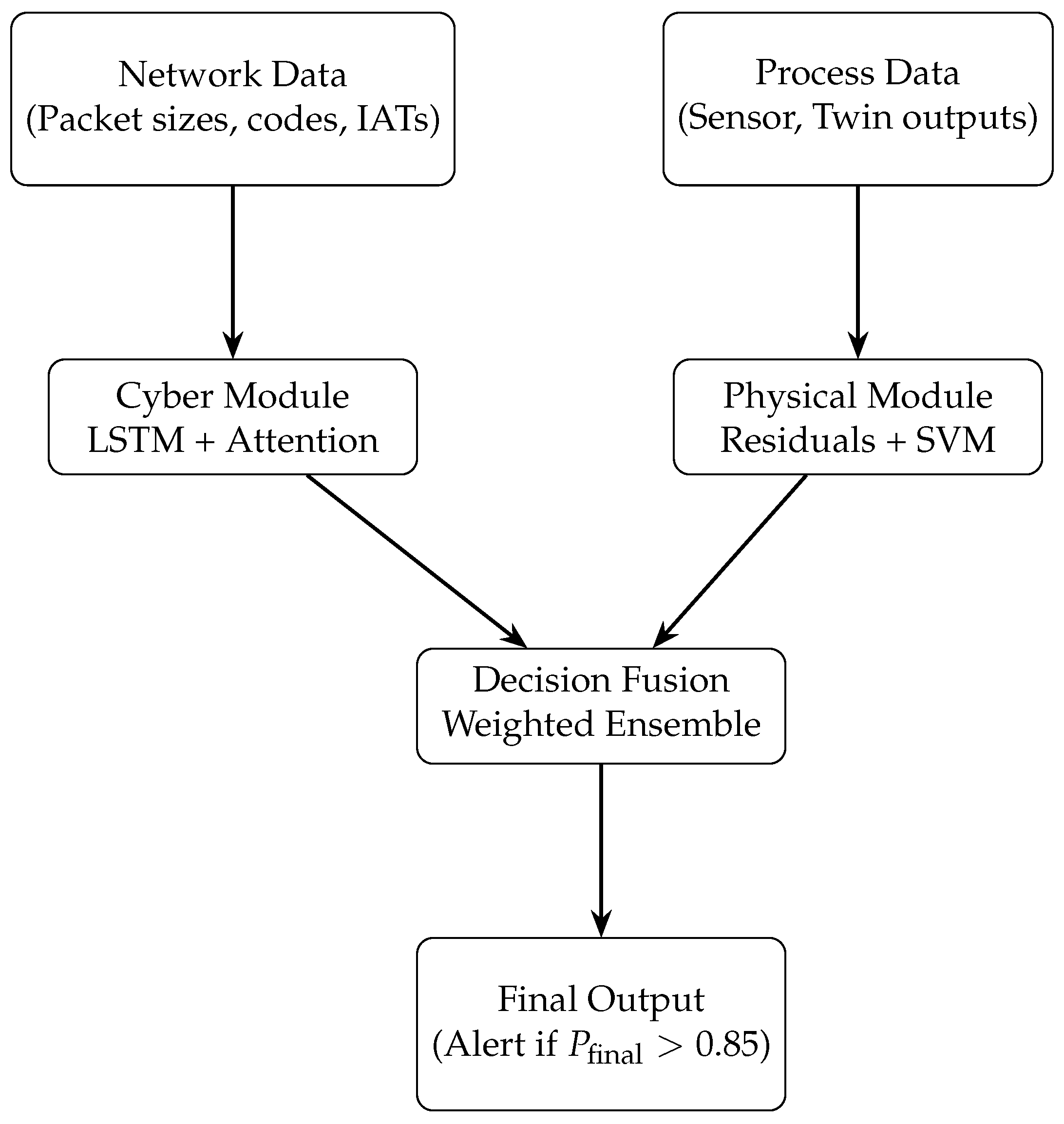
3.3. Hybrid Anomaly Detector
Cyber Module:
Physical Module:
Decision Fusion:
3.4. Response Module
Alerting and Human-in-the-Loop:
Mitigation Actions:
- Stage 1: The system raises visual and audible alarms on the HMI, while logging all relevant forensic data (such as network packet captures and process sensor snapshots) for post-incident analysis.
- Stage 2: If the anomaly persists or is classified as critical, the system enforces PLC command lockdown by restricting process control to a predefined whitelist of safe operations, preventing further unauthorized manipulation.
- Stage 3: In the event of sustained or high-severity attack, the system can automatically trigger fail over to redundant backup controllers to maintain process continuity and safety.
Adaptive Learning and Concept Drift:
4. Case Study: Water Treatment Plant
4.1. Testbed Configuration
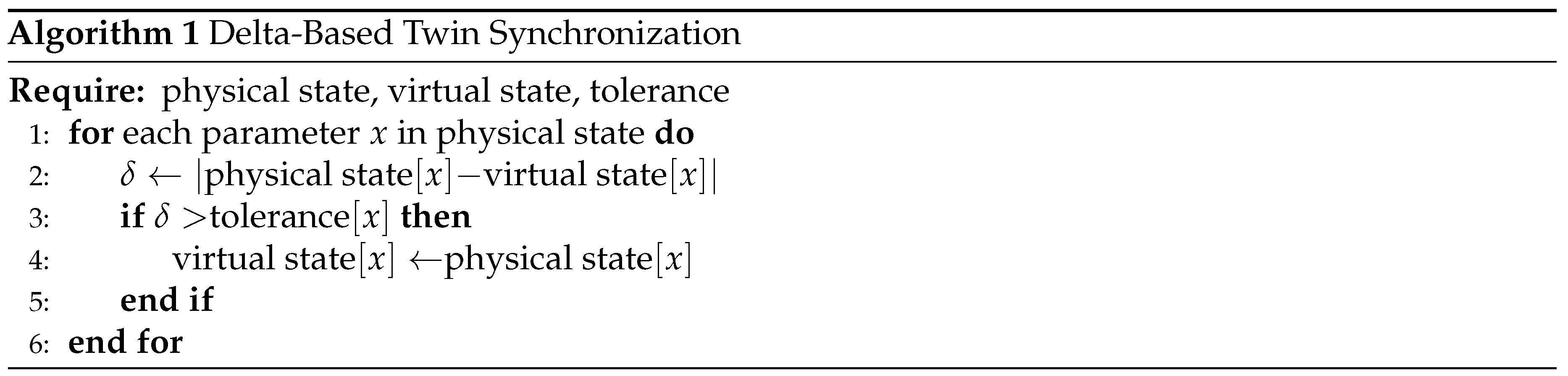
4.2. Digital Twin Implementation
4.3. Attack Scenarios
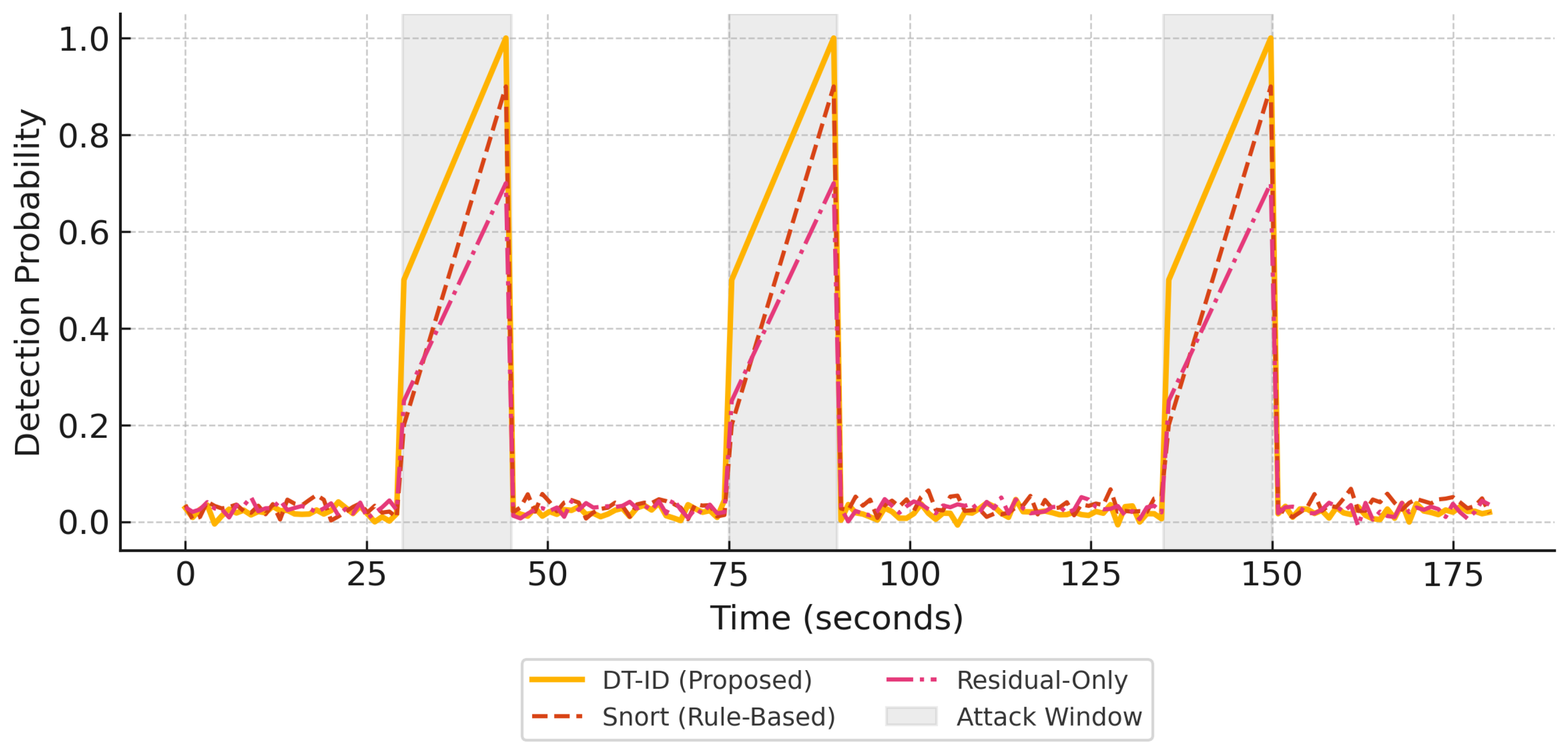
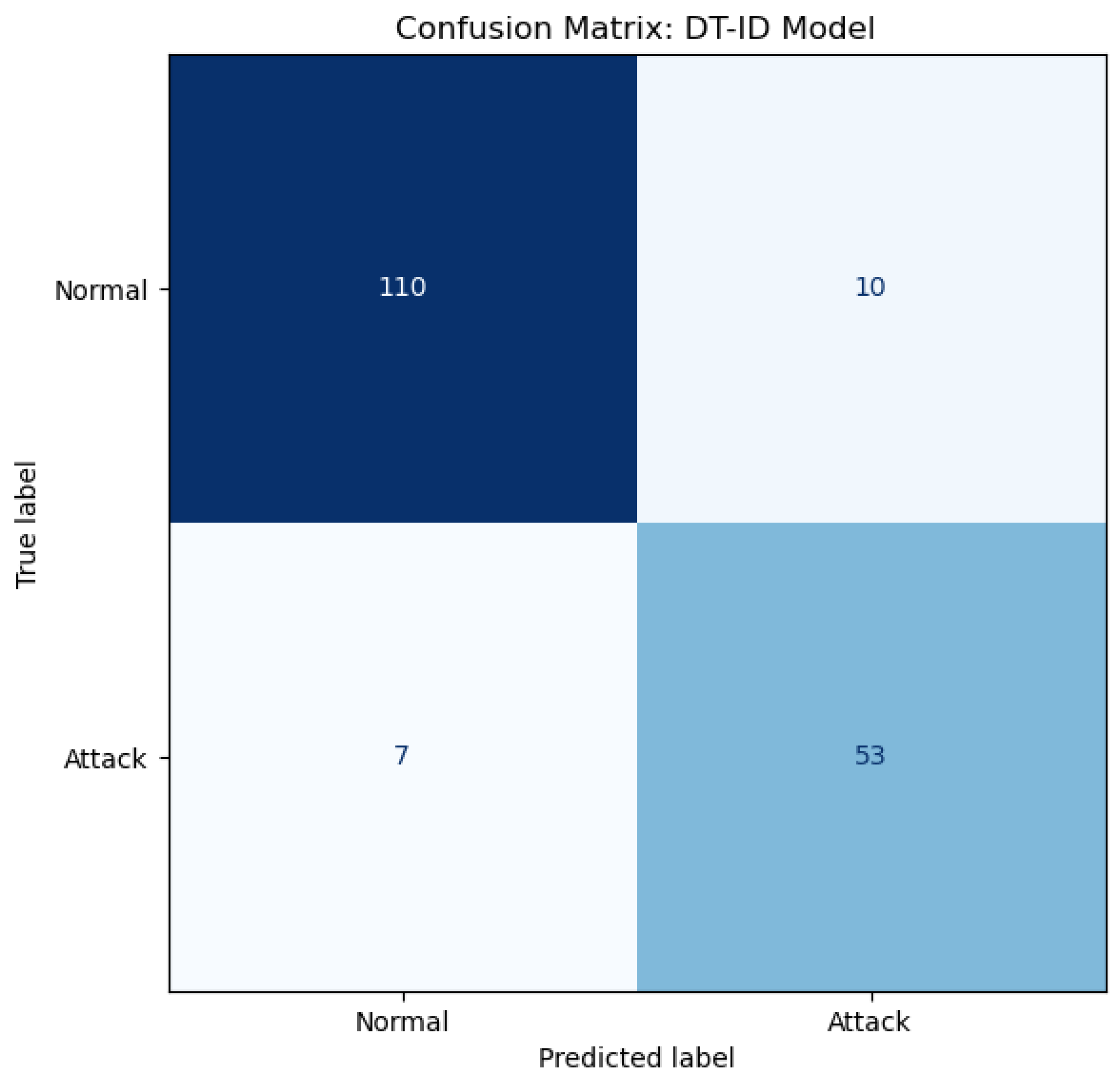
4.4. Validation Metrics and Baselines
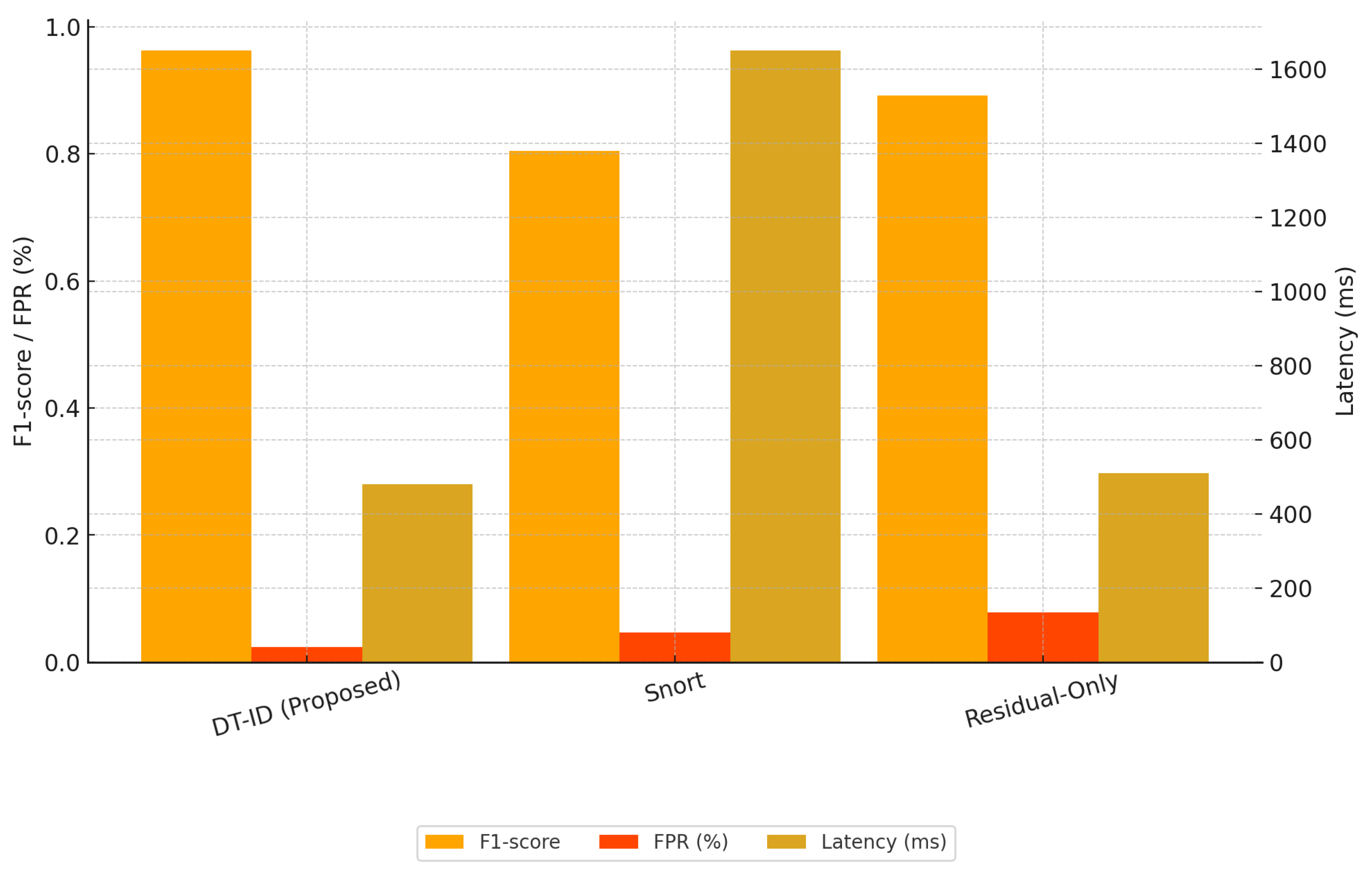
- Snort IDS (Rule-Based): A signature-based intrusion detection engine using Modbus/TCP rules.
- Physics-Only Residual Detector: Flags physical anomalies using residual thresholds without learning or cyber analysis.
4.5. Simulation Results
4.6. Implementation Challenges and Solutions
- Physics-Guided Hybrid Detection: By fusing model-based residual analysis from a high-fidelity digital twin with cyber anomaly scores from LSTM-based learning, the framework combines the precision of process-aware monitoring with the adaptability of data-driven detection. This hybrid architecture improves detection sensitivity, especially for stealthy false data injection (FDI) attacks that may evade purely signature-based or statistical methods.
- Adversarial-Aware Attack Simulation: The framework features a configurable attack simulation engine that supports both conventional ICS threats and synthetically generated zero-day scenarios using adversarial machine learning techniques. This design provides rigorous, repeatable testing of IDS performance under a broad spectrum of threat conditions, including adaptive adversaries.
- Adaptive Decision Fusion and Threshold Optimization: A dynamic decision fusion mechanism combines cyber and physical anomaly scores with empirically tuned weights (0.3/0.7), optimized via grid search to maximize F1-score. Thresholds for detection (e.g., ) are calibrated using ROC analysis on validation data, ensuring a strong tradeoff between sensitivity and specificity.
- Edge-Cloud Operational Synergy: The system architecture supports distributed deployment: real-time anomaly scoring is handled at the edge (near PLCs and sensors), while batch retraining and forensic analysis are conducted in the cloud. This hybrid execution model enables both low-latency response and scalable analytics.
- Resilience via Concept Drift Adaptation: The detection models (LSTM and SVM) are retrained periodically using recent data and evaluated for performance drift using the Page-Hinkley test. This ensures that the DT-ID system maintains relevance in evolving operational conditions without manual recalibration.
- Integrated Replay and Visualization: The use of Unity 3D for visual twin representation and AWS IoT TwinMaker for state orchestration enables comprehensive replay of attack scenarios, operator insight, and real-time visualization bridging the gap between technical anomaly alerts and actionable engineering decisions.
5. Conclusions
References
- Dragos Inc.. The Industrial Security Year in Review, 2024. [Online]. Available: https://www.dragos.com.
- Zetter, K. Countdown to Zero Day: Stuxnet and the Launch of the World’s First Digital Weapon; Crown: New York, NY, USA, 2014. [Google Scholar]
- Case, A.; Morgus, R. Industroyer: Biggest threat to industrial control systems since Stuxnet, 2017. ESET, [Online]. Available: https://www.welivesecurity.com.
- FireEye. Attackers deploy new ICS attack framework ’TRITON’ and cause operational disruption, 2017. [Online]. Available: https://www.fireeye.com.
- Roesch, M. Snort: Lightweight intrusion detection for networks. In Proceedings of the Proc. 13th USENIX Conf. Syst. Admin., 1999, pp. 229–238.
- OISF. Suricata: Open Source IDS/IPS/NSM engine. [Online]. Available: https://suricata.io.
- Paxson, V. Bro: A system for detecting network intruders in real-time. Comput. Netw. 1999, 31, 2435–2463. [Google Scholar] [CrossRef]
- Giraldo, J.A.; et al. A survey of physics-based attack detection in cyber-physical systems. ACM Comput. Surv. 2019, 52, 1–36. [Google Scholar] [CrossRef] [PubMed]
- Langner, R. Stuxnet: Dissecting a cyberwarfare weapon. IEEE Security Privacy 2011, 9, 49–51. [Google Scholar] [CrossRef]
- Grieves, M.; Vickers, J. Digital twin: Mitigating unpredictable, undesirable emergent behavior in complex systems. In Transdisciplinary Perspectives on Complex Systems; Springer, 2017; pp. 85–113.
- Oyekan, J.; Hu, H. A digital twin framework for cyber-security monitoring in pipeline transport systems. IEEE Access 2021, 9, 155532–155543. [Google Scholar]
- Zhang, Y.; et al. Digital twin-driven smart manufacturing: Connotation, reference model, applications and research issues. Rob. Comput.-Integr. Manuf. 2020, 61, 101837. [Google Scholar]
- Zhao, Y.; Wang, J.; Chen, Q. A Digital Twin-Driven Cyber-Physical Intrusion Detection System for Industrial IoT: Design and Experimental Validation. IEEE Internet of Things Journal 2023, 10, 10345–10356. [Google Scholar]
- Lin, H.; Xie, S.; Zheng, R. Real-Time Hybrid Anomaly Detection for SCADA Systems Using Digital Twins and Deep Learning. ISA Transactions 2024, 145, 78–89. [Google Scholar] [CrossRef]
- Mohammadi, A.; Farsi, M.; Salah, K. Secure Digital Twin-Based Anomaly Detection in Water Treatment Plants: A GAN-Enhanced Approach. Computers & Security 2023, 133, 103332. [Google Scholar]
- Mitchell, R.; Chen, I.R. A survey of intrusion detection techniques for cyber-physical systems. ACM Comput. Surv. 2014, 46, 55–1. [Google Scholar] [CrossRef]
- Pan, X.; Luo, W.; Song, H. Hybrid Deep Learning and Physics-Guided Digital Twins for Industrial Cyber-Physical Anomaly Detection. Journal of Process Control 2024, 135, 63–73. [Google Scholar]
- Xu, Y.; Yang, Z.; He, D. Towards Zero-Day Attack Detection in Smart Manufacturing: A Digital Twin and Deep Learning Fusion. IEEE Transactions on Industrial Informatics 2024, 20, 6001–6012. [Google Scholar]
- Creswell, A.; et al. Generative adversarial networks: An overview. IEEE Signal Process. Mag. 2018, 35, 53–65. [Google Scholar] [CrossRef]
- iTrust SUTD. Secure Water Treatment (SWaT) Dataset, 2016. [Online]. Available: https://itrust.sutd.edu.sg.
- iTrust SUTD. Water Distribution (WADI) Dataset, 2017. [Online]. Available: https://itrust.sutd.edu.sg.
- Alves, T.; et al. BATADAL: A realistic, scenario-based dataset for testing anomaly detection in water distribution systems. In Proceedings of the Proc. 3rd Int. Workshop Cyber-Physical Syst. for Smart Water Netw. 2017. [Google Scholar]
- Creswell, A.; White, T.; Dumoulin, V.; Arulkumaran, K.; Sengupta, B.; Bharath, A.A. Generative adversarial networks: An overview. IEEE Signal Processing Magazine 2018, 35, 53–65. [Google Scholar] [CrossRef]
| Attack Type | Description | Parameters | Target |
|---|---|---|---|
| FDI | Sensor bias/ramp | Bias: ±20% | Level, pH |
| DoS | Modbus packet flood | /sec | PLC-HMI |
| Recon/Command | Port scan, command injection |
Scan, STOP command | PLC, Actuator |
| Attack Type | Description | Parameters | Objective |
|---|---|---|---|
| FDI | Sensor spoofing | Bias: ±20% | Trigger false tank/pH states |
| DoS | Packet flood | /sec | Disrupt PLC-HMI communication |
| Recon/Cmd | Port scan, STOP cmd |
Scan, Unauthorized cmd |
Compromise process control |
| Method | F1-score | FPR (%) | Latency (ms) |
|---|---|---|---|
| DT-ID (Ours) | 96.3 | 2.4 | 480 |
| Snort IDS | 80.5 | 4.7 | 1650 |
| Physics-Only | 89.2 | 7.8 | 510 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




