Submitted:
09 May 2025
Posted:
13 May 2025
Read the latest preprint version here
Abstract
Keywords:
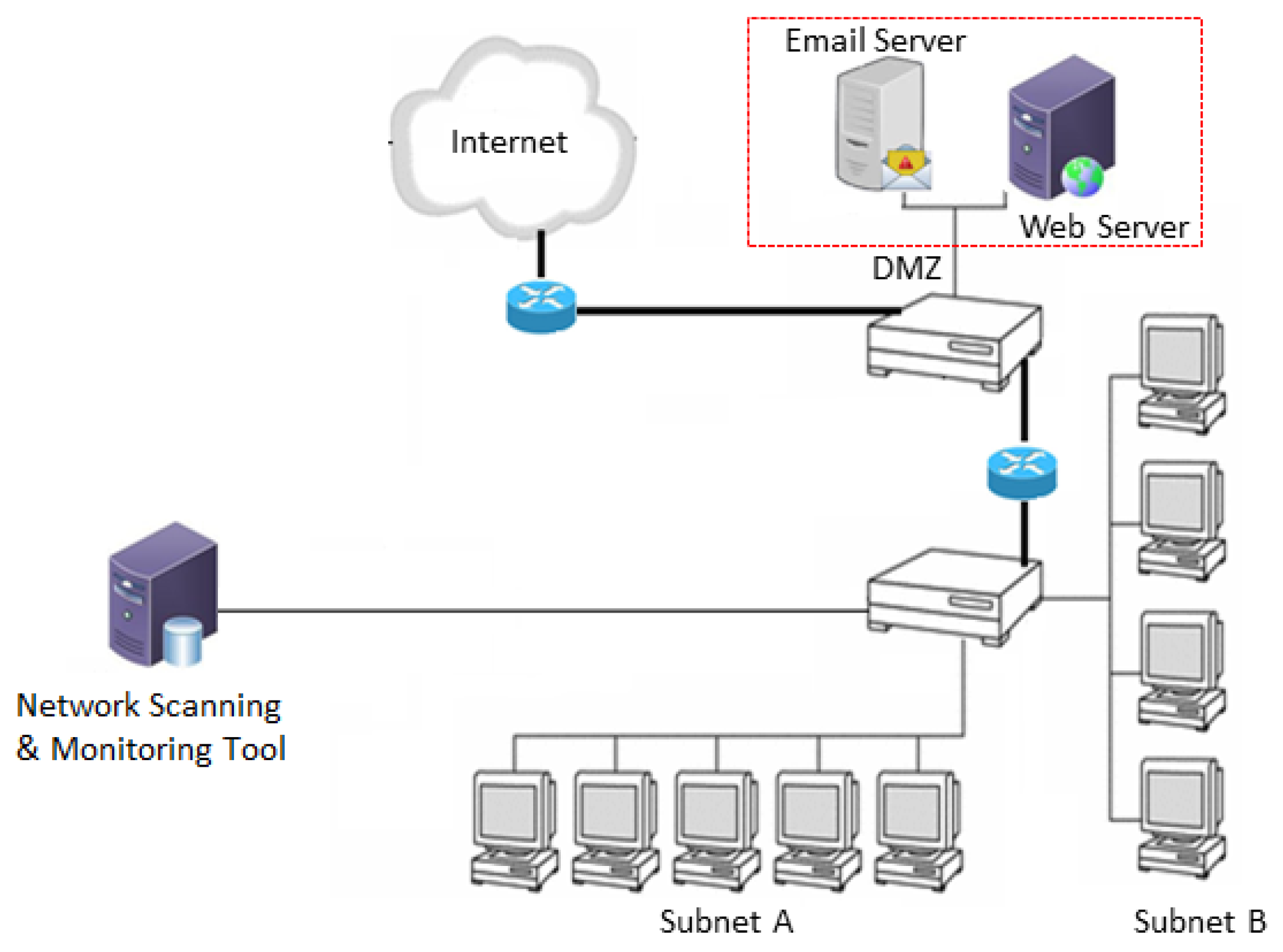
1. Introduction
2. Network Vulnerabilities, Attacks, and Policy Enforcement Methods
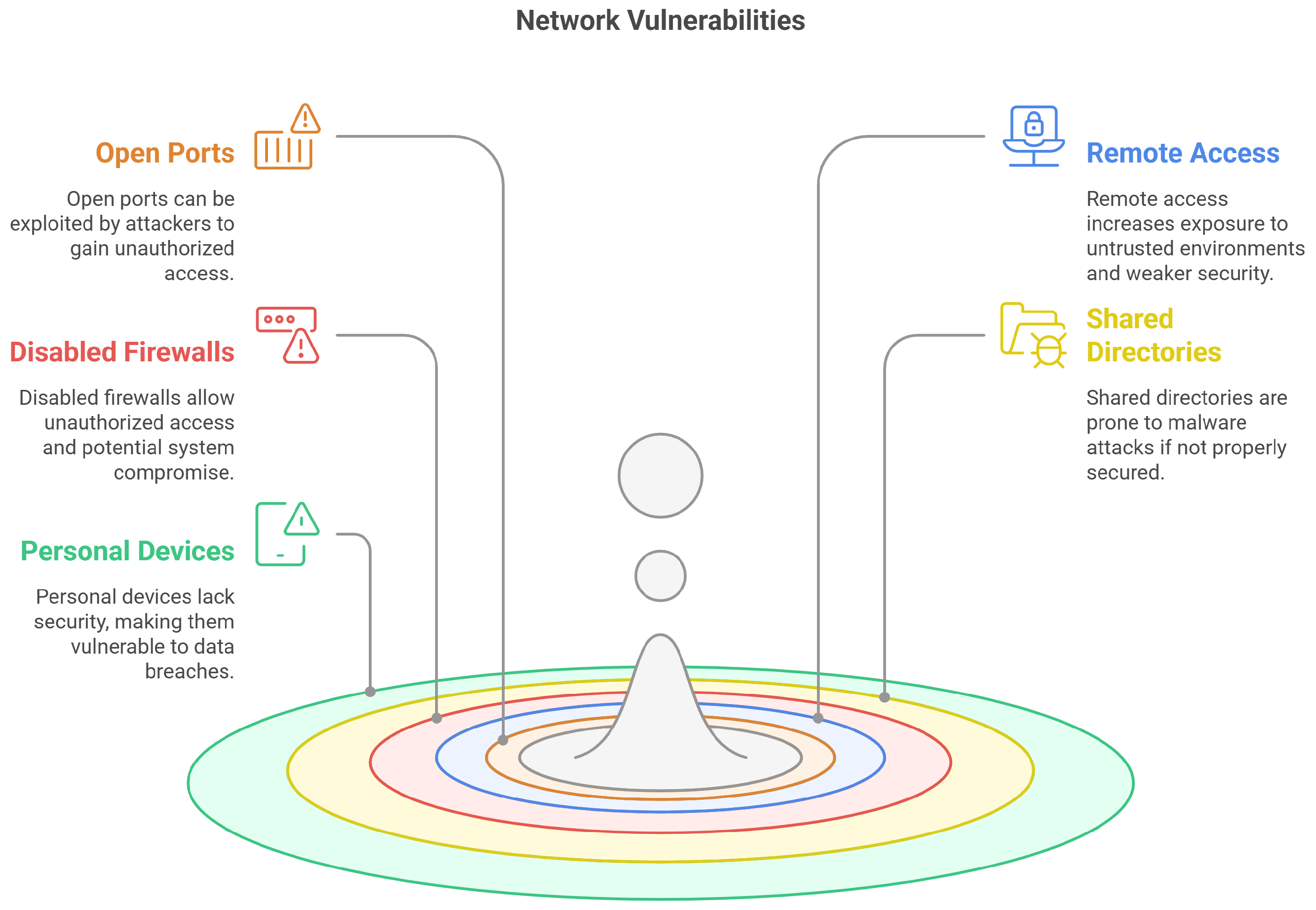
2.1. Common Network Vulnerabilities
2.1.1. Open Ports
2.1.2. Remote Access
2.1.3. Disabled Firewall
2.1.4. Shared Directories
2.1.5. Personal Devices
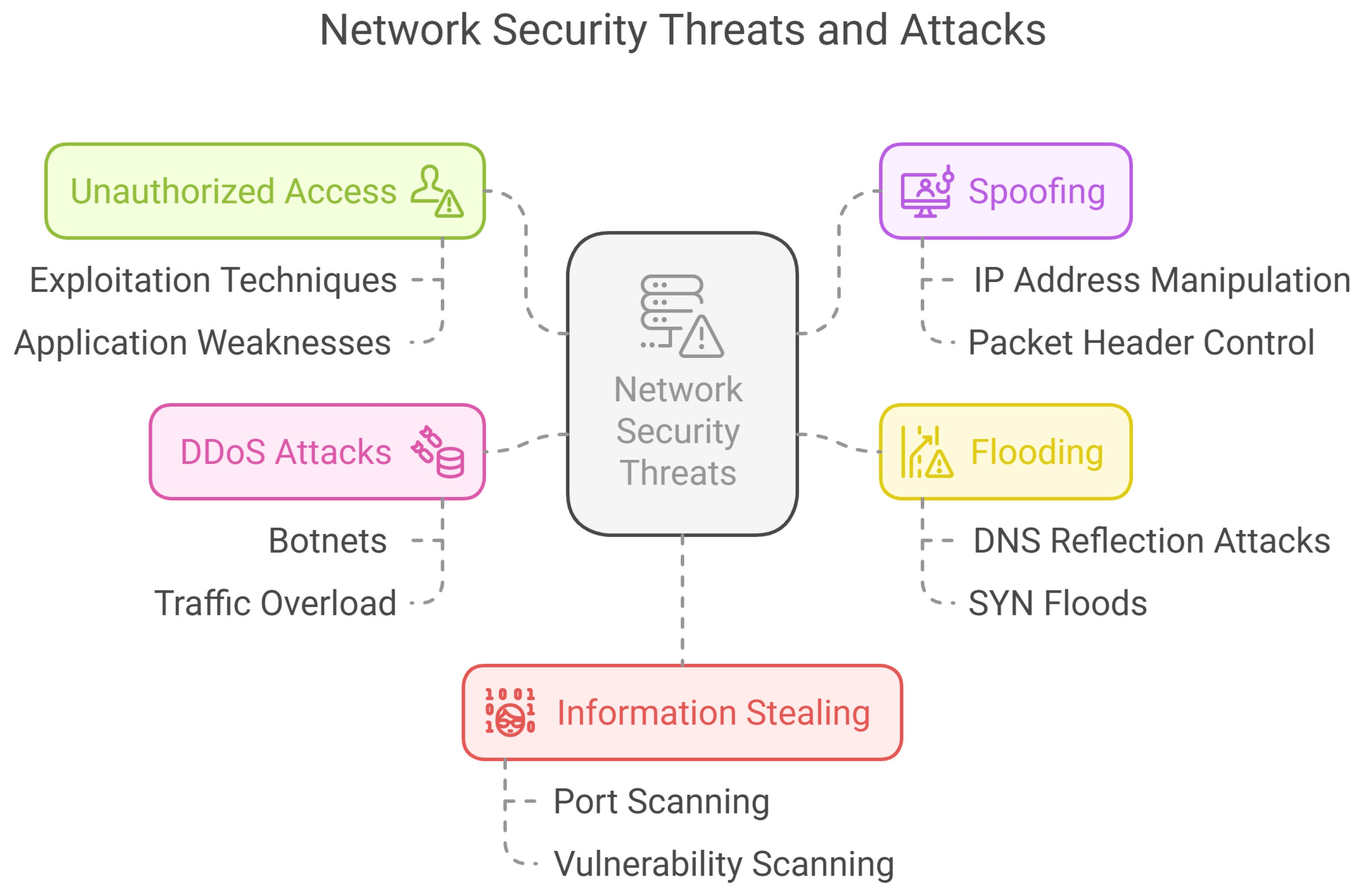
2.2. Common Attacks via Network
2.2.1. Unauthorized Access
2.2.2. Spoofing
2.2.3. Flooding
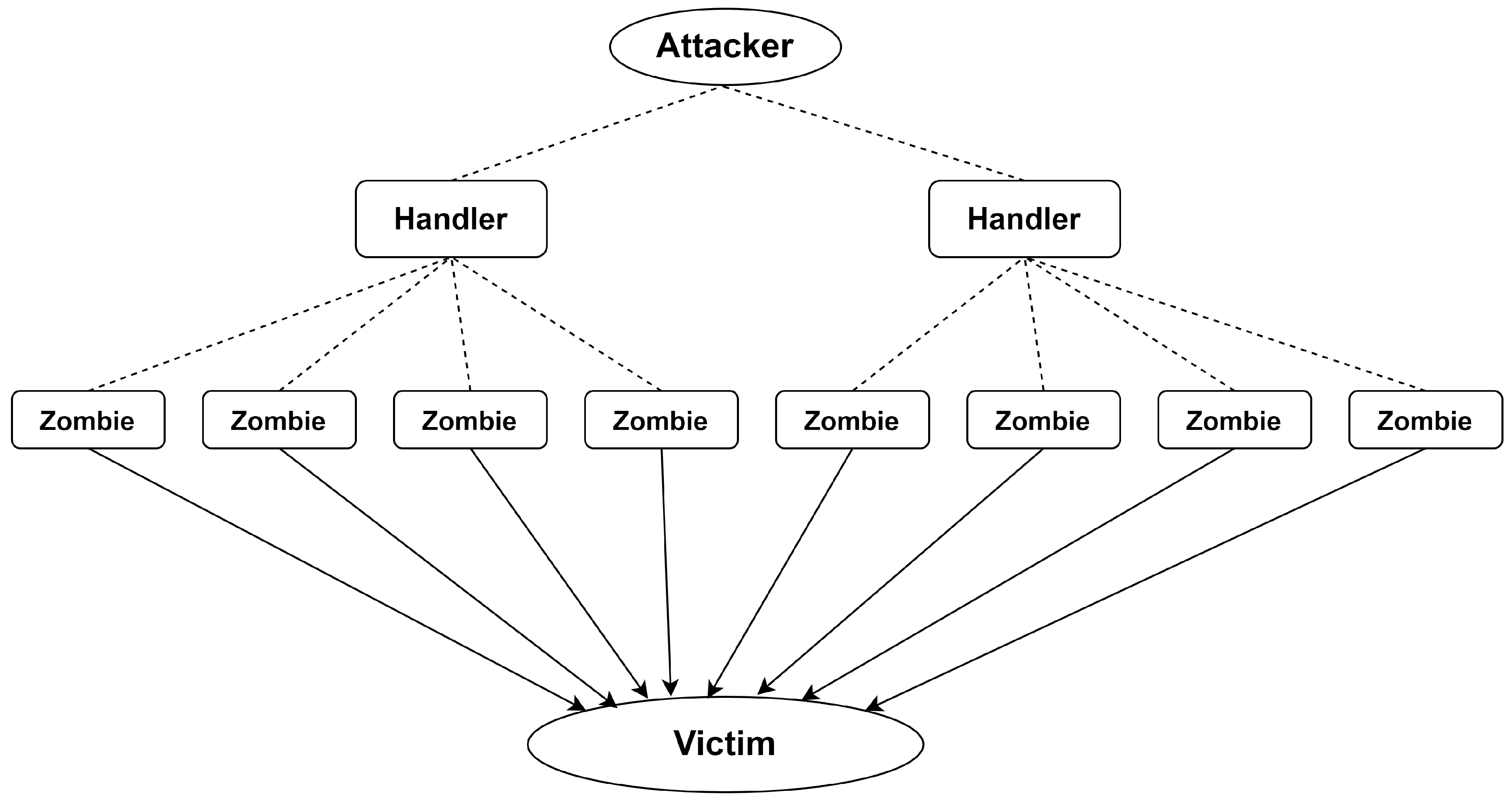
2.2.4. Distributed Denial of Service (DDoS) Attack
- The intruder gathers information about network configuration through port scanners to recognize existing weaknesses in the network.
- The intruder exploits such vulnerabilities to launch the attack over the organization’s network.
- In case of a successful attempt of attack, the attacker further installs and sets up additional software to manage uninterrupted network access channels.
- Finally, the intruder struggles to wash-out any remaining evidence that may be left due to the earlier actions. At this stage, daemons restarted that crashed during the 2nd phase, logs were deleted and various actions were taken accordingly.
2.2.5. Information Stealing
2.3. Policy Enforcement Methods
2.3.1. Guidelines
2.3.2. OS Hardening
2.3.3. Agent-Based Enforcement
2.3.4. Restriction Through Software Defined Networking
2.3.5. Blockchain-Based Policy Enforcement
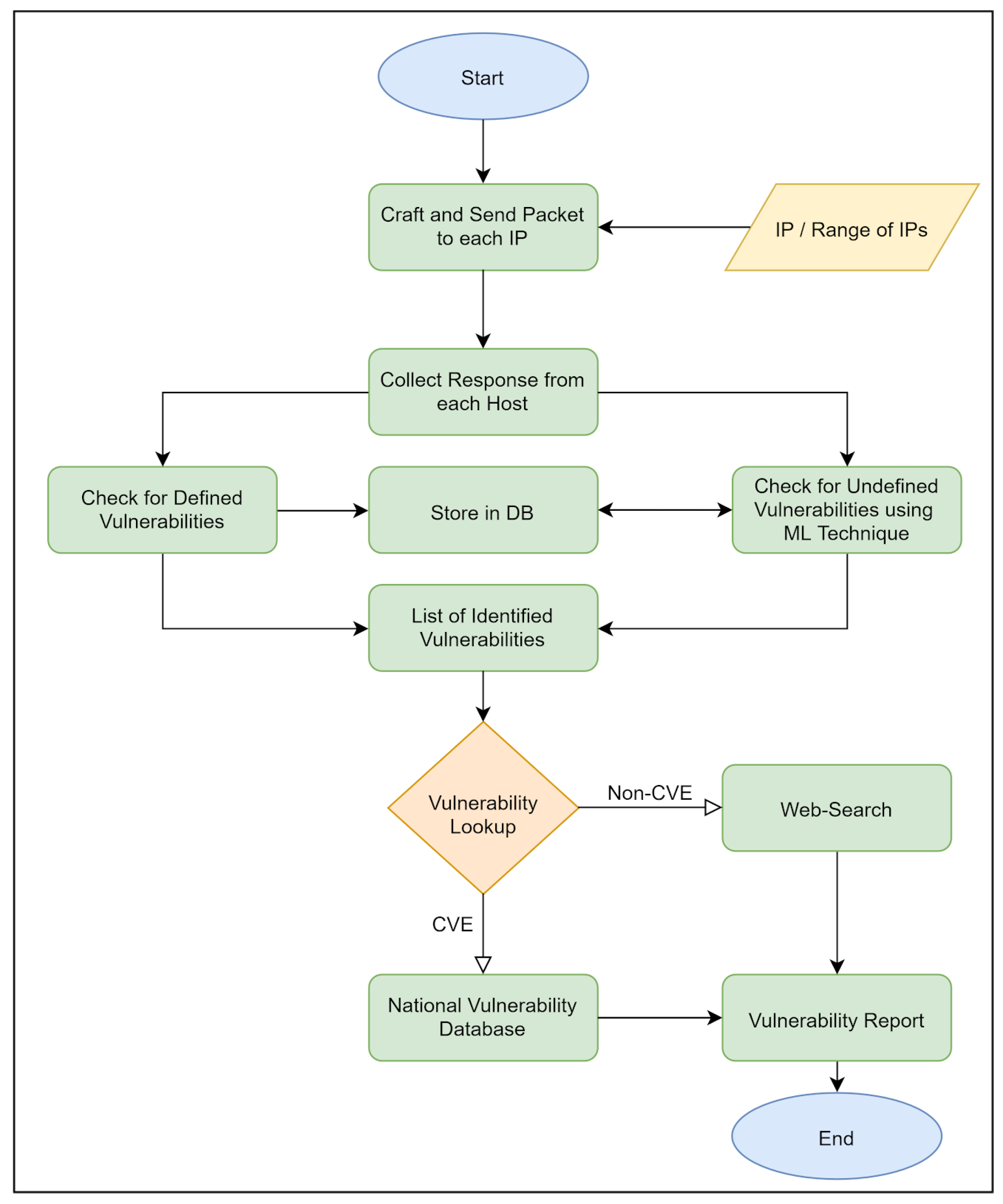
3. Basic Features of a Network Scanner
3.1. IP Scan
3.2. Port Scan
3.2.1. Open Scan
3.2.2. Half-Open Scan
3.2.3. Stealth Scan
3.3. Banner Grabbing/OS Detection
3.4. Server Recognition
3.5. Vulnerability Scan
4. Security Aspects Discoverable via Scanner
4.1. Firewall Status
4.2. Remote Access Status
4.3. Shared Directories
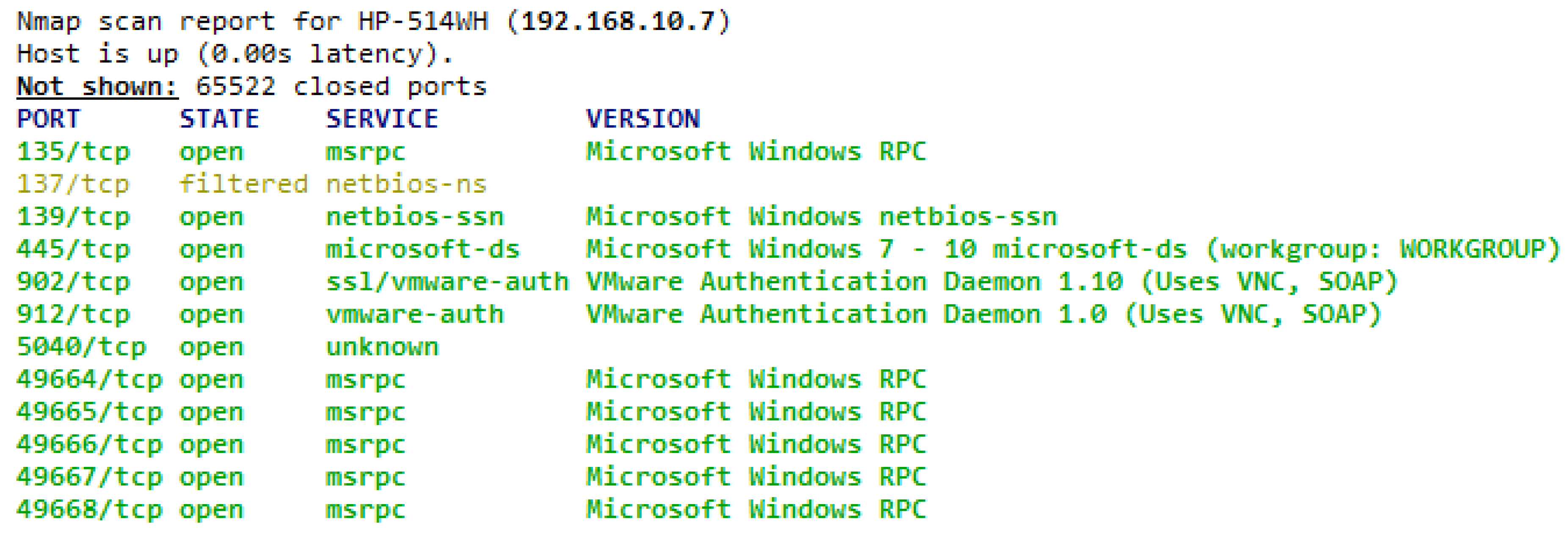
4.4. Malicious Services with Open Ports
4.5. Virtual Machines Recognition
4.6. IP Conflicts
4.7. Wake on LAN
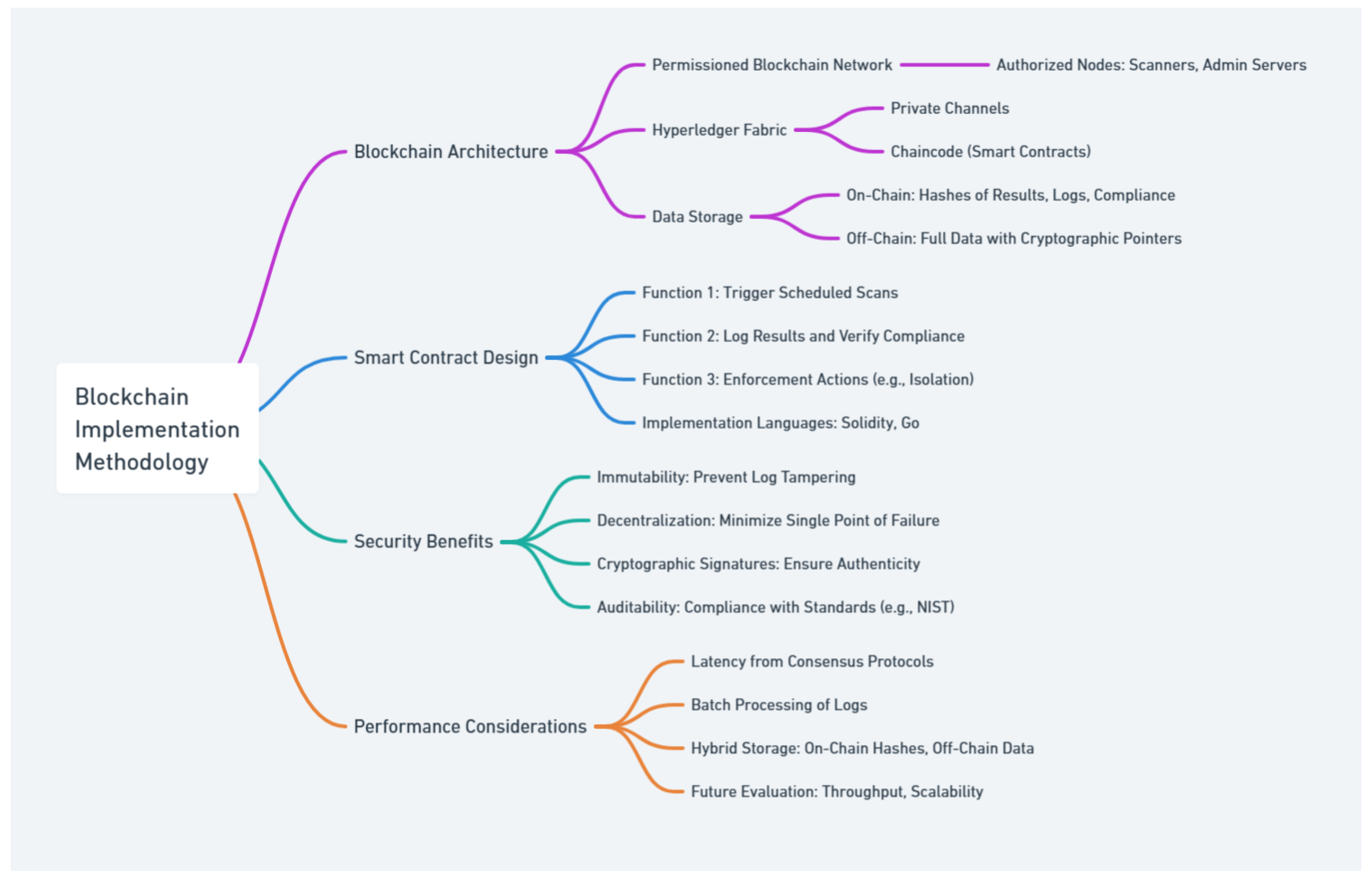
5. Blockchain Implementation Details
5.1. Smart Contract Design
5.2. Security Benefits
5.3. Performance Considerations
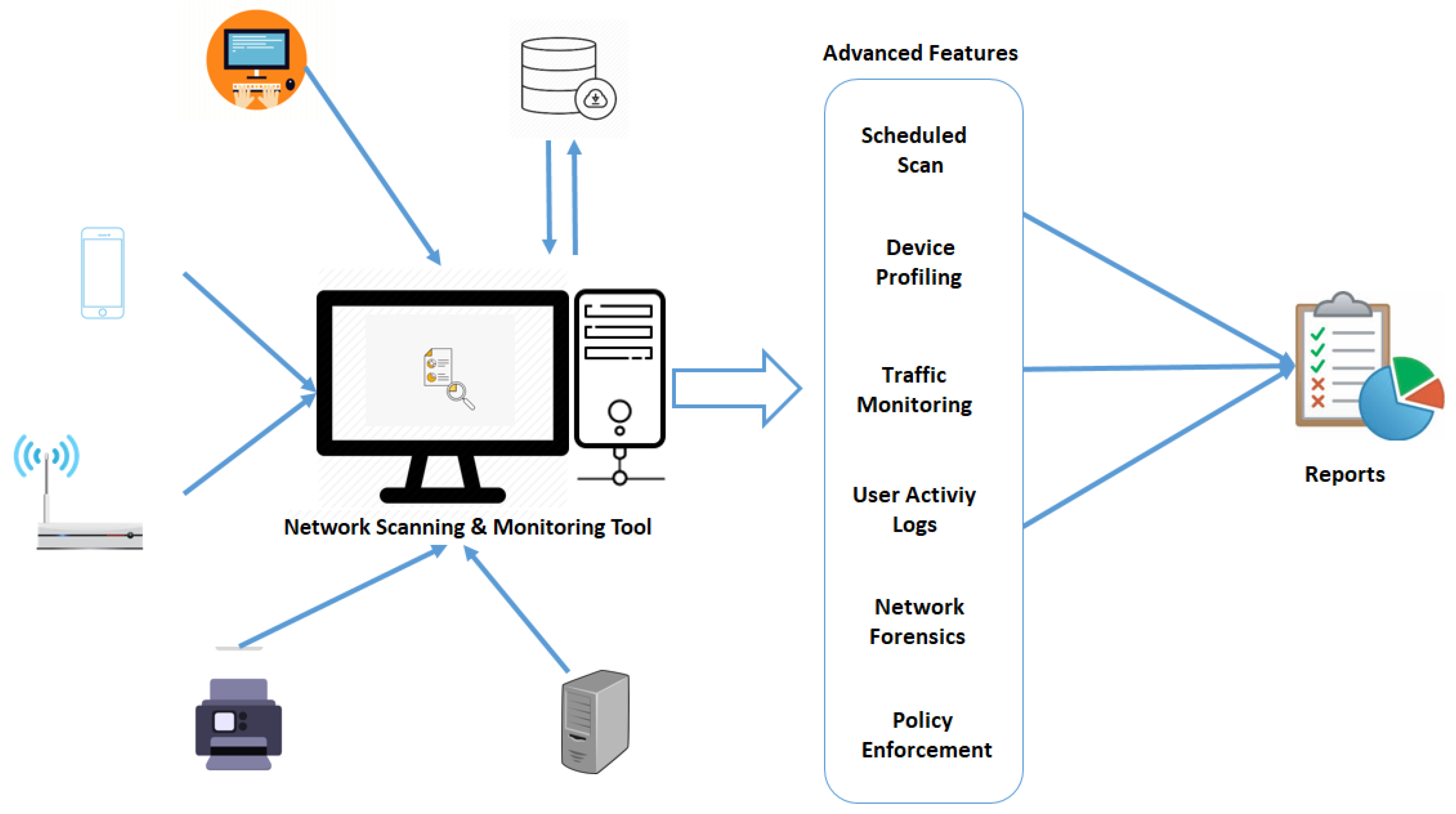
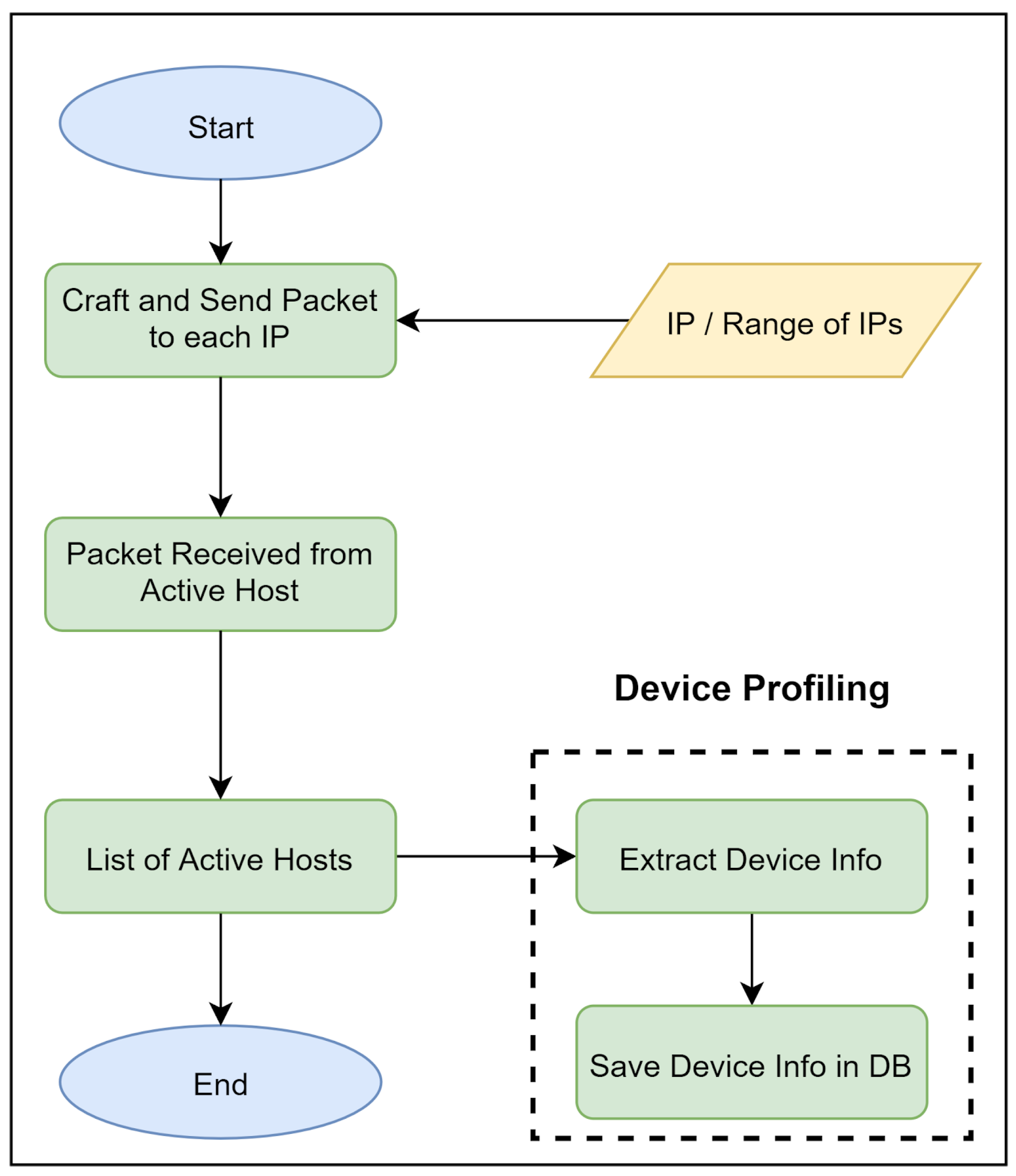
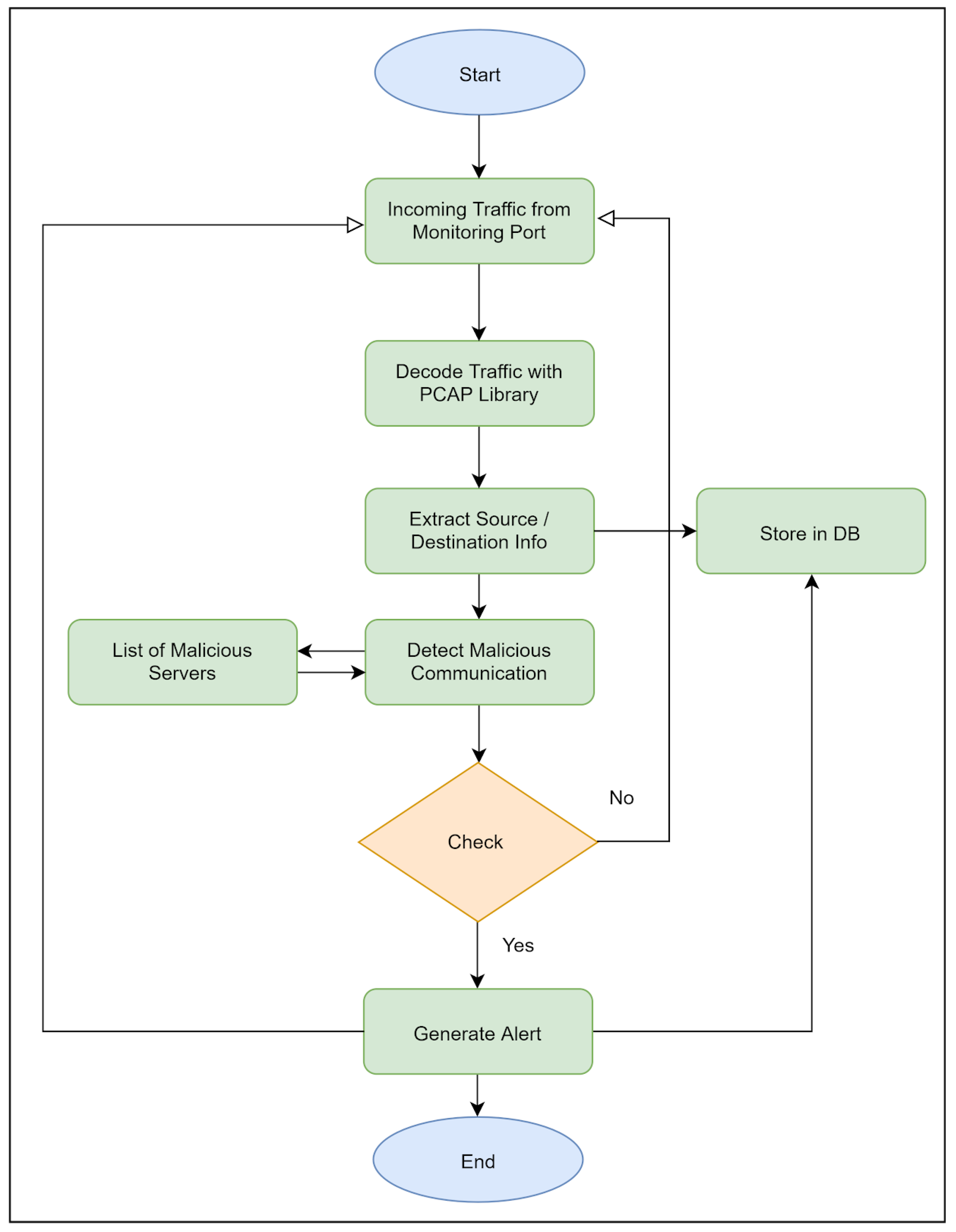
6. Proposed Scanner with Advanced Features
| Algorithm 1 Proposed Network Scanning and Monitoring Algorithm |
|
6.1. Local Database
6.2. Scheduled Scanning
6.3. Device Profiling
6.4. New Device Discovery
6.5. Traffic Monitoring
6.6. User Activity Logs
6.7. Network Forensics
6.8. IDS/IPS Capability Detection
6.9. Blockchain Integrity Checks
6.10. Policy Enforcement
6.11. Customized Report Generation
7. Conclusions and Future Work
Abbreviations
| SYN | Synchronize |
| CR | Custom Reports |
| UP | User Profiling |
| CC | Common Criteria |
| FWS | Firewall Status |
| OS | Operating System |
| NF | Network Forensics |
| IP | Internet Protocol |
| PE | Policy Enforcement |
| SS | Scheduled Scanning |
| DNS | Domain Name System |
| TM | Traffic Monitoring |
| SD | Structured Database |
| IDSE | IDS/IPS Evaluation |
| VMD | Three letter acronym |
| RDS | Remote Desktop Status |
| VD | Vulnerability Detection |
| UDP | User Datagram Protocol |
| VMD | Virtual Machine Detection |
| VMD | Virtual Machine Detection |
| ARP | Address Resolution Protocol |
| TCP | Transmission Control Protocol |
| MPLS | Multiprotocol Label Switching |
| ICMP | Internet Control Message Protocol |
| RARP | Reverse Address Resolution Protocol |
| FIPS | Federal Information Processing Standard |
| NIST | National Institute of Standards and Technology |
References
- Douligeris, C.; Mitrokotsa, A. DDoS Attacks and Defense Mechanisms: Classification and State-of-the-Art. Computer Science Review 2022, 44, 100458. [Google Scholar] [CrossRef]
- Saleem, B.; Ahmed, M.; Zahra, M.; Hassan, F.; Iqbal, M.A.; Muhammad, Z. A survey of cybersecurity laws, regulations, and policies in technologically advanced nations: A case study of Pakistan to bridge the gap. International Cybersecurity Law Review 2024, 5, 533–561. [Google Scholar] [CrossRef]
- Muhammad, Z.; Straub, J. An Analysis of Cyber Threats and the Protective Role of Cyber Insurance in the US Market. In Proceedings of the World Congress in Computer Science, Computer Engineering & Applied Computing; Springer, 2024; pp. 259–272. [Google Scholar]
- Dissanayake, N.; Jayatilaka, A.; Zahedi, M.; Babar, M.A. Software security patch management-A systematic literature review of challenges, approaches, tools and practices. Information and Software Technology 2022, 144, 106771. [Google Scholar] [CrossRef]
- Rahman, A.; Kawshik, K.R.; Sourav, A.A.; Gaji, A.A. Advanced Network Scanning. American Journal of Engineering Research (AJER) 2016, 5, 38–42. [Google Scholar]
- Buczak, A.L.; Guven, E. A Survey of Data Mining and Machine Learning Methods for Cyber Security Intrusion Detection. IEEE Communications Surveys & Tutorials 2021, 23, 1121–1153. [Google Scholar]
- Taylor, R.W.; Fritsch, E.J.; Liederbach, J. Digital crime and digital terrorism; Prentice Hall Press, 2014. [Google Scholar]
- Zhang, C.; Hu, G.; Chen, G.; Sangaiah, A.K.; Zhang, P.; Yan, X.; Jiang, W. Towards a SDN-based integrated architecture for mitigating IP spoofing attack. IEEE Access 2017, 6, 22764–22777. [Google Scholar] [CrossRef]
- National Institute of Standards and Technology. Framework for Improving Critical Infrastructure Cybersecurity. 2018. [Google Scholar]
- Zenmap - Official cross-platform Nmap Security Scanner GUI.
- Sarker, I.H.; Kayes, A.; Badsha, S.; Alqahtani, H.; Watters, P.; Ng, A. Cybersecurity data science: An overview from machine learning perspective. Journal of Big data 2020, 7, 1–29. [Google Scholar] [CrossRef]
- Hamdani, S.W.A.; Abbas, H.; Janjua, A.R.; Shahid, W.B.; Amjad, M.F.; Malik, J.; Murtaza, M.H.; Atiquzzaman, M.; Khan, A.W. Cybersecurity standards in the context of operating system: Practical aspects, analysis, and comparisons. ACM Computing Surveys (CSUR) 2021, 54, 1–36. [Google Scholar] [CrossRef]
- Berardi, D.; Callegati, F.; Melis, A.; Prandini, M. Security network policy enforcement through a SDN framework. In Proceedings of the 2018 28th International Telecommunication Networks and Applications Conference (ITNAC). IEEE; 2018; pp. 1–4. [Google Scholar]
- Toyeer-E-Ferdoush; Rahman, H.; Hasan, M. A convenient way to mitigate DDoS TCP SYN flood attack. Journal of Discrete Mathematical Sciences and Cryptography 2022, 25, 2069–2077. [Google Scholar] [CrossRef]
- Jia, Y.J.; Chen, Q.A.; Lin, Y.; Kong, C.; Mao, Z.M. Open doors for bob and mallory: Open port usage in android apps and security implications. In Proceedings of the 2017 IEEE European Symposium on Security and Privacy (EuroS&P), 2017; pp. 190–203. [Google Scholar]
- Bhakthavatsalam, P.; Malarkodi, B. Analysis of network infrastructure threats using SonicWALL analyser. In Proceedings of the 2016 3rd International Conference on Devices, Circuits and Systems (ICDCS). IEEE; 2016; pp. 6–9. [Google Scholar]
- Rahman, A.; Kawshik, K.R.; Sourav, A.A.; Gaji, A.A. Advanced Network Scanning. American Journal of Engineering Research (AJER) 2016, 5, 38–42. [Google Scholar]
- Kumar, S. Classification and detection of computer intrusions. PhD thesis, Purdue University, 1995. [Google Scholar]
- Mohammed, S.A. Designing Rules to Implement Reconnaissance and Unauthorized Access Attacks for Intrusion Detection System. Iraqi Journal of Information & Communications Technology 2019, 2, 25–43. [Google Scholar]
- Shahid, J.Z.; Cimato, S.; Muhammad, Z. A Sharded Blockchain Architecture for Healthcare Data. In Proceedings of the 2024 IEEE 48th Annual Computers, Software, and Applications Conference (COMPSAC), 2024; pp. 1794–1799. [Google Scholar]
- Lichtblau, F.; Streibelt, F.; Krüger, T.; Richter, P.; Feldmann, A. Detection, classification, and analysis of inter-domain traffic with spoofed source IP addresses. In Proceedings of the 2017 Internet Measurement Conference, 2017; pp. 86–99. [Google Scholar]
- Singh, R.; Thakur, K.; Singh, G.; Gupta, S. Prevention of IP spoofing attack in cyber using artificial Bee colony and artificial neural network. In Proceedings of the Third International Conference on Advanced Informatics for Computing Research, 2019; pp. 1–10. [Google Scholar]
- Verisign.
- Deka, R.K.; Bhattacharyya, D.K.; Kalita, J.K. Granger Causality in TCP Flooding Attack. IJ Network Security 2019, 21, 30–39. [Google Scholar]
- Ahmed, A.A.; Zaman, N.A.K. Attack Intention Recognition: A Review. IJ Network Security 2017, 19, 244–250. [Google Scholar]
- Baishya, R.C.; Hoque, N.; Bhattacharyya, D.K. DDoS Attack Detection Using Unique Source IP Deviation. IJ Network Security 2017, 19, 929–939. [Google Scholar]
- Sattar, I.; Shahid, M.; Abbas, Y. A review of techniques to detect and prevent distributed denial of service (DDoS) attack in cloud computing environment. International Journal of Computer Applications 2015, 115. [Google Scholar] [CrossRef]
- Sun, J.R.; Hwang, M.S. A New Investigation Approach for Tracing Source IP in DDoS attack from Proxy Server. In Proceedings of the ICS; 2014; pp. 850–857. [Google Scholar]
- Jung, J.; et al. Real-time detection of malicious network activity using stochastic models. PhD thesis, Massachusetts Institute of Technology, 2006. [Google Scholar]
- Arshad, J.; Talha, M.; Saleem, B.; Shah, Z.; Zaman, H.; Muhammad, Z. A Survey of Bug Bounty Programs in Strengthening Cybersecurity and Privacy in the Blockchain Industry. Blockchains 2024, 2, 195–216. [Google Scholar] [CrossRef]
- Teodoro, N.; Gonçalves, L.; Serrão, C. NIST CyberSecurity Framework Compliance: A Generic Model for Dynamic Assessment and Predictive Requirements. In Proceedings of the 2015 IEEE Trustcom/BigDataSE/ISPA. IEEE, 2015; Vol. 1, pp. 418–425. [Google Scholar]
- OpenVAS. OpenVAS - Open Vulnerability Assessment Scanner. [Accessed: 2020-06-02].
- Irfan, M.; Ali, S.T.; Ijlal, H.S.; Muhammad, Z.; Raza, S. Exploring the synergistic effects of blockchain integration with IoT and AI for enhanced transparency and security in global supply chains.
- Islam, M.B.E.; Haseeb, M.; Batool, H.; Ahtasham, N.; Muhammad, Z. AI threats to politics, elections, and democracy: A blockchain-based deepfake authenticity verification framework. Blockchains 2024, 2, 458–481. [Google Scholar] [CrossRef]
- Daidone, F.; Carminati, B.; Ferrari, E. Blockchain-based privacy enforcement in the IoT domain. IEEE Transactions on Dependable and Secure Computing 2021, 19, 3887–3898. [Google Scholar] [CrossRef]
- Schiffman, M. The libnet packet construction library. The Million Packet March 2005. [Google Scholar]
- Liu, W. Design and implement of common network security scanning system. In Proceedings of the 2009 International Symposium on Intelligent Ubiquitous Computing and Education. IEEE, 2009; pp. 148–151. [Google Scholar]
- Calderon, P. Nmap Network Exploration and Security Auditing Cookbook: Network discovery and security scanning at your fingertips; Packt Publishing Ltd, 2021. [Google Scholar]
- Jacobson, V.; McCanne, S. libpcap: Packet capture library; Lawrence Berkeley Laboratory: Berkeley, CA.
- Shuguang, W.; Gaogang11, X. libpcap-MT: A General Purpose Packet Capture Library with Multi-Thread. Journal of Computer Research and Development 2011, 5, 756–764. [Google Scholar]
- McCanne, S.; Jacobson, V. The BSD Packet Filter: A New Architecture for User-level Packet Capture. In Proceedings of the USENIX winter, 1993; Vol. 46. [Google Scholar]
- Risso, F.; Degioanni, L. An architecture for high performance network analysis. In Proceedings of the Proceedings. Sixth IEEE Symposium on Computers and Communications. IEEE, 2001; pp. 686–693. [Google Scholar]
- Nmap: The Network Mapper.
- Shah, M.; Ahmed, S.; Saeed, K.; Junaid, M.; Khan, H.; et al. Penetration Testing Active Reconnaissance Phase–Optimized Port Scanning With Nmap Tool. In Proceedings of the 2019 2nd International Conference on Computing, Mathematics and Engineering Technologies (iCoMET). IEEE, 2019; pp. 1–6. [Google Scholar]
- Lyon, G. Nmap: The network mapper–Free security scanner. Nmap. org 2016. [Google Scholar]
- SolarWinds Network Management Tools.
- Dutta, N.; Jadav, N.; Dutiya, N.; Joshi, D. Using Honeypots for ICS Threats Evaluation. In Recent Developments on Industrial Control Systems Resilience; Springer, 2020; pp. 175–196. [Google Scholar]
- Phase, E. Scanning and Enumeration Phase. 2019. [Google Scholar]
- Advanced IP Scanner.
- Angry IP Scanner.
- Dandan, T. Angry IP Scanner. In Cyber security and information; 2017; p. 87. [Google Scholar]
- Free IP Scanner by Eusing.
- Baloch, R. Ethical hacking and penetration testing guide; CRC Press, 2017. [Google Scholar]
- The GNU Netcat.
- Kurth, M.; Gras, B.; Andriesse, D.; Giuffrida, C.; Bos, H.; Razavi, K. NetCAT: Practical Cache Attacks from the Network. 2020. [Google Scholar]
- LanSweeper IP Scanner.
- Erlandson, R. Finding Help and Keeping Up with Changing Technology in Libraries. Technology for Small and One-Person Libraries: A LITA Guide 2013, 21, 125. [Google Scholar]
- HAFSAOUI, M.A.; MANSOUR, H. D ’e development of a computer park management application. PhD thesis, Universit ’e Virtual of Tunis, 2019. [Google Scholar]
- MyLanViewer Network/IP Scanner.
- Garcia, H.C. About monitoring the confidentiality of computer systems. Mathematical machines and systems 2015. [Google Scholar]
- Dandan, T. LAN scan MyLanViewer. In Cyber security and information; 2017; p. 94. [Google Scholar]
- Nessus.
- Anderson, H. Introduction to nessus. SecurityFocus. Saatavilla wwwosoitteessa. 2003. Available online: http://www.securityfocus.com/infocus/1741.
- Wijaya, S.A.A. ATCS System Security Audit Using Nessus. ATCS 2017, 7. [Google Scholar]
- Josephlal, E.F.M.; Adepu, S. Vulnerability Analysis of an Automotive Infotainment System’s WIFI Capability. In Proceedings of the 2019 IEEE 19th International Symposium on High Assurance Systems Engineering (HASE). IEEE, 2019; pp. 241–246. [Google Scholar]
- Memon, I.; Shaikh, R.A.; Fazal, H.; Tunio, H.; Arain, Q.A. The World of Hacking: A Survey. University of Sindh Journal of Information and Communication Technology 2020, 4, 31–37. [Google Scholar]
- Zhang, W.; Banescu, S.; Pasos, L.; Stewart, S.; Ganesh, V. MPro: Combining Static and Symbolic Analysis for Scalable Testing of Smart Contract. arXiv 2019, arXiv:1911.00570. [Google Scholar]
- Singh, R.R.; Tomar, D.S. Network forensics: Detection and analysis of stealth port scanning attack. scanning 2015, 4, 8. [Google Scholar]
- Patel, S.K.; Sonker, A. Internet protocol identification number based ideal stealth port scan detection using snort. In Proceedings of the 2016 8th International Conference on Computational Intelligence and Communication Networks (CICN). IEEE, 2016; pp. 422–427. [Google Scholar]
- Coyle, S. Port Scanning Techniques Tools and Detection. 2024. [Google Scholar]
- Qureshi, M.A.; Ahmed, S.; Mehmood, A.; Shaheen, R.; Dildar, M.S. Vulnerability assessment of operating systems in healthcare: exploitation implications techniques and security. Health Sciences Journal 2024, 2, 104–111. [Google Scholar] [CrossRef]
- Mitre. Common Vulnerabilities and Exposures (CVE). [Accessed: 2020-07-29].
- Bonandir, A.; Yussof, S. An analysis of common vulnerability and exposure (CVE) of software products in the year 2016. International Journal of Advanced Science and Technology 2018, 112, 157–166. [Google Scholar] [CrossRef]
- Firewall.
| Name | FWS | RDS | VMD | UP | DI | CR | VD | NF | IDSE | SS | SD | PE | TM |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| NMAP | ✓ | ✗ | ✓ | ✓ | ✓ | ✗ | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ |
| SolarWinds Scanner | ✗ | ✓ | ✗ | ✗ | ✓ | ✓ | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ |
| Advanced IP Scanner | ✗ | ✓ | ✗ | ✗ | ✓ | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ |
| Angry IP Scanner | ✗ | ✓ | ✗ | ✗ | ✓ | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ |
| Eusing IP Scanner | ✓ | ✗ | ✗ | ✗ | ✓ | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ |
| NetCat | ✓ | ✓ | ✗ | ✗ | ✓ | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ |
| LanSweeper IP Scanner | ✓ | ✓ | ✓ | ✗ | ✓ | ✗ | ✓ | ✗ | ✗ | ✓ | ✗ | ✗ | ✗ |
| MyLanViewer | ✓ | ✓ | ✗ | ✓ | ✓ | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ |
| Slitheris Network Discovery | ✓ | ✗ | ✓ | ✓ | ✓ | ✗ | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ | ✗ |
| Proposed Advanced Scanner | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




