Submitted:
21 April 2025
Posted:
21 April 2025
You are already at the latest version
Abstract
Keywords:
1.0. Introduction

2.0. Problem Statement

3.0. Literature Review
3. Methodology
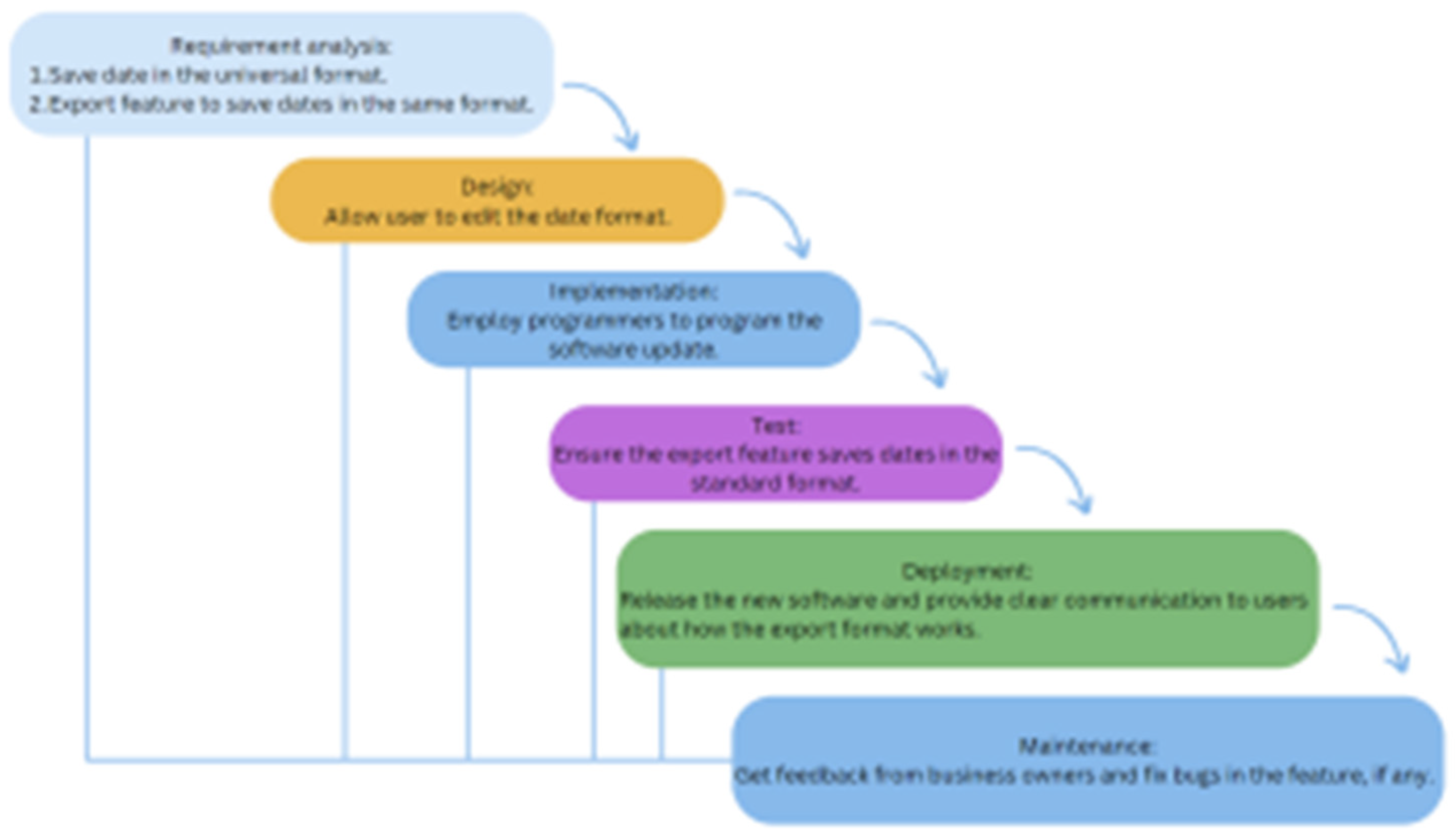
3.1. Standardizing CSV Date Format Using Waterfall Model
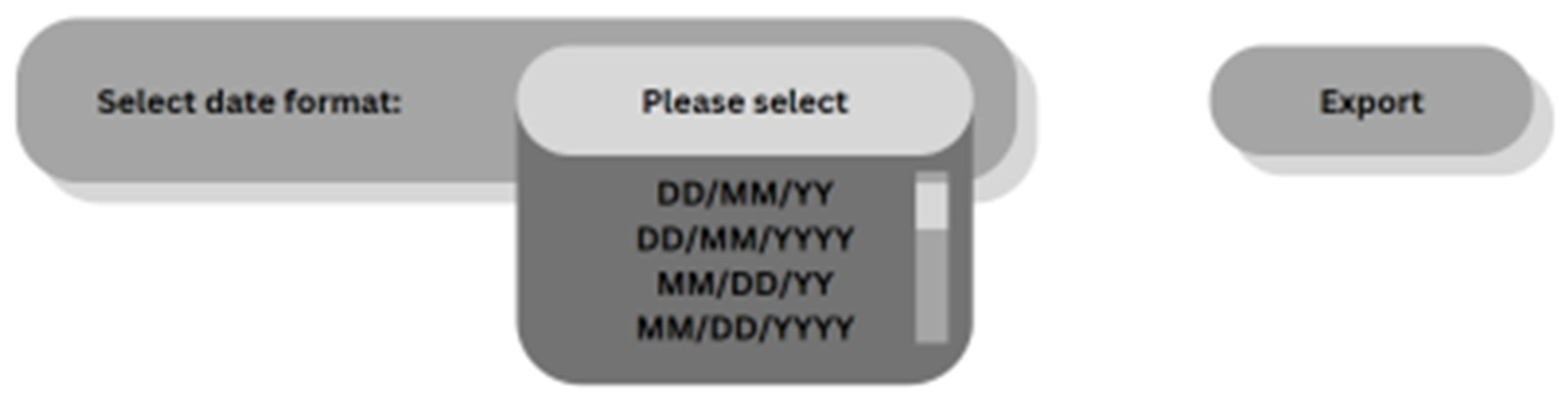
3.2. Enhancing the Graphical User Interface (GUI)
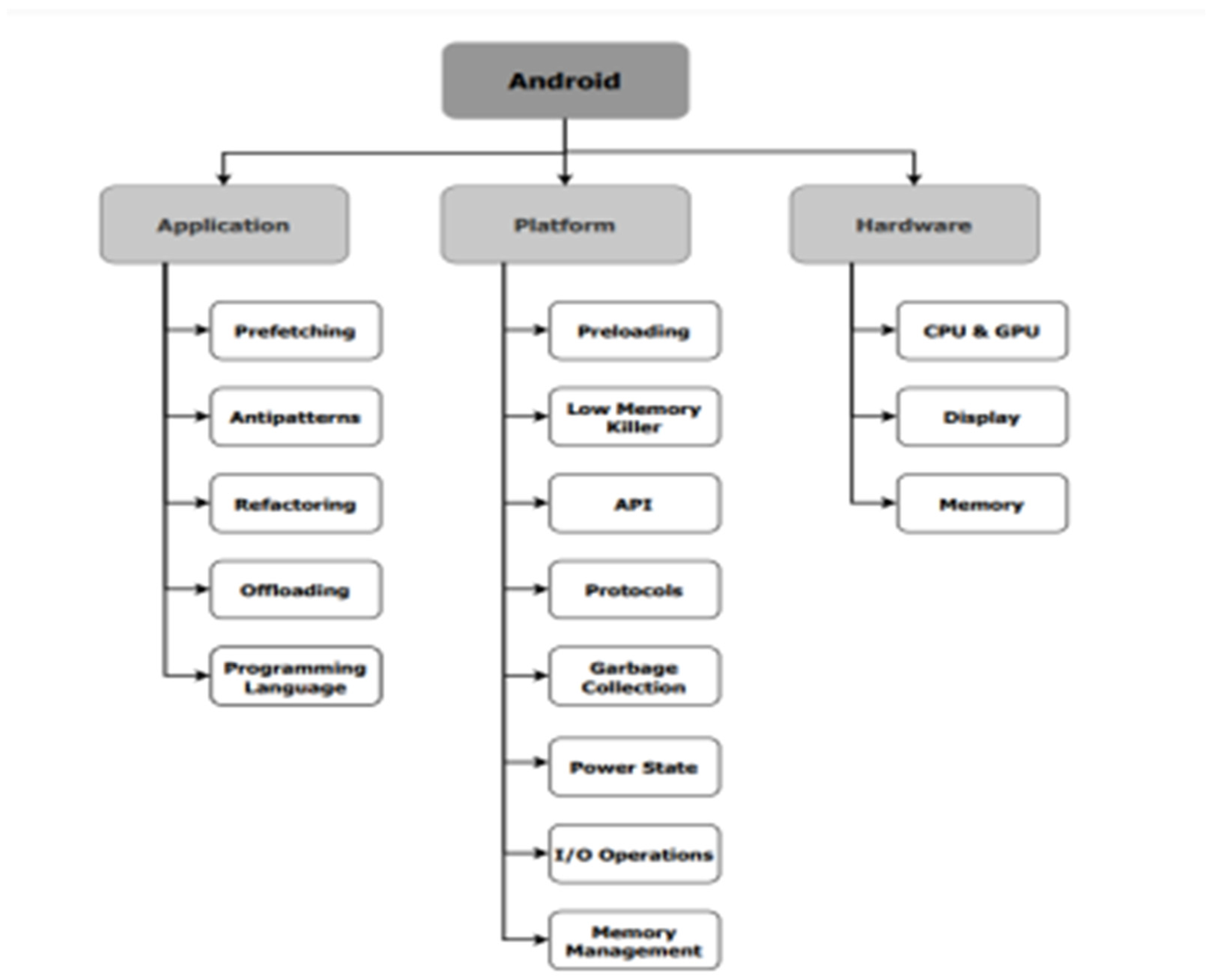
3.4. Android Compatibility Optimization
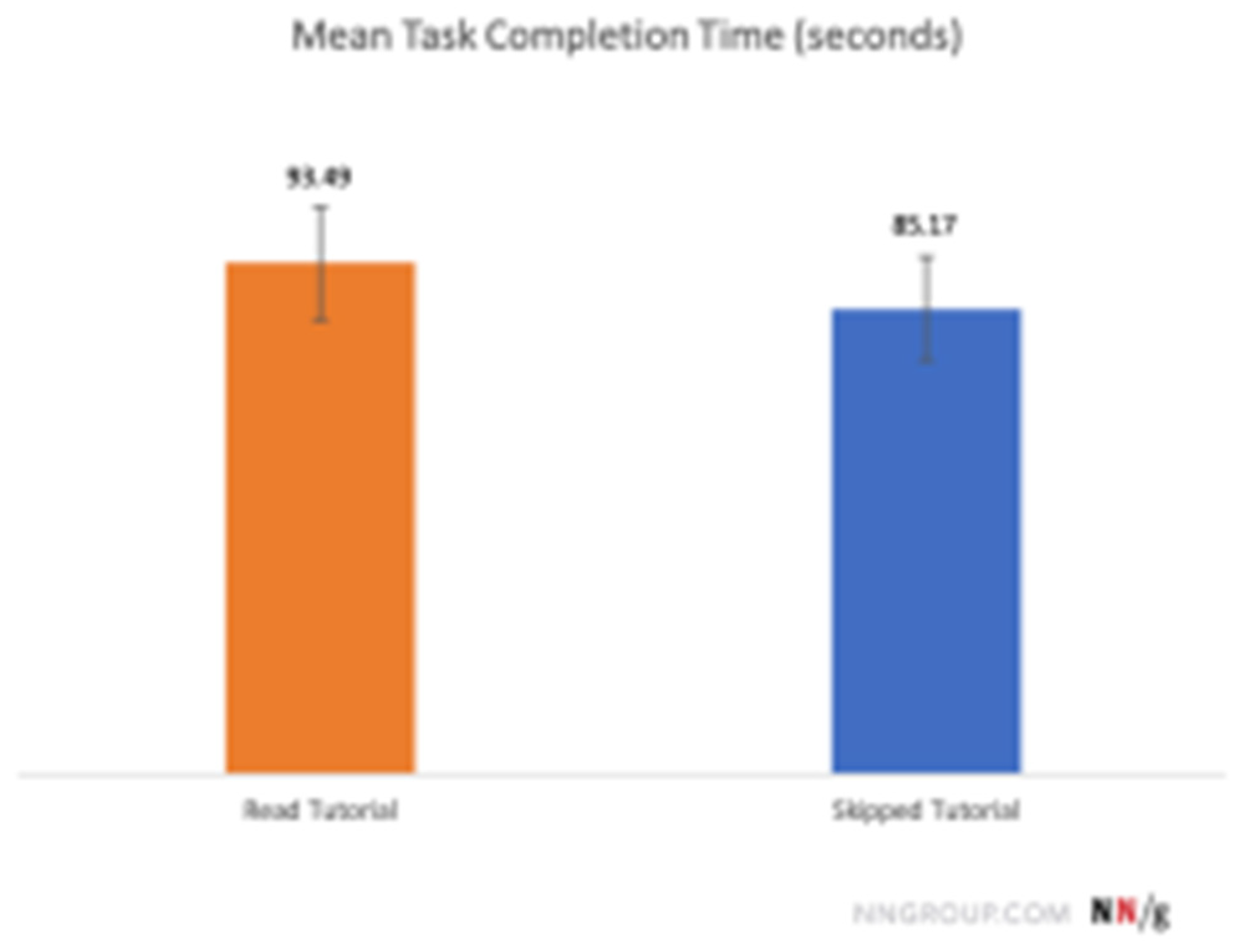
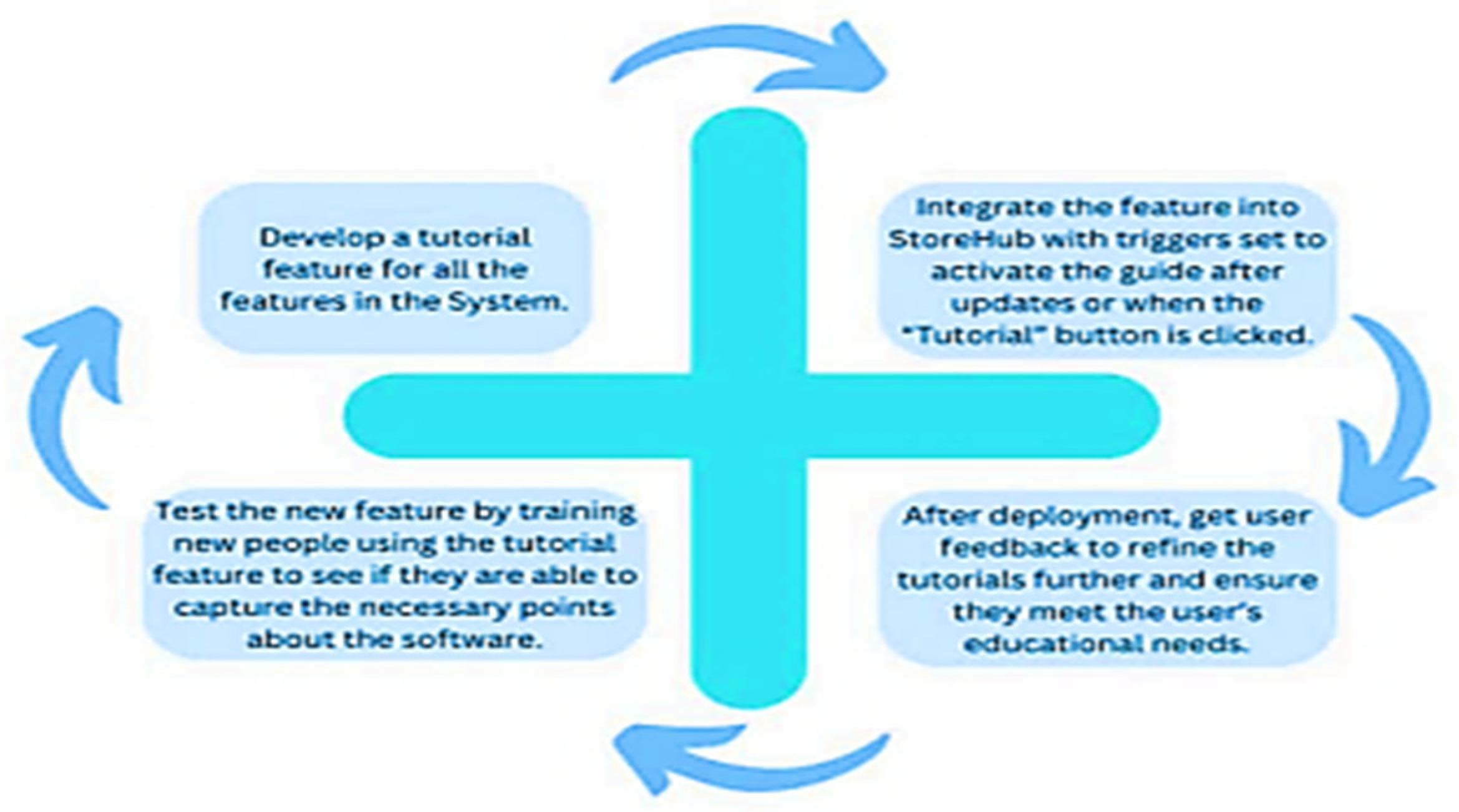
3.5. In-App Tutorial Integration Using Spiral Model
Facial Recognition-Based Attendance Verification
Multi-Factor Authentication (MFA) for System Security
Impact of Solution
4.1. Impact on Customers
4.2. Impact on Employees
4.3. Impact on Business Owners
4.4. Impact on Business Sector
5.0. System Viability
5.1. System Viability - Technically Viable
5.2. System Viability - Economically Viable
6.0. System Requirements
- Interview Candidate - Sate Hut
- Ethical Considerations
| Functional Requirement | Description |
|---|---|
| Sales Management | Handles transactions, print receipts, and applies discounts, promotions, and coupons during checkout. |
| Integration and Compatibility | Connects with other business tools like accounting software and e-commerce platforms and supports various hardware devices such as receipt printers and barcode scanners. |
| Security and Compliance | Secures user access through authentication and authorization, encrypts sensitive data (e.g., payment information), and enables tracking of system activities for compliance. |
| User Interface (UI) | Provides an easy-to-use interface for cashiers and managers, with fast product search during checkout and customizable layouts to meet specific business needs. |
| Multi-Language Support | Allows users to select their preferred language, ensuring that menus and prompts appear in the chosen language, facilitating communication in multilingual settings. |
7.0. Architectural overview
7.1. Platform
7.2. System Architecture
7.3. Modular vs Monolithic Approach
7.4. Technologies / Resources Used:
Future work
Conclusion
References
- Gavrila Gavrila, S., Blanco González-Tejero, C., Gómez Gandía, J. A., & de Lucas Ancillo, A. (2023). The impact of automation and optimization on customer experience: a consumer perspective. Humanities and Social Sciences Communications, 10(1), 1-10. [CrossRef]
- Sauro, J., & Lewis, J. R. (2016). Quantifying the user experience: Practical statistics for user research. Morgan Kaufmann.
- Joyce, A. (2020). Mobile tutorials: Wasted effort or efficiency boost?. Retrieved on, 1.
- Hort, M., Kechagia, M., Sarro, F., & Harman, M. (2021). A survey of performance optimization for mobile applications. IEEE Transactions on Software Engineering, 48(8), 2879-2904. [CrossRef]
- Fanti, M. (2023). Implementing Multifactor Authentication: Protect your applications from cyberattacks with the help of MFA. Packt Publishing Ltd.
- Alferidah, D. K., & Jhanjhi, N. Z. (2020, October). Cybersecurity impact over big data and IoT growth. In 2020 International Conference on Computational Intelligence (ICCI) (pp. 103–108). IEEE (Add DOI if available). [CrossRef]
- Jena, K. K., Bhoi, S. K., Malik, T. K., Sahoo, K. S., Jhanjhi, N. Z., Bhatia, S., & Amsaad, F. (2022). E-learning course recommender system using collaborative filtering models. Electronics, 12(1), 157. [CrossRef]
- Aherwadi, N., Mittal, U., Singla, J., Jhanjhi, N. Z., Yassine, A., & Hossain, M. S. (2022). Prediction of fruit maturity, quality, and its life using deep learning algorithms. Electronics, 11(24), 4100. [CrossRef]
- Kumar, M. S., Vimal, S., Jhanjhi, N. Z., Dhanabalan, S. S., & Alhumyani, H. A. (2021). Blockchain-based peer-to-peer communication in autonomous drone operation. Energy Reports, 7, 7925–7939. [CrossRef]
- Jhanjhi, N. Z., Humayun, M., & Almuayqil, S. N. (2021). Cybersecurity and privacy issues in industrial Internet of Things. Computer Systems Science & Engineering, 37(3), 357–368. [CrossRef]
- Lee, S., Abdullah, A., & Jhanjhi, N. Z. (2020). A review on honeypot-based botnet detection models for smart factory. International Journal of Advanced Computer Science and Applications, 11(6), 319–326. [CrossRef]
- Alappat, M. R. (2023). Multifactor authentication using zero trust. Rochester Institute of Technology.
- Narm, T. S., Hamidinezhad, H., Sabouri, Z., & Darroudi, M. (2024). Green synthesis of silver doped zinc oxide/magnesium oxide nanocomposite for waste water treatment and examination of their cytotoxicity properties. Heliyon, 10(9). [CrossRef]
- Osman, S., Shariff, S. H., & Lajin, M. N. A. (2016). Does innovation contribute to employee performance? Procedia - Social and Behavioral Sciences, 219, 571–577.
- Ashfaq, F., Jhanjhi, N. Z., & Khan, N. A. (2023, April). Badminton player’s shot prediction using deep learning. In Innovation and Technology in Sports: Proceedings of the International Conference on Innovation and Technology in Sports,(ICITS) 2022, Malaysia (pp. 233-243). Singapore: Springer Nature Singapore.
- Ashfaq, F., Jhanjhi, N. Z., Khan, N. A., & Das, S. R. (2023, February). Synthetic crime scene generation using deep generative networks. In International Conference on Mathematical Modeling and Computational Science (pp. 513-523). Singapore: Springer Nature Singapore.
- Alourani, A., Ashfaq, F., Jhanjhi, N. Z., & Ali Khan, N. (2023). BiLSTM-and GNN-Based Spatiotemporal Traffic Flow Forecasting with Correlated Weather Data. Journal of Advanced Transportation, 2023(1), 8962283. [CrossRef]
- Saeed, S., Abdullah, A., Jhanjhi, N. Z., Naqvi, M., & Humayun, M. (2020). Statistical analysis of the pre-and post-surgery in the healthcare sector using high dimension segmentation. In Machine Learning for Healthcare (pp. 159-174). Chapman and Hall/CRC.
- Saleh, M., Jhanjhi, N., & Abdullah, A. (2020, February). Fatima-tuz-Zahra,‘‘Proposing a privacy protection model in case of civilian drone,’’. In Proc. 22nd Int. Conf. Adv. Commun. Technol.(ICACT) (pp. 596-602).
- Kaur, N., Verma, S., Jhanjhi, N. Z., Singh, S., Ghoniem, R. M., & Ray, S. K. (2023). Enhanced QoS-aware routing protocol for delay sensitive data in Wireless Body Area Networks. IEEE Access, 11, 106000-106012. [CrossRef]
- Singh, T., Solanki, A., Sharma, S. K., Jhanjhi, N. Z., & Ghoniem, R. M. (2023). Grey Wolf Optimization-Based CNN-LSTM Network for the Prediction of Energy Consumption in Smart Home Environment. IEEE Access, 11, 114917-114935. [CrossRef]
- Saeed, S., Jhanjhi, N. Z., Naqvi, S. M. R., & Khan, A. (2022). Analytical Approach for Security of Sensitive Business Cloud. Deep Learning in Data Analytics: Recent Techniques, Practices and Applications, 257-266.
- Srinivasan, K., Garg, L., Chen, B. Y., Alaboudi, A. A., Jhanjhi, N. Z., Chang, C. T., ... & Deepa, N. (2021). Expert System for Stable Power Generation Prediction in Microbial Fuel Cell. Intelligent Automation & Soft Computing, 30(1). [CrossRef]
- Javed, D., Jhanjhi, N. Z., Khan, N. A., Ray, S. K., Al Mazroa, A., Ashfaq, F., & Das, S. R. (2024). Towards the future of bot detection: A comprehensive taxonomical review and challenges on Twitter/X. Computer Networks, 254, 110808. [CrossRef]
- Aldughayfiq, B., Ashfaq, F., Jhanjhi, N. Z., & Humayun, M. (2023, April). Yolo-based deep learning model for pressure ulcer detection and classification. In Healthcare (Vol. 11, No. 9, p. 1222). MDPI. [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




