Submitted:
27 February 2025
Posted:
27 February 2025
You are already at the latest version
Abstract
Keywords:
I. Introduction
II. Background Study
| Aspect | Opportunities | Challenges | Ref |
| Enhancing Clinical Decision-Making | Improves treatment recommendations and epidemic outbreak predictions through real-time data analysis. | Integrating diverse data sources such as patient history and genetic information. | [20] |
| Addressing Complex Cybersecurity Threats | Enables early detection and mitigation of vulnerabilities such as XSS and XSRF through dynamic ML models. | Constantly updating models to address evolving threats and ensure data security. | [19] |
| Optimizing Healthcare Operations | Reduces human errors and streamlines medical imaging and patient record management. | Managing noisy data and maintaining operational efficiency at scale. | [20] |
| Quantum Machine Learning Applications | Accelerates algorithms for disease diagnosis and medical imaging through quantum routines | Limited quantum infrastructure and complexity in translating medical data to quantum states. | [17] |
| Reducing Costs in Healthcare | Leverages ML technologies to interpret large datasets, aiding in distinguishing treatment options while reducing costs. | Balancing the cost of implementing ML technologies with achieving measurable outcomes. | [16] |
| Addressing Vulnerabilities in Interconnected Infrastructures | Proposes a scalable and adaptable blockchain model to enhance real-time protection of sensitive patient information and improve vulnerability assessments, yielding better outcomes through the integration of machine learning. | Requires continuous monitoring and adaptation to mitigate risks in outdated and interconnected infrastructures. | [1] |
III. Emerging Threats in Healthcare Domain
| Ref. | Threat type | Threat Insight 1 | Threat Insight 2 |
| [21] | Internal Threats - Healthcare Critical Infrastructure | Attack on the UK National Health Service wannaCry ransomware. | Major theoretical shortfall in current cyber defense architecture. |
| [22] | Security Threats - Healthcare Internet of Things | Open-area deployment & wireless communication security challenge. | Accumulated data sharing and unstructured communication |
| [23] | Security Threats - Wireless Body Area Networks (WBANs) | WBAN devices with limited computational resources are prone to cyberattacks, including data manipulation, denial-of-service (DoS) attacks, and medical information interception. | The absence of robust cryptographic protections and continuous authentication, coupled with the cascading impact of device compromises across networks, threatens critical healthcare operations. |
| [24] | Security Threats - Healthcare Cybersecurity Challenges | The high value of patient records ($50 per record) on the illicit market makes healthcare institutions prime targets for ransomware attacks, data breaches, and system outages. Attackers range from small-time hackers to nation-state actors, motivated by financial gain. | Weaknesses in legacy systems, underfunded IT infrastructure, and poor security practices create vulnerabilities in healthcare systems, exposing them to both targeted ransomware and untargeted attacks exploiting interconnected system flaws. |
| [25] | Internal Threats - Electronic Health Records, IoMT, & BYOD | Critical infrastructures such as electronic health records (EHRs), Internet of Medical Things (IoMT), and connected devices are prime targets for cyberattacks due to their high-value data and operational importance. Emerging risks include vulnerabilities in outdated systems, insider threats, and ransomware attacks disrupting critical medical services. | The proliferation of bring-your-own-device (BYOD) policies, unencrypted storage of sensitive data, and reliance on unsecured networks amplify the risk, making healthcare systems more vulnerable to advanced persistent threats (APTs) and multi-layered attacks targeting human, organizational, and technical layers of security. |
IV. Vulnerability Assessment via ML
V. Patient Data, Patient Safety, and Cyber-attacks
| SN | Data Breaches | Cyberattacks on Patient data and healthcare | Year |
| 1. | Dutch government data lost | Loses hard drive with data of 6.9 million registered donors, from Dutch Minister of Health, Wellness | 2020 |
| 2. | Cense AI medical data leak | Artificial Intelligence company, Cense AI leaks over 2.5 million medical records, publicly visible on the internet | 2020 |
| 2. | Indonesia’s health agency | Personal information of 279 million Indonesians (data stored by BPJS Kesehatan, country’s healthcare and social security agency) | 2021 |
| 3. | Contact tracing Info | Exposed data was all stored in Microsoft’s PowerApps portal service, 38 million records on open internet | 2021 |
| 4. | FlexBooker appointing scheduling breach | Over 3.7 million accounts impacted, US-based appointment scheduling service stolen in cyberattack | 2022 |
| 5. | Maximus zero-day flaw | US government service contractor, having sponsored-programs, federal & local healthcare programs, disclosed data breach of 8 - 11 million people | 2023 |
| 6. | Sav-Rx prescription data breach | Prescription management company, Sav-Rx, impacting 2.8 million Americans, personal data was stolen | 2023 |
| 7. | Welltok data breach | 8.5 million US patients, Healthcare SaaS provider Welltok, file transfer was hacked in data theft attack | 2023 |
| 8. | TIAA data breach | Financial organization, TIAA provides retirement plans, life insurance, 2.3 million individuals, exposed personal information via unauthorized party access | 2023 |
| 9. | Kaiser Permanente data transmitted | Leading healthcare organization in US, Kaiser Permanente, disclosed data breach impacting 13.4 million of its patients and members | 2024 |
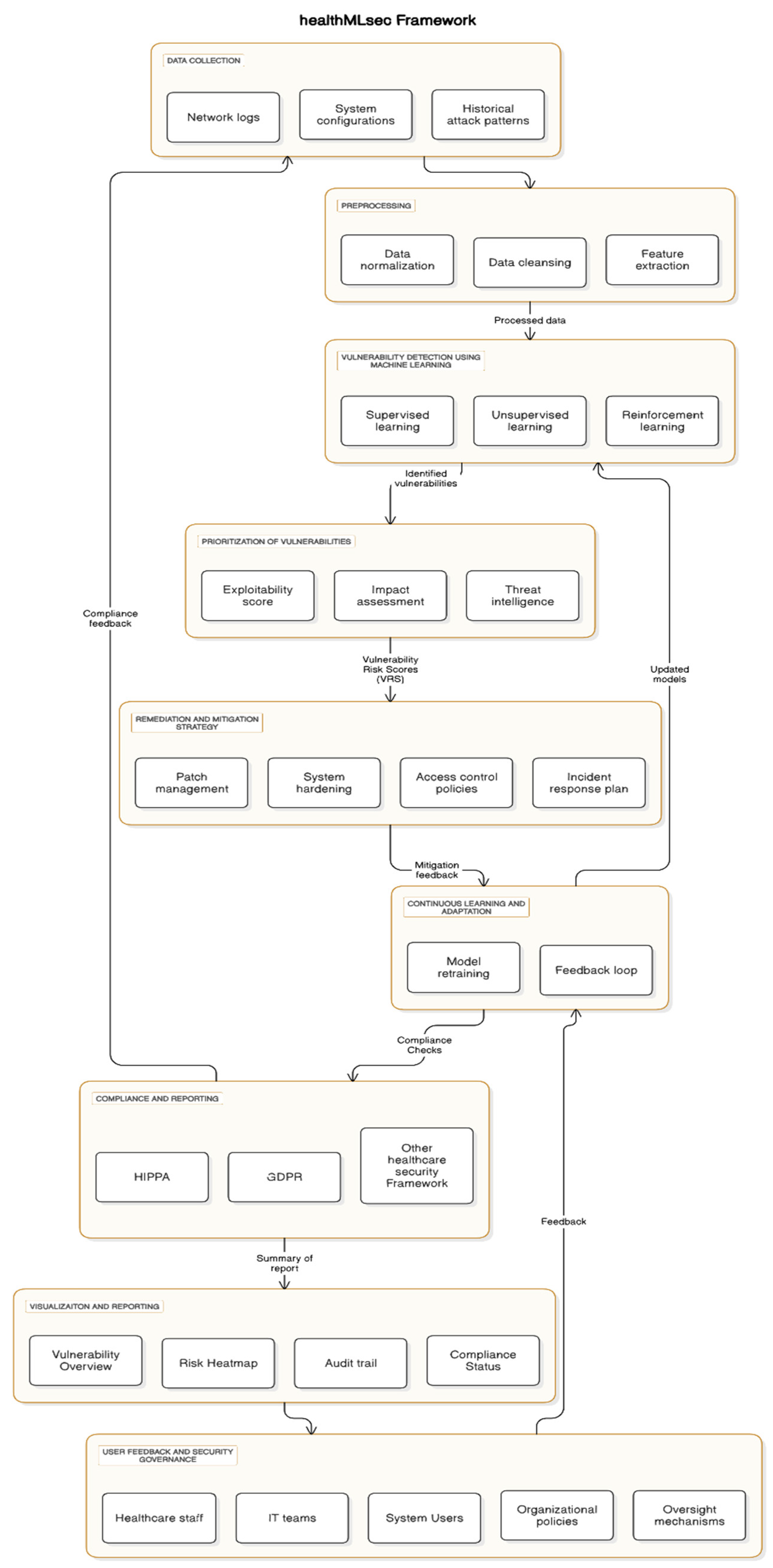
VI. Proposed Framework – healthMLsec
6.1. Data Collection and Preprocessing
6.2. Vulnerability Detection Using Machine Learning
- Supervised Learning Models: These models, such as Random Forests, Support Vector Machines (SVM), and Neural Networks, are trained on historical attack data to identify known attack signatures and vulnerabilities [37].
- Unsupervised Learning Models: Clustering algorithms like K-means or anomaly detection methods are employed to discover novel vulnerabilities that may not have been previously documented [19].
- Reinforcement Learning: In dynamic environments, reinforcement learning can adapt and improve vulnerability detection by learning from new data and constantly evolving threats [38].
6.3. Prioritization of Vulnerabilities
- Exploitability Score: How likely a vulnerability is to be exploited based on historical data and current system configuration [39].
- Impact Assessment: Evaluating the potential consequences of a vulnerability being exploited, such as data breaches, system downtime, or patient safety risks [40].
- Threat Intelligence: Integrating up-to-date threat intelligence feeds to assess the current threat landscape and adjust vulnerability priorities accordingly [41].
6.4. Remediation and Mitigation Strategy
- Patch Management: Ensuring security patches and updates are applied to vulnerable systems promptly.
- System Hardening: Modifying system configurations to reduce the attack surface, such as disabling unnecessary services or closing unused ports.
- Access Control Policies: Strengthening access control and authentication mechanisms to limit unauthorized access to critical systems [42].
- Incident Response Plan: If a breach or attack is detected, the framework guides the development of an incident response plan to mitigate the damage and prevent future occurrences.
6.5. Continuous Learning and Adaptation
- Model Retraining: Periodically retraining the machine learning models with new attack data to improve accuracy and relevance [43].
- Feedback Loop: Integrating feedback from security incidents and remediation actions into the system to enhance its predictive capabilities.
6.6. Compliance and Regulatory Standards
6.7. Visualization and Reporting
- Vulnerability Overview: A summary of detected vulnerabilities, their risk levels, and their current remediation status.
- Risk Heat Map: A visual representation of the system’s security landscape, highlighting areas of high vulnerability.
- Audit Trail: A record of all remediation actions taken, ensuring traceability and accountability.
- Compliance Status: A summary of how well the organization is meeting regulatory requirements.
6.8. User Feedback and Security Governance
- User Feedback: Collected via surveys and secure reporting portals, it refines ML models and addresses usability challenges.
- Security Governance: Establishes policies, roles, and mechanisms to monitor threats, conduct audits and mitigate risks [44].
VII. Conclusion
References
- Kshetri, N. , Mishra, R., Rahman, M. M., & Steigner, T. (2024). HNMblock: Blockchain Technology Powered Healthcare Network Model for Epidemiological Monitoring, Medical Systems Security, and Wellness. [CrossRef]
- Privacy Rights Clearinghouse. “Data Breaches | Privacy Rights Clearinghouse.” Privacy Rights.org, 2020, privacyrights.
- Verizon. (2018). 2018 Data Breach Investigations Report. Verizon Enterprise Solutions. https://www.verizon.com/business/resources/reports/DBIR_2018_Report.pdf.
- Alder, Steve. “19 Healthcare Data Breach Report.” HIPAA Journal, 21 Jan. 2020, www.hipaajournal.com/december-2019-healthcare-data-breach-report/. 20 December.
- IBM. (2020). How much would a data breach cost your business? Retrieved January 12, 2020, from https://www.ibm.com/security/data-breach.
- HIPAA Journal. (2020). 2019 cost of a data breach study reveals increase in U.S. healthcare data breach costs. Retrieved February 15, 2020, from https://www.hipaajournal.com/2019-cost-of-a-data-breach-studyhealthcare-data-breach-costs/.
- Wikina, S. B. (2014). What caused the breach? An examination of use of information technology and health data breaches. Perspectives in Health Information Management, 11, 1–16.
- Ponemon Institute. (2015). 2015 cost of data breach study: Global analysis. Retrieved February 28, 2020, from https://www.ponemon.org/local/upload/file/2015%20Global%20CODB%20FINAL%203%20copy.pdf.
- IBM. (2019). 2019 cost of a data breach report. Retrieved February 17, 2020, from https://www.ibm.com/downloads/cas/ZBZLY7KL.
- Verizon. “2024 Data Breach Investigations Report.” Verizon Business, 2024, www.verizon.com/business/resources/reports/dbir/.
- Rajawat, A. S. , Goyal, S. B., Bedi, P., Jan, T., Whaiduzzaman, M., & Prasad, M. (2023). Quantum machine learning for security assessment in the Internet of Medical Things (IoMT). Future Internet.
- Linardos, V. , Drakaki, M., Tzionas, P., & Karnavas, Y. L. (2022). Machine learning in disaster management: recent developments in methods and applications. Machine Learning and Knowledge Extraction.
- Danso, P. K. , Dadkhah, S., Neto, E. C. P., Zohourian, A., Molyneaux, H., Lu, R., & Ghorbani, A. A. (2023). Transferability of machine learning algorithm for IoT device profiling and identification. IEEE Internet of Things Journal.
- Balantrapu, S. S. (2023). Future Trends in AI and Machine Learning for Cybersecurity. International Journal of Creative Research In Computer Technology and Design.
- Ozkan-Ozay, M. , Akin, E., Aslan, Ö., Kosunalp, S., Iliev, T., Stoyanov, I., & Beloev, I. (2024). A Comprehensive Survey: Evaluating the Efficiency of Artificial Intelligence and Machine Learning Techniques on Cyber Security Solutions. IEEE Access.
- Bhardwaj, R. , Nambiar, A. R., & Dutta, D. (2017, July). A study of machine learning in healthcare. In 2017 IEEE 41st annual computer software and applications conference (COMPSAC) (Vol. 2, pp. 236-241). IEEE.
- Rani, S. , Pareek, P. K., Kaur, J., Chauhan, M., & Bhambri, P. (2023, February). Quantum machine learning in healthcare: Developments and challenges. In 2023 IEEE International Conference on Integrated Circuits and Communication Systems (ICICACS) (pp. 1-7). IEEE.
- Rani, Sita, et al. “Federated Learning for Secure IoMT-Applications in Smart Healthcare Systems: A Comprehensive Review.” Knowledge-Based Systems, 22 May 2023, p. 110658, www.sciencedirect.com/science/article/pii/S0950705123004082. [CrossRef]
- Kshetri, N. , Kumar, D., Hutson, J., Kaur, N., & Osama, O. F. (2024, April). algoXSSF: Detection and analysis of cross-site request forgery (XSRF) and cross-site scripting (XSS) attacks via Machine learning algorithms. In 2024 12th International Symposium on Digital Forensics and Security (ISDFS) (pp. 1-8). IEEE.
- Javaid, M. , Haleem, A., Singh, R. P., Suman, R., & Rab, S. (2022). Significance of machine learning in healthcare: Features, pillars, and applications. International Journal of Intelligent Networks.
- Walker-Roberts, S. , Hammoudeh, M., & Dehghantanha, A. (2018). A systematic review of the availability and efficacy of countermeasures to internal threats in healthcare critical infrastructure. ( 6, 25167–25177.
- Adil, M. , Khan, M. K., Kumar, N., Attique, M., Farouk, A., Guizani, M., & Jin, Z. (2024). Healthcare internet of things: Security threats, challenges, and future research directions. IEEE Internet of Things Journal.
- Mucchi, L. , Jayousi, S., Martinelli, A., Caputo, S., & Marcocci, P. (2019, May). An overview of security threats, solutions, and challenges in wbans for healthcare. In 2019 13th International Symposium on Medical Information and Communication Technology (ISMICT) (pp. 1-6). IEEE.
- Le Bris, A. , & El Asri, W. (2016). State of cybersecurity & cyber threats in healthcare organizations. ESSEC Business School.
- Spanakis, E. G. , Bonomi, S., Sfakianakis, S., Santucci, G., Lenti, S., Sorella, M.,... & Magalini, S. (2020, July). Cyber-attacks and threats for healthcare–a multi-layer thread analysis. In 2020 42nd Annual International Conference of the IEEE Engineering in Medicine & Biology Society (EMBC) (pp. 5705-5708). IEEE.
- Buczak, A. L. , & Guven, E. (2016). A survey of data mining and machine learning methods for cyber security intrusion detection. IEEE Communications Surveys & Tutorials. [CrossRef]
- Kumar Singh, Dr. S. , Vadi, Dr. V. R., Usmani, Dr. A., & Nayak, Dr. P. (2024). Algorithms of machine learning for cloud computing security. IMRJR. [CrossRef]
- Sommer, R. , & Paxson, V. (2010). Outside the closed world: On using machine learning for network intrusion detection. 2010 IEEE Symposium on Security and Privacy. [CrossRef]
- Shah, I. A., Jhanjhi, N. Z., & Brohi, S. N. (2024). Machine learning models for detecting software vulnerabilities. Advances in Web Technologies and Engineering, 1–40.
- Thawait, N. K. (2024). Machine learning in cybersecurity: Applications, challenges, and Future Directions. International Journal of Scientific Research in Computer Science, Engineering, and Information Technology. [CrossRef]
- Meisner, M. (2017). Financial consequences of cyber-attacks leading to data breaches in healthcare sector. Copernican Journal of Finance & Accounting.
- Pycroft, L. , & Aziz, T. Z. (2018). Security of implantable medical devices with wireless connections: The dangers of cyber-attacks. Expert Review of Medical Devices.
- Kavitha, A., Rao, B. S., Akthar, N., Rafi, S. M., Singh, P., Das, S., & Manikandan, G. A Novel Algorithm to Secure Data in New Generation Health Care System from Cyber Attacks Using IoT. International Journal of Electrical and Electronics Research (IJEER) 2022, 10, 270–275.
- Information is Beautiful, World’s Biggest Data Breaches & Hacks, Selected events over 30,000 records stole, https://informationisbeautiful.net/visualizations/worlds-biggest-data-breaches-hacks/.
- Bhardwaj, R., Nambiar, A. R., & Dutta, D. (2017). A study of machine learning in Healthcare. 2017 IEEE 41st Annual Computer Software and Applications Conference (COMPSAC), 236–241. [CrossRef]
- Rani, S. , Kumar Pareek, P., Kaur, J., Chauhan, M., & Bhambri, P. (2023). Quantum machine learning in Healthcare: Developments and challenges. 2023 IEEE International Conference on Integrated Circuits and Communication Systems (ICICACS). [CrossRef]
- Linardos, V. , Drakaki, M., Tzionas, P., & Karnavas, Y. (2022). Machine learning in disaster management: Recent developments in methods and applications. Machine Learning and Knowledge Extraction. [CrossRef]
- Rajawat, A. S. , Goyal, S. B., Bedi, P., Jan, T., Whaiduzzaman, M., & Prasad, M. (2023). Quantum Machine Learning for Security Assessment in the internet of medical things (IOMT). Future Internet. [CrossRef]
- Walker-Roberts, S., Hammoudeh, M., & Dehghantanha, A. A systematic review of the availability and efficacy of countermeasures to internal threats in healthcare critical infrastructure. IEEE Access 2018, 6, 25167–25177. [CrossRef]
- Adil, M., Khan, M. K., Kumar, N., Attique, M., Farouk, A., Guizani, M., & Jin, Z. (2024). Healthcare internet of things: Security threats, challenges, and future research directions. IEEE Internet of Things Journal 2024, 11, 19046–19069. [CrossRef]
- Spanakis, E. G. , Bonomi, S., Sfakianakis, S., Santucci, G., Lenti, S., Sorella, M., Tanasache, F. D., Palleschi, A., Ciccotelli, C., Sakkalis, V., & Magalini, S. (2020). Cyber-attacks and threats for healthcare – a multi-layer thread analysis. 2020 42nd Annual International Conference of the IEEE Engineering in Medicine & Biology Society (EMBC). [CrossRef]
- Javaid, M. , Haleem, A., Pratap Singh, R., Suman, R., & Rab, S. (2022). Significance of machine learning in Healthcare: Features, pillars, and applications. International Journal of Intelligent Networks. [CrossRef]
- Danso, P. K., Dadkhah, S., Pinto Neto, E. C., Zohourian, A., Molyneaux, H., Lu, R., & Ghorbani, A. A. Transferability of machine learning algorithm for IOT device profiling and identification. IEEE Internet of Things Journal 2024, 11(2), 2322–2335. [CrossRef]
- Argaw, S. T. , Troncoso-Pastoriza, J. R., Lacey, D., Florin, M.-V., Calcavecchia, F., Anderson, D., Burleson, W., Vogel, J.-M., O’Leary, C., Eshaya-Chauvin, B., & Flahault, A. (2020). Cybersecurity of hospitals: Discussing the challenges and working towards mitigating the risks. BMC Medical Informatics and Decision Making. [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




