Submitted:
18 February 2025
Posted:
19 February 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
- Additional costs are involved due to inefficient utilization of bandwidth and network resources,
- Large-sized data drastically degrades network performance,
- Billions of connected devices on IoT network make it difficult to manage data traffic, and
1.1. Methodology
1.2. Motivation
1.3. Comparison with Existing Literature
1.4. Novelty and Contribution
- We present a summary, as well as detailed scrutiny and analysis of security and privacy-related issues about EC-assisted IoT services. Also, security objectives and functions on EC-based IoT applications are discussed.
- A classification of data security threats and attacks due to poor design approaches, miss configurations, and implementation flaws is discussed. Also, appropriate mitigation techniques for the detection and prevention of attacks are covered.
- Detailed taxonomy of PUF classification based on silicon and non-silicon-based fabrication is presented, as well as significant performance and quality matrices are discussed.
- A comprehensive summary of AI/ ML-based cryptography techniques for the mitigation of data security and privacy threats is presented. Also, the significance of reliable data sets and training data for the development of accurate ML algorithms is presented in this survey.
- A discussion about future security research goals, privacy-related open challenges, and deeper insights into future research directions in the context of the EC-based IoT ecosystem.
2. Edge Computing
- Processing the sensed data away from the central cloud or data center in real-time.
- Caching, buffering, and optimization of the data close to edge nodes.
- Transforms raw data from edge nodes into a format that can be processed for further deeper analysis.
2.1. Edge Architecture
2.2. Edge Computing Challenges
- Heterogeneity Many hardware devices and communication standards of diverse natures are deployed at edge networks [101]. EC exhibits heterogeneity across multiple dimensions, including hardware architecture, operating systems, programming languages, accessibility, and the nature of tasks [102]. First, edge devices are diverse, generating data in various formats. Second, data is transmitted through various network access technologies, including 3G, 4G, 5G, WiFi, WiMAX, and LPWAN technologies like Sigfox [103]. Third, the heterogeneous edge nodes providing services encompass a variety of devices such as end-user devices, access points, routers, and switches [53,96].
- Coordination between communication and computing The integration of EC into IoT systems adds significant complexity due to the diverse resource constraints and operational requirements of edge servers and IoT devices [101]. Mobile edge computing (MEC) is a computing model that extends cloud computing to the network’s edge [104]. Researchers are exploring the integration of Low Earth Orbit (LEO) satellites with MEC’s for low latency computing offloading services by placing MEC servers on LEO satellites [105] as well as collaborative MEC’s among connected entities [106]. Network slicing divides a single physical network into multiple virtualized, independent, and tailored networks, aligning with the distributed models of EC. It is managed through the combined optimization of computing and communication resources in EC environments [107].
- Partitioning and Offloading Tasks The computational tasks are divided into smaller sub-tasks and routed these tasks for processing either locally on the edge device or offloaded to more powerful edge servers or the cloud. The overall system performance is enhanced by partitioning and offloading tasks while optimally balancing computing and communication resources [108]. Task offloading is a comprehensive process involving application partitioning, decision-making regarding offloading, and executing tasks scattered across the system [109]. The main challenges in designing partitioning and offloading algorithms involve determining the optimal granularity for partitioning, managing resource limitations, adapting to dynamic environments, and addressing the complexity of offloading within blockchain-enabled communication systems [108]. In an MEC system with multiple edge nodes (EN) serving multiple users, user association is pivotal in shaping the task partitioning strategy, necessitating the joint optimization of task partitioning and user association [110].
- Security and privacy issues EC is vulnerable to access control, identity authentication, information security, and privacy protection-related threats [111]. EC characteristics like geographic distribution, heterogeneity, lower latency, lack of standardized protocols, and operating software expand its attack surface [53,60,101]. Conventional security mechanisms such as attribute or group-signature-based access control, homomorphic encryption, and public-key-based authentication require higher computational ability and storage [112]. Securing edge environments is significantly different from traditional IT security. Implementing security measures on edge devices can potentially hinder their internal operations, impacting the real-time capabilities of edge computing. As a result, a key challenge in edge computing is finding the right balance between minimizing latency and meeting security requirements [113]. Edge operations are typically time-sensitive, safety-critical, and autonomous. The security models implemented in EC networks must accommodate factors such as longer device lifespans and support for legacy infrastructure. Quick patching may not always be possible, particularly if updates require reboots, which could jeopardize safety [114].
- Monitoring, Accounting, and Billing It is important to continuously monitor the usage of EC resources, account keeping, and billing-related data for better QoS and charging for EC services. Traditional monitoring and accounting methods typically rely on monitoring interfaces on physical nodes, utilizing hardware probes, and correlating data with control plane and management plane information. However, these approaches often neglect the requirements of the distributed nature intrinsic in an edge environment. A sustainable business model for EC services is needed for monitoring, accounting, and billing purposes. Creating a robust business model proves to be quite challenging due to the mobile nature of users and the limited scope of services. The key focus for EC lies in enhancing resource utilization to its fullest extent and effectively monetizing these resources [115,116].
3. Security and Privacy Challenges
- Transmission: Jamming attacks, sniffing attacks, worm propagation, distributed denial-of-service (DDoS), and similar assaults can disrupt data links by choking the network or observing the data flow.
- Storage: Innumerable sensors and devices produce a gigantic volume of data, which is then stored across various third-party locations. Such arrangement poses issues like, data integrity being seriously challenged due to the distribution of data into many fractions resulting in data packet losses as well as data corruption. Also, adversaries can modify or abuse stored data at third-party locations, leading to data leakage and other privacy issues.
- Computation: The relocation of computational tasks from the cloud to edge nodes in EC demands an establishment of trust between edge servers and end devices.
3.1. Classification of Edge Computing Security Threats
3.2. Mitigation Strategies Against EC Security Challenges
| Strategy | Network layer | Limitations |
|---|---|---|
| Cryptographic Schemes | Communication Layer | Power inefficient, computational ability, storage, etc. |
| Secured data aggregation, deduplication, analysis | Data layer | Consume power, render sensitive data to intruders’ network bandwidth |
| Combined with Blockchain | Architecture layer | Complex system more computing capability |
| Intrusion Detection System (IDS) | Communication Layer | Resource consumption |
| Type of threat | Description | Mitigation strategies |
|---|---|---|
| Hardware or software malware | Unauthorized hardware or software are injected into the edge network that attacks edge servers or devices. Such malware/ trojans interrupt network services and attackers gain control over edge devices and their data. | Side-channel signal analysis, Trojan activation methods, and circuit modification or replacement are the techniques utilized in hardware security [144]. |
| Physical Tampering & Attacks | Attackers may exploit physical access to EC nodes/ devices to extract significant and sensitive cryptographic data, manipulate circuits, and alter or corrupt the software and operating systems. | Techniques such as system analysis and self-destruction are employed to inhibit or alleviate the destructive effects of physical altering and attacks. |
| Routing Information Attacks | Data throughput, latency, and data paths over a network get affected due to routing attacks. Examples of routing information attacks include black holes, grey holes, wormholes, hello flood, etc. | Monitoring malicious traffic and detecting policy violations can serve as effective countermeasures. |
| Distributed Denial of Service (DDoS) Attacks | The continuous transmission of junk data packets toward the target node can exhaust all resources allocated for handling the malicious data packets. This may result in genuine requests getting dropped due to the overload of the target node’s resources. [60]. Three significant DDoS attacks on edge computing devices are outage attacks, sleep deprivation attacks, and battery-draining attacks. | The Detect-and-filter technique is a tool against flooding attacks. Also, behavior control of devices and policy-based mechanisms within the network can mitigate DDoS attacks. |
| Privacy Leakage | Privacy Leakage in EC mainly involves three separate classes of privacy concerns i.e., data privacy, location privacy, and identity privacy. Attackers might exploit the location awareness of EC nodes to detect and track device status or to get access to classified data, posing further risks to privacy. | To address privacy concerns in EC, a privacy-preserving algorithm can be implemented between the cloud server and the edge server or between the end nodes and the edge server. [145]. |
| Eavesdropping or Sniffing | An intruder listens over communication channels to gain access to private data, like the physical location of specific nodes, access or control information of the EC node like node identification or node configuration, message identities (IDs), timestamps, usernames, and passwords. | Data encryption technique at edge nodes with asymmetric AES algorithm before the transmission on vulnerable channels, the realization of the connection between the edge nodes and edge server, and authentication service between the transmitting and receiving points could overcome eavesdropping attacks. [10]. |
| Jamming Attacks | The attacker transmits a wide range of signals with a similar frequency, potentially disrupting network security. Also, it triggers unintentional interference in wireless networks due to induced noise and collisions. | The significant transmission parameters like the signal strength of data packets at the physical layer and the packet loss ratio at the application layer serve as indicators of potential jamming attacks. [146]. |
| Integrity Attacks Against Machine Learning | ML techniques utilized in EC-assisted Internet of Things (IoT) are susceptible to two different categories of data security attacks. Causative attacks involve manipulating and injecting misleading training datasets to compromise the training process of ML models and, Exploratory attacks where adversaries exploit vulnerabilities. | Researchers propose the use of virtual machines (VMs) with boundaries for running ML processes, hence accelerating the testing and deployment of ML models, and systematic study of attacks in simulated environments, or sandboxes [147,148]. |
- Cryptographic schemes: The edge layer which includes local data centers, as well as sensing devices, is vulnerable to security threats. These edge devices need cybersecurity solutions within limited storage and computation capabilities. A Zero-Trust approach is recommended for securing data in the EC paradigm with an assumption that all devices have been compromised and all access has to be strictly monitored and authenticated. The standard encryption/decryption methods are memory and computing exhaustive [128]. ISO/IEC 29192, Lightweight cryptography is a cryptographic algorithm meant for implementation in constrained environments including RFID tags, sensors, contactless smart cards, healthcare devices, etc., for the protection of communication protocols.
-
Secured data aggregation, deduplication, analysis: Data aggregation is a method of clustering the data from various edge nodes by reducing the number of transfers and hence eliminating redundancy. Secure Data Aggregation (SDA) is a highly secure, privacy-preserving, and efficient data compression technique using homomorphic encryption against security attacks such as eavesdropping and forging. The secure deduplication technique removes matching copies of data while supporting data security. It employs Convergent Encryption (CE) for encrypting or decrypting data at the file level, along with a convergent key. [129]. Load distribution is used in EC for even distribution of computational, network traffic, data storage, and security-related tasks across edge devices, edge servers, and the cloud. Thus, load distribution prevents edge devices or servers from getting overwhelmed by diverse tasks while ensuring key security measures like encryption, intrusion detection, and access control are in place. Neto et. al., estimated an optimal number of edge nodes that can be assigned to a particular edge server using equation 1 and further used it in estimating its security factor [130].represents the number of edge devices associated with a particular edge server. Thus, the percentage of devices assigned to edge server i is found by dividing by the total number of devices . is the min-max normalized security Key Performance Indicator (KPI) while regulates priority metrics.
-
Combined with Blockchain: The advantage of implementing blockchain with EC is that it can offer secure data transfer and processing without needing a centralized server by deploying distributed ledger technology. Blockchain governs protocols that collaboratively make judgments involving transaction execution, exercising mechanisms such as voting and consensus algorithms. [7]. Blockchain is a distributed and secured ledger technology based on the zero-trust architecture, offering a strong shield against data privacy and security threats [131]. Blockchains are integrated into EC that documents transactions in an increasing chain of blocks [132,133]. As shown in Figure 9, each block is connected to the previous one by referencing its cryptographic hash value, except the first block, the genesis block. Each block contains a significant piece of information like the previous hash, timestamp, counter-like mechanism for every hash estimation called a nonce, Merkle root representing hash of all the transaction hashes, and transactions (Tx) for a specific time [134]. Consensus algorithms enthuse trust in the network through an agreement among the validated nodes while deciding to generate newer blocks into the blockchain [33].Medhane et. al. proposed a blockchain-enabled Platform-as-a-Service (PaaS) model that ensures data integrity and security of mobile users in an IoT environment [135]. The behavior detection of blockchain nodes using a technique called T2A2vec is carried out by [136] by extracting node account features, transaction time, transaction type, and transaction amount. T2A2vec technique counters tampering of transaction records and carries out authentication of blockchain nodes. BeCome is a blockchain-enabled computation offloading measure used by [137] to ensure data integrity in EC. Also, a nondominated sorting genetic algorithm III (NSGA-III), additive weighting (SAW), and multicriteria decision-making (MCDM) are proposed for optimal resource allocation and offloading strategy. Jangirala et. al. have adopted Lightweight Blockchain-enabled RFID-based Authentication Protocol for Supply Chains (LBRAPS) offers secured and real-time authentication through the integration of blockchain, RFID techniques, and 5G MEC [138]. A decentralized and tamper-proof system using Vickrey-Clarke-Groves (VCG) auction theory is proposed for inducing trust in a collaborative EC while optimizing resource allocation and load balancing [139]. A blockchain-based secured data aggregation (BSDA) approach is used in mobile data collectors (MDCs) for task management and framing of block generation rules [31]. Cheng et. al. integrated blockchain, certificateless cryptography, elliptic curve cryptography, and pseudonym-based cryptography methods in a mutual authentication scheme between the edge servers and devices citecheng2021blockchain. Electronic Health Record (EHR) security is ensured by integrating blockchains in EC while storing users’ data locally on edge devices [140]. A blockchain user or miner estimates a hash value by solving a compute-intensive proof of work (PoW) linking any two immediate blocks after neighboring miners reach a consensus. However, roadblocks are met in resource-limited nodes of the EC network unable to undertake mining and consensus process [141].
- Intrusion Detection System (IDS): In EC networks, intrusion detection systems (IDS) can play a critical role in detecting malicious actions or attacks. IDS investigates data traffic and resource utilization, issues alerts when suspicious behavior is detected. IDS can be characterized into two groups based on their intrusion detection strategies: signature-based and anomaly-based. Signature-based IDS cross-checks monitored events with a database of known intrusion techniques to identify potential threats. In contrast, anomaly-based IDS learn the normal activities of the system and report any abnormalities or inconsistent events [142]. Spadaccino et. al. and Gyamfi et. al. discuss supervised and unsupervised ML models for IDS, for the detection of anomalies in IoT networks, and deployment challenges of this ML on constrained edge devices [75,78]. A signature and anomaly-based Secured Edge Computing Intrusion Detection System (SEC-IDS) framework is proposed by [77] for improved intrusion detection. A hybrid LDA-LR (Linear Discriminant Analysis-Logistic Regression) edge computing model is proposed in [143], utilizing machine learning and an IDS.
3.3. AI Role in EC Security
3.3.1. Machine Learning for Data Security and Privacy
3.3.2. Federated Learning
3.3.3. Multi-Access Edge Computing
3.3.4. Data Anonymisation Techniques
- Data masking: Data masking is a technique of concealing data by creating faux versions of sensitive user data by modifying private information. The process involves modification techniques like shuffling, modest word or character substitution, encryption, or masking data. Common types of data masking are static, dynamic, and on-the-fly data masking.
- Pseudonymization: Pseudonymization removes user identifiers from the data set and replaces them with pseudonyms which hides the data source identity. Pseudonymization is defined in the EU-General Data Protection Regulation (GDPR) as “the processing of personal data in such a manner that the personal data can no longer be attributed to a specific data subject without the use of additional information. Such additional information is kept separately and is subject to technical and organizational measures to ensure that the personal data are not attributed to an identified or identifiable natural person.” [182].
- Generalization: It’s a technique of eliminating identifiable aspects of data to fully remove or reduce its identifiability. Generalization picks up a distinguishable identifier and abstracts it into a more general, lesser distinguishable value. Multiple levels of generalization do exist based on the type of data. An example of a generalization technique is bucketing that group records into smaller buckets and minimizes the risk of data security challenges[183].
- Perturbation Methods: It involves mathematical techniques for the protection of user data privacy. A controlled noise or randomness is added to the data while still able to perform data analysis. These data privacy technique is used in various application domains, including ML, statistics, and cryptography. Another method called the differential privacy technique adds a random noise scaled by a privacy parameter to the original data values.
3.3.5. Intrusion Detection System
- Issue alerts: This class of responses comes from passive IDS systems that issue security alerts via email or text messages. Also, a notification is issued to the security information and event management (SIEM) system, which helps security teams detect user behavior anomalies and apply AI for threat detection and incident response.
- Countermeasure: In this class, Active IDS not only sends alerts, but takes countermeasures like change in access control lists on firewalls to block the suspicious traffic, kill communication-related processes, and redirect traffic to a legitimate part of the network while assessing the threat.
- Signature Based: In this method, network packets are analyzed for attack signatures i.e., unique characteristics or behaviors linked to specific threats. The network traffic patterns are compared with attack signatures identified in the past and saved in an internal database. If a packet matches one of the stored signatures, the IDS alerts it. However, signature databases must be updated from time to time with new threat patterns to be effective against ever-evolving cyber threats.
- Anomaly Based: In this method, the ML approach creates and regularly updates a baseline model of normal network activity. Further, the network activity is compared with the baseline model. It raises alerts if the process uses more bandwidth than usual, or if a device opens a port that is usually closed or has unusual conditions.
- Specification Based: It’s a combination of the previous two methods which consumes more energy and resources to identify new attacks.
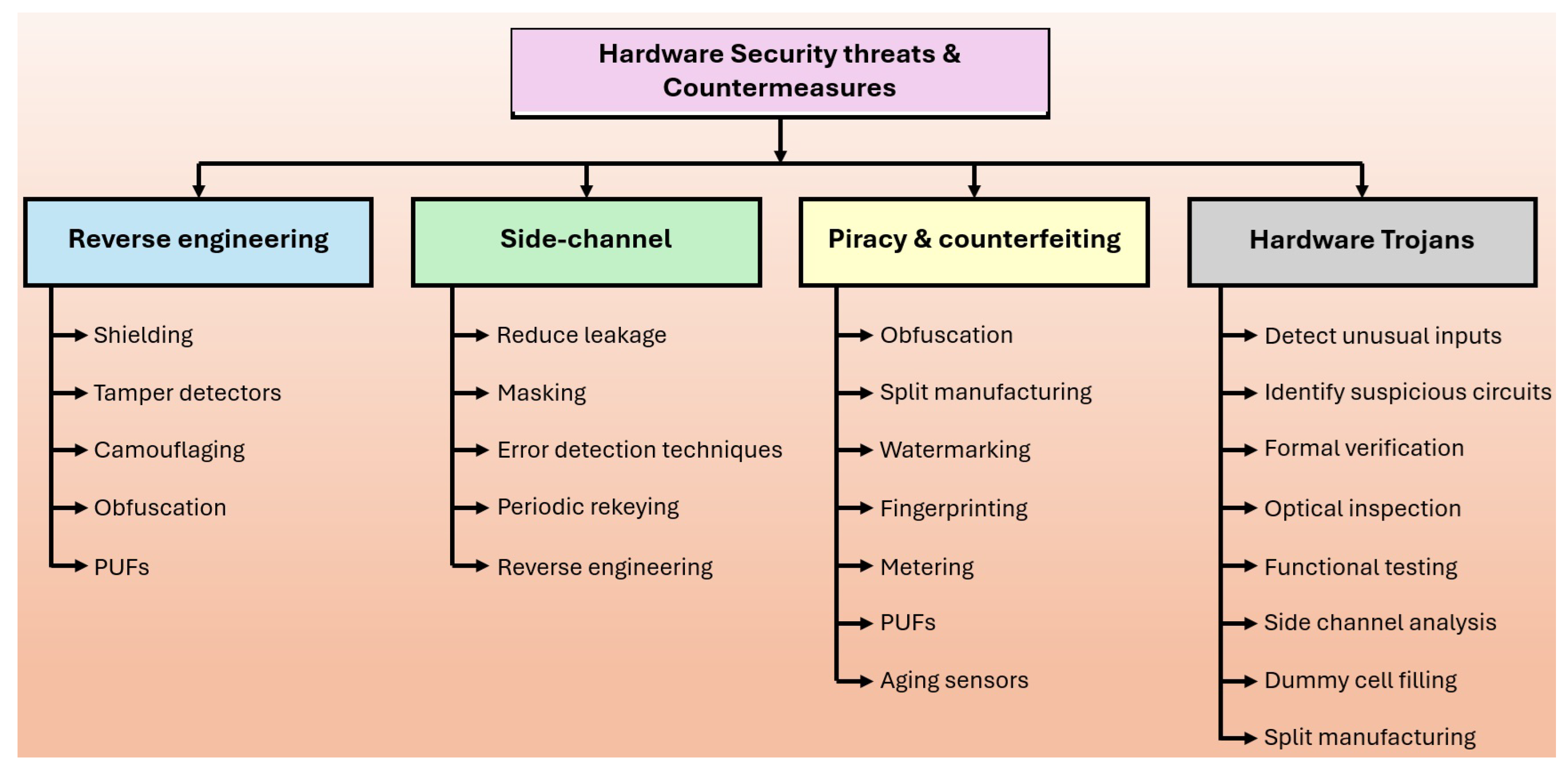
4. Hardware Security
4.1. Physical Unclonable Functions (PUFs)
4.1.1. Application of PUFs
- Identification is an act of claiming identity with a set of attributes, both physical and perceptual, that uniquely define a specific entity. Similar to a biometrical identification scheme, PUF response identification can be used to identify the ICs uniquely. A large range of CRPs is stored in the database along with the device ID implemented with the PUF during enrollment. The verifier chooses a CRP from the CRP database. The identification is considered successful if the obtained response and the CRP database output for a specific input are identical.
- Authentication is an act of identity confirmation based on presented attributes. PUFs generate a secure key from intrinsic and inherent entropies created due to variations in the fabricating process. No standard non-volatile storage is needed as randomness is built-in inside a chip and assures extra protection against the side channel and probing attacks.
- SRAM PUFs, RO PUFs, etc., can generate random numbers with slight modifications in their architecture and find their application in real, or cryptographically secure, random number generators.
- Potential vulnerabilities like copying or reverse engineering can destroy devices’ intrinsic and inherent characteristics and thus modify their output. PUFs are suitable for the generation of secrets in cryptography as they are not kept on the hardware and get generated dynamically at device reset.
4.1.2. PUF Performance Indicators
4.1.3. PUFs as a Root of Trust
4.1.4. Integration of FPGAs Based PUFs with Edge AI
- Model Optimizer converts models from various frameworks like Caffe, TensorFlow, Open Neural Network Exchange (ONNX), and Kaldi to intermediate representation format for faster inference.
- Inference Engine reads the IR format and supports heterogeneous execution across different hardware architectures such as CPU, GPU, Integrated GPU, etc.
- Model Zoo is a common interface for heterogeneous hardware that contains examples to get started with OpenVINO quickly.
5. Open Research Issues
- Heterogeneous EC architecture: The users in a traditional cloud computing approach are masked from hardware in place and how software/ applications performance depends on hardware resources. EC introduces complexity and a need for multi-layered security schemes because of an assortment of standards and protocols [269]. It introduces the need for unique data propagation management schemes among the heterogeneous edge devices [126]. Data privacy is achievable through encryption techniques, but EC architecture makes the existing encryption schemes too cumbersome for the limited processing resources [270].
- Dynamic resources allocation: Contrarily to cloud computing, the resources in the EC network are rather limited; thus, static allocation techniques cannot achieve optimal resource utilization. The dynamic allocation of computing and storage resources in a distributed EC network remains a bigger challenge. The resource allocation strategy in EC is important for ensuring efficient and effective use of resources and maintaining the quality of service (QoS) for applications that demand real-time data processing and low-latency response. The task of partitioning in EC not only poses the challenge of optimal partitioning but also faces challenges in dynamic resource allocation without the computational, storage capacity, or location of edge nodes.
- Data abstraction: The edge node needs a certain amount of training data to carry out analysis tasks. Data abstraction carries out data preprocessing techniques like noise cancellation, data classification, and data computation. Heterogeneous devices use different data formats and data security algorithms cannot be fed with a complete set of raw data, but it should only abstract the relevant part. Storage is a limiting factor while selecting the size of raw data and prediction accuracy. The selection of an optimal data abstraction technique is not easy because of the heterogeneity of devices, different data formats, and different corresponding operations.
- Secured EC nodes: Devices in an EC network need a foolproof access control and an end-to-end threat protection mechanism. Edge security refers to device security, network security, data security, and application-level security focused mainly on the protection and privacy of user data. Mitigation strategies include first the risks definition, uncompromised device functionality, multiuser edge node security, and minimal service levels at user nodes.
- Federated learning (FL): FL refers to a secured ML technique in a distributed environment comprising scattered edge devices or servers while ensuring the user data does not leave the source premises [271]. The research for full-proof privacy and attack mitigation techniques remains a focus of FL. In addition to data security challenges, the communication overhead of FL is comparable to computational overhead. The two significant attacks against FL are poisoning attacks and byzantine attacks. The poisoning attack includes the act of tampering, destroying, or corrupting the edge data used in local training or model generation [272]. Poisoning attacks are relevant to a single edge node or a server, while byzantine attacks are prevalent in the collusion of multi-users distributed learning environment [273].
6. Conclusion
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| AES | Advanced Encryption Key Standard |
| AMQP | Advanced Message Queuing Protocol |
| BR-PUF | Bistable ring PUF |
| CN-PUF | Carbon nanotube-based PUF |
| CO-PUF | Computational optical PUF |
| CRP | Challenge Response Pair |
| DDoS | Distributed Denial-of-Service |
| DL | Deep Learning |
| DP | Differential Privacy |
| DPU | Deep Learning Processor Unit |
| EC | Edge Computing |
| FL | Federated Learning |
| GDPR | General Data Protection Regulation |
| HD | Hamming Distance |
| HE | Homomorphic Encryption |
| HMAC | Hash Message Authentication Code |
| ICN | Information-Centric Networking |
| IDS | Intrusion Detection System |
| MCC | Mobile Cloud Computing |
| MEC | Multi-Access Edge Computing |
| MECCA-PUF | Memory Cell-based Chip Authentication PUF |
| ML | Machine Learning |
| MNO | Mobile Network Operators |
| MQTT | Message Queue Telemetry Transport |
| MVL-PUF | Multiple-valued logic PUF |
| NEM-PUF | Nano-electromechanical PUF |
| ONNX | Open Neural Network Exchange |
| OpenVINO | Open Visual Inference and Neural Network Optimization |
| PE-PUF | Process and environmental PUF |
| PH-PUF | Photonic PUF |
| PRISMA | Preferred Reporting Items for Systematic Reviews and Meta-Analyses |
| PUFs | Physically Unclonable Functions |
| RF-DNA-PUF | Radio-frequency certificates of authenticity |
| RRAM-PUF | reconfigurable resistive RAM PUF |
| RTMS | Realtime Traffic Monitoring Systems |
| SAC | Strict Avalanche Condition |
| SASE | Secure Access Service Edge |
| SC-PUF | ScanPUF |
| SDN | Software Defined Networking |
| SEACOD | Selective Encryption and Component-Oriented Deduplication |
| TERO-PUF | Transient effect ring oscillator PUF |
| VMs | Virtual Machines |
| WBI | Web-Based Intermediaries |
References
- IMD. What is the internet of things (IoT) & why is it important? https://www.imd.org/blog/digital-transformation/internet-of-things/, year = 2024 (accessed September 17, 2024).
- Vailshery, L.S. Number of IoT connections worldwide 2022-2033. https://www.statista.com/statistics/1183457/iot-connected-devices-worldwide/, year = 2024 (accessed September 17, 2024).
- Albreem, M.A.; Sheikh, A.M.; Alsharif, M.H.; Jusoh, M.; Mohd Yasin, M.N. Green Internet of Things (GIoT): Applications, Practices, Awareness, and Challenges. IEEE Access 2021, 9, 38833–38858. [Google Scholar] [CrossRef]
- sptel. Future Development of IoT in Singapore – 2024 & Beyond. https://sptel.com/future-development-of-iot/, year = 2024 (accessed September 15, 2024).
- Sheikh, A.M.; Islam, M.R.; Habaebi, M.H.; Kabbani, A.; Zabidi, S.A.; bin Najeeb, A.R. Securing the IoT Edge Devices Using Advanced Digital Technologies. Asian Journal of Electrical and Electronic Engineering 2024, 4, 52–60. [Google Scholar] [CrossRef]
- Yu, W.; Liang, F.; He, X.; Hatcher, W.G.; Lu, C.; Lin, J.; Yang, X. A survey on the edge computing for the Internet of Things. IEEE access 2017, 6, 6900–6919. [Google Scholar] [CrossRef]
- Alwarafy, A.; Al-Thelaya, K.A.; Abdallah, M.; Schneider, J.; Hamdi, M. A survey on security and privacy issues in edge-computing-assisted internet of things. IEEE Internet of Things Journal 2020, 8, 4004–4022. [Google Scholar] [CrossRef]
- Shi, W.; Cao, J.; Zhang, Q.; Li, Y.; Xu, L. Edge computing: Vision and challenges. IEEE Internet of Things journal 2016, 3, 637–646. [Google Scholar] [CrossRef]
- Shi, W.; Dustdar, S. The Promise of Edge Computing. Computer 2016, 49, 78–81. [Google Scholar] [CrossRef]
- Yahuza, M.; Idris, M.Y.I.B.; Wahab, A.W.B.A.; Ho, A.T.; Khan, S.; Musa, S.N.B.; Taha, A.Z.B. Systematic review on security and privacy requirements in edge computing: State of the art and future research opportunities. IEEE Access 2020, 8, 76541–76567. [Google Scholar] [CrossRef]
- Shi, W.; Dustdar, S. The promise of edge computing. Computer 2016, 49, 78–81. [Google Scholar] [CrossRef]
- Mukherjee, M.; Matam, R.; Shu, L.; Maglaras, L.; Ferrag, M.A.; Choudhury, N.; Kumar, V. Security and privacy in fog computing: Challenges. IEEE Access 2017, 5, 19293–19304. [Google Scholar] [CrossRef]
- Chen, B.; Wan, J.; Celesti, A.; Li, D.; Abbas, H.; Zhang, Q. Edge Computing in IoT-Based Manufacturing. IEEE Communications Magazine 2018, 56, 103–109. [Google Scholar] [CrossRef]
- Premsankar, G.; Di Francesco, M.; Taleb, T. Edge computing for the Internet of Things: A case study. IEEE Internet of Things Journal 2018, 5, 1275–1284. [Google Scholar] [CrossRef]
- Mo, W.; Wang, T.; Zhang, S.; Zhang, J. An active and verifiable trust evaluation approach for edge computing. Journal of Cloud Computing 2020, 9, 1–19. [Google Scholar] [CrossRef]
- Liao, H.; Zhou, Z.; Zhao, X.; Zhang, L.; Mumtaz, S.; Jolfaei, A.; Ahmed, S.H.; Bashir, A.K. Learning-based context-aware resource allocation for edge-computing-empowered industrial IoT. IEEE Internet of Things Journal 2019, 7, 4260–4277. [Google Scholar] [CrossRef]
- Zhang, J.; Chen, B.; Zhao, Y.; Cheng, X.; Hu, F. Data security and privacy-preserving in edge computing paradigm: Survey and open issues. IEEE access 2018, 6, 18209–18237. [Google Scholar] [CrossRef]
- Rupanetti, D.; Kaabouch, N. Combining Edge Computing-Assisted Internet of Things Security with Artificial Intelligence: Applications, Challenges, and Opportunities. Applied Sciences 2024, 14, 7104. [Google Scholar] [CrossRef]
- Xiao, Y.; Jia, Y.; Liu, C.; Cheng, X.; Yu, J.; Lv, W. Edge computing security: State of the art and challenges. Proceedings of the IEEE 2019, 107, 1608–1631. [Google Scholar] [CrossRef]
- Yao, A.; Li, G.; Li, X.; Jiang, F.; Xu, J.; Liu, X. Differential privacy in edge computing-based smart city Applications: Security issues, solutions and future directions. Array 2023, 19, 100293. [Google Scholar] [CrossRef]
- Rao, F.Y.; Bertino, E. Privacy techniques for edge computing systems. Proceedings of the IEEE 2019, 107, 1632–1654. [Google Scholar] [CrossRef]
- Lyu, M.; Ni, Z.; Chen, Q.; Li, F. Edge-DPSDG: An Edge-based Differential Privacy Protection Model for Smart Healthcare. IEEE Transactions on Big Data 2024. [Google Scholar] [CrossRef]
- Jiang, B.; Li, J.; Wang, H.; Song, H. Privacy-preserving federated learning for industrial edge computing via hybrid differential privacy and adaptive compression. IEEE Transactions on Industrial Informatics 2021, 19, 1136–1144. [Google Scholar] [CrossRef]
- Zerraza, I.; Seghir, Z.A.; Hemam, M. An Efficient Lightweight Authentication and Access Control for IoT Edge Devices. International Journal of Safety & Security Engineering 2024, 14. [Google Scholar]
- Rostampour, S.; Bagheri, N.; Bendavid, Y.; Safkhani, M.; Kumari, S.; Rodrigues, J.J. An authentication protocol for next generation of constrained Iot systems. IEEE Internet of Things Journal 2022, 9, 21493–21504. [Google Scholar] [CrossRef]
- Ding, X.; Wang, X.; Xie, Y.; Li, F. A lightweight anonymous authentication protocol for resource-constrained devices in Internet of Things. IEEE Internet of Things Journal 2021, 9, 1818–1829. [Google Scholar] [CrossRef]
- Bourechak, A.; Zedadra, O.; Kouahla, M.N.; Guerrieri, A.; Seridi, H.; Fortino, G. At the confluence of artificial intelligence and edge computing in iot-based applications: A review and new perspectives. Sensors 2023, 23, 1639. [Google Scholar] [CrossRef]
- Chang, Z.; Liu, S.; Xiong, X.; Cai, Z.; Tu, G. A survey of recent advances in edge-computing-powered artificial intelligence of things. IEEE Internet of Things Journal 2021, 8, 13849–13875. [Google Scholar] [CrossRef]
- Huh, J.H.; Seo, Y.S. Understanding edge computing: Engineering evolution with artificial intelligence. IEEE Access 2019, 7, 164229–164245. [Google Scholar] [CrossRef]
- Deng, S.; Zhao, H.; Fang, W.; Yin, J.; Dustdar, S.; Zomaya, A.Y. Edge intelligence: The confluence of edge computing and artificial intelligence. IEEE Internet of Things Journal 2020, 7, 7457–7469. [Google Scholar] [CrossRef]
- Wang, X.; Garg, S.; Lin, H.; Kaddoum, G.; Hu, J.; Hossain, M.S. A secure data aggregation strategy in edge computing and blockchain-empowered internet of things. IEEE Internet of Things Journal 2020, 9, 14237–14246. [Google Scholar] [CrossRef]
- Wang, J.; Wu, L.; Choo, K.K.R.; He, D. Blockchain-based anonymous authentication with key management for smart grid edge computing infrastructure. IEEE Transactions on Industrial Informatics 2019, 16, 1984–1992. [Google Scholar] [CrossRef]
- Bai, F.; Shen, T.; Yu, Z.; Zeng, K.; Gong, B. Trustworthy blockchain-empowered collaborative edge computing-as-a-service scheduling and data sharing in the IIoE. IEEE Internet of Things Journal 2021, 9, 14752–14766. [Google Scholar] [CrossRef]
- Li, B.; Chen, T.; Giannakis, G.B. Secure mobile edge computing in IoT via collaborative online learning. IEEE Transactions on Signal Processing 2019, 67, 5922–5935. [Google Scholar] [CrossRef]
- Wang, K.; Yin, H.; Quan, W.; Min, G. Enabling collaborative edge computing for software defined vehicular networks. IEEE network 2018, 32, 112–117. [Google Scholar] [CrossRef]
- Zhang, P.; Wang, Y.; Kumar, N.; Jiang, C.; Shi, G. A security-and privacy-preserving approach based on data disturbance for collaborative edge computing in social IoT systems. IEEE Transactions on Computational Social Systems 2021, 9, 97–108. [Google Scholar] [CrossRef]
- Begg, R. Digital Supply Chain: Cybersecurity Report Flags Clear and Present Danger. https://www.machinedesign.com/automation-iiot/article/21236851/netscout-digital-supply-chain-cybersecurity-report-flags-clear-and-present-danger/, year = 2022 (Accessed: (September 17, 2022)).
- Jovanovic, B. Internet of Things statistics for 2022 - Taking Things Apart. https://dataprot.net/statistics/iot-statistics/#:~:text=Malware%20attacks%20are%20now%20affecting,a%20third%20of%20infected%20devices., year = 2022 (accessed September 17, 2022).
- Manan, A. Implementation of image processing algorithm on FPGA. Akgec Journal of Technology 2006, 2, 25–28. [Google Scholar]
- Biookaghazadeh, S.; Zhao, M.; Ren, F. Are {FPGAs} Suitable for Edge Computing? In Proceedings of the USENIX Workshop on Hot Topics in Edge Computing (HotEdge 18), 2018.
- Sipola, T.; Alatalo, J.; Kokkonen, T.; Rantonen, M. Artificial intelligence in the IoT era: A review of edge AI hardware and software. In Proceedings of the 2022 31st Conference of Open Innovations Association (FRUCT). IEEE, 2022, pp. 320–331.
- Jiang, S.; He, D.; Yang, C.; Xu, C.; Luo, G.; Chen, Y.; Liu, Y.; Jiang, J. Accelerating mobile applications at the network edge with software-programmable FPGAs. In Proceedings of the IEEE INFOCOM 2018-IEEE Conference on Computer Communications. IEEE, 2018, pp. 55–62.
- Zhao, H.; Ratazzi, P. A Lightweight Hardware-Assisted Security Method for eFPGA Edge Devices. IEEE Internet of Things Journal 2024.
- Ngo, D.M.; Temko, A.; Murphy, C.C.; Popovici, E. FPGA hardware acceleration framework for anomaly-based intrusion detection system in IoT. In Proceedings of the 2021 31st International Conference on Field-Programmable Logic and Applications (FPL). IEEE, 2021, pp. 69–75.
- Zhang, Y.; Zhu, M.; Yang, B.; Liu, L. A Highly Reliable Strong Physical Unclonable Function Design Based on FPGA. In Proceedings of the Journal of Physics: Conference Series. IOP Publishing, 2020, Vol. 1619, p. 012003.
- Xu, T.; Potkonjak, M. Robust and flexible FPGA-based digital PUF. In Proceedings of the 2014 24th International Conference on Field Programmable Logic and Applications (FPL). IEEE; 2014; pp. 1–6. [Google Scholar]
- Guajardo, J.; Kumar, S.S.; Schrijen, G.J.; Tuyls, P. FPGA intrinsic PUFs and their use for IP protection. In Proceedings of the International workshop on cryptographic hardware and embedded systems. Springer; 2007; pp. 63–80. [Google Scholar]
- Kang, H.; Hori, Y.; Satoh, A. Performance evaluation of the first commercial PUF-embedded RFID. In Proceedings of the The 1st IEEE Global Conference on Consumer Electronics 2012. IEEE; 2012; pp. 5–8. [Google Scholar]
- Suh, G.E.; Devadas, S. Physical unclonable functions for device authentication and secret key generation. In Proceedings of the 2007 44th ACM/IEEE Design Automation Conference. IEEE; 2007; pp. 9–14. [Google Scholar]
- Alkabani, Y.; Koushanfar, F.; Potkonjak, M. Remote activation of ICs for piracy prevention and digital right management. In Proceedings of the 2007 IEEE/ACM International Conference on Computer-Aided Design. IEEE; 2007; pp. 674–677. [Google Scholar]
- Keele, S.; et al. Guidelines for performing systematic literature reviews in software engineering, 2007.
- Moher, D.; Liberati, A.; Tetzlaff, J.; Altman, D.G.; PRISMA Group*, t. Preferred reporting items for systematic reviews and meta-analyses: the PRISMA statement. Annals of internal medicine 2009, 151, 264–269. [Google Scholar] [CrossRef]
- Liu, D.; Yan, Z.; Ding, W.; Atiquzzaman, M. A survey on secure data analytics in edge computing. IEEE Internet of Things Journal 2019, 6, 4946–4967. [Google Scholar] [CrossRef]
- Xu, Z.; Liu, W.; Huang, J.; Yang, C.; Lu, J.; Tan, H. Artificial intelligence for securing IoT services in edge computing: a survey. Security and communication networks 2020, 2020, 1–13. [Google Scholar] [CrossRef]
- Lee, J.H.; Kim, H. Security and privacy challenges in the internet of things [security and privacy matters]. IEEE Consumer Electronics Magazine 2017, 6, 134–136. [Google Scholar] [CrossRef]
- Anandakumar, N.N.; Hashmi, M.S.; Tehranipoor, M. FPGA-based Physical Unclonable Functions: A comprehensive overview of theory and architectures. Integration 2021, 81, 175–194. [Google Scholar] [CrossRef]
- Lounis, K.; Zulkernine, M. More Lessons: Analysis of PUF-based Authentication Protocols for IoT. Cryptology ePrint Archive, Paper 2021/1509, 2021. https://eprint.iacr.org/2021/1509.
- Majzoobi, M.; Koushanfar, F.; Potkonjak, M.; Tehranipoor, M.; Wang, C. FPGA-oriented Security. Introduction to Hardware Security and Trust, 2011; 195–231. [Google Scholar]
- Merenda, M.; Porcaro, C.; Iero, D. Edge machine learning for ai-enabled iot devices: A review. Sensors 2020, 20, 2533. [Google Scholar] [CrossRef]
- Ansari, M.S.; Alsamhi, S.H.; Qiao, Y.; Ye, Y.; Lee, B. Security of distributed intelligence in edge computing: Threats and countermeasures. In The cloud-to-thing continuum; Palgrave Macmillan, Cham, 2020; pp. 95–122.
- El-Saleh, A.A.; Sheikh, A.M.; Albreem, M.A.; Honnurvali, M.S. The Internet of Medical Things (IoMT): opportunities and challenges. Wireless Networks, 2024; 1–18. [Google Scholar]
- Liu, H.; Zhang, Y.; Yang, T. Blockchain-Enabled Security in Electric Vehicles Cloud and Edge Computing. IEEE Network 2018, 32, 78–83. [Google Scholar] [CrossRef]
- Bonnah, E.; Shiguang, J. DecChain: A decentralized security approach in Edge Computing based on Blockchain. Future Generation Computer Systems 2020, 113, 363–379. [Google Scholar] [CrossRef]
- Yang, R.; Yu, F.R.; Si, P.; Yang, Z.; Zhang, Y. Integrated Blockchain and Edge Computing Systems: A Survey, Some Research Issues and Challenges. IEEE Communications Surveys & Tutorials 2019, 21, 1508–1532. [Google Scholar] [CrossRef]
- Luo, C.; Xu, L.; Li, D.; Wu, W. Edge computing integrated with blockchain technologies. In Complexity and Approximation; Springer, 2020; pp. 268–288.
- Mendki, P. Blockchain enabled iot edge computing: Addressing privacy, security and other challenges. In Proceedings of the Proceedings of the 2020 The 2nd International Conference on Blockchain Technology, 2020, pp. 63–67.
- Kotevska, O.; Johnson, J.; Kusne, A.G. Analyzing Data Privacy for Edge Systems. In Proceedings of the 2022 IEEE International Conference on Smart Computing (SMARTCOMP). IEEE; 2022; pp. 223–228. [Google Scholar]
- Paillet, D. An Overview of Cybersecurity Best Practices for Edge Computing. Technical report, Schneider Electric, 2021.
- Beekman, J. How to Deal with Edge Computing Security Concerns, 2022.
- van der Walt, S.; Venter, H. Research gaps and opportunities for secure access service edge. In Proceedings of the International Conference on Cyber Warfare and Security, 2022, Vol. 17, pp. 609–619.
- Singh, S.; Sulthana, R.; Shewale, T.; Chamola, V.; Benslimane, A.; Sikdar, B. Machine-Learning-Assisted Security and Privacy Provisioning for Edge Computing: A Survey. IEEE Internet of Things Journal 2022, 9, 236–260. [Google Scholar] [CrossRef]
- Waguie, F.T.; Al-Turjman, F. Artificial intelligence for edge computing security: A survey. In Proceedings of the 2022 International Conference on Artificial Intelligence in Everything (AIE). IEEE; 2022; pp. 446–450. [Google Scholar]
- Zhou, Z.; Chen, X.; Li, E.; Zeng, L.; Luo, K.; Zhang, J. Edge intelligence: Paving the last mile of artificial intelligence with edge computing. Proceedings of the IEEE 2019, 107, 1738–1762. [Google Scholar] [CrossRef]
- Lin, F.; Zhou, Y.; An, X.; You, I.; Choo, K.K.R. Fair resource allocation in an intrusion-detection system for edge computing: Ensuring the security of Internet of Things devices. IEEE Consumer Electronics Magazine 2018, 7, 45–50. [Google Scholar] [CrossRef]
- Spadaccino, P.; Cuomo, F. Intrusion Detection Systems for IoT: opportunities and challenges offered by Edge Computing and Machine Learning. arXiv preprint arXiv:2012.01174, arXiv:2012.01174 2020.
- Singh, A.; Chatterjee, K.; Satapathy, S.C. An edge based hybrid intrusion detection framework for mobile edge computing. Complex & Intelligent Systems 2022, 8, 3719–3746. [Google Scholar]
- Alsubhi, K. A Secured Intrusion Detection System for Mobile Edge Computing. Applied Sciences 2024, 14, 1432. [Google Scholar] [CrossRef]
- Gyamfi, E.; Jurcut, A. Intrusion detection in internet of things systems: a review on design approaches leveraging multi-access edge computing, machine learning, and datasets. Sensors 2022, 22, 3744. [Google Scholar] [CrossRef]
- Long, J.; Liang, W.; Li, K.C.; Zhang, D.; Tang, M.; Luo, H. PUF-based anonymous authentication scheme for hardware devices and IPs in edge computing environment. IEEE Access 2019, 7, 124785–124796. [Google Scholar] [CrossRef]
- Aarella, S.G.; Mohanty, S.P.; Kougianos, E.; Puthal, D. PUF-based Authentication Scheme for Edge Data Centers in Collaborative Edge Computing. In Proceedings of the 2022 IEEE International Symposium on Smart Electronic Systems (iSES). IEEE; 2022; pp. 433–438. [Google Scholar]
- Chen, Z.; Wu, M.; Zhou, Y.; Li, R.; Tan, J.; Ding, D. Puf-cim: Sram-based compute-in-memory with zero bit-error-rate physical unclonable function for lightweight secure edge computing. IEEE Transactions on Very Large Scale Integration (VLSI) Systems 2023, 31, 1234–1247. [Google Scholar] [CrossRef]
- Zhang, J.L.; Wu, Q.; Ding, Y.P.; Lv, Y.Q.; Zhou, Q.; Xia, Z.H.; Sun, X.M.; Wang, X.W. Techniques for design and implementation of an FPGA-specific physical unclonable function. Journal of Computer Science and Technology 2016, 31, 124–136. [Google Scholar] [CrossRef]
- Zhu, C.; Zhu, X.; Ren, J.; Qin, T. Blockchain-enabled federated learning for UAV edge computing network: Issues and solutions. Ieee Access 2022, 10, 56591–56610. [Google Scholar] [CrossRef]
- Nguyen, T.; Nguyen, H.; Gia, T.N. Exploring the integration of edge computing and blockchain IoT: Principles, architectures, security, and applications. Journal of Network and Computer Applications, 103884. [Google Scholar]
- Song, S.; Choi, B.Y.; Kim, D. Selective encryption and component-oriented deduplication for mobile cloud data computing. In Proceedings of the 2016 International Conference on Computing, Networking and Communications (ICNC). IEEE; 2016; pp. 1–5. [Google Scholar]
- Zhao, Y.; Wang, W.; Li, Y.; Meixner, C.C.; Tornatore, M.; Zhang, J. Edge computing and networking: A survey on infrastructures and applications. IEEE Access 2019, 7, 101213–101230. [Google Scholar] [CrossRef]
- Cheng, G.; Chen, Y.; Deng, S.; Gao, H.; Yin, J. A Blockchain-Based Mutual Authentication Scheme for Collaborative Edge Computing. IEEE Transactions on Computational Social Systems 2022, 9, 146–158. [Google Scholar] [CrossRef]
- Zeyu, H.; Geming, X.; Zhaohang, W.; Sen, Y. Survey on Edge Computing Security. In Proceedings of the 2020 International Conference on Big Data, Artificial Intelligence and Internet of Things Engineering (ICBAIE); 2020; pp. 96–105. [Google Scholar] [CrossRef]
- Mollah, M.B.; Azad, M.A.K.; Vasilakos, A. Secure data sharing and searching at the edge of cloud-assisted internet of things. IEEE Cloud Computing 2017, 4, 34–42. [Google Scholar] [CrossRef]
- Bhat, S.A.; Sofi, I.B.; Chi, C.Y. edge computing and its convergence with blockchain in 5G and beyond: security, challenges, and opportunities. IEEE Access 2020, 8, 205340–205373. [Google Scholar] [CrossRef]
- Microsoft. What is edge computing? https://azure.microsoft.com/en-us/resources/cloud-computing-dictionary/what-is-edge-computing/, year = 2022 (accessed October 18, 2022).
- Shi, W.; Cao, J.; Zhang, Q.; Li, Y.; Xu, L. Edge Computing: Vision and Challenges. IEEE Internet of Things Journal 2016, 3, 637–646. [Google Scholar] [CrossRef]
- Mohanan, R. What Is Edge Computing? Components, Examples, and Best Practices. https://www.spiceworks.com/tech/edge-computing/articles/what-is-edge-computing/ , year = 2022 (accessed October 18, 2022).
- Hemminger, S.; et al. Network emulation with NetEm. In Proceedings of the Linux conf au. Citeseer, 2005, Vol. 5, p. 2005.
- Li, W.; Chen, Z.; Gao, X.; Liu, W.; Wang, J. Multimodel framework for indoor localization under mobile edge computing environment. IEEE Internet of Things Journal 2018, 6, 4844–4853. [Google Scholar] [CrossRef]
- Khan, W.Z.; Ahmed, E.; Hakak, S.; Yaqoob, I.; Ahmed, A. Edge computing: A survey. Future Generation Computer Systems 2019, 97, 219–235. [Google Scholar] [CrossRef]
- Toczé, K.; Nadjm-Tehrani, S. A taxonomy for management and optimization of multiple resources in edge computing. Wireless Communications and Mobile Computing 2018, 2018. [Google Scholar] [CrossRef]
- Albreem, M.A.; Sheikh, A.M.; Bashir, M.J.; El-Saleh, A.A. Towards green Internet of Things (IoT) for a sustainable future in Gulf Cooperation Council countries: Current practices, challenges and future prospective. Wireless Networks 2023, 29, 539–567. [Google Scholar] [CrossRef]
- Varghese, B.; Wang, N.; Barbhuiya, S.; Kilpatrick, P.; Nikolopoulos, D.S. Challenges and opportunities in edge computing. In Proceedings of the 2016 IEEE International Conference on Smart Cloud (SmartCloud). IEEE; 2016; pp. 20–26. [Google Scholar]
- howpublished = https://sunkur.medium.com/challenges-in-edge-computing-ec9237b5ab77, year = 2022 (accessed November 12, 2022), S.R. Challenges in Edge Computing.
- Kong, L.; Tan, J.; Huang, J.; Chen, G.; Wang, S.; Jin, X.; Zeng, P.; Khan, M.K.; Das, S.K. Edge-Computing-Driven Internet of Things: A Survey. ACM Computing Surveys (CSUR) 2022. [Google Scholar] [CrossRef]
- Schäfer, D.; Edinger, J.; VanSyckel, S.; Paluska, J.M.; Becker, C. Tasklets: Overcoming heterogeneity in distributed computing systems. In Proceedings of the 2016 IEEE 36th International Conference on Distributed Computing Systems Workshops (ICDCSW). IEEE; 2016; pp. 156–161. [Google Scholar]
- Carvalho, G.; Cabral, B.; Pereira, V.; Bernardino, J. Edge computing: current trends, research challenges and future directions. Computing 2021, 103, 993–1023. [Google Scholar] [CrossRef]
- Sun, J.; Gu, Q.; Zheng, T.; Dong, P.; Qin, Y. Joint communication and computing resource allocation in vehicular edge computing. International Journal of Distributed Sensor Networks 2019, 15, 1550147719837859. [Google Scholar] [CrossRef]
- Jia, M.; Zhang, L.; Wu, J.; Guo, Q.; Gu, X. Joint computing and communication resource allocation for edge computing towards Huge LEO networks. China Communications 2022, 19, 73–84. [Google Scholar] [CrossRef]
- Ning, Z.; Huang, J.; Wang, X.; Rodrigues, J.J.; Guo, L. Mobile edge computing-enabled internet of vehicles: Toward energy-efficient scheduling. IEEE Network 2019, 33, 198–205. [Google Scholar] [CrossRef]
- Wang, X.; Han, Y.; Leung, V.C.; Niyato, D.; Yan, X.; Chen, X. Convergence of edge computing and deep learning: A comprehensive survey. IEEE Communications Surveys & Tutorials 2020, 22, 869–904. [Google Scholar]
- Chen, H.; Qin, W.; Wang, L. Task partitioning and offloading in IoT cloud-edge collaborative computing framework: a survey. Journal of Cloud Computing 2022, 11, 1–19. [Google Scholar] [CrossRef]
- Saeik, F.; Avgeris, M.; Spatharakis, D.; Santi, N.; Dechouniotis, D.; Violos, J.; Leivadeas, A.; Athanasopoulos, N.; Mitton, N.; Papavassiliou, S. Task offloading in Edge and Cloud Computing: A survey on mathematical, artificial intelligence and control theory solutions. Computer Networks 2021, 195, 108177. [Google Scholar] [CrossRef]
- Feng, M.; Krunz, M.; Zhang, W. Task partitioning and user association for latency minimization in mobile edge computing networks. In Proceedings of the IEEE INFOCOM 2021-IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS). IEEE; 2021; pp. 1–6. [Google Scholar]
- Ometov, A.; Molua, O.L.; Komarov, M.; Nurmi, J. A survey of security in cloud, edge, and fog computing. Sensors 2022, 22, 927. [Google Scholar] [CrossRef] [PubMed]
- Sha, K.; Yang, T.A.; Wei, W.; Davari, S. A survey of edge computing-based designs for IoT security. Digital Communications and Networks 2020, 6, 195–202. [Google Scholar]
- Ahmadi, S. Security Implications of Edge Computing in Cloud Networks. Ahmadi, S.(2024) Security Implications of Edge Computing in Cloud Networks. Journal of Computer and Communications 2024, 12, 26–46. [Google Scholar]
- Accenture. Edge Computing. https://www.accenture.com/bg-en/insights/cloud/edge-computing-index, year = 2024 (accessed September 15, 2024).
- Abhishek, A.; Adeniyi-Jones, C.; Van Hensbergen, E.; Balmakhtar, M. Accounting and resource scheduling at the edge. HotEdge’20, 2020. [Google Scholar]
- Ahmed, E.; Ahmed, A.; Yaqoob, I.; Shuja, J.; Gani, A.; Imran, M.; Shoaib, M. Bringing Computation Closer toward the User Network: Is Edge Computing the Solution? IEEE Communications Magazine 2017, 55, 138–144. [Google Scholar] [CrossRef]
- howpublished = https://itsecuritywire.com/featured/edge-computing-four-cybersecurity-challenges-in-2022/, year = 2022 (accessed February 8, 2023), U.S. Edge Computing: Four Cybersecurity Challenges in 2022.
- Wu, W.; Zhang, Q.; Wang, H.J. Edge computing security protection from the perspective of classified protection of cybersecurity. In Proceedings of the 2019 6th International Conference on Information Science and Control Engineering (ICISCE). IEEE; 2019; pp. 278–281. [Google Scholar]
- Mall, A.; Singh, P.; Thute, A.; Khapre, S.P.; Shankar, A. Security issues of edge computing in IoT. In Proceedings of the Proceedings of International Conference on Machine Intelligence and Data Science Applications: MIDAS 2020. Springer, 2021, pp. 567–579.
- Ranaweera, P.; Jurcut, A.D.; Liyanage, M. Survey on multi-access edge computing security and privacy. IEEE Communications Surveys & Tutorials 2021, 23, 1078–1124. [Google Scholar]
- Uddin, R.; Kumar, S.A.; Chamola, V. Denial of service attacks in edge computing layers: Taxonomy, vulnerabilities, threats and solutions. Ad Hoc Networks 2024, 152, 103322. [Google Scholar]
- Fazeldehkordi, E.; Grønli, T.M. A Survey of Security Architectures for Edge Computing-Based IoT. IoT 2022, 3, 332–365. [Google Scholar] [CrossRef]
- Hassan, N.; Gillani, S.; Ahmed, E.; Yaqoob, I.; Imran, M. The Role of Edge Computing in Internet of Things. IEEE Communications Magazine 2018, 56, 110–115. [Google Scholar] [CrossRef]
- Alwakeel, A.M. An overview of fog computing and edge computing security and privacy issues. Sensors 2021, 21, 8226. [Google Scholar] [CrossRef]
- Guynes, S.; Parrish, J.; Vedder, R. Edge computing societal privacy and security issues. Acm Sigcas Computers and Society 2020, 48, 11–12. [Google Scholar] [CrossRef]
- Mukherjee, M.; Matam, R.; Mavromoustakis, C.X.; Jiang, H.; Mastorakis, G.; Guo, M. Intelligent edge computing: Security and privacy challenges. IEEE Communications Magazine 2020, 58, 26–31. [Google Scholar] [CrossRef]
- Zhu, W.; Zhou, C.; Jiang, L. A Trusted Internet of Things Access Scheme for Cloud Edge Collaboration. Electronics 2024, 13, 1026. [Google Scholar] [CrossRef]
- howpublished = https://www.xsoccorp.com/post/data-encryption-for-the-edge, year = 2021 (accessed June 19, 2023), R.B. Data Encryption for the Edge.
- Kwon, H.; Hahn, C.; Kim, D.; Hur, J. Secure deduplication for multimedia data with user revocation in cloud storage. Multimedia Tools and Applications 2017, 76, 5889–5903. [Google Scholar] [CrossRef]
- Neto, E.C.P.; Dadkhah, S.; Ghorbani, A.A. Sustainable and Secure Optimization of Load Distribution in Edge Computing. In Proceedings of the 2022 IEEE 19th International Conference on Smart Communities: Improving Quality of Life Using ICT, IoT and AI (HONET). IEEE; 2022; pp. 040–045. [Google Scholar]
- Li, D.; Zhang, E.; Lei, M.; Song, C. Zero trust in edge computing environment: a blockchain based practical scheme. Mathematical Biosciences and Engineering 2022, 19, 4196–4216. [Google Scholar] [CrossRef]
- Wu, Y.; Dai, H.N.; Wang, H. Convergence of blockchain and edge computing for secure and scalable IIoT critical infrastructures in industry 4.0. IEEE Internet of Things Journal 2020, 8, 2300–2317. [Google Scholar] [CrossRef]
- Dong, J.; Song, C.; Zhang, T.; Li, Y.; Zheng, H. Integration of edge computing and blockchain for provision of data fusion and secure big data analysis for Internet of Things. Wireless Communications and Mobile Computing 2022, 2022, 9233267. [Google Scholar] [CrossRef]
- Ding, X.; Guo, J.; Li, D.; Wu, W. Pricing and budget allocation for IoT blockchain with edge computing. IEEE Transactions on Cloud Computing 2022, 11, 1608–1621. [Google Scholar] [CrossRef]
- Medhane, D.V.; Sangaiah, A.K.; Hossain, M.S.; Muhammad, G.; Wang, J. Blockchain-enabled distributed security framework for next-generation IoT: An edge cloud and software-defined network-integrated approach. IEEE Internet of Things Journal 2020, 7, 6143–6149. [Google Scholar] [CrossRef]
- Wang, S.; Liu, Z.; Wang, H.; Wang, J. Ensuring security in edge computing through effective blockchain node detection. Journal of Cloud Computing 2023, 12, 1–16. [Google Scholar] [CrossRef]
- Xu, X.; Zhang, X.; Gao, H.; Xue, Y.; Qi, L.; Dou, W. BeCome: Blockchain-enabled computation offloading for IoT in mobile edge computing. IEEE Transactions on Industrial Informatics 2019, 16, 4187–4195. [Google Scholar] [CrossRef]
- Jangirala, S.; Das, A.K.; Vasilakos, A.V. Designing secure lightweight blockchain-enabled RFID-based authentication protocol for supply chains in 5G mobile edge computing environment. IEEE Transactions on Industrial Informatics 2019, 16, 7081–7093. [Google Scholar] [CrossRef]
- Gao, Q.; Xiao, J.; Cao, Y.; Deng, S.; Ouyang, C.; Feng, Z. Blockchain-based collaborative edge computing: efficiency, incentive and trust. Journal of Cloud Computing 2023, 12, 72. [Google Scholar] [CrossRef]
- Mandarino, V.; Pappalardo, G.; Tramontana, E. A Blockchain-Based Electronic Health Record (EHR) System for Edge Computing Enhancing Security and Cost Efficiency. Computers 2024, 13, 132. [Google Scholar] [CrossRef]
- Xiong, Z.; Zhang, Y.; Niyato, D.; Wang, P.; Han, Z. When mobile blockchain meets edge computing. IEEE Communications Magazine 2018, 56, 33–39. [Google Scholar] [CrossRef]
- Spadaccino, P.; Cuomo, F.; et al. Intrusion detection systems for iot: opportunities and challenges offered by edge computing. Journal on Future and Evolving Technologies 2022. [Google Scholar] [CrossRef]
- Mahadevappa, P.; Murugesan, R.K.; Al-Amri, R.; Thabit, R.; Al-Ghushami, A.H.; Alkawsi, G. A secure edge computing model using machine learning and IDS to detect and isolate intruders. MethodsX 2024, 12, 102597. [Google Scholar] [CrossRef]
- howpublished = https://www.trentonsystems.com/blog/is-edge-computing-secure, year = 2020 (accessed January 14, 2023), B.D. Is Edge Computing Secure?
- Xia, Q.; Tao, Z.; Li, Q. Privacy issues in edge computing. In Fog/Edge Computing For Security, Privacy, and Applications; Springer, 2021; pp. 147–169.
- Adil, M.; Almaiah, M.A.; Omar Alsayed, A.; Almomani, O. An anonymous channel categorization scheme of edge nodes to detect jamming attacks in wireless sensor networks. Sensors 2020, 20, 2311. [Google Scholar] [CrossRef]
- Liang, F.; Hatcher, W.G.; Liao, W.; Gao, W.; Yu, W. Machine learning for security and the internet of things: the good, the bad, and the ugly. IEEE Access 2019, 7, 158126–158147. [Google Scholar] [CrossRef]
- Sheikh, A.M.; Islam, M.R.; Habaebi, M.H.; Zabidi, S.A.; Najeeb, A.R.B.; Basahel, A. Machine Learning (ML) assisted Edge security framework on FPGAs. In Proceedings of the 2023 9th International Conference on Computer and Communication Engineering (ICCCE). IEEE; 2023; pp. 155–160. [Google Scholar]
- Meuser, T.; Lovén, L.; Bhuyan, M.; Patil, S.G.; Dustdar, S.; Aral, A.; Bayhan, S.; Becker, C.; de Lara, E.; Ding, A.Y.; et al. Revisiting Edge AI: Opportunities and Challenges. IEEE Internet Computing 2024, 28, 49–59. [Google Scholar] [CrossRef]
- Mendez, J.; Bierzynski, K.; Cuéllar, M.; Morales, D.P. Edge Intelligence: Concepts, Architectures, Applications, and Future Directions. ACM Transactions on Embedded Computing Systems (TECS) 2022, 21, 1–41. [Google Scholar] [CrossRef]
- Wang, C.; Yuan, Z.; Zhou, P.; Xu, Z.; Li, R.; Wu, D.O. The security and privacy of mobile edge computing: An artificial intelligence perspective. IEEE Internet of Things Journal 2023. [Google Scholar] [CrossRef]
- Xu, D.; Li, T.; Li, Y.; Su, X.; Tarkoma, S.; Jiang, T.; Crowcroft, J.; Hui, P. Edge intelligence: Empowering intelligence to the edge of network. Proceedings of the IEEE 2021, 109, 1778–1837. [Google Scholar] [CrossRef]
- Raimundo, R.; Rosário, A. The impact of artificial intelligence on data system security: A literature review. Sensors 2021, 21, 7029. [Google Scholar] [CrossRef] [PubMed]
- Montini, H. Artificial Intelligence in Cybersecurity: How to Use The Technology. https://www.provendata.com/blog/ai-in-cybersecurity/ , year = 2024 (accessed October 8, 2024).
- Alowais, S.A.; Alghamdi, S.S.; Alsuhebany, N.; Alqahtani, T.; Alshaya, A.I.; Almohareb, S.N.; Aldairem, A.; Alrashed, M.; Bin Saleh, K.; Badreldin, H.A.; et al. Revolutionizing healthcare: the role of artificial intelligence in clinical practice. BMC medical education 2023, 23, 689. [Google Scholar] [CrossRef] [PubMed]
- Wang, F.; Zhang, M.; Wang, X.; Ma, X.; Liu, J. Deep learning for edge computing applications: A state-of-the-art survey. IEEE Access 2020, 8, 58322–58336. [Google Scholar] [CrossRef]
- Sun, Y.; Ochiai, H.; Esaki, H. Decentralized deep learning for multi-access edge computing: A survey on communication efficiency and trustworthiness. IEEE Transactions on Artificial Intelligence 2021, 3, 963–972. [Google Scholar] [CrossRef]
- Wu, H.; Han, H.; Wang, X.; Sun, S. Research on artificial intelligence enhancing internet of things security: A survey. Ieee Access 2020, 8, 153826–153848. [Google Scholar] [CrossRef]
- Kulin, M.; Kazaz, T.; De Poorter, E.; Moerman, I. A Survey on Machine Learning-Based Performance Improvement of Wireless Networks: PHY, MAC and Network Layer. Electronics 2021, 10, 318. [Google Scholar] [CrossRef]
- Hua, H.; Li, Y.; Wang, T.; Dong, N.; Li, W.; Cao, J. Edge Computing with Artificial Intelligence: A Machine Learning Perspective. ACM Computing Surveys 2023, 55, 1–35. [Google Scholar] [CrossRef]
- Munir, A.; Blasch, E.; Kwon, J.; Kong, J.; Aved, A. Artificial intelligence and data fusion at the edge. IEEE Aerospace and Electronic Systems Magazine 2021, 36, 62–78. [Google Scholar] [CrossRef]
- Sedjelmaci, H.; Senouci, S.M.; Ansari, N.; Boualouache, A. A trusted hybrid learning approach to secure edge computing. IEEE Consumer Electronics Magazine 2021, 11, 30–37. [Google Scholar] [CrossRef]
- Gassend, B.; Clarke, D.; Van Dijk, M.; Devadas, S. Silicon physical random functions. In Proceedings of the Proceedings of the 9th ACM Conference on Computer and Communications Security, 2002; pp. 148–160.
- Shamsoshoara, A.; Korenda, A.; Afghah, F.; Zeadally, S. A survey on physical unclonable function (PUF)-based security solutions for Internet of Things. Computer Networks 2020, 183, 107593. [Google Scholar] [CrossRef]
- Murphy, D. The Role of Machine Learning in Data Security. https://www.lepide.com/blog/the-role-of-machine-learning-in-data-security/, year = 2023 (accessed January 24, 2024).
- Rigaki, M.; Garcia, S. A survey of privacy attacks in machine learning. ACM Computing Surveys 2023, 56, 1–34. [Google Scholar] [CrossRef]
- Shen, T.; Ding, L.; Sun, J.; Jing, C.; Guo, F.; Wu, C. Edge Computing for IoT Security: Integrating Machine Learning with Key Agreement. In Proceedings of the 2023 3rd International Conference on Consumer Electronics and Computer Engineering (ICCECE); 2023; pp. 474–483. [Google Scholar] [CrossRef]
- Nassif, A.B.; Talib, M.A.; Nasir, Q.; Dakalbab, F.M. Machine learning for anomaly detection: A systematic review. Ieee Access 2021, 9, 78658–78700. [Google Scholar] [CrossRef]
- Murshed, M.S.; Murphy, C.; Hou, D.; Khan, N.; Ananthanarayanan, G.; Hussain, F. Machine learning at the network edge: A survey. ACM Computing Surveys (CSUR) 2021, 54, 1–37. [Google Scholar] [CrossRef]
- Brecko, A.; Kajati, E.; Koziorek, J.; Zolotova, I. Federated learning for edge computing: A survey. Applied Sciences 2022, 12, 9124. [Google Scholar] [CrossRef]
- Abreha, H.G.; Hayajneh, M.; Serhani, M.A. Federated learning in edge computing: a systematic survey. Sensors 2022, 22, 450. [Google Scholar] [CrossRef]
- Feng, Y.; Qi, Y.; Li, H.; Wang, X.; Tian, J. Leveraging federated learning and edge computing for recommendation systems within cloud computing networks. In Proceedings of the Third International Symposium on Computer Applications and Information Systems (ISCAIS 2024). SPIE, 2024, Vol. 13210, pp. 279–287.
- Li, X.; Wu, W. Recent Advances of Blockchain and Its Applications. Journal of Social Computing 2022, 3, 363–394. [Google Scholar] [CrossRef]
- Moore, E.; Imteaj, A.; Rezapour, S.; Amini, M.H. A Survey on Secure and Private Federated Learning Using Blockchain: Theory and Application in Resource-constrained Computing. IEEE Internet of Things Journal, 2023; 1–1. [Google Scholar] [CrossRef]
- Ni, S.; He, Y.; Chen, L.; Wang, Y.; Yu, F. A Survey of Edge Computing Resource Allocation Strategies Based on Federated Learning. In Proceedings of the 2023 International Conference on Networking and Network Applications (NaNA); 2023; pp. 116–121. [Google Scholar] [CrossRef]
- Wang, R.; Lai, J.; Zhang, Z.; Li, X.; Vijayakumar, P.; Karuppiah, M. Privacy-preserving federated learning for internet of medical things under edge computing. IEEE journal of biomedical and health informatics 2022, 27, 854–865. [Google Scholar] [CrossRef]
- Mahbub, M.; Gazi, M.S.A.; Provat, S.A.A.; Islam, M.S. Multi-access edge computing-aware internet of things: MEC-IoT. In Proceedings of the 2020 Emerging Technology in Computing, Communication and Electronics (ETCCE). IEEE; 2020; pp. 1–6. [Google Scholar]
- Zhang, P.; Durresi, M.; Durresi, A. Mobile privacy protection enhanced with multi-access edge computing. In Proceedings of the 2018 IEEE 32nd International Conference on Advanced Information Networking and Applications (AINA). IEEE; 2018; pp. 724–731. [Google Scholar]
- Mao, Y.; You, C.; Zhang, J.; Huang, K.; Letaief, K.B. A survey on mobile edge computing: The communication perspective. IEEE communications surveys & tutorials 2017, 19, 2322–2358. [Google Scholar]
- Zhang, Y.; Zhang, Y. The Future of Mobile Edge Computing. Mobile Edge Computing, 2022; 81–105. [Google Scholar]
- Ortega-Fernandez, I.; Martinez, S.E.K.; Orellana, L.A.; Soldatos, J.; Kyriazis, D. Large Scale Data Anonymisation for GDPR Compliance. Big Data and Artificial Intelligence in Digital Finance, 2022; 325. [Google Scholar]
- Regulation, G.D.P. General data protection regulation (GDPR). Intersoft Consulting, Accessed in October 2018, 24. [Google Scholar]
- howpublished = https://cloud.google.com/dlp/docs/concepts-bucketing#:~:text=Generalization%20is%20the%20process%20of,depending%20on%20the%20data%20type., year = accessed 1st Feb 2024, G.C. Generalization and bucketing.
- Khraisat, A.; Gondal, I.; Vamplew, P.; Kamruzzaman, J. Survey of intrusion detection systems: techniques, datasets and challenges. Cybersecurity 2019, 2, 1–22. [Google Scholar] [CrossRef]
- Cybersecurity, A. Intrusion Detection Systems (IDS) explained. https://cybersecurity.att.com/solutions/intrusion-detection-system/ids-explained, year = 2024 (accessed September 17, 2024).
- Arisdakessian, S.; Wahab, O.A.; Mourad, A.; Otrok, H.; Guizani, M. A survey on IoT intrusion detection: Federated learning, game theory, social psychology, and explainable AI as future directions. IEEE Internet of Things Journal 2022, 10, 4059–4092. [Google Scholar] [CrossRef]
- Sadhu, P.K.; Yanambaka, V.P.; Abdelgawad, A. Internet of things: Security and solutions survey. Sensors 2022, 22, 7433. [Google Scholar] [CrossRef] [PubMed]
- Sidhu, S.; Mohd, B.J.; Hayajneh, T. Hardware security in IoT devices with emphasis on hardware trojans. Journal of Sensor and Actuator Networks 2019, 8, 42. [Google Scholar] [CrossRef]
- Hu, W.; Chang, C.H.; Sengupta, A.; Bhunia, S.; Kastner, R.; Li, H. An overview of hardware security and trust: Threats, countermeasures, and design tools. IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems 2020, 40, 1010–1038. [Google Scholar] [CrossRef]
- Meneghello, F.; Calore, M.; Zucchetto, D.; Polese, M.; Zanella, A. IoT: Internet of threats? A survey of practical security vulnerabilities in real IoT devices. IEEE Internet of Things Journal 2019, 6, 8182–8201. [Google Scholar] [CrossRef]
- Yang, K.; Blaauw, D.; Sylvester, D. Hardware designs for security in ultra-low-power IoT systems: An overview and survey. IEEE Micro 2017, 37, 72–89. [Google Scholar] [CrossRef]
- Cirne, A.; Sousa, P.R.; Resende, J.S.; Antunes, L. Hardware security for IoT identity assurance. development 2021, 9, 11. [Google Scholar]
- Pourrahmani, H.; Yavarinasab, A.; Monazzah, A.M.H.; et al. A review of the security vulnerabilities and countermeasures in the Internet of Things solutions: A bright future for the Blockchain. Internet of Things 2023, 23, 100888. [Google Scholar] [CrossRef]
- Jin, Y. Introduction to hardware security. Electronics 2015, 4, 763–784. [Google Scholar] [CrossRef]
- Rahman, M.T.; Shi, Q.; Tajik, S.; Shen, H.; Woodard, D.L.; Tehranipoor, M.; Asadizanjani, N. Physical inspection & attacks: New frontier in hardware security. In Proceedings of the 2018 IEEE 3rd International Verification and Security Workshop (IVSW). IEEE, 2018, pp. 93–102.
- Aqeel, M.; Ali, F.; Iqbal, M.W.; Rana, T.A.; Arif, M.; Auwul, M.R. A review of security and privacy concerns in the internet of things (IoT). Journal of Sensors 2022, 2022, 5724168. [Google Scholar] [CrossRef]
- Japa, A.; Majumder, M.K.; Sahoo, S.K.; Vaddi, R.; Kaushik, B.K. Hardware security exploiting post-CMOS devices: fundamental device characteristics, state-of-the-art countermeasures, challenges and roadmap. IEEE Circuits and Systems Magazine 2021, 21, 4–30. [Google Scholar] [CrossRef]
- Li, K.F.; Attarmoghaddam, N. Challenges and methodologies of hardware security. In Proceedings of the 2018 IEEE 32nd International Conference on Advanced Information Networking and Applications (AINA). IEEE; 2018; pp. 928–933. [Google Scholar]
- Tsvetanov, F. Sensor network hardware security. In Proceedings of the AIP Conference Proceedings. AIP Publishing, 2022, Vol. 2570.
- Batina, L.; Jauernig, P.; Mentens, N.; Sadeghi, A.R.; Stapf, E. INVITED: In Hardware We Trust : Gains and Pains of Hardware-assisted Security. In Proceedings of the 2019 56th ACM/IEEE Design Automation Conference (DAC); 2019; pp. 1–4. [Google Scholar]
- Hassija, V.; Chamola, V.; Gupta, V.; Jain, S.; Guizani, N. A survey on supply chain security: Application areas, security threats, and solution architectures. IEEE Internet of Things Journal 2020, 8, 6222–6246. [Google Scholar] [CrossRef]
- Obeng, Y.; Nolan, C.; Brown, D. Hardware security through chain assurance. In Proceedings of the 2016 Design, Automation & Test in Europe Conference & Exhibition (DATE); 2016; pp. 1535–1537. [Google Scholar]
- Akter, S.; Khalil, K.; Bayoumi, M. Hardware security in the internet of things: A survey. In Proceedings of the 2023 IEEE 36th International System-on-Chip Conference (SOCC). IEEE; 2023; pp. 1–6. [Google Scholar]
- Maharmeh, H.A.; Alhawari, M.; Hung, C.C.; Ismail, M. Hardware security threats and countermeasures: a study of obfuscation, camouflaging and PUFs. International Journal of Multimedia Intelligence and Security 2019, 3, 271–292. [Google Scholar] [CrossRef]
- Akter, S.; Khalil, K.; Bayoumi, M. A survey on hardware security: Current trends and challenges. IEEE Access 2023, 11, 77543–77565. [Google Scholar] [CrossRef]
- Babaei, A.; Schiele, G. Physical unclonable functions in the internet of things: State of the art and open challenges. Sensors 2019, 19, 3208. [Google Scholar] [CrossRef]
- Shariffuddin, S.; Sivamangai, N.; Napolean, A.; Naveenkumar, R.; Kamalnath, S.; Saranya, G. Review on Arbiter Physical Unclonable Function and its Implementation in FPGA for IoT Security Applications. In Proceedings of the 2022 6th International Conference on Devices, Circuits and Systems (ICDCS); 2022; pp. 369–374. [Google Scholar] [CrossRef]
- Bergfalck, L.; Engström, J. Designing a Physical Unclonable Function for Cryptographic Hardware, 2021.
- Al-Meer, A.; Al-Kuwari, S. Physical Unclonable Functions (PUF) for IoT Devices. arXiv preprint arXiv:2205.08587, arXiv:2205.08587 2022.
- Liu, Y.; Xie, Y.; Bao, C.; Srivastava, A. A combined optimization-theoretic and side-channel approach for attacking strong physical unclonable functions. IEEE Transactions on Very Large Scale Integration (VLSI) Systems 2017, 26, 73–81. [Google Scholar] [CrossRef]
- Shah, N.; Chatterjee, D.; Sapui, B.; Mukhopadhyay, D.; Basu, A. Introducing Recurrence in Strong PUFs for Enhanced Machine Learning Attack Resistance. IEEE Journal on Emerging and Selected Topics in Circuits and Systems 2021, 11, 319–332. [Google Scholar] [CrossRef]
- Xu, Y.; Lao, Y.; Liu, W.; Zhang, Z.; You, X.; Zhang, C. Mathematical Modeling Analysis of Strong Physical Unclonable Functions. IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems 2020, 39, 4426–4438. [Google Scholar] [CrossRef]
- Ma, X.; Wang, P.; Li, G.; Zhou, Z. Machine learning attacks resistant strong PUF design utilizing response obfuscates challenge with lower hardware overhead. Microelectronics Journal 2023, 142, 105977. [Google Scholar] [CrossRef]
- Cao, Y.; Xu, J.; Wu, J.; Wu, S.; Huang, Z.; Zhang, K. Advances in Physical Unclonable Functions Based on New Technologies: A Comprehensive Review. Mathematics 2023, 12, 77. [Google Scholar] [CrossRef]
- Su, H. Novel design in mixed-signal and machine learning resilient architecture physical unclonable functions. PhD thesis, University of Southampton, 2021.
- Magyari, A.; Chen, Y. Integrating Lorenz Hyperchaotic Encryption with Ring Oscillator Physically Unclonable Functions (RO-PUFs) for High-Throughput Internet of Things (IoT) Applications. Electronics 2023, 12, 4929. [Google Scholar] [CrossRef]
- Zhuang, Y.; Mursi, K.T.; Gaoxiang, L. A challenge obfuscating interface for arbiter PUF variants against machine learning attacks. arXiv preprint arXiv:2103.12935, 2021; arXiv:2103.12935 2021. [Google Scholar]
- Avvaru, S.V.S.; Zhou, C.; Satapathy, S.; Lao, Y.; Kim, C.H.; Parhi, K.K. Estimating delay differences of arbiter PUFs using silicon data. In Proceedings of the 2016 Design, Automation & Test in Europe Conference & Exhibition (DATE); 2016; pp. 543–546. [Google Scholar]
- Wang, K.; Shi, J.; Lai, W.; He, Q.; Xu, J.; Ni, Z.; Liu, X.; Pi, X.; Yang, D. All-silicon multidimensionally-encoded optical physical unclonable functions for integrated circuit anti-counterfeiting. Nature Communications 2024, 15, 3203. [Google Scholar] [CrossRef]
- Chung, M.K.; Kim, M.U.; Han, J.W.; Yang, J.S.; Kim, B.J.; Jo, M.S.; Jung, S.Y.; Kim, S.H.; Yoon, J.B. Contribution of MEMS to Physical Unclonable Functions (PUFs): Random Configuration of PDMS Nano-Structure for Optical PUF. In Proceedings of the 2024 IEEE 37th International Conference on Micro Electro Mechanical Systems (MEMS); 2024; pp. 521–524. [Google Scholar] [CrossRef]
- Lu, X.; Hong, L.; Sengupta, K. CMOS optical PUFs using noise-immune process-sensitive photonic crystals incorporating passive variations for robustness. IEEE Journal of Solid-State Circuits 2018, 53, 2709–2721. [Google Scholar] [CrossRef]
- Wang, Y.; Xi, X.; Orshansky, M. Lattice PUF: A strong physical unclonable function provably secure against machine learning attacks. In Proceedings of the 2020 IEEE International Symposium on Hardware Oriented Security and Trust (HOST). IEEE; 2020; pp. 273–283. [Google Scholar]
- Zhou, Z.; Li, G.; Wang, P. A challenge-screening strategy for enhancing the stability of strong PUF based on machine learning. Microelectronics Journal 2023, 131, 105667. [Google Scholar] [CrossRef]
- Wu, L.; Hu, Y.; Zhang, K.; Li, W.; Xu, X.; Chang, W. Flam-puf: A response–feedback-based lightweight anti-machine-learning-attack puf. IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems 2022, 41, 4433–4444. [Google Scholar] [CrossRef]
- Zhu, B.; Jiang, X.; Huang, K.; Yu, M. A Response-Feedback-Based Strong PUF with Improved Strict Avalanche Criterion and Reliability. Sensors 2023, 24, 93. [Google Scholar] [CrossRef]
- Wang, Y.; Zhang, G.; Mei, X.; Gu, C. A High-Reliability, Non-CRP-Discard Arbiter PUF Based on Delay Difference Quantization. IEEE Transactions on Circuits and Systems I: Regular Papers, 2024; 1–13. [Google Scholar] [CrossRef]
- Wang, Y.; Wang, C.; Gu, C.; Cui, Y.; O’Neill, M.; Liu, W. A dynamically configurable PUF and dynamic matching authentication protocol. IEEE Transactions on Emerging Topics in Computing 2021, 10, 1091–1104. [Google Scholar] [CrossRef]
- Zhou, Z.; Wang, P.; Li, G. Bagua Protocol: A Whole-Process Configurable Protocol for IoT Sensing Devices Security Based on Strong PUF. IEEE Internet of Things Journal 2024, 11, 805–819. [Google Scholar] [CrossRef]
- Zhou, Z.; Li, G.; Wang, P.; Ye, M. Matrix encryption based anti-machine learning attack algorithm for strong PUF. In Proceedings of the 2021 IEEE 14th International Conference on ASIC (ASICON). IEEE; 2021; pp. 1–4. [Google Scholar]
- Tun, N.W.; Mambo, M. Secure PUF-Based Authentication Systems. Sensors 2024, 24, 5295. [Google Scholar] [CrossRef]
- Felicetti, C.; Lanuzza, M.; Rullo, A.; Saccà, D.; Crupi, F. Exploiting Silicon Fingerprint for Device Authentication Using CMOS-PUF and ECC. In Proceedings of the 2021 IEEE International Conference on Smart Internet of Things (SmartIoT); 2021; pp. 229–236. [Google Scholar] [CrossRef]
- Zhuang, Y.; Li, G. A lightweight PUF-based authentication protocol. arXiv preprint arXiv:2405.13146, arXiv:2405.13146 2024.
- Jin, C.; Burleson, W.; van Dijk, M.; Rührmair, U. Programmable access-controlled and generic erasable PUF design and its applications. Journal of Cryptographic Engineering 2022, 12, 413–432. [Google Scholar] [CrossRef]
- Li, H.; Cao, W.; Wang, C.; Zhu, X.; Liao, G.; He, Z. FOM-CDS PUF: A Novel Configurable Dual State Strong PUF Based on Feedback Obfuscation Mechanism against Modeling Attacks. IEICE Transactions on Fundamentals of Electronics, Communications and Computer Sciences 2023, 106, 1311–1321. [Google Scholar] [CrossRef]
- Dubrova, E.; Näslund, O.; Degen, B.; Gawell, A.; Yu, Y. CRC-PUF: A machine learning attack resistant lightweight PUF construction. In Proceedings of the 2019 IEEE European symposium on security and privacy workshops (EuroS&PW). IEEE, 2019, pp. 264–271.
- Zhang, Y.; He, Z.; Wan, M.; Liu, J.; Gu, H.; Zou, X. A SC PUF standard cell used for key generation and anti-invasive-attack protection. IEEE Transactions on Information Forensics and Security 2021, 16, 3958–3973. [Google Scholar] [CrossRef]
- Lee, S.; Oh, M.K.; Kang, Y.; Choi, D. RC PUF: A low-cost and an easy-to-design PUF for resource-constrained IoT devices. In Proceedings of the Information Security Applications: 20th International Conference, WISA 2019, Revised Selected Papers 20. Springer, 2020, pp. 275–285. Jeju Island, South Korea, 21–24 August 2019. [Google Scholar]
- Kroeger, T.; Cheng, W.; Guilley, S.; Danger, J.L.; Karimi, N. Assessment and Mitigation of Power Side-Channel-Based Cross-PUF Attacks on Arbiter-PUFs and Their Derivatives. IEEE Transactions on Very Large Scale Integration (VLSI) Systems 2022, 30, 187–200. [Google Scholar] [CrossRef]
- Wang, W.; Chen, Q.; Yin, Z.; Srivastava, G.; Gadekallu, T.R.; Alsolami, F.; Su, C. Blockchain and PUF-based lightweight authentication protocol for wireless medical sensor networks. IEEE Internet of Things Journal 2021, 9, 8883–8891. [Google Scholar] [CrossRef]
- Asif, R.; Ghanem, K.; Irvine, J. Proof-of-puf enabled blockchain: Concurrent data and device security for internet-of-energy. Sensors 2020, 21, 28. [Google Scholar] [CrossRef]
- Choi, S.; Zage, D.; Choe, Y.R.; Wasilow, B. Physically Unclonable Digital ID. In Proceedings of the 2015 IEEE International Conference on Mobile Services. IEEE; 2015; pp. 105–111. [Google Scholar]
- P, S.; Krishnammal, P.M. Study of different silicon Physical Unclonable Functions. In Proceedings of the 2016 International Conference on Wireless Communications, Signal Processing and Networking (WiSPNET); 2016; pp. 81–85. [Google Scholar] [CrossRef]
- Joshi, S.; Mohanty, S.P.; Kougianos, E. Everything you wanted to know about PUFs. IEEE Potentials 2017, 36, 38–46. [Google Scholar] [CrossRef]
- Ram, S.K.; Sahoo, S.R.; Das, B.B.; Mahapatra, K.; Mohanty, S.P. Securing Things: A Novel CRO Applicable in PUF and Recycled IC Detection. 2022. [Google Scholar]
- Bhargava, M. Reliable, secure, efficient physical unclonable functions. PhD thesis, Carnegie Mellon University, 2013.
- Schaub, A.; Danger, J.L.; Rioul, O.; Guilley, S. The big picture of delay-PUF dependability. In Proceedings of the 2020 European Conference on Circuit Theory and Design (ECCTD). IEEE; 2020; pp. 1–4. [Google Scholar]
- Jouini, Z.C.; Danger, J.L.; Bossuet, L. Performance evaluation of physically unclonable function by delay statistics. In Proceedings of the 2011 IEEE 9th International New Circuits and systems conference. IEEE; 2011; pp. 482–485. [Google Scholar]
- Fedorkow, G.; Hardjono, T. Mind Your Roots of Trust! Authorea Preprints 2024. [Google Scholar]
- CYSEC. Securing Edge Devices: The Crucial Role of Root of Trust in a Connected World. https://www.cysec.com/iot-edge/, year = accessed October 30, 2024.
- Knowledge Center, S.E. Root of Trust: Trusted environment for secure functions. https://semiengineering.com/knowledge_centers/semiconductor-security/root-of-trust/, year = accessed October 30, 2024.
- Zimmer, V.; Krau, M. Establishing the root of trust. UEFI. org document dated August 2016. [Google Scholar]
- Ehret, A.; Moore, P.; Stojkov, M.; Kinsy, M.A. Hardware Root-of-Trust Support for Operational Technology Cybersecurity in Critical Infrastructures. In Proceedings of the 2023 IEEE High Performance Extreme Computing Conference (HPEC). IEEE; 2023; pp. 1–7. [Google Scholar]
- Chaintoutis, C.; Akriotou, M.; Mesaritakis, C.; Komnios, I.; Karamitros, D.; Fragkos, A.; Syvridis, D. Optical PUFs as physical root of trust for blockchain-driven applications. IET Software 2019, 13, 182–186. [Google Scholar] [CrossRef]
- Rojas-Muñoz, L.F.; Sánchez-Solano, S.; Martínez-Rodríguez, M.C.; Camacho-Ruiz, E.; Navarro-Torrero, P.; Karmakar, A.; Fernández-García, C.; Tena-Sánchez, E.; Potestad-Ordóñez, F.E.; Casado-Galán, A.; et al. Cryptographic Security Through a Hardware Root of Trust. In Proceedings of the International Symposium on Applied Reconfigurable Computing. Springer; 2024; pp. 106–119. [Google Scholar]
- Chuang, K.K.H.; Chen, H.M.; Wu, M.Y.; Yang, E.C.S.; Hsu, C.C.H. Quantum Tunneling PUF: A Chip Fingerprint for Hardware Security. In Proceedings of the 2021 International Symposium on VLSI Technology, Systems and Applications (VLSI-TSA); 2021; pp. 1–2. [Google Scholar] [CrossRef]
- Hamadeh, H.; Tyagi, A. Physical unclonable functions (pufs) entangled trusted computing base. In Proceedings of the 2019 IEEE International Symposium on Smart Electronic Systems (iSES)(Formerly iNiS). IEEE; 2019; pp. 177–180. [Google Scholar]
- Bathalapalli, V.K.; Mohanty, S.P.; Kougianos, E.; Iyer, V.; Rout, B. PUFchain 4. 0: Integrating PUF-based TPM in distributed ledger for security-by-design of IoT. In Proceedings of the Proceedings of the Great Lakes Symposium on VLSI 2023, 2023, pp. 231–236. [Google Scholar]
- Colombier, B.; Bossuet, L.; Fischer, V.; Hély, D. Key reconciliation protocols for error correction of silicon PUF responses. IEEE Transactions on Information Forensics and Security 2017, 12, 1988–2002. [Google Scholar] [CrossRef]
- Schrijen, G.J.; Garlati, C. Physical unclonable functions to the rescue. Proceedings of the Embedded World 2018. [Google Scholar]
- Dave McCarthy, P.R.; Kanaracus, C. Increasing Intelligence at the Edge with AI. Technical report, International Data Corporation (IDC), 2022.
- Ahmad, J.; Jervis, M.; Venkata, R. Intel® FPGAs and SoCs with Intel® FPGA AI Suite and OpenVINO Toolkit Drive Embedded/Edge AI/Machine Learning Applications.
- Xu, C.; Jiang, S.; Luo, G.; Sun, G.; An, N.; Huang, G.; Liu, X. The Case for FPGA-Based Edge Computing. IEEE Transactions on Mobile Computing 2022, 21, 2610–2619. [Google Scholar] [CrossRef]
- Al-Asli, M.; Elrabaa, M.E.; Abu-Amara, M. FPGA-based symmetric re-encryption scheme to secure data processing for cloud-integrated internet of things. IEEE Internet of Things Journal 2018, 6, 446–457. [Google Scholar] [CrossRef]
- Martínez-Rodríguez, M.C.; Rojas-Muñoz, L.F.; Camacho-Ruiz, E.; Sánchez-Solano, S.; Brox, P. Efficient RO-PUF for generation of identifiers and keys in resource-constrained embedded systems. Cryptography 2022, 6, 51. [Google Scholar] [CrossRef]
- Mukhtar, N.; Mehrabi, A.; Kong, Y.; Anjum, A. Edge enhanced deep learning system for IoT edge device security analytics. Concurrency and Computation: Practice and Experience 2021, p. e6764.
- Huffmire, T.; Brotherton, B.; Sherwood, T.; Kastner, R.; Levin, T.; Nguyen, T.D.; Irvine, C. Managing security in FPGA-based embedded systems. IEEE Design & Test of Computers 2008, 25, 590–598. [Google Scholar]
- Kolosov, D.; Kelefouras, V.; Kourtessis, P.; Mporas, I. Anatomy of Deep Learning Image Classification and Object Detection on Commercial Edge Devices: A Case Study on Face Mask Detection. IEEE Access 2022, 10, 109167–109186. [Google Scholar] [CrossRef]
- Vitis AI Library User Guide - UG1354 (v2.0) January 20, 2022. pp. 1–401.
- Rahman, A.; Hassanain, E.; Hossain, M.S. Towards a secure mobile edge computing framework for Hajj. IEEE Access 2017, 5, 11768–11781. [Google Scholar] [CrossRef]
- Cao, K.; Liu, Y.; Meng, G.; Sun, Q. An overview on edge computing research. IEEE access 2020, 8, 85714–85728. [Google Scholar] [CrossRef]
- Yang, Q.; Liu, Y.; Chen, T.; Tong, Y. Federated machine learning: Concept and applications. ACM Transactions on Intelligent Systems and Technology (TIST) 2019, 10, 1–19. [Google Scholar] [CrossRef]
- Cui, Z.; Zhao, P.; Hu, Z.; Cai, X.; Zhang, W.; Chen, J. An improved matrix factorization based model for many-objective optimization recommendation. Information Sciences 2021, 579, 1–14. [Google Scholar] [CrossRef]
- Zhai, K.; Ren, Q.; Wang, J.; Yan, C. Byzantine-robust federated learning via credibility assessment on non-IID data. arXiv preprint arXiv:2109.02396, arXiv:2109.02396 2021.
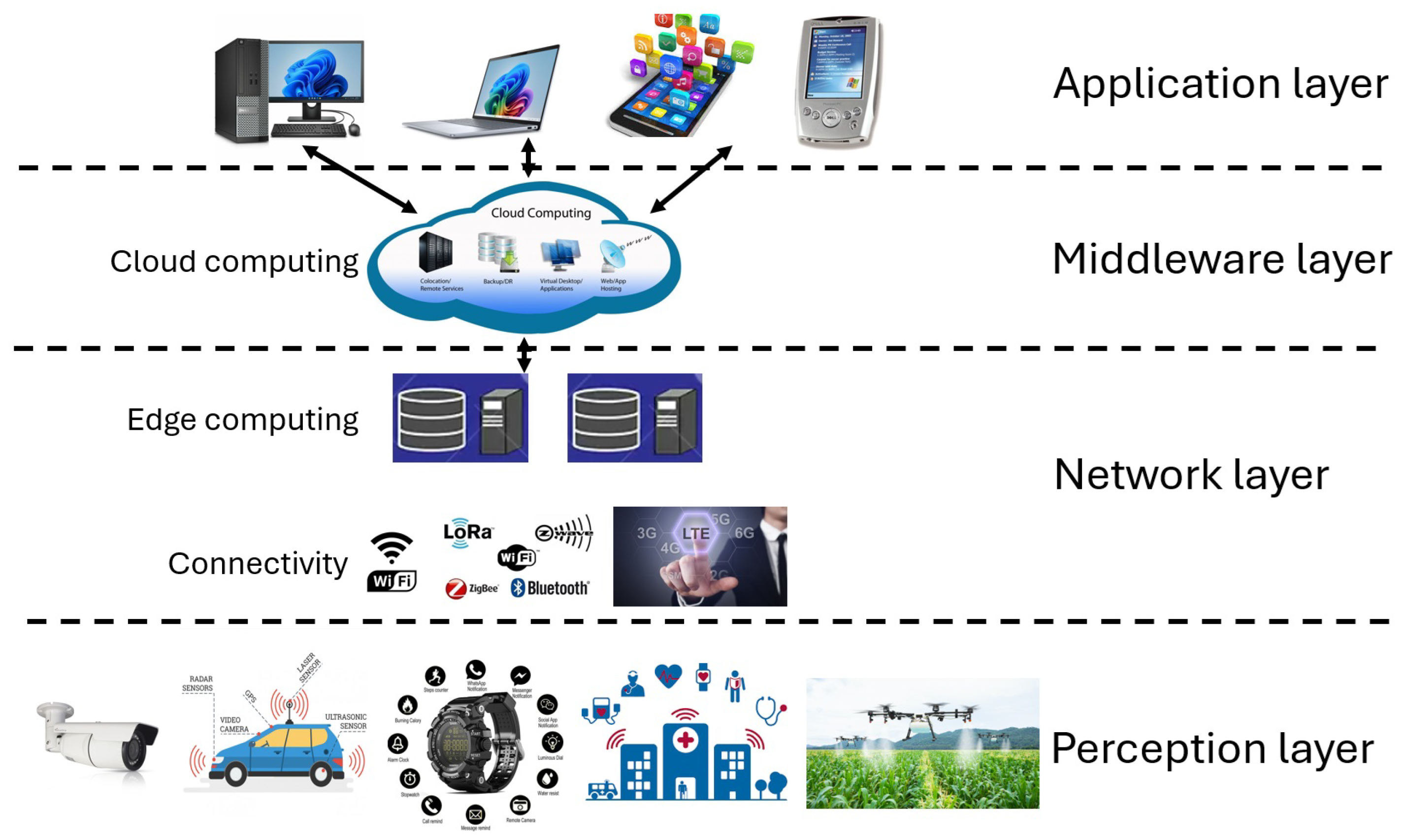
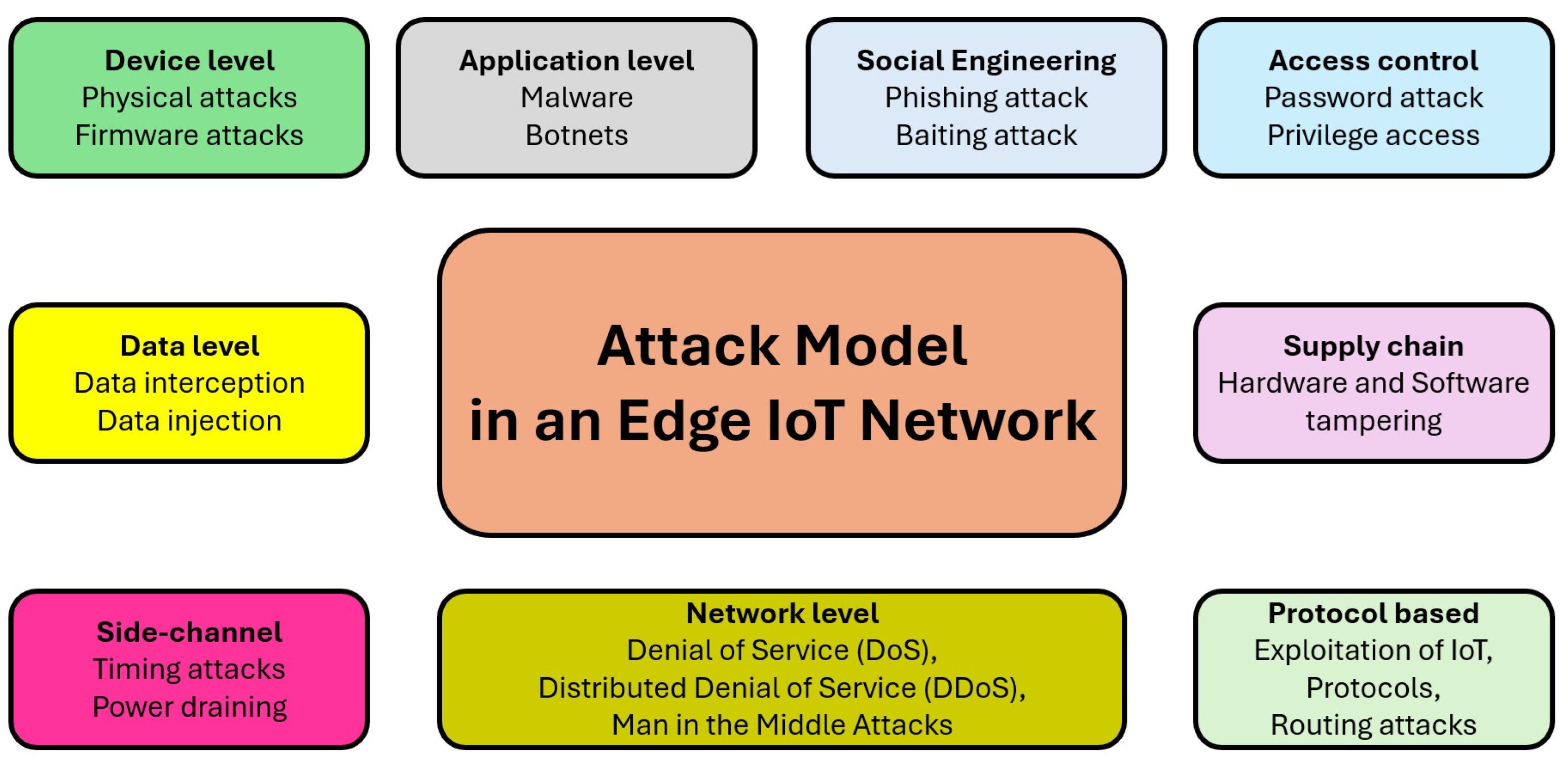
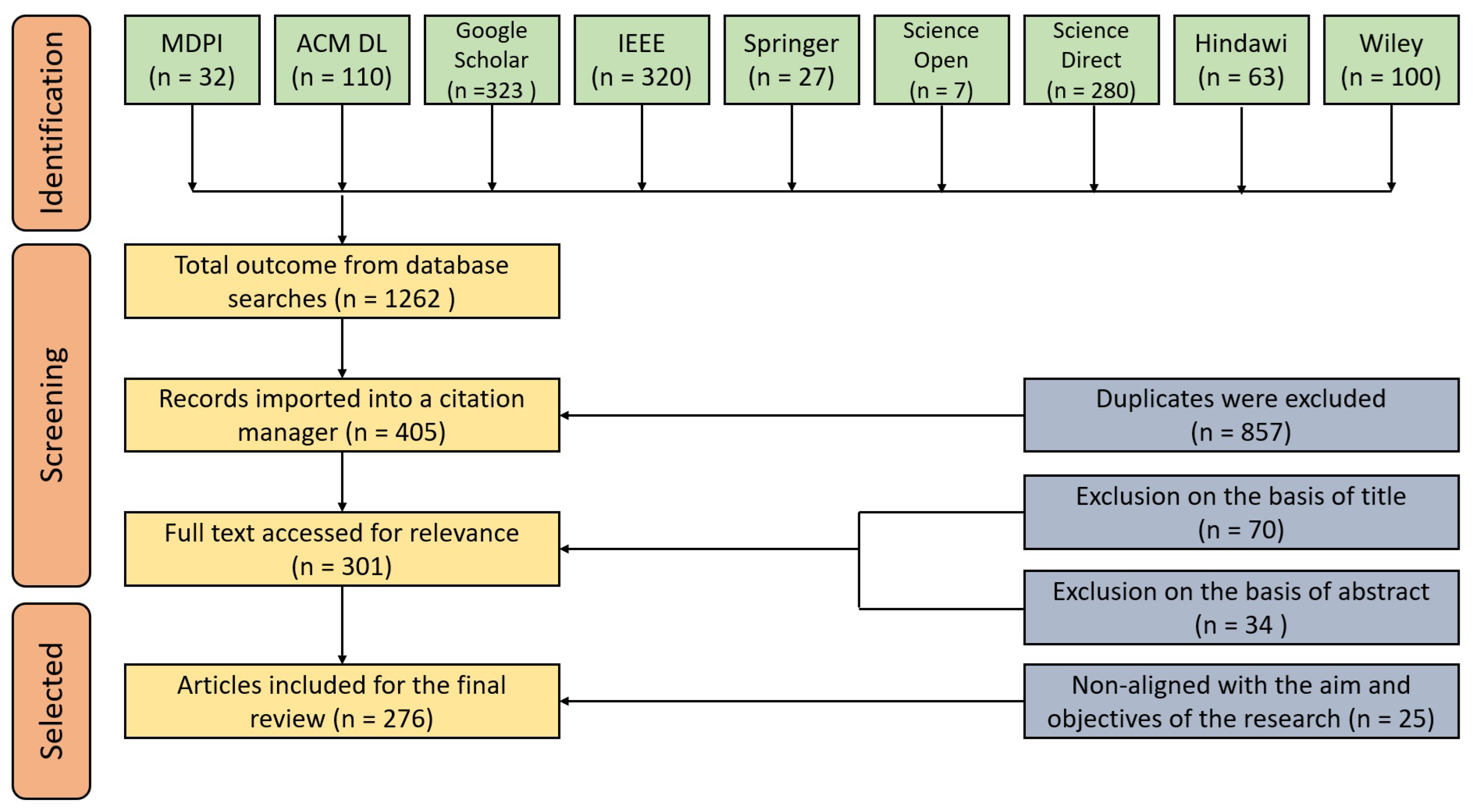
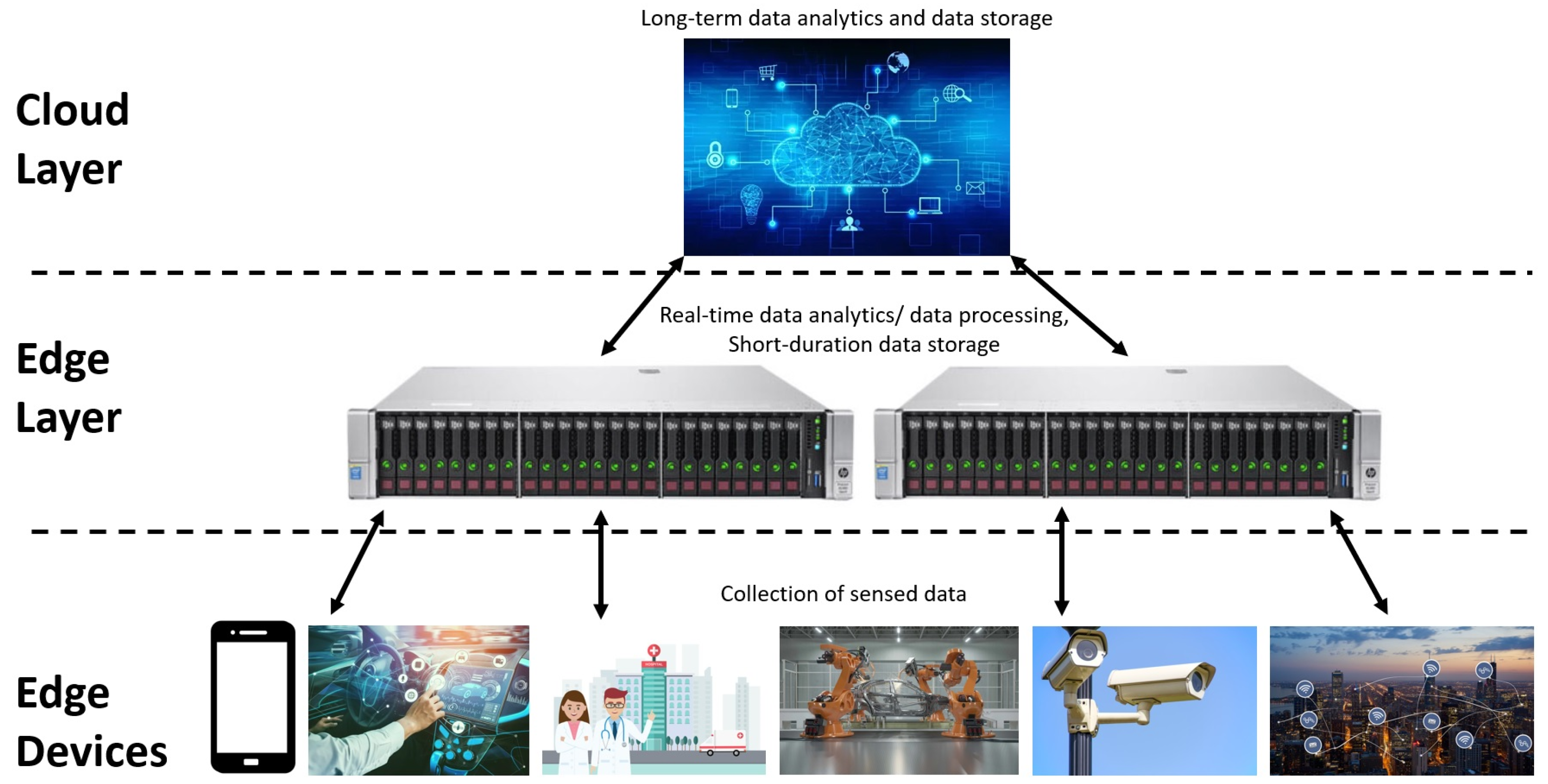
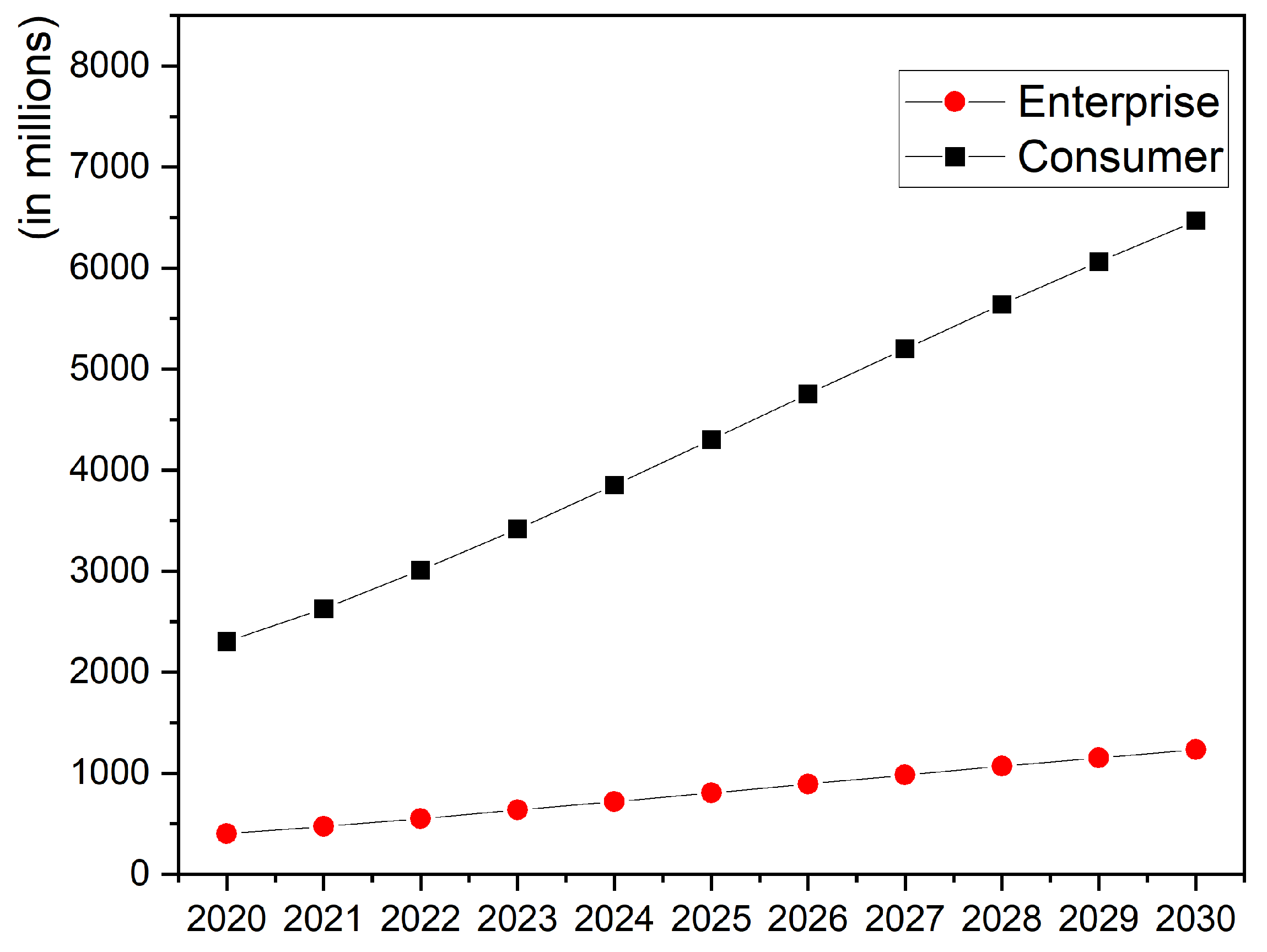
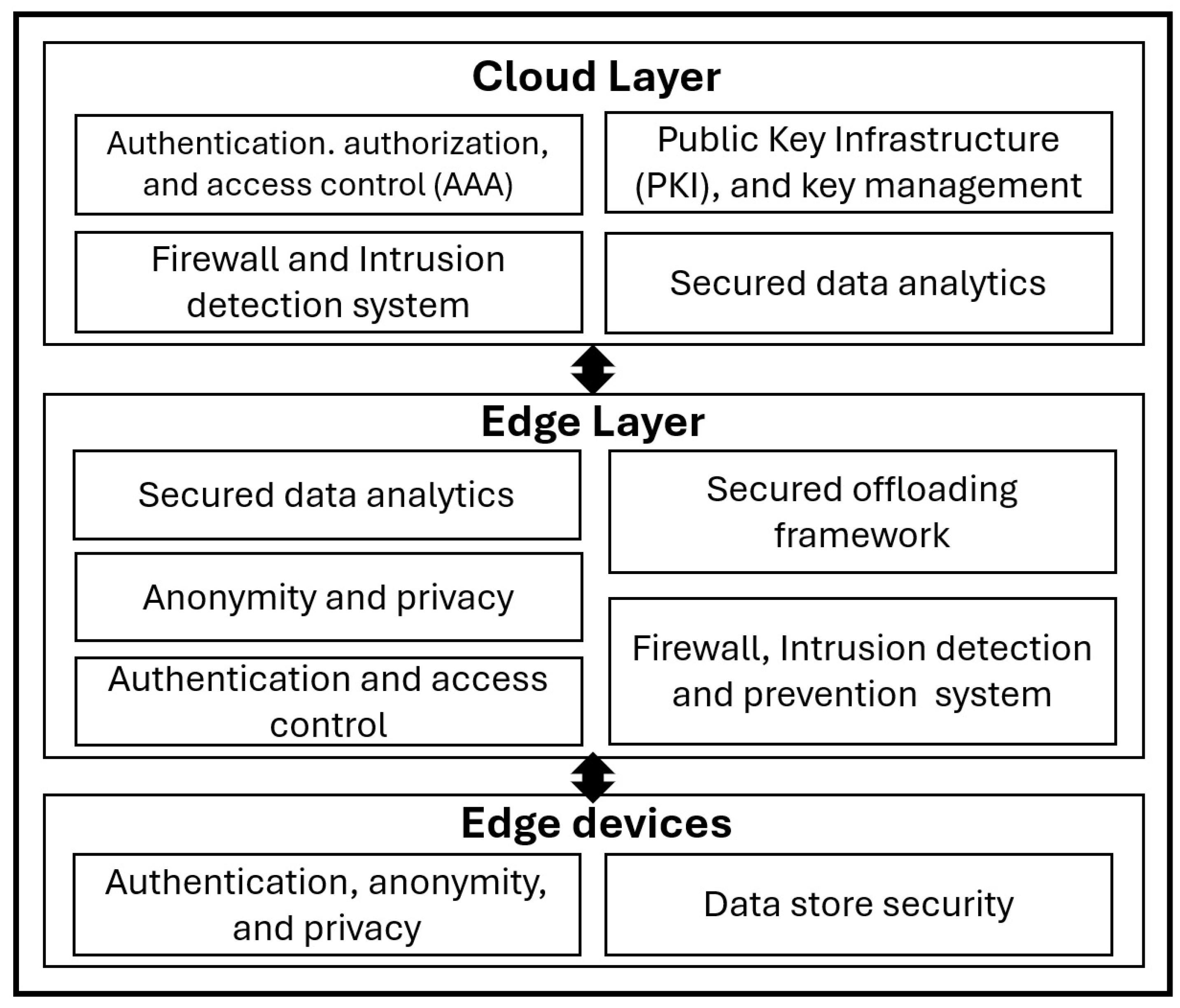
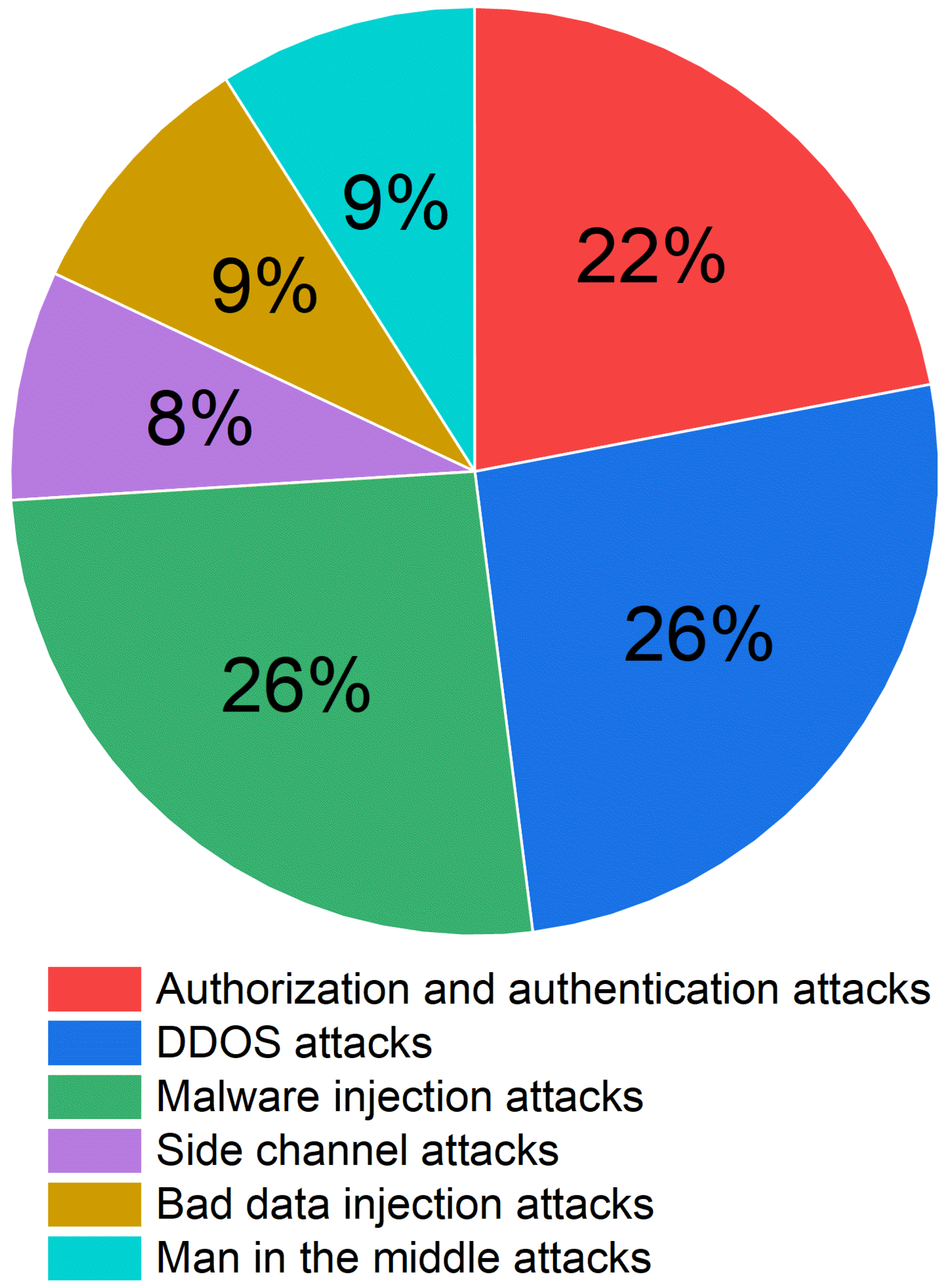
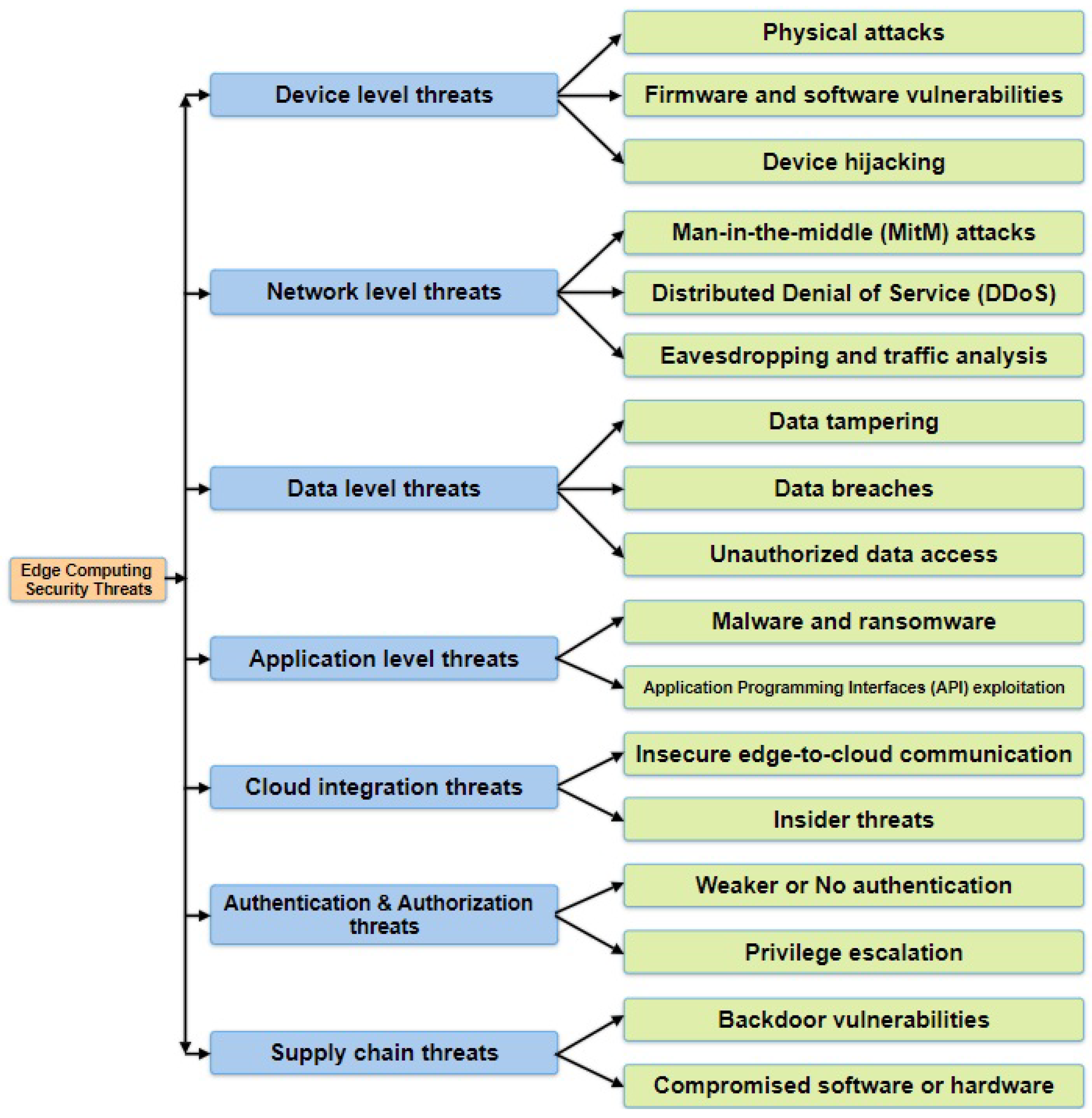
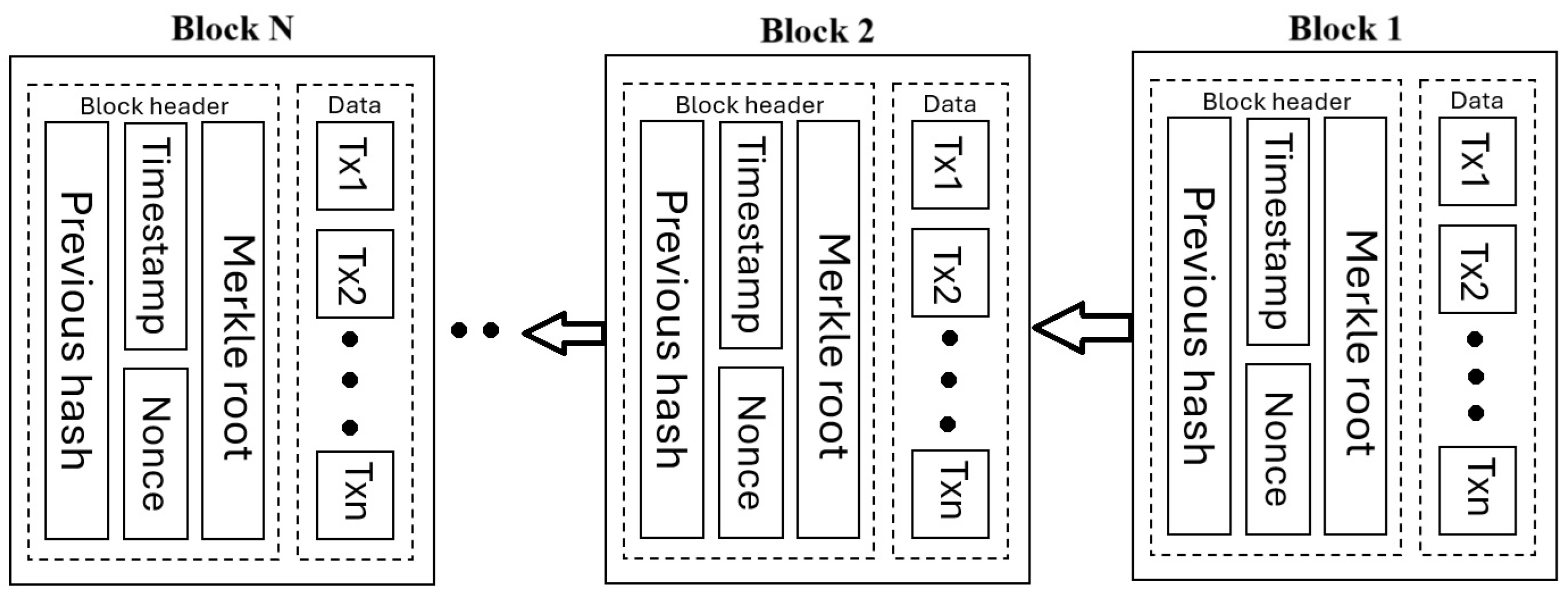
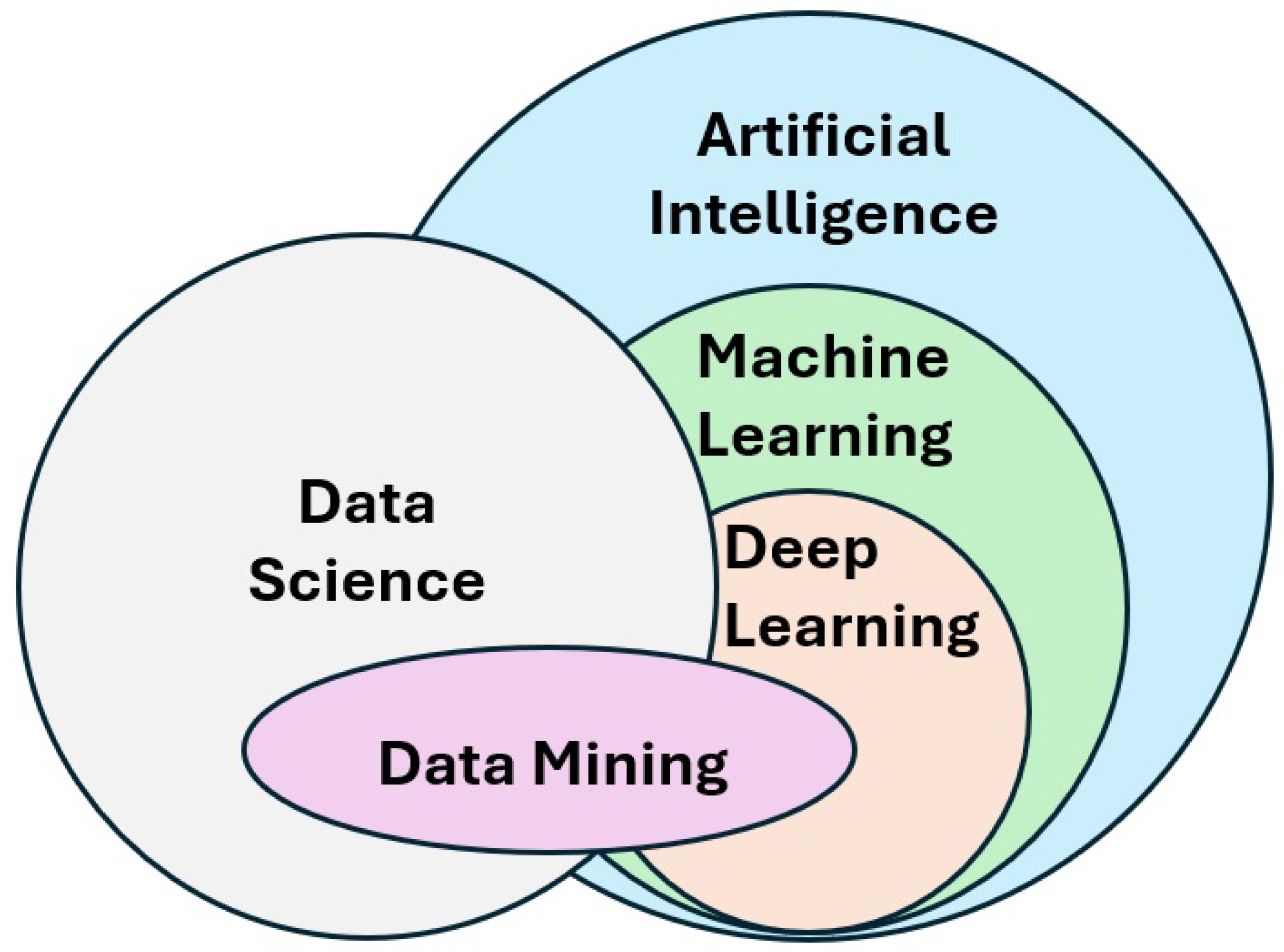
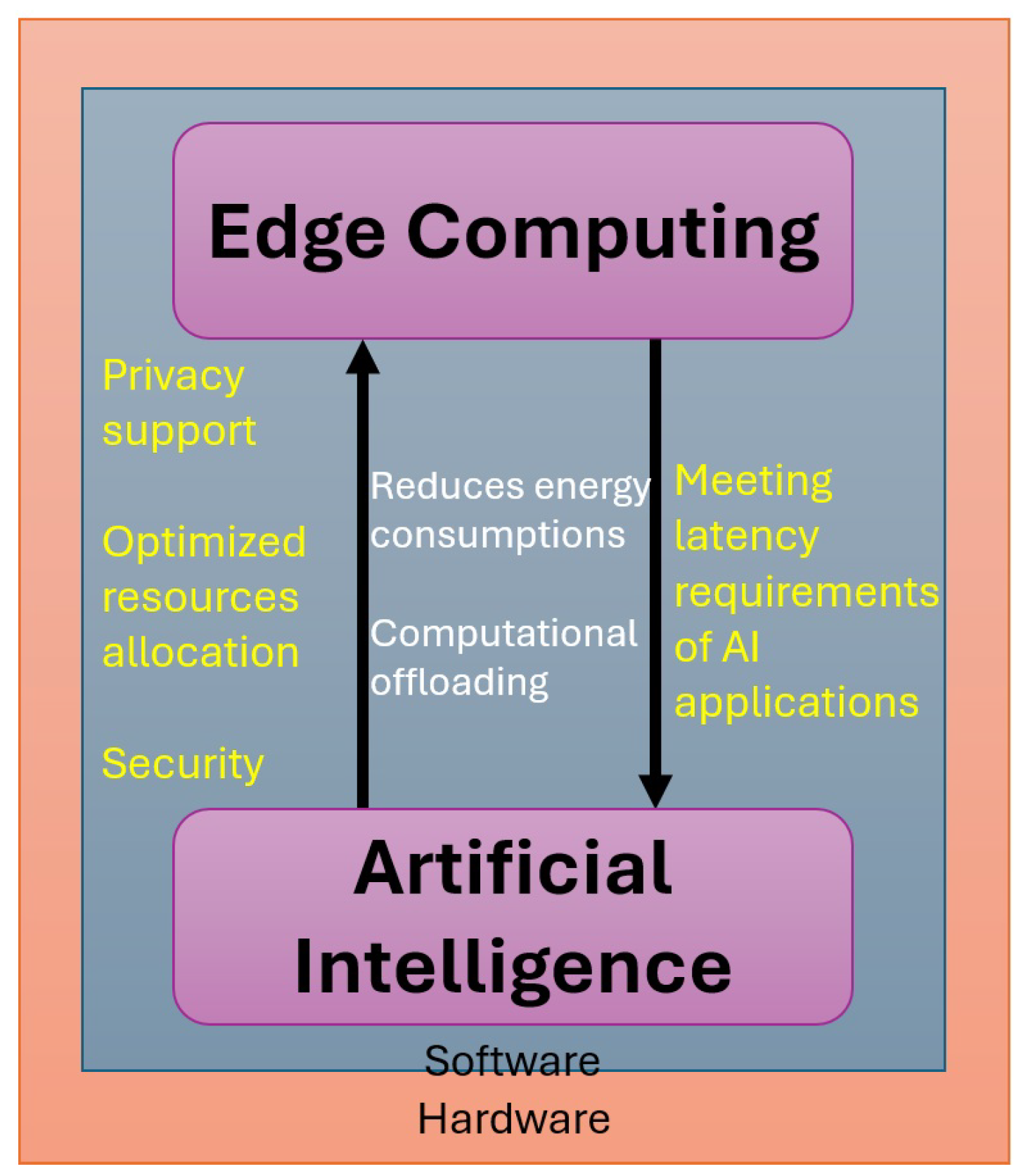
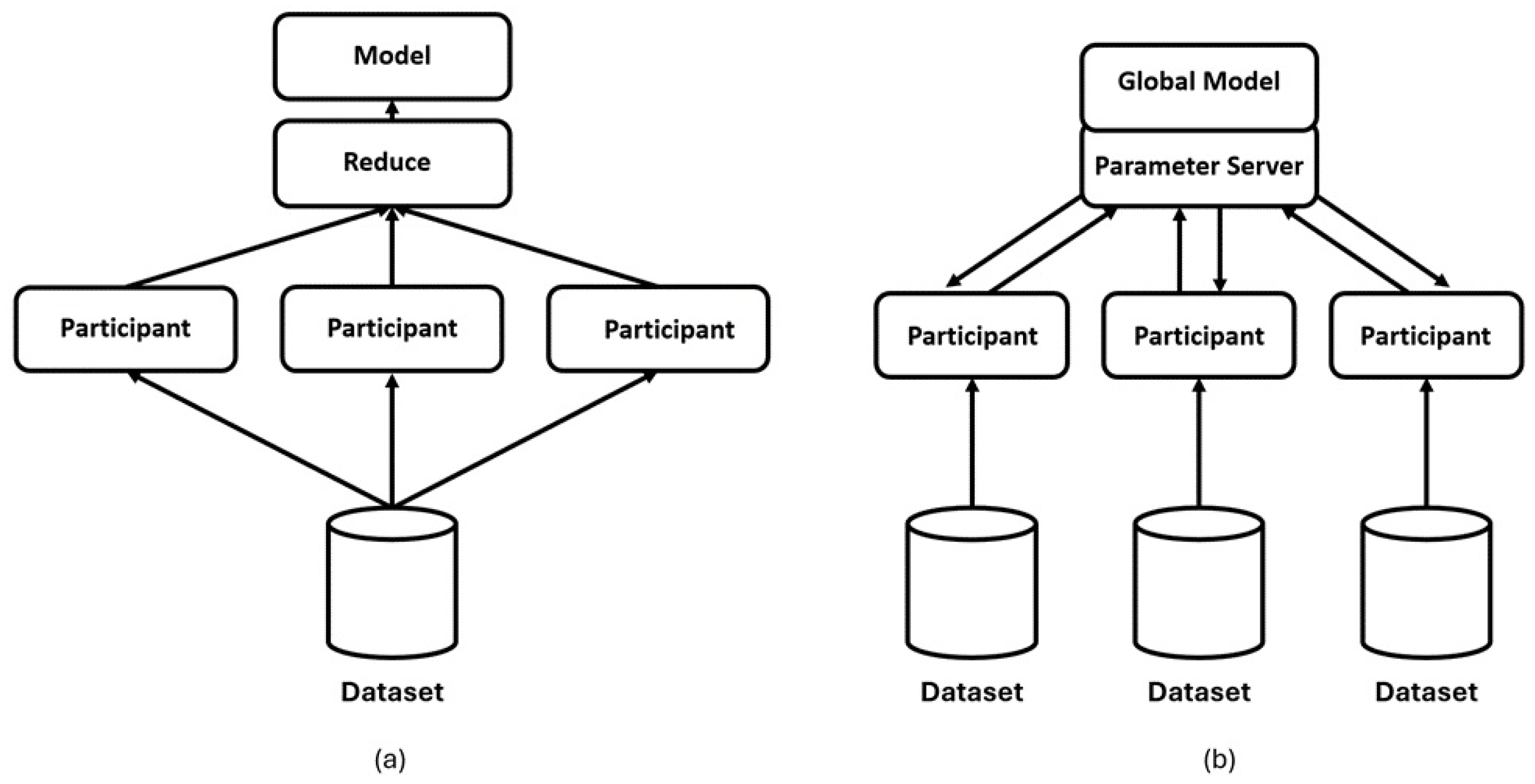
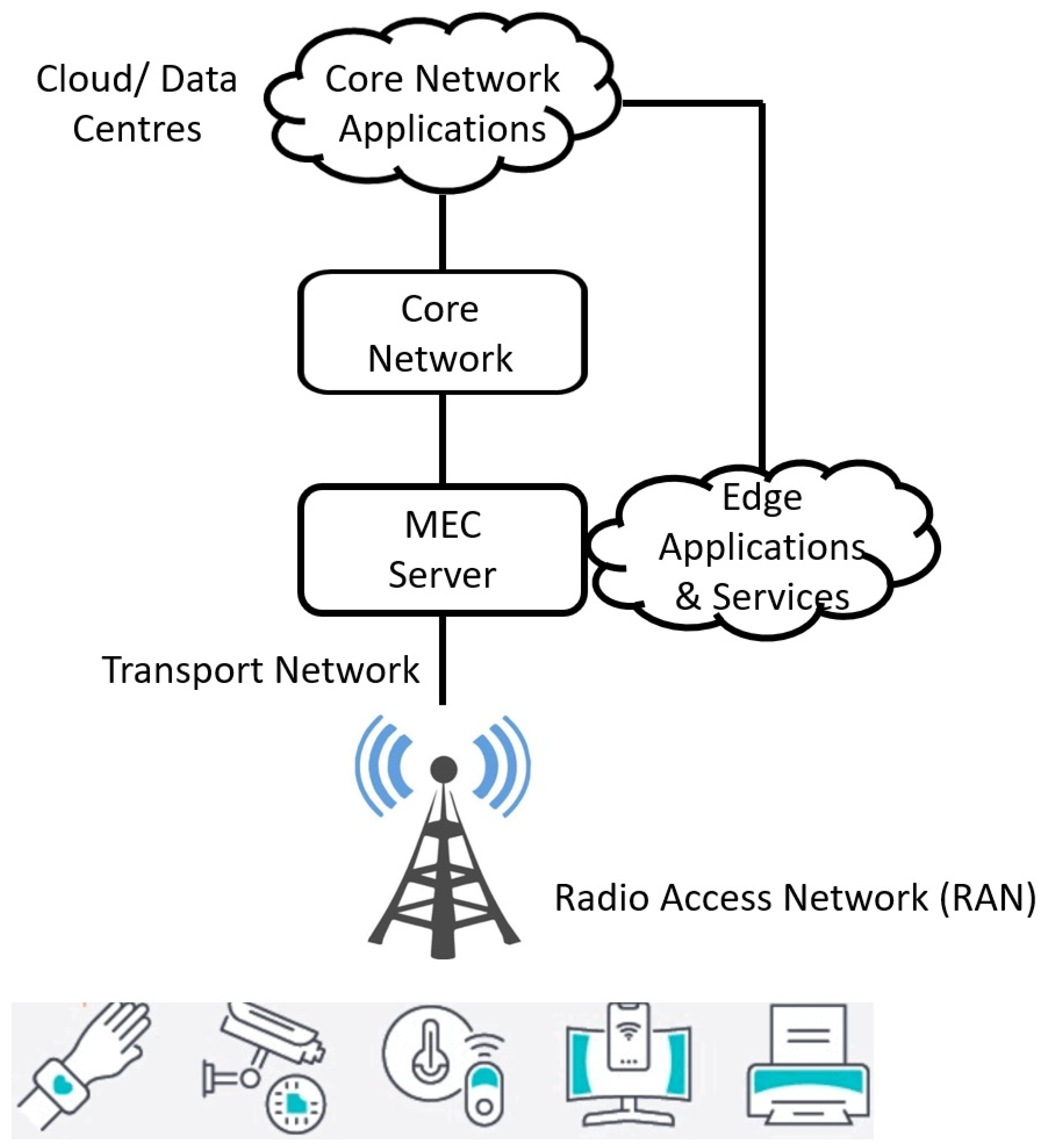
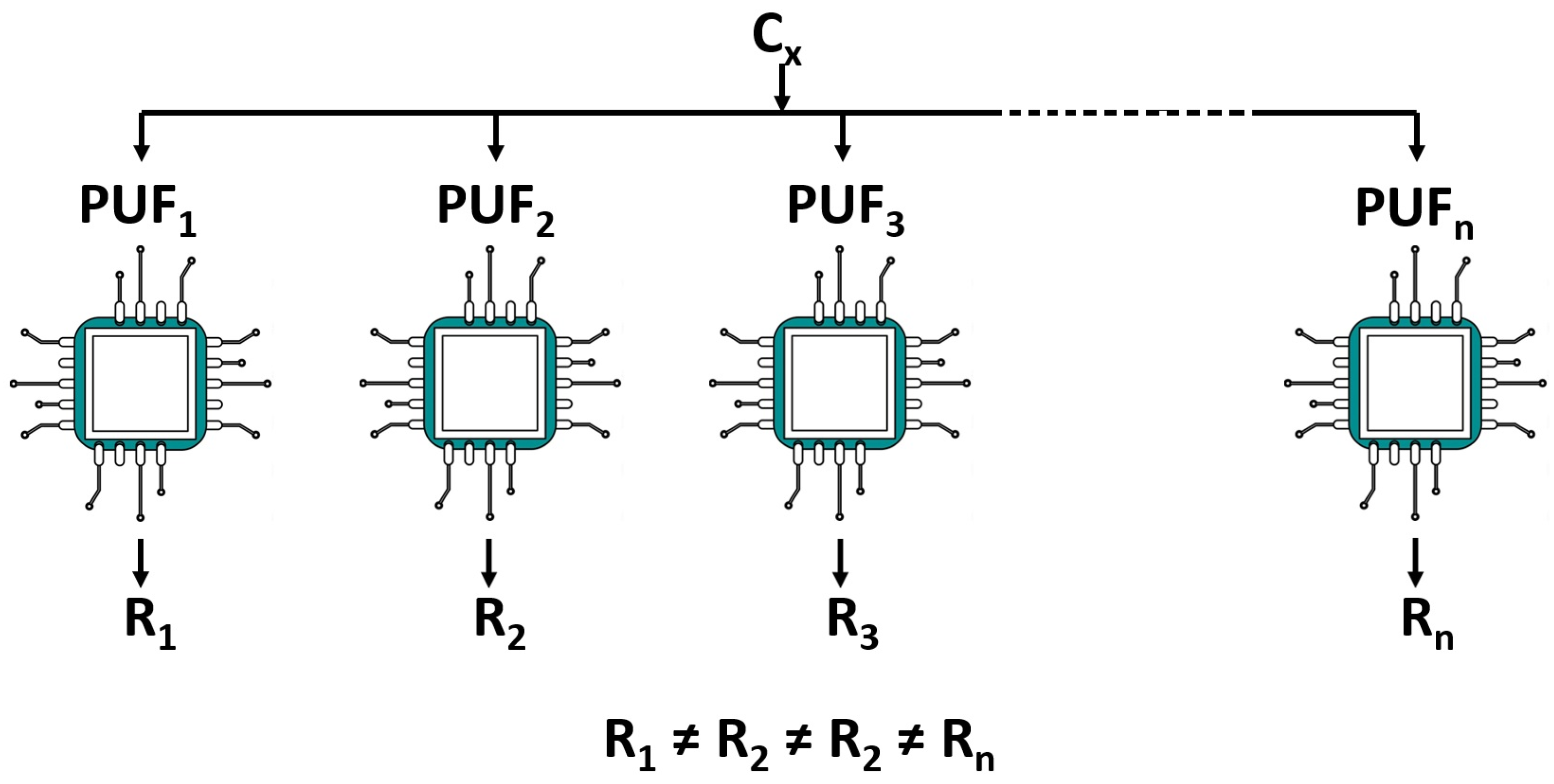
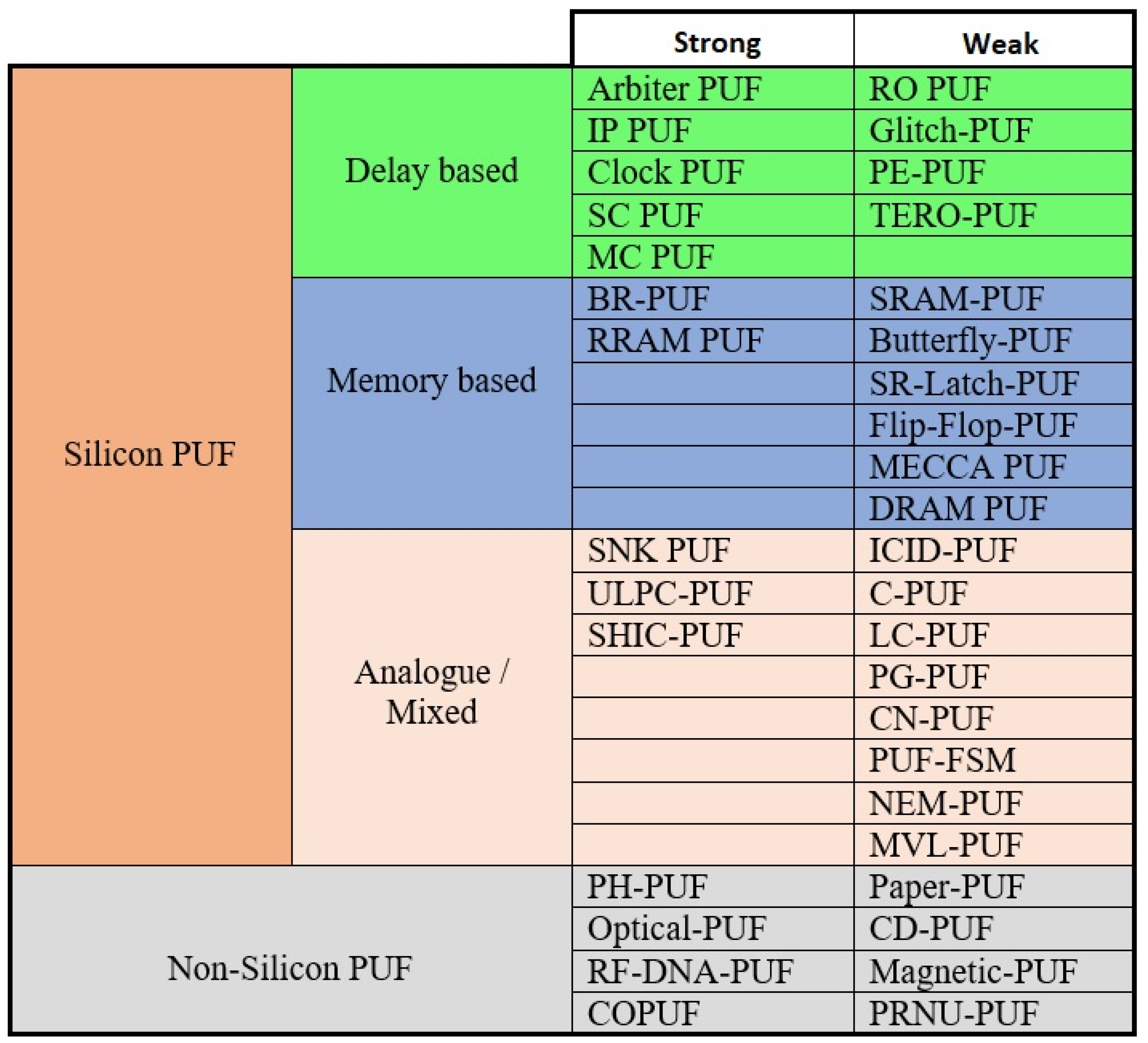
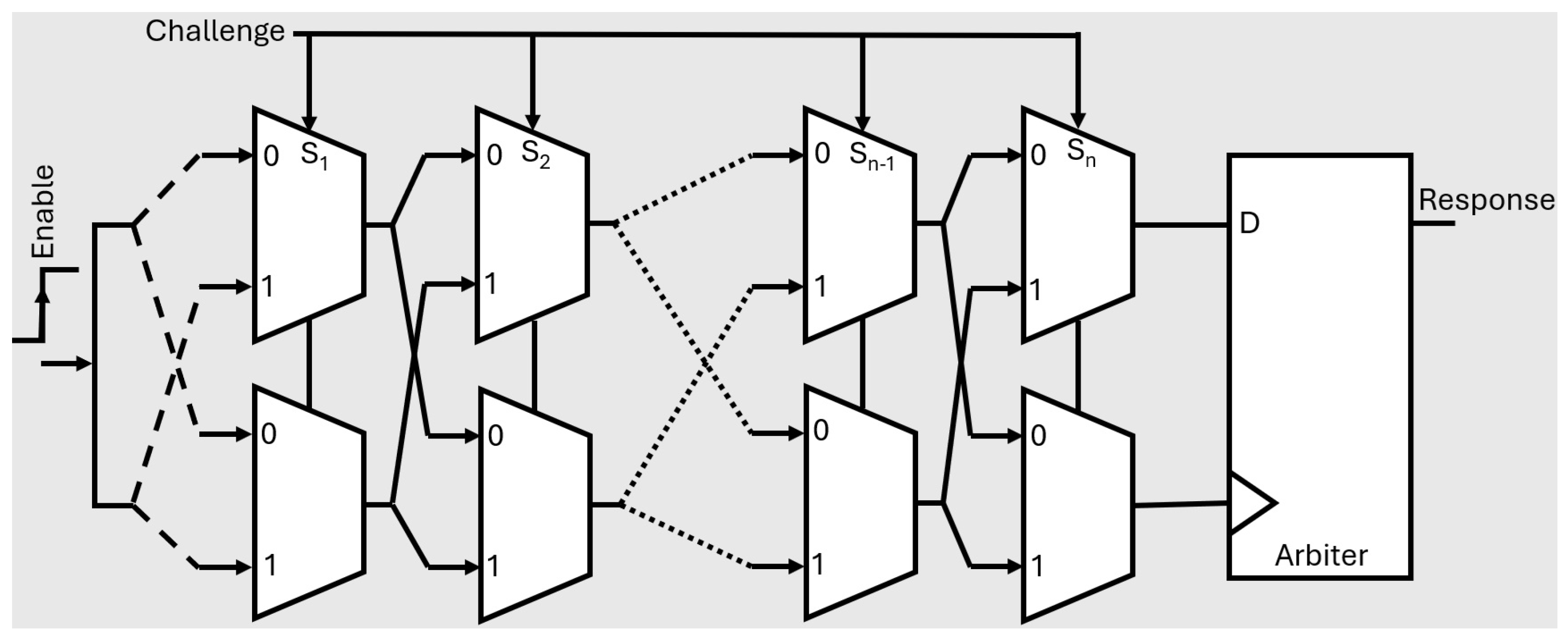
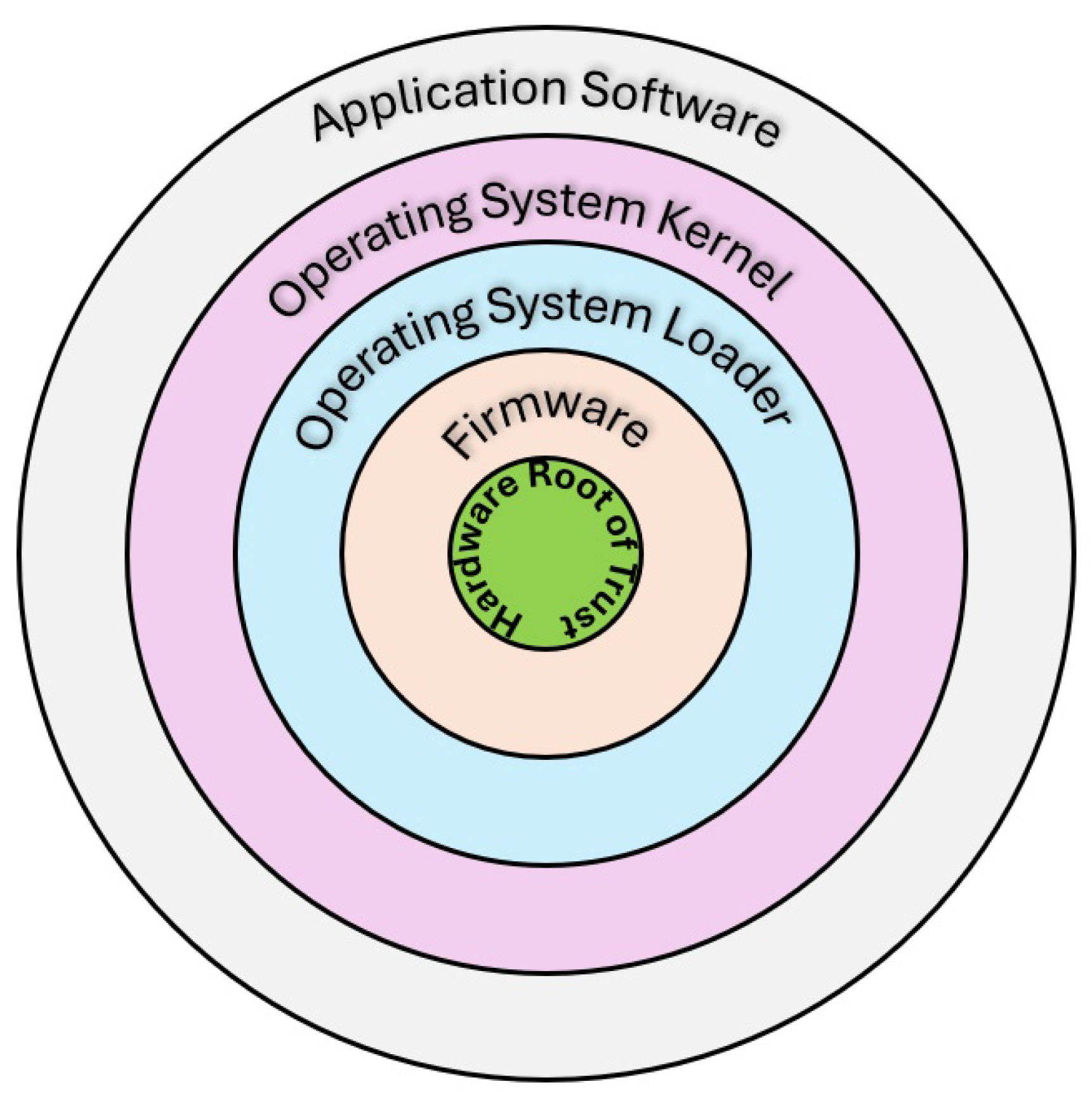
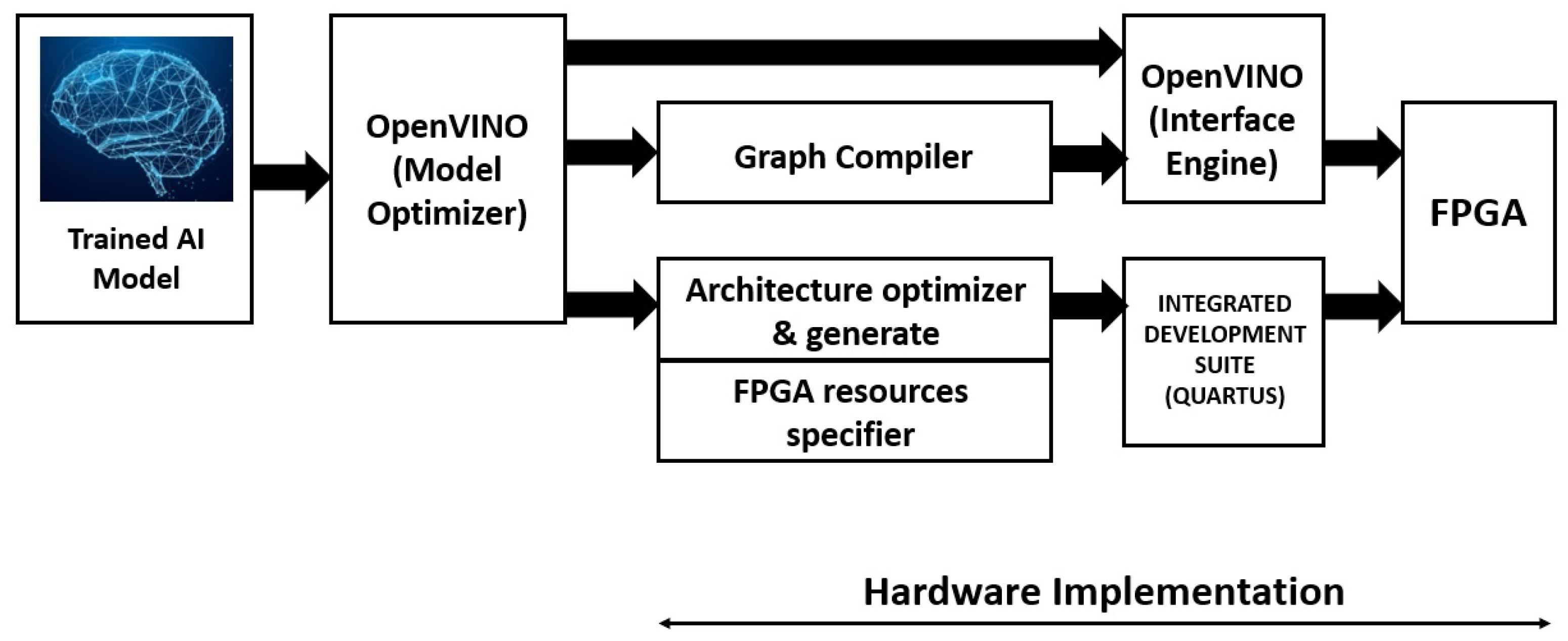
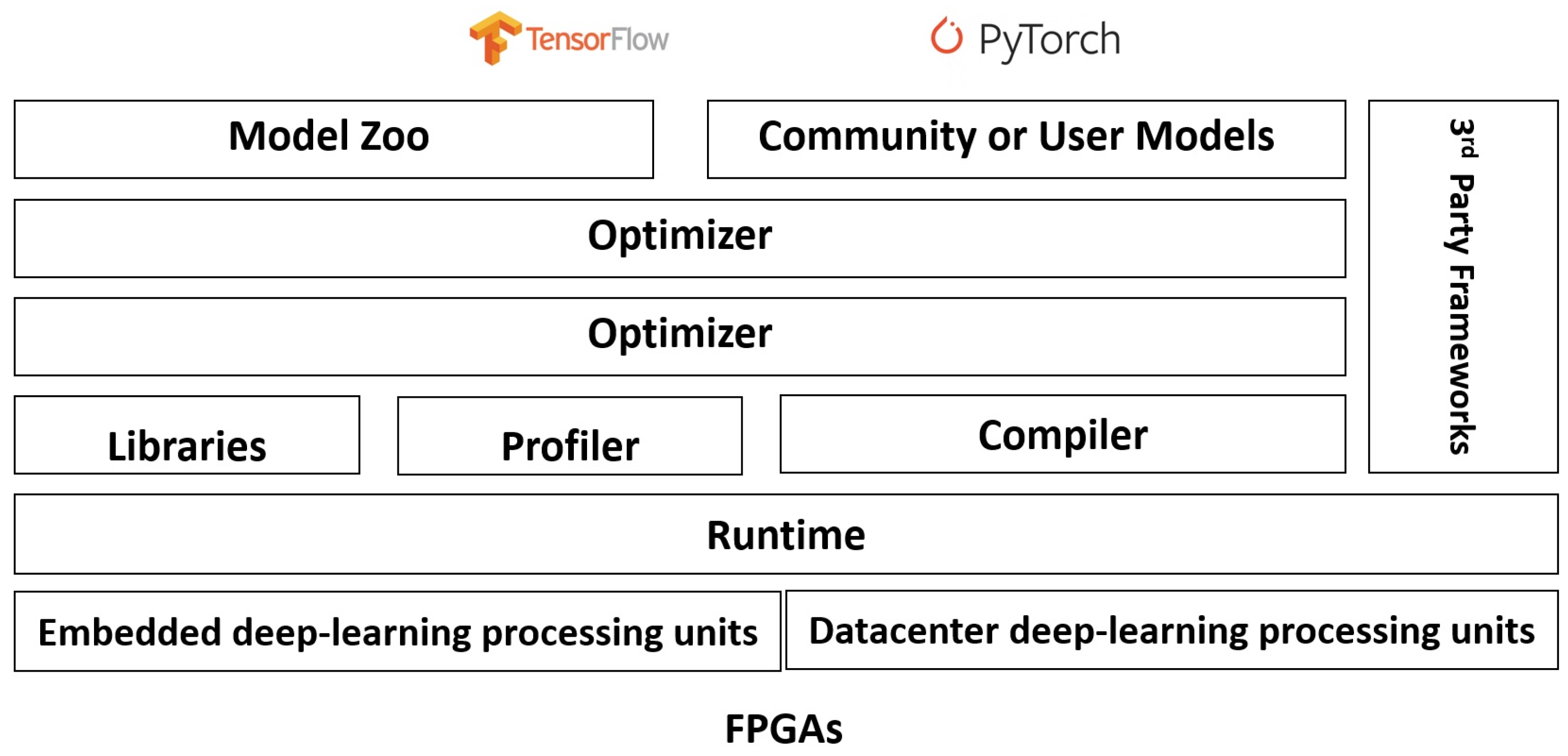
| Reference | Scope | Focus | Limitations |
|---|---|---|---|
| [7,10,59,62,63,64,65,66] | Review of Opportunities and Challenges in EC | Conversations on EC-assisted IoT architectures, data security and privacy-related challenges alongside insights into potential future research directions. Implementation of AI/ ML-assisted cryptography algorithms and protocols is crucial for ensuring reliable access and control over network, storage, and computation across numerous distributed edge nodes. | Limited resources at edge devices act as a barrier in terms of scalability, and flexibility issues. Also, cryptography protocols have difficulty protecting endless data streams or as the data arrives [67]. |
| [17,68,69,70] | Network security architecture | Secure access service edge (SASE) network architecture integrated with Virtual Private Network (VPN) and software-defined wide area network (SD-WAN) characteristics ensures secured web gateways, firewalls, and zero-trust network access. | Converging network access and security into a single network architectural model may be a challenge. |
| [18,49,58,71,72,73] | ML and deep learning (DL) models in the context of Edge security. | Discussion on centralized, decentralized, and hybrid architectures implementing AI at the edge as well as technologies like federated learning, model compression, gradient compression, DNN splitting, and gossip-based training. | Maintaining and updating the ML models over time and training on the cloud. |
| [74,75,76,77,78] | Intrusion detection system. | Host-based Intrusion Detection Systems (HIDS) monitor individual devices, while Network-based Intrusion Detection Systems (NIDS) analyze network traffic for potential threats. | The limited computational and storage capabilities of edge nodes limit the processing or storage of large-scale data. |
| [79,80,81,82] | PUF enabled digital fingerprint | PUFs utilize the distinctive physical traits of edge devices to offer robust authentication, secure key management, and tamper resistance while eliminating the need for stored cryptographic keys. | Highly sensitive to environmental factors like temperature, voltage, and electromagnetic interference, PUFs exhibit unique challenge-response pairs (CRPs) and are vulnerable to machine learning attacks. |
| Characteristics | Cloud computing | Edge computing |
|---|---|---|
| Deployment | Centralized | Distributed |
| Latency | High | Low |
| Computational | Unlimited | Limited |
| Storage | Unlimited | Limited |
| Scalability | High | Low |
| Privacy | High risk | Data stays at source |
| Security | A robust security plan, and proactive monitoring against attacks is required | It requires, to a lesser degree, a powerful security plan |
| Strategy | Description |
|---|---|
| Edge Node Security | Uniform security levels are applied at edge nodes to ensure appropriate safety protocols. Different security levels may allow attackers to break through the nodes with weaker security algorithms. |
| Full-time Monitoring | Warrants nonstop monitoring of edge nodes while offering network clarity to users through a collaborating interface. |
| Proper Encryption | A complicated algorithm or a secure password exchanged exclusively between legitimate senders and recipients, granting access solely to genuine users. |
| Intrusion Detection System | Identifies any abnormality or illegal access and alerts the user in case of dubious activities. |
| User Behavior Profiling | Maintaining a record of users’ behavior and keeping track of activities apart from normal behavior to detect an attacker’s presence. |
| Cryptographic Techniques | Secures significant data using codes that block security attacks through a secret key. |
| Data Confidentiality | Mitigates privacy concerns while restricting unauthorized data transactions, data loss, data tampering, data breaches, and related issues. |
| Article | PUF type | Stages | Uniqueness [mean (std)] | Uniformity [mean (std)] | Reliability [mean (std)] |
|---|---|---|---|---|---|
| [222] | Lattice PUF | 1000 | 50.00% (1.58%) | 49.98% (1.58%) | 1.26% (2.88%) |
| [224] | FLAM-PUF | 64/128 | 49.73% / 49.99% | 49.81% / 49.85% | 95.59%/96.58% |
| [225] | Strong response-feedback PUF | 32/64/128 | 50.17 (1.41) / 50.00 (0.31) / 49.99 (0.21) | 49.54 (3.67)/ 50.05 (2.79)/ 49.93 (1.78) | - |
| [226] | DDQ-APUF | 64/ 128 | 47.28%/ 47.65% | 50%/ 50% | 99.95%/ 99.91% |
| [234] | FOM-CDS PUF | 17 | 47.38%(RO mode)/ 53.79% (TERO mode)/ 50.33% (Full mode) | 47.71% (RO mode)/ 56.23% (TERO mode)/ 53.68% (Full mode) | 3.1% CRO-PUF/ 9.14% Dual mode/ 7.91% FOM-CDS PUF |
| [235] | CRC-PUF | 128 | 49.9978% | 50.0777% | - |
| [237] | RC-PUF | 32 | 27.3% (bit delay = 2 us)/ 30.9% (bit delay = 32 us) | 50.3% (bit delay = 2 us)/ 50.3% (bit delay = 32 us) | 96.2% (bit delay = 2 us)/ 98.5% (bit delay = 32 us) |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).