Submitted:
27 February 2025
Posted:
03 March 2025
You are already at the latest version
Abstract
The rise of online activities and the increasing prevalence of artificial intelligence (AI) in sociotechnical systems have brought about both significant opportunities and ethical challenges. Among these challenges, one of the most relevant is addressing digital threats such as sexual exploitation leading to sextortion (a form of coercion) that disproportionately affects vulnerable groups, such as minors. This paper advocates the integration of blockchain technology into AI systems to enhance trust, transparency, and ethical governance in combating such threats. The paper argues that by adhering to ethical guidelines through the integration of blockchain operations that bring about strong decentralization, immutability, and auditability, ethical issues in AI are better managed. The paper adopts a mixed research approach of qualitative analyses and conceptual model to develop some set of blockchain-integrated AI operations. Through a literature review of related works on sexual exploitation leading to sextortion, we first identified digital technologies that enable sexual exploitation, the role of AI in mitigating sexual exploitations, ethical issues in these AI applications and blockchain concepts that address them. Then we adopted BPMN modelling to conceptually describe blockchain operations that will limit AI ethical risks. The paper highlights the critical intersection of ethical AI development, social resilience, and digital ethics and addresses the complexities of integrating technologies while emphasizing the need for interdisciplinary collaboration for developing AI applications that address social issues.
Keywords:
1. Introduction
2. Preliminaries
2.1. Related Technical Concepts
2.1.1. AI Concepts
2.1.2. Blockchain Concepts
2.2. Contrasting the Core Domains: Blockchain versus AI
2.3. Research Methodology
3. Digital Technologies roles in Sexual Exploitation, AI for Social Good and Ethical Concerns
3.1. Related Literature on Digital Technologies that Enables Sexual Exploitations
3.2. Related Literature on AI for Addressing Sexual Exploitation
3.3. Ethical Issues from AI Applications and Blockchain roles in their Mitigation
4. Blockchain Operations that Address Ethical and Trust Issues in AI Systems
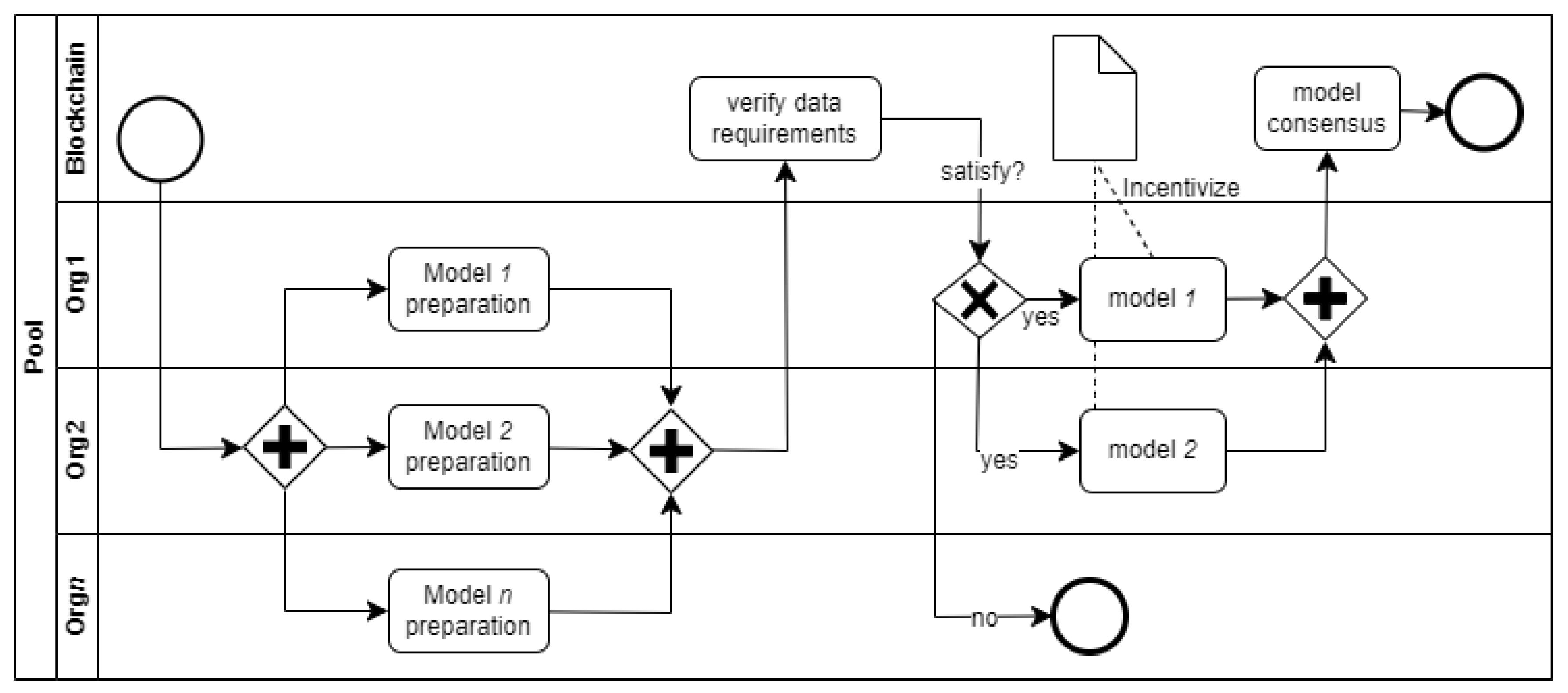
4.1. Blockchain-Enabled Federated Machine Learning
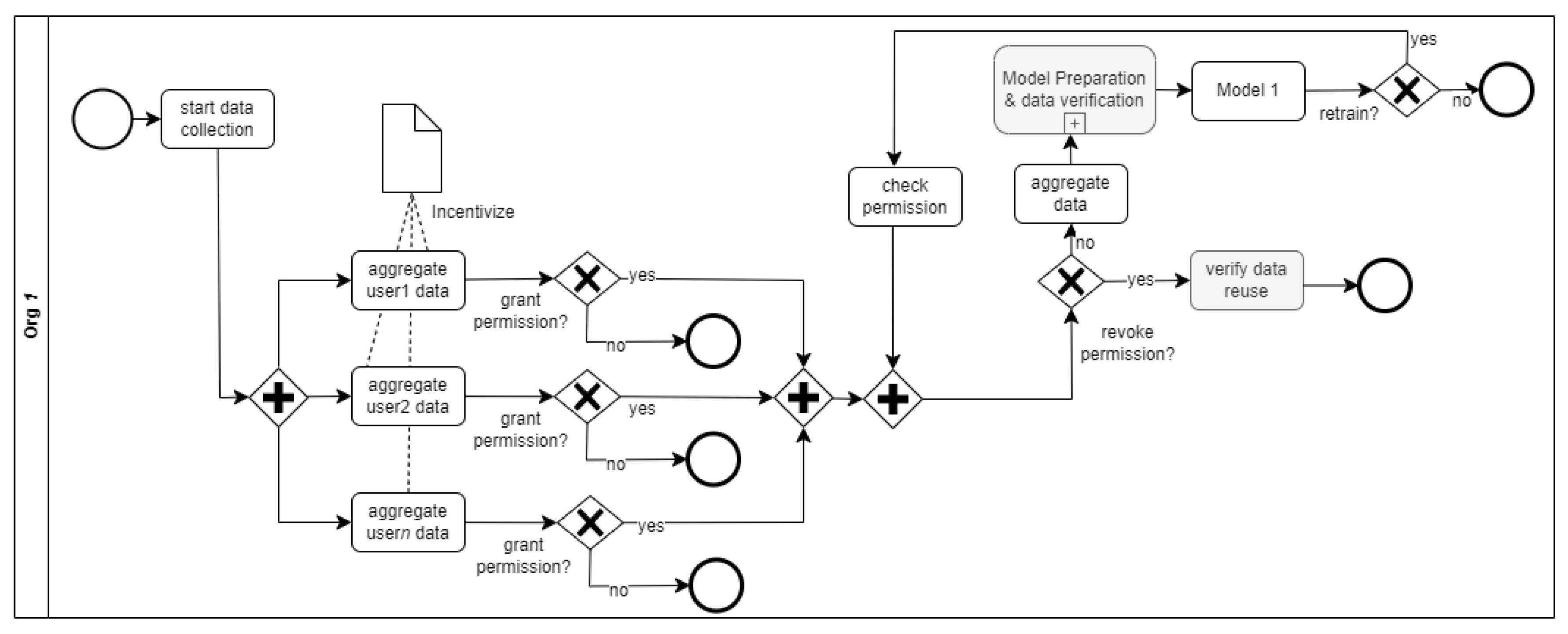
4.2. Blockchain-enabled data wallet
4.3. Privacy Aware Data Processing
4.4. Token Economics Model
5. Discussions: Research Implications
5.1. Integration Complexity and Innovation
5.2. Technological Neutrality and Ethics
5.3. Counteracting Bias and Discrimination
5.4. Economic and Social Equity
5.5. Legal Implications of Blockchain-integrated AI System
5.6. Implementation Considerations for Blockchain Integrated Ethical AI
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
Abbreviations
- ADM: Automated Decision-Making
- AI: Artificial Intelligence
- ALTAI: Assessment List for Trustworthy AI
- AML: Anti-Money Laundering
- BIAI: Blockchain-Integrated AI
- CJEU: Court of Justice of the European Union
- CPRA: California Privacy Rights Act
- DCAP: Decentralized Conditional Anonymous Payment
- DApp: Decentralized Application
- GDPR: General Data Protection Regulation
- HIPAA: Health Insurance Portability and Accountability Act
- LLM: Large Language Model
- ML: Machine Learning
- NFT: Non-Fungible Token
- NLP: Natural Language Processing
- SVG: Scalable Vector Graphics
- TPKS: Tindak Pidana Kekerasan Seksual (Indonesian law on sexual violence)
- ZKP: Zero-Knowledge Proof
References
- Ahmet, E. The Impact of Artificial Intelligence on Social Problems and Solutions: An Analysis on The Context of Digital Divide and Exploitation. Yeni Medya 2022, 2022, 247–264. [Google Scholar]
- Baum, S.D. Artificial interdisciplinarity: Artificial intelligence for research on complex societal problems. Philosophy & Technology 2021, 34, 45–63. [Google Scholar]
- Shen, Y.; Heacock, L.; Elias, J.; Hentel, K.D.; Reig, B.; Shih, G.; Moy, L. ChatGPT and other large language models are double-edged swords, 2023.
- Patchin, J.W.; Hinduja, S. Sextortion Among Adolescents: Results From a National Survey of U.S. Youth. Sexual Abuse: A Journal of Research and Treatment 2018, 32, 30–54. [Google Scholar] [CrossRef]
- Federal Bureau of Investigation. Sextortion: A Growing Threat Targeting Minors, 2024. Accessed: 2024-08-20.
- Henry, N.; Umbach, R. Sextortion: Prevalence and correlates in 10 countries. Computers in Human Behavior 2024, 158, 108298. [Google Scholar] [CrossRef]
- Sheikh, M.M.R.; Rogers, M.M. Technology-facilitated sexual violence and abuse in low and middle-income countries: A scoping review. Trauma, Violence, & Abuse 2024, 25, 1614–1629. [Google Scholar]
- Ray, A.; Henry, N. Sextortion: A Scoping Review. Trauma, Violence, & Abuse 2025, 26, 138–155. [Google Scholar]
- Paat, Y.F.; Markham, C. Digital crime, trauma, and abuse: Internet safety and cyber risks for adolescents and emerging adults in the 21st century. Social Work in Mental Health 2021, 19, 18–40. [Google Scholar] [CrossRef]
- Okolie, C. Artificial intelligence-altered videos (deepfakes), image-based sexual abuse, and data privacy concerns. Journal of International Women’s Studies 2023, 25, 11. [Google Scholar]
- Von Eschenbach, W.J. Transparency and the black box problem: Why we do not trust AI. Philosophy & Technology 2021, 34, 1607–1622. [Google Scholar]
- Ahuja, R.; Chug, A.; Gupta, S.; Ahuja, P.; Kohli, S. Classification and clustering algorithms of machine learning with their applications. Nature-inspired computation in data mining and machine learning, 2020; 225–248. [Google Scholar]
- White, J.; Hays, S.; Fu, Q.; Spencer-Smith, J.; Schmidt, D.C. Chatgpt prompt patterns for improving code quality, refactoring, requirements elicitation, and software design. arXiv, 2023; arXiv:2303.07839. [Google Scholar]
- Gifu, D.; Silviu-Vasile, C. Artificial Intelligence vs. Human: Decoding Text Authenticity with Transformers. Future Internet 2025, 17, 38. [Google Scholar] [CrossRef]
- Lu, Y.; Liu, S.; Zhang, Q.; Xie, Z. RTLLM: An open-source benchmark for design rtl generation with large language model. In Proceedings of the 2024 29th Asia and South Pacific Design Automation Conference (ASP-DAC). IEEE; 2024; pp. 722–727. [Google Scholar]
- Nazir, A.; Chakravarthy, T.K.; Cecchini, D.A.; Khajuria, R.; Sharma, P.; Mirik, A.T.; Kocaman, V.; Talby, D. LangTest: A comprehensive evaluation library for custom LLM and NLP models. Software Impacts, 2024; 100619. [Google Scholar]
- Zelaya, C.V.G. Towards explaining the effects of data preprocessing on machine learning. In Proceedings of the 2019 IEEE 35th international conference on data engineering (ICDE). IEEE; 2019; pp. 2086–2090. [Google Scholar]
- Abburi, H.; Suesserman, M.; Pudota, N.; Veeramani, B.; Bowen, E.; Bhattacharya, S. Generative ai text classification using ensemble llm approaches. arXiv, 2023; arXiv:2309.07755. [Google Scholar]
- Ardabili, S.; Mosavi, A.; Várkonyi-Kóczy, A.R. Advances in machine learning modeling reviewing hybrid and ensemble methods. In Proceedings of the International conference on global research and education. Springer, 2019, pp. 215–227.
- Swan, M. Blockchain: Blueprint for a new economy; " O’Reilly Media, Inc.", 2015.
- Pahlajani, S.; Kshirsagar, A.; Pachghare, V. Survey on private blockchain consensus algorithms. In Proceedings of the 2019 1st International Conference on Innovations in Information and Communication Technology (ICIICT). IEEE; 2019; pp. 1–6. [Google Scholar]
- Cuccuru, P. Beyond bitcoin: an early overview on smart contracts. International Journal of Law and Information Technology 2017, 25, 179–195. [Google Scholar] [CrossRef]
- Di Angelo, M.; Salzer, G. Tokens, types, and standards: identification and utilization in Ethereum. In Proceedings of the 2020 IEEE International Conference on Decentralized Applications and Infrastructures (DAPPS). IEEE; 2020; pp. 1–10. [Google Scholar]
- Zhang, C.; Wu, C.; Wang, X. Overview of Blockchain Consensus Mechanism. In Proceedings of the 2020 2nd International Conference on Big Data Engineering; 2020. [Google Scholar] [CrossRef]
- Kaur, S.; Chaturvedi, S.; Sharma, A.; Kar, J. A Research Survey on Applications of Consensus Protocols in Blockchain. Secur. Commun. Networks 2021, 2021, 6693731:1–6693731:22. [Google Scholar] [CrossRef]
- Zhang, C.; Wang, R.; Tsai, W.; He, J.; Liu, C.L.; Li, Q. Actor-based Model for Concurrent Byzantine Fault-tolerant Algorithm. In Proceedings of the 2019 International Conference on Computer, Network, Communication and Information Systems (CNCI 2019). [CrossRef]
- Belle, V.; Papantonis, I. Principles and Practice of Explainable Machine Learning. Frontiers in Big Data 2020, 4. [Google Scholar] [CrossRef]
- Ramkumar, P.; Kunze, K.; Haeberle, H.S.; Karnuta, J.; Luu, B.C.; Nwachukwu, B.U.; Williams, R.J. Clinical and Research Medical Applications of Artificial Intelligence. Arthroscopy 2020. [Google Scholar] [CrossRef]
- Sachan, S.; Yang, J.; Xu, D.; Benavides, D.E.; Li, Y. An explainable AI decision-support-system to automate loan underwriting. Expert Syst. Appl. 2020, 144, 113100. [Google Scholar] [CrossRef]
- Marevac, E.; Patković, S.; Žunić, E. Decision-making AI for customer worthiness and viability. 2023 22nd International Symposium INFOTEH-JAHORINA (INFOTEH), 2023; 1–6. [Google Scholar] [CrossRef]
- Kannan, K.; Singh, A.; Verma, M.; Jayachandran, P.; Mehta, S. Blockchain-Based Platform for Trusted Collaborations on Data and AI Models. 2020 IEEE International Conference on Blockchain (Blockchain), 2020; 82–89. [Google Scholar] [CrossRef]
- Salama, R.; Al-turjman, F. AI in Blockchain Towards Realizing Cyber Security. 2022 International Conference on Artificial Intelligence in Everything (AIE), 2022; 471–475. [Google Scholar] [CrossRef]
- Heeager, L.T.; Nielsen, P.A. A conceptual model of agile software development in a safety-critical context: A systematic literature review. Information and Software Technology 2018, 103, 22–39. [Google Scholar] [CrossRef]
- Abdel-Aty, T.A.; Negri, E. Conceptualizing the digital thread for smart manufacturing: A systematic literature review. Journal of Intelligent Manufacturing 2024, 35, 3629–3653. [Google Scholar] [CrossRef]
- Naeem, M.; Ozuem, W.; Howell, K.; Ranfagni, S. A step-by-step process of thematic analysis to develop a conceptual model in qualitative research. International journal of qualitative methods 2023, 22, 16094069231205789. [Google Scholar] [CrossRef]
- Karagöz, N.A.; Demirörs, O. Conceptual modeling notations and techniques. In Conceptual modeling for discrete-event simulation; CRC Press, 2010; pp. 195–226. [Google Scholar]
- Recker, J.; Indulska, M.; Green, P.; et al. How good is BPMN really? Insights from theory and practice 2006. [Google Scholar]
- Makinde, O.A.; Olamijuwon, E.; Ichegbo, N.K.; Onyemelukwe, C.; Ilesanmi, M.G. The nature of technology-facilitated violence and abuse among young adults in sub-Saharan Africa. The Emerald international handbook of technology-facilitated violence and abuse, 2021; 83–101. [Google Scholar]
- Lyttle Storrod, M. “It Started With a Nude”: Gangs & Technology-Facilitated Sexual Violence. International Criminal Justice Review 2024, 34, 245–261. [Google Scholar]
- Saputra, D.H.; Prakarsa, A. Enhancing Detection Mechanisms: Law Enforcement Strategies Identifying Suspected Financial Transactions of Child Sexual Exploitation Crimes. In Proceedings of the ACOSEC: ASEAN Conference on Sexual Exploitation of Children. Atlantis Press; 2024; pp. 120–126. [Google Scholar]
- Sunde, N.; Sunde, I.M. Conceptualizing an AI-based police robot for preventing online child sexual exploitation and abuse: Part I–The theoretical and technical foundations for PrevBOT. Nordic Journal of Studies in Policing 2021, 8, 1–21. [Google Scholar] [CrossRef]
- Ali, M.I. Strategies for Intervention and Prevention in Online Child Sexual Exploitation. Teisė 2024, 132, 145–155. [Google Scholar]
- Stockhem, O. Improving the international regulation of cybersextrafficking of women and children through the use of data science and artificial intelligence. PhD thesis, 2020.
- Rita, M.N.; Shava, F.B. Chatbot driven web-based platform for online safety and sexual exploitation awareness and reporting in Namibia. In Proceedings of the 2021 International Conference on Artificial Intelligence, Big Data, Computing and Data Communication Systems (icABCD). IEEE, 2021; pp. 1–5.
- Phippen, A.; Bond, E. Image recognition in child sexual exploitation material—Capabilities, ethics and rights. Policing in the Era of AI and Smart Societies, 2020; 179–198. [Google Scholar]
- Alsoubai, A.; Song, J.; Razi, A.; Naher, N.; De Choudhury, M.; Wisniewski, P.J. From’Friends with Benefits’ to’Sextortion:’A nuanced investigation of adolescents’ online sexual risk experiences. Proceedings of the ACM on human-computer interaction 2022, 6, 1–32. [Google Scholar]
- Blancaflor, E.; Garcia, J.I.; Magno, F.D.; Vilar, M.J. Deepfake Blackmailing on the Rise: The Burgeoning Posterity of Revenge Pornography in the Philippines. In Proceedings of the Proceedings of the 2024 9th International Conference on Intelligent Information Technology; 2024; pp. 295–301. [Google Scholar]
- Borau, S. Deception, discrimination, and objectification: Ethical issues of female AI agents. Journal of Business Ethics, 2024; 1–19. [Google Scholar]
- Alex, N.; Sotiris, M. Designing Artificial Intelligence Equipped Social Decentralized Autonomous Organizations for Tackling Sextortion Cases Version 0.7. arXiv, 2023; arXiv:2312.14090. [Google Scholar]
- Lee, G.H.; Shin, S.Y. Federated learning on clinical benchmark data: performance assessment. Journal of medical Internet research 2020, 22, e20891. [Google Scholar]
- Norta, A.; Hawthorne, D.; Engel, S.L. A privacy-protecting data-exchange wallet with ownership-and monetization capabilities. In Proceedings of the 2018 International Joint Conference on Neural Networks (IJCNN). IEEE; 2018; pp. 1–8. [Google Scholar]
- Butt, A.; Junejo, A.Z.; Ghulamani, S.; Mahdi, G.; Shah, A.; Khan, D. Deploying Blockchains to Simplify AI Algorithm Auditing. In Proceedings of the 2023 IEEE 8th International Conference on Engineering Technologies and Applied Sciences (ICETAS). IEEE; 2023; pp. 1–6. [Google Scholar]
- Chaffer, T.J.; Charles von Goins, I.; Cotlage, D.; Okusanya, B.; Goldston, J. Decentralized Governance of AI Agents 2024.
- Himmelsbach, T.; Mou, Y.; Decker, S.; Heinzl, A. Towards Federated Machine Learning and Distributed Ledger Technology-based Data Monetization. In Proceedings of the VLDB Workshops; 2023. [Google Scholar]
- Nassar, M.; Salah, K.; Ur Rehman, M.H.; Svetinovic, D. Blockchain for explainable and trustworthy artificial intelligence. Wiley Interdisciplinary Reviews: Data Mining and Knowledge Discovery 2020, 10, e1340. [Google Scholar]
- Singh, N.; Dayama, P.; Pandit, V. Zero knowledge proofs towards verifiable decentralized ai pipelines. In Proceedings of the International Conference on Financial Cryptography and Data Security. Springer; 2022; pp. 248–275. [Google Scholar]
- Balta, D.; Sellami, M.; Kuhn, P.; Schöpp, U.; Buchinger, M.; Baracaldo, N.; Anwar, A.; Ludwig, H.; Sinn, M.; Purcell, M.; et al. Accountable federated machine learning in government: engineering and management insights. In Proceedings of the Electronic Participation: 13th IFIP WG 8.5 International Conference, ePart 2021, Proceedings 13. Granada, Spain, 7–9 September 2021; Springer, 2021; pp. 125–138. [Google Scholar]
- Yang, Q.; Liu, Y.; Chen, T.; Tong, Y. Federated machine learning: Concept and applications. ACM Transactions on Intelligent Systems and Technology (TIST) 2019, 10, 1–19. [Google Scholar] [CrossRef]
- Unal, D.; Hammoudeh, M.; Khan, M.A.; Abuarqoub, A.; Epiphaniou, G.; Hamila, R. Integration of federated machine learning and blockchain for the provision of secure big data analytics for Internet of Things. Computers & Security 2021, 109, 102393. [Google Scholar]
- Angraal, S.; Krumholz, H.; Schulz, W. Blockchain Technology: Applications in Health Care. Circulation: Cardiovascular Quality and Outcomes 2017, 10, e003800. [Google Scholar]
- for Disease Control, C. Prevention. Health Insurance Portability and Accountability Act of 1996 (HIPAA), 2023. https://www.cdc.gov/phlp/php/resources/health-insurance-portability-and-accountability-act-of-1996-hipaa.html, Accessed: 2024-09-24.
- Ponsam, J.G.; Duvvuri, S.; Roy, S. Electronic Healthcare Management System Using Blockchain Technology. In Proceedings of the 2023 International Conference on Circuit Power and Computing Technologies (ICCPCT). IEEE; 2023; pp. 869–877. [Google Scholar]
- Tang, Y.; Xiong, J.; Becerril-Arreola, R.; Iyer, L. Ethics of blockchain: A framework of technology, applications, impacts, and research directions. Information Technology & People 2020, 33, 602–632. [Google Scholar]
- Reddy, B.; Madhushree.; Aithal, P. Blockchain as a Disruptive Technology in Healthcare and Financial Services - a Review Based Analysis on Current Implementations. Organizations & Markets: Policies & Processes eJournal 2020.
- Dagher, G.G.; Mohler, J.; Milojkovic, M.; Marella, P.B. Ancile: Privacy-Preserving Framework for Access Control and Interoperability of Electronic Health Records Using Blockchain Technology. Sustainable Cities and Society 2018, 39, 283–297. [Google Scholar] [CrossRef]
- Bodemer, O. The Unseen Guardian: How Blockchain, Java, and AI Stealthily Became the Sherlock Holmes of Cybersecurity. Authorea Preprints 2023. [Google Scholar]
- Paquet-Clouston, M.; Romiti, M.; Haslhofer, B.; Charvat, T. Spams meet Cryptocurrencies: Sextortion in the Bitcoin Ecosystem. Proceedings of the 1st ACM Conference on Advances in Financial Technologies 2019. [Google Scholar] [CrossRef]
- Fahlevi, M.; Moeljadi.; Aisjah, S.; Djazuli, A. Corporate Governance in the Digital Age: A Comprehensive Review of Blockchain, AI, and Big Data Impacts, Opportunities, and Challenges. E3S Web of Conferences 2023. [CrossRef]
- Otoum, S.; Mouftah, H. Enabling Trustworthiness in Sustainable Energy Infrastructure Through Blockchain and AI-Assisted Solutions. IEEE Wireless Communications 2021, 28, 19–25. [Google Scholar] [CrossRef]
- Lescisin, M.; Mahmoud, Q. A Blockchain-Based Solution for Defining and Enforcing Personal Data Access Policies. 2023 International Conference on Information Technology (ICIT), 2023; 118–124. [Google Scholar] [CrossRef]
- Michaelson, P. Arbitrating Disputes Involving Blockchains, Smart Contracts, and Smart Legal Contracts. Cybersecurity 2020. [Google Scholar] [CrossRef]
- Ranjan, A.; Singh, A.N.; Kumar, A.; Manoj, T.; Kumar. Transforming Judicial Systems with Blockchain: A Court Case Governance System for Tamper-Proof and Transparent Legal Processes. In Proceedings of the 2023 International Conference on Applied Intelligence and Sustainable Computing (ICAISC), 2023. [CrossRef]
- Yeoh, P. Regulatory issues in blockchain technology. Journal of Financial Regulation and Compliance 2017, 25, 196–208. [Google Scholar] [CrossRef]
- Nguyen, Q.; Dang, Q.V. Blockchain Technology for the Advancement of the Future. In Proceedings of the 2018 4th International Conference on Green Technology and Sustainable Development (GTSD); 2018; pp. 483–486. [Google Scholar] [CrossRef]
- Miao, Y.; Liu, Z.; Li, H.; Choo, K.; Deng, R. Privacy-Preserving Byzantine-Robust Federated Learning via Blockchain Systems. IEEE Transactions on Information Forensics and Security 2022, 17, 2848–2861. [Google Scholar] [CrossRef]
- Feng, L.; Zhao, Y.; Guo, S.; Qiu, X.; Li, W.; Peng, Y. Blockchain-based Asynchronous Federated Learning for Internet of Things. IEEE Transactions on Computers, 2021; 1–1. [Google Scholar] [CrossRef]
- Lo, S.K.; Liu, Y.; Lu, Q.; Wang, C.; Xu, X.; young Paik, H.; Zhu, L. Toward Trustworthy AI: Blockchain-Based Architecture Design for Accountability and Fairness of Federated Learning Systems. IEEE Internet of Things Journal 2023, 10, 3276–3284. [Google Scholar] [CrossRef]
- Chang, Y.; Fang, C.; Sun, W. A Blockchain-Based Federated Learning Method for Smart Healthcare. Computational Intelligence and Neuroscience 2021, 2021. [Google Scholar] [CrossRef]
- Glaesser, F. Does the Transparent Blockchain Technology Offer Solutions to the Algorithmic Fairness Problem? Artificial Intelligence - Law, 2018. [Google Scholar] [CrossRef]
- Kafali, E.; Preuveneers, D.; Semertzidis, T.; Daras, P. Defending Against AI Threats with a User-Centric Trustworthiness Assessment Framework. Big Data and Cognitive Computing 2024, 8, 142. [Google Scholar] [CrossRef]
- Varghese, I.K.; et al. Blockchain Technology in the Intrusion Detection Domain. International Journal on Recent and Innovation Trends in Computing and Communication 2023. [Google Scholar] [CrossRef]
- Pagano, T.P.; et al. Bias and Unfairness in Machine Learning Models: A Systematic Review on Datasets, Tools, Fairness Metrics, and Identification and Mitigation Methods. Big Data Cogn. Comput. 2023, 7, 15. [Google Scholar] [CrossRef]
- Özdayi, M.S.; Kantarcioglu, M.; Malin, B. Leveraging blockchain for immutable logging and querying across multiple sites. BMC Medical Genomics 2020. [Google Scholar] [CrossRef]
- Helo, P.; Hao, Y. Blockchains in operations and supply chains: A model and reference implementation. Comput. Ind. Eng. 2019, 136, 242–251. [Google Scholar] [CrossRef]
- Ma, S.; Cao, Y.; Xiong, L. Efficient logging and querying for blockchain-based cross-site genomic dataset access audit. BMC Medical Genomics 2019, 13. [Google Scholar] [CrossRef]
- Butt, A.; Junejo, A.Z.; Ghulamani, S.; Mahdi, G.; Shah, A.; Khan, D. Deploying Blockchains to Simplify AI Algorithm Auditing. In Proceedings of the 2023 IEEE 8th International Conference on Engineering Technologies and Applied Sciences (ICETAS); 2023; pp. 1–6. [Google Scholar] [CrossRef]
- Salah, K.; Rehman, M.H.; Nizamuddin, N.; Al-Fuqaha, A.I. Blockchain for AI: Review and Open Research Challenges. IEEE Access 2019, 7, 10127–10149. [Google Scholar] [CrossRef]
- Yeung, K. Regulation by Blockchain: The Emerging Battle for Supremacy between the Code of Law and Code as Law. Law 2018. [Google Scholar] [CrossRef]
- Mumporeze, N.; Han-Jin, E.; Nduhura, D. Let’s spend a night together; i will increase your salary: an analysis of sextortion phenomenon in Rwandan society. Journal of Sexual Aggression 2019, 27, 120–137. [Google Scholar] [CrossRef]
- Fawole, O. Economic Violence To Women and Girls. Trauma, Violence, & Abuse 2008, 9, 167–177. [Google Scholar] [CrossRef]
- Caarten, A.B.; van Heugten, L.; Merkle, O. The intersection of corruption and gender-based violence: Examining the gendered experiences of sextortion during migration to South Africa. African journal of reproductive health 2022, 26 6, 45–54. [Google Scholar]
- Anonymous. Decentralizing Privacy: Protecting Personal Data by Blockchain. International Journal of Innovative Technology and Exploring Engineering, 2023. [CrossRef]
- Kapoor, O.; et al. Implementing decentralized storage using blockchain to address data ownership and privacy concerns. International Journal of Advance Research, Ideas and Innovations in Technology 2018, 4, 2015–2020. [Google Scholar]
- Zyskind, G.; Nathan, O.; Pentland, A. Decentralizing Privacy: Using Blockchain to Protect Personal Data. In Proceedings of the 2015 IEEE Security and Privacy Workshops; 2015; pp. 180–184. [Google Scholar] [CrossRef]
- Zuboff, S. The age of surveillance capitalism. In Social theory re-wired; Routledge, 2023; pp. 203–213.
- Li, G.; Zhao, Q.; Wang, Y.; Qiu, T.; Xie, K.; Feng, L. A Blockchain-Based Decentralized Framework for Fair Data Processing. IEEE Transactions on Network Science and Engineering 2021, 8, 2301–2315. [Google Scholar] [CrossRef]
- Chen, Y.; Bellavitis, C. Blockchain Disruption and Decentralized Finance: The Rise of Decentralized Business Models. Stevens Institute of Technology - School of Business Research Paper Series, 2019. [Google Scholar] [CrossRef]
- Vishwa, A.; Hussain, F. A Blockchain-Based Approach for Multimedia Privacy Protection and Provenance. In Proceedings of the 2018 IEEE Symposium Series on Computational Intelligence (SSCI); 2018; pp. 1941–1945. [Google Scholar] [CrossRef]
- Paquet-Clouston, M.; Romiti, M.; Haslhofer, B.; Charvat, T. Spams meet Cryptocurrencies: Sextortion in the Bitcoin Ecosystem. Proceedings of the 1st ACM Conference on Advances in Financial Technologies 2019. [Google Scholar] [CrossRef]
- PARASCHIVEANU, V.; RICHARDSON, G.; VOICU-DOROBANȚU, R. EDUCATION 3.0: BLOCKCHAIN-BACKED MOOCS. eLearning & Software for Education 2020, 3. [Google Scholar]
- Antinucci, M. EU Ethical Charter on the Use of Artificial Intelligence in Judicial Systems with a part of the law being established on Blockchain as a trojan horse anti-counterfeiting in a Global perspective. Courier of Kutafin Moscow State Law University 2020. [Google Scholar] [CrossRef]
- Patil, S.; Desai, D. AI Enabled Blockchain solution for the Indian Judicial System. In Proceedings of the 2023 International Conference on Emerging Smart Computing and Informatics (ESCI). IEEE; 2023; pp. 1–6. [Google Scholar]
- Rao, S.; Fernandes, S.; Raorane, S.; Syed, S.F. A Novel Approach for Digital Evidence Management Using Blockchain. SSRN Electronic Journal 2020. [Google Scholar] [CrossRef]
- Tian, Z.; Li, M.; Qiu, M.; Sun, Y.; Su, S. Block-DEF: A secure digital evidence framework using blockchain. Inf. Sci. 2019, 491, 151–165. [Google Scholar] [CrossRef]
- Bazarhanova, A.; Magnusson, J.; Lindman, J.; Chou, E.; Nilsson, A. Blockchain-based electronic identification: cross-country comparison of six design choices 2019.
- Lin, C.; He, D.; Huang, X.; Khan, M.; Choo, K. DCAP: A Secure and Efficient Decentralized Conditional Anonymous Payment System Based on Blockchain. IEEE Transactions on Information Forensics and Security 2020, 15, 2440–2452. [Google Scholar] [CrossRef]
- Myeong, S.; Jung, Y. Administrative Reforms in the Fourth Industrial Revolution: The Case of Blockchain Use. Sustainability 2019. [Google Scholar] [CrossRef]
- Marinakis, V.; Koutsellis, T.; Nikas, A.; Doukas, H. AI and Data Democratisation for Intelligent Energy Management. Energies 2021. [Google Scholar] [CrossRef]
- Parker, B.; Bach, C. The Synthesis of Blockchain, Artificial Intelligence and Internet of Things. European Journal of Engineering Research and Science 2020, 5, 588–593. [Google Scholar] [CrossRef]
- Li, Z. Confronting algorithm bias risks: Will blockchain provide new opportunities or challenges for data protection law? Dublin L. & Pol. Rev. 2021, 2, 43. [Google Scholar]
- Chaturvedi, A. Defining Legal Responsibility in the Age of AI: Addressing Gaps in Data Privacy Regulation. Indian J. Integrated Rsch. L. 2023, 3, 1. [Google Scholar]
- Murthy, M.S. Data protection law and policy in the USA: An overview. Issue 3 Indian JL & Legal Rsch. 2022, 4, 1. [Google Scholar]
- Zuo, Y.; Guo, J.; Gao, N.; Zhu, Y.; Jin, S.; Li, X. A Survey of Blockchain and Artificial Intelligence for 6G Wireless Communications. IEEE Communications Surveys & Tutorials 2023, 25, 2494–2528. [Google Scholar] [CrossRef]
- Yulianto, S.; Hendric, H.L.; Warnars, S.; Prabowo, H.; Hidayanto, A. Security Risks and Best Practices for Blockchain and Smart Contracts: A Systematic Literature Review. 2023 International Conference on Information Management and Technology (ICIMTech), 2023; 1–6. [Google Scholar] [CrossRef]
- Han, J.; Lee, J.; Li, T. DAO Governance. SSRN Electronic Journal 2023. [Google Scholar] [CrossRef]
| Digital Technologies | Roles in Enabling Sextortion | Impact | Referenced Studies |
|---|---|---|---|
| Mobile apps, virtual reality platforms, social media. | Non-consensual taking, sharing, or threats to share personal, intimate images or videos. | Psychological and emotional, social, financial and behavioural impacts, physical harm | [7] |
| Social media platforms, messaging apps, online dating sites, camera and video-enabled devices, email and online communication channels | Grooming, harassment, and non-consensual sharing of intimate images, cyberstalking, romance scams, revenge porn and sextortion, coercive messages | Violence, digital harassment, image-based abuse, sexual aggression and/or coercion, and gender-/sexuality-based harassment | [38] |
| Social networking, online hosting services, advanced encryption techniques | Recruit victims, advertise services, store and share illicit content, protecting their communications and data from detection | Mental health risks, psychological terrorism | [9] |
| Social media, messaging apps, GPS tracking apps, online video-sharing platforms, cloud storage and digital media sharing | Coercion, harassment, and dissemination of sexually explicit content, coerced sexting and sextortion, cyberstalking and monitoring of victims, recording and distribution of sexual assaults, and storing and disseminating explicit content. | Sexual violence and exploitation | [39] |
| Internet, online platforms, mobile phones, messaging apps, and live-streaming technology | Advertise victims and connect with potential clients, communicate covertly, coordinate logistics, broadcasting of exploitative content, non-consensual explicit content | Fear, anxiety, anger, humiliation, shame, self-blame, suicidal ideation and suicide, depression, financial scam | [8] |
| AI’s Roles in Enabling Sextortion | AI’s Roles in Preventing Sextortion | Ethical Issues | Referenced Studies |
|---|---|---|---|
| - | Detecting suspicious transaction patterns related to sexual exploitation. | Accuracy (false positives), bias, and privacy (data misuse) | [40] |
| - | Identification of sexualised content in public chatrooms. | Contextual understanding, freedom of speech, and privacy (data misuse) | [41] |
| - | Elimination of sexual exploitation materials. | Censorship, and bias | [42] |
| - | Data warehousing on sexual exploitation incidents. | Privacy (data misuse), security (data breaches), and data retention (duration). | [43] |
| - | Natural language Chatbots for reporting incidents of sexual exploitations. | Accessibility, trust issues, and privacy (confidentiality). | [44] |
| - | Image analyses for identification of sexual exploitation materials. | Accuracy, bias, and privacy (data misuse). | [45] |
| - | Content moderation on social media platforms. | Transparency, accountability, and bias | [46] |
| Deepfake images for blackmailing | - | - | [47] |
| Image-based sexual abuse through altered altered images and recordings. | - | - | [10] |
| Sexualisation of female AI agents | - | - | [48] |
| - | Preventing sextortion by personalised education, detecting sextortion by coercive behaviour detection, and supporting victims through gamified mental therapy. | Privacy (data usage and sensitivity), bias (limited data set), data consent, and regulation (multi-jurisdiction) | [49] |
| Ethical issues in AI | Blockchain concept | Blockchain role in Mitigation | Referenced Studies |
|---|---|---|---|
| Accuracy (false positives) | Federated machine learning. | Like other ensemble AI systems, it can improve the performance of the models and also provide more representative datasets since data is distributed across different locations, countries and regions ensuring that systems that mitigate sexual exploitation have higher performance | [50] |
| Privacy (data use/misuse) | Data wallet | Permission granting and revoking to prevent unauthorised data usage thereby ensuring that victims of sexual exploitation maintains control and use of their data in training AI systems | [51] |
| Bias | Data auditability | Auditable datasets on the blockchain provides transparency and help in identifying biases in datasets | [52] |
| Contextual understanding | - | - | - |
| Censorship (freedom of speech) | DAO governance | Community-based governance of AI processes instead of centrally controlled ensures decisions on what constitute sexual exploitations are reached in a more democratic manner | [53] |
| Accessibility | Token economics | Token-based reward mechanisms can be implemented to incentivize data owners and organizations to independently run federated AI models thereby making them decentralized and more accessible instead of propriety model ownership by cental entities | [54] |
| Trustability | Smart contracts | On-chain logic is verifiable and ethical guidelines can be encoded in smart contracts ensuring that the basis for identifying sexual exploitations are verifiable and transparent | [55] |
| Accoutability | - | - | - |
| Security (confidentiality) | Zero-knowledge proof systems | Privacy-aware data processing systems such as homomorphic encryption can be adopted in processing confidential data such even there is data breaches, information and data of victims of sexual exploitations remain hidden | [56] |
| Regulation (legal jurisdictions) | Federated machine learning | Data are processed at the point where they are generated adhering to local regulations this ensures that different legal jurisdictions and regulations regarding the processing of sensitive data are adhered to specific to locations where the decentralized AI models run. | [57] |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




