Submitted:
07 January 2025
Posted:
07 January 2025
You are already at the latest version
Abstract
Keywords:
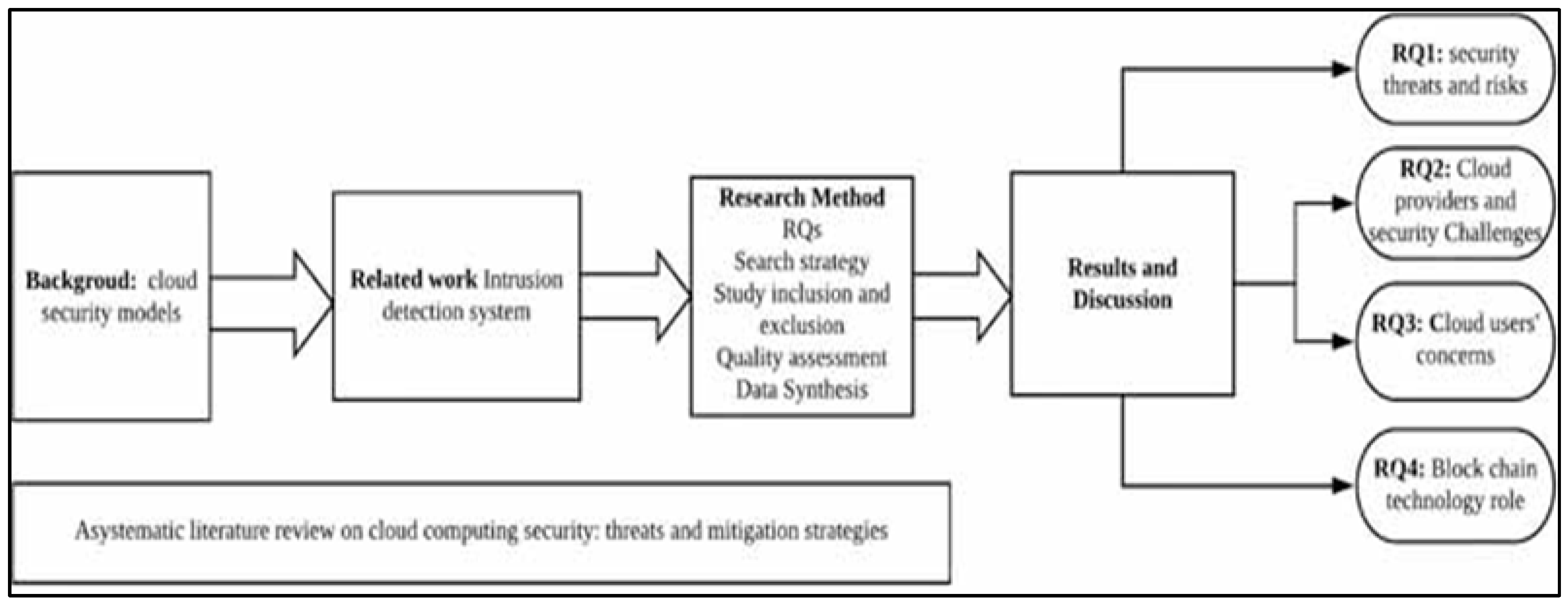
1. Cloud Computing Background
1.1. Cloud Computing Development History
1.2. Cloud Computing Security Development
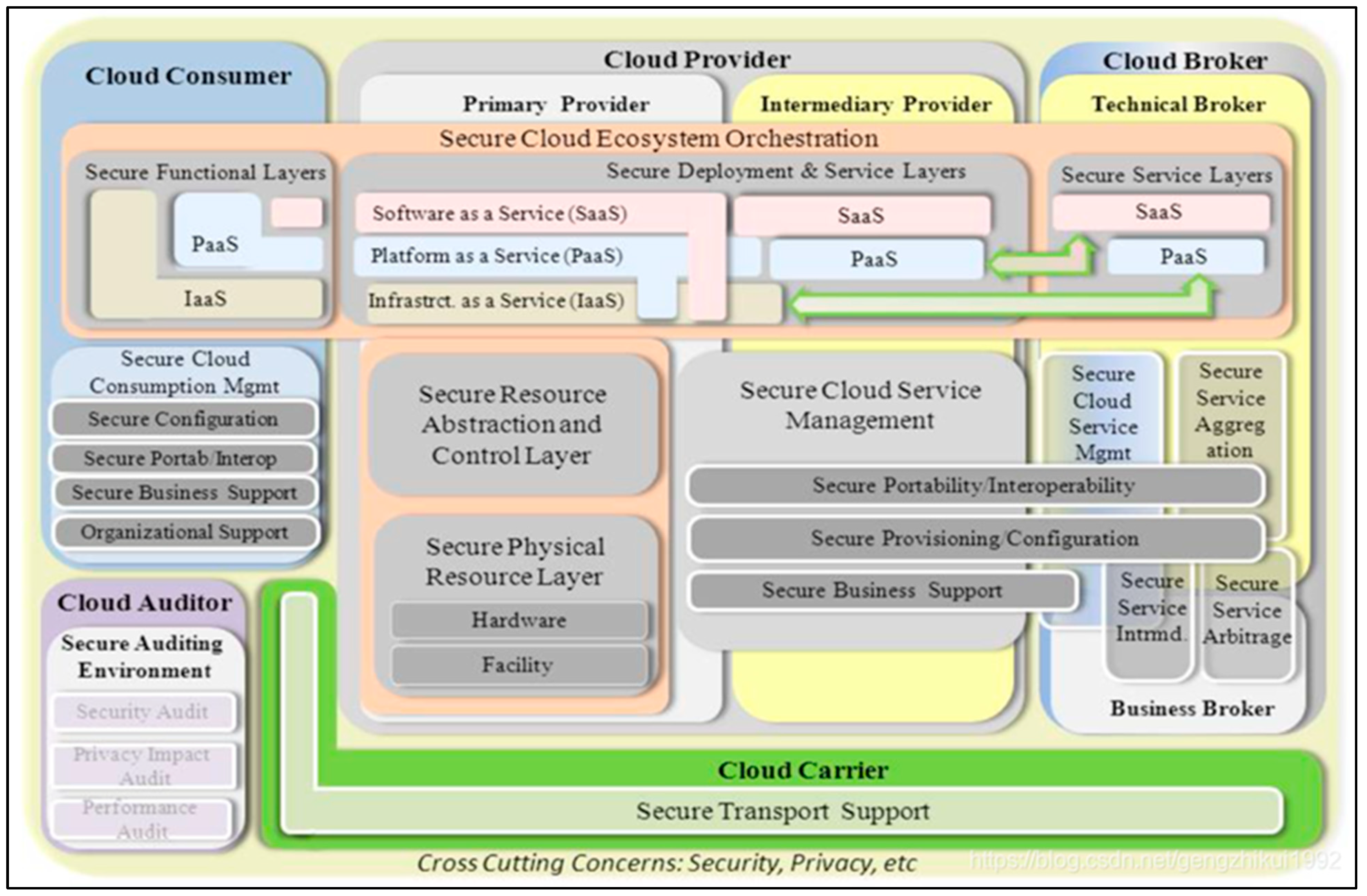
1.3. Three Components of the NIST Cloud Computing Security Reference Architecture
2. Detailed Discussion
2.1. Component
2.1.1. Data
2.1.2. Applications
2.1.3. Operating System (OS)
2.1.4. Virtualization
2.1.5. Servers
2.1.6. Storage
2.1.7. Networking
2.2. Process
- 1. Understand What Cloud Security Is
- 2. Look at the Important Parts of Cloud Security
- 3. Understand the Risks
- 4. Learn About the Tools to Protect the Cloud
- 5. Recognize the Challenges
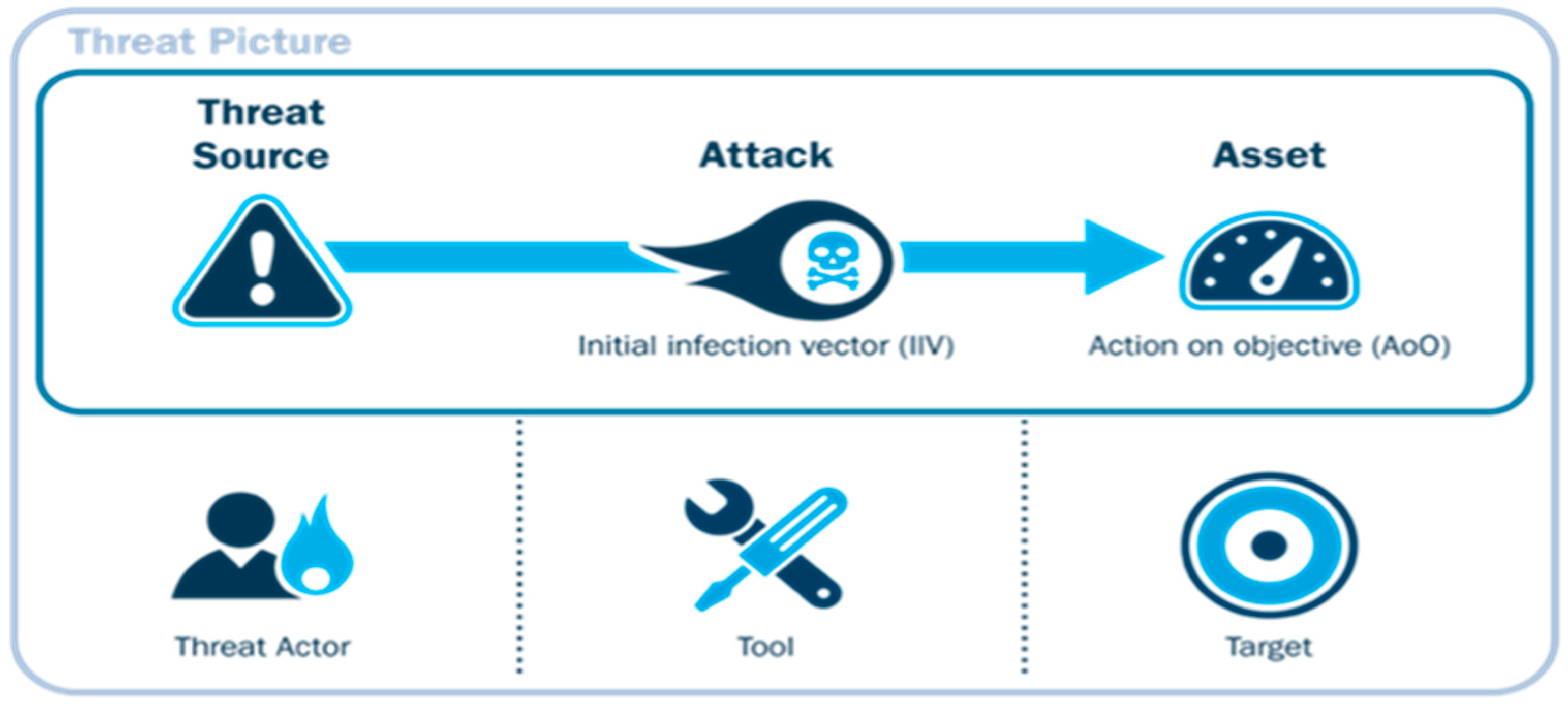
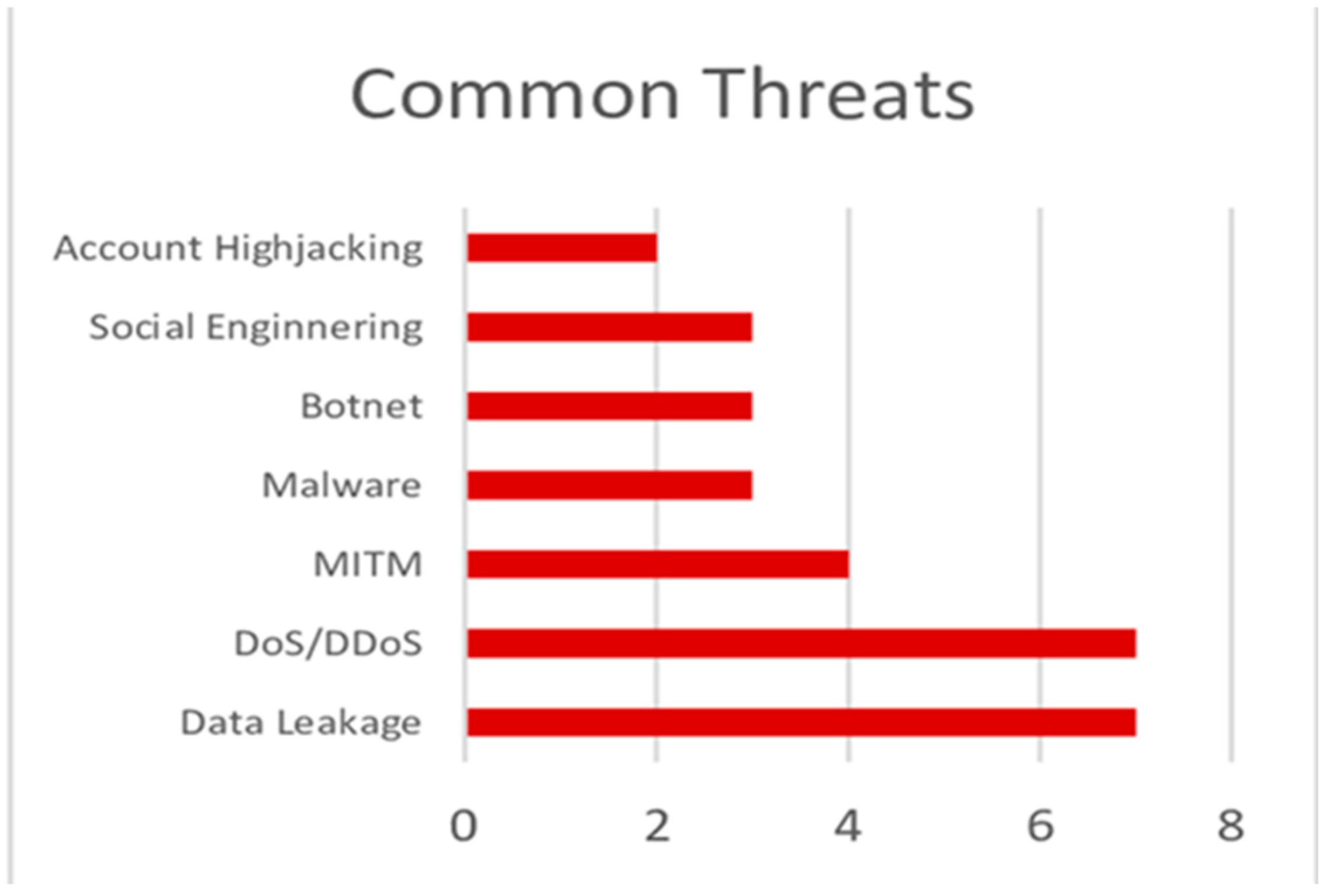
2.3. Threat
2.4. Example
3. Impact
3.1. Benefits
3.2. Limitations
3.3. Future
4. Security Countermeasures
- Data Leakage:
- DoS/DDoS:
- Botnet:
- Account hijacking:
- Malware:
- MITM:
- Social Engineering:
5. Proposed Countermeasures
5.1. Enhanced Zero Trust Model
5.2. AI Enhanced Threats Detection Technologies
6. Conclusion
References
- Alex, S. A. , Jhanjhi, N., Humayun, M., Ibrahim, A. O., & Abulfaraj, A. W. (2022). Deep LSTM Model for Diabetes Prediction with Class Balancing by SMOTE. W. ( 11(17), 2737. [CrossRef]
- Alferidah, D. K. , & Jhanjhi, N. (2020). Cybersecurity Impact over Bigdata and IoT Growth. 2020 International Conference on Computational Intelligence (ICCI). [CrossRef]
- Alkinani, M. H. , Almazroi, A. A., Jhanjhi, N., & Khan, N. A. (2021). 5G and IoT Based Reporting and Accident Detection (RAD) System to Deliver First Aid Box Using Unmanned Aerial Vehicle. A. ( 21(20), 6905. [CrossRef]
- Allan Liu, T. Y. (2018). Overview of Cloud Storage. International Journal of Scientific & Technology(1).
- Alqahtani, K. S. , & Albalawi, A. M. (2023). REVIEWING OF CYBERSECURITY THREATS, ATTACKS, AND MITIGATION TECHNIQUES IN CLOUD COMPUTING ENVIRONMENT. Journal of Theoretical and Applied Information, 3698. [Google Scholar]
- Ananna, F. F. , Nowreen, R., Jahwari, S. S. R. A., Costa, E. A., Angeline, L., & Sindiramutty, S. R. (2023). Analysing Influential factors in student academic achievement: Prediction modelling and insight. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence. [CrossRef]
- Azam, H. , Dulloo, M. I., Majeed, M. H., Wan, J. P. H., Xin, L. T., & Sindiramutty, S. R. (2023). Cybercrime Unmasked: Investigating cases and digital evidence. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence. [CrossRef]
- Azam, H. , Dulloo, M. I., Majeed, M. H., Wan, J. P. H., Xin, L. T., Tajwar, M. A., & Sindiramutty, S. R. (2023). Defending the digital Frontier: IDPS and the battle against Cyber threat. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence. [CrossRef]
- Azam, H. , Tajwar, M. A., Mayhialagan, S., Davis, A. J., Yik, C. J., Ali, D., & Sindiramutty, S. R. (2023). Innovations in Security: A study of cloud Computing and IoT. International Journal of Emerging Multidisciplinaries Computer Science & Artificial Intelligence. [CrossRef]
- Azam, H. , Tan, M., Pin, L. T., Syahmi, M. A., Qian, A. L. W., Jingyan, H., Uddin, M. F., & Sindiramutty, S. R. (2023). Wireless Technology Security and Privacy: A Comprehensive Study. Preprints.org. [CrossRef]
- Babbar, H. , Rani, S., Masud, M., Verma, S., Anand, D., & Jhanjhi, N. (2021). Load balancing algorithm for migrating switches in software-defined vehicular networks. Computers, Materials & Continua/Computers, Materials & Continua (Print). [CrossRef]
- Bader Alouffi, M. H. (2021). A Systematic Literature Review on Cloud Computing Security: Threats and Mitigation Strategies. IEEE Access, 9, 57792-57807. [CrossRef]
- Brohi, S. N. , Jhanjhi, N., Brohi, N. N., & Brohi, M. N. (2020). Key Applications of State-of-the-Art Technologies to Mitigate and Eliminate COVID-19.pdf. TECHRxiv. [CrossRef]
- Chellammal Surianarayanan, P. R. (2023). Cloud Networking. In P. R. Chellammal Surianarayanan, Essentials of Cloud Computing (pp. 105-141). Springer, Cham.
- Chesti, I. A. , Humayun, M., Sama, N. U., & Jhanjhi, N. (2020). Evolution, Mitigation, and Prevention of Ransomware. 2020 2nd International Conference on Computer and Information Sciences (ICCIS). [CrossRef]
- CloudFlare. (n.d.). How to prevent DDoS attacks | Methods and tools. CloudFlare: https://www.cloudflare.
- CloudFlare. (n.d.). What is Anycast? | How does Anycast work? CloudFlare: https://www.cloudflare.
- CloudFlare. (n.d.). What is rate limiting? | Rate limiting and bots. CloudFlare: https://www.cloudflare.
- CloudFlare. (n.d.). Zero Trust security | What is a Zero Trust network? CloudFlare: https://www.cloudflare.
- Conteh, N. &. (2016). Cybersecurity:risks, vulnerabilities and countermeasures to prevent social engineering attacks. nternational Journal of Advanced Research in Computer Science, 6(23), 31-38. [CrossRef]
- Deyan Chen, H. Z. (2012). Data Security and Privacy Protection Issues in Cloud Computing. 2012 International Conference on Computer Science and Electronics Engineering, 647-651. [CrossRef]
- Dogra, V. , Singh, A., Verma, S., Kavita, N., Jhanjhi, N. Z., & Talib, M. N. (2021). Analyzing DistilBERT for Sentiment Classification of Banking Financial News. In Lecture notes in networks and systems (pp. 501–510). [CrossRef]
- Fabrizio Marozzo, L. B. (2022). Cloud Computing for Big Data Analysis. Applied Sciences, 12(20). [CrossRef]
- Fang Liu, J. T. (2011). NIST Cloud Computing Reference Architecture. NIST Pubs.
- Farber, S. (2024, ). Cloud Data Security & Protection: Everything You Need to Know. Paloalto Networks: https://www.paloaltonetworks. 6 March.
- Fatima-Tuz-Zahra, N. , Jhanjhi, N., Brohi, S. N., Malik, N. A., & Humayun, M. (2020). Proposing a Hybrid RPL Protocol for Rank and Wormhole Attack Mitigation using Machine Learning. 2020 2nd International Conference on Computer and Information Sciences (ICCIS). [CrossRef]
- Foster, I. A. (2013, June). NIST’s Security Reference Architecture for the Cloud-First Initiative, /: https, 2013. [Google Scholar]
- GeeksforGeeks. (2020, ). Advantages and Disadvantages of Cloud Security. GeeksforGeeks: https://www.geeksforgeeks. 24 June.
- Gopi, R. , Sathiyamoorthi, V., Selvakumar, S., Manikandan, R., Chatterjee, P., Jhanjhi, N. Z., & Luhach, A. K. (2021). Enhanced method of ANN based model for detection of DDoS attacks on multimedia internet of things. Multimedia Tools and Applications, 6739. [Google Scholar] [CrossRef]
- Gouda, W. , Almurafeh, M., Humayun, M., & Jhanjhi, N. Z. (2022). Detection of COVID-19 based on chest x-rays using deep learning. Healthcare. [CrossRef]
- Gounder, M. &. (2017). New Ways To Fight Malware. International Journal of Scientific & Technology Research, 6(6), 313-318.
- Gregg Lindemulder, M. K. (2024, ). What is a man-in-the-middle (MITM) attack? IBM: https://www.ibm. 11 June.
- Humayun, M. , Sujatha, R., Almuayqil, S. N., & Jhanjhi, N. Z. (2022). A Transfer Learning Approach with a Convolutional Neural Network for the Classification of Lung Carcinoma. Z. ( 10(6), 1058. [CrossRef]
- Humayun, M. , Jhanjhi, N. Z., Alsayat, A., & Ponnusamy, V. (2021). Internet of things and ransomware: Evolution, mitigation and prevention. Egyptian Informatics Journal.
- Hussain, K. , Rahmatyar, A. R., Riskhan, B., Sheikh, M. a. U., & Sindiramutty, S. R. (2024). Threats and Vulnerabilities of Wireless Networks in the Internet of Things (IoT). 2024 IEEE 1st Karachi Section Humanitarian Technology Conference (KHI-HTC). [CrossRef]
- International Business Machines Corparation. (2024, ). What are the benefits of cloud computing? IBM: https://www.ibm. 13 August.
- International Business Machines Corporation. (2024, ). What is a cloud server? IBM: https://www.ibm. 8 August.
- International Business Machines Corporation. (2024, ). Cloud Computing. IBM: https://www.ibm. 14 February.
- Jayachander Surbiryala, C. R. (2019). Cloud Computing: History and Overview. 2019 IEEE Cloud Summit, 1-7. [CrossRef]
- Jhanjhi, N. , Humayun, M., & Almuayqil, S. N. (2021). Cyber security and privacy issues in industrial internet of things. N. ( 37(3), 361–380. [CrossRef]
- Jun, A. Y. M. , Jinu, B. A., Seng, L. K., Maharaiq, M. H. F. B. Z., Khongsuwan, W., Junn, B. T. K., Hao, A. a. W., & Sindiramutty, S. R. (2024). Exploring the Impact of Crypto-Ransomware on Critical Industries: Case Studies and Solutions. Preprints.org. [CrossRef]
- Kasam, A. (2024, ). Ways to Prevent Cloud Account Hijacking. ITSecurity Wire: https://itsecuritywire. 4 March.
- Khalil, I. &. (2014). Cloud Computing Security: A Survey. Computers, 3(1), 1-35. [CrossRef]
- Khan, N. A. , Jhanjhi, N. Z., Brohi, S. N., & Nayyar, A. (2020). Chapter Three-Emerging use of UAV’s: secure communication protocol issues and challenges, Editor (s): Fadi Al-Turjman, Drones in Smart-Cities.
- Kost, E. (2024, ). 8 Data Leak Prevention Strategies in 2024. UpGuard: https://www.upguard. 18 November.
- Kumar, M. S. , Vimal, S., Jhanjhi, N., Dhanabalan, S. S., & Alhumyani, H. A. (2021). Blockchain based peer to peer communication in autonomous drone operation. Energy Reports. [CrossRef]
- Lim, M. , Abdullah, A., Jhanjhi, N., Khan, M. K., & Supramaniam, M. (2019). Link Prediction in Time-Evolving Criminal Network with deep Reinforcement learning technique. IEEE Access, 1848. [Google Scholar] [CrossRef]
- Manchuri, A. , Kakera, A., Saleh, A., & Raja, S. (2024). pplication of Supervised Machine Learning Models in Biodiesel Production Research - A Short Review. Borneo Journal of Sciences and Technology. [CrossRef]
- Morrow, T. (2018, ). 12 Risks, Threats, & Vulnerabilities in Moving to the Cloud. SEI Blog: https://insights.sei.cmu. 5 March.
- Morrow, T. (2018, March 5). 12 Risks, Threats, & Vulnerabilities in moving to the cloud, 5 March.
- Mughal, M. A. , Ullah, A., Cheema, M. A. Z., Yu, X., & Jhanjhi, N. Z. (2024). An intelligent channel assignment algorithm for cognitive radio networks using a tree-centric approach in IoT. Alexandria Engineering Journal, 91, 152-160.
- Nayyar, A. , Gadhavi, L., & Zaman, N. (2021). Machine learning in healthcare: review, opportunities and challenges. In Elsevier eBooks (pp. 23–45). [CrossRef]
- Nazir, R. &. (2020). Cloud Computing Applications: A Review. EAI Endorsed Transactions on Cloud Systems, 6, 164667. [CrossRef]
- Paloalto Networks. (n.d.). What is Zero Trust Architecture (ZTA)? Paloalto Networks: https://www.paloaltonetworks.
- PingIdentity. (n.d.). What Is a Botnet Attack and How to Prevent It. PingIdentity: https://www.pingidentity.com/en/resources/cybersecurity-fundamentals/threats/botnet-attack.
- Puzas, D. (2024, ). 12 Cloud Security Issues: Risks, Threats, and Challenges. CrowdStrike: https://www.crowdstrike. 1 April.
- Ramachandran, R. (2024, ). Evolving Threats to Cloud Computing Infrastructure and Suggested Countermeasures. ISACA: https://www.isaca. 16 April 2024. [Google Scholar]
- Ravichandran, N. , Tewaraja, T., Rajasegaran, V., Kumar, S. S., Gunasekar, S. K. L., & Sindiramutty, S. R. (2024). Comprehensive Review Analysis and Countermeasures for Cybersecurity Threats: DDoS, Ransomware, and Trojan Horse Attacks. Preprints.org. [CrossRef]
- Sadiku, M. &. (2016). Social Engineering: An Introducction. The Journal of Scientific and Engineering Research, 3(3), 64-66.
- Saleh, M. , Jhanjhi, N., & Abdullah, A. (2020, February). Fatima-tuz-Zahra,‘‘Proposing a privacy protection model in case of civilian drone,’’. In Proc. 22nd Int. Conf. Adv. Commun. Technol.(ICACT) (pp. 596-602).
- Sama, N. U. , Zen, K., Humayun, M., Jhanjhi, N. Z., & Rahman, A. U. (2022). Security in wireless body sensor network: A multivocal literature study. Applied System Innovation.
- Seng, Y. J. , Cen, T. Y., Raslan, M. a. H. B. M., Subramaniam, M. R., Xin, L. Y., Kin, S. J., Long, M. S., & Sindiramutty, S. R. (2024). In-Depth Analysis and Countermeasures for Ransomware Attacks: Case Studies and Recommendations. Preprints.org. [CrossRef]
- Shah, I. A. , Jhanjhi, N. Z., & Laraib, A. (2022). Cybersecurity and blockchain usage in contemporary business. In Advances in information security, privacy, and ethics book series (pp. 49–64). [CrossRef]
- Sharma, R. , Singh, A., Kavita, N., Jhanjhi, N. Z., Masud, M., Jaha, E. S., & Verma, S. (2021). Plant disease diagnosis and image classification using deep learning. Computers, Materials & Continua/Computers, Materials & Continua (Print). [CrossRef]
- Sharma, S. K. (2024). AI-Enhanced Cyber Threat Detection and Response Systems. Shodh Sagar Journal of Artificial Intelligence and Machine Learning, 1, 43-48. [CrossRef]
- Shukur, H. &. ( 1(2), 98–105. [CrossRef]
- Sindiramutty, S. R. , Jhanjhi, N. Z., Tan, C. E., Khan, N. A., Shah, B., & Manchuri, A. R. (2024). Cybersecurity measures for logistics industry. In Advances in information security, privacy, and ethics book series (pp. 1–58). [CrossRef]
- Sindiramutty, S. R. , Jhanjhi, N. Z., Tan, C. E., Khan, N. A., Shah, B., Yun, K. J., Ray, S. K., Jazri, H., & Hussain, M. (2024). Future trends and emerging threats in drone cybersecurity. In Advances in information security, privacy, and ethics book series (pp. 148–195). [CrossRef]
- Sindiramutty, S. R. , Jhanjhi, N. Z., Tan, C. E., Yun, K. J., Manchuri, A. R., Ashraf, H., Murugesan, R. K., Tee, W. J., & Hussain, M. (2024). Data security and privacy concerns in drone operations. In Advances in information security, privacy, and ethics book series (pp. 236–290). [CrossRef]
- Sindiramutty, S. R. , Jhanjhi, N., Tan, C. E., Lau, S. P., Muniandy, L., Gharib, A. H., Ashraf, H., & Murugesan, R. K. (2024). Industry 4.0. In Advances in logistics, operations, and management science book series (pp. 342–405). [CrossRef]
- Sindiramutty, S. R. , Tan, C. E., & Wei, G. W. (2024). Eyes in the sky. In Advances in information security, privacy, and ethics book series (pp. 405–451). [CrossRef]
- Sindiramutty, S. R. , Tan, C. E., Shah, B., Khan, N. A., Gharib, A. H., Manchuri, A. R., Muniandy, L., Ray, S. K., & Jazri, H. (2024). Ethical considerations in drone cybersecurity. In Advances in information security, privacy, and ethics book series (pp. 42–87). [CrossRef]
- Singhal, V. , Jain, S. S., Anand, D., Singh, A., Verma, S., Kavita, N., Rodrigues, J. J. P. C., Jhanjhi, N. Z., Ghosh, U., Jo, O., & Iwendi, C. (2020). Artificial Intelligence Enabled Road Vehicle-Train Collision Risk Assessment Framework for Unmanned railway level crossings. IEEE Access, 1138. [Google Scholar] [CrossRef]
- Siva Raja Sindiramutty, H. A. (2023). Innovations in Security: A Study of Cloud Computing and IoT. International Journal of Emerging Multidisciplinaries: Computer Science & Artificial Intelligence. [CrossRef]
- Threats, T. (2024, ). Top Threats to Cloud Computing 2024. ISACA. Cloud Security Alliance: https://cloudsecurityalliance. 8 May 2024. [Google Scholar]
- Tigera. (2021, ). Cloud Security: Challenges and 5 Technologies That Can Help. Tigera: https://www.tigera. 1 December.
- Trendmicro. (2020, ). Cloud Security: Key Concepts, Threats, and Solutions. Trendmicro: https://www.trendmicro. 14 May.
- Vijayalakshmi, B. , Ramar, K., Jhanjhi, N. Z., Verma, S., Kaliappan, M., Vijayalakshmi, K.,... & Ghosh, U. (2021). An attention-based deep learning model for traffic flow prediction using spatiotemporal features towards sustainable smart city. International Journal of Communication Systems.
- Waheed, A. , Seegolam, B., Jowaheer, M. F., Sze, C. L. X., Hua, E. T. F., & Sindiramutty, S. R. (2024). Zero-Day Exploits in Cybersecurity: Case Studies and Countermeasure. preprints.org. [CrossRef]
- Wen, B. O. T. , Syahriza, N., Xian, N. C. W., Wei, N. G., Shen, T. Z., Hin, Y. Z., Sindiramutty, S. R., & Nicole, T. Y. F. (2023). Detecting cyber threats with a Graph-Based NIDPS. In Advances in logistics, operations, and management science book series (pp. 36–74). [CrossRef]
- Zain Tahir, M. A. (2015). CLOUD COMPUTING INFLUENCE ON OPERATING SYSTEM. SCIENCE INTERNATIONAL.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



