Introduction
The Internet of Things (IoT) has emerged as a transfor- mative paradigm, enabling interconnected devices to share data and perform tasks autonomously across diverse domains, including smart cities, healthcare, agriculture, and industrial automation [
1,
2]. As IoT networks expand, the need for scalable, energy-efficient, and long-range communication technologies becomes increasingly critical. LoRaWAN (Long Range Wide Area Network) has gained significant attention as a leading low-power wide-area network (LPWAN) protocol due to its ability to support long-range communication with minimal energy consumption [
3,
4].
LoRaWAN operates on top of the LoRa (Long Range) phys- ical layer and is specifically designed to address the constraints of IoT applications, such as limited power, bandwidth, and computational resources [
5,
6]. It provides key features like adaptive data rates, bi-directional communication, and robust security mechanisms, making it suitable for large-scale IoT deployments [
7]. Despite its advantages, the protocol faces several challenges, including network scalability, interference
in unlicensed frequency bands, and the need for enhanced security against evolving cyber threats [
8,
9].
This review article explores the current state of LoRaWAN protocols in IoT, highlighting the challenges, recent innova- tions, and potential future directions. The discussion encom- passes various aspects of the protocol, such as its architecture, performance in large-scale deployments, and advancements in security mechanisms. Furthermore, the review aims to provide insights into emerging research trends and novel applications that could shape the future of LoRaWAN in the IoT ecosystem [
10,
11].
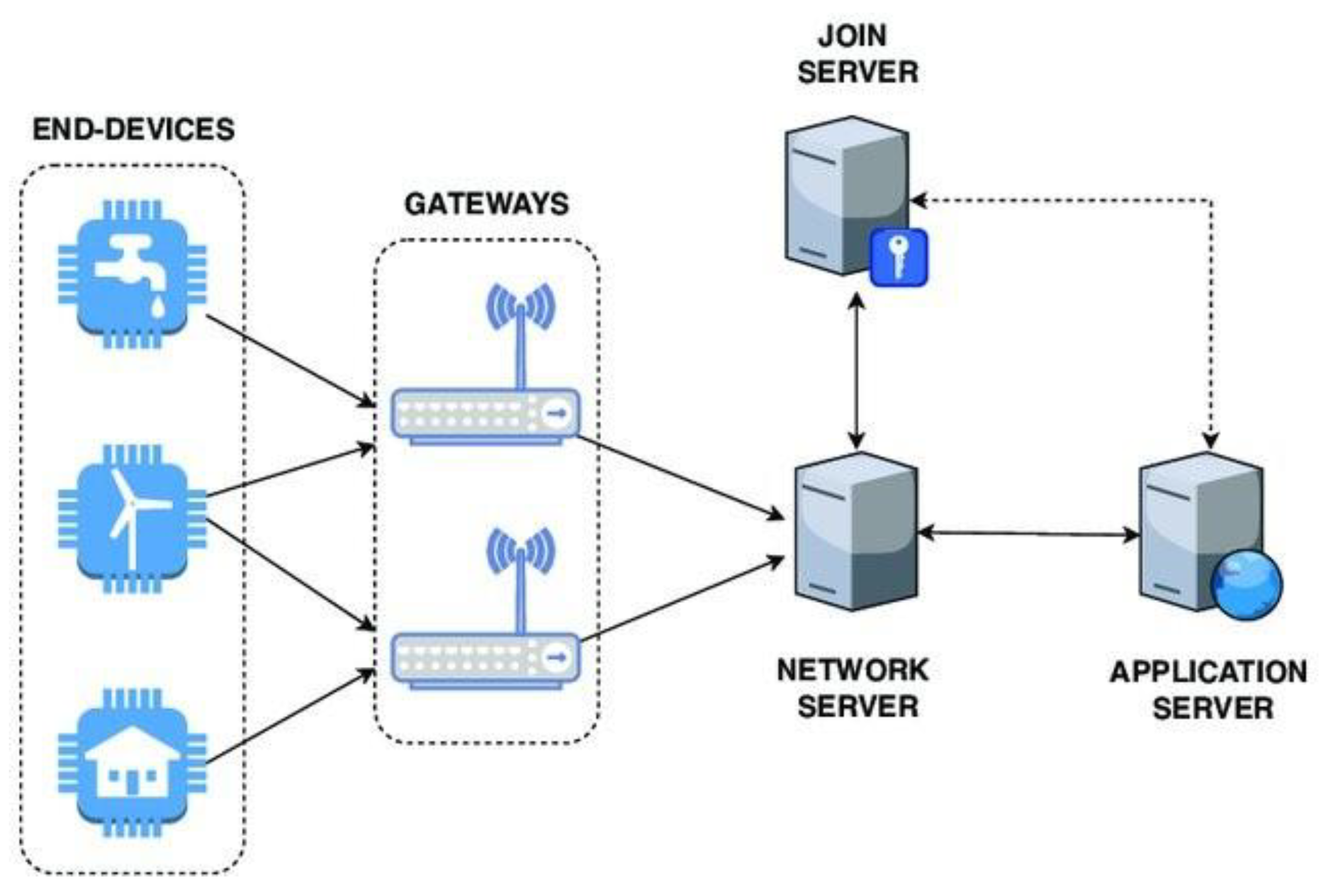
Figure 1.
Architecture of a LoRaWAN Network [
12].
Figure 1.
Architecture of a LoRaWAN Network [
12].
Architecture and Technical Details
The LoRaWAN architecture is a hierarchical system de- signed to enable long-range communication for Internet of Things (IoT) devices, optimizing power consumption and scalability [
7,
8]. The architecture consists of four primary components: End Devices, Gateways, Network Servers, and Application Servers. These components work together to sup- port bi-directional communication and manage the complexi- ties of data transmission, security, and network management.
A. End Devices
End devices, or nodes, are low-power IoT devices equipped with LoRa transceivers. These devices are responsible for
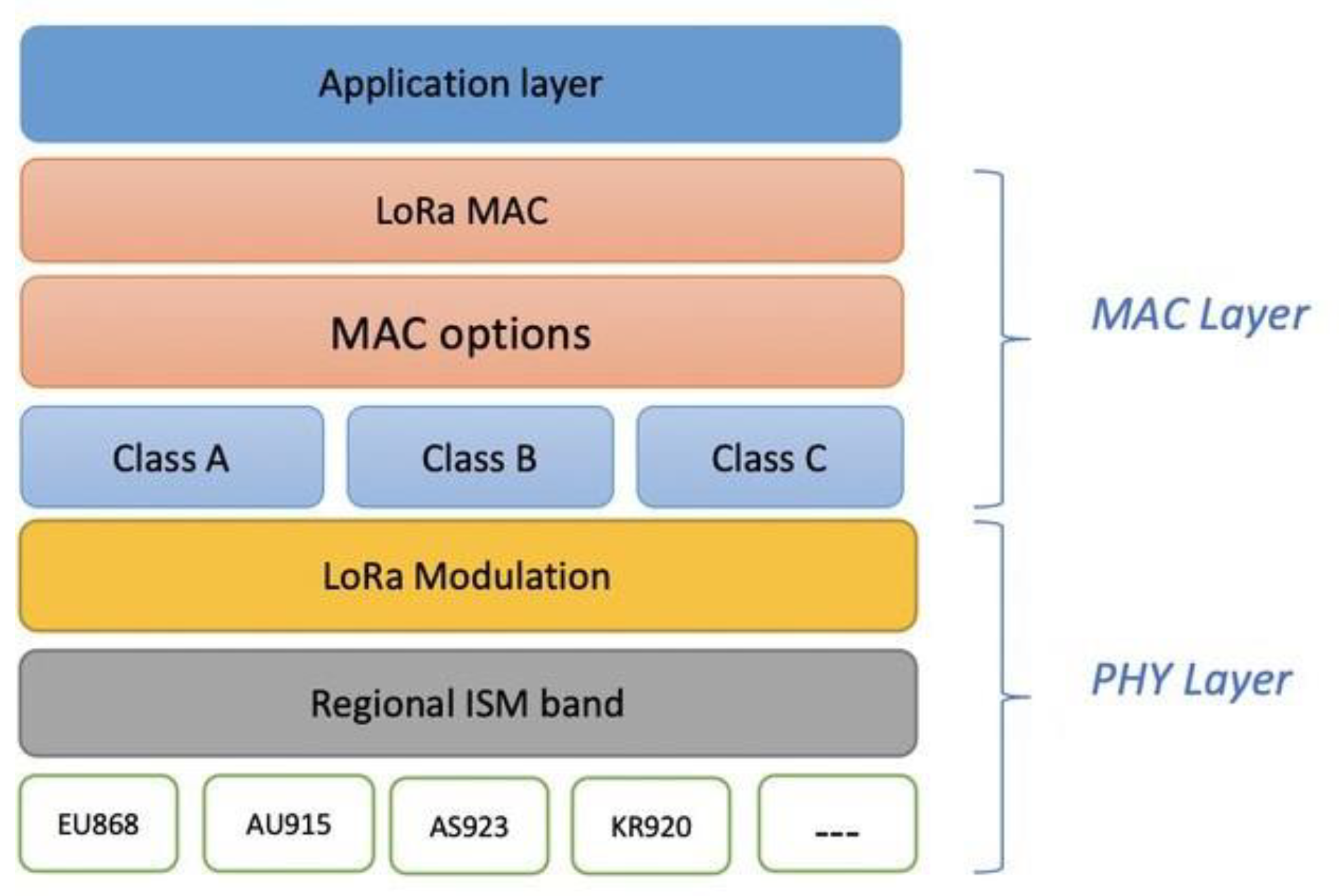
Figure 2.
LoRa/LoRaWAN literature taxonomy. [
13].
Figure 2.
LoRa/LoRaWAN literature taxonomy. [
13].
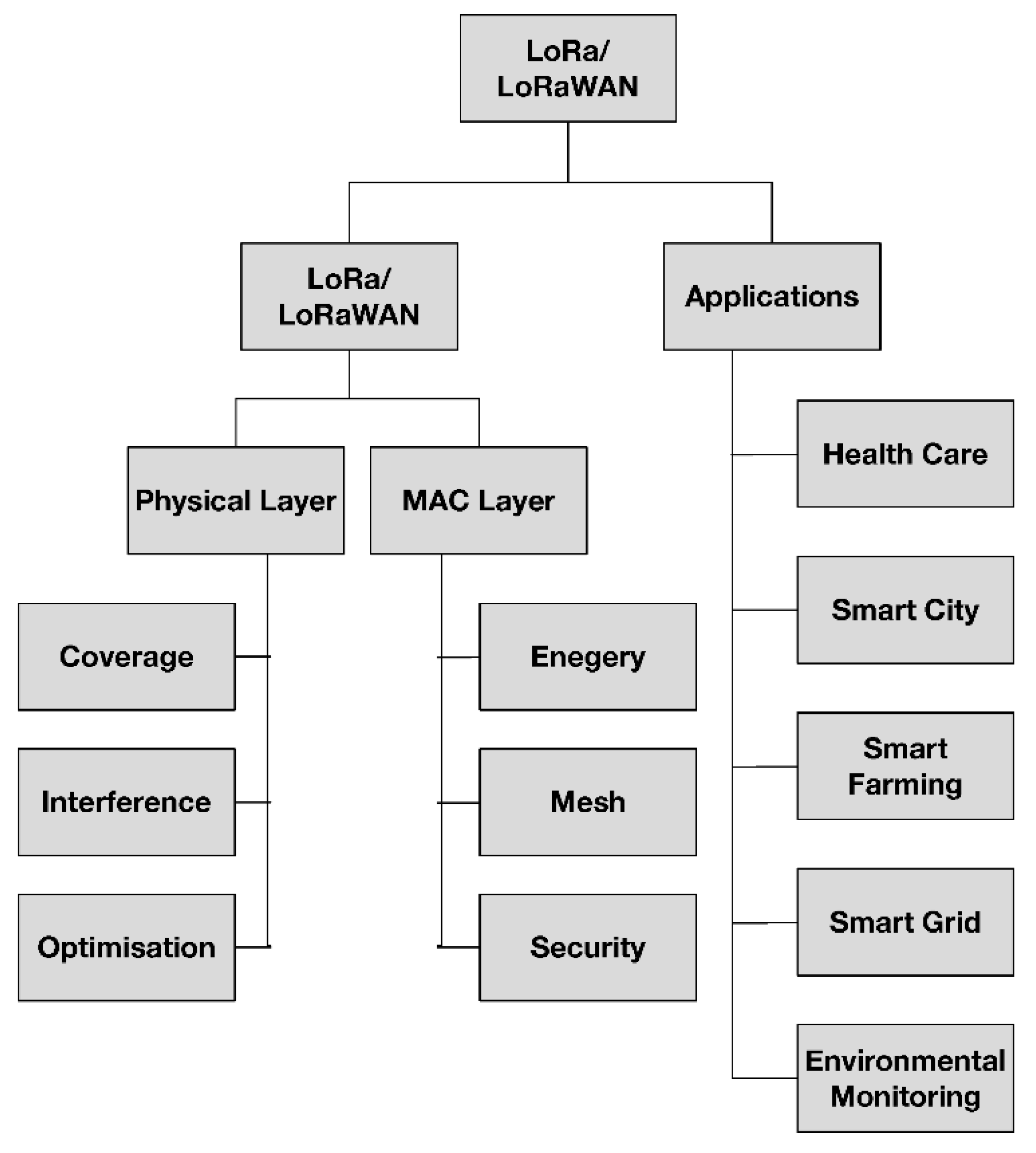
collecting and transmitting data to gateways using the LoRa physical layer [
3]. End devices operate in one of three classes, designed to balance energy efficiency and latency require- ments:
Class A: Devices in this class use an ALOHA-based protocol for uplink communication and open two receive windows for downlink communication after each uplink transmission. This design minimizes power consumption but results in higher latency [
7].
Class B: These devices extend Class A functionality by synchronizing with the network through periodic beacons, allowing scheduled downlink communication [
5].
Class C: Devices in this class keep their receive windows open except during uplink transmission, enabling low- latency communication but at the expense of higher power consumption [
7].
Gateways
Gateways serve as intermediaries between end devices and the network server. These devices forward uplink transmis- sions from end devices to the network server and relay downlink messages from the network server to the devices [
8]. Gateways operate using the LoRaWAN MAC layer and communicate with the network server via standard IP connec- tions, such as Ethernet or cellular networks [
3].
A. Network Server
The network server is a critical component responsible for managing data traffic, optimizing network performance, and ensuring security [
7]. It handles tasks such as:
Figure 3.
LoRaWAN Protocol Stack [
14].
Figure 3.
LoRaWAN Protocol Stack [
14].
Adaptive Data Rate (ADR): Adjusting the transmission parameters of end devices to optimize energy efficiency and maintain reliable communication [
5].
Duplicate Packet Detection: Identifying and discarding duplicate packets received from multiple gateways [
8].
Device Authentication: Ensuring secure communication through mutual authentication of devices and servers [
7].
A. Application Server
The application server processes and interprets the data received from end devices, providing it to end-users or other applications [
10]. It also ensures application-level security by decrypting the payloads and managing device-specific application keys [
7].
A. Communication Protocols
LoRaWAN uses a star-of-stars topology, where gateways act as concentrators for end devices [
5]. The protocol employs the Chirp Spread Spectrum (CSS) modulation technique at the physical layer, enabling robust long-range communication even in the presence of noise and interference [
3]. Data transmission uses unlicensed ISM frequency bands, such as 868 MHz in Europe and 915 MHz in North America, ensuring global applicability [
7,
8].
This modular and flexible architecture allows LoRaWAN to cater to a wide range of IoT applications, from low-power sensor networks to latency-sensitive industrial deployments.
Challenges Associated with Protocol
While LoRaWAN has established itself as a leading protocol for IoT applications, it faces several challenges that impact its scalability, performance, and reliability [
7,
15].
A. Scalability Issues
One of the key challenges with LoRaWAN is ensuring scal- ability in dense network deployments. The use of unlicensed spectrum, combined with the ALOHA-based communication mechanism, can lead to increased collisions as the number of end devices grows [
8]. This limits the network’s ability to
handle a large number of simultaneous transmissions, affecting overall performance [
3].
A. Interference and Noise
LoRaWAN networks are prone to interference and noise due to their operation in unlicensed Industrial, Scientific, and Medical (ISM) bands. The coexistence of multiple LoRaWAN networks and other devices within the same frequency bands can degrade communication quality [
5]. Furthermore, Chirp Spread Spectrum (CSS) modulation, while robust, is not immune to interference [
7].
A. Security Concerns
Despite robust encryption mechanisms, LoRaWAN faces security challenges such as eavesdropping, replay attacks, and key management issues. The reliance on pre-shared keys for device authentication and encryption makes the network vulnerable to key compromise [
10,
16].
A. Energy Constraints
Energy efficiency is a critical concern for end devices in LoRaWAN networks. While the protocol supports low-power operation, prolonged communication, retransmissions due to collisions, and high-duty-cycle operations can deplete device batteries quickly [
7,
8].
A. Quality of Service (QoS)
LoRaWAN does not natively support mechanisms for prior- itizing data packets, which can be problematic for applications requiring low latency and high reliability [
3]. The lack of QoS differentiation can result in degraded performance for critical IoT applications.
A. Regulatory Limitations
The duty cycle limitations imposed by regional regulations, such as ETSI in Europe, restrict the maximum time a device can transmit, further complicating network design and reduc- ing throughput [
8].
Addressing these challenges is critical for advancing Lo- RaWAN’s role in IoT ecosystems. Ongoing research and innovations aim to enhance scalability, improve security, and optimize energy efficiency to meet the growing demands of IoT applications.
Challenges Associated with Protocol
While LoRaWAN has established itself as a leading protocol for IoT applications, it faces several challenges that impact its scalability, performance, and reliability [
7,
15].
A. Scalability Issues
One of the key challenges with LoRaWAN is ensuring scal- ability in dense network deployments. The use of unlicensed spectrum, combined with the ALOHA-based communication mechanism, can lead to increased collisions as the number of end devices grows [
8]. This limits the network’s ability to handle a large number of simultaneous transmissions, affecting overall performance [
3].
A. Interference and Noise
LoRaWAN networks are prone to interference and noise due to their operation in unlicensed Industrial, Scientific, and Medical (ISM) bands. The coexistence of multiple LoRaWAN networks and other devices within the same frequency bands can degrade communication quality [
5]. Furthermore, Chirp Spread Spectrum (CSS) modulation, while robust, is not immune to interference [
7].
A. Security Concerns
Despite robust encryption mechanisms, LoRaWAN faces security challenges such as eavesdropping, replay attacks, and key management issues. The reliance on pre-shared keys for device authentication and encryption makes the network vulnerable to key compromise [
10,
16].
A. Energy Constraints
Energy efficiency is a critical concern for end devices in LoRaWAN networks. While the protocol supports low-power operation, prolonged communication, retransmissions due to collisions, and high-duty-cycle operations can deplete device batteries quickly [
7,
8].
A. Quality of Service (QoS)
LoRaWAN does not natively support mechanisms for prior- itizing data packets, which can be problematic for applications requiring low latency and high reliability [
3]. The lack of QoS differentiation can result in degraded performance for critical IoT applications.
A. Regulatory Limitations
The duty cycle limitations imposed by regional regulations, such as ETSI in Europe, restrict the maximum time a device can transmit, further complicating network design and reduc- ing throughput [
8].
Addressing these challenges is critical for advancing Lo- RaWAN’s role in IoT ecosystems. Ongoing research and innovations aim to enhance scalability, improve security, and optimize energy efficiency to meet the growing demands of IoT applications.
Recent Innovations and Solutions to
Challenges
Recent advancements in LoRaWAN technology have ad- dressed many of the challenges associated with its deployment and scalability. Innovative solutions in network management, interference mitigation, and security enhancement are paving the way for more reliable and efficient IoT applications.
A. Scalability Enhancements
To address scalability issues, adaptive channel allocation and dynamic duty cycle management have been proposed [
8]. These techniques optimize the utilization of available spectrum by dynamically reallocating channels and adjusting transmis- sion parameters based on network conditions. Furthermore, the implementation of hybrid MAC protocols that combine ALOHA with scheduled access can significantly reduce packet collisions in dense deployments [
15].
A. Interference Mitigation
The introduction of frequency hopping techniques has shown promise in mitigating interference in LoRaWAN net- works [
3]. By periodically changing transmission frequencies, devices can avoid persistent interference in specific channels. Advanced error correction algorithms, such as Forward Error Correction (FEC), have also been integrated to improve data integrity in noisy environments [
5].
A. Security Enhancements
Emerging solutions to enhance LoRaWAN security include the implementation of blockchain for secure key management and device authentication [
16]. Additionally, lightweight en- cryption algorithms tailored for resource-constrained devices are being developed to strengthen end-to-end security [
10].
A. Energy Optimization
Energy-efficient communication schemes, such as adaptive power control and energy harvesting techniques, are being explored to extend the battery life of end devices [
7]. These methods dynamically adjust transmission power and leverage environmental energy sources to reduce reliance on battery power.
A. Quality of Service (QoS) Improvements
To address QoS challenges, priority-based scheduling algo- rithms have been introduced to differentiate between critical and non-critical data packets [
8]. These algorithms ensure timely delivery of high-priority messages, enhancing the re- liability of mission-critical applications.
A. Regulatory Compliance
Advanced duty cycle optimization algorithms are being de- veloped to maximize throughput within regulatory constraints [
5]. These algorithms intelligently schedule transmissions to comply with regional regulations while maintaining efficient data flow.
These innovations demonstrate the evolving nature of Lo- RaWAN technology and its adaptability to the complex re- quirements of modern IoT ecosystems. Future research and development will likely focus on further enhancing these solutions to ensure the protocol remains a cornerstone of IoT communication.
Future Research Directions
The continuous evolution of IoT ecosystems and the grow- ing demands for efficient, secure, and scalable communication networks necessitate ongoing advancements in LoRaWAN technology. This section highlights key areas where future research can address existing limitations and unlock new potential for the protocol.
A. Advanced Network Scalability Solutions
Future research should explore novel approaches to improve LoRaWAN’s scalability in dense deployments. Techniques such as machine learning-based adaptive resource allocation and predictive congestion management could dynamically op- timize network performance [
17]. Additionally, investigating hybrid protocols that integrate LoRaWAN with other com- munication technologies may enhance network capacity and reliability [
18].
A. Interference and Spectrum Utilization
As the number of devices operating in unlicensed frequency bands increases, developing sophisticated interference miti- gation strategies becomes critical. Future studies could fo- cus on advanced spectrum-sharing algorithms, cognitive radio techniques, and cross-technology coexistence mechanisms to improve communication quality [
3]. Additionally, expanding the use of licensed spectrum for critical applications may warrant exploration.
A. Enhanced Security Frameworks
To address emerging cybersecurity threats, future research must prioritize the development of advanced security frame- works. Techniques such as quantum-resistant encryption, de- centralized key management using blockchain, and real-time anomaly detection through AI-driven methods can signifi- cantly bolster LoRaWAN’s security [
16,
19].
A. Energy Efficiency and Sustainability
With the increasing emphasis on sustainability, research should aim to further optimize energy consumption in Lo- RaWAN networks. Promising directions include the integra- tion of energy harvesting technologies, AI-driven power man- agement, and the development of ultra-low-power hardware for IoT devices [
7,
10].
A. Support for Quality of Service (QoS)
Enhancing LoRaWAN’s ability to support diverse QoS requirements is crucial for its adoption in latency-sensitive applications. Future efforts could focus on developing adaptive QoS management schemes, such as traffic prioritization and delay-aware routing, to ensure reliable performance across various use cases [
8].
A. Integration with Emerging Technologies
The convergence of LoRaWAN with emerging technologies like 5G, edge computing, and AI offers immense potential for innovation. Research should explore synergies between these technologies to enable intelligent, adaptive, and context- aware IoT networks [
11]. Additionally, leveraging digital twin technology to simulate and optimize LoRaWAN deployments may provide valuable insights.
A. Standardization and Global Interoperability
To promote widespread adoption, future research should emphasize the development of standardized protocols and in- teroperability frameworks. This includes harmonizing regional regulatory requirements, ensuring cross-vendor compatibility, and enabling seamless integration with diverse IoT ecosystems [
10].
These research directions hold the promise of overcoming current limitations and expanding the scope of LoRaWAN in IoT applications. By addressing these challenges, the proto- col can solidify its position as a cornerstone of future IoT networks.
Conclusions
LoRaWAN has emerged as a critical enabler for long-range, low-power communication in the rapidly evolving IoT ecosys- tem. Its unique characteristics, such as long-range coverage, low power consumption, and cost-effective deployment, make it a promising solution for diverse IoT applications, including smart cities, agriculture, industrial monitoring, and healthcare [
3,
7]. Despite its widespread adoption, LoRaWAN faces several challenges, including scalability issues, interference, energy constraints, and security vulnerabilities, that hinder its performance in dense and large-scale deployments [
8,
10].
Recent advancements have addressed many of these limita- tions by introducing innovations such as adaptive channel allo- cation, frequency hopping, energy optimization schemes, and enhanced security mechanisms [
11,
16]. These solutions have significantly improved the protocol’s reliability, efficiency, and robustness in real-world IoT applications. However, as IoT networks continue to scale and new use cases emerge, additional research is needed to tackle challenges related to quality of service, regulatory compliance, and security in resource-constrained environments [
18,
19].
The future of LoRaWAN lies in its integration with comple- mentary technologies, such as machine learning, blockchain, and edge computing, to achieve intelligent, secure, and adap- tive IoT communication systems [
10,
19]. Moreover, the development of hybrid communication protocols and novel energy-harvesting techniques will play a crucial role in over- coming current limitations and enhancing network efficiency [
7,
11]. With continued research and development, Lo- RaWAN has the potential to remain a cornerstone technology for scalable and sustainable IoT deployments in the coming years.
In summary, this review has highlighted the architecture, challenges, innovations, and future directions of the Lo- RaWAN protocol. By addressing existing limitations and em- bracing emerging technologies, LoRaWAN can evolve to meet the growing demands of next-generation IoT applications, enabling a smarter and more connected world [
3,
7,
8].
References
- L. Atzori, A. Iera, and G. Morabito, “The internet of things: A survey,”.
-
Computer networks, vol. 54, no. 15, pp. 2787–2805, 2010.
- J. Gubbi, R. Buyya, S. Marusic, and M. Palaniswami, “Internet of things (iot): A vision, architectural elements, and future directions,” Future generation computer systems, vol. 29, no. 7, pp. 1645–1660, 2013. [CrossRef]
- M. Centenaro, L. Vangelista, A. Zanella, and M. Zorzi, “Long-range communications in unlicensed bands: The rising stars in the iot and smart city scenarios,” IEEE Wireless Communications, vol. 23, no. 5,.
- pp. 60–67, 2016.
- T. Rault, A. Bouabdallah, and Y. Challal, “Energy efficiency in wireless sensor networks: A top-down survey,” Computer networks, vol. 67, pp. 104–122, 2014. [CrossRef]
- Augustin, J. Yi, T. Clausen, and W. Townsley, “A study of lora: Long range low power networks for the internet of things,” Sensors, vol. 16, no. 9, p. 1466, 2016. [CrossRef]
- F. Samie, L. Bauer, and J. Henkel, “Can we develop energy-efficient iot applications without compromising qos?” Proceedings of the 14th ACM Conference on Embedded Network Sensor Systems, pp. 279–280, 2016.
- F. Adelantado, X. Vilajosana, P. Tuset-Peiro, B. Martinez, J. Melia- Segui, and T. Watteyne, “Understanding the limits of lorawan,” IEEE Communications Magazine, vol. 55, no. 9, pp. 34–40, 2017. [CrossRef]
- Reynders, W. Meert, and S. Pollin, “An overview of lorawan,” In Proceedings of ISWCS, pp. 1–7, 2018.
- Slama, “The internet of things: Connecting the physical world to the cloud,” Springer, 2016.
- X. Li and P. Jiang, “A survey on the integration of blockchain with iot to enhance performance and address challenges,” IEEE Access, vol. 7,.
- pp. 21 045–21 064, 2019.
- Q. Huang and K. Du, “Recent advances in lorawan for iot: A survey,”.
-
Sensors, vol. 20, p. 5046, 2020.
- V. Ribeiro, R. Holanda, A. Ramos, and J. J. Rodrigues, “Enhancing key management in lorawan with permissioned blockchain,” Sensors, vol. 20, no. 11, p. 3068, 2020. [CrossRef]
- M. A. Ertu¨rk, M. A. Aydın, M. T. Bu¨yu¨kakkas¸lar, and H. Evirgen, “A survey on lorawan architecture, protocol and technologies,” Future internet, vol. 11, no. 10, p. 216, 2019. [CrossRef]
- M. Baddula, B. Ray, and M. Chowdhury, “Performance evaluation of aloha and csma for lorawan network,” in 2020 IEEE Asia-Pacific Conference on Computer Science and Data Engineering (CSDE). IEEE, 2020, pp. 1–6.
- Slinowsky and T. Rajabioun, “Scalability and performance analysis of lorawan for the internet of things,” IoT, vol. 1, no. 2, pp. 120–134, 2020.
- M. O. Farooq and M. Waseem, “A review on lorawan security for iot: Current solutions, open issues, and future directions,” Future Internet, vol. 12, no. 4, p. 63, 2020.
- L. Atzori, A. Iera, and G. Morabito, “The internet of things: A survey on enabling technologies, protocols, and applications,” Computer Networks, vol. 170, p. 107118, 2020.
- Adelantado, X. Vilajosana, P. Tuset-Peiro, B. Martinez, J. Melia`- Segu´ı, and T. Watteyne, “Understanding the limits of lorawan,” IEEE Communications Magazine, vol. 57, no. 6, pp. 34–40, 2019. [CrossRef]
- L. Zhu, X. Tan et al., “Secure iot communication enabled by blockchain,” Future Generation Computer Systems, vol. 125, pp. 615– 630, 2021.
|
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).