Submitted:
24 October 2024
Posted:
25 October 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
- for certain risks, the user can independently choose between a quantitative or qualitative method of risk assessment, depending on the available data,
- The ERM user can, in accordance with his needs, independently adjust the method of risk assessment through adjustable risk matrices (matrix size, x and y axes, calculation, ALARP zone, specific Heat map),
- The ERM user can independently choose the risk assessment methodology for a specific risk: risk matrix, Kinney method, API 580, 581, heuristic model, etc.
- The user of ERM can supplement the knowledge base in accordance with his needs or in accordance with compliance with prescribed regulations.
2. Methodology
- Connecting ISO 31000 and COSO framework,
- Application of expert knowledge in hazard identification,
- Connecting hazard and risk,
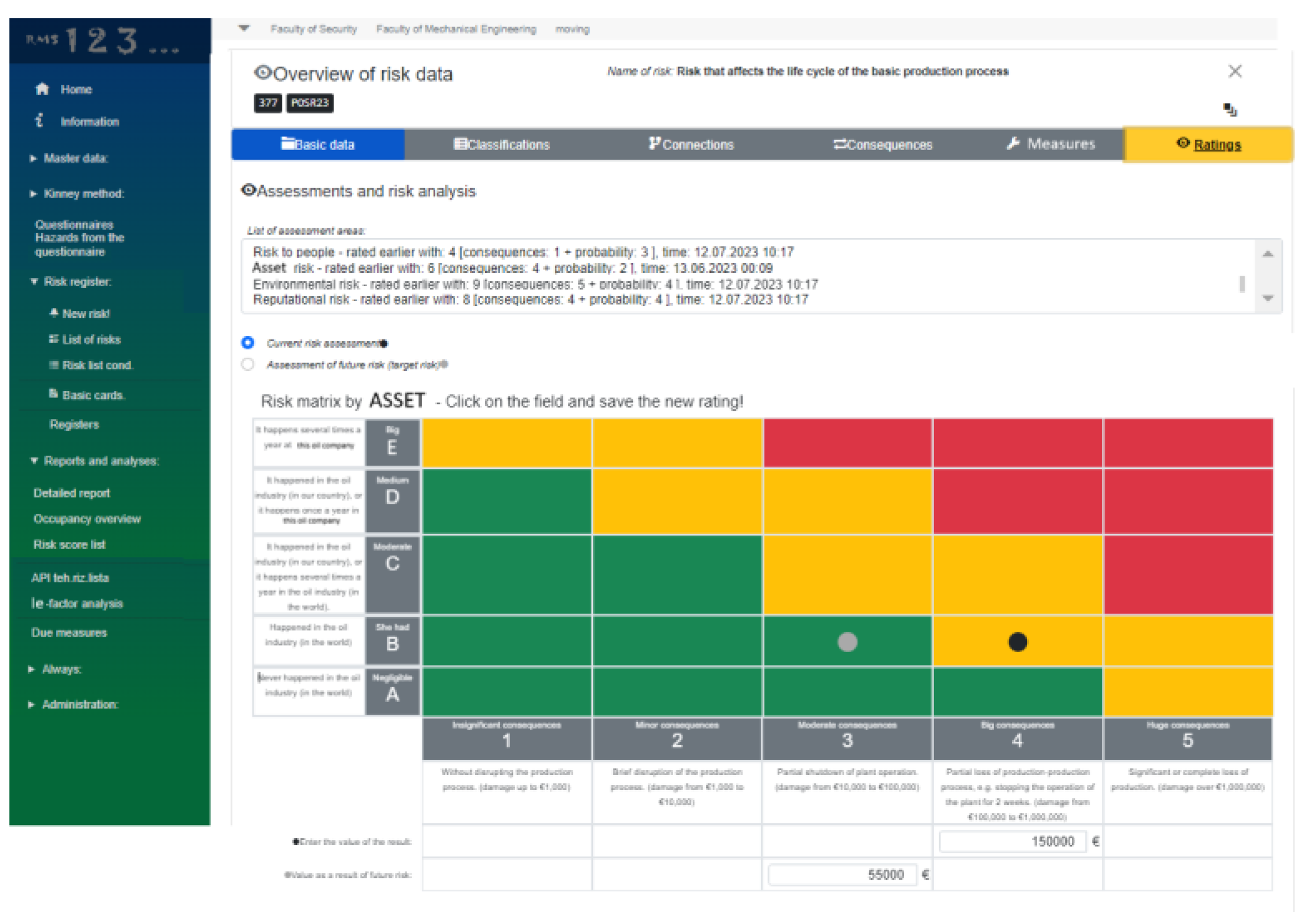
- Determination of risk appetite and adjustment of the risk matrix accordingly (5x5 matrices, 3x3 matrix, etc.) for as much risk types as needed (asset, safety, environment, reputation etc.),
- Different risk assessment methodologies (quantitative, qualitative, semi-qualitative) Kinney, API 581, FMEA, etc.).
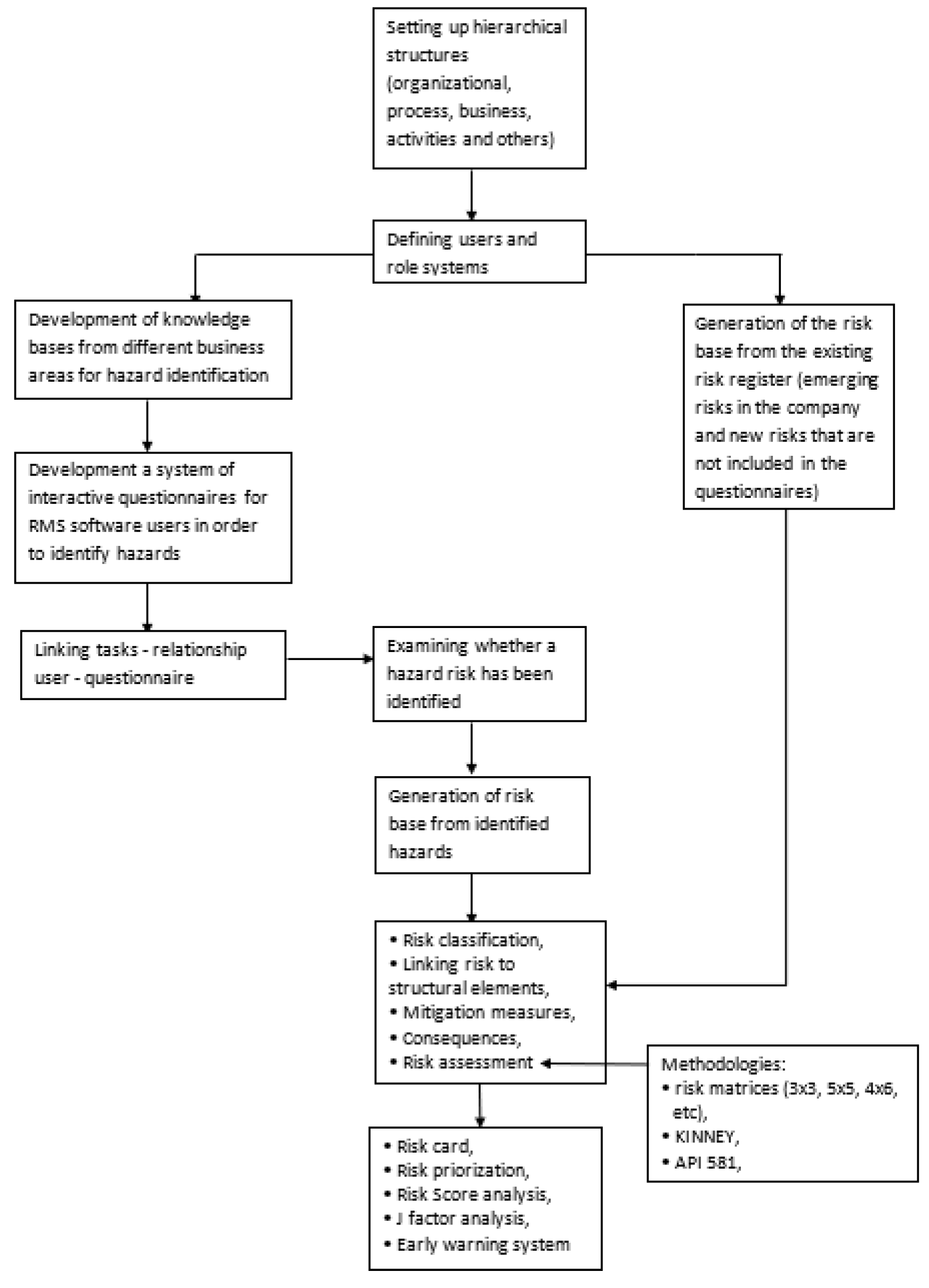
- External experts input knowledge in database: This step involves external experts providing their insights and knowledge into a centralized database.
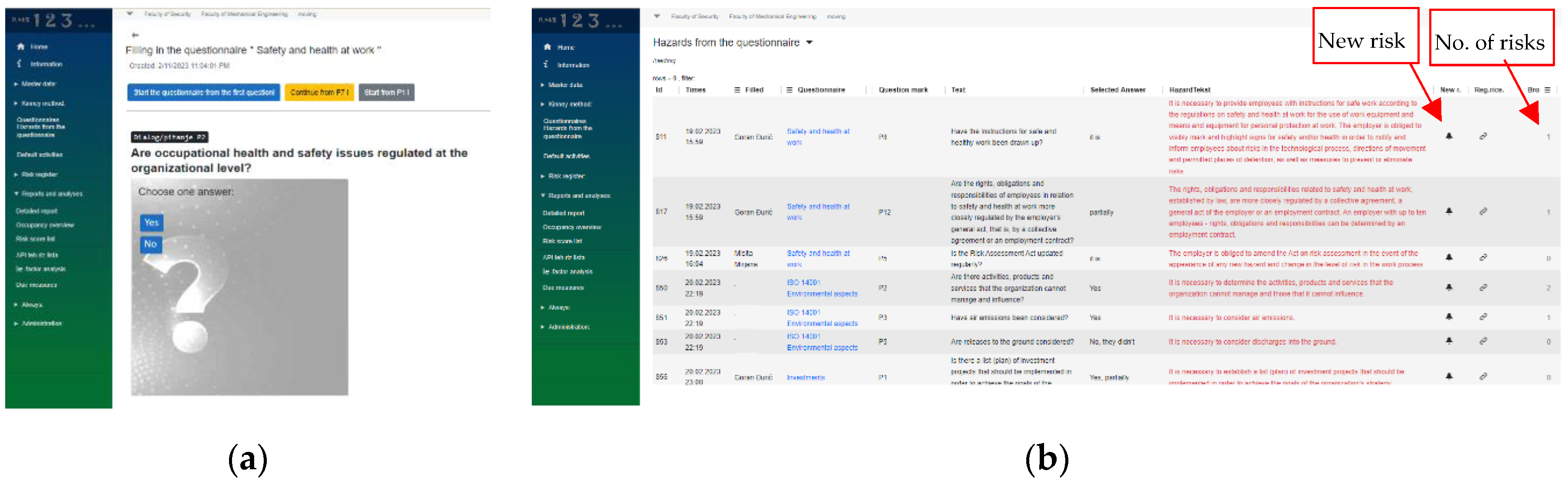
- Internal experts go through questionnaires: Internal experts review and respond to questionnaires created by external experts or surveys designed to assess various hazards. This step is important in order to give possibility for internal experts to see their risks from a different angle, that is, from external expertise and the generated heuristic knowledge base.
- Hazard database is generated according to internal experts’ answers: Based on the responses provided by internal experts, a hazard database is compiled or updated.
- Form this point joint team work of internal and external experts is needed to make suitable decision: Is a hazard a risk? At this juncture, there’s a decision point where the experts evaluates whether a hazard identified in the database poses a risk or not.
-
If Yes, then the flowchart branches out further:
- Additional steps might include risk assessment, risk mitigation strategies, etc.
-
If No, then the flowchart may lead to actions such as:
- Further assessment to understand why it’s not considered a risk.
- Updating the hazard database accordingly.
- Closing the assessment loop.
- Regardless of the process of generating risks arising from hazards, the risk base is supplemented with the entry of acknowledged risks (existing risks in the observed company)
- Risk Management process, updating classification, updating mitigation measures, updating risk assessments, etc.
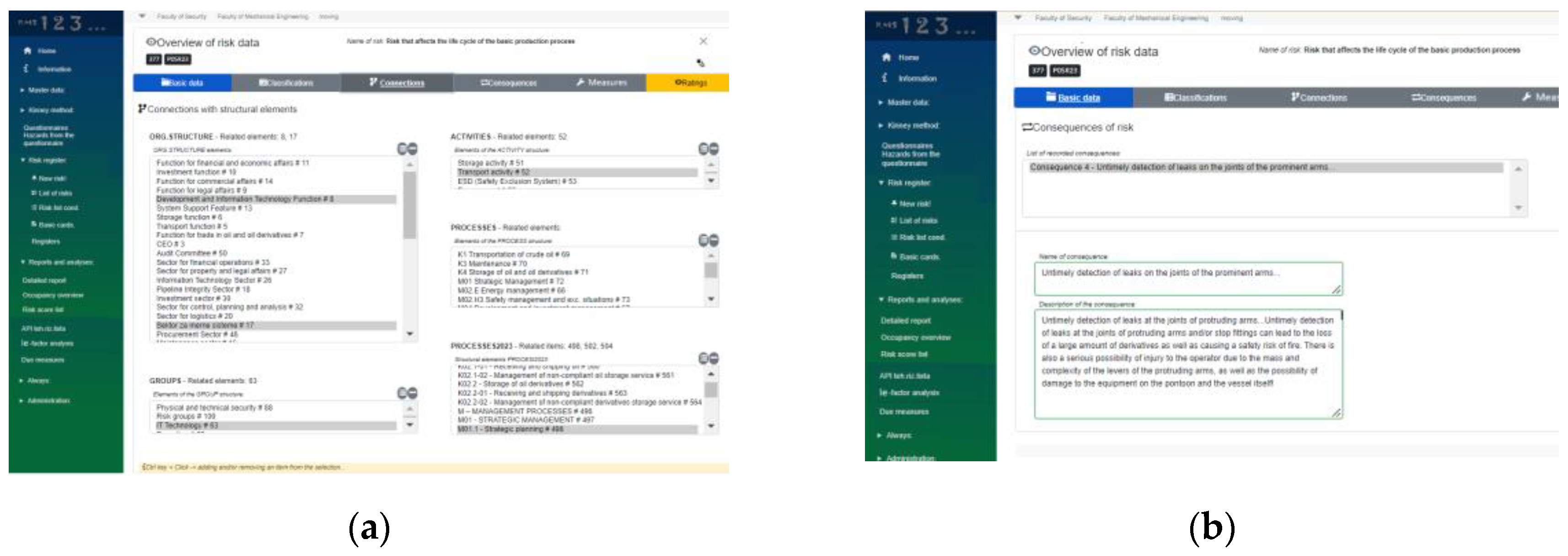
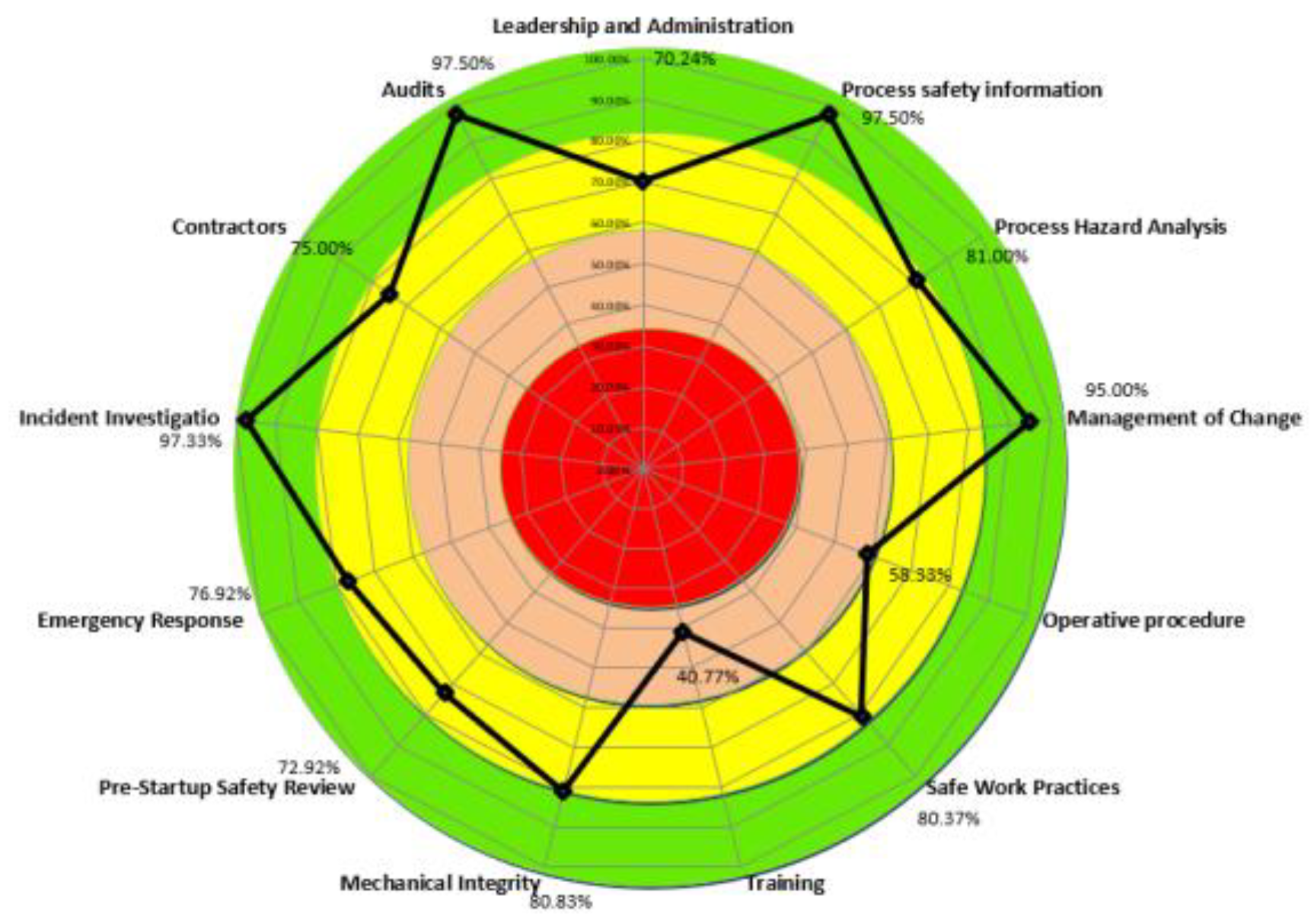
- Finally, based on the implemented processes of connecting risks with elements of organizational structures & units (COSO framework), it is possible to generate different risk cards, perform Risk Score analysis and Ie-factor (Investment effectiveness) analysis.
3. Software Solution RMS
- Implementation of the procedure of risk source identification in business-production system,
- Usage of expert knowledge from more than 52 business areas,
- Usage of risk management standards like ISO 31000 and COSO approach,
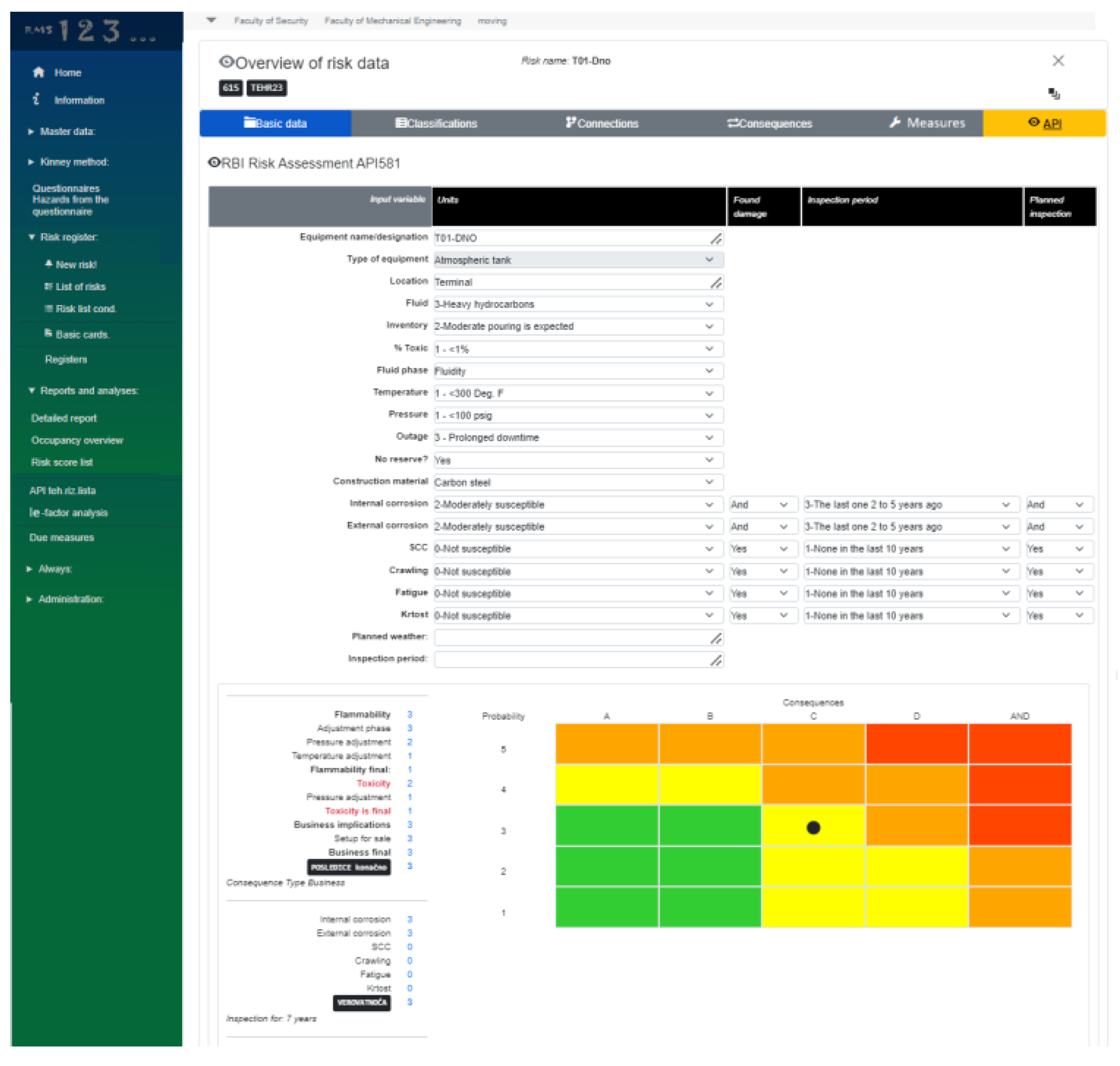
- Usage of applicable technical standards like API 580.
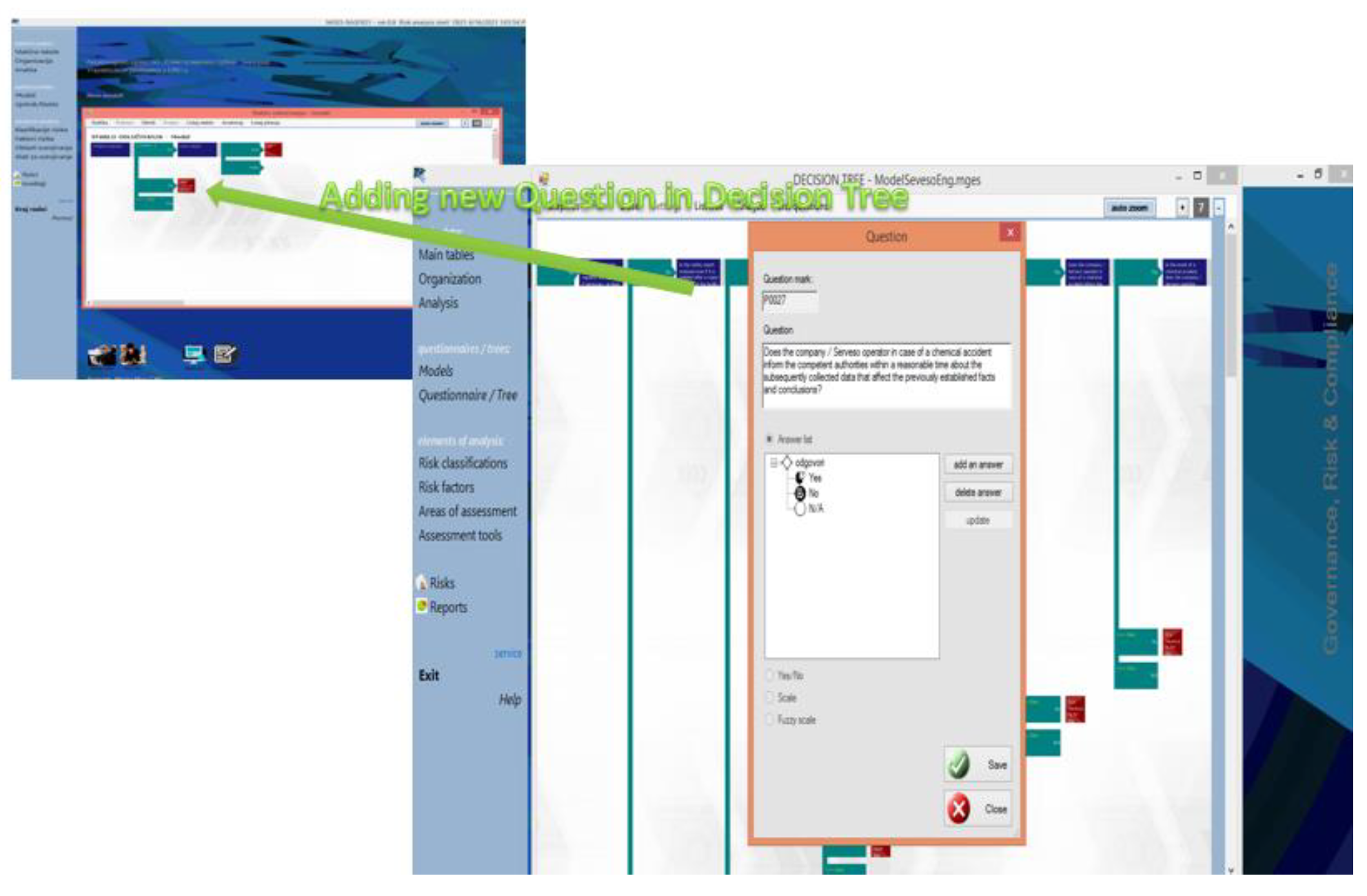
- Integrated knowledge database allows updating, expanding or adapting to a specific business-production decision tree system,
- Integrated knowledge database enables the definition of new decision trees if a user has the need to store specific knowledge in the identification of risk sources, characteristic for a particular business system.
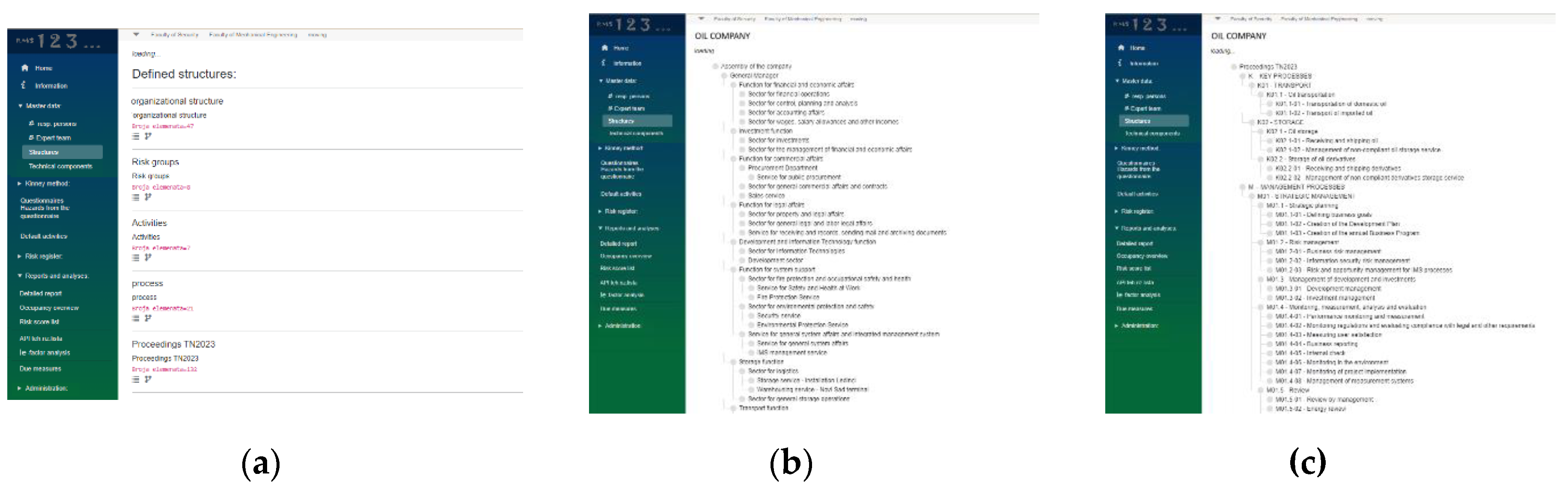
- Home page
- Information
-
Master data
- Responsibile persons (internal experts)
- Expert tim (external)
- Stuctures
-
Organisational structure
- Hierarhical structure of processess
- Hierarhical structure of strategic objecitves
- Hierarhical structure of business areas
- Hierarhical structure of different risk groups
- Project Management (management of tasks)
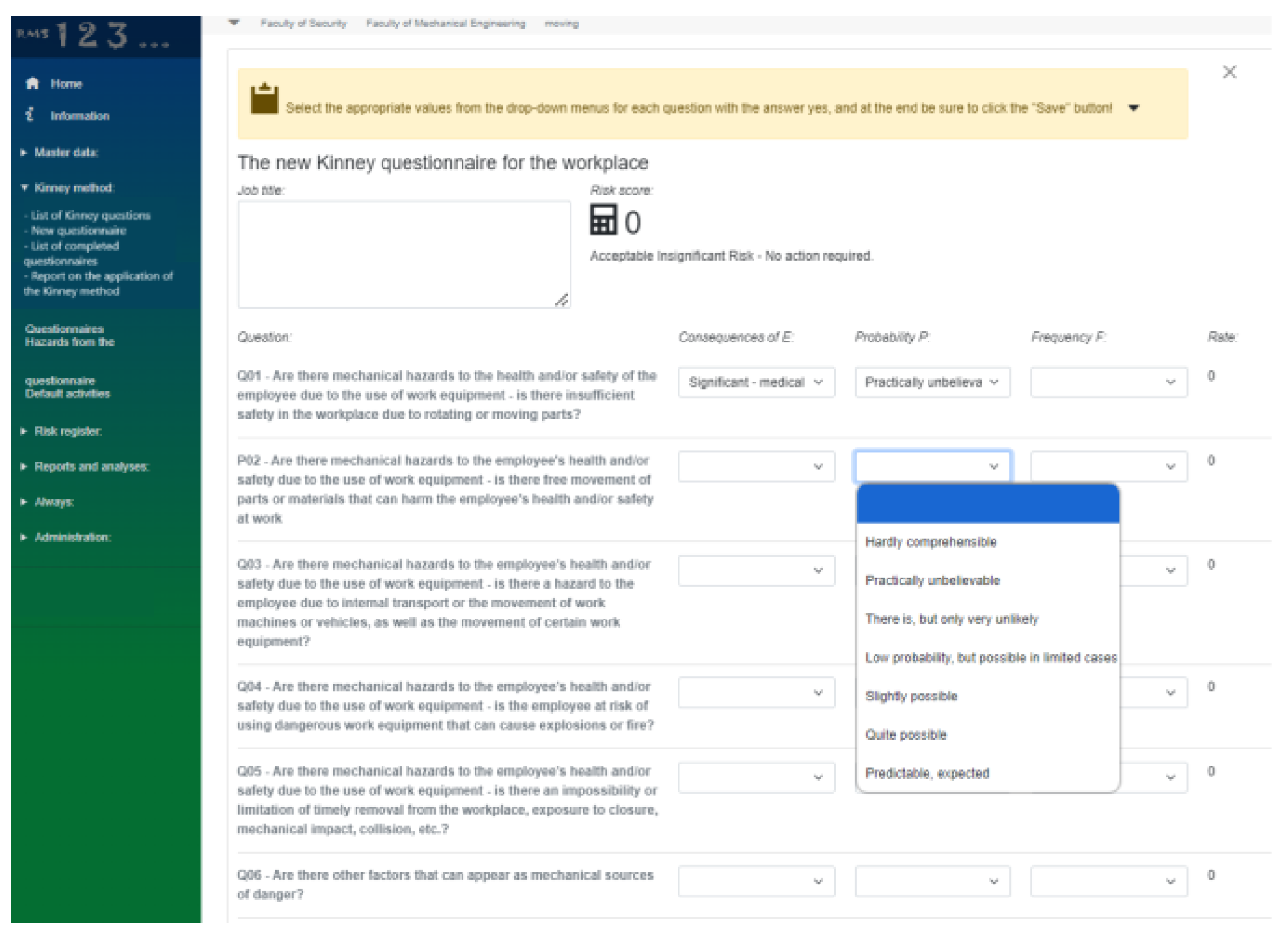
- The Kinney Method
- Risk Based Inspections (API 580 and similar)
- Questionnaires / Models
- Hazards
- Elements of analysis (Elements of risk matrices, Risk calculation, etc.)
-
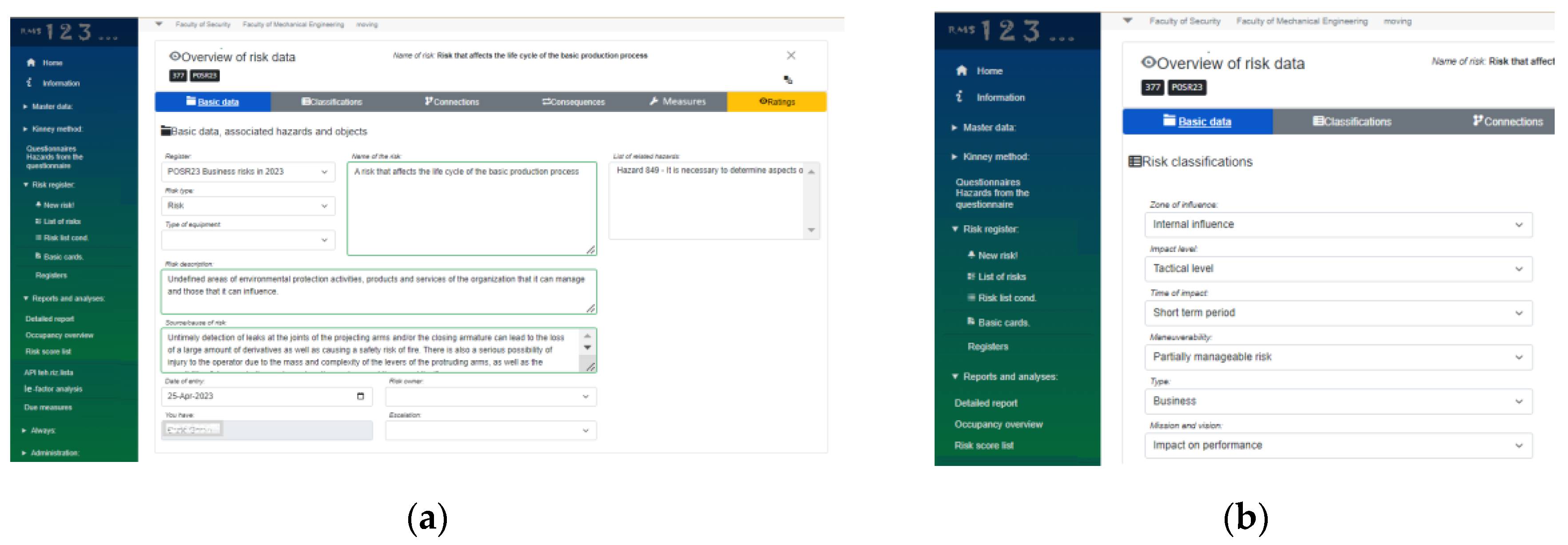
Risks Register
- New Risk
- List of Risks
- Risk cards
- Registers
- Risk Reports and Analysis
-
Detailed report
- Occupancy overviews
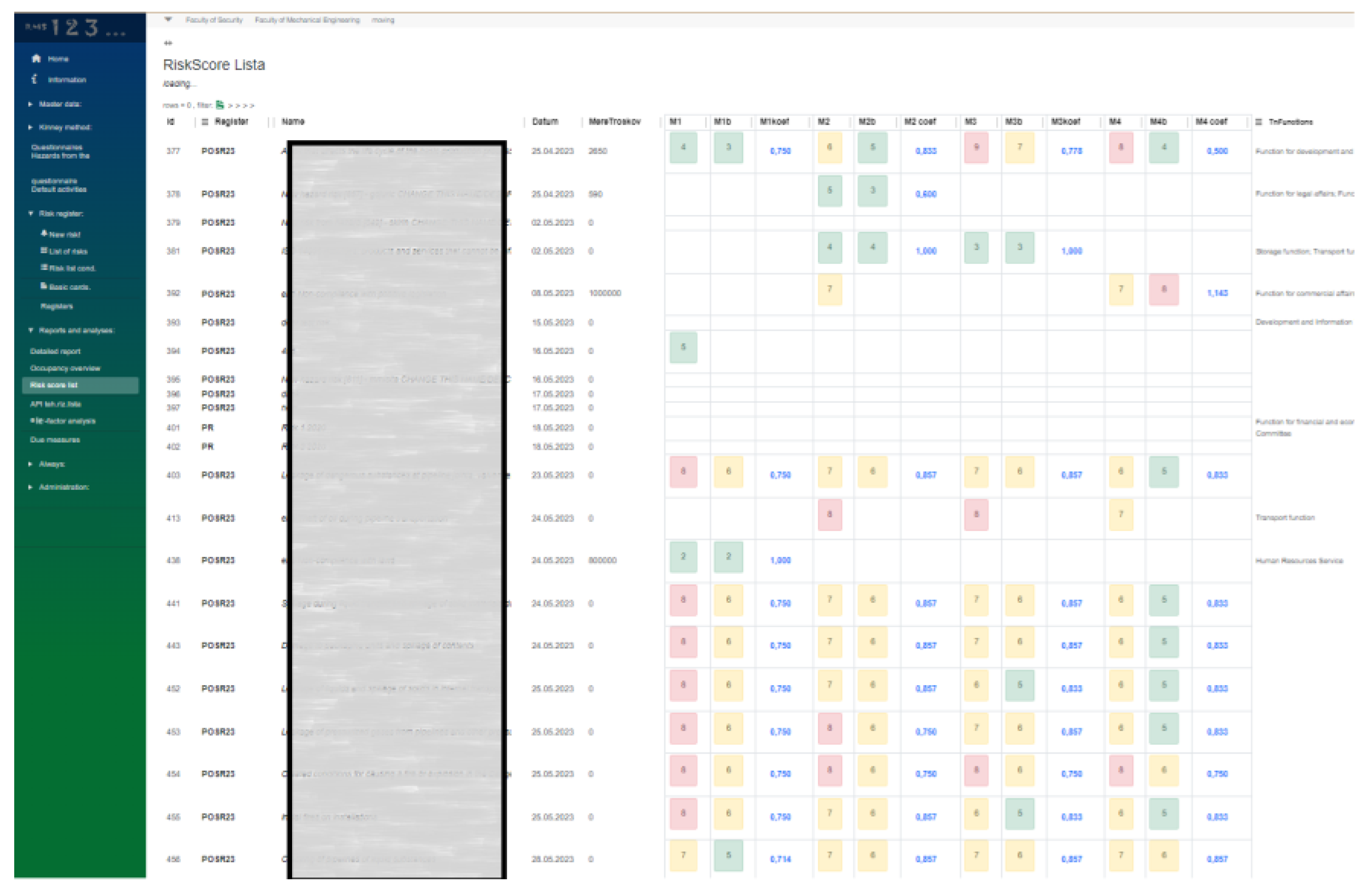
- Risk Score list (risks structured from largest to smallest (or by other criteria))
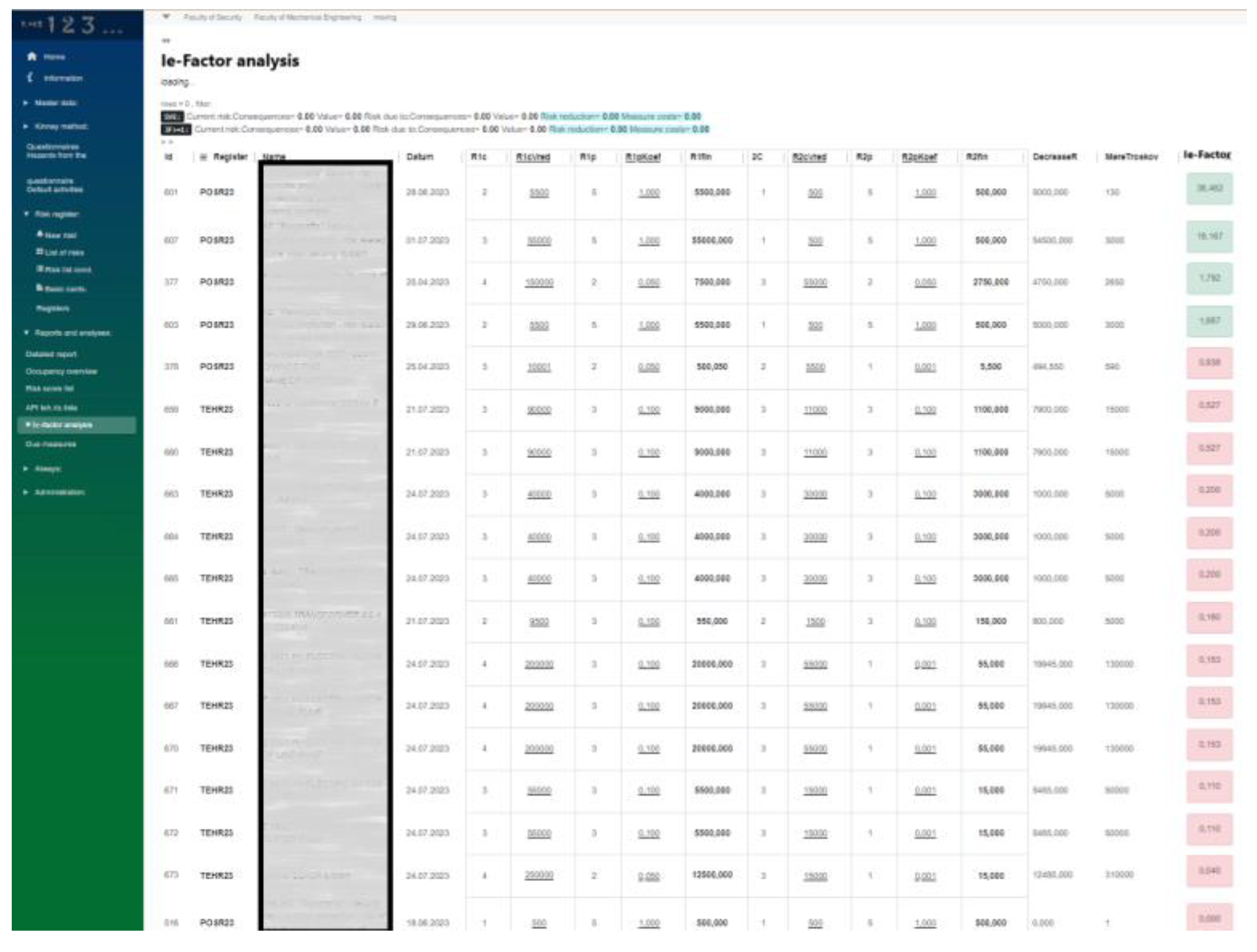
- Ie-factor (Investment effectiveness) analysis
- Administration
- Logout
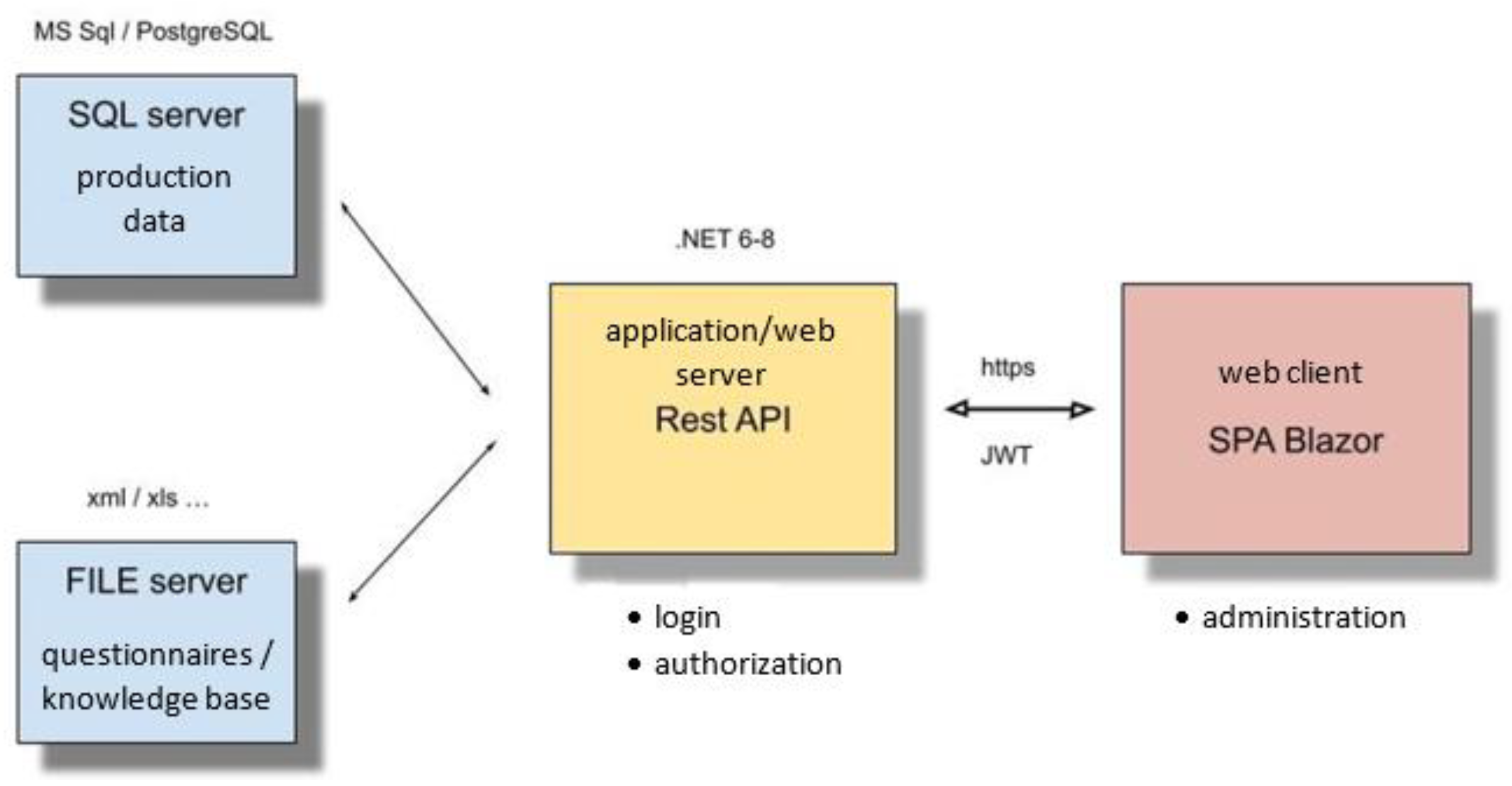
3.1. RMS Architecture
- the system support the parallel simultaneous cooperative work of many users with the same and simultaneous parallel sessions with independent and shared data warehouses,
- the system support execution on virtual machines,
- the system is not limited by the number of entities and the amount of data processed other than the hardware resources involved, and the limitations of the RDBMS used
- Client layer – any web-enabled devices, single page application (Blazor) - Web application with interactive user interface,
- Business layer - server, .NET 8, Rest API logic services,
- Data layer - server, MS SQL server / PostgreSql server, Windows / Linux,
- Questionnaire layer/knowledge base – file server, Windows / Linux,
3.2. Knowledge Database
- Safety and Health at Work,
- Business risks,
- COSO framework [26],
- Investments,
- Security risks,
- Managing environmental responsibilities according to the ISO 14000 standard
- Workplace (safety) risks,
- Information security management system according to the ISO 27000 standard,
- Food safety management system according to the ISO 22000 standard,
- Occupational safety and health management system according to the ISO 45001 standard,
- SEVESO standard and others.
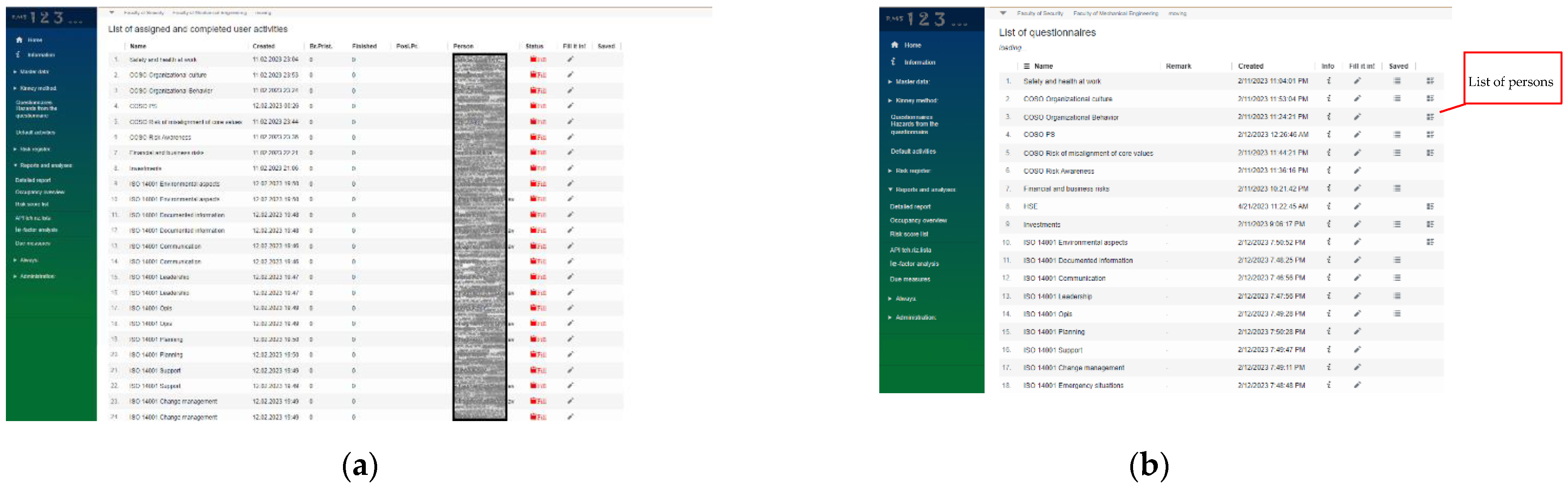
3.3. Project Management
- linking the respondent’s ID to the appropriate questionnaire, so that the user could have an overview of unfinished tasks when logging in to the RMS software
- more than one users need to fill out the same questionnaire (for example, in the specific example we had 4 people in charge of fire protection), which indicates that it is necessary to prevent duplication of hazards in the hazard database, but also to save all respondents’ answers.
3.4. COSO Framework
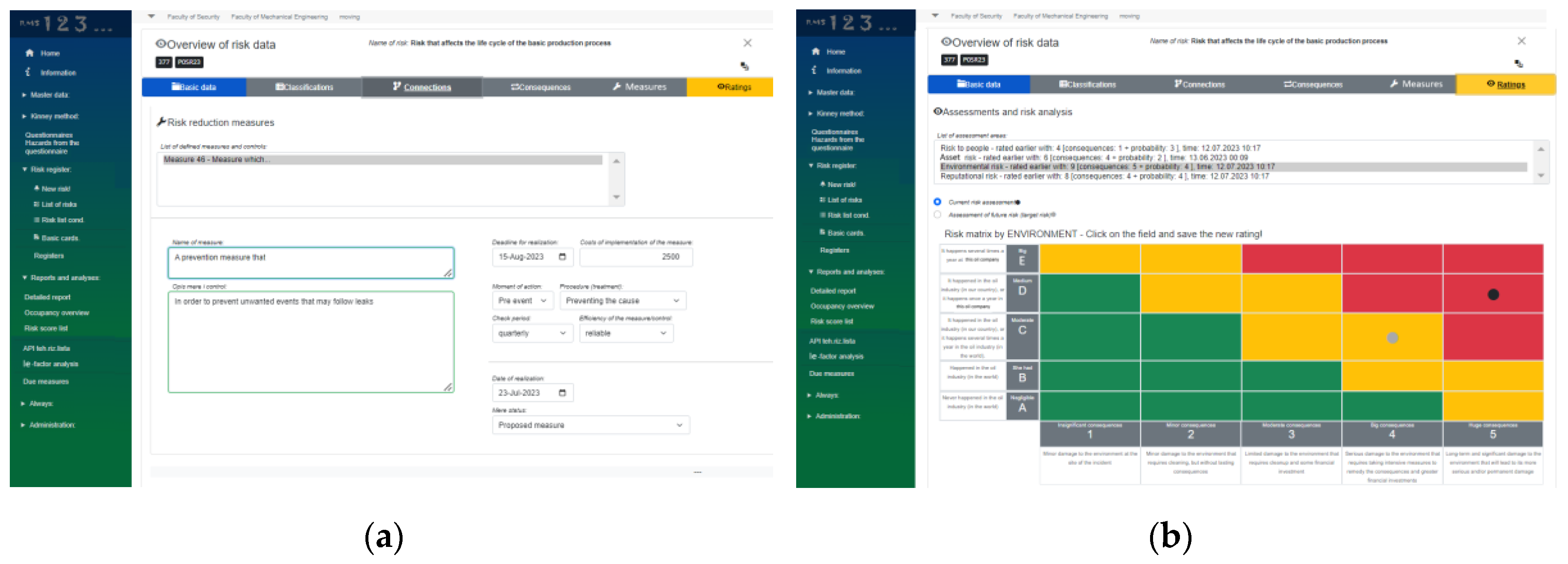
3.5. Risk Assessment
3.6. Suppoted Methodologies
3.7. Reporting
- Ie-factor>1 - these results are colored green (in Figure 14), i.e., they indicate that the difference between the future value of the risk and the current value of the risk divided by the total value of the recommended measures is positive and that it is profitable to invest in risk reduction activities
- Ie-factor<1 - these results are colored red (in Figure 14), and they indicate that the recommended measures are greater than the difference between the future risk value and the current risk value, and that it is not profitable to invest in these mitigating activities.
4. Conclusions
Author Contributions
Funding
Data Availability Statement
Institutional Review Board Statement
Informed Consent Statement
Acknowledgments
Conflicts of Interest
References
- Addo-Tenkorang, R. Helo P. (2011). Enterprise Resource Planning (ERP): A Review Literature Report, Proceedings of the World Congress on Engineering and Computer Science 2011 Vol II WCECS 2011, October 19-21, 2011, San Francisco, USA.
- Giambona, E.G. John R., Harvey, C.R., Bodnar, G.M. (2018). The Theory and Practice of Corporate Risk Management: Evidence from the Field, Financial Management, pages 783 – 83.
- Merna, T. , Faisal, F., Al-Thani (2015). Corporate Risk Management An Organisational Perspectiv, John Wiley & Sons Ltd.
- Yun, J. The effect of enterprise risk management on corporate risk management. Finance Research Letters 2023, 55, 103950. [Google Scholar] [CrossRef]
- Mahmood, A. , Lloyd, M. ERP System Implementation in Large Enterprises - A Systematic Literature Review. Journal of Enterprise Information Management 2017, 30. [Google Scholar] [CrossRef]
- Malik, S.A. Holt, B., Freeman, J. (2013). Enterprise Risk Management (ERM): A New Way of Looking at Risk Management at an Organisational Level, Conference Paper, Conference: EUROXXVI, Rome, Italy.
- Francisku, A.A. , Ridwan, H., Kevin, B.S. The State-of-The-Art of Enterprise Risk Management Maturity Models: A Review. Annals of R.S.C.B. 2021, 25, 4005–4014. [Google Scholar]
- Mahmood, F. , Zahid, A.H. (2019). ERP issues and challenges: a research synthesis, Kybernetes, Emerald Publishing Limited 0368-492X. [CrossRef]
- Fraser, J. , Simkins, B. (2016). The challenges of and solutions for implementing enterprise risk management, Business Horizons BUSHOR-1317; No. of Pages 10. [CrossRef]
- Abrams, C. von Känel, J., Müller, S., Pfitzmann, B., Ruschka-Taylor, S. (2006). Optimized Enterprise Risk Management, Computer Science, RZ 3657 (# 99677), 24 pages.
- Stefanou, C.J. A framework for the ex-ante evaluation of ERP software. European Journal of Information Systems 2001, 10, 204–215. [Google Scholar] [CrossRef]
- Valashani, M.A. , Abukari, A.M. ERP Systems Architecture for The Modern Age: A Review of the State of the Art Technologies. Journal of Applied Intelligent Systems & Information Sciences 2020, 1, 70–90. Available online: www.journal.research.fanap.com. [CrossRef]
- Söderholm, P. Karim, R. (2010). An Enterprise Risk Management framework for evaluation of eMaintenance, The 1st international workshop and congress on eMaintenance 22-24 June, Luleå, Sweden, ISBN 978-91-7439-120-6.
- Mohamed, A.A.E. , Eman, N., Mervat, H.G. Benefits and challenges of cloud ERP systems e A systematic literature review. Future Computing and Informatics Journal 2016, 1, 1–9. Available online: http://www.journals.elsevier.com/future-computing-and-informatics-journal/.
- Mohamed, S.S. , Abdulkader, A. A new comprehensive framework for enterprise information security risk management. Applied Computing and Informatics 2011, 9, 107–118. [Google Scholar]
- Louis, A.C. What’s Wrong with Risk Matrices? Risk Analysis 2008, 28. [Google Scholar]
- Arena, M. , Arnaboldi, M., Azzone G. Is enterprise risk management real? Journal of Risk Research 2011, 14, 779–797. [Google Scholar] [CrossRef]
- Bromiley, P. , McShane, M., Nair, A., Rustambekov, E. Enterprise Risk Management: Review, Critique, and Research Directions. Long Range Planning 2015, 48, 265–276. [Google Scholar] [CrossRef]
- Essex, D.E. The black art of risk. PM Network 2005, 19, 88–92. [Google Scholar]
- Patterson, T. The Use of Information Technology in Risk Management, September 2015, White Paper, aicpa.org/FRC.
- Pandey S., K. Mustafa K. (2012). A Comparative Study of Risk Assessment Methodologies for Information Systems, Buletin Teknik Elektro dan Informatika (Bulletin of Electrical Engineering and Informatics) Vol.1, No.2, June 2012, pp. 111~122, ISSN: 2089-3191.
- Bromiley, P. McShane, M., Nair, A., Rustambekov, E (201.4). Enterprise Risk Management: Review, Critique, and Research Directions, Long Range Planning xxx, 1-12.
- Mitterbaur, P. , Pesendorfer, J., Schmidinger, E. Opportunities and risks of IT solutions for ERM” ACRN Oxford. Journal of Finance and Risk Perspectives 2016, 5, 15–29. [Google Scholar]
- Dikmen, I. , Birgonul, M.T. and Arikan, A.E. A critical review of risk management support tools. In: Khosrowshahi, F. (Ed.), 20th Annual ARCOM Conference, 1-3 Heriot WattUniversity. Association of Researchers in Construction Management 2004, 2, 1145–54. [Google Scholar]
- Khan, M.A. , Khan, S., Sadiq, M. Systematic Review of Software Risk Assessment and Estimation Models. International Journal of Engineering and Advanced Technology (IJEAT) 2012, 1, 298–305, ISSN: 2249-8958 (Online). [Google Scholar]
- Stanojevic, P. , Misita, M., Djuric, G. (2023). Software System for Risk Management Based on Artificial Intelligence, Second memorial scientific conference ‘’Predrag Maric’’ (on Serbian), pp. 144-154. ISBN 987-86-80144-63-4.
- Committee of Sponsoring Organizations of the Treadway Commission (COSO) (2004). Enterprise Risk Management - Integrated Framework, Pricewaterhouse Coopers LLP.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



