Submitted:
11 May 2024
Posted:
13 May 2024
You are already at the latest version
Abstract
Keywords:
1. Introduction
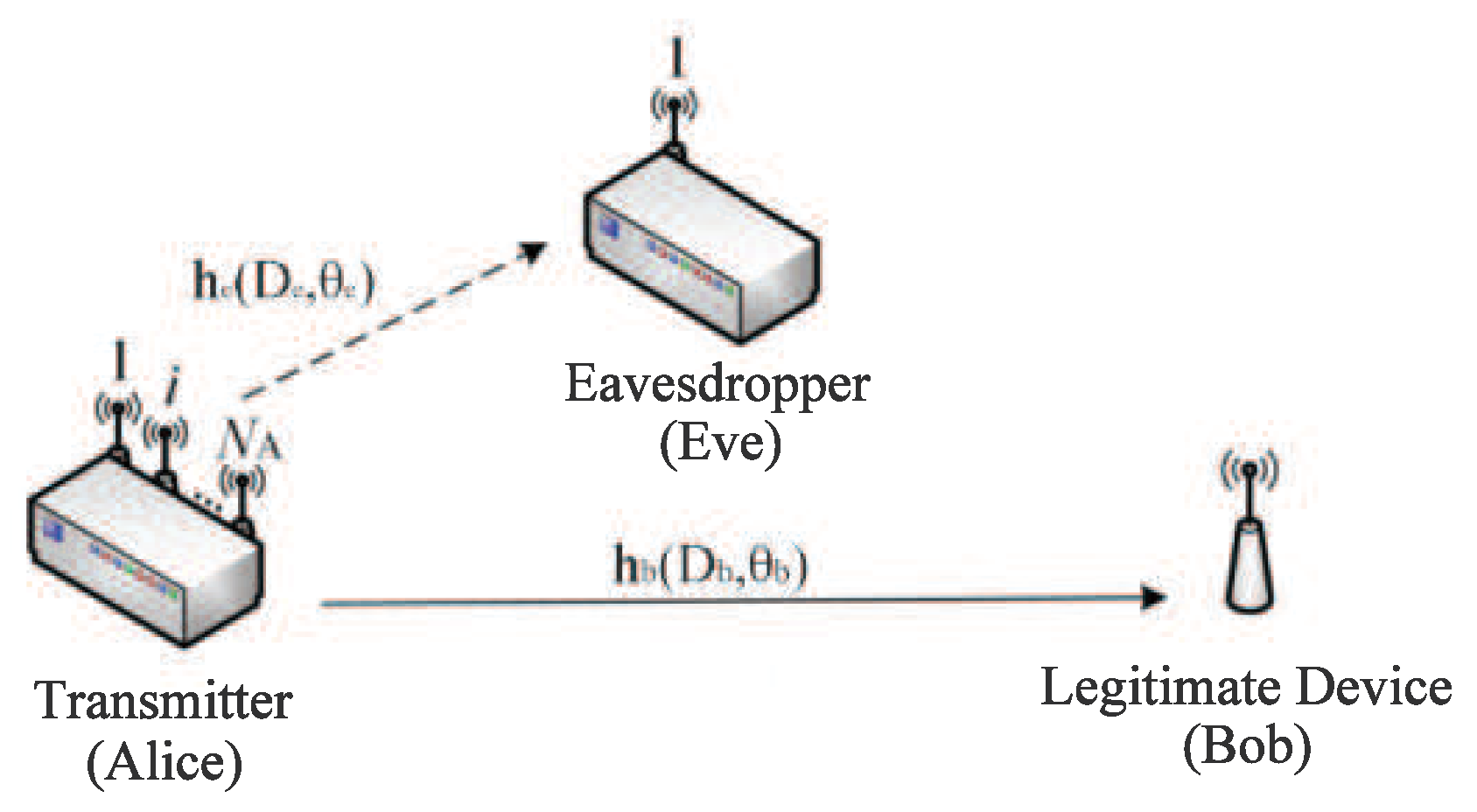
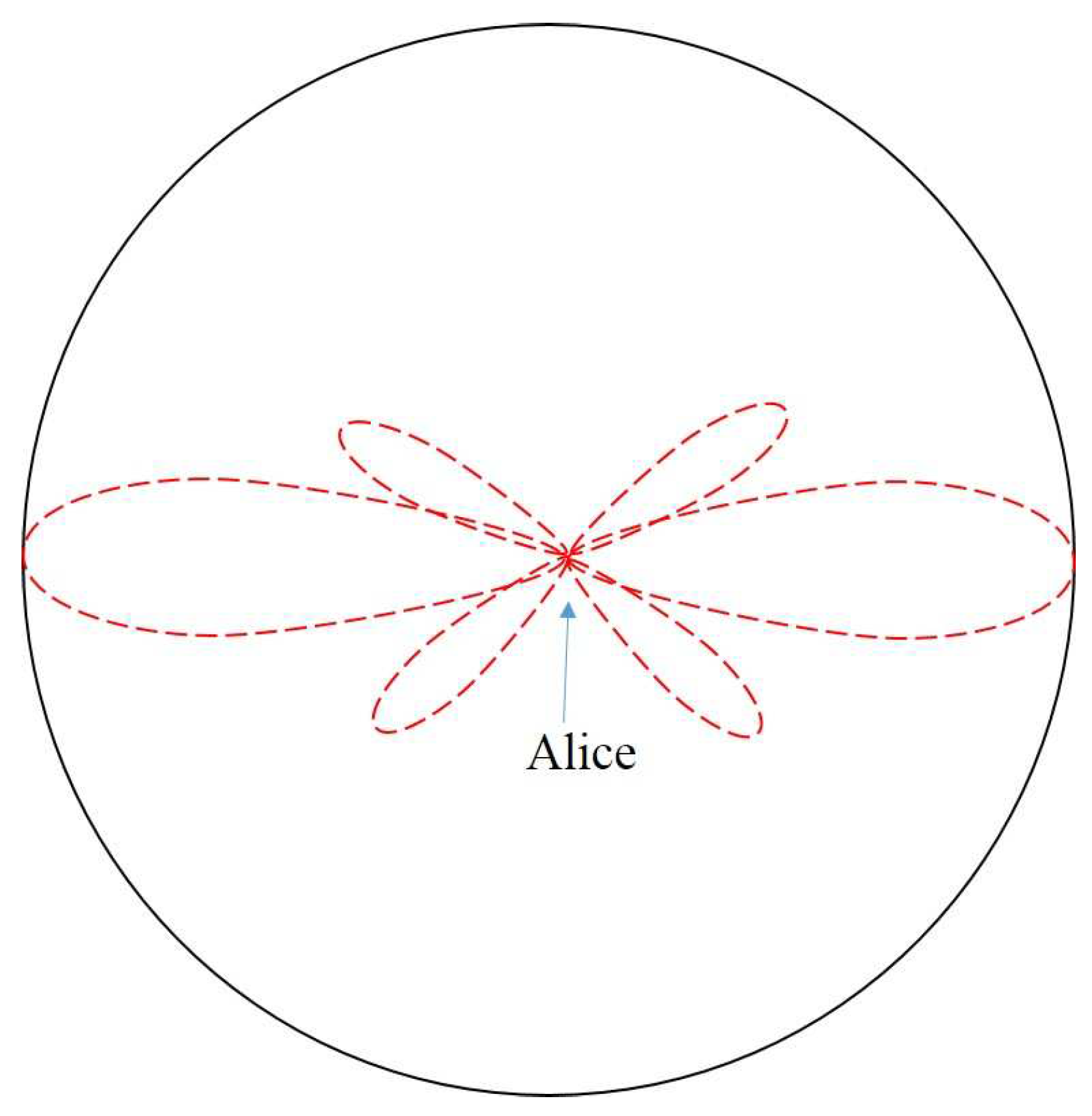
2. System Model
3. Spatial Secrecy Outage Probability
4. Simulation Results
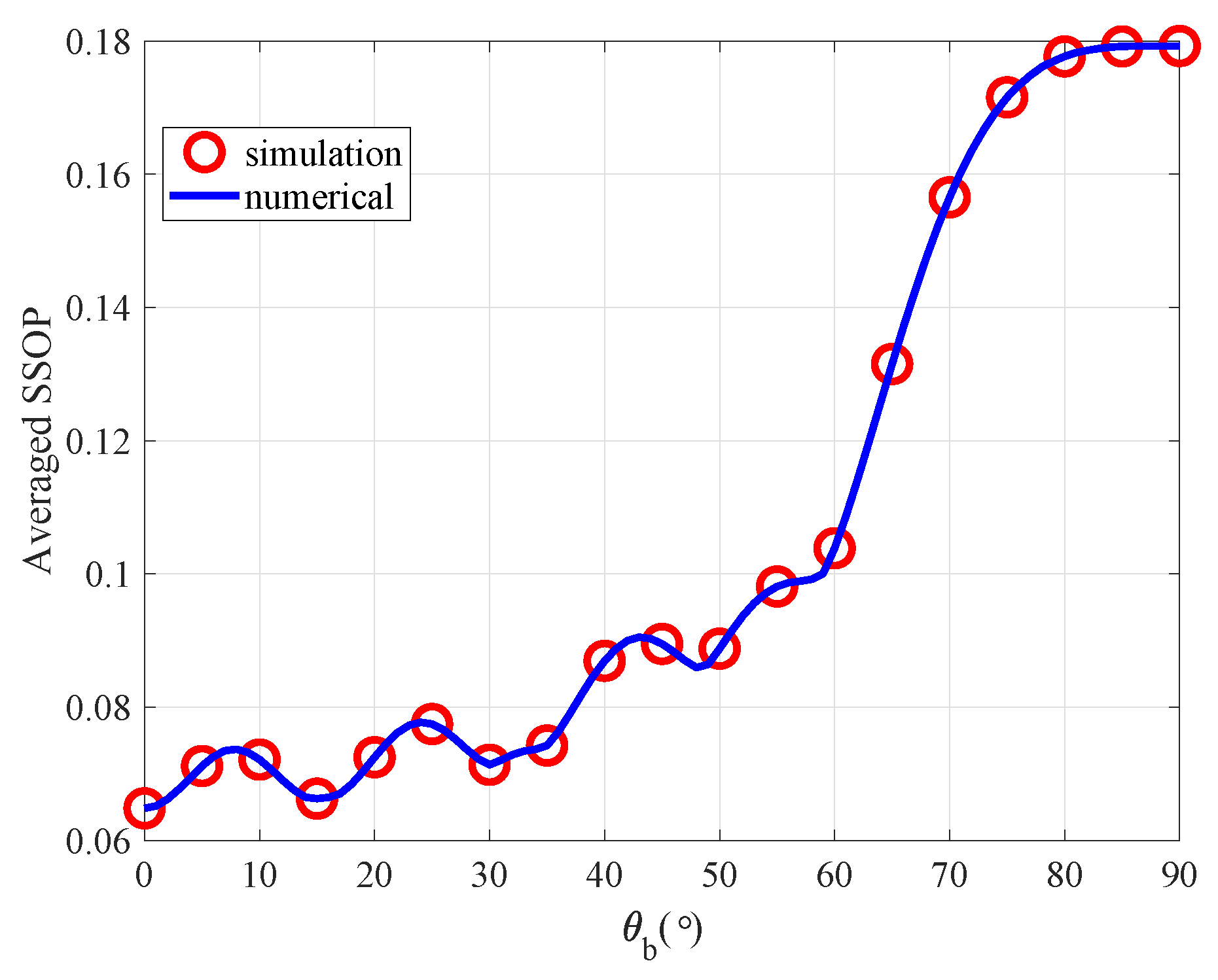
4.1. The Impact for the Averaged SSOP versus Bob’s Different Value of
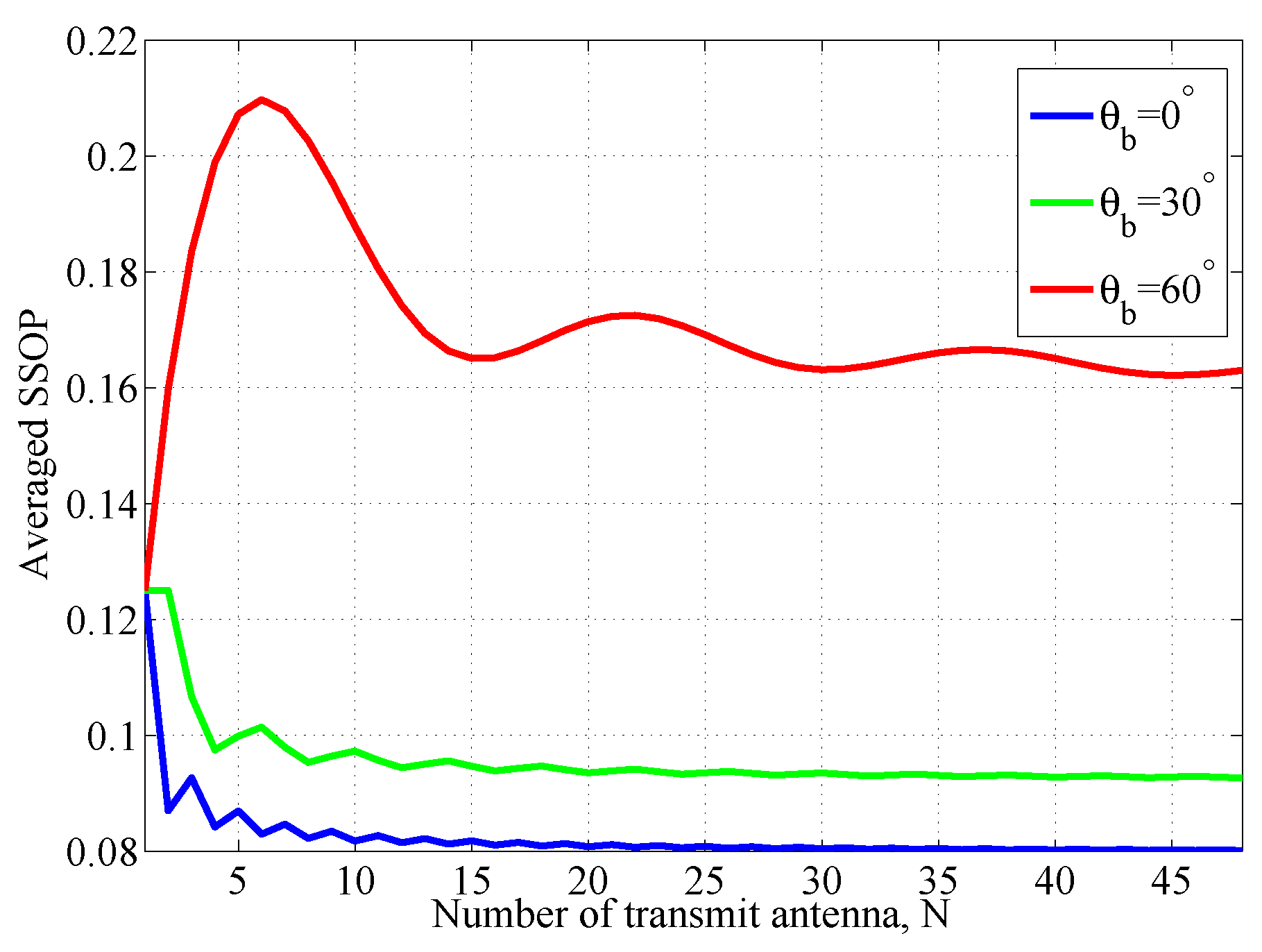
4.2. The Averaged SSOP versus Different Value of N
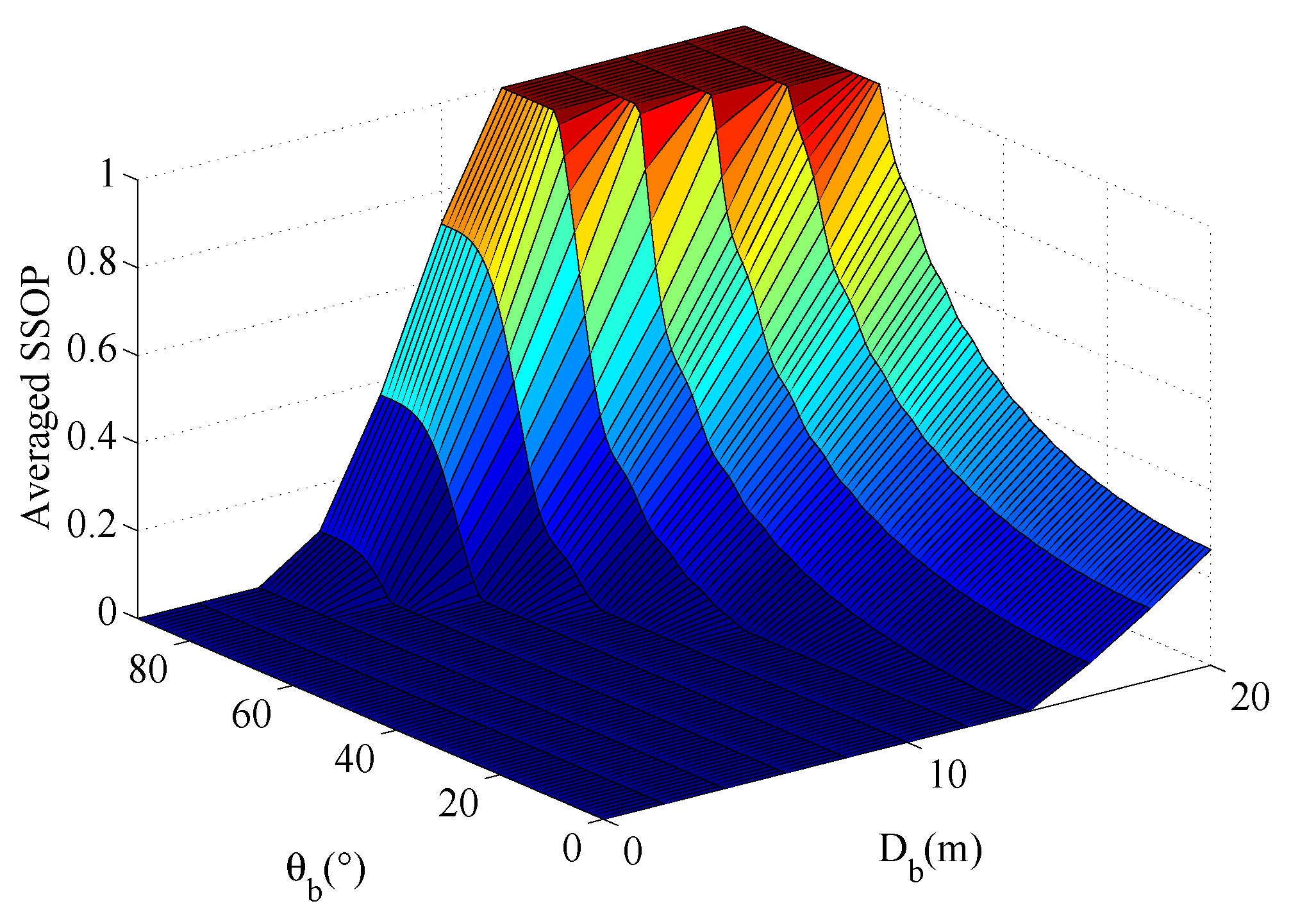
4.3. The Averaged SSOP versus Different Value of and
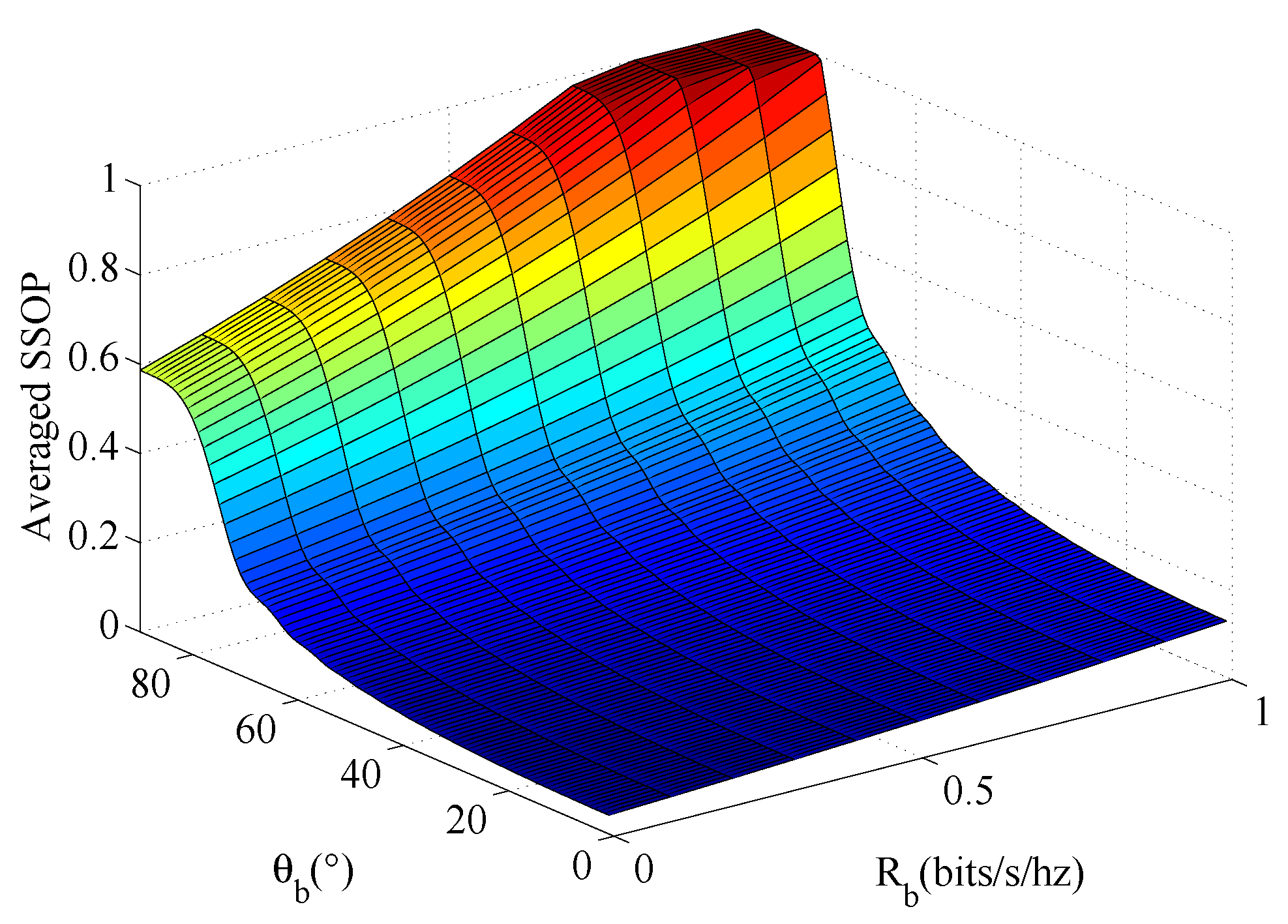
4.4. The Averaged SSOP versus Different Value of and
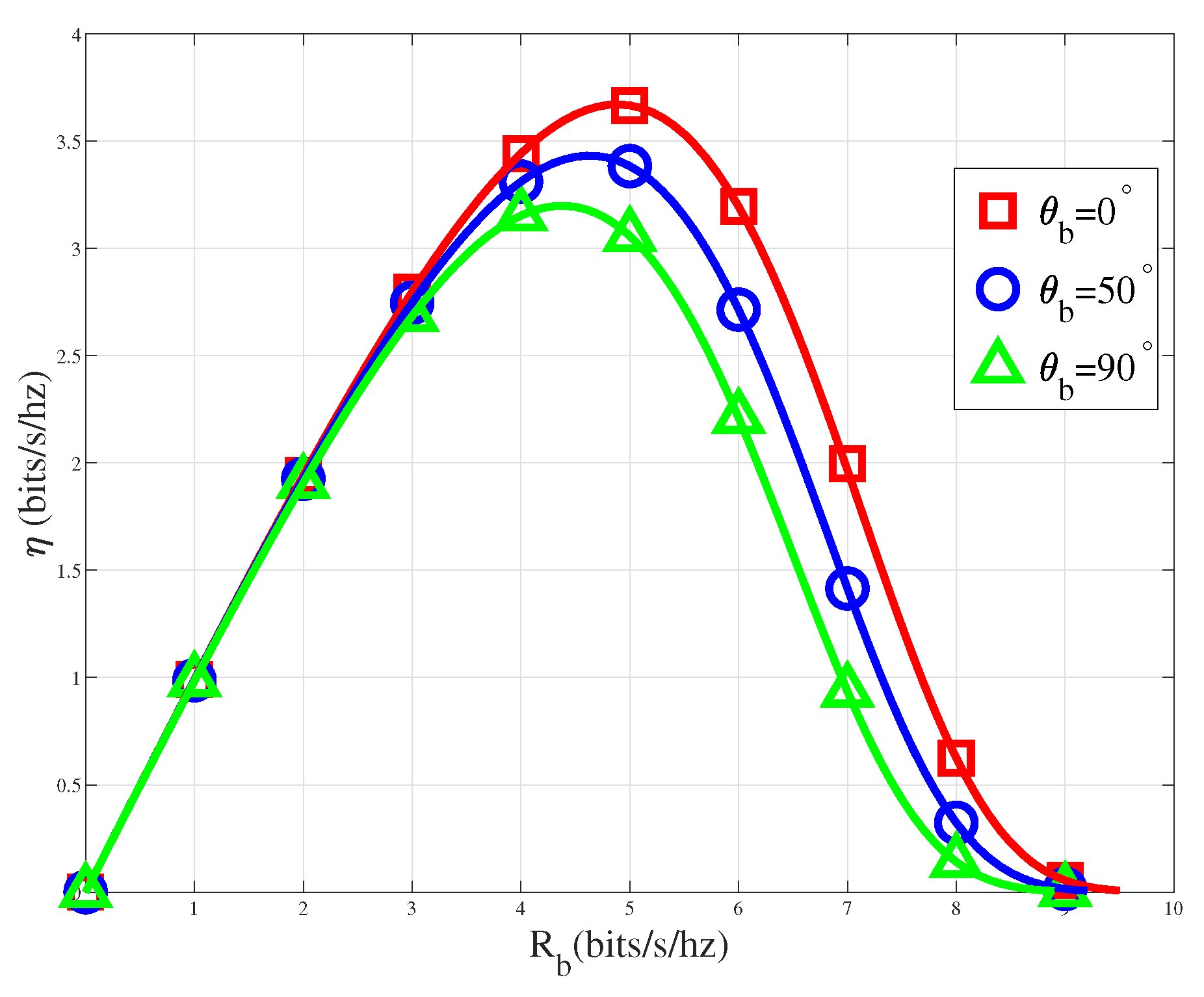
4.5. The Relationship between System Throughput versus the Legitimate Channel Transmission Rate
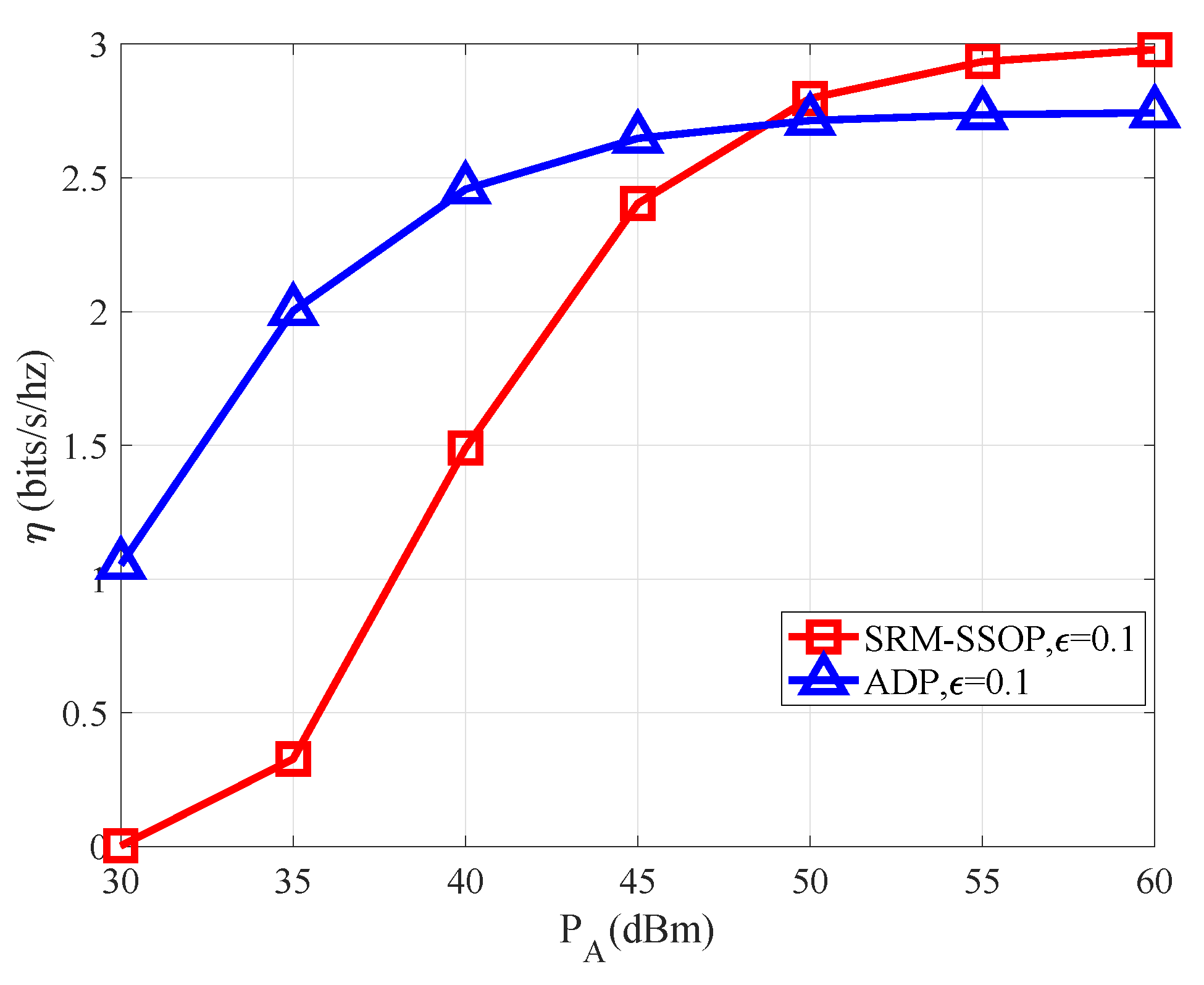
4.6. The Relationship between System Throughput versus Different Transmission Power Levels
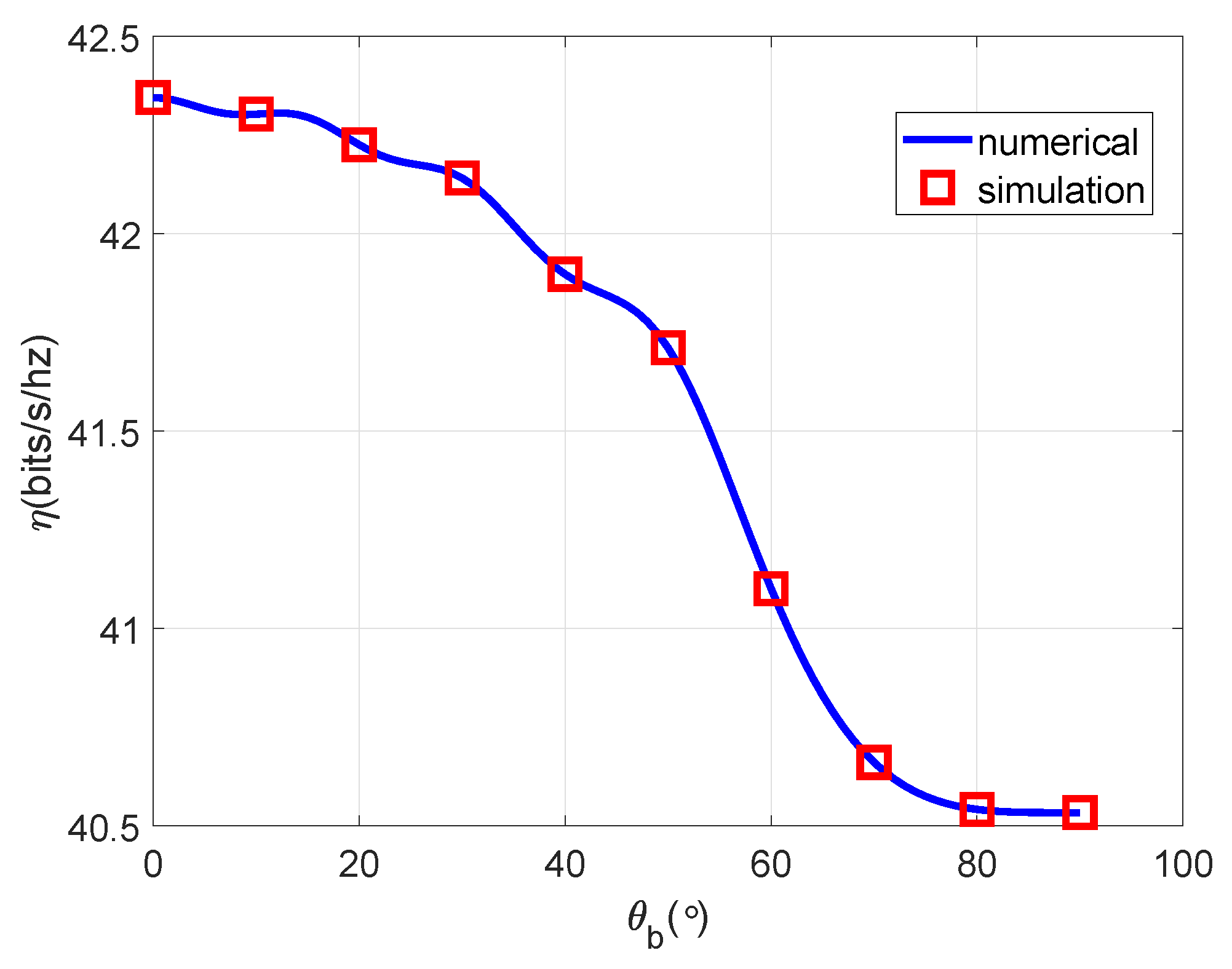
4.7. The Relationship between System Throughput versus Bob’s Azimuth Angle
5. Conclusions
Funding
References
- Liu, Y.; Chi, C.; Zhang, Y.; Tang, T. Identification and Resolution for Industrial Internet: Architecture and Key Technology. IEEE Internet of Things Journal 2022, 9, 16780–16794. [Google Scholar] [CrossRef]
- Serror, M.; Hack, S.; Henze, M.; Schuba, M.; Wehrle, K. Challenges and Opportunities in Securing the Industrial Internet of Things. IEEE Transactions on Industrial Informatics 2021, 17, 2985–2996. [Google Scholar] [CrossRef]
- Mcginthy, J.M.; Michaels, A.J. Secure Industrial Internet of Things Critical Infrastructure Node Design. IEEE Internet of Things Journal 2019, 6, 8021–8037. [Google Scholar] [CrossRef]
- Yao, P.; Yan, B.; Yang, T.; Wang, Y.; Yang, Q.; Wang, W. Security-Enhanced Operational Architecture for Decentralized Industrial Internet of Things: A Blockchain-Based Approach. IEEE Internet of Things Journal 2024, 11, 11073–11086. [Google Scholar] [CrossRef]
- Ud Din, I.; Bano, A.; Awan, K.A.; Almogren, A.; Altameem, A.; Guizani, M. LightTrust: Lightweight Trust Management for Edge Devices in Industrial Internet of Things. IEEE Internet of Things Journal 2023, 10, 2776–2783. [Google Scholar] [CrossRef]
- Yousuf, T.; Mahmoud, R.; Aloul, F.; Zualkernan, I. Internet of Things (IoT) Security: Current Status, Challenges and Countermeasures 2015.
- Al-Fuqaha, A.; Guizani, M.; Mohammadi, M.; Aledhari, M.; Ayyash, M. Internet of Things: A Survey on Enabling Technologies, Protocols, and Applications. IEEE Communications Surveys and Tutorials 2015, 17, 2347–2376. [Google Scholar] [CrossRef]
- Kokoris-Kogias, E.; Voutyras, O.; Varvarigou, T. TRM-SIoT: A scalable hybrid trust and reputation model for the social Internet of Things. IEEE International Conference on Emerging Technologies and Factory Automation, 2016.
- Lin, J.; Yang, X.; Yu, W.; Fu, X. Towards Effective En-Route Filtering against Injected False Data in Wireless Sensor Networks. Global Telecommunications Conference, 2011.
- Suo, H.; Wan, J.; Zou, C.; Liu, J. Security in the Internet of Things: A Review. IEEE 2012. [Google Scholar]
- Mukherjee, A. Physical-Layer Security in the Internet of Things: Sensing and Communication Confidentiality Under Resource Constraints. Proceedings of the IEEE 2015, 103, 1747–1761. [Google Scholar] [CrossRef]
- Mcginthy, J.M.; Michaels, A.J. Secure Industrial Internet of Things Critical Infrastructure Node Design. IEEE Internet of Things Journal 2019, 6, 8021–8037. [Google Scholar] [CrossRef]
- Ji, Z.; Yeoh, P.L.; Chen, G.; Zhang, J.; Zhang, Y.; He, Z.; Yin, H.; Li, Y. Physical-Layer-Based Secure Communications for Static and Low-Latency Industrial Internet of Things. IEEE Internet of Things Journal 2022, 9, 18392–18405. [Google Scholar] [CrossRef]
- Lipps, C.; Herbst, J.; Klingel, S.; Franke, L.; Wolff, A.; Rüb, M.; Reddy, R.; Rahm, M.; Schotten, H.D. Connectivity in the era of the (I) IoT: about security, features and limiting factors of reconfigurable intelligent surfaces. Discover Internet of Things 2023, 3, 16. [Google Scholar] [CrossRef]
- Yu, S.; Wu, F.; Chen, B.; Cao, R.; Yang, Z.; Li, K. A parallel game model-based intrusion response system for cross-layer security in industrial internet of things. Concurrency and Computation: Practice and Experience 2023, 35, e7826. [Google Scholar] [CrossRef]
- Chen, H.; Hu, M.; Yan, H.; Yu, P. Research on industrial internet of things security architecture and protection strategy. 2019 International conference on virtual reality and intelligent systems (ICVRIS). IEEE, 2019, pp. 365–368.
- Mcginthy, J.M.; Michaels, A.J. Secure industrial Internet of Things critical infrastructure node design. IEEE Internet of Things Journal 2019, 6, 8021–8037. [Google Scholar] [CrossRef]
- Islam, S.N.; Baig, Z.; Zeadally, S. Physical layer security for the smart grid: Vulnerabilities, threats, and countermeasures. IEEE Transactions on Industrial Informatics 2019, 15, 6522–6530. [Google Scholar] [CrossRef]
- Xu, L. Secure transmission strategy of network communication layer relay based on satellite transmission. 2020 2nd International Conference on Information Technology and Computer Application (ITCA). IEEE, 2020, pp. 268–271.
- Nguyen, H.N.; Nguyen, N.L.; Nguyen, N.T.; Le, A.T.; Ha, N.D.X.; Do, D.T.; Voznak, M. Reliable and secure transmission in multiple antennas hybrid satellite-terrestrial cognitive networks relying on NOMA. IEEE Access 2020, 8, 215044–215056. [Google Scholar] [CrossRef]
- Liu, M.; Liu, Z.; Lu, W.; Chen, Y.; Gao, X.; Zhao, N. Distributed few-shot learning for intelligent recognition of communication jamming. IEEE Journal of Selected Topics in Signal Processing 2021, 16, 395–405. [Google Scholar] [CrossRef]
- Liu, M.; Wang, J.; Zhao, N.; Chen, Y.; Song, H.; Yu, F.R. Radio frequency fingerprint collaborative intelligent identification using incremental learning. IEEE Transactions on Network Science and Engineering 2021, 9, 3222–3233. [Google Scholar] [CrossRef]
- Liu, M.; Liu, C.; Li, M.; Chen, Y.; Zheng, S.; Zhao, N. Intelligent passive detection of aerial target in space-air-ground integrated networks. China Communications 2022, 19, 52–63. [Google Scholar] [CrossRef]
- Li, B.; Zhou, Z.; Zou, W.; Sun, X.; Du, G. On the efficient beam-forming training for 60GHz wireless personal area networks. IEEE Transactions on Wireless Communications 2013, 12, 504–515. [Google Scholar] [CrossRef]
- Bashar, B.S.; Rhazali, Z.; Elwi, T.A.; Misran, H.; Ismail, M.M.; Mahdi, M.; Alanssari, A.I. Antenna Beam forming Technology Based Enhanced Metamaterial Superstrates. 2022 IEEE 3rd KhPI Week on Advanced Technology (KhPIWeek). IEEE, 2022, pp. 1–5.
- Xiong, Q.; Gong, Y.; Liang, Y.C.; Li, K.H. Achieving secrecy of MISO fading wiretap channels via jamming and precoding with imperfect channel state information. IEEE Wireless Communications Letters 2014, 3, 357–360. [Google Scholar] [CrossRef]
- Barb, G.; Otesteanu, M. Digital GoB-based Beamforming for 5G communication systems. 2020 international symposium on antennas and propagation (ISAP). IEEE, 2021, pp. 469–470.
- Talak, R.; Karaman, S.; Modiano, E. Improving age of information in wireless networks with perfect channel state information. IEEE/ACM Transactions on Networking 2020, 28, 1765–1778. [Google Scholar] [CrossRef]
- Shi, W.; Pang, S.; Zhang, W. Linear shrinkage receiver for slow fading channels under imperfect channel state information. 2022 IEEE Information Theory Workshop (ITW). IEEE, 2022, pp. 338–343.
- Xie, R.; Tang, Q.; Liang, C.; Yu, F.R.; Huang, T. Dynamic computation offloading in IoT fog systems with imperfect channel-state information: A POMDP approach. IEEE Internet of Things Journal 2020, 8, 345–356. [Google Scholar] [CrossRef]
- Yilmaz, B.B.; Prvulovic, M.; Zajić, A. Electromagnetic side channel information leakage created by execution of series of instructions in a computer processor. IEEE Transactions on Information Forensics and Security 2019, 15, 776–789. [Google Scholar] [CrossRef]
- Niu, H.; Xiao, Y.; Lei, X.; Wang, G.; Xiao, M.; Mumtaz, S. When the CSI from Alice to Bob is Unavailable: What Can Eve Do to Eliminate the Artificial Noise? 2022 IEEE 96th Vehicular Technology Conference (VTC2022-Fall). IEEE, 2022, pp. 1–5.
- Xia, G.; Lin, Y.; Liu, T.; Shu, F.; Hanzo, L. Transmit antenna selection and beamformer design for secure spatial modulation with rough CSI of Eve. IEEE Transactions on Wireless Communications 2020, 19, 4643–4656. [Google Scholar] [CrossRef]
- Chen, Y.; Zhu, G.; Xu, J. Over-the-air computation with imperfect channel state information. 2022 IEEE 23rd International Workshop on Signal Processing Advances in Wireless Communication (SPAWC). IEEE, 2022, pp. 1–5.
- Mukherjee, A.; Fakoorian, S.A.A.; Huang, J.; Swindlehurst, A.L. Principles of Physical Layer Security in Multiuser Wireless Networks: A Survey. IEEE Communications Surveys & Tutorials 2014, 16, 1550–1573. [Google Scholar]
- Wang, J.; Lee, J.; Wang, F.; Quek, T. Jamming-Aided Secure Communication in Massive MIMO Rician Channels. IEEE Transactions on Wireless Communications 2015, 14, 6854–6868. [Google Scholar] [CrossRef]
- Sarma, S.; Shukla, S.; Kuri, J. Joint scheduling & jamming for data secrecy in wireless networks. International Symposium on Modeling & Optimization in Mobile, 2013.
- Zheng, T.X.; Wang, H.M.; Yin, Q. On Transmission Secrecy Outage of a Multi-Antenna System With Randomly Located Eavesdroppers. IEEE Communications Letters 2014, 18, 1299–1302. [Google Scholar] [CrossRef]
- Hao, L.; Wang, X.; Hou, W. Security enhancement in cooperative jamming using compromised secrecy region minimization. Information Theory, 2013.
- Yan, S.; Malaney, R.; Nevat, I.; Peters, G.W. Optimal Information-Theoretic Wireless Location Verification. Vehicular Technology IEEE Transactions on 2014, 63, 3410–3422. [Google Scholar] [CrossRef]
- Yan, S.; Malaney, R.; Nevat, I.; Peters, G.W. Signal strength based wireless location verification under spatially correlated shadowing. 2014 IEEE International Conference on Communications (ICC). IEEE, 2014, pp. 2617–2623.
- Yan, S.; Malaney, R. Line-of-sight based beamforming for security enhancements in wiretap channels. 2014 International Conference on IT Convergence and Security (ICITCS). IEEE, 2014, pp. 1–4.
- Li, Z.; Mu, P.; Li, Z.; Zhang, W.; Zhang, Y. An Adaptive Transmission Scheme for Slow Fading Wiretap Channel with Channel Estimation Errors. IEEE Globecom 2016, 2016. [Google Scholar]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).



