Submitted:
04 December 2023
Posted:
05 December 2023
You are already at the latest version
Abstract
Keywords:
1. Introduction
- What are the risks associated with cloud manufacturing in Industry 4.0?
- How can provenance blockchain be used to provide greater transparency and traceability in the cloud manufacturing process using AI-enabled predictive auditing?
- How can this system help in mitigating cloud manufacturing risks in Industry 4.0?
2. Literature Review
- (a)
- Eavesdropping attack: an attack mechanism in which, the communications from authorised devices to others like them are captured in between by eavesdropping devices (called listeners);
- (b)
- Masquerading attack by capturing packets of unsecured IIoTs: an attack mechanism in which an unauthorised cyber physical system captures packets from unsecured IIoTs and masquerades as an authorised controller to the cloud hosted manufacturing applications;
- (c)
- Distributed Denial of Service (DDoS): an attack mechanism in which, massive scale storms of packets are bombarded to the cyber physical systems through unprotected Internet connections compromised by the attackers thus overloading the computing systems, networking links, and cyber physical controllers;
- (d)
- Side channel attacks: these are penetration attacks through the side channels into the manufacturing network, which are less monitored or ignored by the monitoring systems;
- (e)
- Cross-side scripting attacks: these are Trojan scripts that can be mixed with the running scripts through SQL injection;
- (f)
- Automated code-based attacks (such as Bots): these are penetration attacks caused by pre-programmed automatic codes;
- (g)
- Exploit-based attacks: these are attacks orchestrated through open source programs created by hacking experts;
- (h)
- Identity thefts (of authorised IIoT devices): these are caused by eavesdropping attacks to capture authentication and authorisation details of IIoT devices;
- (i)
- Insider trading and proliferation: insiders engaged in malicious activities such as injecting Trojan codes in running programs or opening firewall ports for external attackers to launch their exploits;
- (j)
- Fake sensor data feeding and actuation attacks in control systems: these are well planned targeted attacks. For example, the attacker may send false signals of lowering valve pressure in a key pipeline thus causing the control system to gradually increase the pressure in the pipeline leading to an explosion;
- (a)
- Validating the identity of cyber physical system enabled with IIoT communications;
- (b)
- Tracking rapid deployments and Internet-enabling of millions of cyber physical systems;
- (c)
- Traceability of cyber physical systems added, modified, and removed; especially installed on mobile assets;
- (d)
- Validating fidelity of sensor data sent for influencing process events interpreted out of the sensory data and the decision-making algorithms running the actuation commands;
- (e)
- Establishing accountability and liability of individuals owning the cyber physical systems;
- (f)
- Inter-cloud assurances of cyber security;
- (g)
- Algorithmic transparency (accountability of performance and behaviours of algorithms deployed for controlling operations of cyber physical systems);
- (h)
- Cyber physical systems indulging into erroneous or malicious processing thus affecting the execution of smart contracts negatively;
3. Methodology
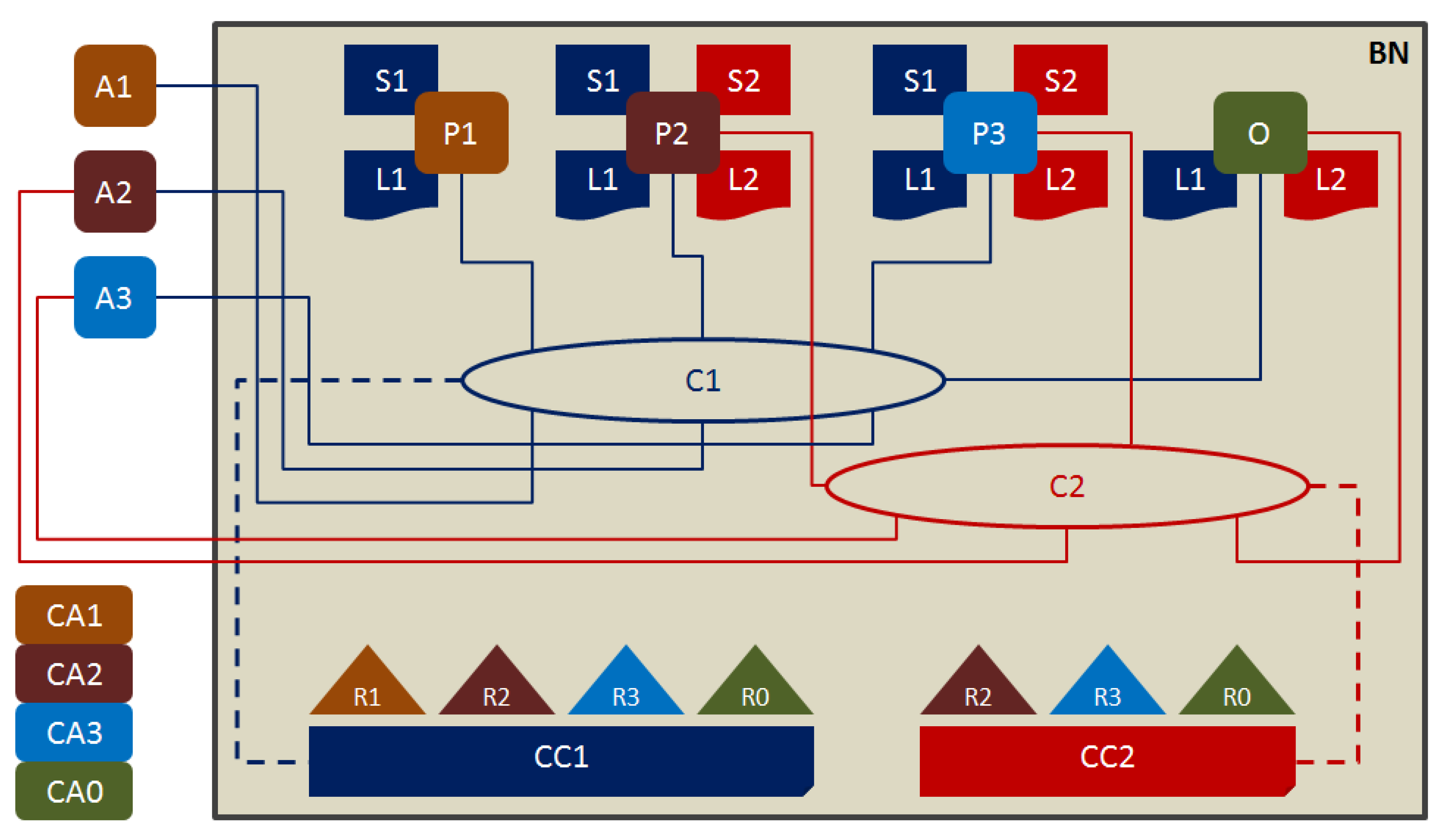
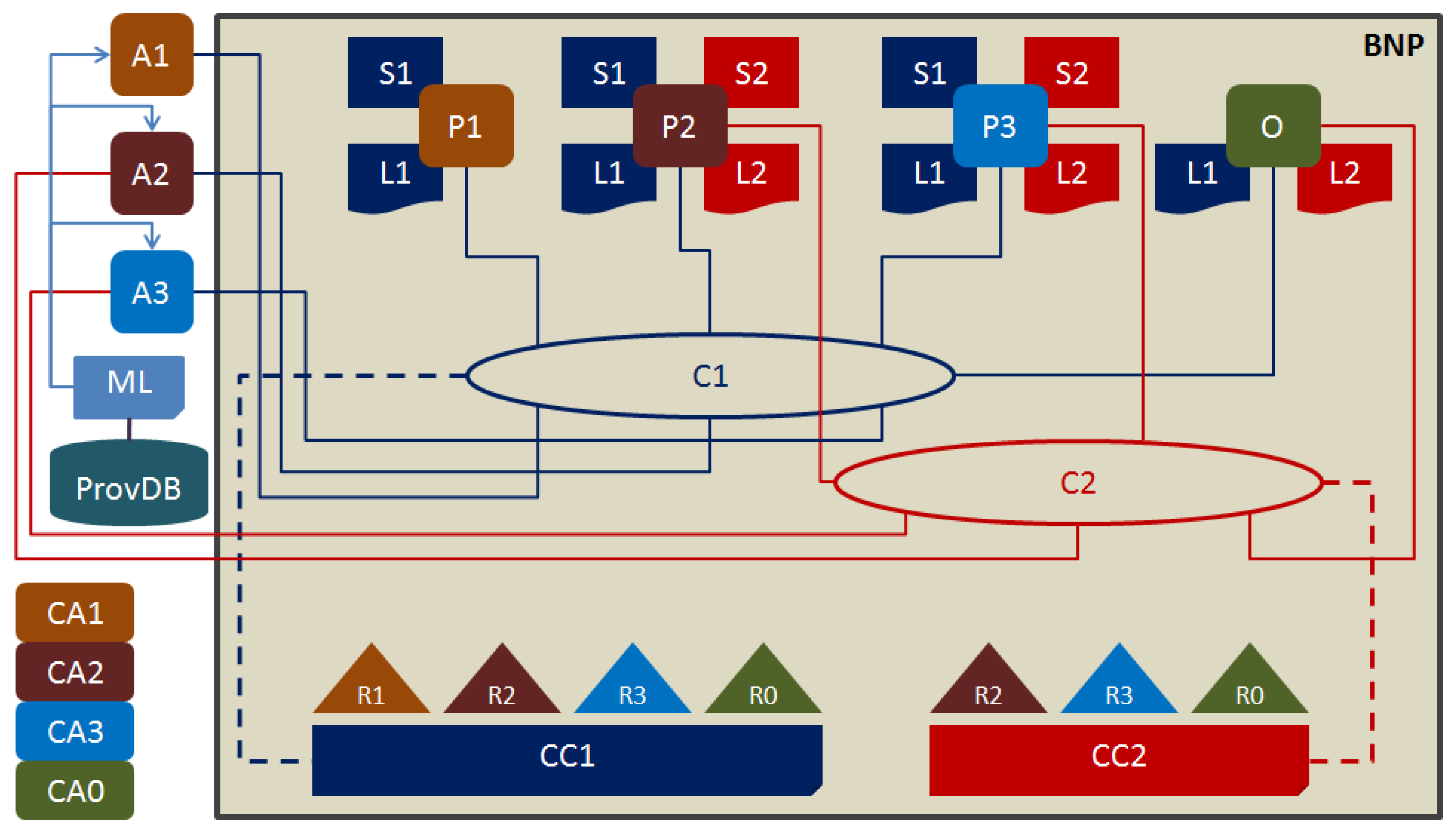
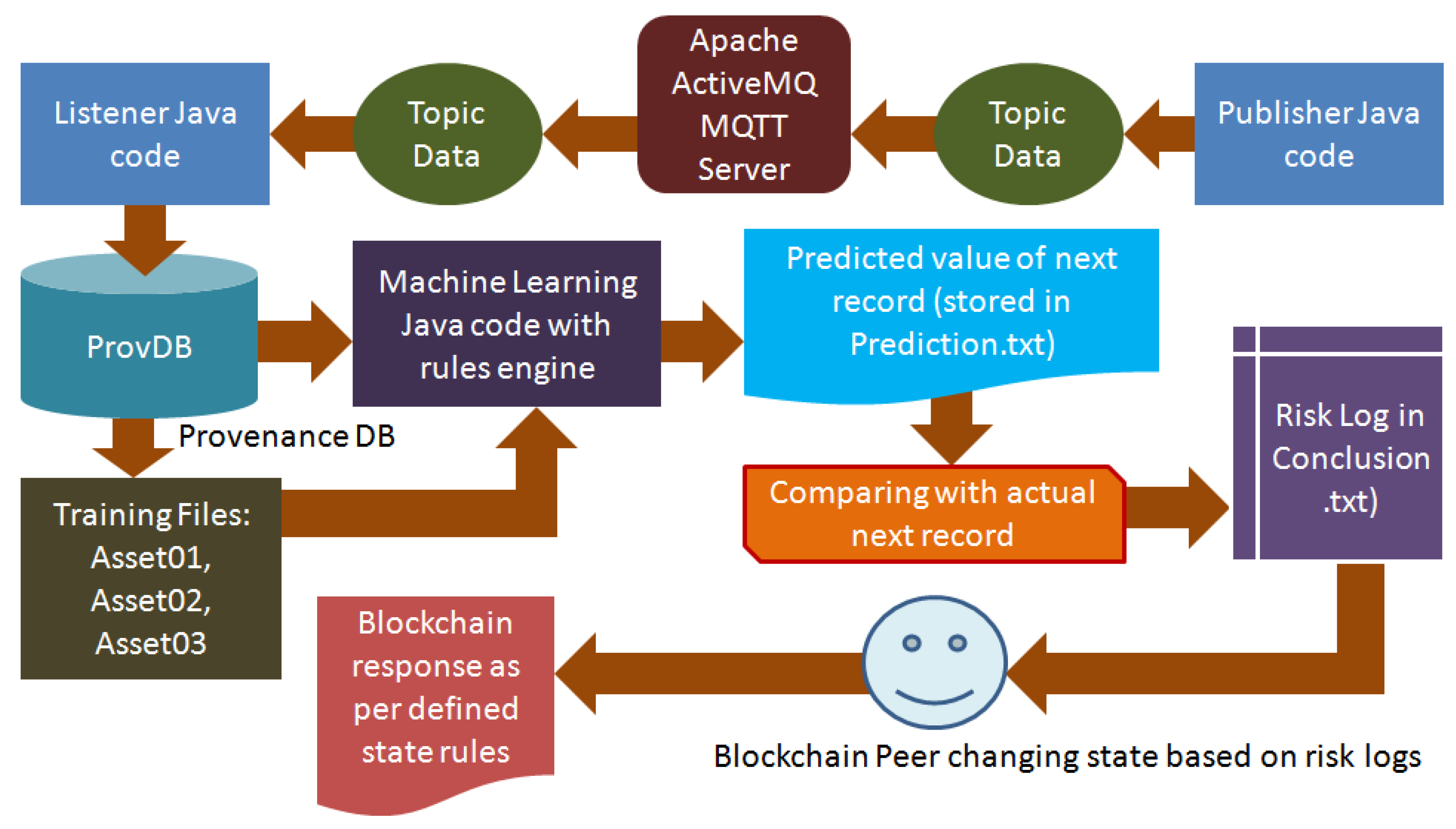
4. Primary Research
- (a)
- MQTT Broker Server using Apache ActiveMQ: The package ActiveMQ-5.15.0 was used to setup a MQTT broker server in Ubuntu 22.04. This package was selected because of its compatibility with Java 8 version.
- (b)
- Publisher Java code: programmed using Java 8; Java 8 was selected because CORDA for open source development is available with packages compatible with up to Java 8 version only. Professional versions of CORDA are available on higher versions of Java. As stated in previous section, this code should be embedded in the firmware of the IIoT devices. However, for the purpose of testing this research executed the code several times through Ubuntu 22.04 terminal by manipulating the input data at every event.
- (c)
- Listener Java code: programmed using Java 8: this file is responsible to receive the data transmitted through the MQTT connections and save them into a ProvDB file to be read by the machine learning algorithm.
- (d)
- Provenance database in the ARFF format: The file was created by the Listener java code in ProvDB.csv;
- (e)
- Machine Learning code in Java with and in-built rules engine called WEKA: The package selected was weka-3.7.0 because it is compatible with Java 8; the rules or risk assessment and logging were defined as detailed in the previous section; the machine learning code picks up the latest data from the ProvDB and then compares it with the latest next state predictions using 80% records for training and 20% for testing. Based on the predictions the machine learning populates the respective state files of Assets A01, A02, and A03 along with the latest risk values. The verbose report to be analysed by the blockchain peers is entered in conclusion.txt file in append mode (new records added to the older records).
- (f)
- CORDA blockchain framework with state rules defined in Java 8: To create smart contract state rules in CORDA, six Java files were configured: IOUState.java, IOUContract.java, IOUSchemaV1.java, ContractTests.java, ExampleFlow.java, and FlowTests.java. IOU is the name of smart contract tested in this experiment. While configuring these files, a database file named “iou.changelog-v1.xml” is configured automatically. This is the change log database comprising state changes of the smart contract named IOU. All the variables created in Schema and other files such as States and Flow, should have an existing record in the change log database.
- Step 1: Run the ActiveMQ console;
- Step 2: Run the Listener.java file; this opens the MQTT connections in the ActiveMQ console;
- Step 3: Run the Publisher.java and transmit data for location coordinates and weight carried out by a Forklift;
- Step 4: Run the machinelearning.java file;
- Step 5: Open the CORDA console through IntelliJ Idea;
- Step 6: Try entering the latest values received in assetplain.txt, and analysing the risk log in conclusion.txt and entering the appropriate risk value (updates sent to the smart ledger of the smart contract);
- Step 7: Observe the responses from the CORDA smart ledger and write the full report by analysing it and all the files generated by the machine learning code;
4. Discussion
- (a)
- the machine learning algorithm decides that risk is either at NONE or at LOW level such that the state change in the CORDA smart contract is allowed;
- (b)
- the machine learning algorithm decides that risk is either at MEDIUM or at HIGH level such that the state change in the CORDA smart contract is prohibited instructing the blockchain peers to conduct investigations;
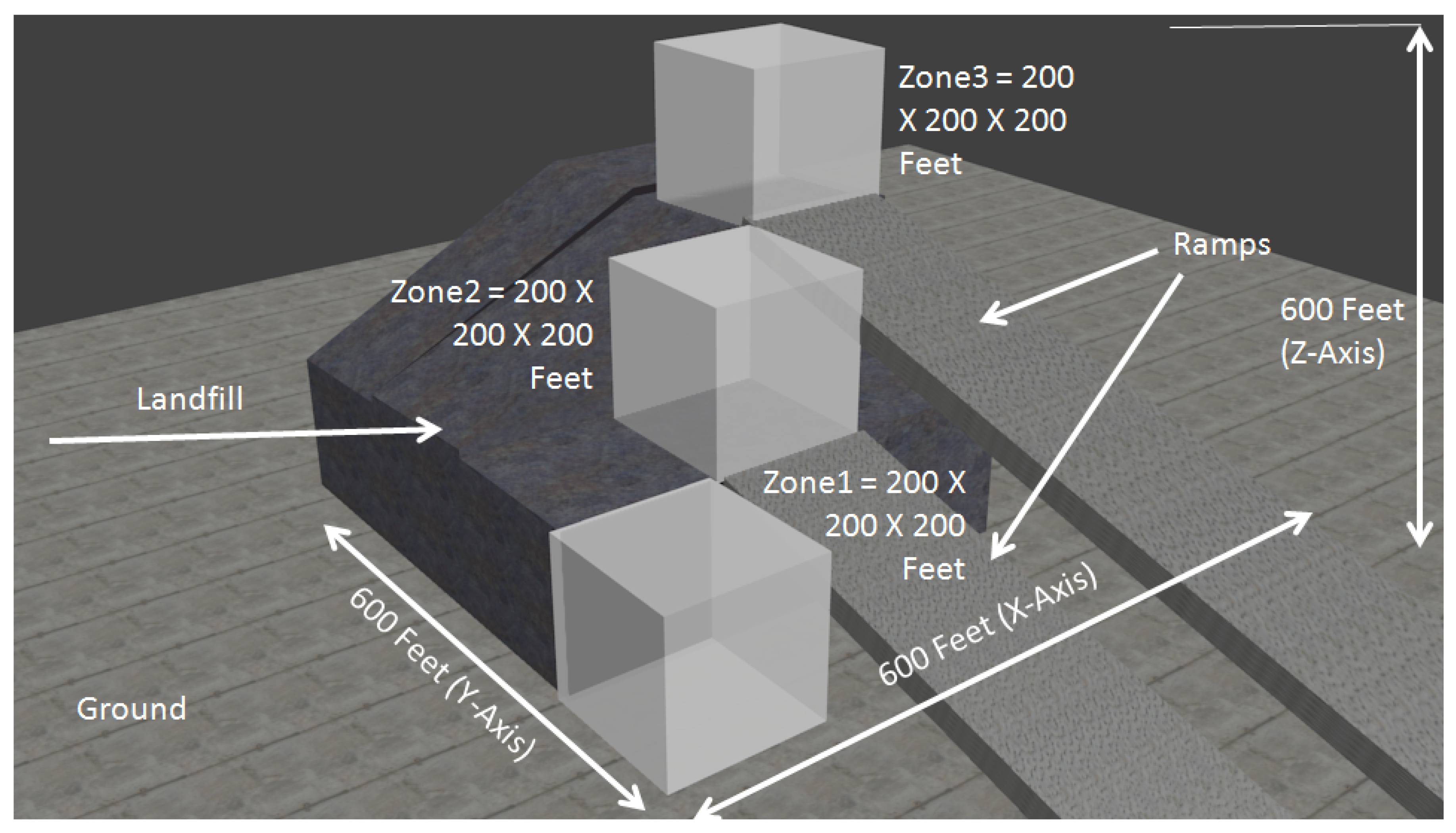
- Asset01 (A01): X = 1 to 200, Y = 1 to 200, and Z = 1 to 200 feet, and weight = 100 KG;
- Asset02 (A02): X = 201 to 400 feet, Y = 201 to 400 feet, and Z = 201 to 400 feet, and weight = 125 KG;
- Asset03 (A02): X = 401 to 600 feet, Y = 401 to 600 feet, and Z = 401 to 600 feet, and weight = 150 KG;
- (a)
- Validating the identity of cyber physical systems enabled with IIoT communications: This concern is clearly addressed in this research as the identity of the cyber physical system is registered in the MQTT broker server, in the ProvDB of the machine learning, in the training and testing database of machine learning, and in the smart contract of the blockchain.
- (b)
- Tracking rapid deployments and Internet-enabling of millions of cyber physical systems: With the system of smart contracts and smart ledgers in place, even millions of cyber physical systems shall be registered and prepared for tracking and tracing before assignment to smart contracts. However, the IT capacities of the cloud manufacturing and the network bandwidth should be sufficient to handle volumes of data generated by millions of cyber physical systems in real time.
- (c)
- Traceability of cyber physical systems added, modified, and removed; especially installed on mobile assets: The machine learning shall continuously track the operational state changes of the cyber physical systems and log risks accordingly for the blockchain peers monitoring the system. Major changes like addition, modification, and removal cannot go unnoticed by the machine learning. There may be false alarms because of communication interruptions (like data received in a topic stops temporarily) but the traceability and tracking will always be ON.
- (d)
- Validating fidelity of sensor data sent for influencing process events interpreted out of the sensory data and the decision-making algorithms running the actuation commands: This is a tough challenge. The validity of fidelity of sensor data can only be made by decision-making algorithms comprising of engineering knowledge integrated. This system can, however, report inconsistencies in the state changes through its predictive capability and log risks. This may be of some help to the engineers operating the cyber physical systems.
- (e)
- Establishing accountability and liability of individuals owning the cyber physical systems: This concern will be addressed by the system designed. At the time of registration of the assets, the ownership and accountability details will be recorded in the blockchain. The smart contracting parties will be fully liable for the assets registered and allocated to the contract. Further, blockchain peers from all contracting parties will monitor the operations thus ensuring timely detection of risks logged by the machine learning.
- (f)
- Inter-cloud assurances of cyber security: Inter-cloud assurance is possible in this solution if the same MQTT broker and machine learning systems are implemented for all the contracting parties interfacing through multi-cloud blockchain. If multiple brokers and machine learning systems need to be implemented in a multi-site environment then replication of data between the Conclusion.txt files implemented in multiple clouds should be implemented.
- (g)
- Algorithmic transparency (accountability of performance and behaviours of algorithms deployed for controlling operations of cyber physical systems): This is another tough challenge to be addressed. Performance and behaviours of algorithms require much deeper monitoring and control by sophisticated systems having full knowledge about the operating behaviours and performance metrics of the algorithms. This system can help by detecting changes in the already progressing patterns and reporting them as risks at different levels depending upon the rules defined in the machine learning code and the blockchain state rules.
- (h)
- Cyber physical systems indulging into erroneous or malicious processing using exploits, scripting attacks, bots, device identity theft, and other means thus affecting the execution of smart contracts negatively: Detection of exploits, scripting attacks, bots, etc. need to be enabled through intrusion detection and prevention systems. This solution can detect operational anomaly caused by such malicious software attacks through machine learning but cannot detect presence of the software. Any anomaly causing negative execution of smart contract will be detected through machine learning and traced to the device using provenance data. Negative execution will breach the blockchain state transition rules and hence transactions will be rejected promoting for investigations. Attempts of device identity theft will also be difficult for the attackers because three levels of registration in MQTT broker, machine learning ProvDB database, and the blockchain smart contract will cause deterrence for the attack planners. There is high chance that the attackers will not be able to plan a perfect breach of this entire system, although they should never be underestimated.
5. Conclusions
- What are the risks associated with cloud manufacturing in Industry 4.0?
- How can provenance blockchain be used to provide greater transparency and traceability in the cloud manufacturing process using AI-enabled predictive auditing?
- How can this system help in mitigating cloud manufacturing risks in Industry 4.0?
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Ghomi, Einollah Jafarnejad, Amir Masoud Rahmani, and Nooruldeen Nasih Qader. "Cloud manufacturing: challenges, recent advances, open research issues, and future trends." The International Journal of Advanced Manufacturing Technology 102, no. 9, 2019, pp. 3613-3639.
- Ming K. Lim, Weiqing Xiong, Chao Wang. “Cloud manufacturing architecture: a critical analysis of its development, characteristics and future agenda to support its adoption”. Industrial Management and Data Systems, 121, no. 10, 2021, pp. 2143-2180.
- Petri Helo, Yuqiuge Hao, Valeriia Boldosova, Rayko Toshev. "Cloud manufacturing ecosystem analysis and design". Robotics and Computer-Integrated manufacturing, 67, 2021, pp. 1-15.
- A. Felsberger, F. H. Qaiser, A. Choudhary, G. Reiner. The impact of Industry 4.0 on the reconciliation of dynamic capabilities: evidence from the European manufacturing industries. Production Planning & Control, 33 (2-3): 277-300, 2022, Taylor & Francis.
- J. Furnival, R. Boaden, K. Walshe. A dynamic capabilities view of improvement capability. Journal of Health Organization and Management, 33 (7/8): 821-834, 2019, Emerald.
- D. Mamedio, C. Rocha, D. Szczepanik, H. Kato. Strategic alliances and dynamic capabilities: a systematic review. Journal of Strategy and Management, 12 (1): pp. 83-102, 2019, Emerald.
- Ustundag, Alp, Emre Cevikcan, Kartal Yagiz Akdil, Alp Ustundag, and Emre Cevikcan. "Maturity and readiness model for industry 4.0 strategy." Industry 4.0: Managing the digital transformation. Switzerland: Springer International Publishing, 2018, pp.61-94.
- Salkin, Ceren, Mahir Oner, Alp Ustundag, and Emre Cevikcan. "A conceptual framework for Industry 4.0." Industry 4.0: managing the digital transformation. Switzerland: Springer International Publishing, 2018, pp. 3-23.
- Ustundag, Alp, Emre Cevikcan, Beyzanur Cayir Ervural, and Bilal Ervural. "Overview of cyber security in the industry 4.0 era." Industry 4.0: managing the digital transformation. Switzerland: Springer International Publishing, 2018, pp. 267-284.
- Sobers, R. "Cybersecurity Statistics and Trends for 2022" Varonis, 2022. Available: https://www.varonis.com/blog/cybersecurity-statistics/ [Accessed: 04 March 2022].
- Brooks, C. "Cybersecurity in 2022 – A Fresh Look at Some Very Alarming Stats" Forbes, 2022. Available: https://www.forbes.com/sites/chuckbrooks/2022/01/21/cybersecurity-in-2022--a-fresh-look-at-some-very-alarming-stats/?sh=53d0641b6b61 [Accessed: 04 March 2023].
- DiMase, Daniel, Zachary A. Collier, Kenneth Heffner, and Igor Linkov. "Systems engineering framework for cyber physical security and resilience." Environment Systems and Decisions 35, no. 2 (2015): 291-300.
- Reddy, Elizabeth, Baki Cakici, and Andrea Ballestero. "Beyond mystery: Putting algorithmic accountability in context." Big Data & Society 6, no. 1 (2019): 2053951719826856.
- Lepri, Bruno, Nuria Oliver, Emmanuel Letouzé, Alex Pentland, and Patrick Vinck. "Fair, transparent, and accountable algorithmic decision-making processes." Philosophy & Technology 31, no. 4 (2018): 611-627.
- Shaikh, Farooq Israr Ahmed "Security Framework for the Internet of Things Leveraging Network Telescopes and Machine Learning" University of South Florida, 2019. Published PHD Thesis.
- Gupta, Ruchika, Rakesh Kumar Phanden, Shubham Sharma, Priyank Srivastava, and Prateek Chaturvedi. "Security in manufacturing systems in the age of industry 4.0: Pitfalls and possibilities." In Advances in Industrial and Production Engineering, pp. 105-113. Springer, Singapore, 2021.
- Walker-Roberts Steven, Mohammad Hammoudeh, Omar Aldabbas, Mehmet Aydin, and Ali Dehghantanha. "Threats on the horizon: Understanding security threats in the era of cyber-physical systems." The Journal of Supercomputing, 76 (4): 2643-2664, 2020.
- Sadeghi, Ahmad-Reza, Christian Wachsmann, and Michael Waidner. "Security and privacy challenges in industrial internet of things." In 2015 52nd ACM/EDAC/IEEE Design Automation Conference (DAC), pp. 1-6. IEEE, 2015.
- Urquhart, Lachlan, and Derek McAuley. "Avoiding the internet of insecure industrial things." Computer law & security review 34, no. 3 (2018): 450-466.
- Sigwart, Marten, Michael Borkowski, Marco Peise, Stefan Schulte, and Stefan Tai. "A secure and extensible blockchain-based data provenance framework for the Internet of Things." Personal and Ubiquitous Computing (2020): 1-15.
- Ali, Saqib, Guojun Wang, Md Zakirul Alam Bhuiyan, and Hai Jiang. "Secure data provenance in cloud-centric internet of things via blockchain smart contracts." In 2018 IEEE SmartWorld, Ubiquitous Intelligence & Computing, Advanced & Trusted Computing, Scalable Computing & Communications, Cloud & Big Data Computing, Internet of People and Smart City Innovation (SmartWorld/SCALCOM/UIC/ATC/CBDCom/IOP/SCI), pp. 991-998. IEEE, 2018.
- Terzi, Sofia, Angeliki Zacharaki, Alexandros Nizamis, Konstantinos Votis, Dimosthenis Ioannidis, Dimitrios Tzovaras, and Ioannis Stamelos. "Transforming the supply-chain management and industry logistics with blockchain smart contracts." In Proceedings of the 23rd Pan-Hellenic conference on informatics, pp. 9-14. 2019.
- Carata, Lucian. "Provenance-based computing." PhD diss., University of Cambridge, 2019.
- Li, Jin, Xiaofeng Chen, Qiong Huang, and Duncan S. Wong. "Digital provenance: Enabling secure data forensics in cloud computing." Future Generation Computer Systems 37 (2014): 259-266.
- Ali, Mufajjul. "Provenance-based data traceability model and policy enforcement framework for cloud services." PhD diss., University of Southampton, 2016.
- Nwafor, Ebelechukwu, Andre Campbell, David Hill, and Gedare Bloom. "Towards a provenance collection framework for internet of things devices." In 2017 IEEE SmartWorld, Ubiquitous Intelligence & Computing, Advanced & Trusted Computed, Scalable Computing & Communications, Cloud & Big Data Computing, Internet of People and Smart City Innovation (SmartWorld/SCALCOM/UIC/ATC/CBDCom/IOP/SCI), pp. 1-6. IEEE, 2017.
- Suhail, Sabah, Choon Seong Hong, Zuhaib Uddin Ahmad, Faheem Zafar, and Abid Khan. "Introducing secure provenance in IoT: Requirements and challenges." In 2016 International Workshop on Secure Internet of Things (SIoT), pp. 39-46. IEEE, 2016.
- Zhao, Shanshan, Shancang Li, and Yufeng Yao. "Blockchain enabled industrial Internet of Things technology." IEEE Transactions on Computational Social Systems 6, no. 6 (2019): 1442-1453.
- Banerjee, Arnab. "Blockchain technology: supply chain insights from ERP." In Advances in computers, vol. 111, pp. 69-98. Elsevier, 2018.
- Suriarachchi, Isuru, Sachith Withana, and Beth Plale. "Big provenance stream processing for data intensive computations." In 2018 IEEE 14th International Conference on e-Science (e-Science), pp. 245-255. IEEE, 2018.
- Pasquier Thomas, Jatinder Singh, Julia Powles, David Eyers, Margo Seltzer, and Jean Bacon. "Data provenance to audit compliance with privacy policy in the Internet of Things." Personal and Ubiquitous Computing 22, no. 2 (2018): 333-344.
- Han Hongdan, Shiwakoti Radha K., Jarvis Robin, Mordi Chima, Botchie David. Accounting and auditing with blockchain technology and artificial Intelligence: A literature review. International Journal of Accounting Information Systems, 48, no. 100598 (2023): 1-16.
- Hyperledger. Fabric Docs - Introduction. Hyperledger Fabric 2023. Available at: https://hyperledger-fabric.readthedocs.io/en/release-2.5/blockchain.html [Accessed: 02 May 2023].
- CORDA. CORDA Community Edition Key Concepts. CORDA Community 4.10, 2023. Available at: https://docs.r3.com/en/platform/CORDA/4.10/community/about-CORDA/CORDA-key-concepts.html [Accessed: 02 May 2023].
- CORDA. Building your first basic CORDApp. CORDA App Docs, 2023, Available at https://docs.r3.com/en/platform/CORDA/4.10/community/get-started/tutorials/build-basic-CORDApp/basic-CORDApp-intro.html [Accessed: 03 May 2023].
- Saunders Mark., Lewis Philip., Thornhill Adrian. Research Methods for Business Students. 5th Edition, 2009, London: Pearson.
- Bryman, Alan and Bell, Emma. Business Research Methods. 3rd Edition, 2011, Oxford: Oxford University Press.
- Creswell, John W. Research Design: Qualitative, Quantitative, and Mixed Methods. 4th Edition, 2014, LA: Sage.
- Kaaniche, Nesrine, Sana Belguith, Maryline Laurent, Ashish Gehani, and Giovanni Russello. "Prov-Trust: towards a trustworthy SGX-based data provenance system." In Proceedings of the 17th International Joint Conference on e-Business and Telecommunications-Volume 3: SECRYPT, pp. 225-237. ScitePress, 2020.
- Liang, Xueping, Sachin Shetty, Deepak Tosh, Charles Kamhoua, Kevin Kwiat, and Laurent Njilla. "Provchain: A blockchain-based data provenance architecture in cloud environment with enhanced privacy and availability." In 2017 17th IEEE/ACM International Symposium on Cluster, Cloud and Grid Computing (CCGRID), pp. 468-477. IEEE, 2017.
- Ramachandran, Aravind, and Murat Kantarcioglu. "Smartprovenance: a distributed, blockchain based dataprovenance system." In Proceedings of the Eighth ACM Conference on Data and Application Security and Privacy, pp. 35-42. 2018.
- Ruan, Pingcheng, Gang Chen, Tien Tuan Anh Dinh, Qian Lin, Beng Chin Ooi, and Meihui Zhang. "Fine-grained, secure and efficient data provenance on blockchain systems." Proceedings of the VLDB Endowment 12, no. 9, pp. 975-988. 2019.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).



