Submitted:
19 July 2023
Posted:
19 July 2023
Read the latest preprint version here
Abstract
Keywords:
1. Introduction
- Ch1.
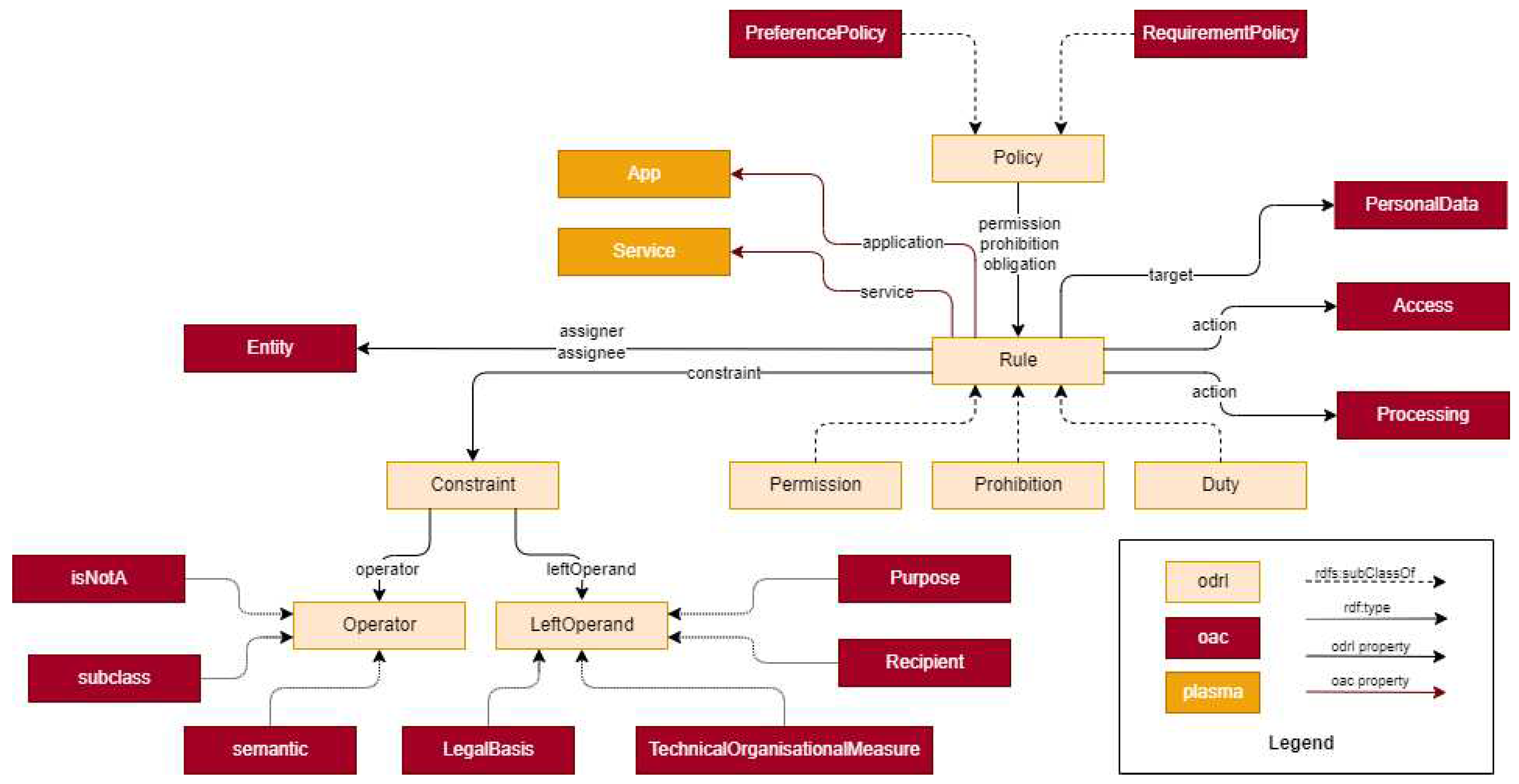
- Users’ policies as a precursor of consent -– Previous studies have shown that the current access control mechanisms supported by the Solid protocol are not enough to deal with GDPR requirements, however, there is work being developed to introduce a policy language – the Open Digital Rights Language (ODRL) – “for Expressing Consent through Granular Access Control Policies”3 [22]. User policies can enable compliance with several requirements of the GDPR. Pursuant to Articles 13 and 14 [1], data controllers have the obligation to provide the data subject information about the processing of their personal data and users’ policies can enable communication of this information. Furthermore, information about the processing of personal data is a prerequisite for obtaining valid consent pursuant to Articles 7 and 4 (11) [1].
- Ch2.
- Automation of consent –- Decentralised ecosystems, such as the one involving Solid Pods, rely on the existence of authorizations to provide access to (personal) data. Since its users are the ones specifying the access authorizations, said systems provide a fertile ground for research on the automation of access to resources – in this case, a data request might be automatically accepted, with no further action from the user, if the user had previously added a policy in its Pod stating that said access can be granted. Whether such automation can be considered consent under the GDPR is still up for debate. Even though there is no provision in GDPR prohibiting the expression of consent in advance, for it to be valid, the conditions set in Article 7 and Article 4 (11) [1] must also be met. In addition to the requirement of consent to be informed, the controller must be able to prove that consent was freely given, specific and explicit.
- Ch3.
- Dealing with health data for biomedical research – The processing of GDPR’s special categories of personal data, such as data concerning health, is prohibited by default and brings extra “burdens” to data controllers. In addition to identifying a legal basis under Article 6 [1], they must rely on an exception under Article 9 [1]. Also, at the national level, further limitations regarding the processing of health data can be introduced. There are however certain derogations when health data are processed for scientific research or for the management of public health (Recital 52 [1]).
2. Background –- Decentralising the Web with Solid
2.1. Solid overview
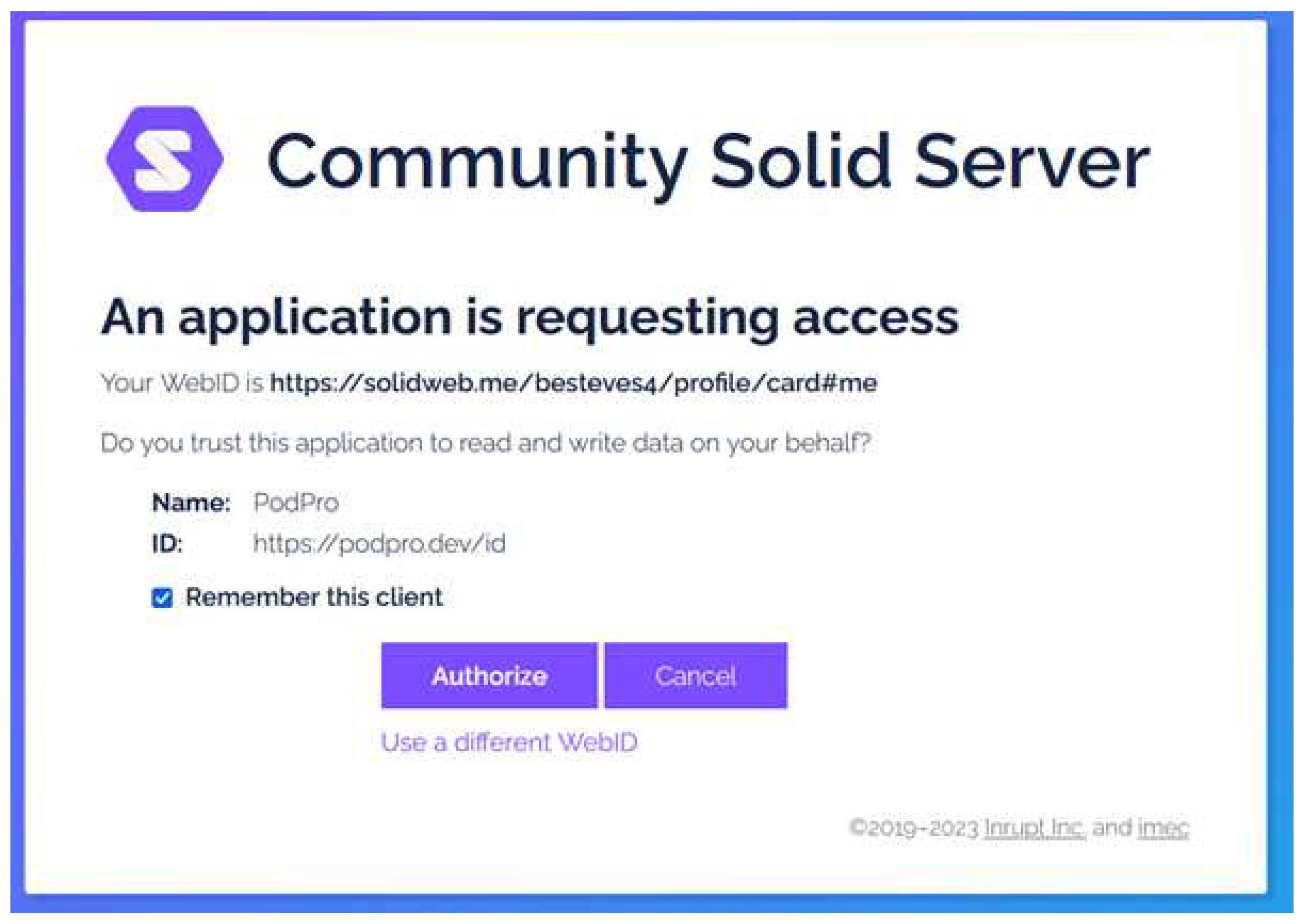
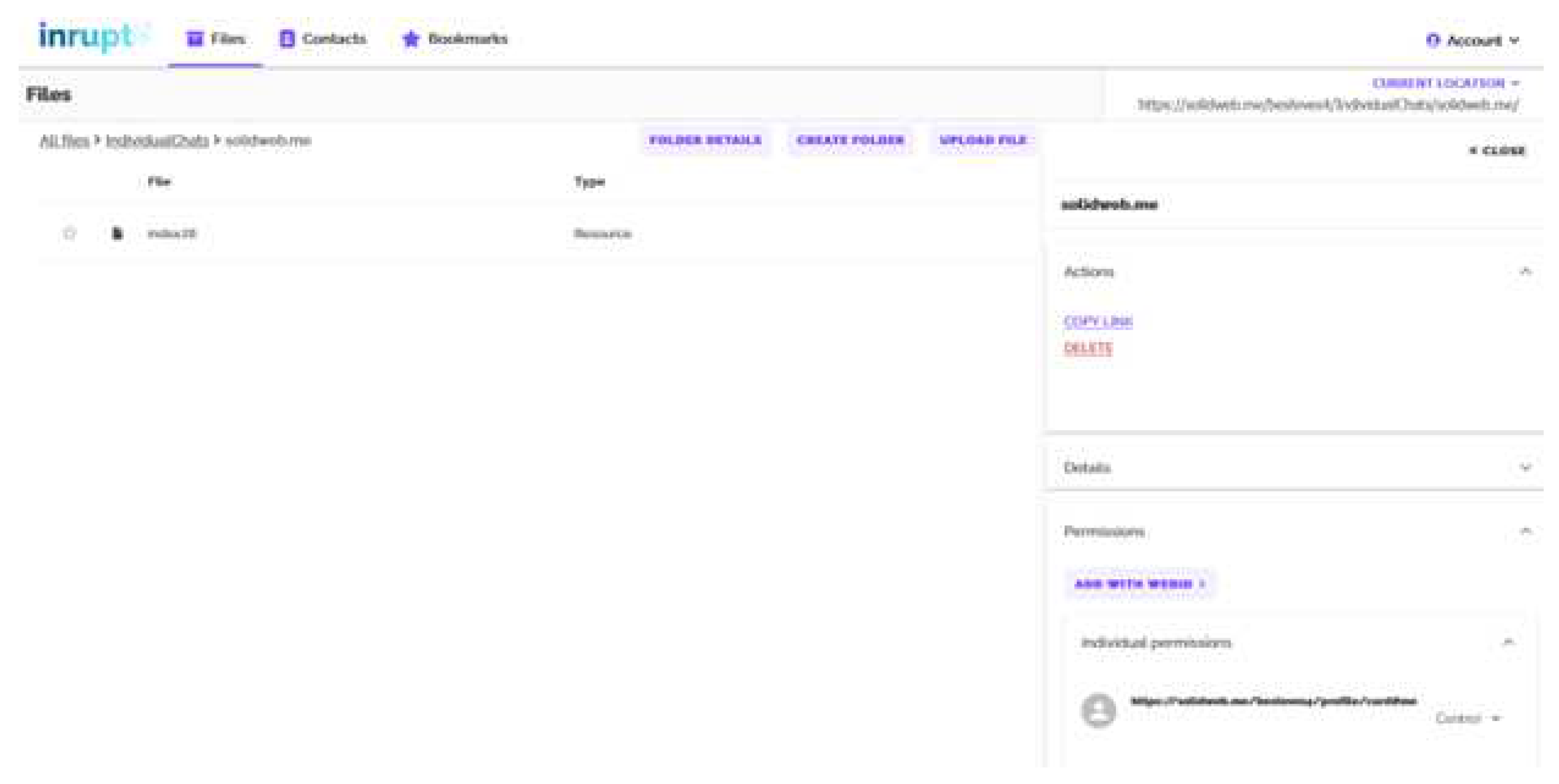
2.2. Access control in Solid
| Listing 1. WAC authorization that makes a WebID profile, https://solidweb.me/besteves4/profile/card, readable by any agent. |
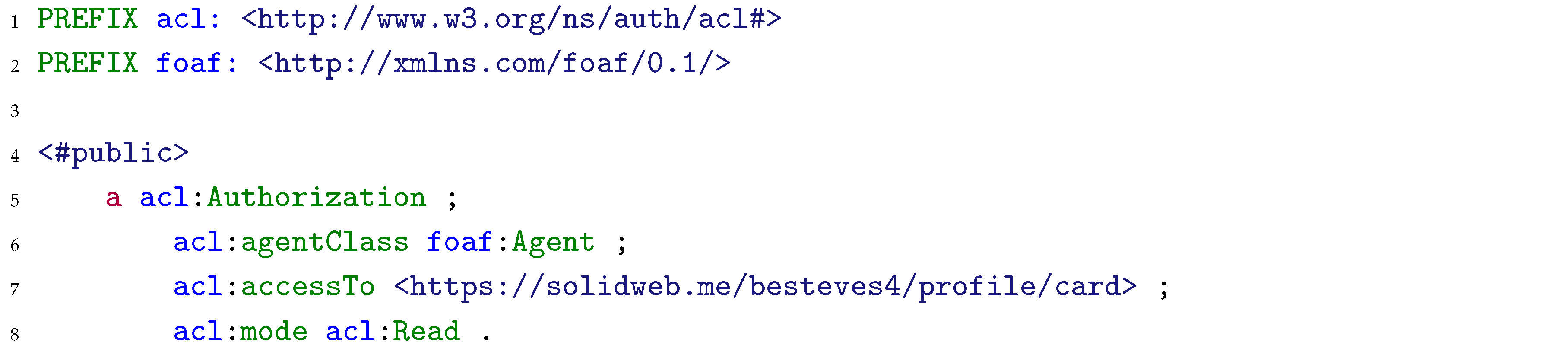 |
| Listing 2. ACP authorization that makes a WebID profile, https://solidweb.me/besteves4/profile/card, readable by any agent using any client application. |
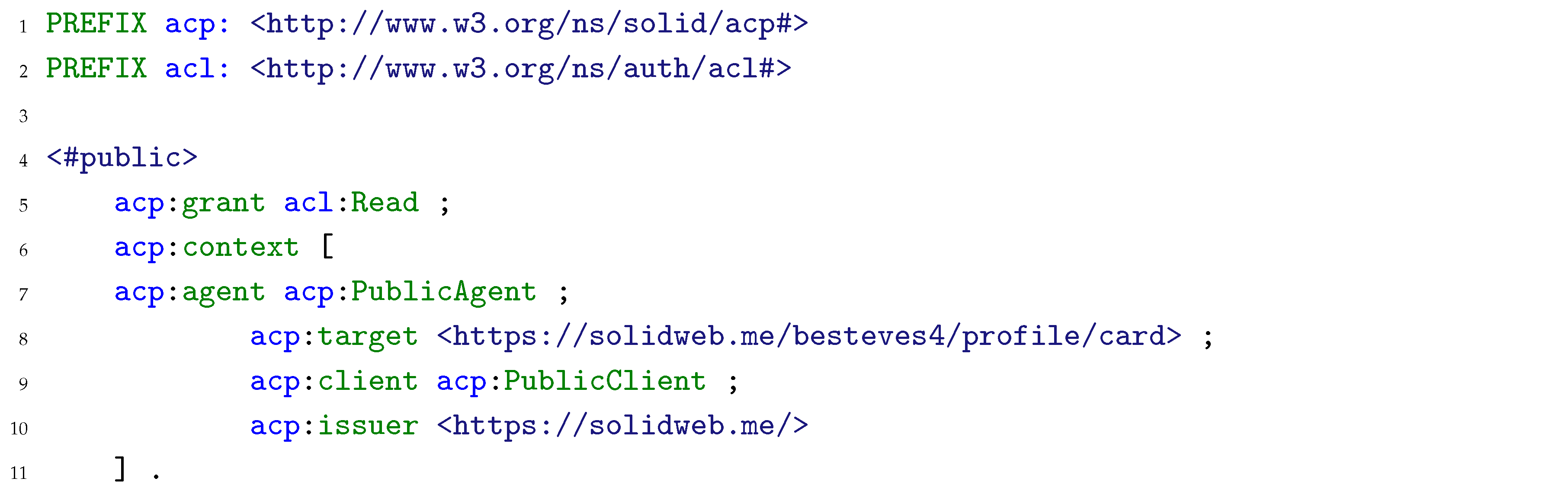 |
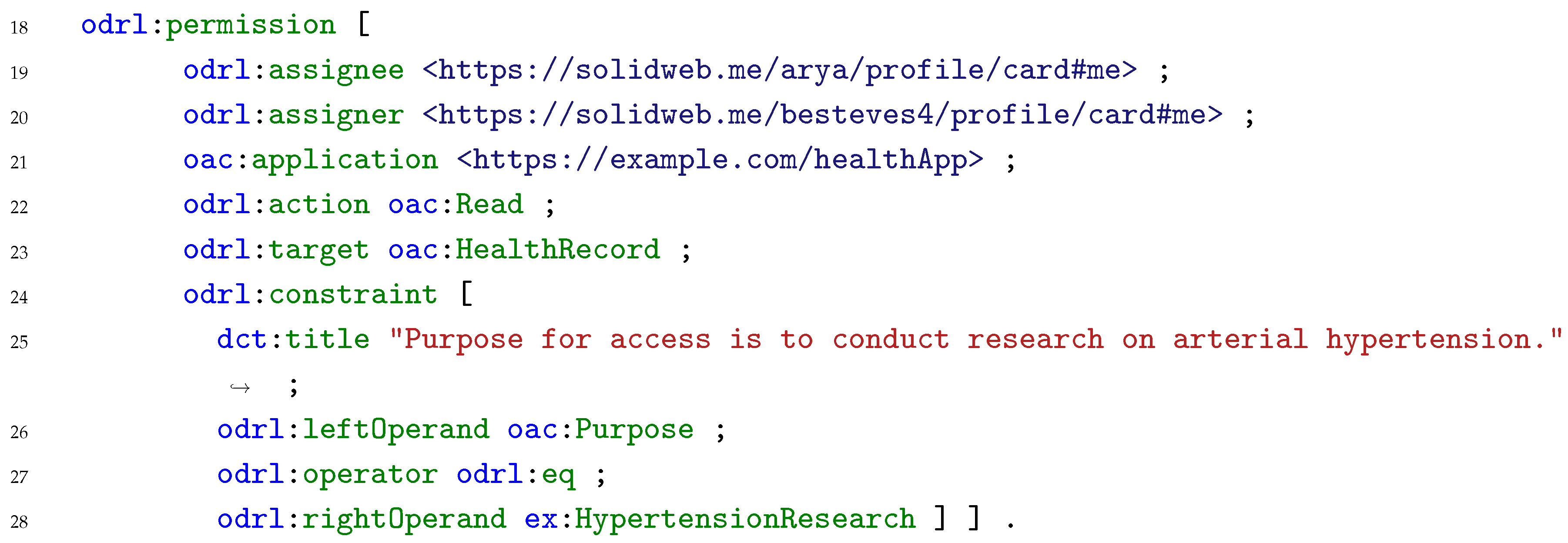
| Listing 3. An example ODRL offer policy generated by https://solidweb.me/besteves4/profile/card#me, stating that health records data can be accessed for the purpose of health, medical or biomedical research. |
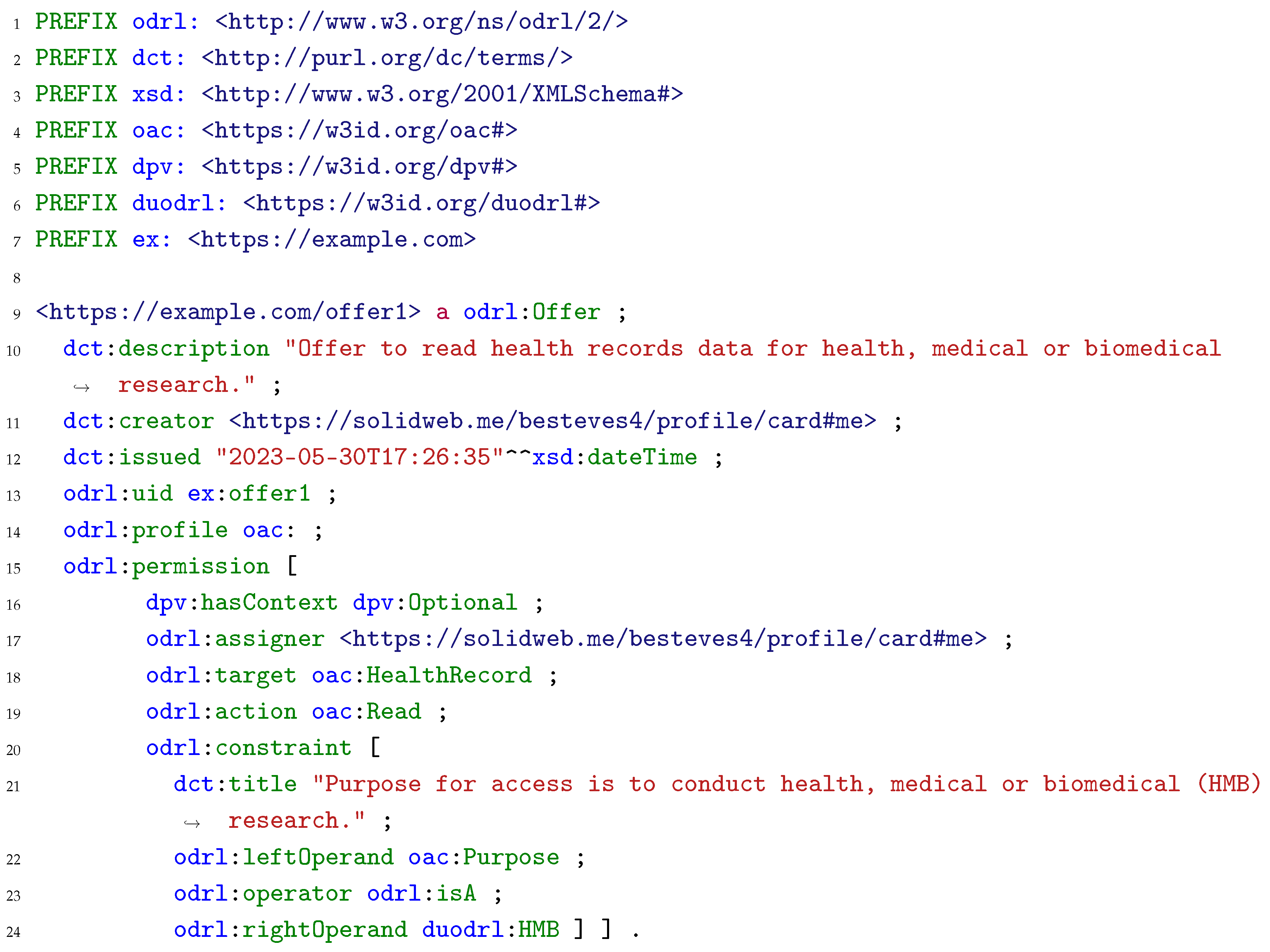 |
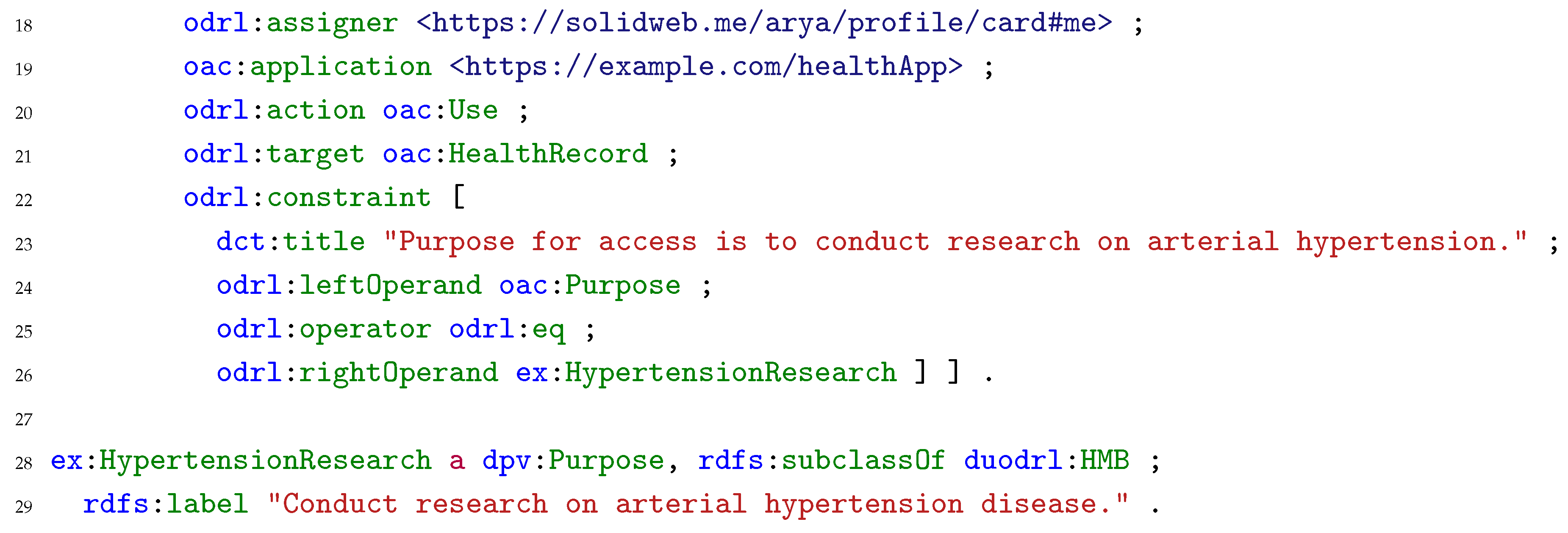
| Listing 4. An example ODRL Request policy made by https://solidweb.me/arya/profile/card#me, using the https://example.com/healthApp application, to use health records data from https://solidweb.me/besteves4/profile/card#me to conduct research on arterial hypertension disease. |
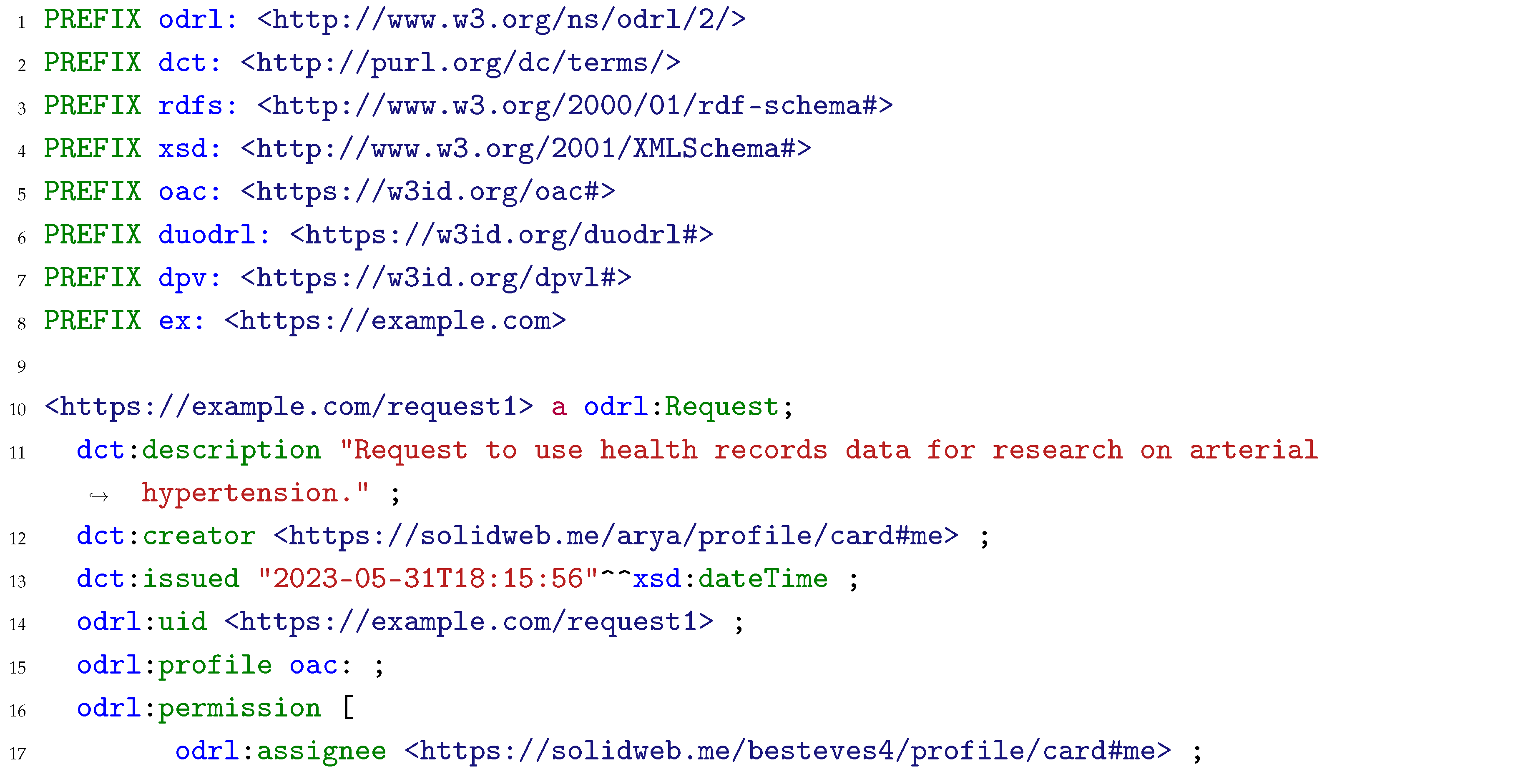 |
 |
2.3. Other related works
3. Describing the distinction between consent and granting access to a resource
| Listing 5. An example ODRL Agreement policy that grants https://solidweb.me/arya/profile/card#me read access to health records data from https://solidweb.me/besteves4/profile/card#me to conduct research on arterial hypertension disease. |
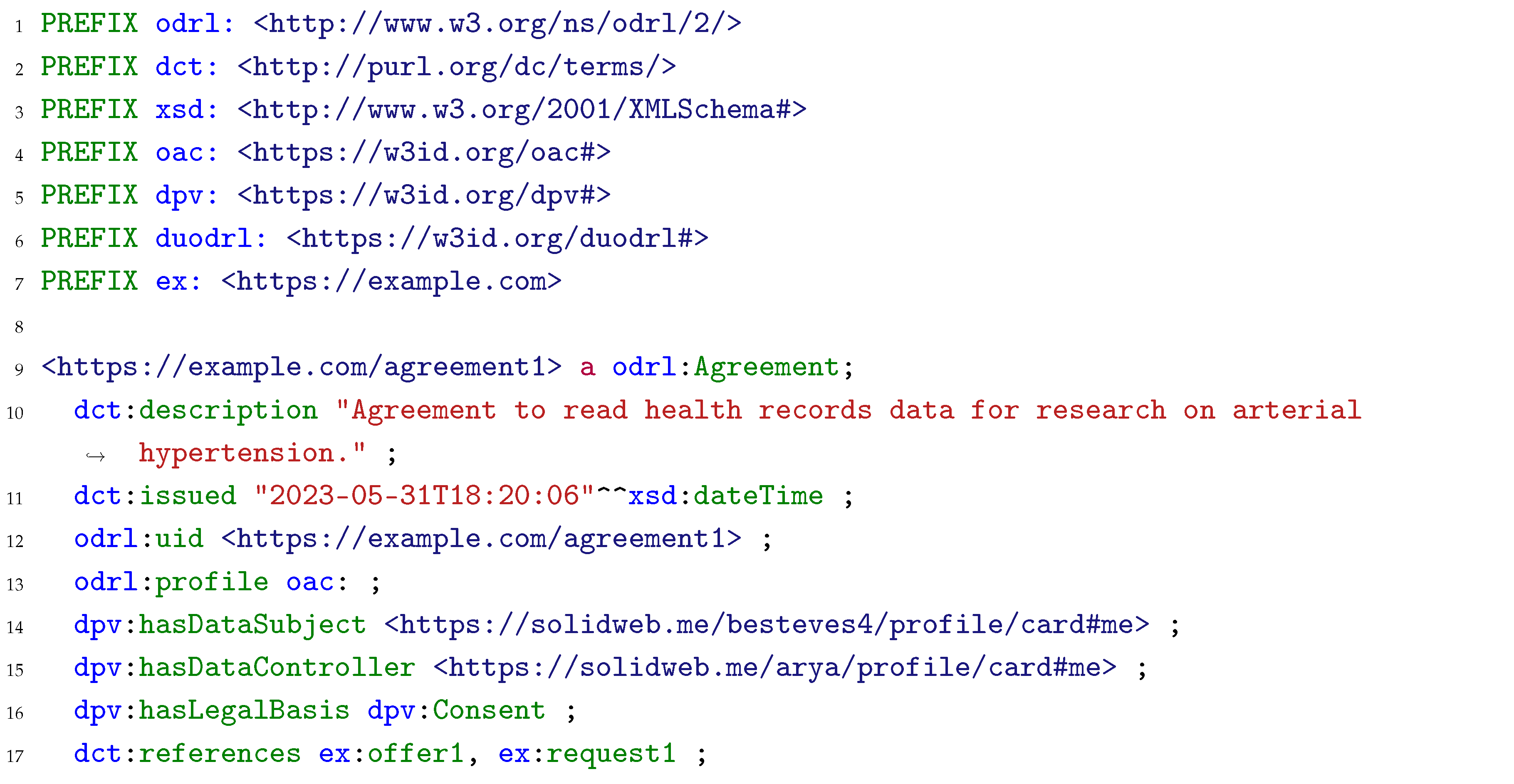 |
 |
4. Can consent be automated?
4.1. Expressing consent in advance
4.2. Expressing specific consent
4.2.1. Specificity of purpose and processing operations
4.2.2. Assessing compatibility between preferences and requests
- (a)
- any link between the purposes for which the personal data have been collected and the purposes of the intended further processing;
- (b)
- the context in which the personal data have been collected, in particular regarding the relationship between data subjects and the controller;
- (c)
- the nature of the personal data, in particular, whether special categories of personal data are processed [...];
- (d)
- the possible consequences of the intended further processing for data subjects;
- (e)
- the existence of appropriate safeguards, which may include encryption or pseudonymisation.
Purpose Specification Principle
Use Limitation Principle
- (a)
- with the consent of the data subject; or
- (b)
- by the authority of law.
4.2.3. The fine line dividing expressing and delegating consent
4.3. Specific data controllers? Or categories of recipients?
4.3.1. The moment when the identity of the controller is disclosed
4.3.2. The difference between controllers and recipients of personal data
4.4. The special case of biomedical research
| Listing 6. An example ODRL offer policy generated by https://solidweb.me/arya/profile/card#me, stating that a dataset can be accessed for the purpose of health, medical or biomedical research in the context of Project X, provided that the entity requesting data provides documentation of ethical approval. |
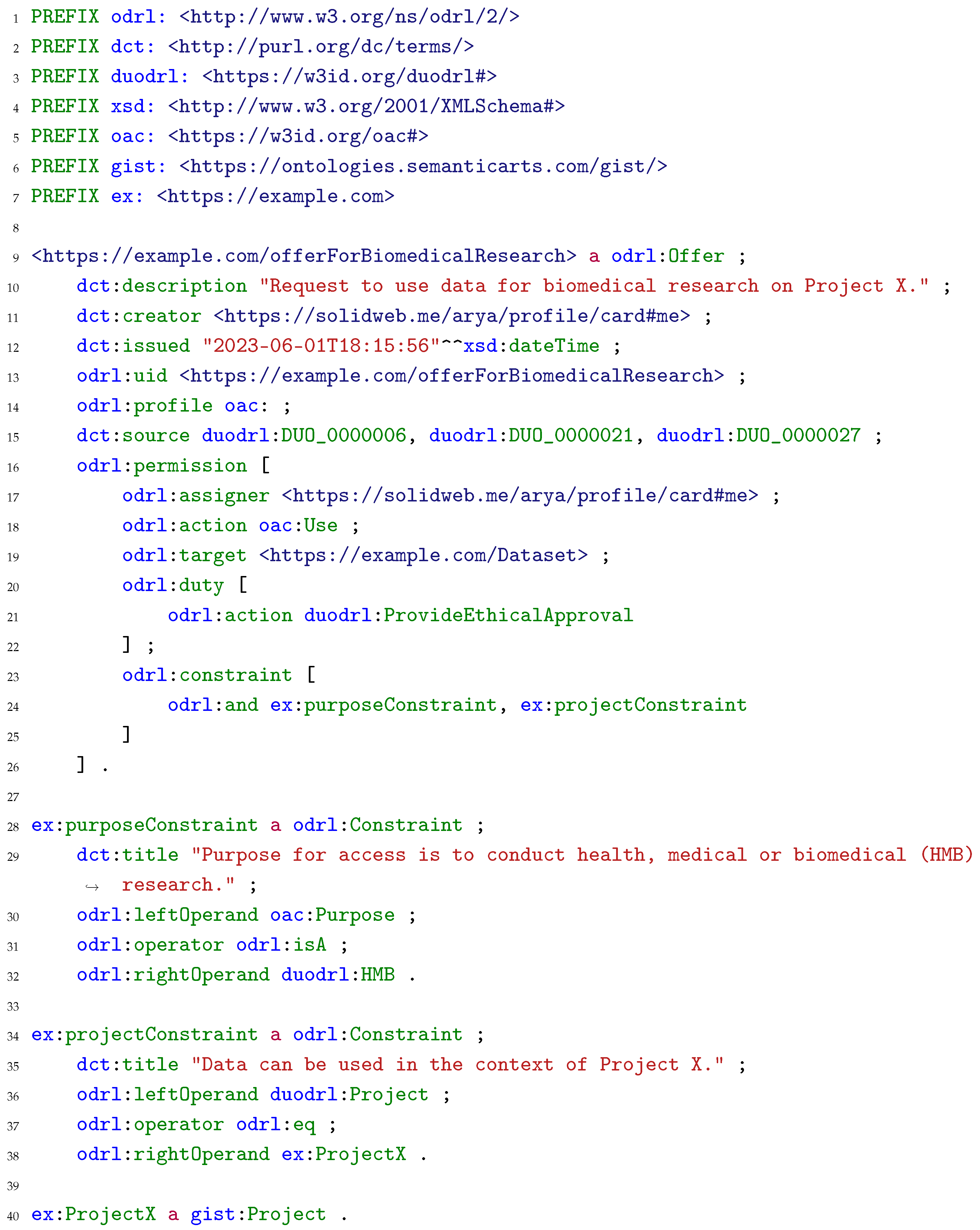 |
4.4.1. A stricter regime
4.4.2. A series of derogations
A. The purpose limitation principle
B. The obligation to provide information
C. Alternative legal bases beyond consent
5. Future Research & Concluding Remarks
Funding
Conflicts of Interest
References
- Regulation (EU) 2016/679 of the European Parliament and of the Council of on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation), 2018. 27 April.
- Bradford, A. The Brussels Effect: How the European Union Rules the World; Oxford University Press, 2019. [CrossRef]
- Terpstra, A.; Schouten, A.P.; Rooij, A.d.; Leenes, R.E. Improving privacy choice through design: How designing for reflection could support privacy self-management. First Monday 2019, 24. [Google Scholar] [CrossRef]
- Linden, T.; Khandelwal, R.; Harkous, H.; Fawaz, K. The Privacy Policy Landscape After the GDPR. In Proceedings of the Proceedings on Privacy Enhancing Technologies, Vol. 1; 2020; pp. 47–64. [Google Scholar] [CrossRef]
- Mohan, J.; Wasserman, M.; Chidambaram, V. Analyzing GDPR Compliance Through the Lens of Privacy Policy. In Proceedings of the Heterogeneous Data Management, Polystores, and Analytics for Healthcare; Gadepally, V.; Mattson, T.; Stonebraker, M.; Wang, F.; Luo, G.; Laing, Y.; Dubovitskaya, A., Eds. Springer International Publishing, Lecture Notes in Computer Science; 2019; pp. 82–95. [Google Scholar] [CrossRef]
- European Commission. Communication from the Commission to the European Parliament, the Council, the European Economic and Social Committee and the Committee of the Regions - A European strategy for data, 2020.
- Regulation (EU) 2022/868 of the European Parliament and of the Council of on European data governance and amending Regulation (EU) 2018/1724 (Data Governance Act) (Text with EEA relevance), 2022. Legislative Body: CONSIL, EP. 30 May.
- Mariani, M.M.; Ek Styven, M.; Teulon, F. Explaining the intention to use digital personal data stores: An empirical study. Technological Forecasting and Social Change 2021, 166. [Google Scholar] [CrossRef]
- Craglia, M.; Scholten, H.; Micheli, M.; Hradec, J.; Calzada, I.; Luitjens, S.; Ponti, M.; Boter, J. Digitranscope: The governance of digitally transformed society; Publications Office of the European Union, 2021.
- Ilves, L.K.; Osimo, D. A roadmap for a fair data economy. Policy Brief, Sitra and the Lisbon Council, 2019.
- Verbrugge, S.; Vannieuwenborg, F.; Van der Wee, M.; Colle, D.; Taelman, R.; Verborgh, R. Towards a personal data vault society: an interplay between technological and business perspectives. In Proceedings of the 2021 60th FITCE Communication Days Congress for ICT Professionals: Industrial Data – Cloud, Low Latency and Privacy (FITCE); 2021; pp. 1–6. [Google Scholar] [CrossRef]
- Supervisor, E.D.P. TechDispatch #3/2020 - Personal Information Management Systems. Technical report, 2021.
- Janssen, H.; Cobbe, J.; Singh, J. Personal information management systems: a user-centric privacy utopia? Internet Policy Review 2020, 9. [Google Scholar] [CrossRef]
- Janssen, H.; Cobbe, J.; Norval, C.; Singh, J. Decentralized data processing: personal data stores and the GDPR. International Data Privacy Law 2020, 10, 356–384. [Google Scholar] [CrossRef]
- Van Damme, S.; Mechant, P.; Vlassenroot, E.; Van Compernolle, M.; Buyle, R.; Bauwens, D. Towards a Research Agenda for Personal Data Spaces: Synthesis of a Community Driven Process. In Proceedings of the Electronic Government; Janssen, M.; Csáki, C.; Lindgren, I.; Loukis, E.; Melin, U.; Viale Pereira, G.; Rodríguez Bolívar, M.P.; Tambouris, E., Eds. Springer International Publishing, Lecture Notes in Computer Science; 2022; pp. 563–577. [Google Scholar] [CrossRef]
- Edwards, L.; Finck, M.; Veale, M.; Zingales, N. Data subjects as data controllers: a Fashion(able) concept? Internet Policy Review 2019. [Google Scholar]
- Chomczyk Penedo, A. Self-sovereign identity systems and European data protection regulations: an analysis of roles and responsibilities. In Proceedings of the Open Identity Summit 2021. Gesellschaft für Informatik e.V. 2021; pp. 95–5468. [Google Scholar]
- Verborgh, R. Paradigm shifts for the decentralized Web, 2017-12-20.
- De Bot, D.; Haegemans, T. Data Sharing Patterns as a Tool to Tackle Legal Considerations about Data Reuse with Solid: Theory and Applications in Europe. Digita research reports, 2021.
- Lodge, T.; Crabtree, A.; Brown, A. Developing GDPR Compliant Apps for the Edge. In Proceedings of the Data Privacy Management, Cryptocurrencies and Blockchain Technology; Garcia-Alfaro, J.; Herrera-Joancomartí, J.; Livraga, G.; Rios, R., Eds. Springer International Publishing, Lecture Notes in Computer Science; 2018; pp. 313–328. [Google Scholar] [CrossRef]
- Pandit, H.J. Making Sense of Solid for Data Governance and GDPR. Information 2023, 14. [Google Scholar] [CrossRef]
- Esteves, B.; Pandit, H.J.; Rodríguez-Doncel, V. ODRL Profile for Expressing Consent through Granular Access Control Policies in Solid. In Proceedings of the 2021 IEEE European Symposium on Security and Privacy Workshops (EuroS PW); 2021; pp. 298–0657. [Google Scholar] [CrossRef]
- Debackere, L.; Colpaert, P.; Taelman, R.; Verborgh, R. A Policy-Oriented Architecture for Enforcing Consent in Solid. In Proceedings of the Companion Proceedings of the Web Conference 2022.; pp. 202222516–524. [CrossRef]
- Akaichi, I. Semantic Technology based Usage Control for Decentralized Systems, [2206.04947 [cs, eess]]. [CrossRef]
- Braun, C.H.J.; Käfer, T. Attribute-based Access Control on Solid Pods using Privacy-friendly Credentials. In Proceedings of the Proceedings of the Poster and Demo Track and Workshop Track of the 18th International Conference on Semantic Systems Co-Located with 18th International Conference on Semantic Systems (SEMANTiCS 2022); 2022. [Google Scholar]
- Sambra, A.V.; Mansour, E.; Hawke, S.; Zereba, M.; Greco, N.; Ghanem, A.; Zagidulin, D.; Aboulnaga, A.; Berners-Lee, T. Solid: A Platform for Decentralized Social Applications Based on Linked Data. Technical report, 2016.
- Iannella, R.; Villata, S. ODRL Information Model 2.2, URL: https://www.w3.org/TR/odrl-model/, 2018.
- Pandit, H.J.; Polleres, A.; Bos, B.; Brennan, R.; Bruegger, B.; Ekaputra, F.J.; Fernández, J.D.; Hamed, R.G.; Kiesling, E.; Lizar, M.; et al. Creating a Vocabulary for Data Privacy: The First-Year Report of Data Privacy Vocabularies and Controls Community Group (DPVCG). In Proceedings of the On the Move to Meaningful Internet Systems: OTM 2019 Conferences; Panetto, H.; Debruyne, C.; Hepp, M.; Lewis, D.; Ardagna, C.A.; Meersman, R., Eds. Springer International Publishing, Vol. 11877; 2019; pp. 714–730. [Google Scholar] [CrossRef]
- Havur, G.; Sande, M.; Kirrane, S. Greater Control and Transparency in Personal Data Processing:. In Proceedings of the Proceedings of the 6th International Conference on Information Systems Security and Privacy. [CrossRef]
- De Mulder, G.; De Meester, B.; Heyvaert, P.; Taelman, R.; Dimou, A.; Verborgh, R. PROV4ITDaTa: Transparent and direct transferof personal data to personal stores. In Proceedings of the Companion Proceedings of the Web Conference 2021.; pp. 202121695–697. [CrossRef]
- Esteves, B.; Rodríguez-Doncel, V.; Longares, R. Automating the Response to GDPR’s Right of Access. In Legal Knowledge and Information Systems; IOS Press, 2022; pp. 170–175. [CrossRef]
- Esteves, B.; Rodríguez-Doncel, V.; Pandit, H.J.; Mondada, N.; McBennett, P. Using the ODRL Profile for Access Control for Solid Pod Resource Governance. In Proceedings of the The Semantic Web: ESWC 2022 Satellite Events; Groth, P.; Rula, A.; Schneider, J.; Tiddi, I.; Simperl, E.; Alexopoulos, P.; Hoekstra, R.; Alam, M.; Dimou, A.; Tamper, M., Eds. Springer International Publishing, Lecture Notes in Computer Science; 2022; pp. 16–20. [Google Scholar] [CrossRef]
- Bailly, H.; Papanna, A.; Brennan, R. Prototyping an End-User User Interface for the Solid Application Interoperability Specification Under GDPR. In Proceedings of the The Semantic Web; Pesquita, C.; Jimenez-Ruiz, E.; McCusker, J.; Faria, D.; Dragoni, M.; Dimou, A.; Troncy, R.; Hertling, S., Eds. Springer Nature Switzerland, Lecture Notes in Computer Science; 2023; pp. 557–573. [Google Scholar] [CrossRef]
- Hochstenbach, P.; De Roo, J.; Verborgh, R. RDF Surfaces: Computer Says No. In Proceedings of the 1st Workshop on Trusting Decentralised Knowledge Graphs and Web Data; 2023. [Google Scholar]
- Sun, C.; Gallofré Ocaña, M.; van Soest, J.; Dumontier, M. ciTIzen-centric DAta pLatform (TIDAL): Sharing distributed personal data in a privacy-preserving manner for health research. Semantic Web, I: 14, 977–996. Publisher; -01. [CrossRef]
- Janeiro Digital at Solid World: NHS Personal Health Stores with XFORM Health and Solid, 2021.
- Ausloos, J.; Ausloos, J. The Right to Erasure in EU Data Protection Law; Oxford Data Protection & Privacy Law, Oxford University Press, 2020.
- Lynskey, O. The Foundations of EU Data Protection Law; Oxford Studies in European Law, Oxford University Press, 2015.
- Kranenborg, H.R. Article 8 – Protection of Personal Data. In The EU Charter of Fundamental Rights; Hart Publishing, 2014.
- European Data Protection Board. Guidelines 2/2019 on the processing of personal data under Article 6(1)(b) GDPR in the context of the provision of online services to data subjects, 2019.
- European Data Protection Board. Guidelines 05/2020 on Consent under Regulation 2016/679 Version 1.1, 2020.
- Article 29 Data Protection Working Party. Opinion 15/2011 on the definition of consent.
- Article 29 Data Protection Working Party. Guidelines on consent under Regulation 2016/679.
- Solove, D.J. Privacy Self-Management and the Consent Dilemma. Harvard Law Review 2012, 126. [Google Scholar]
- Kosta, E. Consent in European Data Protection Law; Martinus Nijhoff Publishers, 2013.
- Article 29 Data Protection Working Party. Article 29 Data Protection Working Party comments in response to W3C’s public consultation on the W3C Last Call Working Draft, , Tracking Preference Expression (DNT). 24 April.
- Directive 2002/58/EC of the European Parliament and of the Council of concerning the processing of personal data and the protection of privacy in the electronic communications sector (Directive on privacy and electronic communications), 2002. 12 July.
- Legea 506/2004 Privind Prelucrarea Datelor cu Caracter Personal si Protectia Vietii Private in Sectorul Comunicatiilor Electronice.
- Article 29 Data Protection Working Party. WP 29 Working Document on the processing of personal data relating to health in electronic health records (EHR).
- Nissenbaum, H. Privacy as Contextual Integrity. Washington Law Review 2004, 79, 119. [Google Scholar]
- Pandit, H.J.; Esteves, B. Enhancing Data Use Ontology (DUO) for Health-Data Sharing by Extending it with ODRL and DPV. Under Revision in the Semantic Web Journal 2023. [Google Scholar]
- Colnago, J.; Cranor, L.F.; Acquisti, A.; Stanton, K.H. Is it a concern or a preference? In An investigation into the ability of privacy scales to capture and distinguish granular privacy constructs. In Proceedings of the 18th Symposium on Usable Privacy and Security (SOUPS 2022); 2022; pp. 331–346. [Google Scholar]
- Sheehan, M. Can Broad Consent be Informed Consent? Public Health Ethics 2011, 4, 226–235. [Google Scholar] [CrossRef] [PubMed]
- Article 29 Data Protection Working Party. Guidelines on Transparency under Regulation 2016/679, 2018.
- European Data Protection Board. Guidelines 07/2020 on the concepts of controller and processor in the GDPR, 2020.
- Woolley, J.P.; Kirby, E.; Leslie, J.; Jeanson, F.; Cabili, M.N.; Rushton, G.; Hazard, J.G.; Ladas, V.; Veal, C.D.; Gibson, S.J.; et al. Responsible sharing of biomedical data and biospecimens via the “Automatable Discovery and Access Matrix” (ADA-M). npj Genomic Medicine 2018, 3, 1–6. [Google Scholar] [CrossRef] [PubMed]
- European Data Protection Supervisor. A Preliminary Opinion on data protection and scientific research, 2020.
- UK Government. Consultation outcome - Data: a new direction - government response to consultation, 2022.
- Proposal for a REGULATION OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL on the European Health Data Space, 2022.
- EDPB-EDPS Joint Opinion 03/2022 on the Proposal for a Regulation on the European Health Data Space, 2022.
- Dedecker, R.; Slabbinck, W.; Wright, J.; Hochstenbach, P.; Colpaert, P.; Verborgh, R. What’s in a Pod? – A knowledge graph interpretation for the Solid ecosystem. In Proceedings of the Proceedings of the 6th Workshop on Storing, Querying and Benchmarking Knowledge Graphs; pp. 2022327981–96.
- Braun, C.H.J.; Käfer, T. Self-verifying Web Resource Representations Using Solid, RDF-Star and Signed URIs. In Proceedings of the The Semantic Web: ESWC 2022 Satellite Events; Groth, P.; Rula, A.; Schneider, J.; Tiddi, I.; Simperl, E.; Alexopoulos, P.; Hoekstra, R.; Alam, M.; Dimou, A.; Tamper, M., Eds. Springer International Publishing, Lecture Notes in Computer Science; 2022; pp. 138–142. [Google Scholar] [CrossRef]
- Article 29 Data Protection Working Party. Opinion 03/2013 on purpose limitation, 2013.
- Charter of Fundamental Rights of the European Union, 2000.
| 1 | Trust has been proven as an important factor that positively influences the perceived usefulness and ease of use of digital personal datastores [8]. |
| 2 | |
| 3 | Beatriz Esteves is the lead author of this work. |
| 4 | |
| 5 | |
| 6 | |
| 7 | |
| 8 | |
| 9 | |
| 10 | |
| 11 | |
| 12 | |
| 13 | |
| 14 | |
| 15 | |
| 16 | |
| 17 | |
| 18 | |
| 19 | |
| 20 | |
| 21 | |
| 22 | |
| 23 | |
| 24 | |
| 25 | |
| 26 | |
| 27 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).



