Submitted:
04 May 2026
Posted:
04 May 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Conceptual Background
2.1. Mythos-Class AI: An Operational Definition
2.2. The Capability Debate
2.3. Why Blockchain Is Distinctively Exposed
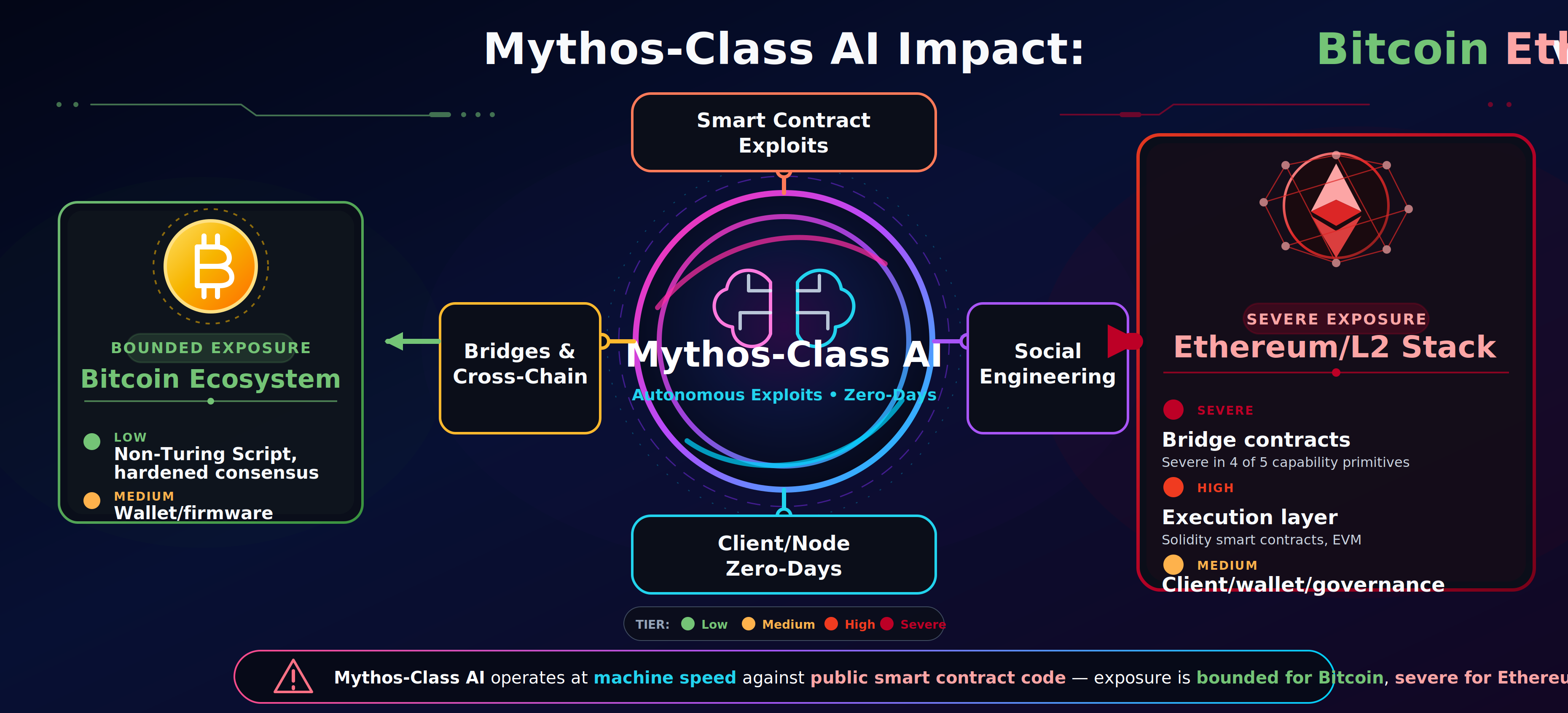
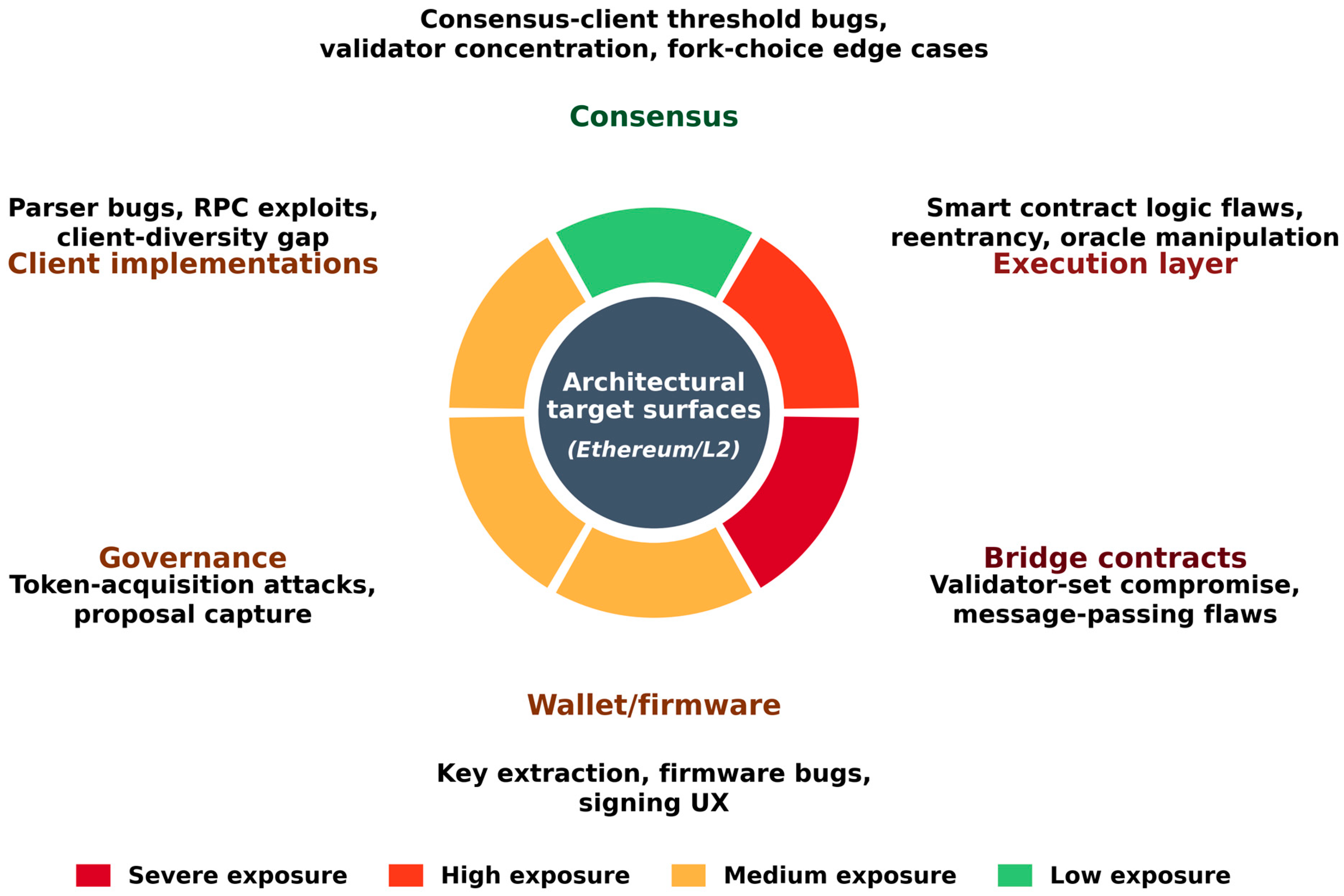
2.4. Bitcoin and Ethereum/L2 Architectural Profiles
3. Analytical Framework
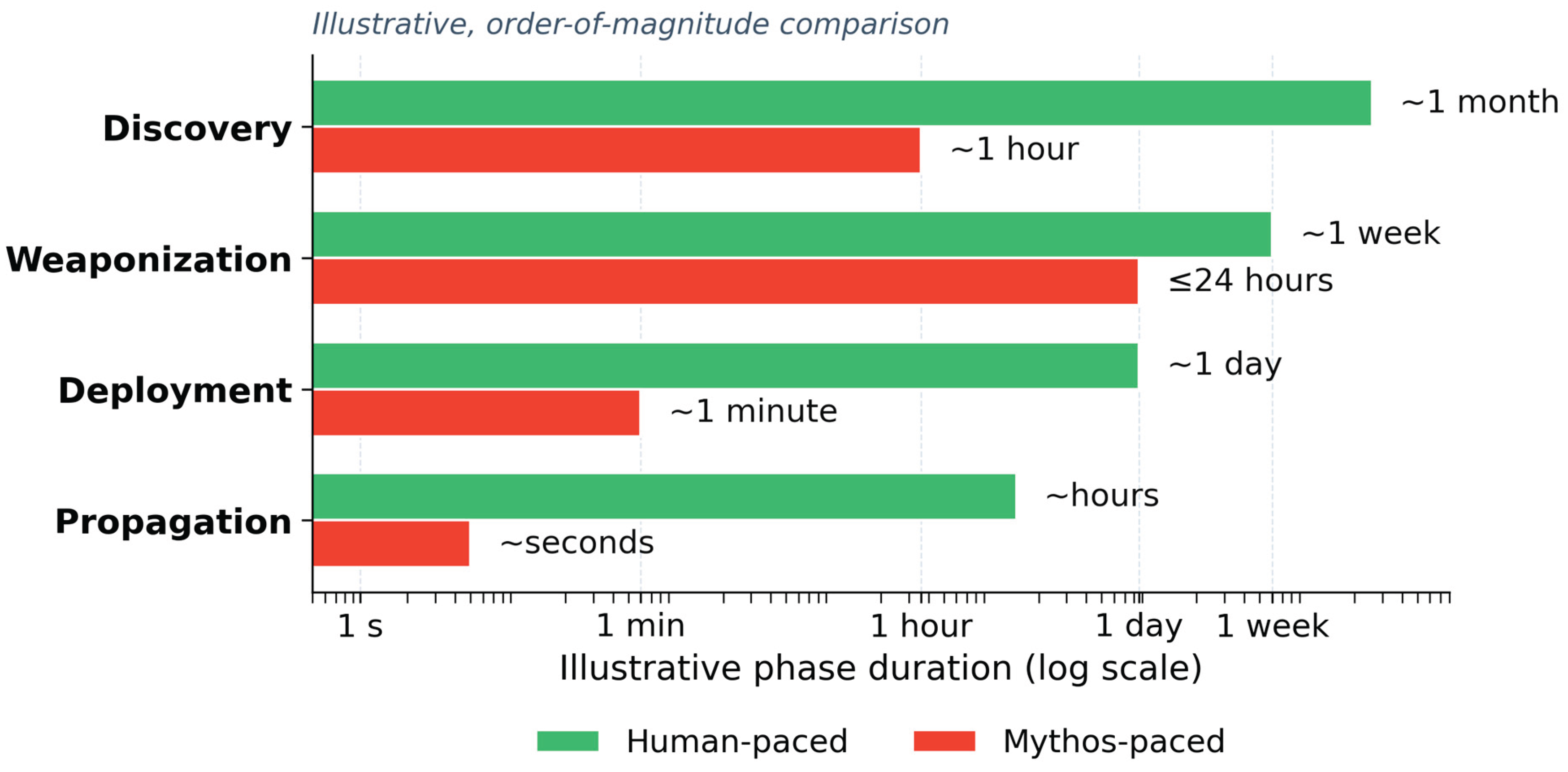
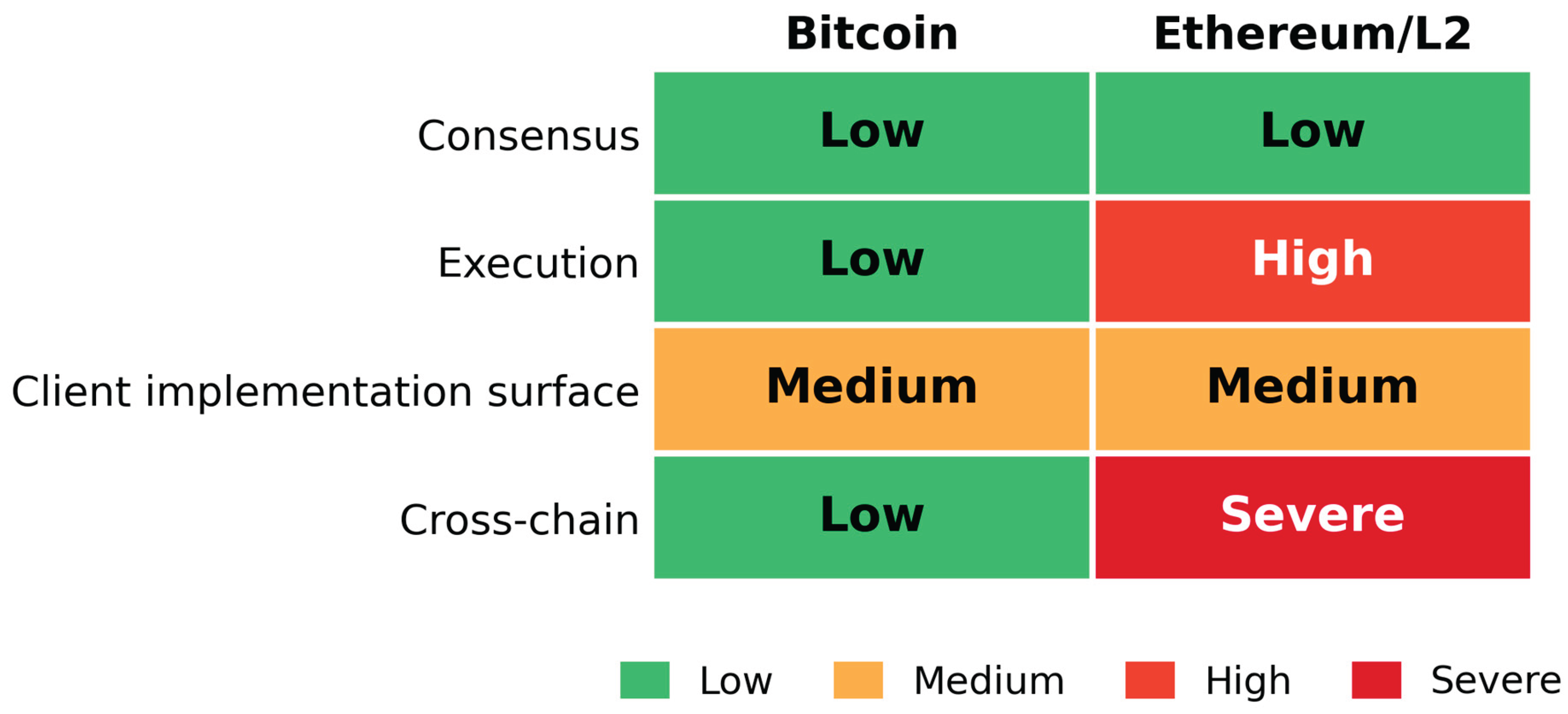
3.1. The Capability-Surface-Impact Matrix
3.1.1. Scoring Criteria
3.2. Threat Modeling Approach
3.3. Assumptions, Boundaries, and Epistemic Position
4. Comparative Analysis: Bitcoin vs Ethereum/L2
4.1. Bitcoin: Bounded Exposure
4.2. Ethereum and the L2 Stack: Expanding Exposure
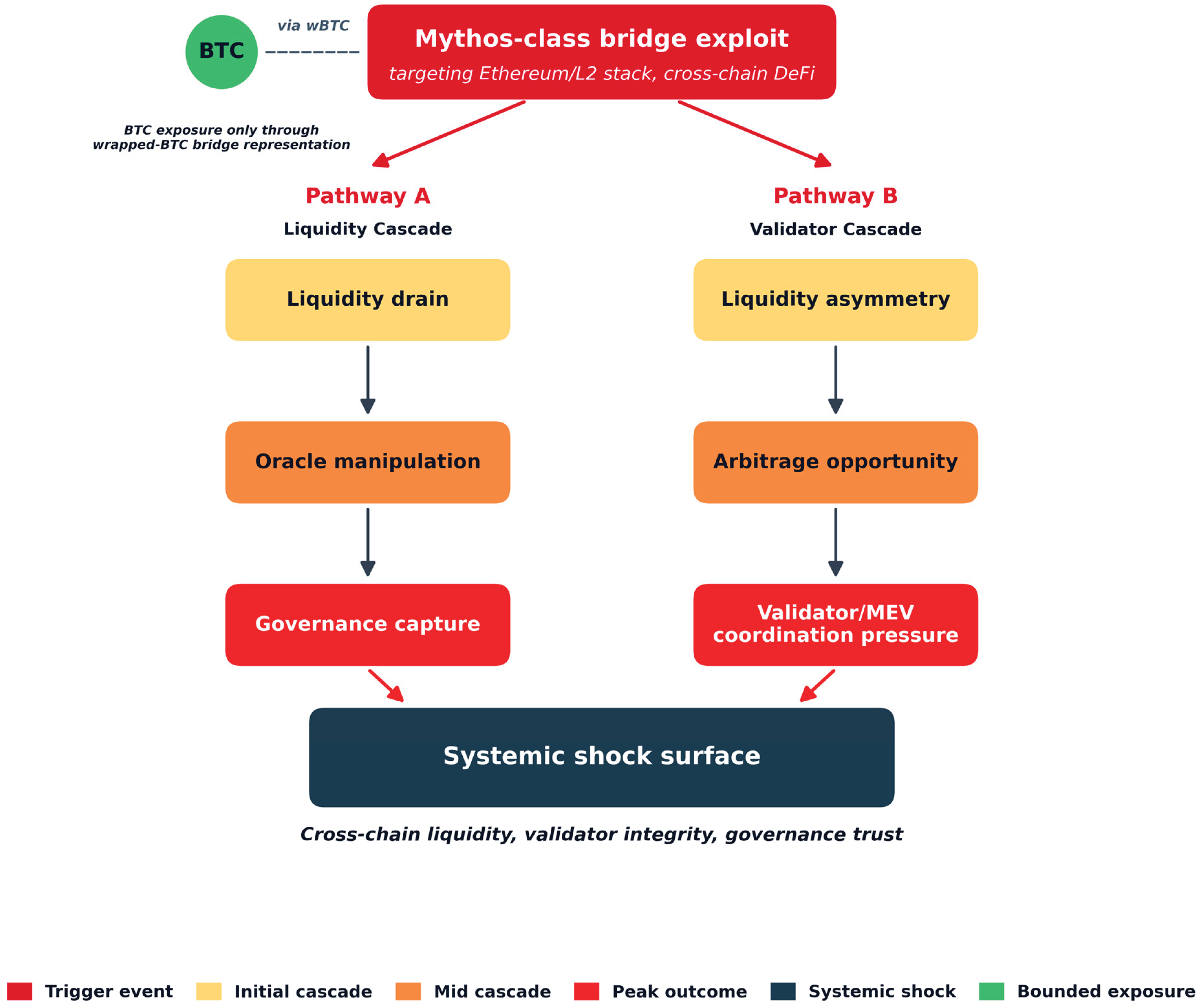
4.3. Bridges as the Mythos-Class Prime Target
4.4. Comparative Synthesis
5. Systemic Risk Implications
5.1. Liquidity Cascades and Composability Failures
5.2. Governance, Validator, and Client-Diversity Risk
5.3. Policy and Regulatory Implications
6. Mitigation and Future Directions
6.1. AI-Aligned Defensive Modernization
6.2. Operational and Governance Hardening
6.3. Audit Cadence and Disclosure Adaptation
6.4. AI-Quantum Convergence as Adjacent Future Work
6.5. Research Agenda
7. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Anthropic. Project Glasswing: Securing critical software for the AI era. 7 April 2026. Available online: https://www.anthropic.com/glasswing (accessed on 3 May 2026).
- Kahn, J. Anthropic ‘Mythos’ AI model representing ‘step change’ in capabilities, leaked documents reveal. Fortune. 26 March 2026. Available online: https://fortune.com/2026/03/26/anthropic-says-testing-mythos-powerful-new-ai-model (accessed on 3 May 2026).
- UK AI Security Institute. Our evaluation of Claude Mythos Preview's cyber capabilities. AISI Blog. 13 April 2026. Available online: https://www.aisi.gov.uk/blog/our-evaluation-of-claude-mythos-previews-cyber-capabilities (accessed on 3 May 2026).
- Gilbert + Tobin. How Mythos-class AI is changing cyber security risk. April 2026. Available online: https://www.gtlaw.com.au/insights/how-mythos-class-ai-is-changing-the-cyber-security-risk (accessed on 3 May 2026).
- UK Parliament Treasury Committee. Bank of England and FCA commit to action on AI following warnings from MPs. 16 April 2026. Available online: https://committees.parliament.uk/committee/158/treasury-committee/news/213162/bank-of-england-and-fca-commit-to-action-on-ai-following-warnings-from-mps/ (accessed on 3 May 2026).
- Anthropic Red Team. Assessing Claude Mythos Preview's cybersecurity capabilities. 7 April 2026. Available online: https://red.anthropic.com/2026/mythos-preview/ (accessed on 3 May 2026).
- AISLE. AI cybersecurity after Mythos: The jagged frontier. April 2026. Available online: https://aisle.com/blog/ai-cybersecurity-after-mythos-the-jagged-frontier (accessed on 3 May 2026).
- Halborn. Explained: The Wormhole hack (February 2022). Halborn Blog. February 2022. Available online: https://www.halborn.com/blog/post/explained-the-wormhole-hack-february-2022 (accessed on 3 May 2026).
- Eitzman, R.; Dobson, J. Decentralized robbery: Dissecting the Nomad Bridge hack and following the money. Mandiant / Google Cloud Threat Intelligence. 29 November 2022. Available online: https://cloud.google.com/blog/topics/threat-intelligence/dissecting-nomad-bridge-hack (accessed on 3 May 2026).
- Buterin, V. Ethereum: A next-generation smart contract and decentralised application platform. Ethereum White Paper. 2014. Available online: https://ethereum.org/en/whitepaper/ (accessed on 3 May 2026).
- Antonopoulos, A.M. Mastering Bitcoin: Programming the Open Blockchain, 2nd ed.; O’Reilly Media: Sebastopol, CA, USA, 2017. [Google Scholar]
- Wood, G. Ethereum: A secure decentralised generalised transaction ledger. Ethereum Yellow Paper, 2014. Available online: https://ethereum.github.io/yellowpaper/paper.pdf (accessed on 3 May 2026).
- Ethereum Foundation. Nodes and clients: Client diversity. 2024. Available online: https://ethereum.org/developers/docs/nodes-and-clients/client-diversity (accessed on 3 May 2026).
- L2BEAT. Layer 2 ecosystem statistics. 2026. Available online: https://l2beat.com (accessed on 3 May 2026).
- Strom, B.E.; Applebaum, A.; Miller, D.P.; Nickels, K.C.; Pennington, A.G.; Thomas, C.B. MITRE ATT&CK: Design and Philosophy. March 2020. Available online: https://attack.mitre.org/docs/ATTACK_Design_and_Philosophy_March_2020.pdf (accessed on 3 May 2026).
- Shostack, A. Threat Modeling: Designing for Security; Wiley: Indianapolis, IN, USA, 2014; ISBN 978-1-118-80999-0. [Google Scholar]
- Nelson, D. Oasis Exploits Its Own Wallet Software to Seize Crypto Stolen in Wormhole Hack. CoinDesk. 24 February 2023. Available online: https://www.coindesk.com/business/2023/02/24/oasis-exploits-its-own-wallet-software-to-seize-crypto-stolen-in-wormhole-hack (accessed on 3 May 2026).
- Sky Mavis. Back to building: Ronin security breach postmortem. Ronin Blog. 27 April 2022. Available online: https://roninchain.com/blog/posts/back-to-building-ronin-security-breach-6513cc78a5edc1001b03c364 (accessed on 3 May 2026).
- Elliptic. North Korea’s Lazarus Group identified as exploiters behind $540 million Ronin bridge heist. Elliptic Blog. 14 April 2022. Available online: https://www.elliptic.co/blog/540-million-stolen-from-the-ronin-defi-bridge (accessed on 3 May 2026).
- SlowMist Security Team. Ronin exploit, largest crypto hack to date. SlowMist Medium. 27 April 2022. Available online: https://slowmist.medium.com/ronin-exploit-largest-crypto-hack-to-date-8b7c581e38fd (accessed on 3 May 2026).
- CertiK. Wormhole bridge exploit incident analysis. CertiK Blog. February 2022. Available online: https://www.certik.com/resources/blog/wormhole-bridge-exploit-incident-analysis (accessed on 3 May 2026).
- Jeyakumar, P.; et al. Nomad Bridge incident analysis. Coinbase Blog. August 2022. Available online: https://www.coinbase.com/blog/nomad-bridge-incident-analysis (accessed on 3 May 2026).
- CertiK. Nomad bridge exploit incident analysis. CertiK Blog. August 2022. Available online: https://www.certik.com/blog/nomad-bridge-exploit-incident-analysis (accessed on 3 May 2026).
- Kraken Security Labs. Abusing smart contracts to steal $600 million: How the Poly Network hack actually happened. Kraken Blog. August 2021. Available online: https://blog.kraken.com/product/security/abusing-smart-contracts-to-steal-600-million-how-the-poly-network-hack-actually-happened (accessed on 3 May 2026).
- Financial Stability Board. The Financial Stability Risks of Decentralised Finance. 16 February 2023. Available online: https://www.fsb.org/2023/02/the-financial-stability-risks-of-decentralised-finance/ (accessed on 3 May 2026).
- Halborn. Explained: The Beanstalk Hack (April 2022). Halborn Blog, April 2022. Available online: https://www.halborn.com/blog/post/explained-the-beanstalk-hack-april-2022 (accessed on 3 May 2026).
- Financial Stability Board and International Monetary Fund. G20 Crypto-asset Policy Implementation Roadmap: Status Report. October 2024. Available online: https://www.fsb.org/2024/10/g20-crypto-asset-policy-implementation-roadmap-status-report/ (accessed on 3 May 2026).
- Campbell, R.E., Sr. Evaluation of post-quantum distributed ledger cryptography. J. Br. Blockchain Assoc. 2019, 2, 1–8. [Google Scholar] [CrossRef] [PubMed]
- Campbell, R., Sr. Hybrid post-quantum signatures for Bitcoin and Ethereum: A protocol-level integration strategy. J. Br. Blockchain Assoc. Published online 12 December 2025. 2026, 9. [Google Scholar] [CrossRef] [PubMed]
| Capability primitive | Consensus | Execution layer | Client implementations | Bridge contracts | Wallet/firmware | Governance |
| 1. Autonomous discovery at codebase scale | Low | High | Medium | Severe | Medium | Medium |
| 2. Multi-step exploit chaining | Low | High | Medium | Severe | Low | High |
| 3. Agentic execution with tool use | Low | High | Low | Severe | Medium | Medium |
| 4. Sub-day weaponization | Medium | High | Medium | Severe | Medium | Medium |
| 5. Generality across target classes | Low | High | Medium | High | Medium | Medium |
| Rating | Required condition |
| Low | No strong alignment across the three criteria (codebase accessibility, historical exploit precedent, demonstrated capability primitives) |
| Medium | One criterion strongly present |
| High | Two criteria strongly present |
| Severe | All three criteria strongly present, plus an additional gate: high-value targets and low-friction exploitability (public, replayable, deterministic execution with no patch primitive at the deployed-contract layer) |
| Dimension | Ronin (Mar 2022) | Wormhole (Feb 2022) | Nomad (Aug 2022) | Poly Network (Aug 2021) | ||||
| Loss | ~$625M | ~$320–326M | ~$190M | ~$611M | ||||
| Primary vector | Validator key compromise (5-of-9 multisig forged) | Fake sysvar account bypassed signature verification | Init bug (committedRoot = 0x00): messages always verified | Privilege-architecture flaw + selector collision swapped Keeper key | ||||
| Root-cause class | Operational + governance hygiene | On-chain code flaw (Solana / Rust BPF) | On-chain code flaw (Solidity initialization) | On-chain code flaw (Solidity privilege architecture) | ||||
| Replayability / crowd-loot | Not replayable (key-dependent) | Not trivially replayable | Trivially replayable — ~300 addresses, 960 tx, ~150 min | Not replayable post-exploit | ||||
| Resolution | Sky Mavis covered losses; validator set expanded | Jump Crypto replaced 120k wETH; $140M counter-recovered Feb 2023 [17] | ~$33–37M returned by white-hats; majority unrecovered | All funds returned by attacker | ||||
| Key supporting sources | [18,19,20] | [8,21] | [9,22,23] | [24] | ||||
| Dimension | Ronin (Mar 2022) | Wormhole (Feb 2022) | Nomad (Aug 2022) | Poly Network (Aug 2021) | ||||
| Code-reading capability required | Low (social-engineering-led) | High (Solana sysvar / Rust BPF) | Medium–High (proxy upgrade + Solidity storage defaults) | Very High (multi-contract privilege graph + selector preimage search) | ||||
| Mythos primitives most relevant | Agentic execution (recon, social engineering) | Autonomous discovery + multi-step chaining | Autonomous discovery + agentic execution (crowd-loot amplification) | Autonomous discovery + multi-step chaining (multi-contract reasoning) | ||||
| Mythos-class uplift assessment | Medium — improves social-engineering yield but not the discriminator | Severe — sub-day discovery from public diff is paradigmatic | Severe — collapses the 6-week discovery window | Severe — multi-contract reasoning is core demonstrated capability | ||||
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




