Submitted:
16 April 2026
Posted:
21 April 2026
You are already at the latest version
Abstract
Keywords:
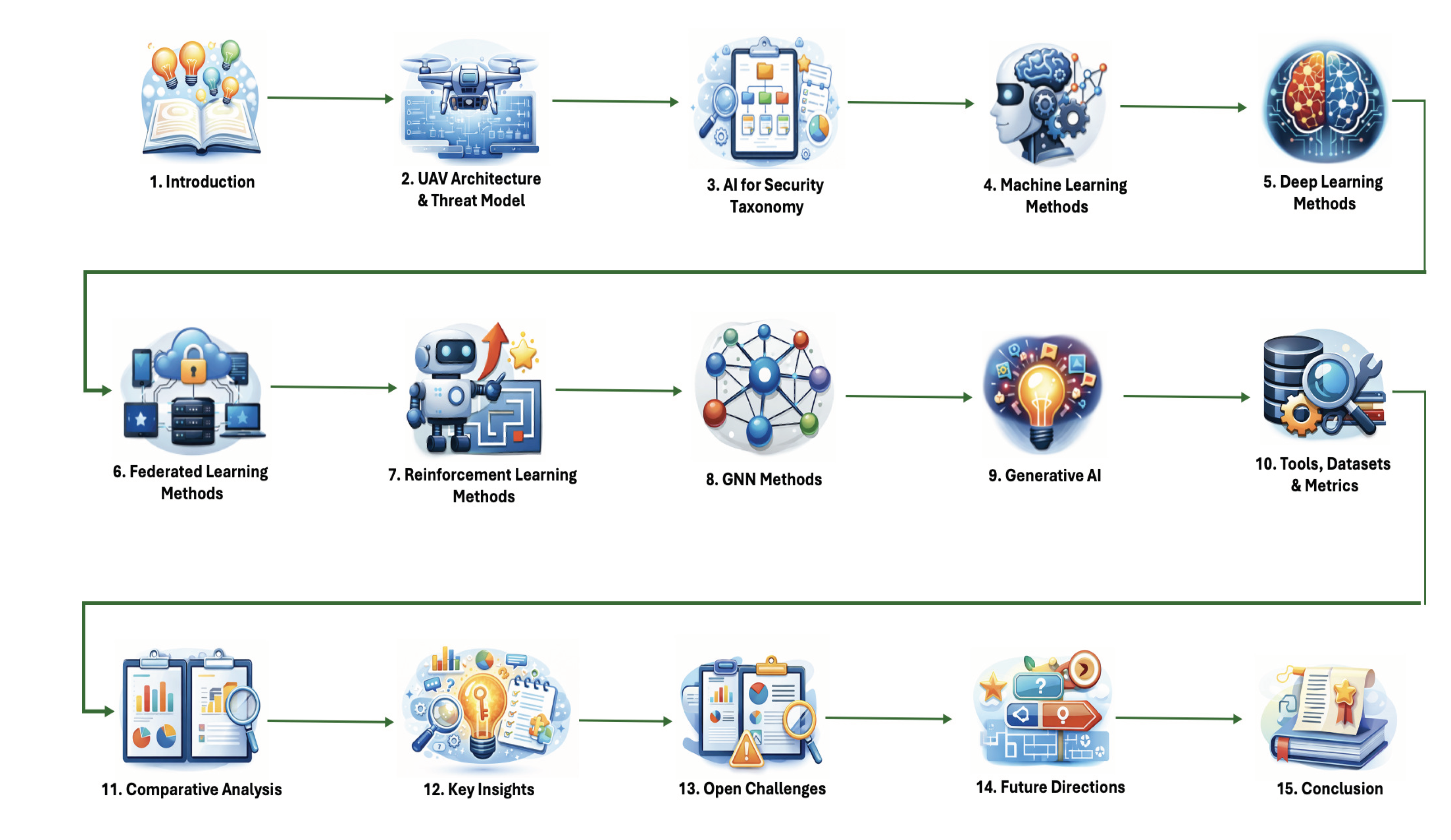
1. Introduction
- We developed a novel taxonomy to classify the AI research used for securing UAVs, which goes beyond classical machine learning and deep learning to cover emerging fields such as federated & reinforcement learning along with GNN and generative AI.
- We proposed a refined taxonomy of UAV threats according to its layered stack.
- We described the tools, datasets and evaluation metrics used as part of the AI research for securing UAV operations.
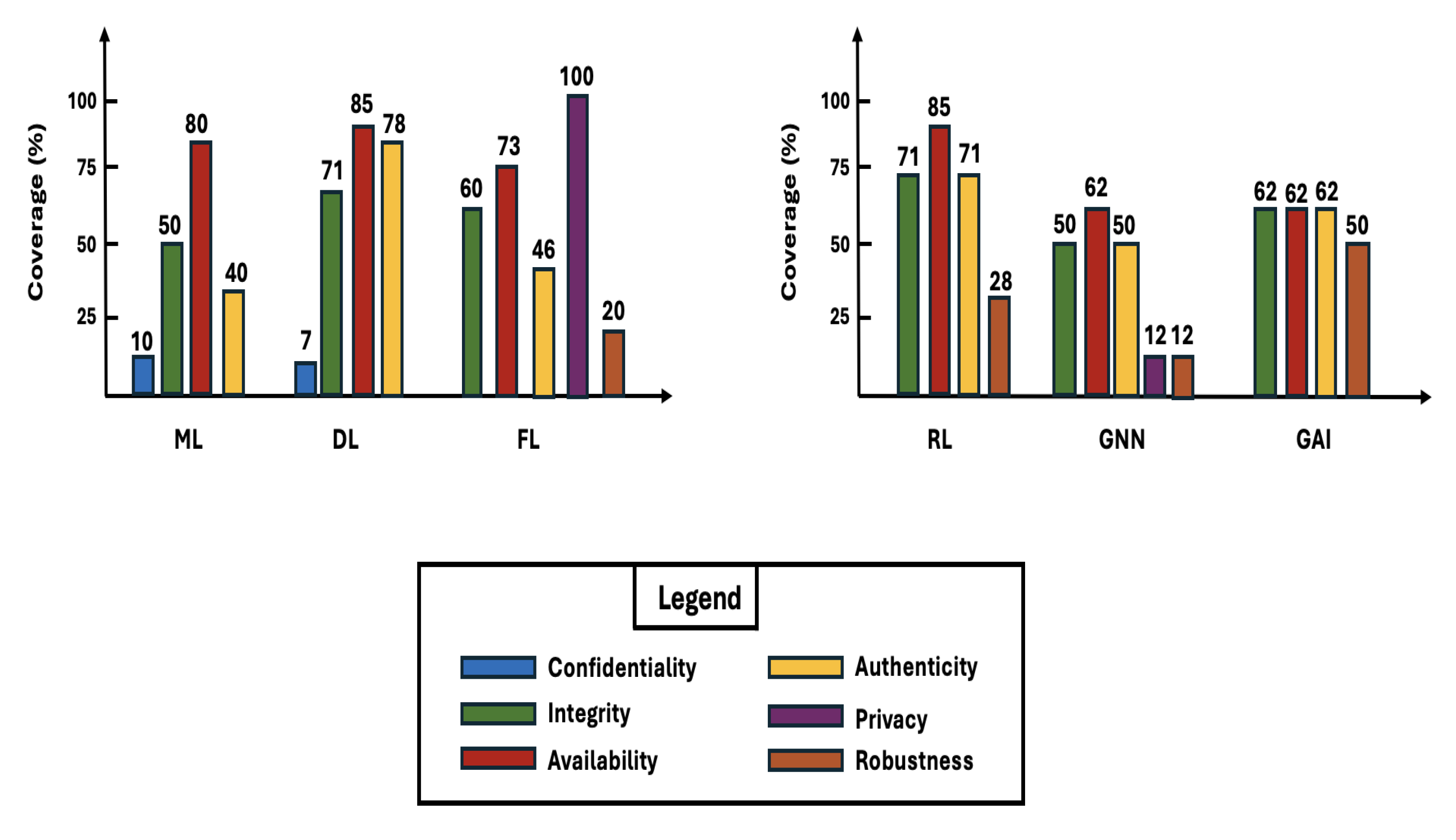
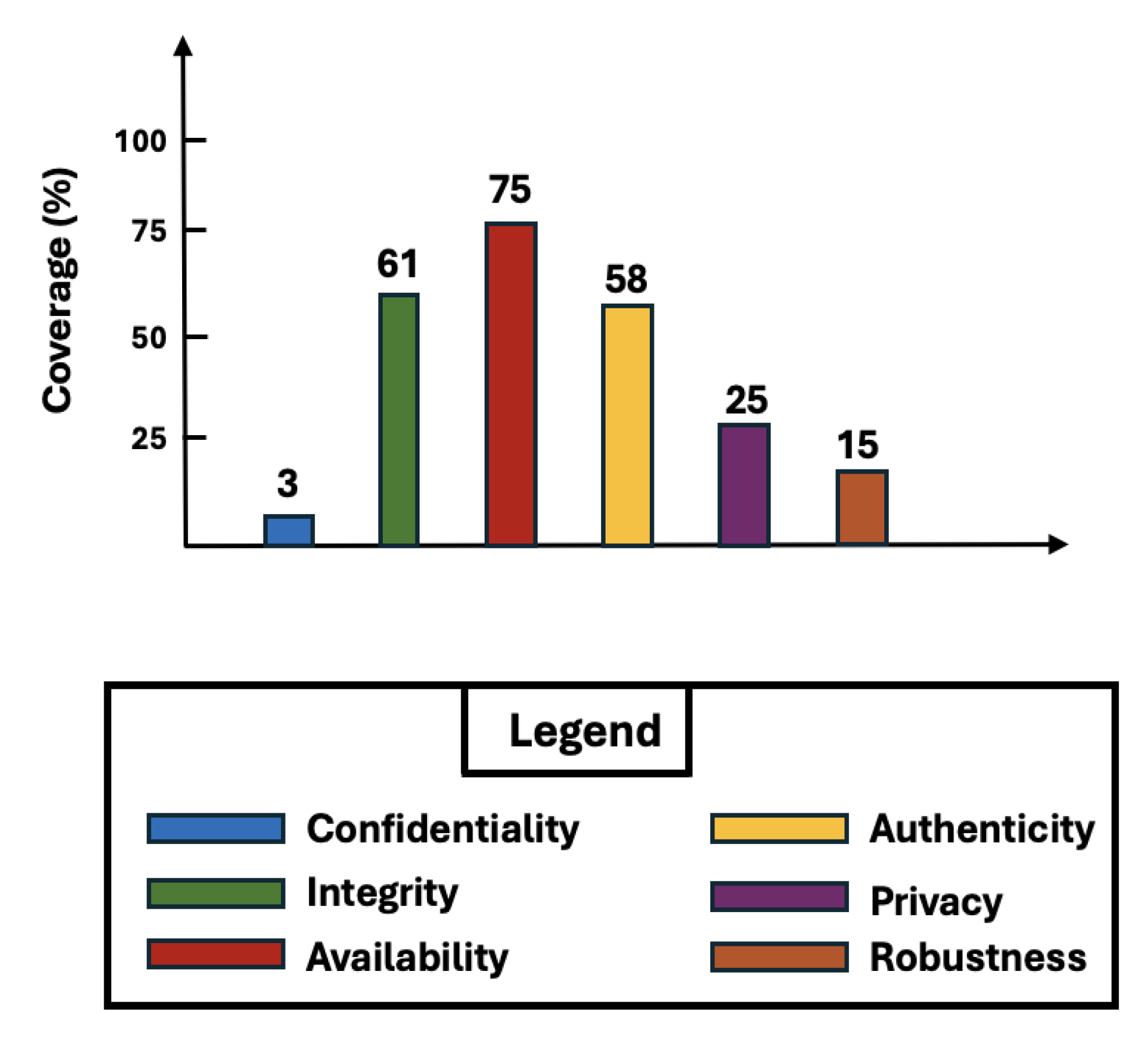
- We highlighted the key insights from our survey by discussing the statistics of coverage of security properties by AI method type versus overall.
- We discussed open challenges and future directions in UAV security using AI.
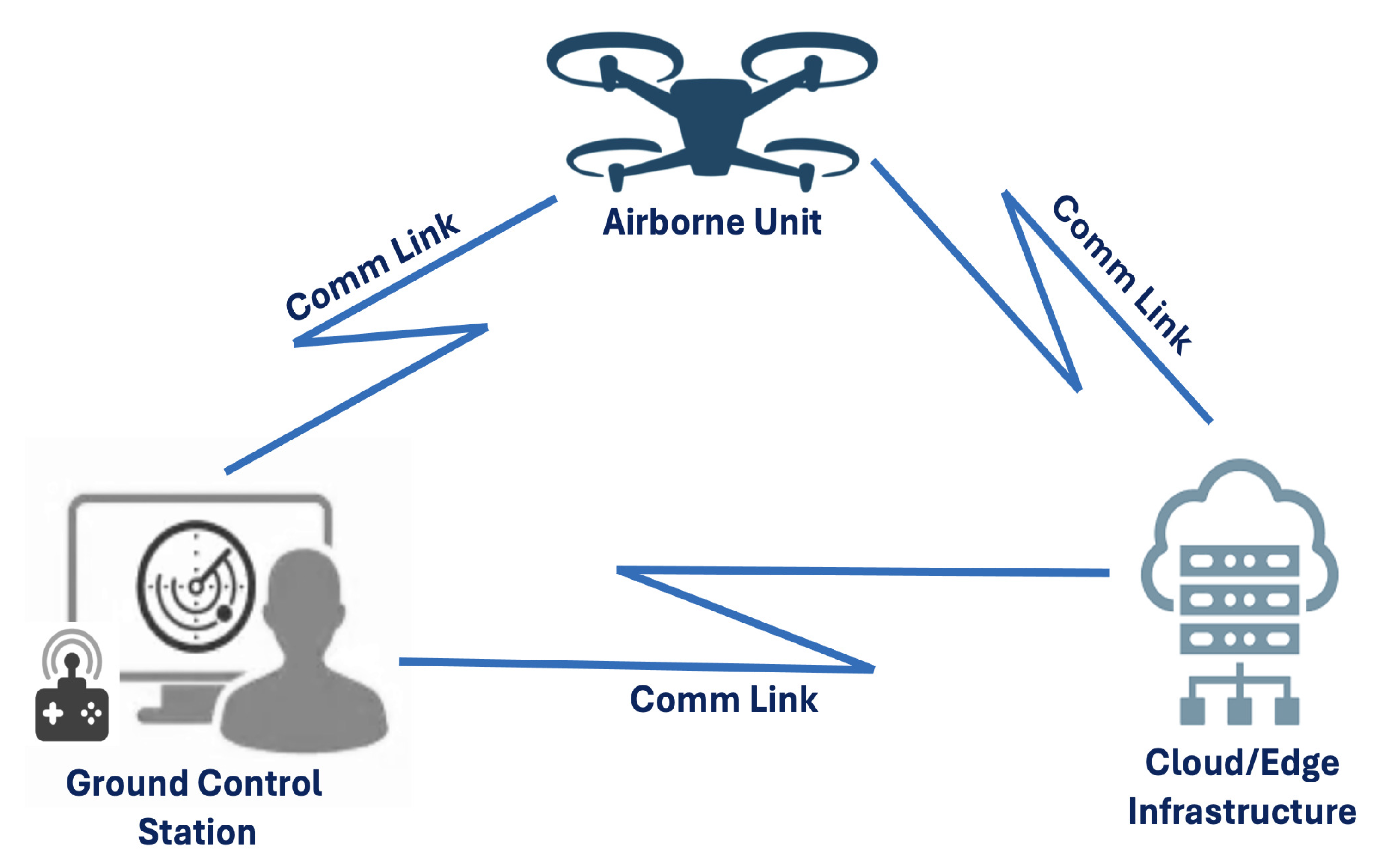
2. UAV Architecture & Threat Model
2.1. UAV Architecture
- Airborne Unit: The physical drone platform includes flight control systems, sensors (GPS, IMU, cameras, and LiDAR), actuators, and mission-specific payloads.
- Ground Control Station (GCS): Interfaces that allow human operators to monitor and control UAVs, send commands, and receive telemetry data.
- Communication Links: Wireless channels (usually radio frequency) are utilized for control, telemetry, video transmission, and swarm coordination among UAVs.
- Cloud or Edge Infrastructure: Some modern unmanned aerial vehicles use cloud-based platforms or adjacent edge servers for computing offloading, data analysis, or fleet coordination.
2.2. Threat Taxonomy in UAV Systems
-
Physical Layer:
- –
- RF Jamming: overwhelms any radio-based communication between the UAV and the GCS by sending high power noise signal on the same frequency.
- –
- Sensor Manipulation: is done by tampering with the inertial and perception sensors used by UAVs to force erroneous state estimations.
- –
- Actuator Manipulation: can be done via various techniques such as signal injection, interference, power disruption and physical tampering.
-
Communication Layer:
- –
- DoS/DDoS: DoS and DDoS attacks aim to overwhelm the UAV’s communication or computing capabilities. This could result in high latency, diminished mission performance, or even a total loss of control.
- –
- MiTM: In MitM scenarios, attackers intercept and manipulate communication between the UAV and the GCS. This facilitate the occurrence of other attacks such as command hijacking, telemetry injection, and illegal access to control channels.
- –
- Message Injection: include leveraging vulnerabilities in widely used protocols in UAV communication to inject malicious data. This includes but is not limited to ADS-B and MAVLink.
-
Navigation Layer
- –
- GPS Spoofing: GPS spoofing [26] entails sending deceptive signals to confuse the UAV’s navigation system, potentially resulting in route diversion or collisions.
- –
- Sensor Fusion Attacks: represents a stealthier version of sensor manipulation as it can evade sensor fusion algorithms such as Kalman Filter.
-
Control Layer:
- –
- Command Injection: leverages vulnerabilities in drone software or communication links in order to take partial or full control of the UAV
- –
- Command Suppression: happens when the attacks injects higher priority or conflicting commands thus overriding the legitimate one sent from GCS.
-
Application Layer:
- –
- Malware: represents any malicious code deployed within the UAV ecosystem to perform malicious actions affecting mostly UAV applications such as mission planning and AI modules.
- –
- Data Poisoning: occurs during training by injecting malicious entries to corrupt the UAV learning mechanism. It occurs during offline or federated training.
- –
- Model Evasion: occurs during runtime inference by injecting adversarial inputs by leveraging lack of robustness that leads to misleading the AI models.
- –
- Software Exploitation: Vulnerabilities in UAV operating systems, firmware, or onboard apps can be used to acquire persistent access, elevate privileges, or disable security features. Once compromised, attackers may maintain covert control over the UAV.
3. Taxonomy of AI Methods for UAV Security
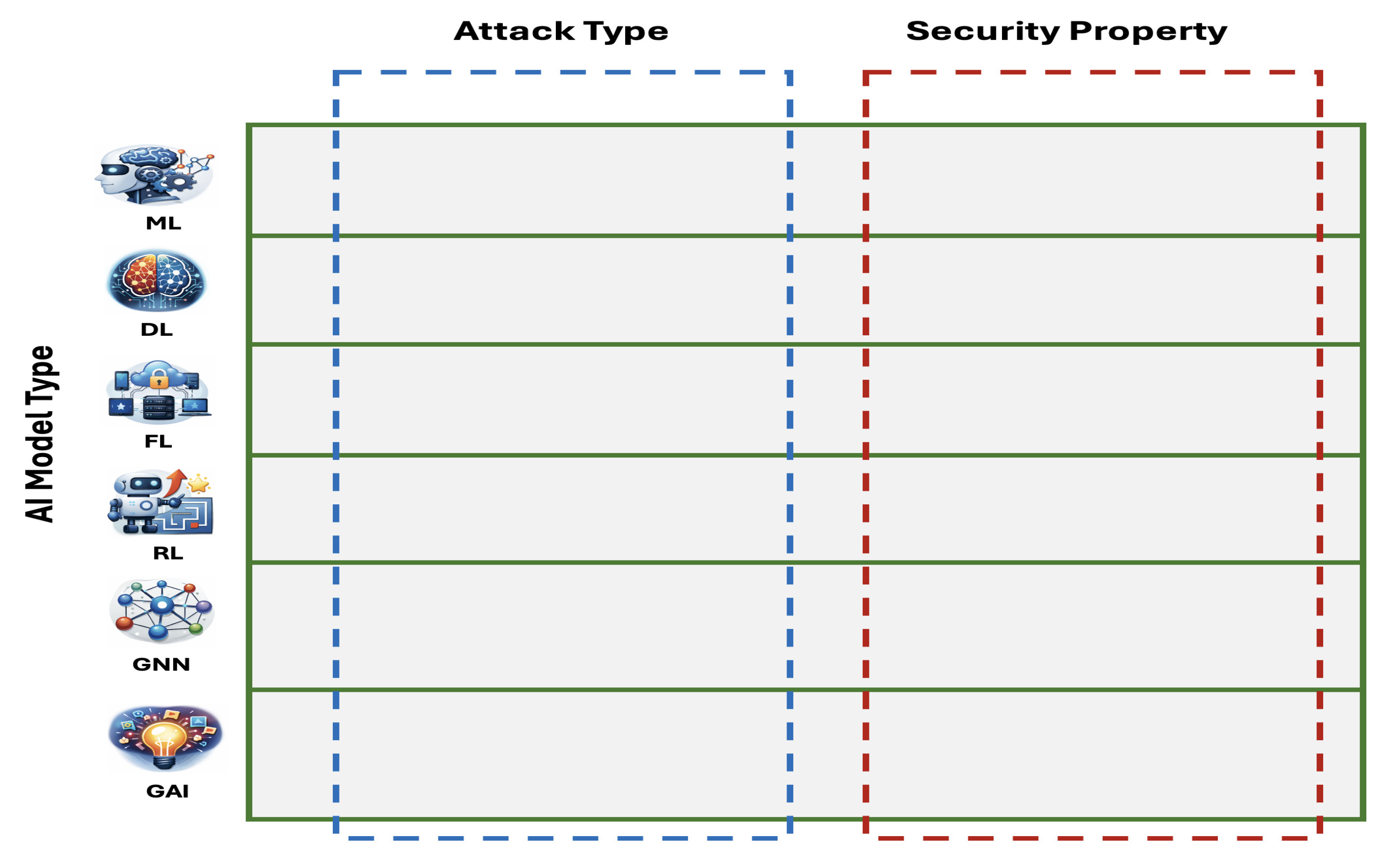
- AI Model Type: this is the main dimension covering all variety of traditional AI models such as ML and DL, and more advanced ones such as FL, RL, GNN and GAI.
- Attack Type: this is the second dimension that covers the cyber attacks thwarted by the AI models in each model type. These attacks are further refined according to the functional UAV layer, i.e. physical layer, communication layer, navigation layer, control layer and application layer.
- Security Property: this is the final dimension, which covers the security properties enforced by the proposed works in each AI model category.
- Publication year: we considered recent papers published between 2020 and 2025.
- Reputable publication venue: IEEE, ACM, Elsevier, Springer, MDPI, or similar journals and/or conferences.
- Scope: directly related to AI methods used for UAV security.
4. Machine Learning Methods
5. Deep Learning Methods
6. Federated Learning Methods
7. Reinforcement Learning Methods
8. Graph Neural Network Methods
9. Generative AI Methods
10. Tools, Datasets & Metrics
11. Comparative Analysis
- Cross-dataset evaluation: almost every work presents findings from a single dataset or simulation environment, raising worries about overfitting and domain specificity. Few studies examined their models across heterogeneous UAV traffic datasets or test applicability to unknown environments—an critical prerequisite for real-world UAV deployments in which operational conditions vary greatly.
- Explainability: while some research use attention processes or feature selection strategies, very few provide interpretable explanations for why a model flags specific telemetry patterns or communication anomalies. This disparity is especially concerning for safety-critical systems like as UAVs, where trust and openness are required.
- Adversarial perturbations: denoising autoencoders, and robustness to faked signals, most studies do not systematically assess resilience to adaptive attacks, data poisoning, physical-layer manipulations, or packet-loss situations. RL studies frequently examine robustness through simulation, however these scenarios seldom mimic the complexities of real wireless environments. Similarly, DL and MTL techniques generally presuppose clean, completely labeled datasets, which are rarely met in practice.
- Reproducibility: most research lack publicly available code, rely on proprietary UAV datasets, or leave out critical information regarding pre-processing, feature extraction, or hyperparameter tweaking. RL-based works rely on proprietary simulation setups, whereas many transformer/GNN-driven frameworks require domain-specific graph structures or non-standardized multi-view input formats. Even when datasets are made public, preparation procedures vary so greatly that identical models may give different findings across research. These constraints highlight the urgent need for consistent datasets, uniform evaluation methodologies, explainable intrusion detection algorithms, and robustness tests that are representative of real-world UAV communication scenarios. Without these enhancements, claimed performance measurements, no matter how good, will be difficult to compare, confirm, or trust in mission-critical UAV security deployments.
12. Key Insights
13. Open Challenges
- Data scarcity: is one of the most fundamental constraints in all techniques. Many UAV-specific datasets, such as GPS spoofing logs, UAVCAN traffic, aerial computing telemetry, or custom RF fingerprints, are extremely small, confidential, or gathered under limited circumstances. Classical machine learning techniques, such as MAVIDS, rely purely on telemetry, whereas many DL- and RL-based algorithms require vast amounts of different training data to avoid overfitting. Even multitask learning frameworks, which normally benefit from shared supervision across tasks, are constrained by the amount and diversity of UAV attack datasets, particularly for hybrid, multi-stage, and zero-day threats. Generative AI has showed promise for developing synthetic attack data, but there are still concerns about distribution fidelity, temporal consistency, and the risk of increasing dataset biases.
- Real-time Constraints: present significant deployment issues. UAV platforms have limited onboard computing, memory, and energy resources, but must detect and respond to assaults with millisecond latency. Although many works, such as distributed IDS designs (e.g., E-DIDS), lightweight fuzzy rough set systems, and pruned deep networks (UAV-DiPNID), significantly reduce inference time, more complex methods, such as GNNs, RL agents, and multi-view MTL architectures, continue to struggle to meet hard real-time deadlines in flight. Reinforcement learning and MTL models are more adaptable, but their inference pipelines might be computationally demanding without additional optimization, model reduction, or hardware acceleration.
- Explainability: remains weak across nearly all surveyed methodologies. Classical machine learning techniques (e.g., PCA-based anomaly detection, decision trees, and SVMs) allow for partial interpretation, but most deep models including CNN-LSTMs, transformers, GNNs, multi-view architectures, and RL policies—function as black boxes. Only a few efforts explicitly incorporate explainability, such as the explainable DRL adversarial detection framework that employs APF and PER. However, the bulk of cutting-edge systems cannot provide practical explanations for why an assault was identified, what variables influenced the conclusion, or how the UAV should change its behavior. This gap is significant in safety-critical aviation contexts where human operators require transparency and verified logic.
- Adversarial robustness: is another big outstanding topic. Deep learning-based IDS models, such as CNNs, LSTMs, transformers, and GNNs, are especially susceptible to evasion attacks, perturbation-based spoofing, and idea drift. While a few studies have examined adversarial settings (e.g., DRL agents tested against adversarial perturbations, denoising autoencoder-enhanced IDSs), the majority of studies continue to assume clean or stationary data distributions. UAV networks are dynamic and vulnerable to hostile actors capable of jamming, replaying, model poisoning, and RF fingerprint obfuscation. Without thorough robustness studies, IDS performance on static datasets may not be consistent with real-world resilience.
- Absence of set benchmarks: greatly hinders the comparability and repeatability of investigations. The datasets used in UAV intrusion detection research are inconsistent: NSL-KDD, UNSW-NB15, AWID, WSN-BFSF, KDD-CUP99, CSE-CIC IDS2018, CIC-DDoS2019, UAVCAN logs, RF fingerprint datasets, simulated COOJA traffic, and custom flight logs. Many UAV-focused datasets are private, corporate, or simulator-generated, making it impossible to replicate results. Metrics such as accuracy, F1, recall, fall-out rate, latency, energy consumption, and robustness margins vary greatly, making cross-paper comparisons useless. Multitask learning systems complicate evaluation by introducing many objectives (e.g., anomaly detection, device identification, attack classification) with no consistent reporting requirements.
14. Future Directions
- Federated MTL: due to the heterogeneous and distributed nature of UAV systems, federated MTL is a promising solution that leverages shared representation with different task-specific heads. This can deal with intermittent client participation that is common in UAV swarms, non-IID data distribution while performing all tasks jointly thus making models less complex and potentially more efficient. Challenges in implementing such solution include dealing with data poisoning, integration with differential privacy and handling communication constraints.
- Digital Twins: can be very beneficial in replicating UAV systems thus aiding in simulating attacks and validating defense mechanisms. The benefits include bundling the cyber, physical and AI dimension together facilitating real-time communication between the UAV and its twin while the possibility of being integrated with RL paradigm. Challenges include dealing with the tradeoff between fidelity and computational cost of such solution, and the ability of accurately model the noise.
- Benchmark Creation: most existing datasets are fragmented and non-reproducible making the creation of open and curated benchmark a pressing need. Some of the key requirements for such benchmarks is that they have to cover attacks from various layers, multi-modal data and realistic UAV protocols such as ADS-B and MAVLink. Challenges include dealing with distributed and federated environments in addition to including and dealing with adversarial attacks.
- Trustworthy AI for UAV Security: the issue with current black-box AI models is that they lack trust in dealing with safety-critical use cases. Some research direction include leveraging explainable AI in making attack detection decisions. Also, another interesting research direction is predicting attacks with high confidence even in the presence of adversarial attacks. In addition, with the rise of popular risk frameworks, such as NIST AI Risk Management Frameworks, it is needed to seamlessly align trustworthy AI solution for UAV security with them. Balancing robustness, explainability and real-time constraints represent the key challenges.
15. Conclusion
Author Contributions
Data Availability Statement
Conflicts of Interest
References
- Fahlstrom, P.G.; Gleason, T.J.; Sadraey, M.H. Introduction to UAV systems; John Wiley & Sons, 2022. [Google Scholar]
- Fan, B.; Li, Y.; Zhang, R.; Fu, Q. Review on the technological development and application of UAV systems. Chinese Journal of Electronics 2020, 29(2), 199–207. [Google Scholar] [CrossRef]
- Zhi, Yueyan; Fu, Zhangjie; Sun, Xingming; Yu, Jingnan. Security and privacy issues of UAV: A survey. Mobile Networks and Applications 2020, 25(no. 1), 95–101. [Google Scholar] [CrossRef]
- Kacem, T.; Barreto, A.; Wijesekera, D.; Costa, P. ADS-Bsec: A novel framework to secure ADS-B. ICT Express 2017, 3(4), 160–163. [Google Scholar] [CrossRef]
- Sarkar, N.I.; Gul, S. Artificial intelligence-based autonomous UAV networks: A survey. Drones 2023, 7(5), 322. [Google Scholar] [CrossRef]
- Cordill, B.; Fang, D.; Xu, S. A Comprehensive Survey of Security and Privacy in UAV Systems. IEEE Access 2025, 13, 117843–117866. [Google Scholar] [CrossRef]
- Tsao, K.-Y.; Girdler, T.; Vassilakis, V. G. A Survey of Cyber Security Threats and Solutions for UAV Communications and Flying Ad-Hoc Networks. Ad Hoc Networks 2022, 133, 102894. [Google Scholar] [CrossRef]
- Rahman, K.; Aziz, M. A.; Kashif, A. U.; Cheema, T. A. Detection of Security Attacks Using Intrusion Detection System for UAV Networks: A Survey. In Big Data Analytics and Computational Intelligence for Cybersecurity; Ouaissa, M., Boulouard, Z., Ouaissa, M., Khan, I. U., Kaosar, M., Eds.; Springer International Publishing: Cham, 2022; pp. pp 109–123. [Google Scholar] [CrossRef]
- AL-Syouf, R. A.; Bani-Hani, R. M.; AL-Jarrah, O. Y. Machine Learning Approaches to Intrusion Detection in Unmanned Aerial Vehicles (UAVs). Neural Comput & Applic 2024, 36(29), 18009–18041. [Google Scholar] [CrossRef]
- Bithas, P. S.; Michailidis, E. T.; Nomikos, N.; Vouyioukas, D.; Kanatas, A. G. A Survey on Machine-Learning Techniques for UAV-Based Communications. Sensors 2019, 19(23), 5170. [Google Scholar] [CrossRef]
- Syed, F.; Gupta, S.K.; Hamood Alsamhi, S.; Rashid, M.; Liu, X. A survey on recent optimal techniques for securing unmanned aerial vehicles applications. Transactions on Emerging Telecommunications Technologies 2021, 32(7), e4133. [Google Scholar] [CrossRef]
- Sarıkaya, B. S.; Bahtiyar, Ş. A Survey on Security of UAV and Deep Reinforcement Learning. Ad Hoc Networks 2024, 164, 103642. [Google Scholar] [CrossRef]
- Wang, X.; Zhao, Z.; Yi, L.; Ning, Z.; Guo, L.; Yu, F. R.; Guo, S. A Survey on Security of UAV Swarm Networks: Attacks and Countermeasures. ACM Comput. Surv. 2024, 57(3), 74:1–74:37. [Google Scholar] [CrossRef]
- Adil, M.; Jan, M. A.; Liu, Y.; Abulkasim, H.; Farouk, A.; Song, H. A Systematic Survey: Security Threats to UAV-Aided IoT Applications, Taxonomy, Current Challenges and Requirements With Future Research Directions. IEEE Transactions on Intelligent Transportation Systems 2023, 24(2), 1437–1455. [Google Scholar] [CrossRef]
- Tlili, F.; Ayed, S.; Fourati, L.C. Advancing UAV security with artificial intelligence: A comprehensive survey of techniques and future directions. Internet of Things 2024, 27, 101281. [Google Scholar] [CrossRef]
- Yang, Z.; Zhang, Y.; Zeng, J.; Yang, Y.; Jia, Y.; Song, H.; Lv, T.; Sun, Q.; An, J. AI-Driven Safety and Security for UAVs: From Machine Learning to Large Language Models. Drones 2025, 9(6), 392. [Google Scholar] [CrossRef]
- Abro, G. E. M.; Zulkifli, S. A. B. M.; Masood, R. J.; Asirvadam, V. S.; Laouiti, A. Comprehensive Review of UAV Detection, Security, and Communication Advancements to Prevent Threats. Drones 2022, 6(10), 284. [Google Scholar] [CrossRef]
- Jacobsen, R. H.; Marandi, A. Security Threats Analysis of the Unmanned Aerial Vehicle System. IEEE Military Communications Conference (MILCOM), 2021; pp. pp 316–322. [Google Scholar] [CrossRef]
- Pandey, G. K.; Gurjar, D. S.; Nguyen, H. H.; Yadav, S. Security Threats and Mitigation Techniques in UAV Communications: A Comprehensive Survey. IEEE Access 2022, 10, 112858–112897. [Google Scholar] [CrossRef]
- Fotouhi, A.; Qiang, H.; Ding, M.; Hassan, M.; Giordano, L. G.; Garcia-Rodriguez, A.; Yuan, J. Survey on UAV Cellular Communications: Practical Aspects, Standardization Advancements, Regulation, and Security Challenges. IEEE Communications Surveys & Tutorials 2019, 21(4), 3417–3442. [Google Scholar] [CrossRef]
- Alzubaidi, A. A. Systematic Literature Review for Detecting Intrusions in Unmanned Aerial Vehicles Using Machine and Deep Learning. IEEE Access 2025, 13, 58576–58599. [Google Scholar] [CrossRef]
- Mohsan, S. A. H.; Othman, N. Q. H.; Li, Y.; Alsharif, M. H.; Khan, M. A. Unmanned Aerial Vehicles (UAVs): Practical Aspects, Applications, Open Challenges, Security Issues, and Future Trends. Intel Serv Robotics 2023, 16(1), 109–137. [Google Scholar] [CrossRef]
- Ogab, M.; Zaidi, S.; Bourouis, A.; Calafate, C. T. Machine Learning-Based Intrusion Detection Systems for the Internet of Drones: A Systematic Literature Review. IEEE Access 2025, 13, 96681–96714. [Google Scholar] [CrossRef]
- Sharifi, I.; Ghazanfari, M.; Taye, A.; Wei, P.; Ahmed, M.; Tae Kim, H.; Ghasemi, M.; Gupta, V.; Dahle, N.W.; Canady, R.; Diaz-Gonzalez, A. A Survey of Security Challenges and Solutions for UAS Traffic Management (UTM) and small Unmanned Aerial Systems (sUAS). AIAA SCITECH 2026 Forum, 2026; p. p. 2892. [Google Scholar]
- Umrani, M.I.; Butler, B.; O’Driscoll, A.; Davy, S. Toward Secure Complex UAV Cyber-Physical Systems: A Unified Threat Taxonomy and Cross-Layer Survey of Cybersecurity Challenges. In Internet of Things; 2026; p. 101902. [Google Scholar]
- Chamola, V.; Kotesh, P.; Agarwal, A.; Naren; Gupta, N.; Guizani, M. A Comprehensive Review of Unmanned Aerial Vehicle Attacks and Neutralization Techniques. Ad Hoc Networks 2021, 111, 102324. [CrossRef]
- Zhou, Z.H. Machine learning; Springer nature, 2021. [Google Scholar]
- Whelan, J.; Almehmadi, A.; El-Khatib, K. Artificial Intelligence for Intrusion Detection Systems in Unmanned Aerial Vehicles. Computers and Electrical Engineering 2022, 99, 107784. [Google Scholar] [CrossRef]
- Moustafa, N.; Jolfaei, A. Autonomous Detection of Malicious Events Using Machine Learning Models in Drone Networks. In Proceedings of the 2nd ACM MobiCom Workshop on Drone Assisted Wireless Communications for 5G and Beyond DroneCom ’20; Association for Computing Machinery: New York, NY, USA, 2020; pp. pp 61–66. [Google Scholar] [CrossRef]
- Shafique, A.; Mehmood, A.; Elhadef, M. Detecting Signal Spoofing Attack in UAVs Using Machine Learning Models. IEEE Access 2021, vol. 9, 93803–93815. [Google Scholar] [CrossRef]
- Agnew, D.; Aguila, A. D.; Mcnair, J. Enhanced Network Metric Prediction for Machine Learning-Based Cyber Security of a Software-Defined UAV Relay Network. in IEEE Access 2024, vol. 12, 54202–54219. [Google Scholar] [CrossRef]
- Wu, Y.; Yang, L.; Zhang, L.; Nie, L.; Zheng, L. Intrusion Detection for Unmanned Aerial Vehicles Security: A Tiny Machine Learning Model. IEEE Internet of Things Journal 2024, 11(12), 20970–20982. [Google Scholar] [CrossRef]
- Fu, R.; Ren, X.; Li, Y.; Wu, Y.; Sun, H.; Al-Absi, M. A. Machine-Learning-Based UAV-Assisted Agricultural Information Security Architecture and Intrusion Detection. IEEE Internet of Things Journal 2023, 10(21), 18589–18598. [Google Scholar] [CrossRef]
- Shrestha, R.; Omidkar, A.; Roudi, S. A.; Abbas, R.; Kim, S. Machine-Learning-Enabled Intrusion Detection System for Cellular Connected UAV Networks. Electronics 2021, 10(13), 1549. [Google Scholar] [CrossRef]
- Whelan, J.; Sangarapillai, T.; Minawi, O.; Almehmadi, A.; El-Khatib, K. Novelty-Based Intrusion Detection of Sensor Attacks on Unmanned Aerial Vehicles. In Proceedings of the 16th ACM Symposium on QoS and Security for Wireless and Mobile Networks; Q2SWinet ’20; Association for Computing Machinery: New York, NY, USA, 2020; pp. pp 23–28. [Google Scholar] [CrossRef]
- Cai, Z.; Liu, Z.; Kou, L. Reliable UAV Monitoring System Using Deep Learning Approaches. IEEE Transactions on Reliability 2022, vol. 71(no. 2), 973–983. [Google Scholar] [CrossRef]
- Mehmood, R. T.; Ahmed, G.; Siddiqui, S. Simulating ML-Based Intrusion Detection System for Unmanned Aerial Vehicles (UAVs) Using COOJA Simulator. 2022 16th International Conference on Open Source Systems and Technologies (ICOSST), 2022; pp. pp 1–10. [Google Scholar] [CrossRef]
- Alipour-Fanid, A.; Dabaghchian, M.; Wang, N.; Wang, P.; Zhao, L.; Zeng, K. Machine Learning-Based Delay-Aware UAV Detection and Operation Mode Identification Over Encrypted Wi-Fi Traffic. IEEE Transactions on Information Forensics and Security 2020, 15, 2346–2360. [Google Scholar] [CrossRef]
- LeCun, Y.; Bengio, Y.; Hinton, G. Deep learning. nature 2015, 521(7553), 436–444. [Google Scholar] [CrossRef]
- Tlili, F.; Ayed, S.; Chaari Fourati, L. Exhaustive Distributed Intrusion Detection System for UAVs Attacks Detection and Security Enforcement (E-DIDS). Computers & Security 2024, 142, 103878. [Google Scholar] [CrossRef]
- Medhi, J.; Liu, R.; Wang, Q.; Chen, X. A Lightweight and Efficient Intrusion Detection System (IDS) for Unmanned Aerial Vehicles. Neural Computing and Applications 2025, 37(20), 15819–15836. [Google Scholar] [CrossRef]
- Niyonsaba, S.; Konate, K.; Soidridine, M.M. Deep learning based intrusion detection for cybersecurity in unmanned aerial vehicles network. In 2024 International Conference on Electrical, Computer and Energy Technologies (ICECET; IEEE, July 2024; pp. 1–6. [Google Scholar]
- Mughal, U. A.; Alkhrijah, Y.; Almadhor, A.; Yuen, C. Deep Learning for Secure UAV-Assisted RIS Communication Networks. IEEE Internet of Things Magazine 2024, 7(2), 38–44. [Google Scholar] [CrossRef]
- Tang, X.; Liu, N.; Zhang, R.; Han, Z. Deep Learning-Assisted Secure UAV-Relaying Networks With Channel Uncertainties. IEEE Transactions on Vehicular Technology 2022, 71(5), 5048–5059. [Google Scholar] [CrossRef]
- Haque, E.; Hasan, K.; Ahmed, I.; Alam, M. S.; Islam, T. Enhancing UAV Security Through Zero Trust Architecture: An Advanced Deep Learning and Explainable AI Analysis. arXiv 2024. [Google Scholar] [CrossRef]
- Abu Al-Haija, Q.; Al Badawi, A. High-Performance Intrusion Detection System for Networked UAVs via Deep Learning. Neural Comput & Applic 2022, 34(13), 10885–10900. [Google Scholar] [CrossRef]
- Kaelbling, L.P.; Littman, M.L.; Moore, A.W. Reinforcement learning: A survey. Journal of artificial intelligence research 1996, 4, 237–285. [Google Scholar] [CrossRef]
- Bouhamed, O.; Bouachir, O.; Aloqaily, M.; Al Ridhawi, I. Lightweight ids for uav networks: A periodic deep reinforcement learning-based approach. In 2021 IFIP/IEEE International Symposium on Integrated Network Management (IM); IEEE, May 2021; pp. 1032–1037. [Google Scholar]
- Ramadan, R.A.; Emara, A.H.; Al-Sarem, M.; Elhamahmy, M. Internet of drones intrusion detection using deep learning. Electronics 2021, 10(21), 2633. [Google Scholar] [CrossRef]
- Mughal, U. A.; Hassler, S. C.; Ismail, M. Machine Learning-Based Intrusion Detection for Swarm of Unmanned Aerial Vehicles. 2023 IEEE Conference on Communications and Network Security (CNS), 2023; pp. pp 1–9. [Google Scholar] [CrossRef]
- Alzahrani, A. Novel Approach for Intrusion Detection Attacks on Small Drones Using ConvLSTM Model. IEEE Access 2024, 12, 149238–149253. [Google Scholar] [CrossRef]
- Jalil Hadi, H.; Cao, Y.; Li, S.; Hu, Y.; Wang, J.; Wang, S. Real-Time Collaborative Intrusion Detection System in UAV Networks Using Deep Learning. IEEE Internet of Things Journal 2024, 11(20), 33371–33391. [Google Scholar] [CrossRef]
- Miao, S.; Pan, Q.; Zheng, D. Unmanned aerial vehicle intrusion detection: Deep-meta-heuristic system. Vehicular Communications 2024, 46, 100726. [Google Scholar] [CrossRef]
- Benjamin, K.; Kacem, T. UAV DoS Attack Detection using a Hybrid Transformer-LSTM Approach. In 2025 International Wireless Communications and Mobile Computing (IWCMC); IEEE, May 2025; pp. 1702–1708. [Google Scholar]
- Kacem, T.; Tossou, S. ADS-B replay attack detection using transformers. In 2024 International Wireless Communications and Mobile Computing (IWCMC); IEEE, May 2024; pp. 144–149. [Google Scholar]
- Kairouz, P.; McMahan, H.B. Advances and open problems in federated learning. Foundations and trends in machine learning 2021, 14(1-2), 1–210. [Google Scholar] [CrossRef]
- Zhang, H.; Zhou, F.; Wang, W.; Wu, Q.; Yuen, C. A Federated Learning-Based Lightweight Network With Zero Trust for UAV Authentication. IEEE Transactions on Information Forensics and Security 2025, 20, 7424–7437. [Google Scholar] [CrossRef]
- Ceviz, O.; Sadioglu, P.; Sen, S.; Vassilakis, V. G. A Novel Federated Learning-Based IDS for Enhancing UAVs Privacy and Security. Internet of Things 2025, 31, 101592. [Google Scholar] [CrossRef]
- He, X.; Chen, Q.; Tang, L.; Wang, W.; Liu, T. CGAN-Based Collaborative Intrusion Detection for UAV Networks: A Blockchain-Empowered Distributed Federated Learning Approach. IEEE Internet of Things Journal 2023, 10(1), 120–132. [Google Scholar] [CrossRef]
- Ceviz, O.; Sadioğlu, P.; Sen, S.; Vassilakis, V. A Novel Federated Learning-Based Intrusion Detection System for Flying Ad Hoc Networks; 2023. [Google Scholar] [CrossRef]
- Lu, Y.; Yang, T.; Zhao, C.; Chen, W.; Zeng, R. A Swarm Anomaly Detection Model for IoT UAVs Based on a Multi-Modal Denoising Autoencoder and Federated Learning. Computers & Industrial Engineering 2024, 196, 110454. [Google Scholar] [CrossRef]
- da Silva, L.; Ferrao, I.; Dezan, C.; Espes, D.; Castelo Branco, K. Anomaly-Based Intrusion Detection System for In-Flight and Network Security in UAV Swarm; 2023; pp. pp 812–819. [Google Scholar] [CrossRef]
- da Silva, L. M.; Ferrão, I. G.; Diniz, B. A.; Carciofi, T. P.; Ziliol, V. D.; Dezan, C.; Espes, D.; Branco, K. R. L. J. C. Collaborative Intrusion Detection System for Network and Flight Security in Unmanned Aerial Vehicles Group. 2025 International Conference on Unmanned Aircraft Systems (ICUAS), 2025; pp. pp 1027–1034. [Google Scholar]
- Ceviz, O.; Sen, S.; Sadioglu, P. Distributed Intrusion Detection in Dynamic Networks of UAVs Using Few-Shot Federated Learning. In Security and Privacy in Communication Networks; Alrabaee, S., Choo, K.-K. R., Damiani, E., Deng, R. H., Eds.; Springer Nature Switzerland: Cham, 2026; pp. pp 131–153. [Google Scholar] [CrossRef]
- He, X.; Chen, Q.; Tang, L.; Wang, W.; Liu, T.; Li, L.; Liu, Q.; Luo, J. Federated continuous learning based on stacked broad learning system assisted by digital twin networks: An incremental learning approach for intrusion detection in UAV networks. IEEE Internet of Things Journal 2023, 10(22), 19825–19838. [Google Scholar] [CrossRef]
- Mowla, N. I.; Tran, N. H.; Doh, I.; Chae, K. Federated Learning-Based Cognitive Detection of Jamming Attack in Flying Ad-Hoc Network. IEEE Access 2020, vol. 8, 4338–4350. [Google Scholar] [CrossRef]
- Fahim-Ul-Islam, Md.; Chakrabarty, A.; Hakimi, H. S.; Maidin, S. S. FedWGCA: A Federated Learning Based AAV Intrusion Detection With Gradient Clipping and Attention-Based Neural Networks. IEEE Open Journal of the Computer Society 2025, 6, 1799–1809. [Google Scholar] [CrossRef]
- Zeng, Q.; Olatunde-Salawu, S.; Nait-Abdesselam, F. FGA-IDS: A Federated Learning and GAN-Augmented Intrusion Detection System for UAV Networks. 2024 IEEE 10th International Conference on Collaboration and Internet Computing (CIC), 2024; pp. pp 50–59. [Google Scholar] [CrossRef]
- Deng, J.; Wang, W.; Wang, L.; Bashir, A.K.; Gadekallu, T.R.; Feng, H.; Lv, M.; Fang, K. FIDSUS: Federated intrusion detection for securing UAV swarms in smart aerial computing. In IEEE Internet of Things Journal; 2025. [Google Scholar]
- Chai, Y.; Liu, M.; Li, M. Navigation spoofing and jamming signals identification of UAV based on federated learning. IEEE Internet of Things Journal, 2025. [Google Scholar]
- Cui, X.; Wu, J.; Fan, X.; Yu, Q.; Wang, T.; Li, G.; Luo, C. Online personalized federated learning methods for intrusion detection in dynamic UAV networks. International Conference on Wireless Artificial Intelligent Computing Systems and Applications, 2025, June; Springer Nature Singapore: Singapore; pp. 394–405. [Google Scholar]
- Ntizikira, E.; Lei, W.; Alblehai, F.; Saleem, K.; Lodhi, M. A. Secure and Privacy-Preserving Intrusion Detection and Prevention in the Internet of Unmanned Aerial Vehicles. Sensors 2023, 23(19), 8077. [Google Scholar] [CrossRef]
- Sethi, K.; Sai Rupesh, E.; Kumar, R.; Bera, P.; Venu Madhav, Y. A Context-Aware Robust Intrusion Detection System: A Reinforcement Learning-Based Approach. Int. J. Inf. Secur. 2020, 19(6), 657–678. [Google Scholar] [CrossRef]
- Islam, M. R.; Yusupov, K.; Muminov, I.; Sahlabadi, M.; Yim, K. Cybersecurity in UAVs: An Intrusion Detection System Using UAVCAN and Deep Reinforcement Learning. In Advances on Broad-Band Wireless Computing, Communication and Applications; Barolli, L., Ed.; Springer Nature Switzerland: Cham, 2025; pp. pp 123–131. [Google Scholar]
- Tao, J.; Han, T.; Li, R. Deep-Reinforcement-Learning-Based Intrusion Detection in Aerial Computing Networks. IEEE Network 2021, 35(4), 66–72. [Google Scholar] [CrossRef]
- Arthur, M. P. Detecting Signal Spoofing and Jamming Attacks in UAV Networks Using a Lightweight IDS. 2019 International Conference on Computer, Information and Telecommunication Systems (CITS), 2019; pp. pp 1–5. [Google Scholar] [CrossRef]
- Benfriha, S.; Labraoui, N.; Bany Salameh, H. A.; Bensaid, R. Reinforcement Learning-Based Drone-Client Selection for Efficient Federated Learning-Based Intrusion Detection in FANETs. Cluster Comput 2025, 28(8), 549. [Google Scholar] [CrossRef]
- Hickling, T.; Aouf, N.; Spencer, P. Robust Adversarial Attacks Detection Based on Explainable Deep Reinforcement Learning for UAV Guidance and Planning. IEEE Transactions on Intelligent Vehicles 2023, 8(10), 4381–4394. [Google Scholar] [CrossRef]
- Zhou, J.; Cui, G.; Hu, S.; Zhang, Z.; Yang, C.; Liu, Z.; Wang, L.; Li, C.; Sun, M. Graph neural networks: A review of methods and applications. AI open 2020, 1, 57–81. [Google Scholar] [CrossRef]
- Wang, G.; Ai, J.; Mo, L.; Yi, X.; Wu, P.; Wu, X.; Kong, L. Anomaly Detection for Data from Unmanned Systems via Improved Graph Neural Networks with Attention Mechanism. Drones 2023, 7(5), 326. [Google Scholar] [CrossRef]
- Swamy, K. K.; Sophia, S. Detecting Poisoning Attacks in UAVs via Spatio-Temporal Graph Neural Network and Walrus Optimizer. 2025 5th International Conference on Soft Computing for Security Applications (ICSCSA); 2025, pp. pp 2004–2011. [CrossRef]
- El Rai, M. C.; Darseesh, M. Dual-Branch Graph Attention Network for Cyber-Physical Intrusion Detection System for Unmanned Aerial Vehicles. 2025 International Conference on Communication, Computing, Networking, and Control in Cyber-Physical Systems (CCNCPS), 2025; pp. pp 381–384. [Google Scholar] [CrossRef]
- Sun, Z.; Teixeira, A. M. H.; Toor, S. GNN-IDS: Graph Neural Network Based Intrusion Detection System. In Proceedings of the 19th International Conference on Availability, Reliability and Security; ARES ’24; Association for Computing Machinery: New York, NY, USA, 2024; pp. pp 1–12. [Google Scholar] [CrossRef]
- Mustafa Abro, G. E.; Abdallah, A. M. Graph Attention Networks For Anomalous Drone Detection: RSSI-Based Approach with Real-World Validation. Expert Systems with Applications 2025, 273, 126913. [Google Scholar] [CrossRef]
- Mughal, U. A.; Atat, R.; Ismail, M. Graph Neural Network-Based Intrusion Detection System for a Swarm of UAVs. MILCOM 2024 - 2024 IEEE Military Communications Conference (MILCOM), 2024; pp. pp 578–583. [Google Scholar] [CrossRef]
- Majumder, R.; Comert, G.; Werth, D.; Gale, A.; Chowdhury, M.; Salek, M. S. Graph-Powered Defense: Controller Area Network Intrusion Detection for Unmanned Aerial Vehicles. arXiv 2025. [Google Scholar] [CrossRef]
- Du, Y.; Li, Y.; Cheng, P.; Han, Z.; Wang, Y. UGL: A Comprehensive Hybrid Model Integrating GCN and LSTM for Enhanced Intrusion Detection in UAV Controller Area Networks. Computer Networks 2025, 262, 111157. [Google Scholar] [CrossRef]
- Feuerriegel, S.; Hartmann, J.; Janiesch, C.; Zschech, P. Generative AI: S. Feuerriegel et al. Business & information systems engineering 2024, 66(1), 111–126. [Google Scholar]
- Asif, M.; Rahman, M. A.; Akkaya, K.; Shahriar, H.; Cuzzocrea, A. Adversarial Data-Augmented Resilient Intrusion Detection System for Unmanned Aerial Vehicles. 2023 IEEE International Conference on Big Data (BigData), 2023; pp. pp 5428–5437. [Google Scholar] [CrossRef]
- El Alami, H.; Rawat, D. B. DroneDefGANt: A Generative AI-Based Approach for Detecting UAS Attacks and Faults. ICC 2024 - IEEE International Conference on Communications, 2024; pp. pp 1933–1938. [Google Scholar] [CrossRef]
- Zhao, C.; Du, H.; Niyato, D.; Kang, J.; Xiong, Z.; Kim, D. I.; Shen, X.; Letaief, K. B. Enhancing Physical Layer Communication Security Through Generative AI with Mixture of Experts. IEEE Wireless Communications 2025, 32(3), 176–184. [Google Scholar] [CrossRef]
- Panda, D. K.; Guo, W. Generative Adversarial Evasion and Out-of-Distribution Detection for UAV Cyber-Attacks. arXiv 2025. [Google Scholar] [CrossRef]
- Sarikaya, B. S.; Bahtiyar, Ş. Generative Adversarial Networks for Synthetic Jamming Attacks on UAVs. 2024 9th International Conference on Computer Science and Engineering (UBMK), 2024; pp. pp 760–765. [Google Scholar] [CrossRef]
- Nagendra Kumar, D.; Sundarakantham, K.D.; Dharani, J.; Singh, K. Generative AI Based Blockchain Framework for Secure and Private Communication in Internet of Drones Systems; Social Science Research Network: Rochester, NY September 1, 2025. [Google Scholar] [CrossRef]
- Zeng, Q.; Nait-Abdesselam, F. Leveraging Human-In-The-Loop Machine Learning and GAN-Synthesized Data for Intrusion Detection in Unmanned Aerial Vehicle Networks. ICC 2024 - IEEE International Conference on Communications, 2024; pp. pp 1557–1562. [Google Scholar] [CrossRef]
- Gaber, T.; Ali, T.; Nicho, M.; Torky, M. Robust attacks detection model for internet of flying things based on generative adversarial network (gan) and adversarial training. IEEE Internet of Things Journal 2025. [Google Scholar] [CrossRef]
| Authors | Year | AIMT | ML | DL | FL | RL | GNN | GAI | TDM |
|---|---|---|---|---|---|---|---|---|---|
| Cordill et al. [6] | 2025 | ✓ | ✓ | x | ✓ | x | x | x | x |
| Tsao et al. [7] | 2022 | ✓ | ✓ | ✓ | ✓ | ✓ | x | x | x |
| Bithas et al. [10] | 2019 | ✓ | ✓ | x | ✓ | x | x | x | x |
| Sarikaya and Bahtiyar [12] | 2024 | ✓ | x | x | x | ✓ | x | x | x |
| Wang et al [13] | 2024 | ✓ | ✓ | ✓ | ✓ | ✓ | x | x | x |
| Adil et al. [14] | 2023 | x | x | x | x | x | x | x | x |
| Tlili et al. [15] | 2024 | x | x | x | x | x | x | x | x |
| Yang et al. [16] | 2025 | x | x | x | x | x | x | x | x |
| Abro et al. [17] | 2022 | x | x | x | x | x | x | x | x |
| Pandey et al. [19] | 2022 | ✓ | x | x | x | x | x | x | x |
| Alzubaidi [21] | 2025 | ✓ | ✓ | x | x | x | x | x | ✓ |
| Ogab et al. [23] | 2023 | ✓ | x | x | x | x | x | x | ✓ |
| Our Survey | 2026 | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| Authors | Model | Attack Type | UAV Layer | Security Property |
|---|---|---|---|---|
| Whelan et al [28] | PCA + One Class Classifier | GPS spoofing, Jamming | Physical, Navigation | Availability, Integrity |
| Moustafa and Jolfaei [29] | Decision Tree, DNN, MLP, SVM | networked UAV attacks | Communication | Confidentiality, Integrity, Availability, Authenticity |
| Shafique et al. [30] | SVM + K-Fold | GPS spoofing | Navigation | Availability, Integrity |
| Agnew et al. [31] | Light GBM | DoS (greyhole, blackhole), Jamming | Physical, Communication | Availability |
| Wu et al. [32] | FRS + SNN + RF | DoS, DDoS | Communication | Availability |
| Fu et al. [33] | CNN-LSTM | DDoS, Jamming, Command Injection, Malware, Sensor Manipulation | All | Availability, Authenticity, Integrity |
| Shrestha et al [34] | LR, DT, LDA, KNN, GNB, SGD, K-M | DoS, Botnet, Unauthorized Access | Communication | Availability, Authenticity |
| Whelan et al. [35] | PCA + One Class Classifier | Sensor Manipulation | Physical | Integrity, Authenticity |
| Cai et al. [36] | RF Fingerprinting + CNN + DNN | Data Poisoning, Model Evasion | Application | Authenticity, Privacy, Robustness |
| Mehmood et al. [37] | RF | DoS | Communication | Availability |
| Authors | Model | Attack Type | UAV Layer | Security Property |
|---|---|---|---|---|
| Tlili et al. [40] | LSTM | Jamming, MiTM, GPS Spoofing, Malware | All | Availability, Integrity, Confidentiality, Authenticity |
| Mehdi et al. [41] | DPN | DoS, MiTM | Communication | Availability, Integrity, Authenticity |
| Niyonsaba [42] | CNN + LSTM | DoS, DDoS, MiTM | Communication | Availability, Authenticity |
| Mughal et all. [43] | LSTM + DDPG | Jamming | Physical | Availability |
| Tang et al [44] | DNN + DQN | Jamming | Physical | Availability |
| Haque et al. [45] | PCA + DNN | MiTM, Command Injection | Communication, Control | Authenticity, Integrity |
| Abu AL-Haija and Badawi [46] | Deep CNN | DoS, MiTM, Command Injection | Communication, Control | Availability, Integrity, Authenticity |
| Ramadan et al. [49] | LSTM + RNN | DoS, Malware, Botnet, MiTM | Communication, Application | Availability, Integrity, Authenticity |
| Mughal et al. [50] | FNN, CNN, RNN | Message Injection, DoS | Communication | Integrity, Availability, Authenticity |
| Alzahrani [51] | CNN, LSTM, CNN-LSTM, convLSTM | DoS, MiTM, Message Injection | Communication | Availability, Integrity, Authenticity |
| Jalil Hadi [52] | FFCNN | DoS, Message Injection | Communication | Availability, Integrity, Authenticity |
| Miao et al. [53] | CNN-biLSTM | DoS, GPS Spoofing, Command Injection | Communication, Navigation, Control | Availability, Integrity, Authenticity |
| Benjamin and Kacem [54] | Transformer + LSTM | DoS, DDoS | Communication | Availability |
| Kacem and Tossou [55] | Transformer | ADS-B Message Injection | Communication | Authenticity, Integrity |
| Authors | Model | Attack Type | UAV Layer | Security Property |
|---|---|---|---|---|
| Zhang et al. [57] | LSNet | Message Injection, Command Injection, Model Poisoning | Communication, Control, Application | Integrity, Authenticity, Privacy, Robustness |
| Ceviz et al. [58,60] | FedAvg + CNN + DNN | DoS | Communication | Availability, Privacy |
| He et al. [59] | CGAN-LSTM + BFA | Jamming, DoS, MiTM, Model Poisoning | Communication, Application | Availability, Privacy, Integrity, Robustness |
| Lu ey al. [61] | L-MDAE | Sensor Manipulation, DoS | Physical, Communication | Availability, Integrity, Authenticity, privacy |
| Da Silva et al. [62,63] | Light GBM | GPS Spoofing, Jamming | Physical, Navigation | Availability, Integrity, Authenticity, Privacy |
| Ceviz [64] | Few Shot Learning | DoS | Communication | Availability, Privacy |
| Mowala et al. [66] | Custom Model | Jamming | Physical | Availability, Privacy |
| Fahim-Ul-Islam et al. [67] | FedWGCA | Model Poisoning | Application | Robustness, Privacy |
| Zeng [68] | FL + GAN | Jamming, Message Injection, DoS, GPS Spoofing, Model Evasion | All | Integrity, Authenticity, Availability, Privacy, Robustness |
| Deng et al. [69] | Custom | DoS, Command Injection, Message Injection | Communication, Control | Availability, Integrity, Authenticity, Privacy |
| Chai et al. [70] | TCN-Transformer | GPS Spoofing, Jamming | Physical, Navigation | Availability, Integrity, Privacy |
| Cui et al. [71] | OPFL | DoS, Message Injection, MiTM | Communication | Integrity, Authenticity, Availability, Privacy |
| Ntizikira et al. [72] | DP + CNN-LSTM | DoS, DDoS, MiTM, Message Injection, Code Injection | Communication, Control | Availability, Integrity, Authenticity, Privacy |
| Authors | Model | Attack Type | UAV Layer | Security Property |
|---|---|---|---|---|
| Bouhamed et al. [48] | DQN | Command Injection, DoS | Communication | Availability, Authenticity, Integrity |
| Sethi et al. [73] | DQN | DoS, MiTM, Message Injection, Data Poisoning, Model Evasion | Communication, Application | Availability, Integrity, Authenticity, Robustness |
| Islam et al. [74] | DQN | DoS, Message Injection | Communication | Availability, Integrity, Authenticity |
| Tao et al. [75] | DDPG | GPS Spoofing, Jamming | Physical, Navigation | Availability, Authenticity, Integrity |
| Arthur et a. [76] | STL + SVM + DQN | Jamming, Message Injection | Physical, Communication | Availability, Authenticity, Integrity |
| Benfriha et al. [77] | RL + FDL | DoS | Communication | Availability |
| Hickling et al. [78] | DDPG + PER + APF | Data Poisoning, Model Evasion | Application | Robustness |
| Authors | Model | Attack Type | UAV Layer | Security Property |
|---|---|---|---|---|
| Wang et al. [80] | GAT + Bi-LSTM | Anomaly Detection | Physical | N/A |
| Swamy and Sophia [81] | STFGNNet-WO + PPFL | Data Poisoning | Application | Privacy, Robustness |
| El Rai and Darseesh [82] | Dual-GAT | DoS, Message Injection | Communication | Availability, Authenticity, Integrity |
| Sun et al. [83] | GAT, GCN, GCN-EW | DoS | Communication | Availability |
| Mustafa Abro and Abdallah [84] | GAT | Anomaly Detection | Physical | N/A |
| Mughal et al. [85] | ChebNet | DoS, Message Injection | Communication | Availability, Integrity, Authenticity |
| Majumder et al.[86] | GCNNs, GATs, GraphSAGE, GT | DoS, Message Injection | Communication | Availability, Integrity, Authenticity |
| Du et al. [87] | GCN + LSTM | DoS, Message Injection | Communication | Availability, Integrity, Authenticity |
| Authors | Model | Attack Type | UAV Layer | Security Property |
|---|---|---|---|---|
| Asif et al. [89] | GAN | Jamming, GPS Spoofing, Model Evasion | Physical, Communication, Application | Availability, Integrity, Authenticity, Robustness |
| El Alami and Rawat[90] | GAN + Transformers | Actuator Manipulation, Jamming, GPS Spoofing | Physical, Navigation | Availability, Integrity, Authenticity |
| Zhao et al. [91] | MoE-enabled GAI | Jamming, MiTM, Message Injection | Physical, Communication | Availability, Authenticity, Integrity |
| Panda and Guo [92] | CGAN + CVAE | DoS, Message Injection, MiTM, Model Evasion | Communication, Application | Availability, Integrity, Authenticity, Robustness |
| Sarrikaya and Bahtiyar [93] | CTGAN + GC + VAE | Jamming | Physical | Availability |
| Nagendra Kumar et al. [94] | GAN + zk-SNARK + PBFT | Message Injection, MiTM | Communication | Integrity, Authenticity |
| Zeng and Nait-Abdesselam [95] | HITL-ML + GAN | Model Evasion | Application | Robustness |
| Gaber et al. [96] | GAN + ML classifiers | Model Evasion | Application | Robustness |
| AI Model | C (%) | I (%) | Av (%) | Au (%) | P (%) | R (%) | # Papers |
|---|---|---|---|---|---|---|---|
| ML | 10 | 50 | 80 | 40 | 0 | 0 | 10 |
| DL | 7 | 71 | 85 | 78 | 0 | 0 | 14 |
| FL | 0 | 60 | 73 | 46 | 100 | 20 | 15 |
| RL | 0 | 71 | 85 | 71 | 0 | 28 | 7 |
| GNN | 0 | 50 | 62 | 50 | 12 | 12 | 8 |
| GAI | 0 | 62 | 62 | 62 | 0 | 50 | 8 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.




