Submitted:
15 April 2026
Posted:
16 April 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. The Scope of Our Survey and Contributions
- This survey is organized in a comprehensive way to serve as a roadmap for academic researchers to obtain knowledge of integrating threat intelligence to develop advanced IDS.
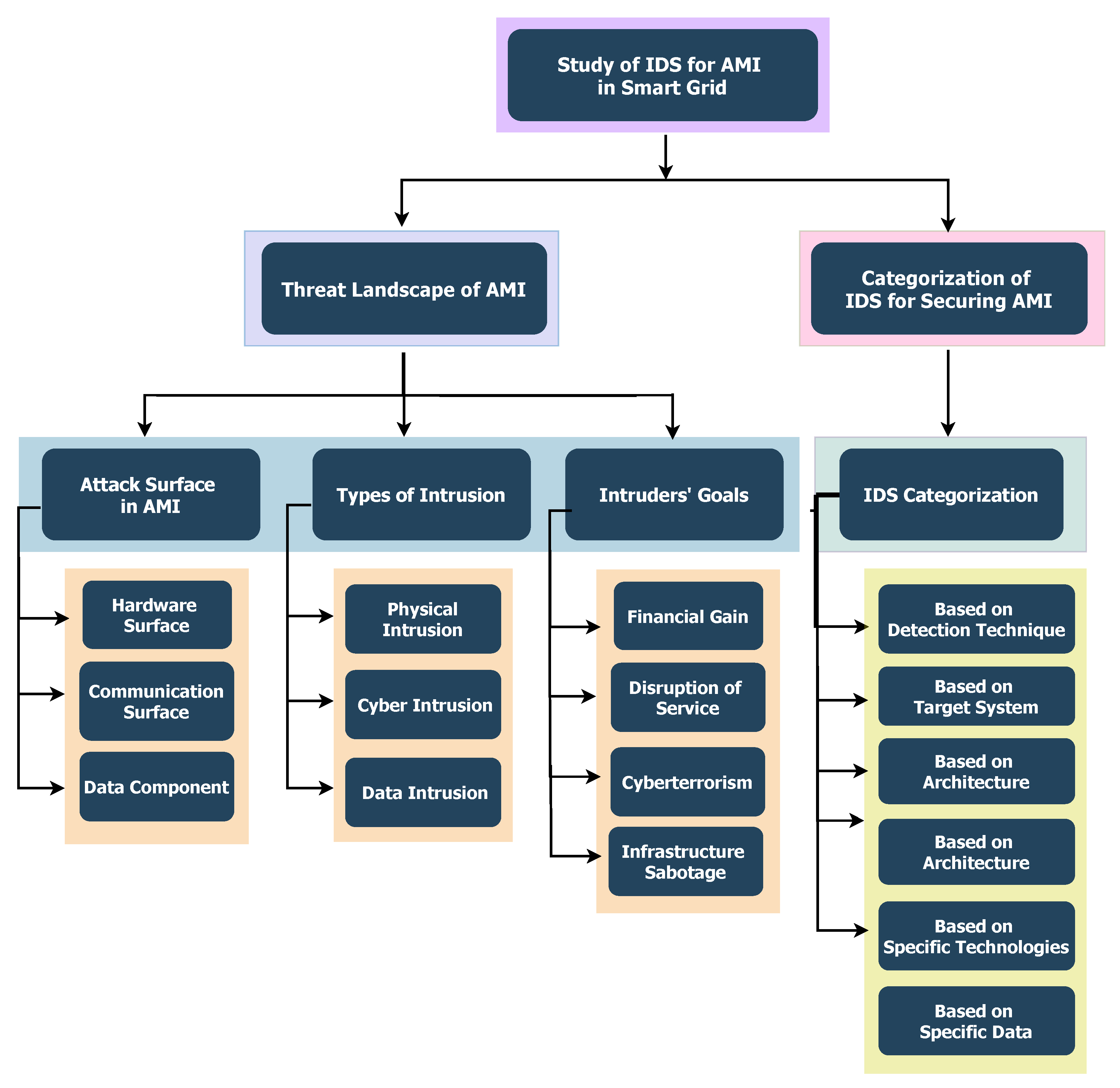
- First, A taxonomy-based review is presented in a Figure 2, framing a comprehensive overview of AMI security challenges associated with the IDS development. The vulnerabilities of AMI components, which create the attack surfaces for a range of intrusions, along with their threat landscape, are overviewed in the survey that undermines AMI and SG security. Additionally, the paper examines the malicious objectives or goals of attackers or intruders underlying diverse security attacks and intrusive activities in detail.
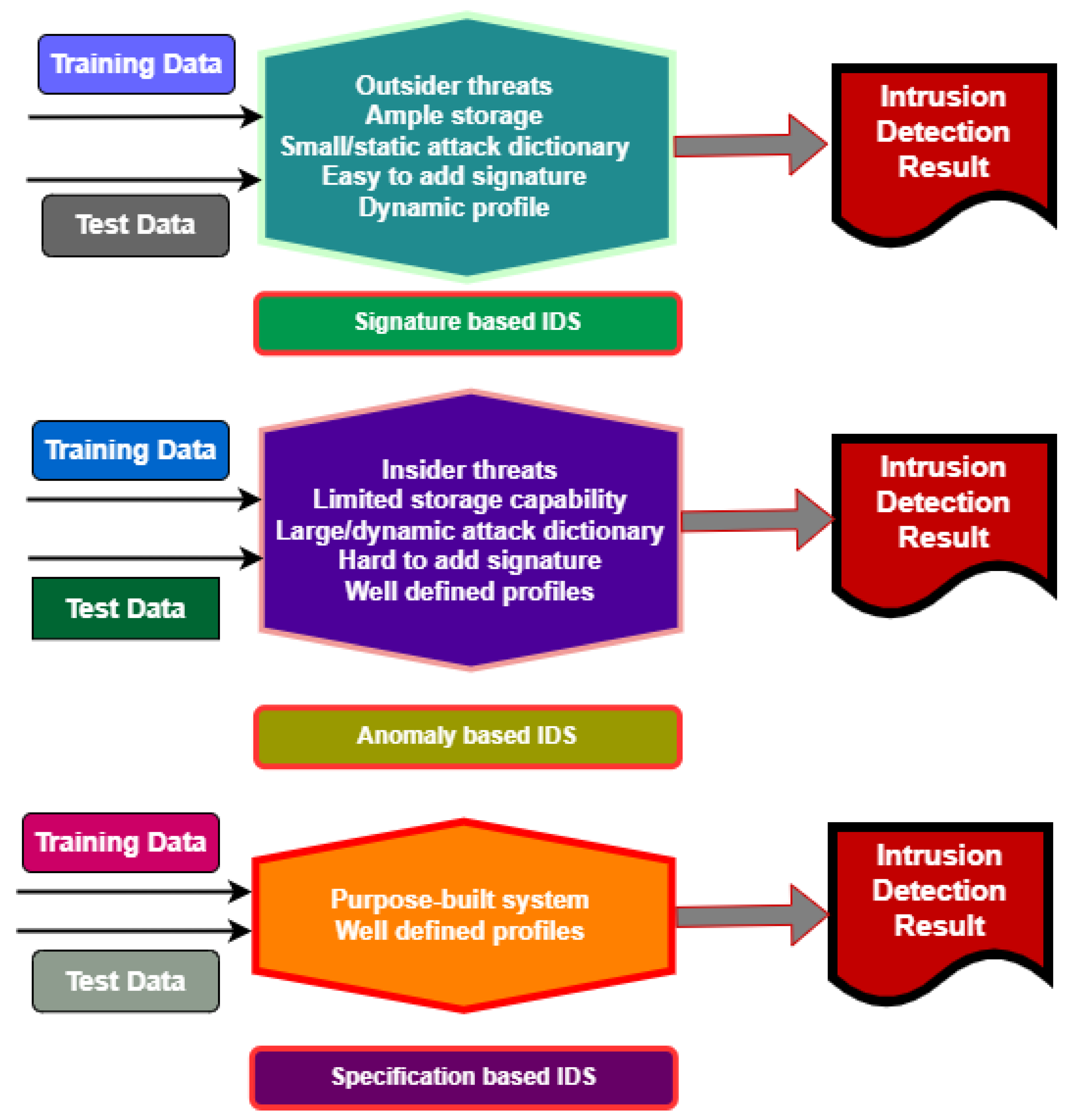
- Second, a general background on IDS as robust countermeasures, addressing the security aspects of AMI in the SG, is provided. The IDS overview various categories of IDSs, including detection mechanisms, architectures, and related factors with conventional approaches and advanced architectural distinctions, and different diverse technologies for deployments across AMI and SG paradigm.
- Third, the survey compares various IDSs for AMI and SG systems to identify what several current and novel IDSs focusing on AMI are computationally lacking, in order to be more effective and robust at detecting actual attacks or assaults that threaten the AMI system.
- Then, A prospective defence-in-depth approach is proposed to address security gaps identified in recent literature, leading to the design of intelligent IDSs for AMI. Security-critical components are identified and integrated to enable comprehensive monitoring of intrusive activities targeting AMI.
- Finally, the design algorithm for developing the MIDS is introduced with guidelines for integrating essential components to build an effective MIDS for AMI. The proposed scalable architecture of MIDS and the related key research challenges requiring systematic investigation are highlighted.
2. AMI Security Background
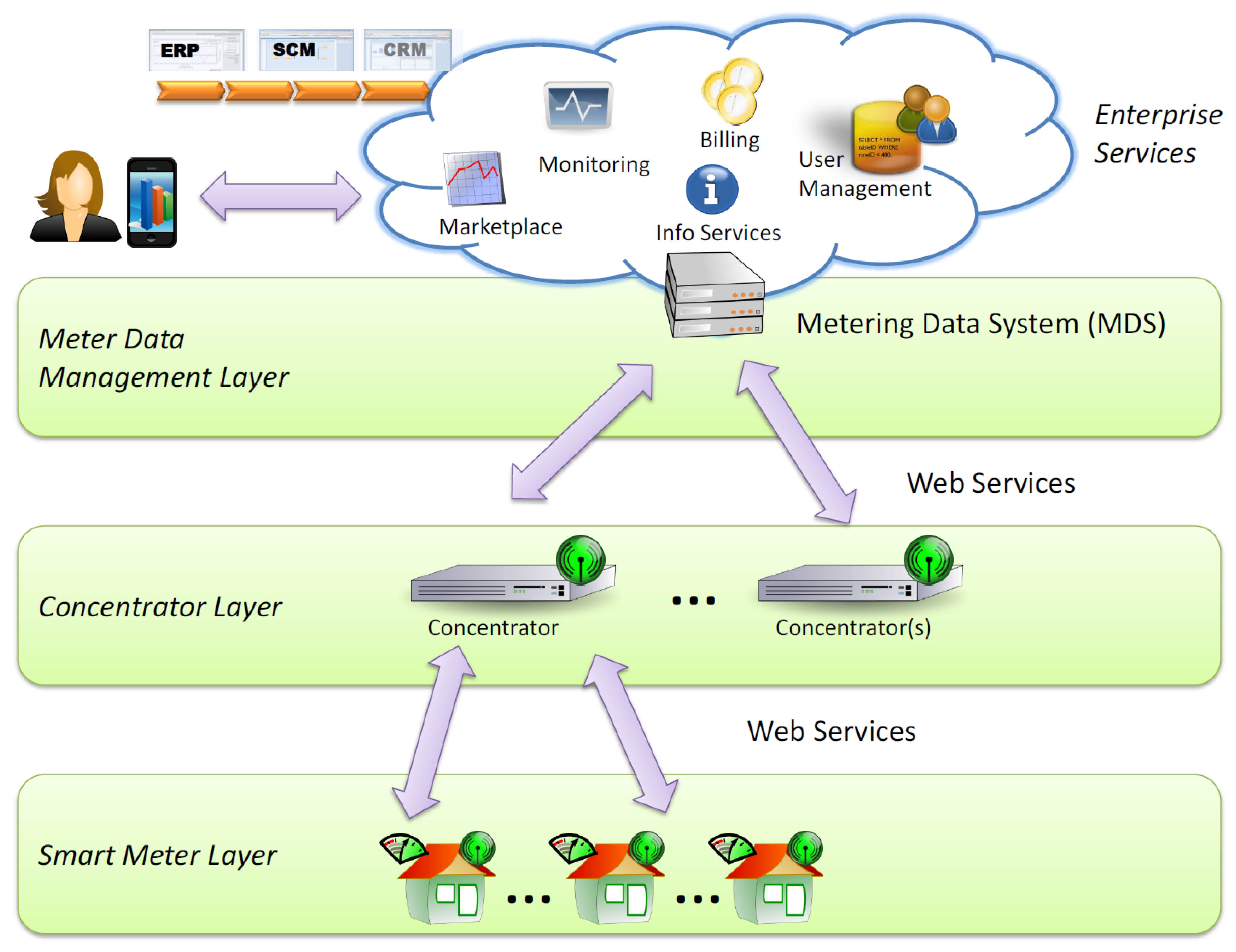
2.1. Overview of AMI Architecture
- Meter Layer: This is the layer where residential meters passively control and measure the energy consumption or production of the devices to which they are attached.
- Concentrator Layer: The meters communicate with this layer through various protocols, many of which are proprietary, to submit their measurements. The data reported is aggregated and submitted to the Metering Data System (MDS).
- Metering Data Management Layer (MDMS): Here, usage data and infrastructure-related events are collected for long-term storage, analysis, and management. To facilitate several managerial applications such as forecasting and invoicing, different enterprise services typically employ this [1].
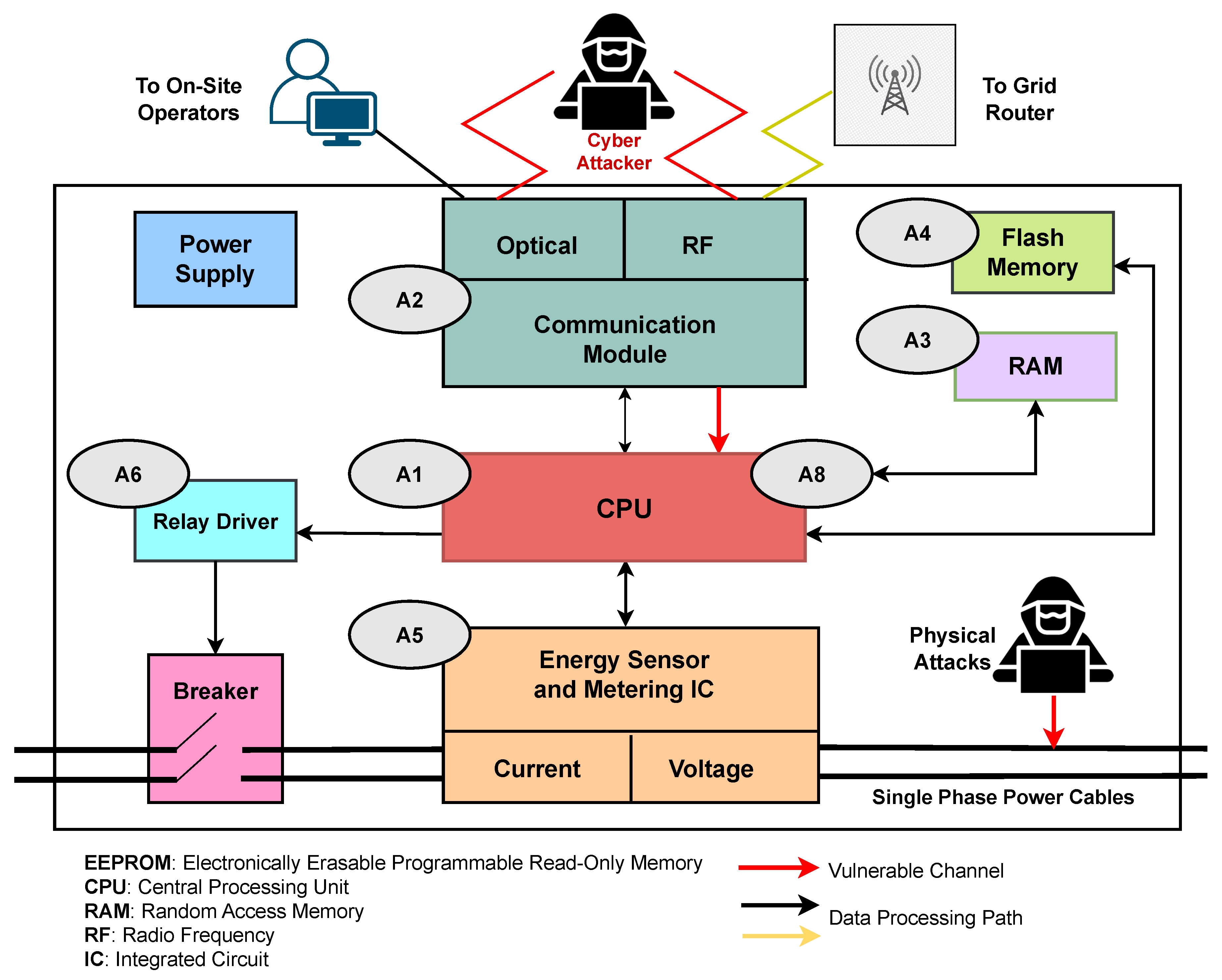
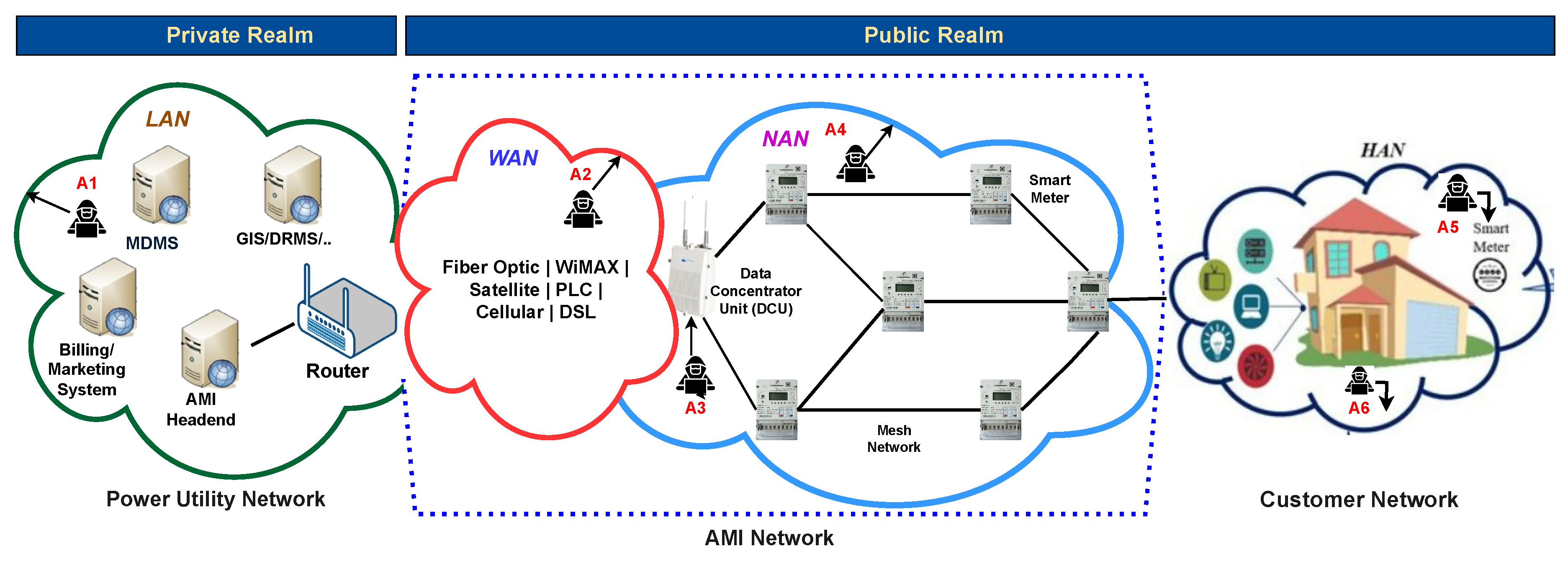
2.2. Attack Surface: AMI Paradigm
- —
- CPU (A1): Malware installation that results in dummy operations exhausts the computational resources of the CPU.
- —
- Communication Module (A2): The communication channels may be disabled or manipulated unintentionally. Furthermore, AMI devices communicate over frequency bands that are vulnerable to monitoring, jamming, or compromise.
- —
- RAM (A3): Metering and communication applications may also experience freezing or slowdown due to RAM exhaustion. To address these errors, the kernels of operating systems (OS) either terminate the application(s) that are currently running or reboot the system.
- —
- Flash Memory (A4): Attackers can alter recorded consumption data, device calibration, and operation modes by modifying configuration registers.
- —
- Sensor (A5)/Actuator Compromise (A6): The utility system can disconnect a customer by sending a tripping command.
- —
- Inter-Board Communications (A7): The low-level communication protocols that are implemented by all components are depicted in Figure 3 can be analyzed and adjusted to accommodate the attacker’s requirements. These attacks are typically isolated due to the physical access requirements.
2.3. Type of Intrusion on AMI
- Denial of Power (DoP): Denial of power service to a consumer through intrusions on smart meters individually. This form of attack can cause substantial harm when targeted at critical users. A denial-of-service (DoS) is a potential attack on an AMI that results in service denial, that is, a power interruption, in which the attacker floods the AMI’s communication network (e.g., wireless channels or control servers) with excessive, fake requests or traffic. A denial-of-service (DoS) attack in the AMI communication network, as defined by [18,24], is an attempt to overwhelm a targeted computer system or network with traffic or requests to disrupt routine operations and prevent authorized users from accessing it. This is what such an attack may entail. Alternatively, the intruder exploits the cyber vulnerabilities in the AMI’s communication protocols to inundate the system. In particular, another potential cyber-attack, Man-in-the-Middle (MitM), can exploit the vulnerability of a legacy protocol, such as Modbus [27], to compromise the AMI system by intercepting the communication channel between two parties and can cause the denial of energy [28,29,30]. Two frequently utilized MitM attack strategies are ARP spoofing and DNS spoofing. In a replay attack, a hacker intercepts previously obtained data, maliciously retransmits it to impersonate the original sender, and gains unauthorized access to the system’s network. One of the security threats that isolated SGs face is the replay attack, which involves the fraudulent delay of data transmission [31].
- Theft of Power (ToP): With an aim to steal power from the utility, individual smart meters are targeted by various attacks. Consumers or attackers may covertly reconnect to the electricity and intentionally disconnect from the power utility, or can manipulate the legacy protocols by cyber attacks to create discrepancies or break the agreement between physical consumption and recorded data. In addition, data stored in a smart meter may be altered to inaccurately represent power consumption across multiple smart meters. Smart meter manipulation is a common form of cyber intrusion or attack for energy theft [3,20,32,33,34].
- Disruption of Grid (DoG): A large number of smart meter compromises can lead to instability in the power grid, as these are able to be connected and disconnected rapidly in erratic sequences. The power grid may suffer partial failure and pervasive power loss if it cannot absorb this transient behaviour on a sufficiently large scale. For instance, the False Data Injection Attack (FDIA), which manipulates data collected by AMI sensors to mislead grid operational decisions, thereby disrupting grid service [35,36]. Coupled with the limited defence resources and the broad deployment of SMs, other potential cyber attacks, such as Distributed Denial of Service (DDoS), Authentication Attacks, Meter Spoofing and Energy Fraud Attacks, Data Confidentiality Attacks, etc., aim to compromise the AMI system [37,38].
2.4. Intruders’ Goals
- 1.
- Espionage and Intelligence Gathering: Espionage targeting AMI in SG constitutes a complex danger necessitating aggressive and extensive cybersecurity strategies[48]. With an aim to monitor consumer profiles, the attackers gather intelligence on the smart grid’s infrastructure, architecture, operations, and cyber–physical vulnerabilities, which can be used for subsequent reconnaissance assaults or state-sponsored attacks by interrupting the grid’s activities as geopolitical objectives.
- 2.
- Privacy Invasion and Data Theft: As the AMI deals with different types of data, the power consumption data contains sensitive customer-level information. Any invasion of the data, including the data breaches, theft of sensitive consumer data, confidential information, billing data, or energy consumption patterns, can pose significant risks to both consumers and electricity companies [3,49]. When this data is leaked or sold on the black market, it can be misused for different malevolent purposes, either physical crime or cyber exploitation. Different type of organized crime groups including cybercriminals can get a dual-use of this data by planning large-scale residential intrusions (e.g., determining when a residence is vacant) or targeting infrastructure by exploiting Weak grid assets.
- 3.
- 4.
- Financial Profit: The cyber criminals can manipulate billing information propagated from SMs to fraud, including energy theft by decreasing energy charges for specific clients or inflating bills to become financial gainers, which may incur substantial economic loss for utilities and result in a decline in consumer confidence[50].
- 5.
- Unauthorized Control: Gaining unauthorized access or control over any cyber-physical devices of AMI, such as smart meters or a security breach of the communication channel, can allow the attacker or hacker to manipulate energy flow, tamper with meter readings, disable devices, or engage in any malevolent activities [51].
- 6.
- Sabotage and Infrastructure Damage: The reliability of AMI depends on the integrity of thousands of field devices such as SMs and communication links, which are mostly distributed. Inflict physical damage on these components, i.e., physical sabotage of SMs, DCs, or communication links can severely hamper AMI by interrupting data flows from the field to the utility center or fault induction [15]. Such tangible damage to grid infrastructure can potentially cause disruption of the energy supply.
3. Overview of Intrusion Detection Systems
3.1. Categorization of IDS Based on Detection Technique:
3.1.1. Categorization Based on Target System:
3.1.2. Categorization Based on Architecture:
3.1.3. Categorization Based on Specific Technologies:
3.1.4. Categorization Based on Specific Data:
3.2. Performance Metrics of IDS:
- True Positives (TP): Correctly predicted positive cases.
- True Negatives (TN): Correctly predicted negative cases.
- False Positives (FP): Incorrectly predicted positive cases (actual negative).
- False Negatives (FN): Incorrectly predicted negative cases (actual positive).
- Attack packet injected at 12:00:05
- IDS raised an alert at 12:00:07
- Detection Latency = (12:00:07 - 12:00:05) = 2 seconds [116].
4. IDS Applied to AMI
5. Research Trends and Direction
- 1.
- Can the current IDS capture and integrate all the relevant data, that is, the multi-modality of data from the AMI system, in a scalable way?
- 2.
- Can the IDS identify an actual assault by analyzing the fused features collected among different layers of AMI data?
- 3.
- Do the chosen multimodal features enhance the ability of IDS to detect intrusion?
- 4.
- How can the scalability issues be addressed by the architectural design of the proposed MIDS?
- 5.
- If the system is under attack, can it determine the type of attack and the layer from which it originated?
5.1. An Experimental Framework for Developing Scalable IDS
- Validate if an attack is real by correlating multimodal data.
- Detect large-scale, coordinated cyber attacks that individual HD-IDSs might miss.
- Classify the attack type and trigger an appropriate response to protect the AMI network.
- Continuously improve its detection model through learning from aggregated alerts.
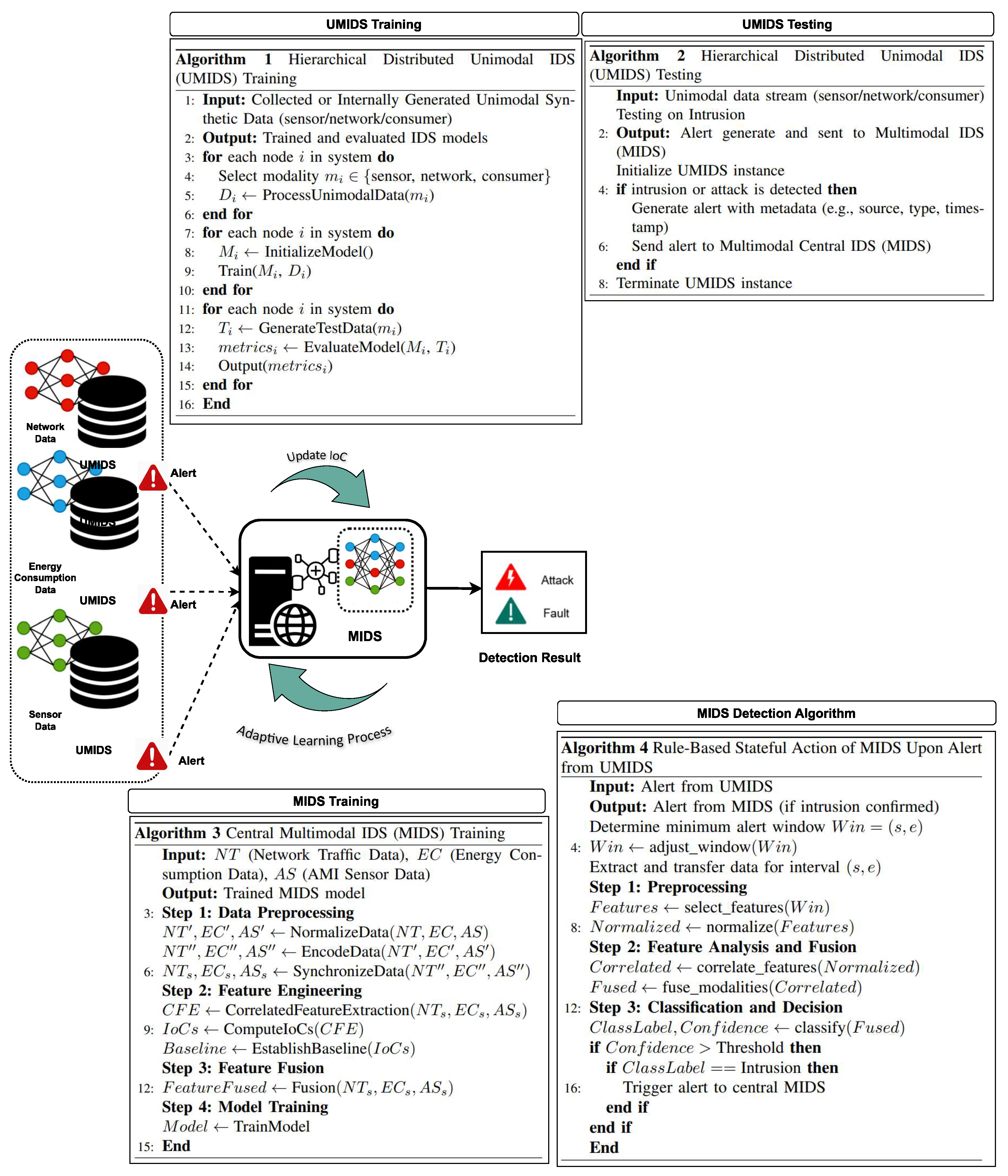
- Multimodal IDS: The framework should include tools for selecting and fusing multimodal features. A modality refers to a distinct type of data or signal, including network statistics, sensor data, log data, etc. Multimodal systems combine these modalities to increase the effectiveness of IDS [9]. Kiflay et al. presented the potential of multimodal data in the Network Intrusion Detection System (NIDSs) by integrating flow-based and payload characteristics to address the shortcomings of conventional machine learning-based NIDSs by improving detection accuracy and reliability [123]. In another study, Farhan et al. employed a multimodal approach to develop effective IoT-based NIDSs by combining trained text and texture features to classify various attacks targeting SG [121]. Federated Learning (FL), an emerging ML technique, can also leverage multimodal data and maintain data privacy [137,138]. Unfortunately, federated multimodal IDS does not scale well, particularly in such a hierarchical system.
- Correlation-Based Feature Extraction (CFE): is a technique utilized in machine learning and data analysis to discern and extract the most relevant features for a model by analyzing the correlations among variables (features) inside the dataset. The objective is to identify features that exhibit strong correlations with the target variable (the output or label) while discarding redundant or less useful features. The proposed IDSs feature IoC that can prevent AMI from severe cyber threats and protect the system from further disruption. Li et al. employed correlation-based feature selection (CFS) for developing ML-based classifiers for IDSs targeting SG [139]. Correlation-based feature extraction is an effective technique for identifying the most pertinent features by examining their connections to the target variable and their interrelationships with other features. It streamlines models, enhances accuracy, and minimizes the likelihood of overfitting. The CFE works on with an evaluation function to choose a subset of features where the linear correlation coefficient for two continuous random variables, X and Y, is defined as:
- Feature Fusion: Feature fusion implies the process of combining features of multiple types or modalities extracted from different data sources (modalities) with an aim to improve the accuracy and robustness of IDS in AMI. Feature fusion in an MIDS for AMI in SG involves integrating various data modalities—such as network traffic, energy consumption, and sensor data—into a cohesive representation to enhance the identification of cyber-physical attacks. This approach identifies communication anomalies by utilizing network data, reveals irregular usage patterns from abnormal energy consumption data, and detects physical invasions or environmental anomalies from the sensor data, thereby creating a comprehensive view of the system. To enhance detection accuracy and robustness of this type of IDS, fusing features can be a robust technique that detects potential attack routes and reduces false positives and negatives through cross-modal validation. Feature fusion allows MIDS to utilize temporal patterns, such as energy usage spikes caused by network abnormalities, and spatial correlations, like sensor readings from nearby meters. Using fused features, deep learning, attention processes, and graph-based models can reveal intricate interactions among modalities. This enables the identification of complex assaults, including DoS, MitM attacks (detected by network and energy data anomalies), electricity theft (via inconsistencies in energy, meter, and sensor data), and replay attacks. Feature fusion creates robust IDSs that protect AMI [140,141].
- An Indicators of Compromise (IoC): is a metric or forensic evidence indicating a system or network has been infiltrated by a cyberattack or security incident, and calculating IoCs from relevant features and including them in both the training set and the detection set. One such example of useful IoCs is correlation-based statistics, which have been shown, in some cases [127], to improve intrusion detection and classification.
- Co-Learning: Co-learning or training is the methodology for generating additional labelled training samples when labelled data are scarce in a multimodal context[142]. This implies a collaborative learning method in which multiple modalities (e.g., network traffic, system logs, sensor data, user behaviour) are concurrently or cooperatively analyzed. This approach enhances MIDSs with improved detection efficacy, robustness, and flexibility by intelligently integrating heterogeneous inputs. Particularly, it is a crucial technique for MIDSs which aim at real-time, high-stakes systems where dependence on a single data stream poses significant risks. The basic IDS algorithm constructs weak classifiers on the basis of each modality, mutually enhancing one another using labels for unlabeled inputs.
6. Conclusions
Nomenclature
| AMI | Advanced metering infrastructure |
| SM | Smart meter |
| IoT | Internet of Things |
| FDIA | False data injection attack |
| DoS | Denial of Service |
| ICT | Information and communication technologies |
| SG | Smart Grid |
| MitM | Man-in-the-Middle |
| TPR | True Positive Rate |
| SCADA | Supervisory Control and Data Acquisition |
| CIA | Confidentiality, Integrity, and Availability |
| FL | Federated Learning |
| CPS | Cyber-physical system |
| IDS | Intrusion detection system |
| DSM | Demand side management |
| DNP3 | Distributed network protocol version 3.0 |
| APT | Advanced persistent threat |
| MIDS | Multimodal intrusion detection system |
| UMIDS | Unimodal intrusion detection system |
| NIDS | Network intrusion detection system |
| ICS | Industrial control system |
| TTPs | Tactics, Techniques, and Procedures |
| IoC | Indicator of Compromise |
| HIDS | Host intrusion detection system |
References
- Karnouskos, S.; Da Silva, P.G.; Ilic, D. Assessment of high-performance smart metering for the web service enabled smart grid era. In Proceedings of the Proceedings of the 2nd ACM/SPEC International Conference on Performance engineering, 2011, pp. 133–144.
- Gope, P.; Sikdar, B. Privacy-aware authenticated key agreement scheme for secure smart grid communication. IEEE Transactions on Smart Grid 2018, 10, 3953–3962. [CrossRef]
- Jokar, P.; Arianpoo, N.; Leung, V.C. Electricity theft detection in AMI using customers’ consumption patterns. IEEE Transactions on Smart Grid 2015, 7, 216–226. [CrossRef]
- McDaniel, P.; McLaughlin, S. Security and privacy challenges in the smart grid. IEEE security & privacy 2009, 7, 75–77. [CrossRef]
- Lázaro, J.; Astarloa, A.; Rodríguez, M.; Bidarte, U.; Jiménez, J. A Survey on Vulnerabilities and Countermeasures in the Communications of the Smart Grid. Electronics 2021, 10, 1881. [CrossRef]
- Otuoze, A.O.; Mustafa, M.W.; Larik, R.M. Smart grids security challenges: Classification by sources of threats. Journal of Electrical Systems and Information Technology 2018, 5, 468–483. [CrossRef]
- Merlino, J.C.; Asiri, M.; Saxena, N. Ddos cyber-incident detection in smart grids. Sustainability 2022, 14, 2730. [CrossRef]
- Radoglou-Grammatikis, P.I.; Sarigiannidis, P.G. Securing the smart grid: A comprehensive compilation of intrusion detection and prevention systems. Ieee Access 2019, 7, 46595–46620. [CrossRef]
- He, H.; Sun, X.; He, H.; Zhao, G.; He, L.; Ren, J. A novel multimodal-sequential approach based on multi-view features for network intrusion detection. IEEE Access 2019, 7, 183207–183221. [CrossRef]
- Agrafiotis, G.; Kalafatidis, S.; Giapantzis, K.; Lalas, A.; Votis, K. Advancing cybersecurity with ai: A multimodal fusion approach for intrusion detection systems. In Proceedings of the 2024 IEEE International Mediterranean Conference on Communications and Networking (MeditCom). IEEE, 2024, pp. 51–56.
- El Mrabet, Z.; Kaabouch, N.; El Ghazi, H.; El Ghazi, H. Cyber-security in smart grid: Survey and challenges. Computers & Electrical Engineering 2018, 67, 469–482. [CrossRef]
- Coelho, P.; Gomes, M.; Moreira, C. Smart metering technology. Microgrids Design and Implementation 2019, pp. 97–137.
- Sun, C.C.; Cardenas, D.J.S.; Hahn, A.; Liu, C.C. Intrusion detection for cybersecurity of smart meters. IEEE Transactions on Smart Grid 2020, 12, 612–622. [CrossRef]
- Carpenter, M.; Goodspeed, T.; Singletary, B.; Skoudis, E.; Wright, J. Advanced metering infrastructure attack methodology. InGuardians white paper 2009.
- Foreman, J.C.; Gurugubelli, D. Identifying the cyber attack surface of the advanced metering infrastructure. The Electricity Journal 2015, 28, 94–103. [CrossRef]
- Shein, R. Security measures for advanced metering infrastructure components. In Proceedings of the 2010 Asia-Pacific Power and Energy Engineering Conference. IEEE, 2010, pp. 1–3.
- Banik, S.; Banik, T. Survey on Simulation and Vulnerability Testing in Smart Grid. preprints.org 2024.
- Yi, P.; Zhu, T.; Zhang, Q.; Wu, Y.; Li, J. A denial of service attack in advanced metering infrastructure network. In Proceedings of the 2014 IEEE International Conference on Communications (ICC). IEEE, 2014, pp. 1029–1034.
- Diovu, R.; Agee, J. A cloud-based openflow firewall for mitigation against DDoS attacks in smart grid AMI networks. In Proceedings of the 2017 IEEE PES PowerAfrica. IEEE, 2017, pp. 28–33.
- Shokry, M.; Awad, A.I.; Abd-Ellah, M.K.; Khalaf, A.A. Systematic survey of advanced metering infrastructure security: Vulnerabilities, attacks, countermeasures, and future vision. Future Generation Computer Systems 2022, 136, 358–377. [CrossRef]
- Khattak, A.M.; Khanji, S.I.; Khan, W.A. Smart meter security: Vulnerabilities, threat impacts, and countermeasures. In Proceedings of the Proceedings of the 13th International Conference on Ubiquitous Information Management and Communication (IMCOM) 2019 13. Springer, 2019, pp. 554–562.
- Yan, Y.; Qian, Y.; Sharif, H.; Tipper, D. A survey on cyber security for smart grid communications. IEEE communications surveys & tutorials 2012, 14, 998–1010. [CrossRef]
- Wang, J.; Shi, D.; Li, Y.; Chen, J.; Ding, H.; Duan, X. Distributed framework for detecting PMU data manipulation attacks with deep autoencoders. IEEE Transactions on smart grid 2018, 10, 4401–4410. [CrossRef]
- Guo, Y.; Ten, C.W.; Hu, S.; Weaver, W.W. Modeling distributed denial of service attack in advanced metering infrastructure. In Proceedings of the 2015 IEEE power & energy society innovative smart grid technologies conference (ISGT). IEEE, 2015, pp. 1–5.
- Banik, S.; Rogers, M.; Mahajan, S.M.; Emeghara, C.M.; Banik, T.; Craven, R. Survey on Vulnerability Testing in the Smart Grid. IEEE Access 2024. [CrossRef]
- Foreman, J.C.; Gurugubelli, D. Cyber attack surface analysis of advanced metering infrastructure. arXiv preprint arXiv:1607.04811 2016.
- Banik, S.; Banik, T.; Banik, S. Using Virtual Environment to Analyze Cyber-Attacks on Smart Grid Protocol. Preprints 2023. [CrossRef]
- Banik, S.; Banik, T.; Hossain, S.; Saha, S.K. Implementing Man-in-the-Middle Attack to Investigate Network Vulnerabilities in Smart Grid Test-bed. arXiv preprint arXiv:2306.00234 2023.
- Kulkarni, S.; Rahul, R.; Shreyas, R.; Nagasundari, S.; Honnavalli, P.B. MITM intrusion analysis for advanced metering infrastructure communication in a smart grid environment. In Proceedings of the Trends in Computational Intelligence, Security and Internet of Things: Third International Conference, ICCISIoT 2020, Tripura, India, December 29-30, 2020, Proceedings 3. Springer, 2020, pp. 256–267.
- Banik, S.; Manicavasagam, R.; Banik, T.; Banik, S. Simulation and Analysis of Cyber-Attack on Modbus Protocol for Smart Grids in Virtual Environment. In Proceedings of the Science and Information Conference. Springer, 2024, pp. 384–401.
- Pavithra, L.; Rekha, D. Prevention of replay attack for isolated smart grid. In Proceedings of the Next Generation Information Processing System: Proceedings of ICCET 2020, Volume 2. Springer, 2021, pp. 251–258.
- Bhattacharjee, S.; Madhavarapu, V.P.K.; Silvestri, S.; Das, S.K. Attack context embedded data driven trust diagnostics in smart metering infrastructure. ACM Transactions on Privacy and Security (TOPS) 2021, 24, 1–36. [CrossRef]
- Khan, Z.A.; Adil, M.; Javaid, N.; Saqib, M.N.; Shafiq, M.; Choi, J.G. Electricity theft detection using supervised learning techniques on smart meter data. Sustainability 2020, 12, 8023. [CrossRef]
- Ismail, M.; Shahin, M.; Shaaban, M.F.; Serpedin, E.; Qaraqe, K. Efficient detection of electricity theft cyber attacks in AMI networks. In Proceedings of the 2018 IEEE wireless communications and networking conference (WCNC). IEEE, 2018, pp. 1–6.
- Na, L.; Xiaohui, X.; Xiaoqin, M.; Xiangfu, M.; Peisen, Y. Fake data injection attack detection in AMI system using a hybrid method. In Proceedings of the 2021 IEEE Sustainable Power and Energy Conference (iSPEC). IEEE, 2021, pp. 2371–2376.
- Bi, J.; Luo, F.; Liang, G.; Yang, X.; He, S.; Dong, Z.Y. Impact assessment and defense for smart grids with FDIA against AMI. IEEE Transactions on Network Science and Engineering 2022, 10, 578–591. [CrossRef]
- Wei, L.; Rondon, L.P.; Moghadasi, A.; Sarwat, A.I. Review of cyber-physical attacks and counter defense mechanisms for advanced metering infrastructure in smart grid. In Proceedings of the 2018 IEEE/PES Transmission and Distribution Conference and Exposition (T&D). IEEE, 2018, pp. 1–9.
- Nabil, M.; Ismail, M.; Mahmoud, M.; Shahin, M.; Qaraqe, K.; Serpedin, E. Deep learning-based detection of electricity theft cyber-attacks in smart grid AMI networks. Deep learning applications for cyber security 2019, pp. 73–102.
- Jokar, P.; Leung, V.C. Intrusion detection and prevention for ZigBee-based home area networks in smart grids. IEEE Transactions on Smart Grid 2016, 9, 1800–1811. [CrossRef]
- Anderson, R.; Fuloria, S. Who controls the off switch? In Proceedings of the 2010 First IEEE International Conference on Smart Grid Communications. IEEE, 2010, pp. 96–101.
- Anwar, A.; Mahmood, A.N.; Tari, Z. Identification of vulnerable node clusters against false data injection attack in an AMI based smart grid. Information Systems 2015, 53, 201–212. [CrossRef]
- Banik, S.; Saha, S.K.; Banik, T.; Hossain, S. Anomaly Detection Techniques in Smart Grid Systems: A Review. arXiv preprint arXiv:2306.02473 2023.
- Aburomman, A.A.; Reaz, M.B.I. A survey of intrusion detection systems based on ensemble and hybrid classifiers. Computers & security 2017, 65, 135–152. [CrossRef]
- Zhou, C.V.; Leckie, C.; Karunasekera, S. A survey of coordinated attacks and collaborative intrusion detection. computers & security 2010, 29, 124–140. [CrossRef]
- Arshad, J.; Azad, M.A.; Amad, R.; Salah, K.; Alazab, M.; Iqbal, R. A review of performance, energy and privacy of intrusion detection systems for IoT. Electronics 2020, 9, 629. [CrossRef]
- Berman, D.S.; Buczak, A.L.; Chavis, J.S.; Corbett, C.L. A survey of deep learning methods for cyber security. Information 2019, 10, 122. [CrossRef]
- Tong, W.; Lu, L.; Li, Z.; Lin, J.; Jin, X. A survey on intrusion detection system for advanced metering infrastructure. In Proceedings of the 2016 Sixth International Conference on Instrumentation & Measurement, Computer, Communication and Control (IMCCC). IEEE, 2016, pp. 33–37.
- Mirzaee, P.H.; Shojafar, M.; Cruickshank, H.; Tafazolli, R. Smart grid security and privacy: From conventional to machine learning issues (threats and countermeasures). IEEE access 2022, 10, 52922–52954. [CrossRef]
- Grochocki, D.; Huh, J.H.; Berthier, R.; Bobba, R.; Sanders, W.H.; Cárdenas, A.A.; Jetcheva, J.G. AMI threats, intrusion detection requirements and deployment recommendations. In Proceedings of the 2012 IEEE Third International Conference on Smart Grid Communications (SmartGridComm). IEEE, 2012, pp. 395–400.
- Marchese, D.; Jin, A.; Fox-Lent, C.; Linkov, I. Resilience for smart water systems. Journal of Water Resources Planning and Management 2020, 146, 02519002. [CrossRef]
- Aravinthan, V.; Namboodiri, V.; Sunku, S.; Jewell, W. Wireless AMI application and security for controlled home area networks. In Proceedings of the 2011 IEEE Power and Energy Society General Meeting. IEEE, 2011, pp. 1–8.
- Faisal, M.A.; Aung, Z.; Williams, J.R.; Sanchez, A. Data-stream-based intrusion detection system for advanced metering infrastructure in smart grid: A feasibility study. IEEE Systems journal 2014, 9, 31–44. [CrossRef]
- Zhang, K.; Hu, Z.; Zhan, Y.; Wang, X.; Guo, K. A smart grid AMI intrusion detection strategy based on extreme learning machine. Energies 2020, 13, 4907. [CrossRef]
- Attia, M.; Sedjelmaci, H.; Senouci, S.M.; Aglzim, E.H. A new intrusion detection approach against lethal attacks in the smart grid: temporal and spatial based detections. In Proceedings of the 2015 Global Information Infrastructure and Networking Symposium (GIIS). IEEE, 2015, pp. 1–3.
- Albuquerque Filho, J.; Brandão, L.C.; Fernandes, B.J.; Maciel, A.M. A review of neural networks for anomaly detection. IEEE Access 2022. [CrossRef]
- Sun, C.C.; Hahn, A.; Liu, C.C. Cyber security of a power grid: State-of-the-art. International Journal of Electrical Power & Energy Systems 2018, 99, 45–56. [CrossRef]
- Denning, D.E. An intrusion-detection model. IEEE Transactions on software engineering 1987, pp. 222–232. [CrossRef]
- Chandola, V.; Banerjee, A.; Kumar, V. Anomaly detection: A survey. ACM computing surveys (CSUR) 2009, 41, 1–58.
- Yen, S.W.; Morris, S.; Ezra, M.A.; Huat, T.J. Effect of smart meter data collection frequency in an early detection of shorter-duration voltage anomalies in smart grids. International journal of electrical power & energy systems 2019, 109, 1–8. [CrossRef]
- Prabhakar, P.; Arora, S.; Khosla, A.; Beniwal, R.K.; Arthur, M.N.; Arias-Gonzáles, J.L.; Areche, F.O.; et al. Cyber Security of Smart Metering Infrastructure Using Median Absolute Deviation Methodology. Security and Communication Networks 2022, 2022. [CrossRef]
- Berthier, R.; Sanders, W.H. Specification-based intrusion detection for advanced metering infrastructures. In Proceedings of the 2011 IEEE 17th Pacific rim international symposium on dependable computing. IEEE, 2011, pp. 184–193.
- Jokar, P.; Nicanfar, H.; Leung, V.C. Specification-based intrusion detection for home area networks in smart grids. In Proceedings of the 2011 IEEE International Conference on Smart Grid Communications (SmartGridComm). IEEE, 2011, pp. 208–213.
- Ruan, H.M.; Yeap, G.W.; Lei, C.L. Hybrid intrusion detection framework for advanced metering infrastructure. In Intelligent Systems and Applications; IOS Press, 2015; pp. 894–903.
- Khan, R.; Albalushi, A.; McLaughlin, K.; Laverty, D.; Sezer, S. Model based intrusion detection system for synchrophasor applications in smart grid. In Proceedings of the 2017 IEEE Power & Energy Society General Meeting. IEEE, 2017, pp. 1–5.
- Zarpelão, B.B.; Miani, R.S.; Kawakani, C.T.; de Alvarenga, S.C. A survey of intrusion detection in Internet of Things. Journal of Network and Computer Applications 2017, 84, 25–37. [CrossRef]
- Liu, Q.; Hagenmeyer, V.; Keller, H.B. A review of rule learning-based intrusion detection systems and their prospects in smart grids. IEEE Access 2021, 9, 57542–57564. [CrossRef]
- Farooqi, A.H.; Khan, F.A. Intrusion detection systems for wireless sensor networks: A survey. In Proceedings of the International Conference on Future Generation Communication and Networking. Springer, 2009, pp. 234–241.
- Kasinathan, P.; Pastrone, C.; Spirito, M.A.; Vinkovits, M. Denial-of-Service detection in 6LoWPAN based Internet of Things. In Proceedings of the 2013 IEEE 9th international conference on wireless and mobile computing, networking and communications (WiMob). IEEE, 2013, pp. 600–607.
- Wallgren, L.; Raza, S.; Voigt, T. Routing attacks and countermeasures in the RPL-based internet of things. International Journal of Distributed Sensor Networks 2013, 9, 794326. [CrossRef]
- Jithish, J.; Alangot, B.; Mahalingam, N.; Yeo, K.S. Distributed anomaly detection in smart grids: a federated learning-based approach. IEEE Access 2023, 11, 7157–7179. [CrossRef]
- Tariq, N.; Alsirhani, A.; Humayun, M.; Alserhani, F.; Shaheen, M. A fog-edge-enabled intrusion detection system for smart grids. Journal of Cloud Computing 2024, 13, 43.
- Faisal, M.A.; Aung, Z.; Williams, J.R.; Sanchez, A. Securing advanced metering infrastructure using intrusion detection system with data stream mining. In Proceedings of the Intelligence and Security Informatics: Pacific Asia Workshop, PAISI 2012, Kuala Lumpur, Malaysia, May 29, 2012. Proceedings. Springer, 2012, pp. 96–111.
- Zhang, Y.; Wang, L.; Sun, W.; Green II, R.C.; Alam, M. Distributed intrusion detection system in a multi-layer network architecture of smart grids. IEEE Transactions on Smart Grid 2011, 2, 796–808.
- Yaacoub, J.P.A.; Salman, O.; Noura, H.N.; Kaaniche, N.; Chehab, A.; Malli, M. Cyber-physical systems security: Limitations, issues and future trends. Microprocessors and microsystems 2020, 77, 103201. [CrossRef]
- Le, A.; Loo, J.; Chai, K.K.; Aiash, M. A specification-based IDS for detecting attacks on RPL-based network topology. Information 2016, 7, 25. [CrossRef]
- Raza, S.; Wallgren, L.; Voigt, T. SVELTE: Real-time intrusion detection in the Internet of Things. Ad hoc networks 2013, 11, 2661–2674. [CrossRef]
- Pongle, P.; Chavan, G. Real time intrusion and wormhole attack detection in internet of things. International Journal of Computer Applications 2015, 121. [CrossRef]
- Thanigaivelan, N.K.; Nigussie, E.; Kanth, R.K.; Virtanen, S.; Isoaho, J. Distributed internal anomaly detection system for Internet-of-Things. In Proceedings of the 2016 13th IEEE annual consumer communications & networking conference (CCNC). IEEE, 2016, pp. 319–320.
- Lo, C.H.; Ansari, N. CONSUMER: A novel hybrid intrusion detection system for distribution networks in smart grid. IEEE Transactions on Emerging Topics in Computing 2013, 1, 33–44. [CrossRef]
- Sahani, N.; Zhu, R.; Cho, J.H.; Liu, C.C. Machine Learning-based Intrusion Detection for Smart Grid Computing: A Survey. ACM Transactions on Cyber-Physical Systems 2023, 7, 1–31. [CrossRef]
- Bondok, A.H.; Mahmoud, M.; Badr, M.M.; Fouda, M.M.; Abdallah, M.; Alsabaan, M. Novel evasion attacks against adversarial training defense for smart grid federated learning. IEEE Access 2023. [CrossRef]
- Sun, X.; Tang, Z.; Du, M.; Deng, C.; Lin, W.; Chen, J.; Qi, Q.; Zheng, H. A hierarchical federated learning-based intrusion detection system for 5g smart grids. Electronics 2022, 11, 2627. [CrossRef]
- Khraisat, A.; Alazab, A.; Singh, S.; Jan, T.; Jr. Gomez, A. Survey on federated learning for intrusion detection system: Concept, architectures, aggregation strategies, challenges, and future directions. ACM Computing Surveys 2024, 57, 1–38.
- Li, B.; Wu, Y.; Song, J.; Lu, R.; Li, T.; Zhao, L. DeepFed: Federated deep learning for intrusion detection in industrial cyber–physical systems. IEEE Transactions on Industrial Informatics 2020, 17, 5615–5624. [CrossRef]
- Vijayanand, R.; Devaraj, D.; Kannapiran, B. A novel deep learning based intrusion detection system for smart meter communication network. In Proceedings of the 2019 IEEE International Conference on Intelligent Techniques in Control, Optimization and Signal Processing (INCOS). IEEE, 2019, pp. 1–3.
- Song, K.; Kim, P.; Tyagi, V.; Rajasekaran, S. Artificial immune system (AIS) based intrusion detection system (IDS) for smart grid advanced metering infrastructure (AMI) networks. Technical report, Virginia Tech, 2018.
- Radoglou Grammatikis, P.; Sarigiannidis, P.; Efstathopoulos, G.; Panaousis, E. ARIES: A novel multivariate intrusion detection system for smart grid. Sensors 2020, 20, 5305. [CrossRef]
- Pan, S.; Morris, T.H.; Adhikari, U. A specification-based intrusion detection framework for cyber-physical environment in electric power system. Int. J. Netw. Secur. 2015, 17, 174–188.
- Mohan, S.N.; Ravikumar, G.; Govindarasu, M. Distributed intrusion detection system using semantic-based rules for SCADA in smart grid. In Proceedings of the 2020 IEEE/PES Transmission and Distribution Conference and Exposition (T&D). IEEE, 2020, pp. 1–5.
- Kwon, Y.; Kim, H.K.; Lim, Y.H.; Lim, J.I. A behavior-based intrusion detection technique for smart grid infrastructure. In Proceedings of the 2015 IEEE Eindhoven PowerTech. IEEE, 2015, pp. 1–6.
- Fadel, E.; Gungor, V.C.; Nassef, L.; Akkari, N.; Malik, M.A.; Almasri, S.; Akyildiz, I.F. A survey on wireless sensor networks for smart grid. Computer Communications 2015, 71, 22–33. [CrossRef]
- Longe, O.M.; Ouahada, K.; Ferreira, H.C.; Rimer, S. Wireless sensor networks and advanced metering infrastructure deployment in smart grid. In Proceedings of the e-Infrastructure and e-Services for Developing Countries: 5th International Conference, AFRICOMM 2013, Blantyre, Malawi, November 25-27, 2013, Revised Selected Papers 5. Springer, 2014, pp. 167–171.
- Banik, S.; Banik, T.; Banik, S. Intrusion detection system in smart grid-a review, 2023.
- Ioulianou, P.; Vasilakis, V.; Moscholios, I.; Logothetis, M. A signature-based intrusion detection system for the internet of things. Information and Communication Technology Form 2018.
- Efstathopoulos, G.; Grammatikis, P.R.; Sarigiannidis, P.; Argyriou, V.; Sarigiannidis, A.; Stamatakis, K.; Angelopoulos, M.K.; Athanasopoulos, S.K. Operational data based intrusion detection system for smart grid. In Proceedings of the 2019 IEEE 24th international workshop on computer aided modeling and design of communication links and networks (CAMAD). IEEE, 2019, pp. 1–6.
- Radoglou-Grammatikis, P.I.; Sarigiannidis, P.G. An anomaly-based intrusion detection system for the smart grid based on cart decision tree. In Proceedings of the 2018 global information infrastructure and networking symposium (GIIS). IEEE, 2018, pp. 1–5.
- Khoei, T.T.; Aissou, G.; Hu, W.C.; Kaabouch, N. Ensemble learning methods for anomaly intrusion detection system in smart grid. In Proceedings of the 2021 IEEE international conference on electro information technology (EIT). IEEE, 2021, pp. 129–135.
- Rose, T.; Kifayat, K.; Abbas, S.; Asim, M. A hybrid anomaly-based intrusion detection system to improve time complexity in the Internet of Energy environment. Journal of Parallel and Distributed Computing 2020, 145, 124–139. [CrossRef]
- AlHaddad, U.; Basuhail, A.; Khemakhem, M.; Eassa, F.E.; Jambi, K. Ensemble model based on hybrid deep learning for intrusion detection in smart grid networks. Sensors 2023, 23, 7464. [CrossRef]
- Pan, S.; Morris, T.; Adhikari, U. Developing a hybrid intrusion detection system using data mining for power systems. IEEE Transactions on Smart Grid 2015, 6, 3104–3113. [CrossRef]
- Chavez, A.; Lai, C.; Jacobs, N.; Hossain-McKenzie, S.; Jones, C.B.; Johnson, J.; Summers, A. Hybrid intrusion detection system design for distributed energy resource systems. In Proceedings of the 2019 IEEE CyberPELS (CyberPELS). IEEE, 2019, pp. 1–6.
- Abou-Elasaad, M.M.; Sayed, S.G.; El-Dakroury, M.M. Smart Grid intrusion detection system based on AI techniques. Journal of Cybersecurity & Information Management 2025, 15. [CrossRef]
- Vigna, G.; Kemmerer, R.A. NetSTAT: A network-based intrusion detection system. Journal of computer security 1999, 7, 37–71.
- Liu, M.; Xue, Z.; Xu, X.; Zhong, C.; Chen, J. Host-based intrusion detection system with system calls: Review and future trends. ACM computing surveys (CSUR) 2018, 51, 1–36.
- Gassais, R.; Ezzati-Jivan, N.; Fernandez, J.M.; Aloise, D.; Dagenais, M.R. Multi-level host-based intrusion detection system for Internet of things. Journal of Cloud Computing 2020, 9, 62. [CrossRef]
- Sen, O.; Hassan, T.; Ulbig, A.; Henze, M. Enhancing scada security: Developing a host-based intrusion detection system to safeguard against cyberattacks. arXiv preprint arXiv:2402.14599 2024.
- Li, B.; Lu, R.; Wang, W.; Choo, K.K.R. Distributed host-based collaborative detection for false data injection attacks in smart grid cyber-physical system. Journal of Parallel and Distributed Computing 2017, 103, 32–41. [CrossRef]
- Hu, Z.; Liu, S.; Luo, W.; Wu, L. Intrusion-detector-dependent distributed economic model predictive control for load frequency regulation with PEVs under cyber attacks. IEEE Transactions on Circuits and Systems I: Regular Papers 2021, 68, 3857–3868. [CrossRef]
- Rani, M.; et al. A review of intrusion detection system in cloud computing. In Proceedings of the Proceedings of International Conference on Sustainable Computing in Science, Technology and Management (SUSCOM), Amity University Rajasthan, Jaipur-India, 2019.
- Abdelkhalek, M.; Ravikumar, G.; Govindarasu, M. Ml-based anomaly detection system for der communication in smart grid. In Proceedings of the 2022 IEEE Power & Energy Society Innovative Smart Grid Technologies Conference (ISGT). IEEE, 2022, pp. 1–5.
- Sen, P.; Waghmare, S. Machine learning based intrusion detection system for real-time smart grid security. In Proceedings of the 2021 13th IEEE PES Asia Pacific Power & Energy Engineering Conference (APPEEC). IEEE, 2021, pp. 1–6.
- Prasad, G.; Huo, Y.; Lampe, L.; Leung, V.C. Machine learning based physical-layer intrusion detection and location for the smart grid. In Proceedings of the 2019 IEEE International Conference on Communications, Control, and Computing Technologies for Smart Grids (SmartGridComm). IEEE, 2019, pp. 1–6.
- Otoum, S.; Kantarci, B.; Mouftah, H.T. Mitigating False Negative intruder decisions in WSN-based Smart Grid monitoring. In Proceedings of the 2017 13th International wireless communications and mobile computing conference (IWCMC). IEEE, 2017, pp. 153–158.
- Cárdenas, A.A.; Baras, J.S.; Seamon, K. A framework for the evaluation of intrusion detection systems. In Proceedings of the 2006 IEEE Symposium on Security and Privacy (S&P’06). IEEE, 2006, pp. 15–pp.
- Bai, K.Z.; Fossaceca, J.M. EM-AUC: A Novel Algorithm for Evaluating Anomaly Based Network Intrusion Detection Systems. Sensors 2024, 25, 78. [CrossRef]
- Puccetti, T.; Ceccarelli, A. Detection Latencies of Anomaly Detectors-An Overlooked Perspective? In Proceedings of the 2024 IEEE 35th International Symposium on Software Reliability Engineering (ISSRE). IEEE, 2024, pp. 37–48.
- Sedik, A.; Faragallah, O.S.; El-sayed, H.S.; El-Banby, G.M.; El-Samie, F.E.A.; Khalaf, A.A.; El-Shafai, W. An efficient cybersecurity framework for facial video forensics detection based on multimodal deep learning. Neural Computing and Applications 2022, pp. 1–18. [CrossRef]
- Raza, A.; Munir, K.; Almutairi, M. A novel deep learning approach for deepfake image detection. Applied Sciences 2022, 12, 9820. [CrossRef]
- Khalid, H.; Kim, M.; Tariq, S.; Woo, S.S. Evaluation of an audio-video multimodal deepfake dataset using unimodal and multimodal detectors. In Proceedings of the Proceedings of the 1st workshop on synthetic multimedia-audiovisual deepfake generation and detection, 2021, pp. 7–15.
- Zhou, F.; Wen, G.; Ma, Y.; Geng, H.; Huang, R.; Pei, L.; Yu, W.; Chu, L.; Qiu, R. A comprehensive survey for deep-learning-based abnormality detection in smart grids with multimodal image data. Applied Sciences 2022, 12, 5336. [CrossRef]
- Ullah, F.; Turab, A.; Ullah, S.; Cacciagrano, D.; Zhao, Y. Enhanced Network Intrusion Detection System for Internet of Things Security Using Multimodal Big Data Representation with Transfer Learning and Game Theory. Sensors 2024, 24, 4152. [CrossRef]
- Zhang, Y.; Wang, J.; Chen, B. Detecting false data injection attacks in smart grids: A semi-supervised deep learning approach. IEEE Transactions on Smart Grid 2020, 12, 623–634. [CrossRef]
- Kiflay, A.; Tsokanos, A.; Fazlali, M.; Kirner, R. Network intrusion detection leveraging multimodal features. Array 2024, 22, 100349. [CrossRef]
- Sweeten, J. Multi-Modal Intrusion Detection in Cyber-Physical Smart Power Grids. Master’s thesis, Tennessee Technological University, 2023.
- Shilay, D.M.; Lorey, K.G.; Weiz, T.; Lovetty, T.; Cheng, Y. Catching anomalous distributed photovoltaics: An edge-based multi-modal anomaly detection. arXiv preprint arXiv:1709.08830 2017. [CrossRef]
- Asiri, M.; Saxena, N.; Gjomemo, R.; Burnap, P. Understanding indicators of compromise against cyber-attacks in industrial control systems: a security perspective. ACM transactions on cyber-physical systems 2023, 7, 1–33.
- Manicavasagam, R. Identifying and Detecting Network Indicators of Compromise (IOCs) for Demand Response Programs. PhD thesis, Tennessee Technological University, 2023.
- Zaboli, A.; Hong, J.; Ştefanov, A.; Liu, C.C.; Hwang, C.S. Large Language Models for Power System Security: A Novel Multi-Modal Approach for Anomaly Detection in Energy Management Systems. IEEE Access 2025, 13, 203558–203585.
- Korba, A.A.; Tamani, N.; Ghamri-Doudane, Y.; et al. Anomaly-based framework for detecting power overloading cyberattacks in smart grid AMI. Computers & Security 2020, 96, 101896. [CrossRef]
- Dong, Y. Correlation-Driven Multi-Level Multimodal Learning for Anomaly Detection on Smart Electric Grid. In Proceedings of the 2025 2nd International Conference on Smart Grid and Artificial Intelligence (SGAI). IEEE, 2025, pp. 254–257.
- Xia, Z.; Tang, H.; Hu, Z.; Zhou, H. Efficient intrusion detection in ami systems based on federated semi-supervised learning. IEEE Transactions on Network Science and Engineering 2025. [CrossRef]
- Broni, K.; Mills, G. Intrusion Detection for Advanced Metering Infrastructure using Machine Learning. In Proceedings of the 2024 IEEE 9th International Conference on Adaptive Science and Technology (ICAST). IEEE, 2024, Vol. 9, pp. 1–8.
- SMH, S.S.F. Real-time implementation of IoT Enabled Cyber Attack Detection System (IoT-E-CADS) in Advanced Metering Infrastructure (AMI) using Machine Learning Technique (MLT). IoT 2024.
- Abdullakutty, F.; Elyan, E.; Johnston, P. A review of state-of-the-art in Face Presentation Attack Detection: From early development to advanced deep learning and multi-modal fusion methods. Information fusion 2021, 75, 55–69. [CrossRef]
- Hadi, H.J.; Cao, Y.; Hussain, F.B.; Ahamad, N.; Alshara, M.A.; Ullah, I.; Javed, Y.; He, Y.; Jamil, A.M. Reducing False Positives in Intrusion Detection System Alerts: A Novel Aggregation and Correlation Model. In Proceedings of the International Conference on Digital Forensics and Cyber Crime. Springer, 2025, pp. 153–167.
- Alserhani, F.M. Alert correlation and aggregation techniques for reduction of security alerts and detection of multistage attack. International Journal of Advanced Studies in Computers, Science and Engineering 2016, 5, 1.
- Huang, W.; Wang, D.; Ouyang, X.; Wan, J.; Liu, J.; Li, T. Multimodal federated learning: Concept, methods, applications and future directions. Information Fusion 2024, 112, 102576. [CrossRef]
- Zhao, Y.; Barnaghi, P.; Haddadi, H. Multimodal federated learning on iot data. In Proceedings of the 2022 IEEE/ACM Seventh International Conference on Internet-of-Things Design and Implementation (IoTDI). IEEE, 2022, pp. 43–54.
- Li, X.J.; Ma, M.; Sun, Y. An adaptive deep learning neural network model to enhance machine-learning-based classifiers for intrusion detection in smart grids. Algorithms 2023, 16, 288. [CrossRef]
- Andresini, G.; Appice, A.; Di Mauro, N.; Loglisci, C.; Malerba, D. Multi-channel deep feature learning for intrusion detection. IEEE Access 2020, 8, 53346–53359. [CrossRef]
- Upadhyay, D.; Manero, J.; Zaman, M.; Sampalli, S. Gradient boosting feature selection with machine learning classifiers for intrusion detection on power grids. IEEE Transactions on Network and Service Management 2020, 18, 1104–1116. [CrossRef]
- Baltrušaitis, T.; Ahuja, C.; Morency, L.P. Multimodal machine learning: A survey and taxonomy. IEEE transactions on pattern analysis and machine intelligence 2018, 41, 423–443. [CrossRef]
- Kang, B.; McLaughlin, K.; Sezer, S. Towards a stateful analysis framework for smart grid network intrusion detection. In Proceedings of the 4th International Symposium for ICS & SCADA Cyber Security Research 2016. BCS Learning & Development, 2016.
| Type of Attacks | Target Surface in AMI | Attacker’s Goals | Potential Threat Actor | |||
|---|---|---|---|---|---|---|
| Espionage | Data Theft | Energy Theft | Disruption of Grid | |||
| Advanced Persistent Threats (APT) | - Network Infrastructure - Physical Infrastructure - Data Concentrators and Gateways - Utility Backend Systems |
✓ | ✓ | ✓ | - Nation-State Actors - Hacktivists - Cybercriminals - Insiders - Competitors |
|
| Denial of Service (DoS) | - NAN Network - Smart Meters - Data Concentrator |
✓ | ✓ | ✓ | - Nation-State Actors - Cybercriminals |
|
| Packet Sniffing | - Network Infrastructure - Communication Channel |
✓ | ✓ | ✓ | - Nation-State Actors - Hacktivists - Cybercriminals - Insiders - Competitors |
|
| Nation-State Attacks | - Eavesdropping - Man-in-the-Middle (MitM) - Replay Attacks - Denial of Service (DoS) - Jamming |
✓ | ✓ | ✓ | - Nation-State Actors - Hacktivists - Cybercriminals |
|
| False Data Injection Attacks (FDIA) | - Manipulating Meter Data - Injecting False Consumption Data |
✓ | ✓ | ✓ | - Nation-State Actors - Hacktivists - Cybercriminals - Insiders - Competitors |
|
| Authentication and Authorization Attacks | - Credential Theft - Privilege Escalation - Unauthorized Remote Access |
✓ | ✓ | ✓ | - Nation-State Actors - Hacktivists - Cybercriminals - Insiders - Competitors |
|
| Malware and Exploits | - Malware Insertion - Exploiting Software Vulnerabilities - RAM Exhaustion - CPU Overloading |
✓ | ✓ | ✓ | - Nation-State Actors - Hacktivists - Cybercriminals - Insiders - Competitors |
|
| Physical Attacks | - Tampering with Smart Meters - Device Theft or Replacement |
✓ | ✓ | ✓ | - Hacktivists - Cybercriminals - Insiders - Competitors |
|
| Rogue Devices Attacks | - Inserting Rogue Smart Meters - Malicious Data Concentrators |
✓ | ✓ | ✓ | - Nation-State Actors - Hacktivists - Cybercriminals - Insiders - Competitors |
|
| Time Synchronization Attacks | - Manipulating Timestamps - Disrupting Time Synchronization Protocols |
✓ | ✓ | ✓ | - Nation-State Actors - Hacktivists - Cybercriminals - Insiders - Competitors |
|
| Social Engineering Attacks | - Phishing - Spear Phishing - Pretexting - Baiting - Quid Pro Quo - Impersonation - Tailgating |
✓ | ✓ | ✓ | - Nation-State Actors - Hacktivists - Cybercriminals - Insiders - Competitors |
|
| Supply Chain Attacks | - Compromised Smart Meters - Malware in Software Updates |
✓ | - Nation-State Actors - Hacktivists - Cybercriminals - Insiders - Competitors |
|||
| Type of IDSs | Detection Accuracy | Scalability | Complexity | New Threat Detection |
|---|---|---|---|---|
| Signature-Based IDSs [94,95] | High for known threats | High | Low | No |
| Anomaly-Based IDSs [87,96,97] | Moderate | Moderate | Moderate | Yes |
| Hybrid IDSs [98,99,100,101] | High | Moderate | High | Yes |
| Network-Based IDSs (NIDSs) [73,102,103] | High | High | Moderate | Yes |
| Host-Based IDSs (HIDSs) [104,105,106] | High | Low | High | Yes |
| Distributed IDSs (DIDSs) [107,108,109] | High | High | High | Yes |
| ML-Based IDSs [80,110,111,112] | High | High | Very High | Yes |
| Ref # | Application domain |
Type of IDSs | Type of Dataset | Type of Attack | Using Multi Modal Data |
Using IoC Metric |
|---|---|---|---|---|---|---|
| Sun et al. [13] 2020 |
AMI | Hybrid IDS | Network Traffic Meter Data |
✗ | ✗ | ✗ |
| Radoglou et al. [87] 2020 |
SG | Anomaly Based IDS |
Network Traffic Modbus Data Operational Data |
DoS Brute Force Port Scanning |
✓ | ✗ |
| Zaboli et al. [128] 2025 |
Scada | ✗ | Energy Consumption Data |
Energy Theft | ✗ | ✗ |
| Korba et al. [129] 2020 |
AMI | Anomaly Based IDS |
Energy Consumption Data |
Power overloading cyberattacks |
✗ | ✗ |
| Sun et al. [82] 2022 |
AMI | Hierarchical Federated Learning IDS (HFed-IDSs) |
Network Traffic Data |
DoS Probing scanning (Probe) Remote to local (R2L) User to root (U2R) |
✗ | ✗ |
| Atef et al. [81] 2023 |
AMI | Federated Learning Based (FL-IDS) |
Energy Consumption Data |
Evasion Attacks | ✗ | ✗ |
| Bhattacharjee et al. [32] 2021 |
AMI smart meters |
Context-aware Anomaly Based IDS |
Power consumption time-series Data |
FDI Attack | ✗ | ✗ |
| Kiflay et al. [123] 2024 |
✗ | Network Based IDS |
Flow-based & Payload-based Data |
Various Cyber Attack |
✓ | ✗ |
| Asiri et al. [126] 2023 |
SCADA | Network Based IDS |
✗ | Various Cyber Attacks |
✗ | ✓ |
| Jacob et al. [124] 2023 |
SG | Graph Neural Networks Based IDS |
CPS Testbed | FDI, Backdoor Brute Force Reverse Shell Ransomware |
✓ | ✗ |
| Rajesh et al. [127] 2023 |
SCADA | Network Based IDS |
Flow-based & Payload-based Data |
Various Cyber Attacks |
✗ | ✓ |
| Li et al. [84] 2020 |
CPS | DeepFed Based IDS |
Network Traffic Data |
Response Injection Reconnaissance Attack Command Injection |
✗ | ✗ |
| Dong et al. [130] 2025 |
Energy Management System | Deep Multimodal Anomaly Based IDS |
Energy Consumption Data |
✗ | ✓ | ✗ |
| Xia et al. [131] 2025 |
AMI | Federated Semi-Supervised IDS |
Network Traffic Data |
Cyber Network-level Attacks | ✗ | ✗ |
| Kenneth et al. [132] 2024 |
AMI | ML Based IDS |
Network Traffic Data |
DoS DDoS |
✗ | ✗ |
| Dong et al. [130] 2025 |
Energy Management System | Deep Multimodal Anomaly Based IDS |
Energy Consumption Data |
✗ | ✓ | ✗ |
| SMH et al. [133] 2024 |
AMI | Anomaly Based IDS |
Meter Data |
FDI Attack | ✗ | ✗ |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




