Submitted:
10 April 2026
Posted:
14 April 2026
You are already at the latest version
Abstract
Keywords:
Introduction
System Architecture
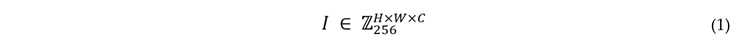
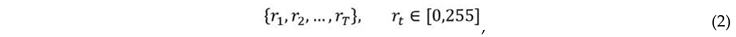
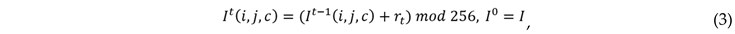
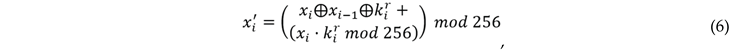
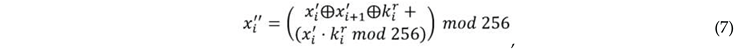
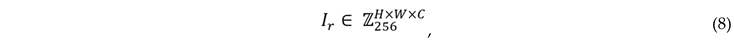
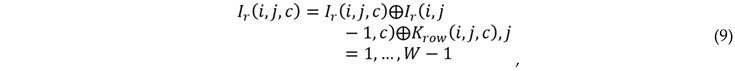
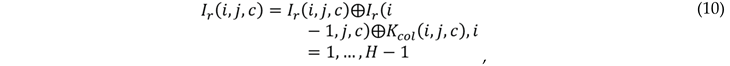
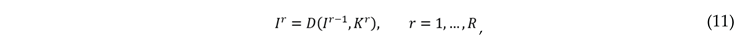
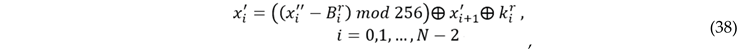
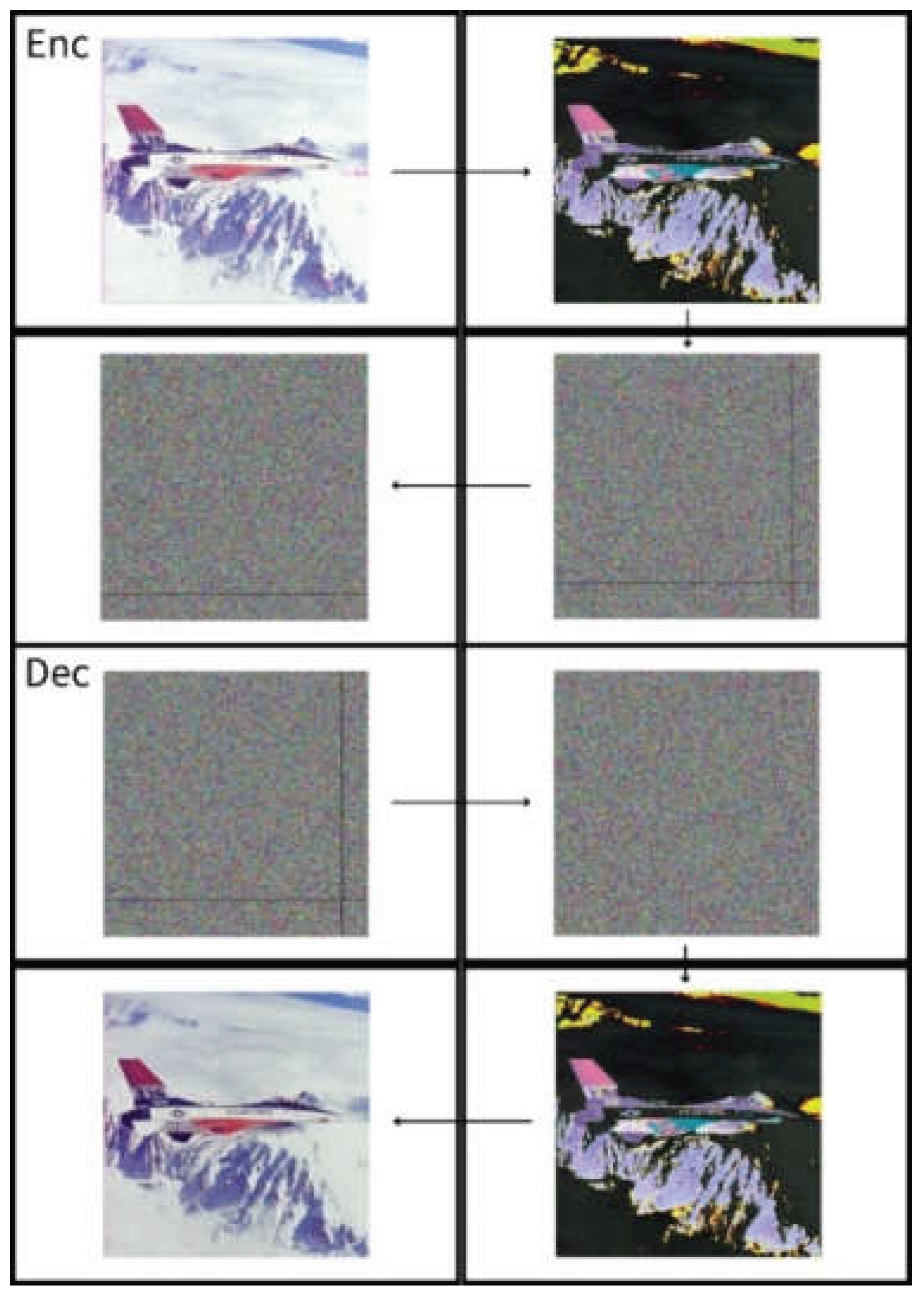
Encryption: Step 1 – Threshold Perturbation and Strong Diffusion


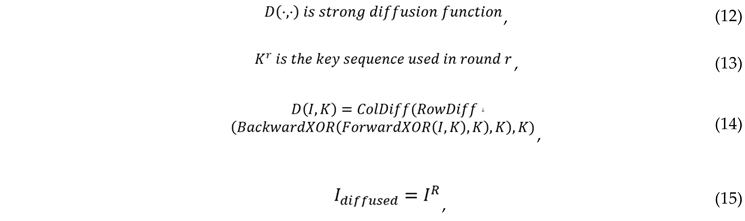
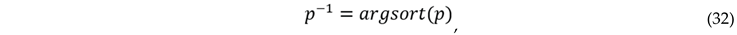
Step2: Padding and Random Permutation
- Row permutation: Each row of the image is shuffled according to an order generated by a random seed.
- Column permutation: Each column of the image is rearranged based on a permutation sequence generated from a random seed.
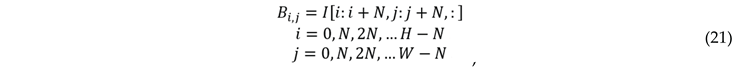
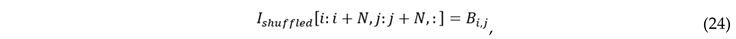
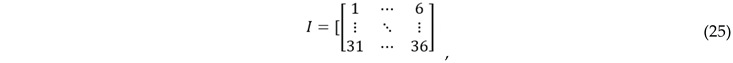
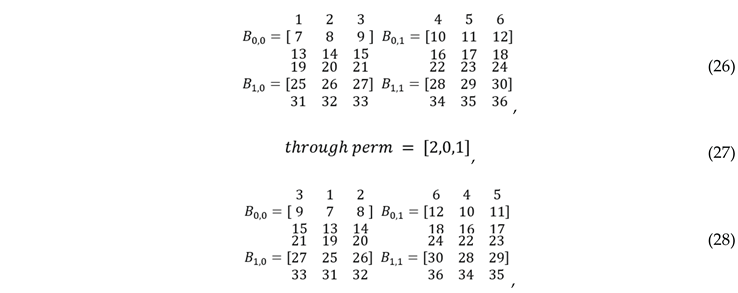
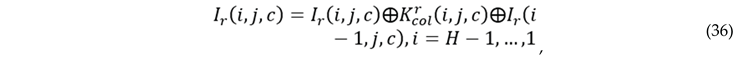
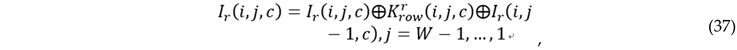
Step3: Sudoku-Based Pixel Permutation
-
Block partitioning: The image is divided into multiple non-overlapping blocks.
-
Intra-block column permutation: For each block Bi,jB_{i,j}Bi,j, the column indices of every row rrr are permuted according to the predefined Sudoku permutation mapping.

-
Color image processing: For color images, the permutation is applied simultaneously across all channels to maintain inter-channel consistency.

-
Reconstruction: After completing the internal permutation within each block, all blocks are reassembled to reconstruct the image.
Step4: Image Rotation Transformation
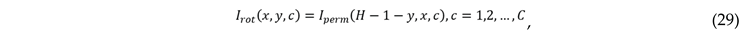
Decryption: Step 1 – Inverse Rotation

Step2: Inverse Pixel Permutation Based on Sudoku Structure


Step3: Inverse Padding and Inverse Row–Column Permutation

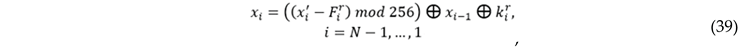
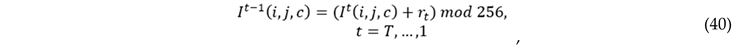
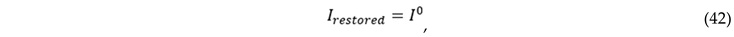
Step4 : Iterative Threshold and Strong Diffusion Decryption


Analysis
Discussion
References
- Mhatre, M.; Kashid, H.; Jain, T.; Chavan, P. BCPIS: Blockchain-based counterfeit product identification system. Journal of Applied Security Research 2022, 1–26. [Google Scholar] [CrossRef]
- Mehta, K.; Dhingra, G.; Mangrulkar, R. Enhancing multimedia security using shortest weight first algorithm and symmetric cryptography. Journal of Applied Security Research 2022, 1–24. [Google Scholar] [CrossRef]
- Saidi, R.; Cherrid, N.; Bentahar, T.; Mayache, H.; Bentahar, A. Number of pixel change rate and unified average changing intensity for sensitivity analysis of encrypted inSAR interferogram. Ingénierie Des Systèmes D’information/Ingénierie Des Systèmes D’Information 2020, 25(5), 601–607. [Google Scholar] [CrossRef]
- Wu, Y.; Noonan, J.; Agaian, S. Npcr and Uaci Randomness Tests for Image Encryption. Cyber Journals: Multidisciplinary, Journals in Science and Technology, Journal of Selected Areas in Telecommunications (JSAT) 2011, 31–38. [Google Scholar]
- Chakraborty, S.; Seal, A.; Roy, M.; Mali, K. A novel lossless image encryption method using DNA substitution and chaotic logistic map. International Journal of Security and Its Applications 2016, 10(2), 205–216. [Google Scholar] [CrossRef]
- Naim, M.; Ali Pacha, A. New chaotic satellite image encryption by using some or all the rounds of the AES algorithm. Information Security Journal: A Global Perspective 2021, 32(3), 187–211. [Google Scholar] [CrossRef]
- Mohammad, O. F.; Rahim, M. S. M.; Zeebaree, S. R. M.; Ahmed, F. A survey and analysis of the image encryption methods. International Journal of Applied Engineering Research 2017, 12(23), 13265–13280. [Google Scholar]
- Mehdi, S. A.; Kadhim, A. A. Image encryption algorithm based on a new five dimensional Hyperchaotic system and Sudoku matrix. 2019 International Engineering Conference (IEC), 2019; IEEE; pp. 188–193. [Google Scholar]
- Deshpande, K.; Girkar, J.; Mangrulkar, R. Security enhancement and analysis of images using a novel Sudoku-based encryption algorithm. Journal of Information and Telecommunication 2023, 7(3), 270–303. [Google Scholar] [CrossRef]
- Felgenhauer, B.; Jarvis, F. Mathematics of Sudoku I. Mathematical Spectrum 2006, 39(1), 15–22. [Google Scholar]
- Menezes; van Oorschot; Vanstone. Handbook of Applied Cryptography, Chapter 7. 1996. [Google Scholar]
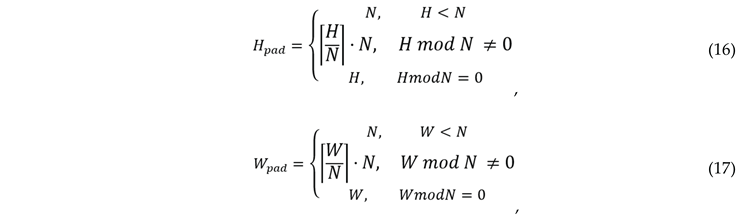
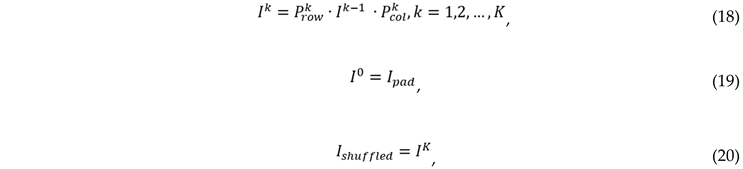
| Image Name | Image Type | Sudoku block size | NPCR (%) | UACI (%) |
|---|---|---|---|---|
| Lena | Color | 9 × 9 | 99.2239 | 33.2896 |
| Airplane (F-16) | Grayscale | 9 × 9 | 99.2333 | 33.3401 |
| Sailboat | Color | 9 × 9 | 99.2269 | 33.3458 |
| Peppers | Color | 9 × 9 | 99.2175 | 33.3203 |
| Tank | Grayscale | 9 × 9 | 99.2313 | 33.3008 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




