Submitted:
09 April 2026
Posted:
10 April 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
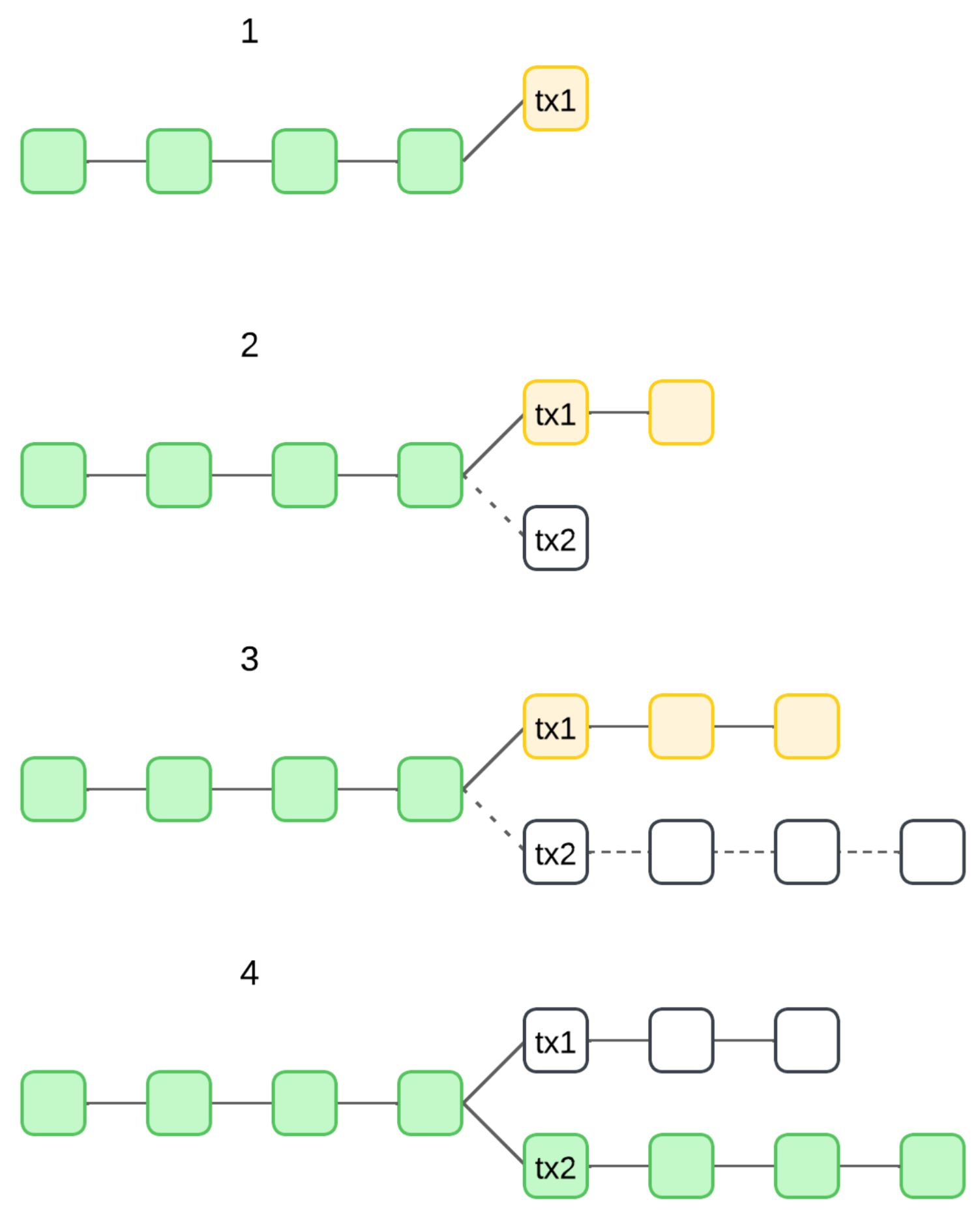
- 1.
-
Transaction Initiation (honest spend).
- The attacker creates a valid transaction and sends it to a merchant or recipient.
- The transaction is broadcast to the network and appears in the mempool (unconfirmed transactions).
- The recipient sees the transaction as pending and may accept it if they trust the network.
- 2.
-
Broadcasting an alternative transaction (malicious spend).
- The attacker creates a second transaction that spends the same coins but directs them to their own wallet instead of the merchant.
- This transaction has the same inputs as the first one but different outputs.
- The attacker does not broadcast it immediately, waiting for the right moment.
- 3.
-
Gaining an advantage in mining (or forging). Depending on the blockchain’s consensus mechanism, the attacker uses different strategies. In PoW chains (e.g., Bitcoin):
- The attacker controls a significant portion of the network’s hash power (usually 50% or more).
- They mine a private fork of the blockchain, keeping their double-spend transaction hidden.
In PoS chains:- The attacker uses a high stake ratio or exploits weaknesses in the forking rules.
- They may attempt a long-range attack or manipulate finality assumptions.
- 4.
-
Overwriting the honest transaction.
- If the attacker’s private chain grows longer than the public chain, it becomes the valid one under the longest chain rule.
- The network reorganizes, and the attacker’s conflicting transaction is included, while the original transaction to the merchant is dropped.
- The merchant, thinking the transaction was valid, may have already delivered goods or services.
- 5.
-
Profit and network impact.
- The attacker retrieves the funds and retains both the goods/services and their original balance.
- The attack damages network trust, causing users to lose confidence in the blockchain.
2. Related Work
3. Materials and Methods
3.1. Ouroboros-like Slot Model and Properties of the Block Creation Function
- 1.
- ;
- 2.
- .
- event “all SLs in TS are honest”;
- event “all SLs in TS are malicious”;
- event “among SLs in TS , both honest and malicious SLs are present”;
- event “TS is empty (there are no SLs in this TS)”;
- event “TS is not empty (there is at least one SL in this TS)”.
3.2. Formal Attack Setup
3.3. Model Scope and State-Space Reduction
- existence of empty timeslots;
- possibility to get several SLs in one timeslot, where each of them may create a valid block and add it to one of the existing chains (an honest SL always adds a newly created block to one of the longest chains).
3.4. The Probability of a Double-Spend Attack for Ouroboros-like Consensus Protocols
4. Numerical Results
5. Discussion
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| ASC | Active Slot Coefficient |
| BCF | Block Creation Function |
| DS | Double-spend |
| PoS | Proof-of-Stake |
| PoW | Proof-of-Work |
| SL | Slot Leader |
| TS | Timeslot |
References
- Sunny, F.A.; Hajek, P.; Munk, M.; Abedin, M.Z.; Satu, M.S.; Efat, M.I.A.; Islam, M.J. A systematic review of blockchain applications. IEEE Access 2022, 10, 59155–59177. [Google Scholar] [CrossRef]
- Renduchintala, T.; Alfauri, H.; Yang, Z.; Pietro, R.D.; Jain, R. A survey of blockchain applications in the fintech sector. Journal of Open Innovation: Technology, Market, and Complexity 2022, 8, 185. [Google Scholar] [CrossRef]
- Al Hwaitat, A.K.; Almaiah, M.A.; Ali, A.; Al-Otaibi, S.; Shishakly, R.; Lutfi, A.; Alrawad, M. A New Blockchain-Based Authentication Framework for Secure IoT Networks. Electronics 2023, 12, 3618. [Google Scholar] [CrossRef]
- AlSalem, T.S.; Almaiah, M.A.; Lutfi, A. Cybersecurity Risk Analysis in the IoT: A Systematic Review. Electronics 2023, 12, 3958. [Google Scholar] [CrossRef]
- Nakamoto, S. A peer-to-peer electronic cash system 2008.
- Karpinski, M.; Kovalchuk, L.; Kochan, R.; Oliynykov, R.; Rodinko, M.; Wieclaw, L. Blockchain Technologies: Probability of Double-Spend Attack on a Proof-of-Stake Consensus. Sensors 2021, 21, 6408. [Google Scholar] [CrossRef] [PubMed]
- Kiayias, A.; Russell, A.; David, B.; Oliynykov, R. Ouroboros: A provably secure proof-of-stake blockchain protocol. In Proceedings of the Annual International Cryptology Conference; Springer: Cham, Switzerland, 2017; pp. 357–388. [Google Scholar]
- David, B.; Gaži, P.; Kiayias, A.; Russell, A. Ouroboros praos: An adaptively-secure, semi-synchronous proof-of-stake blockchain. In Proceedings of the Advances in Cryptology–EUROCRYPT 2018: 37th Annual International Conference on the Theory and Applications of Cryptographic Techniques, Part II 37. Tel Aviv, Israel, 29 April–3 May 2018; Springer: Cham, Switzerland; pp. 66–98. [Google Scholar]
- Badertscher, C.; Gaži, P.; Kiayias, A.; Russell, A.; Zikas, V. Ouroboros genesis: Composable proof-of-stake blockchains with dynamic availability. In Proceedings of the Proceedings of the 2018 ACM SIGSAC Conference on Computer and Communications Security, Toronto, ON, Canada, 15–19 October 2018; pp. 913–930. [Google Scholar]
- Badertscher, C.; Gazi, P.; Kiayias, A.; Russell, A.; Zikas, V. Ouroboros chronos: Permissionless clock synchronization via proof-of-stake. Cryptology ePrint Archive 2019. [Google Scholar]
- Ovezik, C.; Kiayias, A. Decentralization Analysis of Pooling Behavior in Cardano Proof of Stake. In Proceedings of the Proceedings of the Third ACM International Conference on AI in Finance, New York, NY, USA, 2–4 November 2022; pp. 18–26. [Google Scholar]
- Fitzi, M.; Gazi, P.; Kiayias, A.; Russell, A. Proof-of-stake blockchain protocols with near-optimal throughput, 2020.
- Kiayias, A.; Koutsoupias, E.; Marmolejo-Cossío, F.; Stouka, A.P. Balancing Participation and Decentralization in Proof-of-Stake Cryptocurrencies. In Proceedings of the International Symposium on Algorithmic Game Theory; Springer: Cham, Switzerland, 2024; pp. 333–350. [Google Scholar]
- Rosenfeld, M. Analysis of hashrate-based double spending. arXiv 2014, arXiv:1402.2009. [Google Scholar] [CrossRef]
- Pinzón, C.; Rocha, C. Double-spend attack models with time advantange for bitcoin. Electronic Notes in Theoretical Computer Science 2016, 329, 79–103. [Google Scholar] [CrossRef]
- Grunspan, C.; Pérez-Marco, R. Double spend races. International Journal of Theoretical and Applied Finance 2018, 21, 1850053. [Google Scholar] [CrossRef]
- Kovalchuk, L.; Kaidalov, D.; Nastenko, A.; Rodinko, M.; Shevtsov, O.; Oliynykov, R. Decreasing security threshold against double spend attack in networks with slow synchronization. Computer Communications 2020, 154, 75–81. [Google Scholar] [CrossRef]
- Jang, J.; Lee, H.N. Profitable double-spending attacks. Applied Sciences 2020, 10, 8477. [Google Scholar] [CrossRef]
- Hafid, A.; Hafid, A.S.; Makrakis, D. Sharding-Based Proof-of-Stake Blockchain Protocols: Key Components & Probabilistic Security Analysis. Sensors 2023, 23, 2819. [Google Scholar]
- Li, A.; Wei, X.; He, Z. Robust proof of stake: A new consensus protocol for sustainable blockchain systems. Sustainability 2020, 12, 2824. [Google Scholar] [CrossRef]
- Naz, S.; Lee, S.U.J. Sea Shield: A Blockchain Technology Consensus to Improve Proof-of-Stake-Based Consensus Blockchain Safety. Mathematics 2024, 12, 833. [Google Scholar] [CrossRef]
- Mao, H.; Nie, T.; Yu, M.; Dong, X.; Li, X.; Yu, G. SMPTC3: Secure Multi-Party Protocol Based Trusted Cross-Chain Contracts. Mathematics 2024, 12, 2562. [Google Scholar] [CrossRef]
- Gao, Y.; Li, X.; Peng, Z.; Zhang, Y.; Yu, G. NeuChain+: A Sharding Permissioned Blockchain System with Ordering-Free Consensus. Applied Sciences 2024, 14, 4897. [Google Scholar] [CrossRef]
- Chegenizadeh, M.; Li, S.N.; Tessone, C.J. Towards a deeper understanding of the Cardano macro-economics. In Proceedings of the 2024 IEEE International Conference on Blockchain and Cryptocurrency (ICBC); IEEE: New York, NY, USA, 2024; pp. 585–593. [Google Scholar]
- Alshahrani, H.; Islam, N.; Syed, D.; Sulaiman, A.; Al Reshan, M.S.; Rajab, K.; Shaikh, A.; Shuja-Uddin, J.; Soomro, A. Sustainability in blockchain: A systematic literature review on scalability and power consumption issues. Energies 2023, 16, 1510. [Google Scholar] [CrossRef]
- Cao, B.; Zhang, Z.; Feng, D.; Zhang, S.; Zhang, L.; Peng, M.; Li, Y. Performance analysis and comparison of PoW, PoS and DAG based blockchains. Digital Communications and Networks 2020, 6, 480–485. [Google Scholar] [CrossRef]
- Fahim, S.; Rahman, S.K.; Mahmood, S. Blockchain: A comparative study of consensus algorithms PoW, PoS, PoA, PoV. Int. J. Math. Sci. Comput. 2023, 3, 46–57. [Google Scholar] [CrossRef]
- Lepore, C.; Ceria, M.; Visconti, A.; Rao, U.P.; Shah, K.A.; Zanolini, L. A survey on blockchain consensus with a performance comparison of PoW, PoS and pure PoS. Mathematics 2020, 8, 1782. [Google Scholar] [CrossRef]
- Rukhiran, M.; Boonsong, S.; Netinant, P. Sustainable Optimizing Performance and Energy Efficiency in Proof of Work Blockchain: A Multilinear Regression Approach. Sustainability 2024, 16, 1519. [Google Scholar] [CrossRef]
- Hossan, M.R.; Nirob, F.A.; Islam, A.; Rakin, T.M.; Al-Amin, M. A Comprehensive Analysis of Blockchain Technology and Consensus Protocols Across Multilayered Framework. IEEE Access 2024, 12, 63087–63129. [Google Scholar] [CrossRef]
- Ahn, J.; Yi, E.; Kim, M. Blockchain consensus mechanisms: A bibliometric analysis (2014–2024) using vosviewer and r bibliometrix. Information 2024, 15, 644. [Google Scholar] [CrossRef]
- Feller, W. An Introduction to Probability Theory and Its Applications, Volume 2; John Wiley & Sons: Hoboken, NJ, USA, 1991; Volume 81. [Google Scholar]
| l | |||||
|---|---|---|---|---|---|
| 1 | 5 | 10 | 20 | 30 | |
| 0.05 | 0.05263 | ||||
| 0.1 | 0.11111 | ||||
| 0.2 | 0.25000 | 0.00098 | |||
| 0.3 | 0.42857 | 0.01446 | 0.0002 | ||
| f | ||||||
|---|---|---|---|---|---|---|
| 0.05 | 0.1 | 0.2 | 0.5 | 0.8 | 0.9 | |
| 0.05 | 4 | 4 | 4 | 4 | 4 | 4 |
| 0.1 | 6 | 6 | 6 | 6 | 6 | 7 |
| 0.2 | 13 | 13 | 13 | 13 | 13 | 14 |
| 0.3 | 32 | 32 | 32 | 32 | 33 | 35 |
| 0.4 | 133 | 133 | 134 | 135 | 141 | 149 |
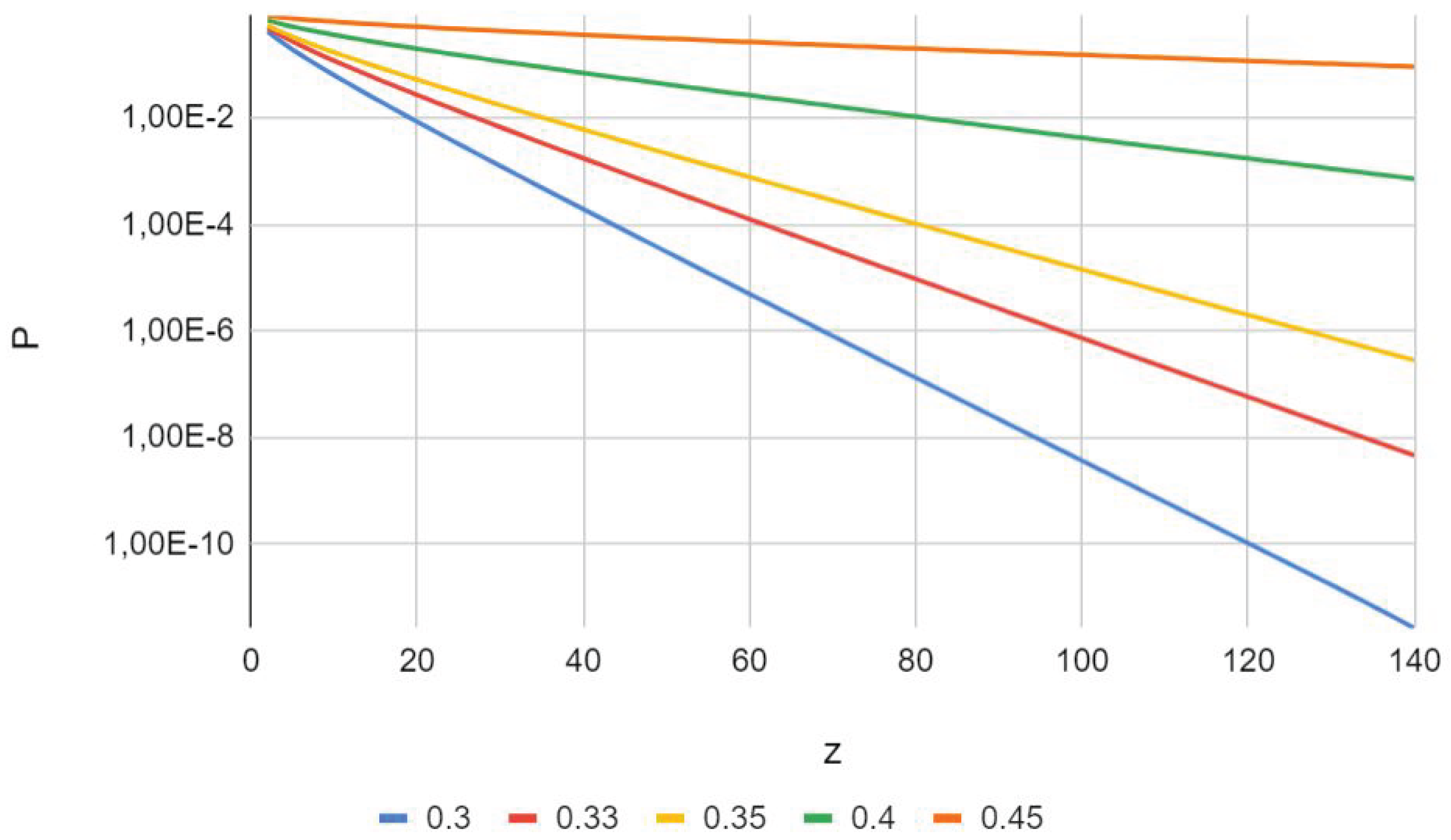
| z | |||||
|---|---|---|---|---|---|
| 0.30 | 0.33 | 0.35 | 0.40 | 0.45 | |
| 1 | 0.600037 | 0.660033 | 0.700030 | 0.800021 | 0.900011 |
| 2 | 0.432023 | 0.509674 | 0.563520 | 0.704015 | 0.850508 |
| 3 | 0.326180 | 0.409946 | 0.470357 | 0.634895 | 0.813754 |
| 4 | 0.252089 | 0.336446 | 0.399709 | 0.579599 | 0.783433 |
| 5 | 0.197632 | 0.279568 | 0.343455 | 0.533150 | 0.757167 |
| 10 | 0.065115 | 0.121586 | 0.174960 | 0.372199 | 0.657938 |
| 20 | 0.008676 | 0.027596 | 0.053580 | 0.204130 | 0.528642 |
| 30 | 0.001277 | 0.006858 | 0.017841 | 0.119114 | 0.439347 |
| 40 | 1.9675 | 0.001777 | 0.006177 | 0.071629 | 0.371400 |
| 50 | 3.1110 | 4.7197 | 0.002189 | 0.043867 | 0.317318 |
| 60 | 5.0044 | 1.2739 | 7.8770 | 0.027200 | 0.273129 |
| 70 | 8.1483 | 3.4781 | 2.8659 | 0.017019 | 0.236396 |
| 80 | 1.3388 | 9.5789 | 1.0513 | 0.010722 | 0.205485 |
| 90 | 2.2151 | 2.6559 | 3.8819 | 0.006792 | 0.179236 |
| 100 | 3.6853 | 7.4034 | 1.4407 | 0.004321 | 0.156787 |
| 110 | 6.1576 | 2.0729 | 5.3701 | 0.002760 | 0.137480 |
| 120 | 1.0306 | 5.8251 | 2.0088 | 0.001768 | 0.120799 |
| 130 | 1.7077 | 1.6420 | 7.5369 | 0.001135 | 0.106331 |
| 140 | 2.5917 | 4.6409 | 2.8352 | 0.000731 | 0.093741 |
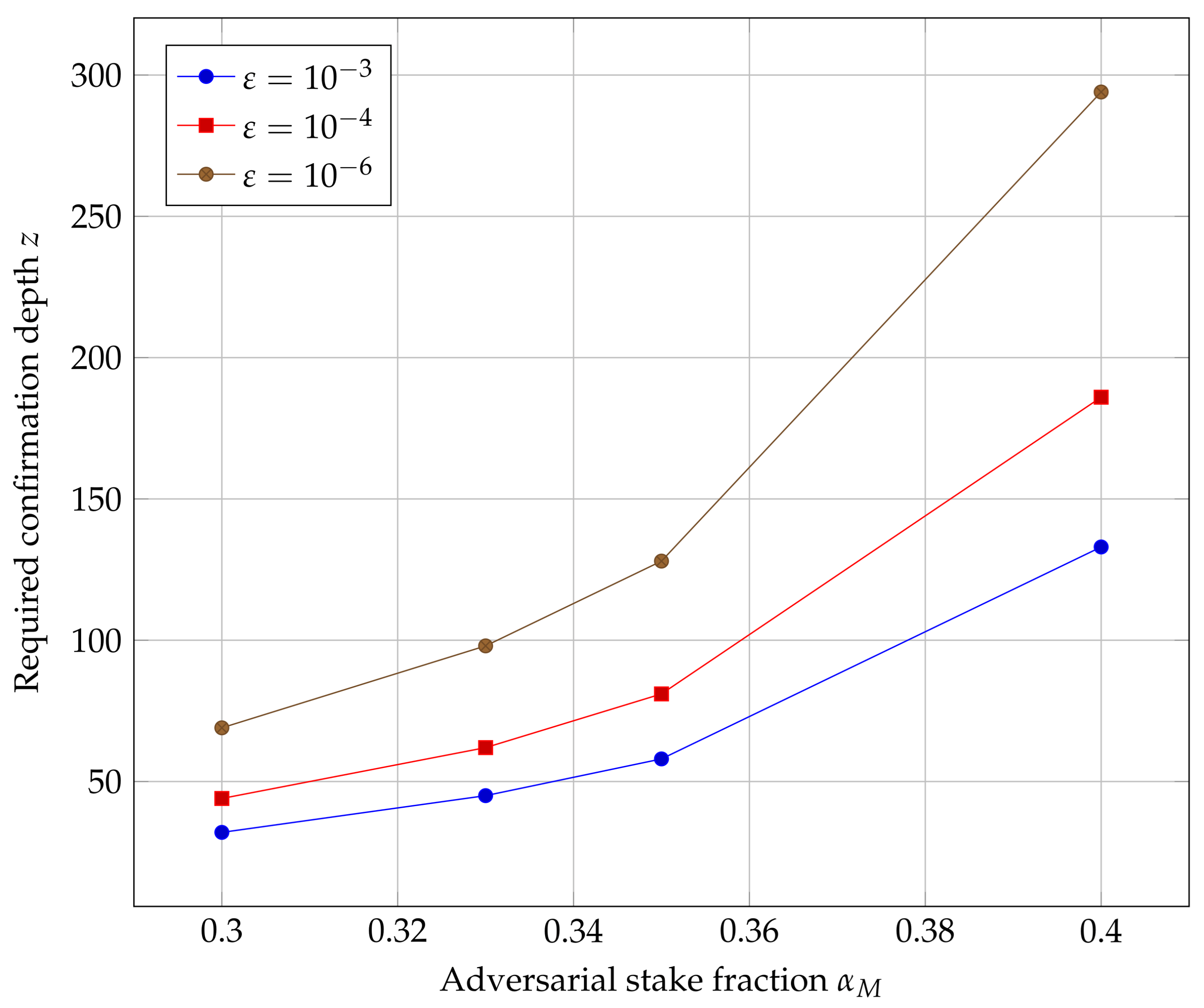
| 0.30 | 32 | 44 | 69 |
| 0.33 | 45 | 62 | 98 |
| 0.35 | 58 | 81 | 128 |
| 0.40 | 133 | 186 | 294 |
| f | z | (Formula) | (DP) | (Monte Carlo) | |
|---|---|---|---|---|---|
| 0.10 | 0.05 | 2 | 0.056009 | 0.056009 | 0.057600 |
| 0.10 | 0.05 | 4 | 0.005457 | 0.005457 | 0.005650 |
| 0.20 | 0.20 | 4 | 0.066851 | 0.066851 | 0.066500 |
| 0.30 | 0.05 | 4 | 0.252089 | 0.252089 | 0.252350 |
| 0.30 | 0.50 | 4 | 0.255199 | 0.255199 | 0.254850 |
| 0.40 | 0.90 | 4 | 0.609586 | 0.609586 | 0.607350 |
| 0.40 | 0.90 | 8 | 0.456269 | 0.456269 | 0.460850 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




