Submitted:
06 April 2026
Posted:
07 April 2026
You are already at the latest version
Abstract
Keywords:
I. Introduction
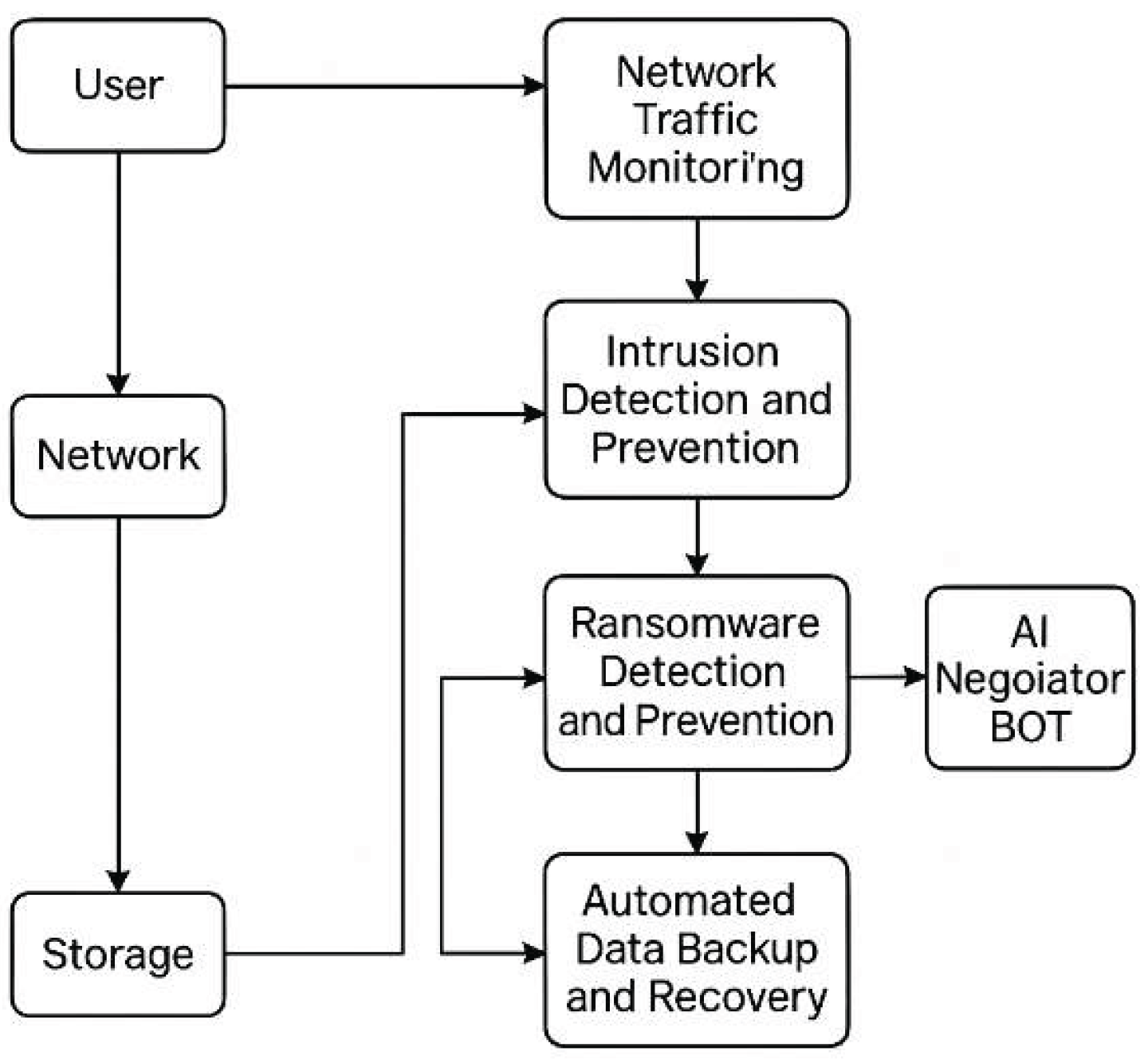
- AI/ML-based network traffic monitoring
- Intrusion detection and prevention system (IDPS)
- Ransomware detection and prevention
- AI-powered Ransom Negotiator BOT (using Ollama)
- Automated backup and recovery (Self-Healing System)
II. Background and Motivation
- AI-driven network monitoring
- ML-based intrusion detection and automated prevention
- Ransomware behavioural analytics
- AI-powered negotiation capabilities (LLMs)
- Automated backup and recovery workflows
- Real-time forensic correlation
- On-device LLMs like Ollama for privacy-preserving analysis
III. Literature Review
- ransomware note interpretation
- negotiation guidance
- log summarization
- automated threat reasoning
- predictive modelling
- automated risk scoring
- adaptive ML policies
- ransomware behaviour forecasting
- AI network monitoring
- ML-based IDS
- behavioural ransomware detection
- automated backup & recovery
- AI-based ransom negotiation
- privacy-preserving local LLMs
IV. System Components Surveyed
- File entropy
- Rapid encryption detection
- Registry tampering
- Suspicious process patterns
- Parse ransom notes
- Extract wallet IDs
- Generate negotiation messages
- Predict attacker behaviour
- Attempt key recovery
- Scheduled incremental backups
- Snapshot verification
- Backup freeze during encryption attack
- Automatic rollback using VSS or rsync
- Clean file restoration with integrity checks
V. Comparative Analysis
| Feature | Traditional Tools | ML IDS | Proposed Unified Platform |
| Network Monitoring | Reactive | Predictive | Continuous AI Monitoring |
| Intrusion Detection | Signature-based | ML-based [2] | AI + Automated Prevention |
| Ransomware Detection | Antivirus-based | Behavioral ML [1,3] | Real-time AI + Isolation |
| Recovery | Manual | Semi-automatic [1] | Fully Automated Self-Healing |
| Negotiation | None | None | AI BOT With Ollama |
VI. Conclusions
Conflicts of Interest
References
- A. K. Upadhyay, P. Dubey, S. Gandhi and S. Jain, "Ransomware Detection And Data Recovery," 2024 International Conference on Electrical Electronics and Computing Technologies (ICEECT), Greater Noida, India, 2024, pp. 1-6. [CrossRef]
- M. S. Rahman, W. Tausif Islam and M. R. Ahmed Khan, "Enhancing Cybersecurity with an Investigation into Network Intrusion Detection System Using Machine Learning," 2024 IEEE 3rd International Conference on Robotics, Automation, Artificial-Intelligence and Internet-of-Things (RAAICON), Dhaka, Bangladesh, 2024, pp. 107-110. [CrossRef]
- J. Tang, "The Proactive Approach to Cyber-Attack Prevention: Countermeasures Against Ransomware," 2024 9th International Conference on Intelligent Computing and Signal Processing (ICSP), Xian, China, 2024, pp. 376-379. [CrossRef]
- S. Chowhan and A. K. Saxena, "Advanced Techniques in Network Traffic Analysis: Utilizing Wireshark For In-Depth Live Data Packet Inspection And Information Capture," 2023 International Conference on Communication, Security and Artificial Intelligence (ICCSAI), Greater Noida, India, 2023, pp. 843-847. [CrossRef]
- S. Cheon, G. Choi and D. Kim, "A Cheating Attack on a Whitelist-based AntiRansomware Solution and its Countermeasure," 2023 IEEE International Conference on Consumer Electronics (ICCE), Las Vegas, NV, USA, 2023, pp. 01-04. [CrossRef]
- C. B. J., S. A. Kudtarkar and Mohana, "Targeted Ransomware Attacks and Detection to Strengthen Cybersecurity Strategies," 2023 Second International Conference on Automation, Computing and Renewable Systems (ICACRS), Tirunelveli, India, 2023, pp. 1039-1044. [CrossRef]
- Y. Prajapati and K. Gosai, "Windows Forensic Analysis and Detection of Ransomware Attacks Using Event Logs and Tools," 2024 4th International Conference on Intelligent Technologies (CONIT), Karnataka, India, 2024, pp. 01-06. [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




