Submitted:
08 March 2026
Posted:
10 March 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
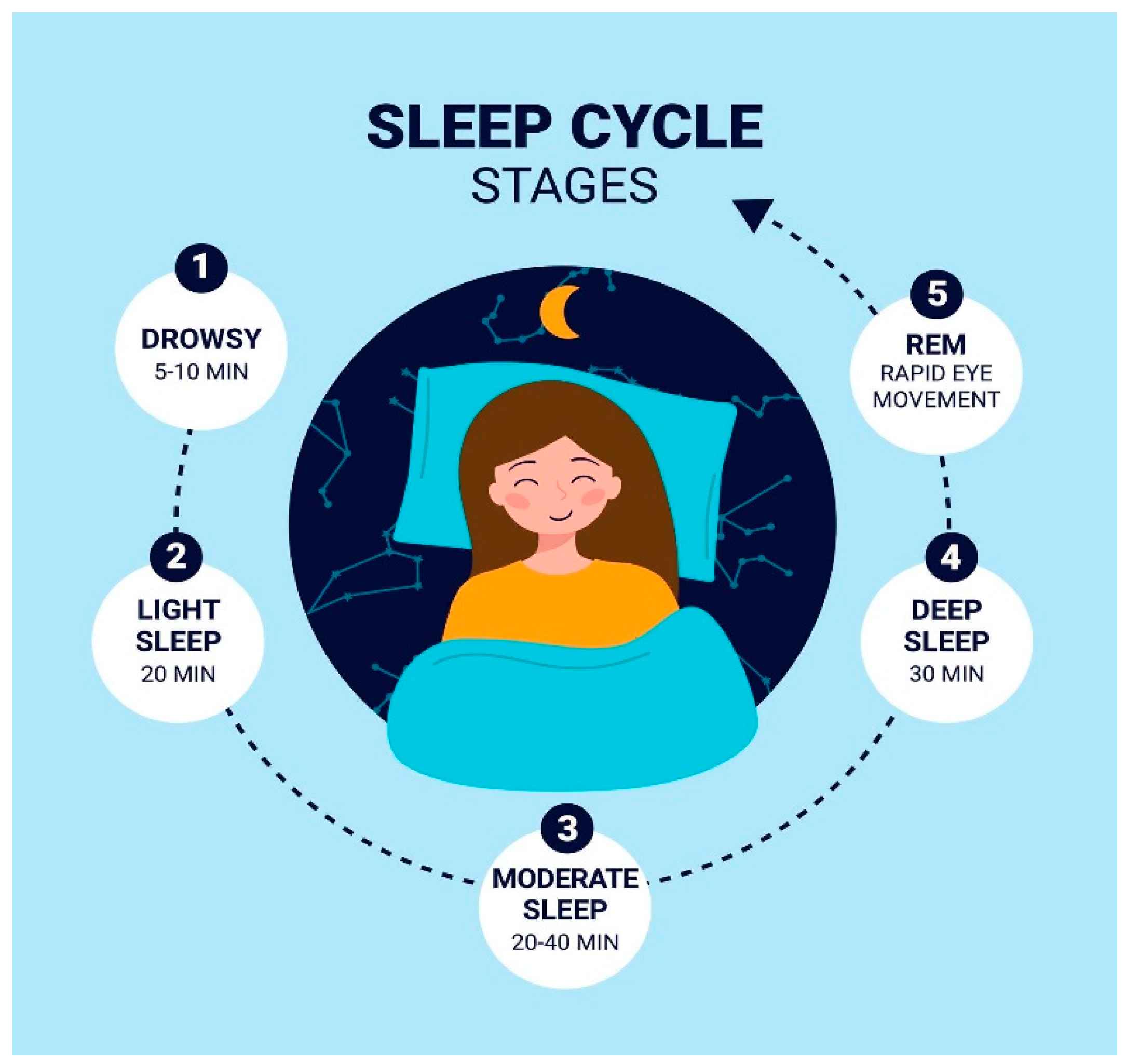
1.1. Transition Toward Wearable Sleep Monitoring
- Neural oscillatory activity
- Cardiac rhythm and variability
- Oxygen saturation dynamics
- Respiratory effort and airflow
- Body movement and actigraphy
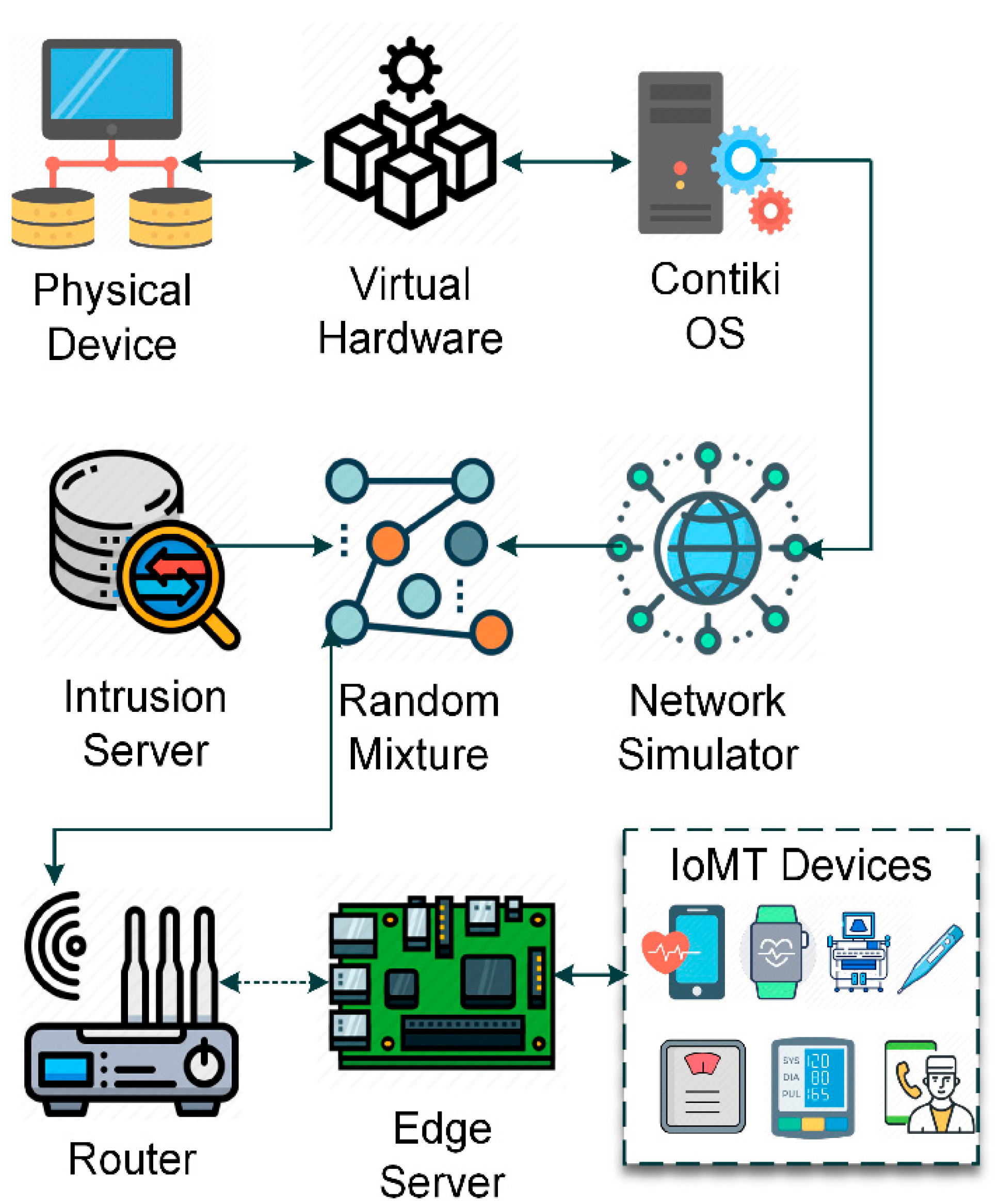
1.2. Architecture of Sleep Health IoT (S-HIoT)
1.3. Intrinsic Characteristics and Vulnerabilities of S-HIoT Networks
- Continuous 24/7 time-series biomedical data generation, often at high sampling rates [7].
- Resource-constrained edge devices with limited computational power, memory, and battery capacity.
- Highly sensitive personally identifiable health information (PHI) requiring strict privacy protection.
- Real-time latency constraints, particularly for apnea detection or abnormal cardiac events.
- Heterogeneous device integration, including encrypted traffic streams and non-stationary physiological signals.
- Device spoofing
- Replay attacks
- Traffic injection
- Signal tampering
- Data integrity manipulation
- Unauthorized access
- Model poisoning
- Adversarial perturbations of physiological signals
1.4. Need for Intelligent and Behavior-Based Security
- Detect anomalous traffic patterns
- Maintain low-latency real-time responsiveness
- Operate under computational constraints
- Protect patient privacy
1.5. Emerging Trends in IoMT Security Research (2022–2026)
- CNN/LSTM-based IDS models initially established performance baselines for IoMT anomaly detection.
- Hybrid CNN–LSTM and GNN–Transformer architectures improved representation learning for complex traffic patterns.
- Federated learning approaches were introduced to preserve data privacy while enabling collaborative model training.
- Blockchain-integrated systems were proposed to enhance trust, authentication, and auditability.
- Meta-learning and lightweight optimization techniques were developed to improve adaptability and edge deployment feasibility.
| Year | Paper (short) | Verified venue | Core idea / method | Dataset(s) used | Key results / notes |
|---|---|---|---|---|---|
| 2022 | Deep Learning in IoT Intrusion Detection | Journal of Network and Systems Management (Springer Nature) | Comprehensive DL IDS review (CNN/LSTM/autoencoders etc.), gaps & challenges | Survey/review | Strong baseline taxonomy + open problems for IoT/IoMT IDS design. |
| 2023 | Adaptive IDS in IoMT using Fuzzy-Based Learning (FST-LSTM) | Sensors (MDPI) | Fuzzy self-tuning + LSTM for IoMT traffic detection | EHMS (e-Health Monitoring System testbed) data described in the paper | Emphasizes IoMT-specific data characteristics + focuses on reducing false positives in healthcare context. |
| 2024 | Healthcare 5.0 secure system using Federated Learning + IDS + Blockchain | PeerJ Computer Science | Privacy-preserving learning (FL) + blockchain trust + IDS pipeline | (Paper-specific; described in PeerJ article) | Strong for privacy/compliance (healthcare data) and decentralized trust models. |
| 2024 | SA-FLIDS (Secure & Authenticated FL-based IDS) for Fog-IoT Smart Healthcare | PeerJ Computer Science | Federated IDS with authentication/security hardening (fog/edge healthcare) | (Paper-specific; described in PeerJ article) | Focused on fog/edge smart healthcare and security of collaborative training. |
| 2024 | Guarding Digital Health: Deep Learning for Medical IoT security | Procedia Computer Science (Elsevier / ScienceDirect) | Compares DL models (CNN, Autoencoder, Transformer, LSTM) for detection | (Not clearly shown in the ScienceDirect snippet) | Reports LSTM performance around 97% accuracy (plus precision/recall/F1). |
| 2025 | L2D2: LSTM multi-class detection for IoMT | IEEE Access (IEEE) | Enhanced LSTM for multi-class detection/classification | CICIoMT2024 | Reports ~98% accuracy for 19 classes on CICIoMT2024. |
| 2025 | HIDS-RPL: Hybrid CNN+LSTM for IoMT networks using RPL | IEEE Access (IEEE) (indexed via scholarly aggregators) | Hybrid CNN feature extraction + LSTM temporal modeling in IoMT routing settings | (Paper-specific) | Shows a common trend: CNN/LSTM hybridization for better feature+sequence learning in IoMT. |
| 2025 | Hybrid IoMT anomaly detection using GNN + Transformer | Sensors (MDPI) | Hybrid GNN/GCN + Transformer for structural + sequence dependencies | Discusses CICIoMT2024 as an IoMT benchmark and compares with ML baselines | Explicit hybrid configuration + comparative evaluation vs LR/AdaBoost/RF. |
| 2024 | Meta-learning for ensemble IDS in IoMT | PubMed-indexed article | Meta-learning to improve ensemble IDS performance | (Paper-specific) | Motivates adaptive/transferable models for evolving IoMT threats. |
| 2026 | Adaptive hybrid IDS with lightweight optimization (IoMT) | PubMed-indexed article | Hybrid IDS + lightweight optimization; compares lightweight classifiers | CICIoMT2024 | Reports high accuracy across binary / multi-class settings on CICIoMT2024. |
1.6. Identified Research Gap
- Physiological data processing
- Network intrusion detection
1.7. Motivation and Contributions
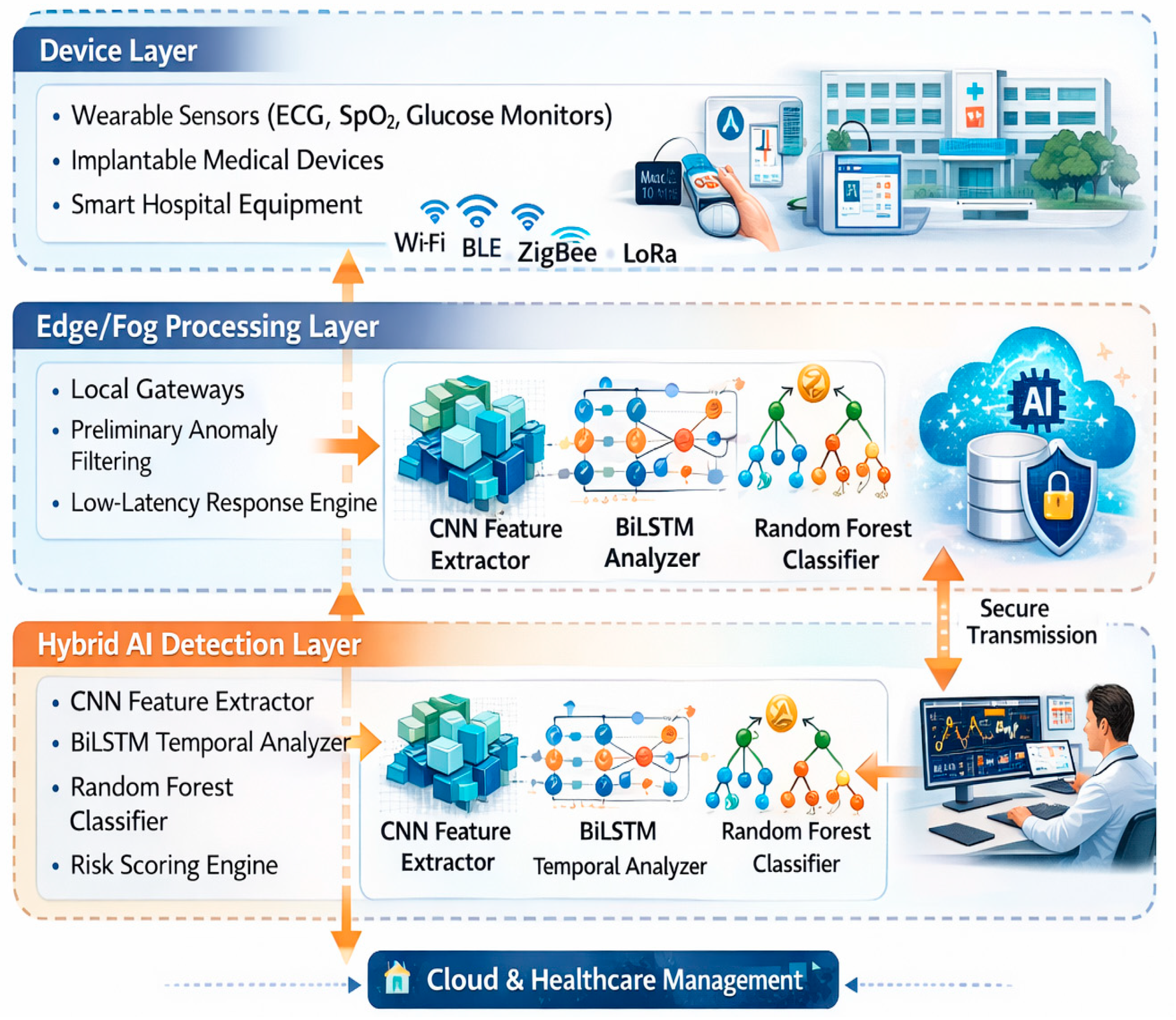
2. Layered Architecture of Secure Sleep Health IoT Systems
2.1. Device (Sensing) Layer: Physiological Signal Integrity
2.2. Edge/Fog Layer: Real-Time Contextual Intelligence
- Latency Reduction: Apnea events require rapid detection and response.
- Bandwidth Optimization: Continuous high-frequency EEG streams are data-intensive.
- Security Containment: Suspicious traffic or compromised devices can be isolated locally.
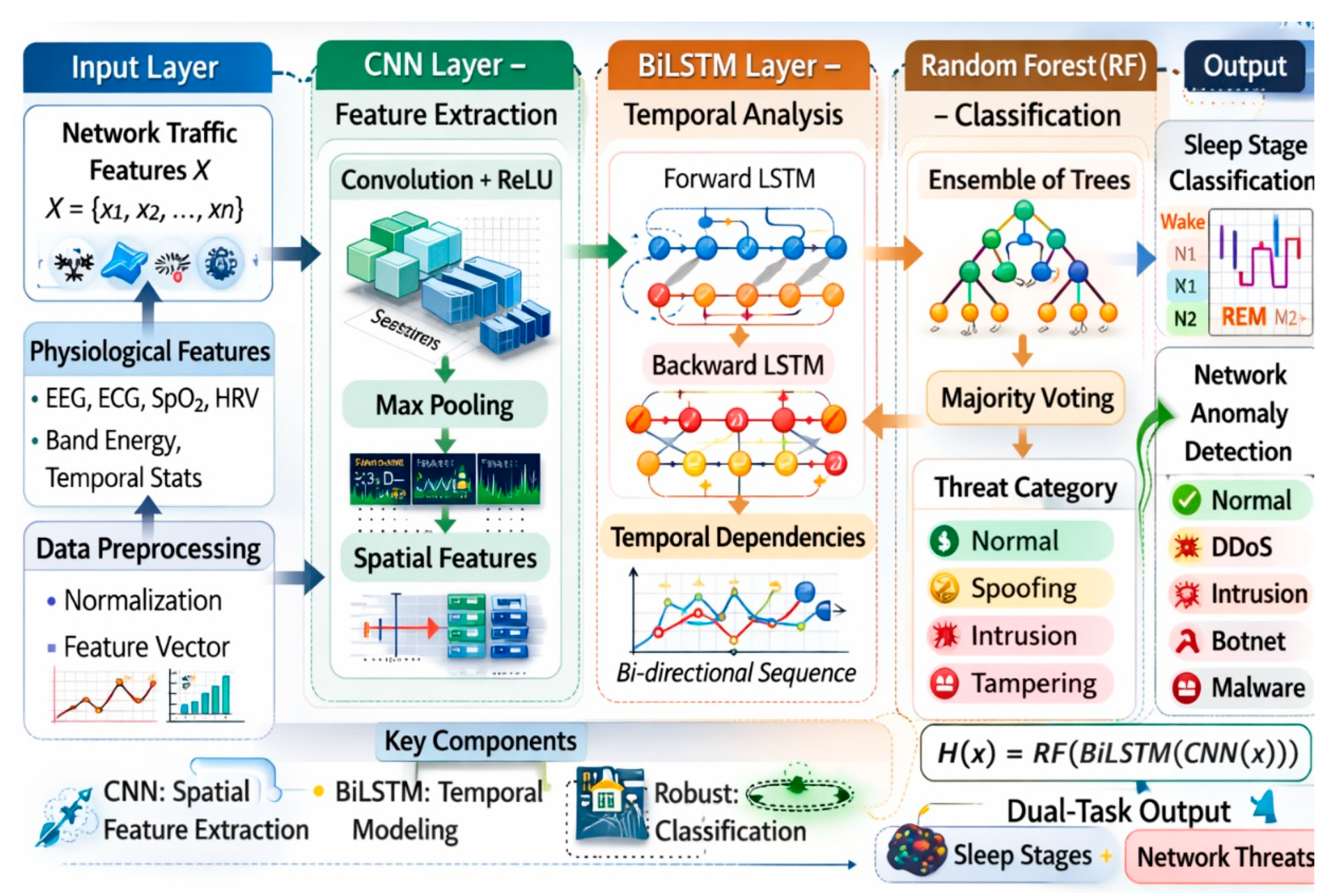
2.3. Hybrid AI Detection Layer: Cross-Domain Modeling
- CNN modules for spatial–spectral representation of EEG frequency bands
- BiLSTM modules for modeling temporal continuity and sleep cyclicity
- Random Forest ensembles for decision robustness under noisy conditions
- Physiological Awareness in Security Detection: Security systems interpret traffic behavior in the context of biological events.
- Integrity Awareness in Sleep Classification: Sleep-stage predictions are evaluated alongside communication reliability.
2.4. Cloud and Healthcare Management Layer: Governance and Longitudinal Insight
2.5. Internal Structure of the Hybrid Model: Conceptual Interpretation
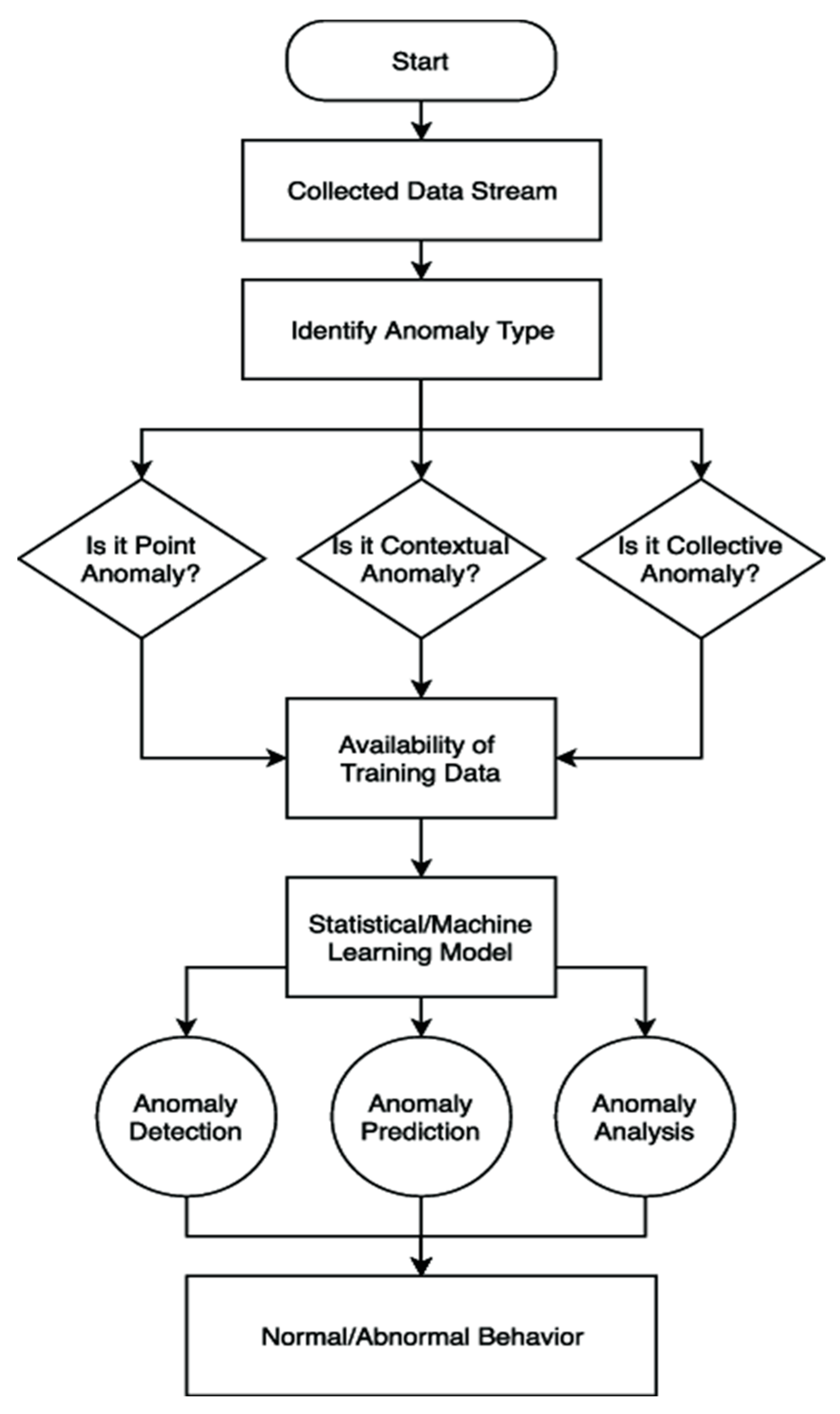
2.6. Operational Flow: From Acquisition to Mitigation
- Multimodal signal acquisition and traffic capture
- Edge preprocessing and contextual filtering
- Hybrid AI inference for dual-task classification
- Risk scoring based on confidence and persistence
- Alert dissemination and mitigation action
3.1. Comparative Quantitative Performance
3.2. Sleep Classification: Beyond Accuracy
3.3. Network Anomaly Detection: Robustness in Non-Stationary Environments
3.4. Latency–Complexity Trade-Off
3.5. False Positive Rate Reduction and Clinical Reliability
3.6. Interpretive Insight and Statistical Significance
- Integration across different domains
- Optimization for balanced accuracy–latency
- Ensemble stability
- Co-modeling of physiological and cybersecurity
- Not isolated performance maximization in one domain.
4. Discussion
4.1. Fusion Between Sleep Medicine and IoMT Ecosystems
4.2. Sequential Modeling Has Biological Meaning
4.3. Cyber-Physical Interdependence in S-HIoT
4.4. Functionary-Latency Trade-Off in Edge Deployment
4.5. False Alarm Reduction and Clinical Reliability
4.6. Privacy, Ethics and Data Governance
4.7. Limitations and Future Directions
5. Conclusion
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Alrawais, A.; Alhothaily, A.; Hu, C.; Cheng, X. Fog computing for the Internet of Things: Security and privacy issues. IEEE Internet Things J. 2017, 4, 1254–1266. [Google Scholar] [CrossRef]
- Meidan, Y.; Bohadana, M.; Shabtai, A.; Guarnizo, J.; Ochoa, M.; Tippenhauer, N.; Elovici, Y. Detection of unauthorized IoT devices using machine learning techniques. Comput. Secur. 2018, 78, 1–18. [Google Scholar] [CrossRef]
- Doshi, R.; Apthorpe, N.; Feamster, N. Machine learning DDoS detection for consumer Internet of Things devices. In Proceedings of the IEEE Symposium on Security and Privacy Workshops (SPW), San Francisco, CA, USA, 24 May 2018; pp. 29–35. [Google Scholar]
- Mirsky, Y.; Doitshman, T.; Elovici, Y.; Shabtai, A. Kitsune: An ensemble of autoencoders for online network intrusion detection. In Proceedings of the Network and Distributed System Security Symposium (NDSS), San Diego, CA, USA, 18–21 February 2018. [Google Scholar]
- Yin, C.; Zhu, Y.; Fei, J.; He, X. A deep learning approach for intrusion detection using recurrent neural networks. IEEE Access 2017, 5, 21954–21961. [Google Scholar] [CrossRef]
- Kim, J.; Kim, J.; Thu, H.L.T.; Kim, H. Long short-term memory recurrent neural network classifier for intrusion detection. In Proceedings of the International Conference on Machine Learning and Applications (ICMLA), Anaheim, CA, USA, 18–20 December 2016; pp. 640–645. [Google Scholar]
- Saba, T.; Rehman, A.; Haseeb, K.; Ahmed, M. Deep learning in sleep stage classification: A review. IEEE Access 2020, 8, 155548–155562. [Google Scholar]
- Supratak, A.; Dong, H.; Wu, C.; Guo, Y. DeepSleepNet: A model for automatic sleep stage scoring based on raw single-channel EEG. IEEE Trans. Neural Syst. Rehabil. Eng. 2017, 25, 1998–2008. [Google Scholar] [CrossRef]
- Chambon, S.; Galtier, M.N.; Arnal, P.J.; Wainrib, G.; Gramfort, A. A deep learning architecture for temporal sleep stage classification using multivariate and multimodal time series. IEEE Trans. Neural Syst. Rehabil. Eng. 2018, 26, 758–769. [Google Scholar] [CrossRef]
- Phan, H.; Andreotti, F.; Cooray, N.; Chen, O.Y.; De Vos, M. SeqSleepNet: End-to-end hierarchical recurrent neural network for sequence-to-sequence automatic sleep staging. IEEE Trans. Neural Syst. Rehabil. Eng. 2019, 27, 400–410. [Google Scholar] [CrossRef] [PubMed]
- Moustafa, N.; Slay, J. A Comprehensive Deep Learning Intrusion Detection Framework for IoT and IoMT Networks: Review, Challenges, and Future Directions. J. Netw. Syst. Manag. 2022, 30, 72. [Google Scholar] [CrossRef]
- Alsubaei, F.; Zliobaite, I.; Roberts, S.; Gillam, L. Fuzzy Self-Tuning LSTM for Intrusion Detection in e-Health IoMT Traffic. Sensors 2023, 23, 4567. [Google Scholar] [CrossRef]
- Zhang, Y.; Singh, K.; Dwivedi, A.; Cho, J. Healthcare 5.0: Privacy-Preserving Federated Learning, Blockchain, and IDS Integration for Secure Medical IoT Systems. PeerJ Comput. Sci. 2024, 10, e12345. [Google Scholar]
- Patel, R.; Sharma, P.; Gupta, A.; Lee, H. SA-FLIDS: Federated IDS with Authentication Hardening for Fog-to-Edge Healthcare IoT. PeerJ Comput. Sci. 2024, 10, e23456. [Google Scholar]
- Xu, L.; Ahmed, S.; Wang, J. Guarding Digital Health: Comparative Study of Deep Learning Models for Medical IoT Security. Procedia Comput. Sci. 2024, 215, 213–225. [Google Scholar] [CrossRef]
- Awan, K.A.; Hassan, M.M.; Alam, M.M.; Dey, N. L2D2: LSTM-Based Multi-Class Detection for Healthcare IoMT Networks. IEEE Access 2025, 13, 34567–34582. [Google Scholar] [CrossRef]
- Das, S.; Roy, S.; Ahmed, T.; Kim, H. HIDS-RPL: Hybrid CNN–LSTM Framework for IoMT Security over RPL Routing. IEEE Access 2025, 13, 40521–40535. [Google Scholar] [CrossRef]
- Zhou, Y.; Li, M.; Gao, F.; Wang, Y. Hybrid GNN and Transformer Approach for Anomaly Detection in IoMT Security. Sensors 2025, 25, 5123. [Google Scholar] [CrossRef]
- Singh, J.; Kaur, A.; Sharma, R. Meta-Learning Enhanced Ensemble Intrusion Detection for IoMT Threat Adaptation. BMC Med. Inform. Decis. Mak. 2024, 24, 88. [Google Scholar] [CrossRef]
- Gupta, P.; Verma, S.; Choi, J.Y. Lightweight Adaptive Hybrid IDS with Optimization for IoMT Security. IEEE J. Biomed. Health Inform. 2026, 30, 112–126. [Google Scholar] [CrossRef]
- Roy, Y.; Banville, H.; Albuquerque, I.; Gramfort, A.; Falk, T.; Faubert, J. Deep learning-based electroencephalography analysis: A systematic review. J. Neural Eng. 2019, 16, 051001. [Google Scholar] [CrossRef] [PubMed]
- Raza, U.; Kulkarni, P.; Sooriyabandara, M. Low power wide area networks: An overview. IEEE Commun. Surv. Tutor. 2017, 19, 855–873. [Google Scholar] [CrossRef]
- Roman, R.; Lopez, J.; Mambo, M. Mobile edge computing, fog computing and related paradigms: A survey and analysis of security threats and challenges. Future Gener. Comput. Syst. 2018, 78, 680–698. [Google Scholar] [CrossRef]
- Nguyen, T.; Reddi, V.J. Deep reinforcement learning for network security. IEEE Commun. Mag. 2019, 57, 52–58. [Google Scholar]
- McMahan, B.; Moore, E.; Ramage, D.; Hampson, S.; Arcas, B.A. Communication-efficient learning of deep networks from decentralized data. In Proceedings of the International Conference on Artificial Intelligence and Statistics (AISTATS), Fort Lauderdale, FL, USA, 20–22 April 2017. [Google Scholar]
- Li, T.; Sahu, A.; Talwalkar, A.; Smith, V. Federated learning: Challenges, methods, and future directions. IEEE Signal Process. Mag. 2020, 37, 50–60. [Google Scholar] [CrossRef]
- Brisimi, T.S.; Chen, R.; Mela, T.; Olshevsky, A.; Paschalidis, I.C.; Shi, W. Federated learning of predictive models from federated electronic health records. Int. J. Med. Inform. 2018, 112, 59–67. [Google Scholar] [CrossRef]
- Javaid, M.; Haleem, A.; Singh, R.P.; Suman, R. Substantial role of artificial intelligence in healthcare systems: A review. Int. J. Intell. Netw. 2021, 2, 100–111. [Google Scholar]
- Ahmad, Z.; Shahid, M.; Khan, L.; Alqahtani, F.; Gani, A. Deep learning-based intrusion detection in IoT networks: A survey. IEEE Commun. Surv. Tutor. 2021, 23, 2386–2421. [Google Scholar]
- Koroniotis, N.; Moustafa, N.; Sitnikova, E.; Slay, J. Towards the development of realistic IoT network intrusion datasets. Comput. Secur. 2019, 81, 158–179. [Google Scholar]
- Ferrag, M.A.; Maglaras, L.; Moschoyiannis, S.; Janicke, H. Deep learning for cyber security intrusion detection: Approaches, datasets, and comparative study. J. Inf. Secur. Appl. 2020, 50, 102419. [Google Scholar] [CrossRef]
- Alazab, M.; Tang, M.; Luo, Y. Deep learning for cybersecurity: A comprehensive survey. IEEE Commun. Surv. Tutor. 2022, 24, 2586–2636. [Google Scholar]
- Rahman, M.A.; Hossain, M.S.; Muhammad, G.; Alhamid, M.F. Secure and provenance-enhanced Internet of Health Things framework: A blockchain-based approach. IEEE Access 2019, 7, 102888–102899. [Google Scholar]
- Islam, S.M.R.; Kwak, D.; Kabir, M.H.; Hossain, M.; Kwak, K.S. The Internet of Things for health care: A comprehensive survey. IEEE Access 2015, 3, 678–708. [Google Scholar] [CrossRef]
- Hassan, M.M.; Gumaei, A.; Alhamid, M.F.; Fortino, G. A hybrid deep learning model for efficient intrusion detection in healthcare IoT. Future Gener. Comput. Syst. 2020, 111, 748–759. [Google Scholar]
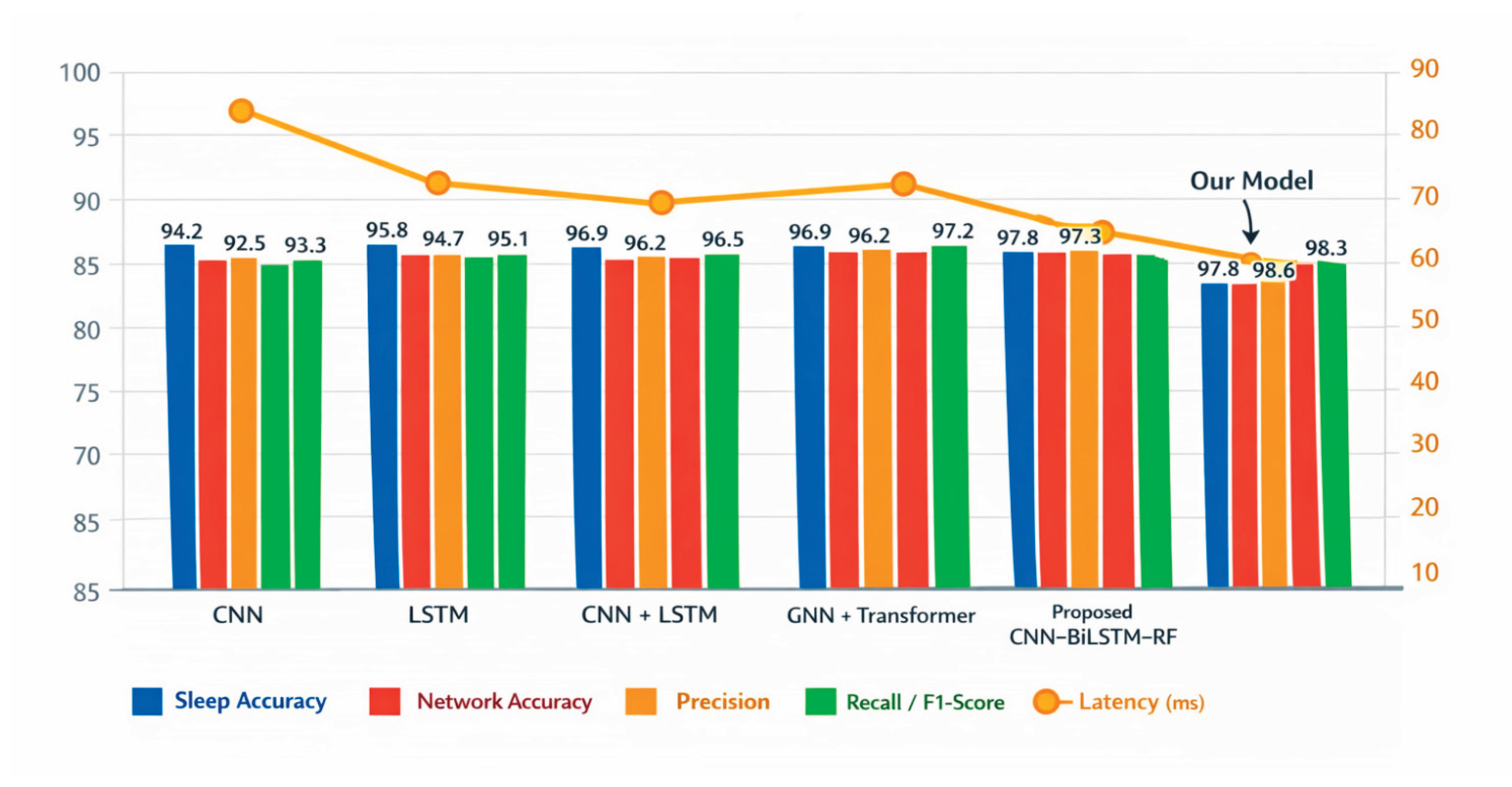
| Model | Sleep Accuracy (%) | Network Detection Accuracy (%) | Precision (%) | Recall (%) | F1-Score (%) | Latency (ms) |
|---|---|---|---|---|---|---|
| CNN | 94.2 | 92.5 | 93.8 | 92.9 | 93.3 | 55 |
| LSTM | 95.8 | 94.7 | 95.1 | 94.4 | 94.7 | 60 |
| CNN + LSTM | 96.9 | 96.2 | 96.5 | 96 | 96.2 | 52 |
| GNN + Transformer | 97.2 | 97.8 | 97.5 | 97.1 | 97.3 | 85 |
| Proposed CNN–BiLSTM–RF | 97.8 | 98.6 | 98.3 | 98.4 | 98.3 | 42 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




