Submitted:
18 February 2026
Posted:
25 February 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. Background and Motivation
1.2. Problem Statement
- In high-value contexts, trust must extend beyond the file integrity to provenance—the document’s origin under an issuing authority. Common designs lack a natively enforced issuer-document linkage; verification often traces addresses or registries rather than reading a formal on-chain relationship. Also, document NFTs are flat and transferable (unsuitable for personal and specific records), and on-chain storage is costly. We design a system for an institutional context, finance-first but domain-agnostic, that (i) cryptographically binds each document to its issuer with tokens, (ii) prevents post-issuance sale or transfer of document tokens, (iii) keeps verification simple and traceable, and (iv) fits role-based, permissioned deployments.
1.3. Research Objectives
- Design a hierarchical tokenization model that encodes a structured issuer-document (parent-child) relationship.
- Implement smart contracts using ERC-721 and ERC-6150 (hierarchical token standard) with necessary features to support the parent-child token logic and non-transferability.
- Integrate an off-chain storage solution for the document payloads while maintaining verification integrity through on-chain cryptographic hashes.
- Deploy the proposed system on a permissioned, Ethereum-compatible multi-node network with governance and access control, mirroring a controlled institutional environment.
- Simulate issuance/verification workflows and conduct a functional evaluation to show that the system preserves document trust and provenance without incurring excessive gas costs or computational overhead, confirming practical feasibility.
1.4. Research Contribution
- A theory-led hierarchical tokenization model that enforces issuer-document lineage on-chain and prohibits token transfer.
- A smart contract realization of hierarchical NFTs (ERC-6150), with a form of soulbound behavior (non-transferability), tailored to document verification.
- An on-chain/off-chain strategy that preserves scalability and recomputable proofs in the context of the proposed model.
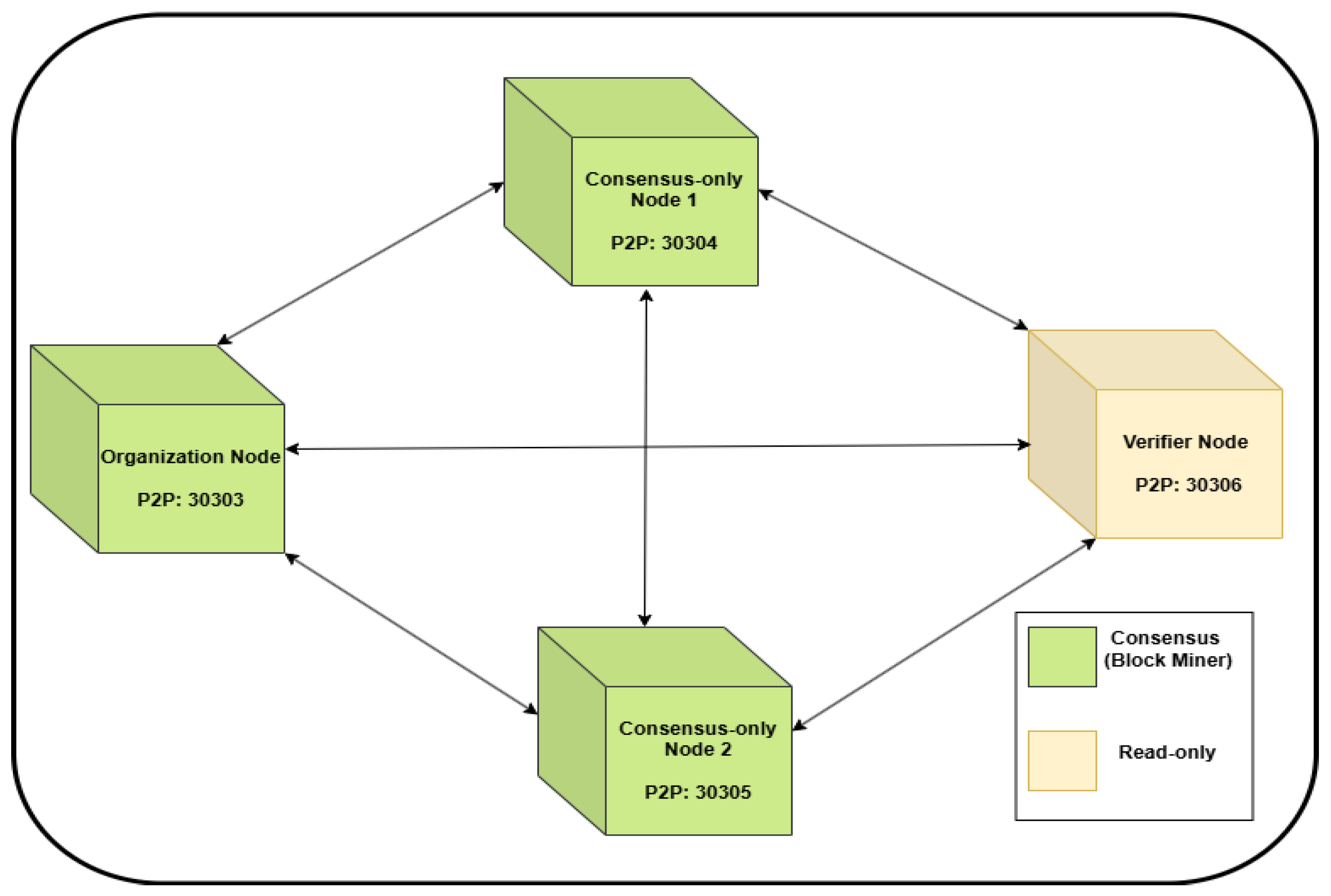
- A four-node, permissioned deployment that demonstrates feasibility and mirrors institutional governance and controlled access.
- A domain-agnostic verification high-value document verification framework, prioritizing financial documents as the initial use case.
1.5. Paper Outline
2. Related Work
2.1. Digital Document Authentication Methods
2.2. Blockchain-Based Document Authentication
2.3. Tokenization of Digital Assets: Identity and Document Assurance
2.3.1. Digital Identity: From SSI/DIDs to Tokenized Credentials
2.3.2. Tokenized Documents: Metadata and Off-Chain Anchoring
2.4. The Need for Hierarchical Token Models
3. Materials and Methods
3.1. Overview of the Hierarchical Model
- Issuer-bound verification. DVTs cannot exist independently; they are hierarchically linked to a legitimate OT, anchoring each document to its issuing institution.
- Scalability and efficiency. On-chain data is minimized to hashes and references, while large document content is stored off-chain.
- Governance and control. Only OT holders are authorized to mint DVTs, aligning token issuance with real-world institutional hierarchies and internal controls.
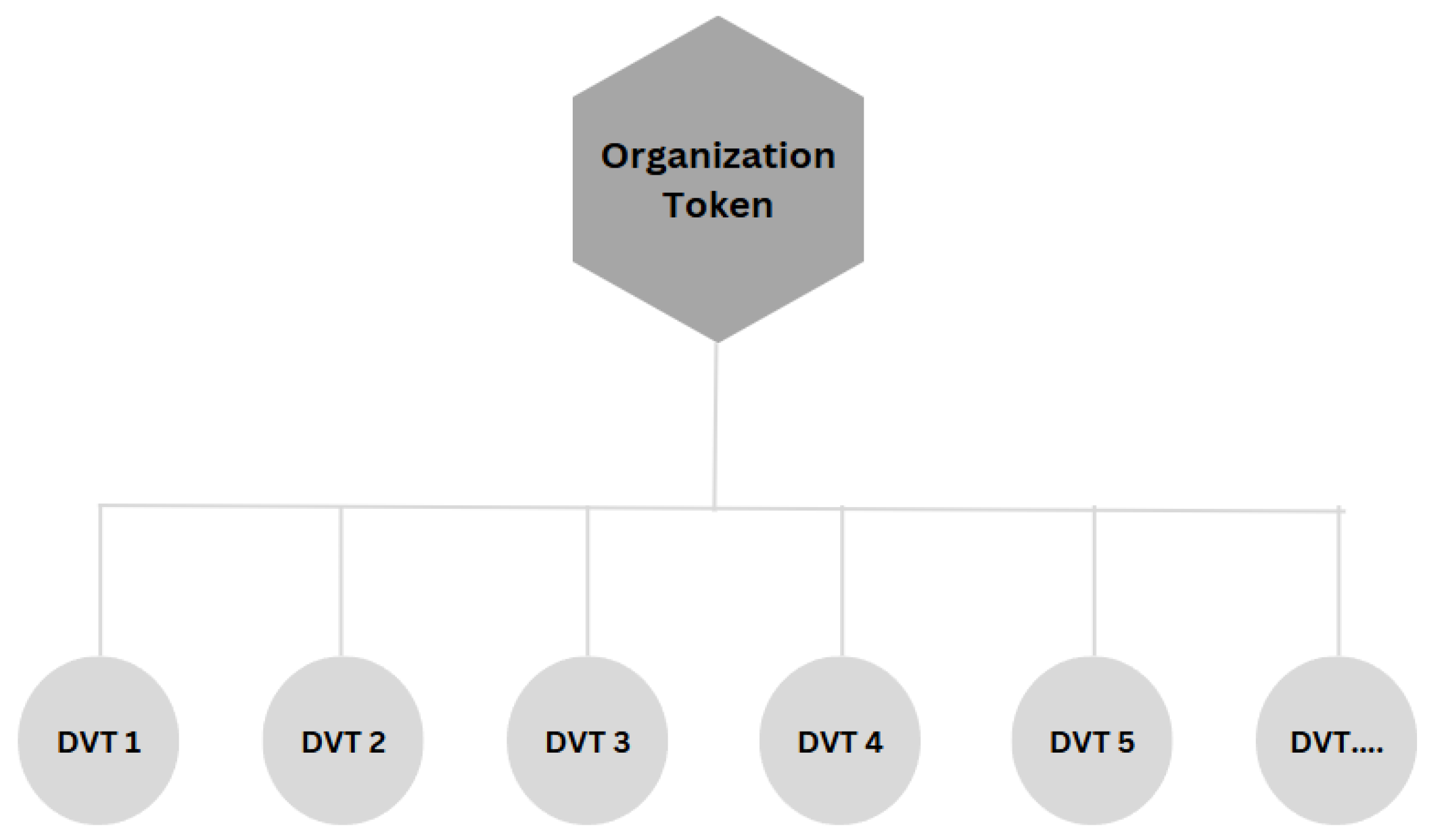
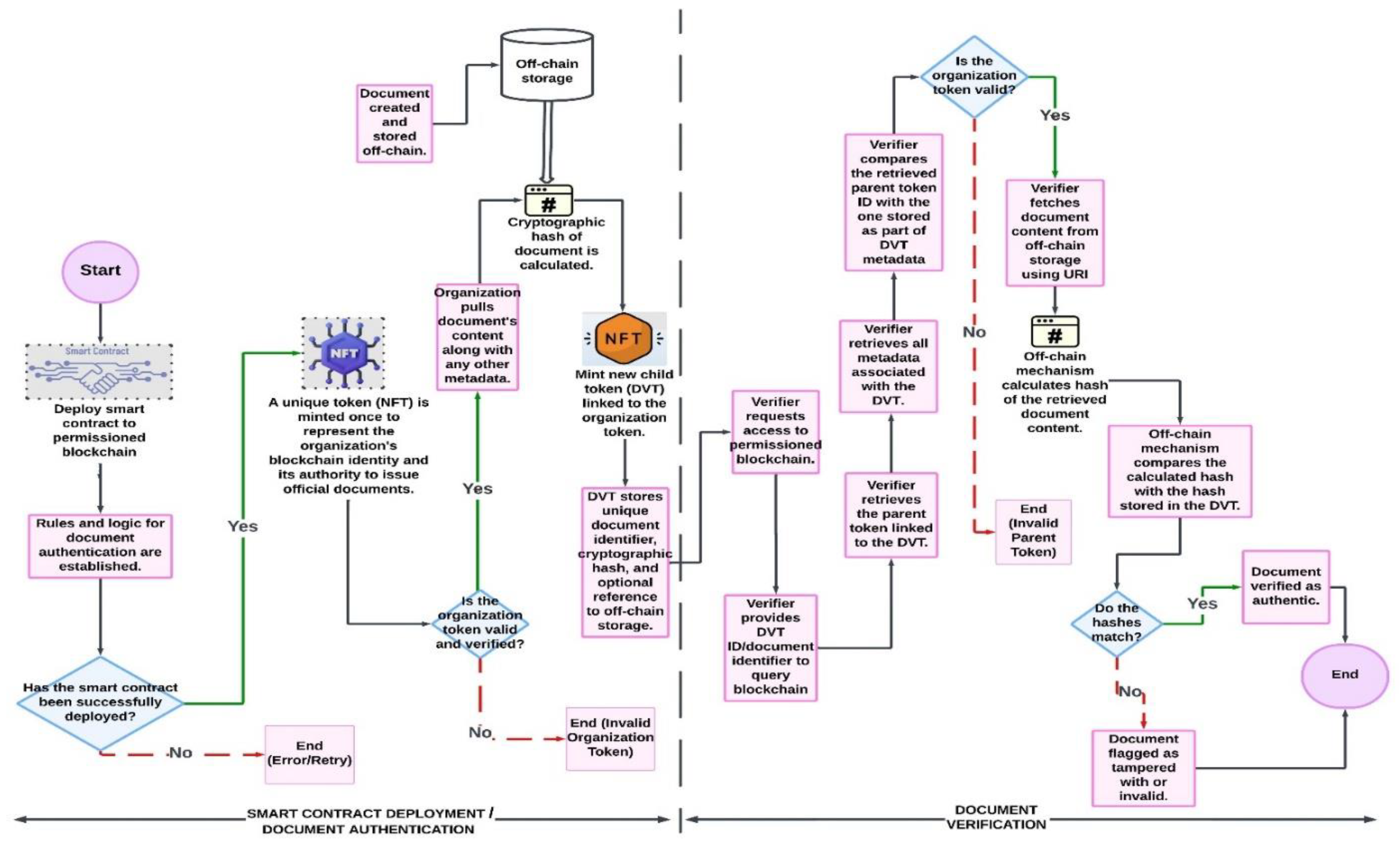
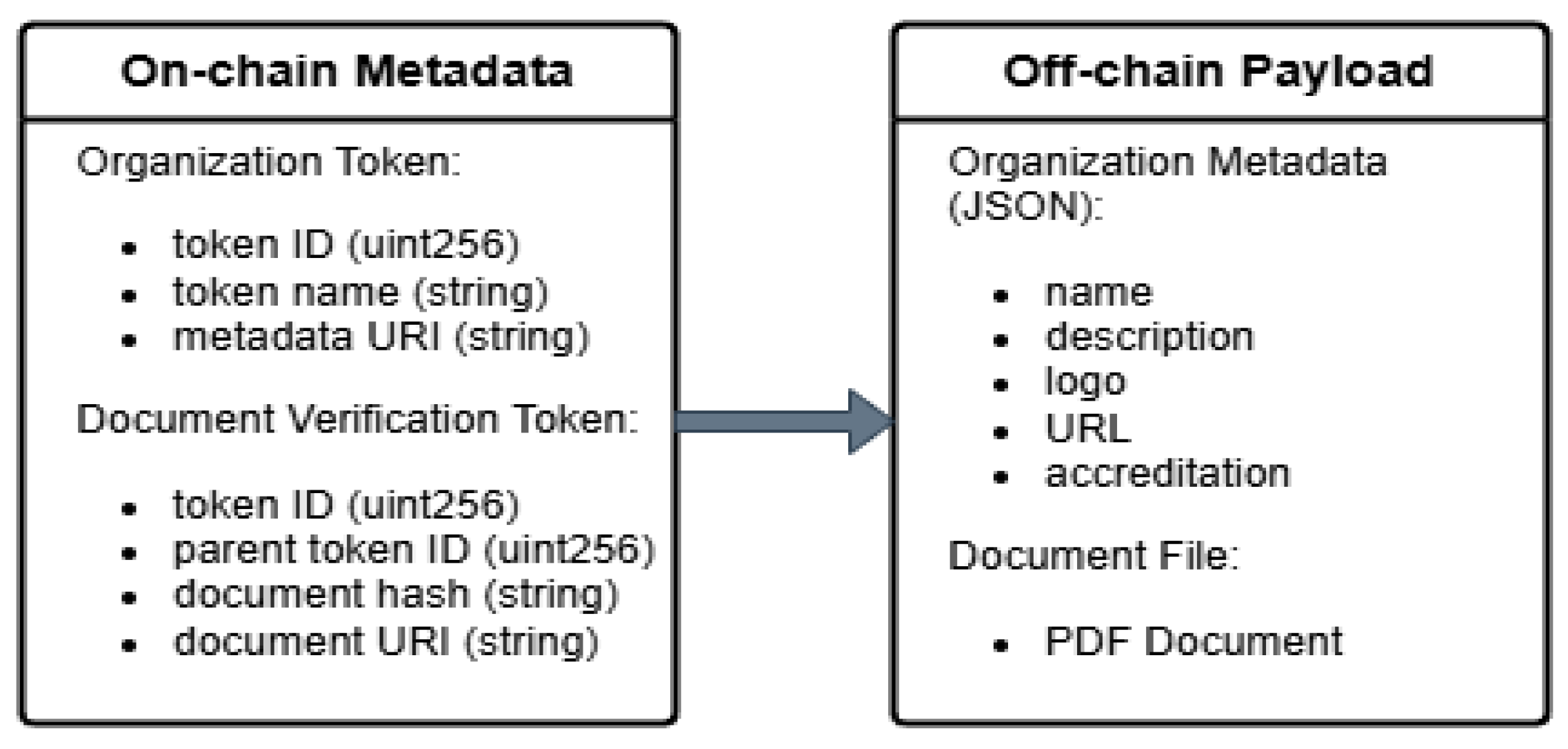
3.2. Model Components
3.2.1. Permissioned Blockchain Network
3.2.2. Organization Token (OT)
3.2.3. Document Verification Token (DVT) and Document Requirements
- Static and finalized. Documents are in their final form at issuance and are not edited afterward.
- Deterministically hashable. Files use formats that yield stable hashes (e.g., PDF, XML) without dependence on external resources.
- Self-contained and time-independent. Content and structure do not change based on access time, environment, or external links.
- Institutionally approved. Each document reflects the institution’s official, authoritative version at the time of issuance.
- Material significance. Only documents whose authenticity materially matter (e.g., certifications, contracts, high-value records) are tokenized.
- Verifiable access. Documents remain accessible for verification, either publicly or through controlled access mechanisms.
3.2.4. Parent–Child Relationship
3.2.5. Off-Chain Storage and Integrity Proofs
3.2.6. Token Standards Compliance
- Implementing parentOf(tokenId) and childrenOf(parentTokenId) functions.
- Overriding the _transfer function to enforce non-transferability for the OT and DVTs.
- Internally mapping each DVT to its OT via a stored parentTokenId.
3.2.7. Role of Smart Contracts
- Which address is permitted to mint an OT
- How DVTs are created and linked to their parent OT
- The rules that disable token transfers.
- How document hashes, URIs, and other metadata are stored immutably on-chain.
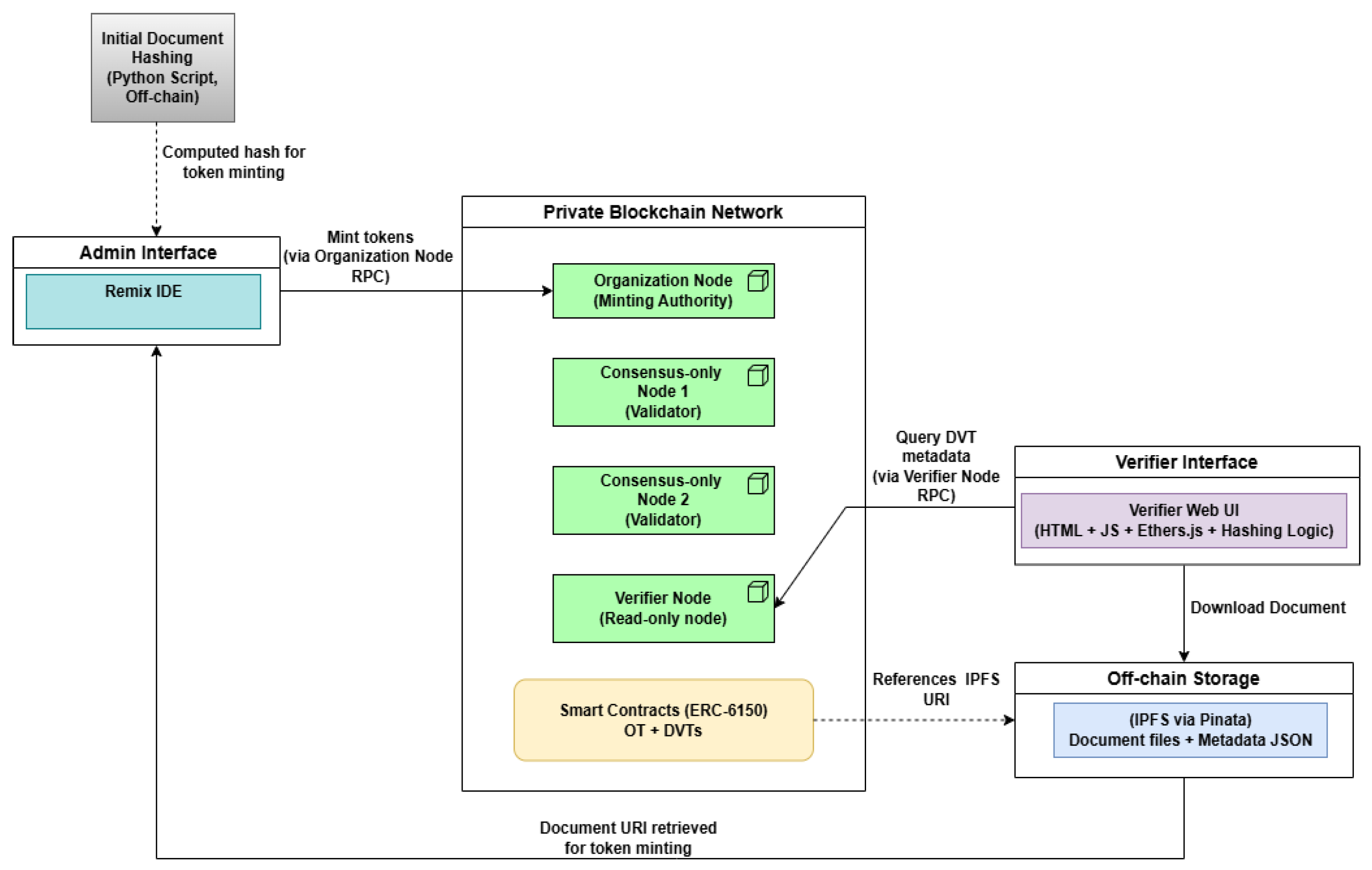
3.3. System Architecture
3.3.1. Logical Architecture
3.3.2. Besu Topology, Deployment, and Permissioning.
3.4. Blockchain Platform Selection and Justification
3.4.1. Selection Criteria.
3.4.2. Choice of Blockchain Platform
3.4.3. Network Parameters and Toolchain
3.5. Algorithms
| Algorithm 1: MintOrganizationToken (OT minting) |
| 1: Input: admin address , orgId, orgName, orgURI. 2: Require that is the authorised admin and has not previously minted an OT. 3: Require that orgId has not been used. 4: Mint a non-fungible token with ID orgId to . 5: Store organisation metadata (orgName, orgURI) under orgId. 6: Record that has an OT and link . 7: Mark the OT as non-transferable (soulbound). 8: Output: OT ID orgId. (used later as parentId for DVTs) |
| Algorithm 2: MintDVT (document token under an OT) |
| 1: Input: issuer address , document hash h, document URI uri. 2: On-chain: fetch parentId = orgTokenIdOf[a]; require parentId ≠ 0 and ownerOf(parentId) = a. 3:Require that and uri have not been used by any previous DVT. 4: Allocate a new DVT ID dvtId from an auto-increment counter. 5: Mint DVT dvtId to and set its parent to parentId. 6: Store DVT metadata (parentId, , uri) and mark hash and URI as used. 7: Mark the DVT as non-transferable (soulbound). 8: Output: DVT ID dvtId |
| Algorithm 3: HierarchicalQueries (parent–child) |
| 1: Input (A): OT ID parentId. 2: Verify that parentId exists. 3: Return the list of DVT IDs childrenOf(parentId). 4: Input (B): DVT ID dvtId. 5: Verify that dvtId exists. 6: Return the parent OT ID parentOf(dvtId). |
| Algorithm 4: Access-Control Check for Minting |
| 1: Input: caller address , action ∈ {MintOT, MintDVT}. 2: If action = MintOT: 3: Require that is the contract owner/admin and has not minted an OT. 4: If true, authorise; otherwise, reject. 5: If action = MintDVT: 6: Require that orgTokenIdOf[a] ≠ 0 and ownerOf(orgTokenIdOf[a]) = a. 7: If true, authorise; otherwise, reject. 8: Output: allow / reject |
| Algorithm 5: Off-Chain Document Verification (hash comparison) |
| 1: Input: DVT ID dvtId. 2: On-chain: via the verifier node, call getParentTokenId(dvtId) to obtain parentId; if parentId does not correspond to a valid Organization Token, classify the document as Not authentic and abort. 3: On-chain: read DVT metadata for dvtId and obtain stored hash h_stored and document URI uri. 4: Off-chain: fetch the document bytes from uri (IPFS or HTTPS). 5: Compute h_computed = Keccak-256 of the fetched bytes. 6: Normalise h_stored and h_computed to the same hex format. 7: If h_computed = h_stored, classify the document as Authentic; otherwise classify as Not authentic. 8: Output: verification result (Authentic / Not authentic) |
3.6. Document Authentication and Verification Workflow (Financial-Document Scenario)
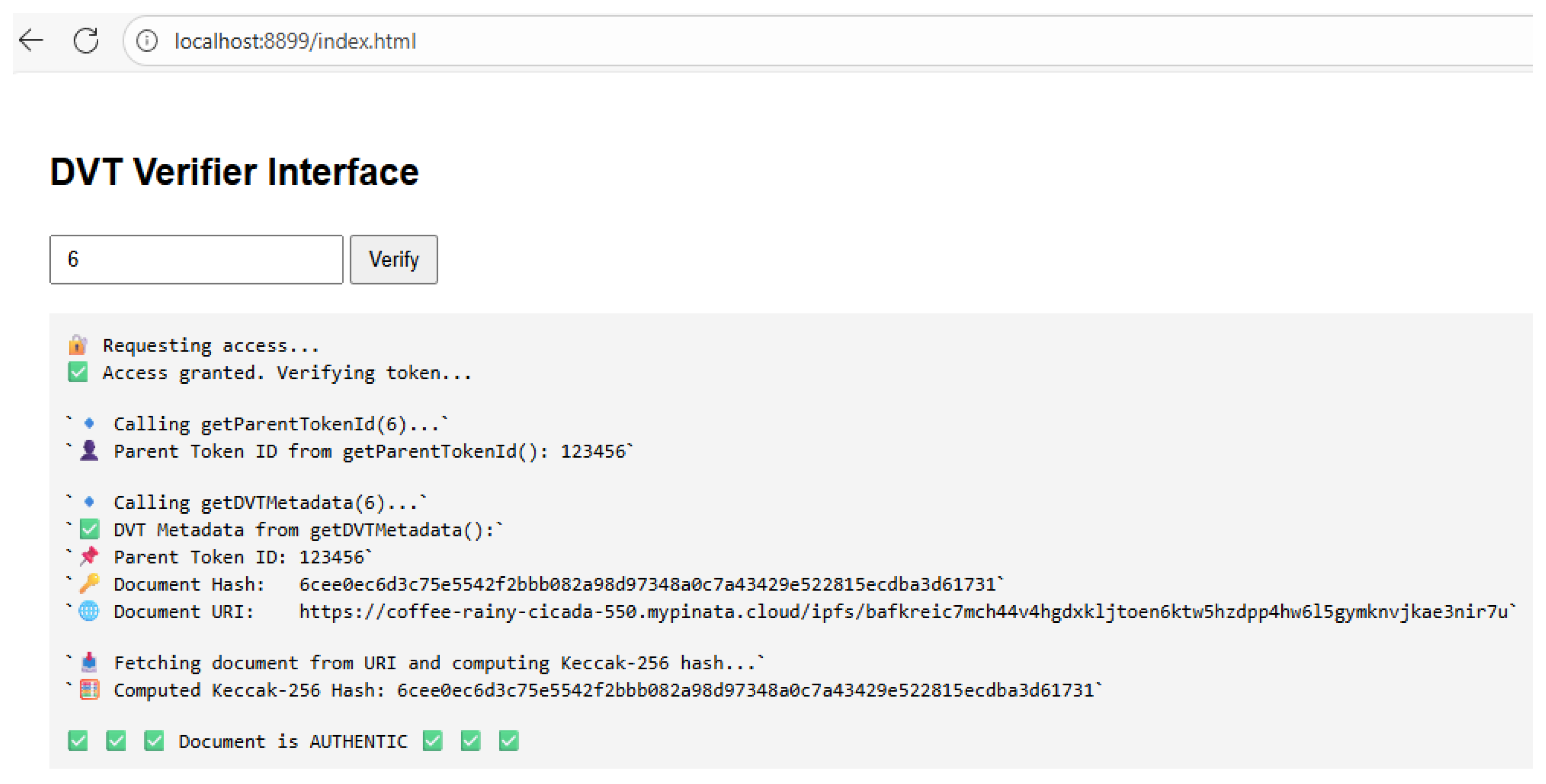
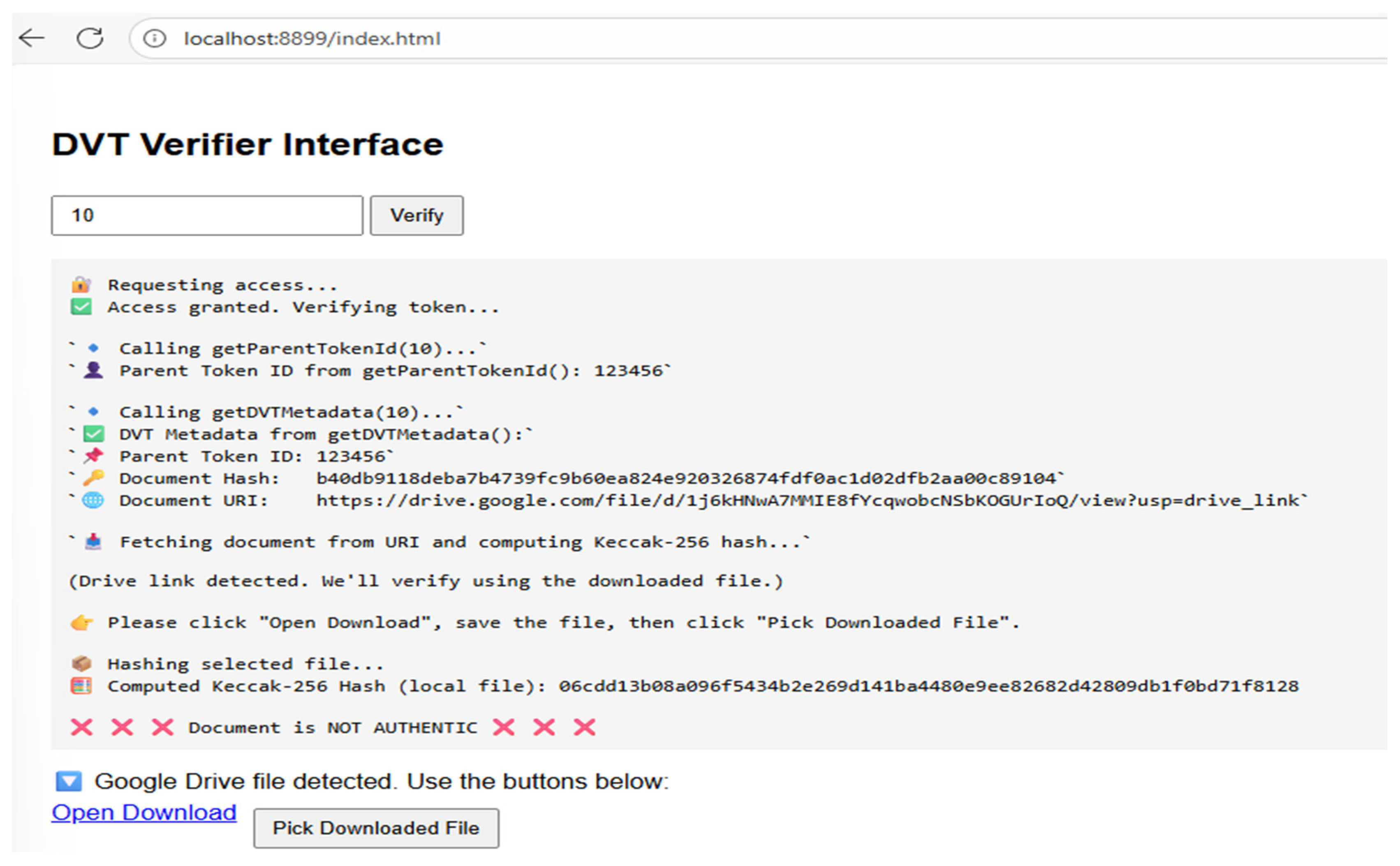
- The verifier compares the parent OT ID returned by getParentTokenId with the parent ID embedded in the DVT metadata. If they do not match, the process is terminated, and the document is treated as untrusted.
- If the parent IDs are consistent, the verifier fetches the document from the off-chain document URI provided in the metadata.
- The verifier recomputes the document hash using the same Keccak-256 algorithm on the fetched bytes.
- The recomputed hash is compared to the hash stored in the DVT metadata. If they match, the document is considered authentic; if not, it is treated as altered or replaced.
4. Implementation and Results.
4.1. Smart-Contract Execution Evidence
4.1.1. Organization Token Minting (Figure 6).
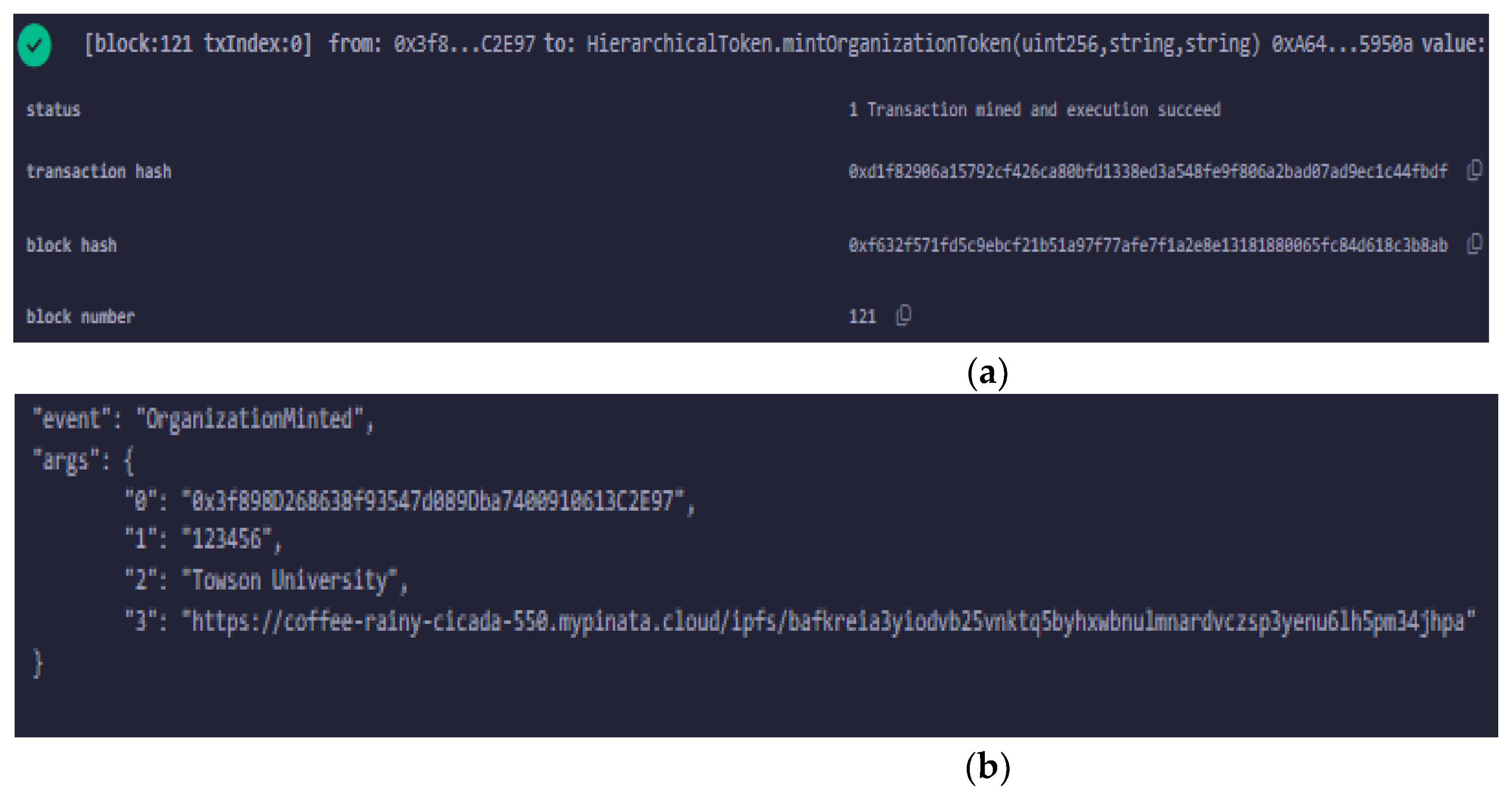
- Figure 6 shows the successful execution of mintOrganizationToken. Panel (a) presents the transaction receipt for the OT with a specified orgId, confirming that the transaction was mined and gas was consumed as expected. Panel (b) shows the corresponding OrganizationMinted event, including the admin address and OT identifier, demonstrating that the organization’s non-transferable anchor token was recorded on-chain and linked to its metadata
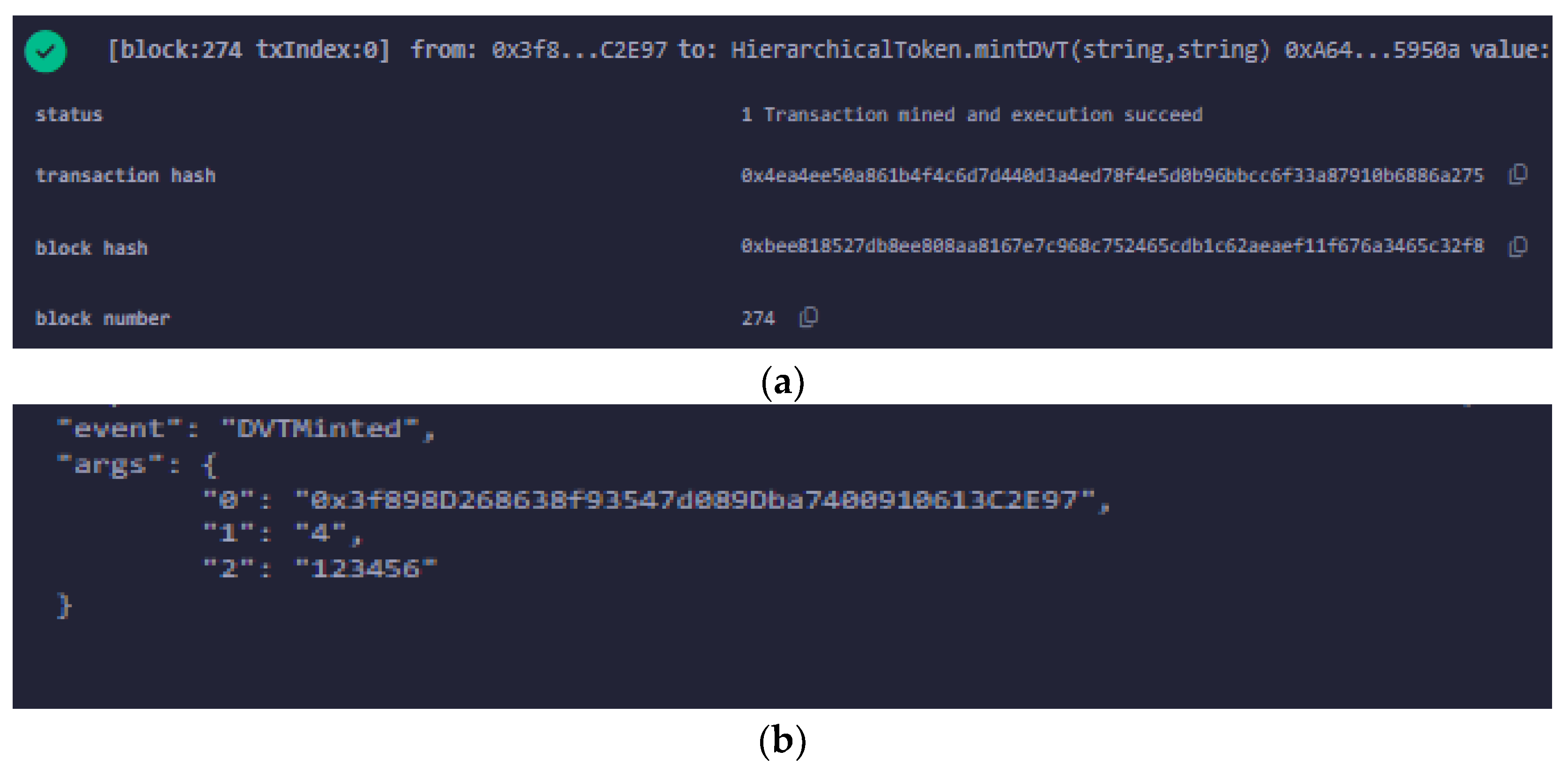
4.1.2. Document Verification Token Minting (Figure 7).
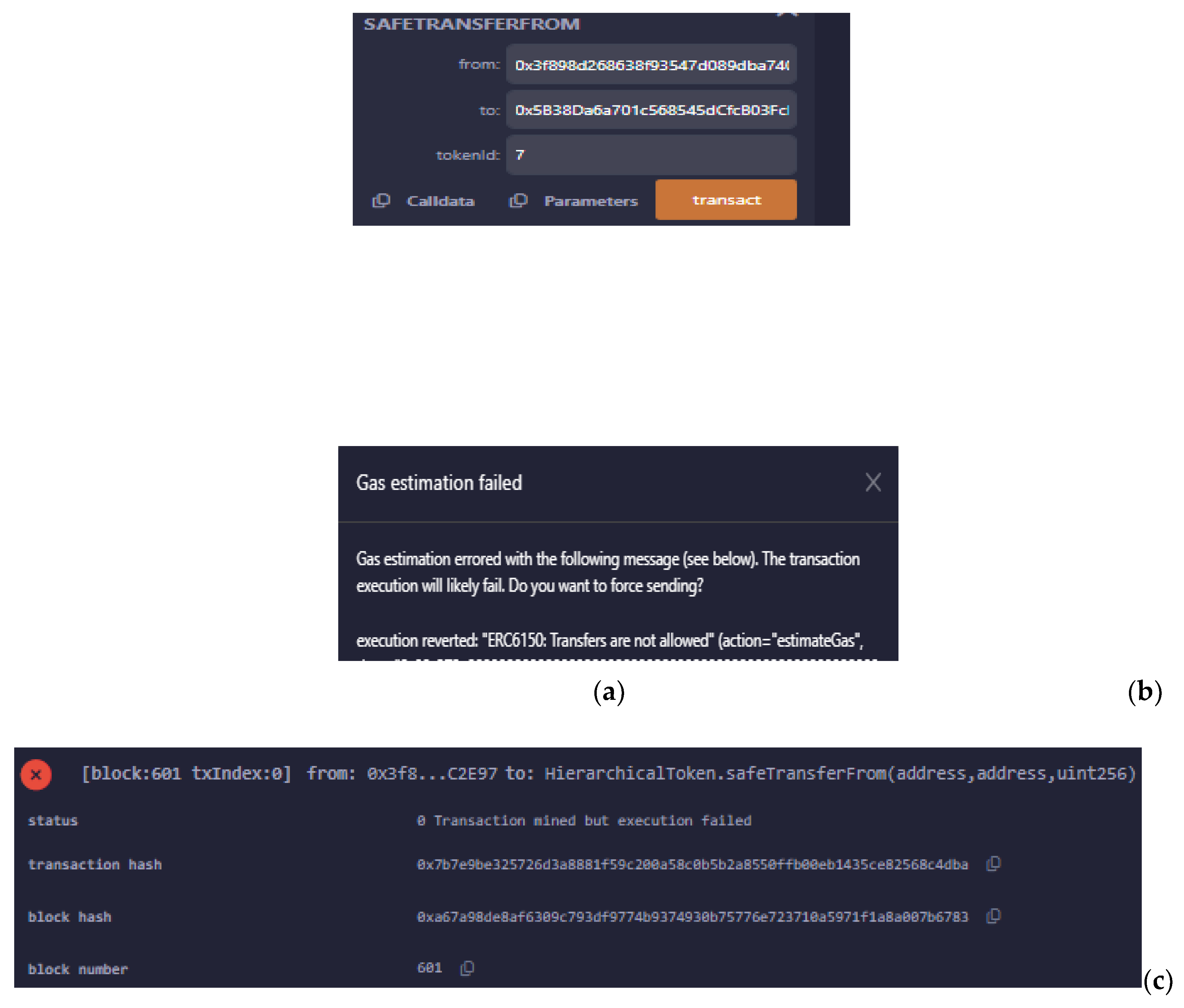
4.1.3. Non-Transferability Enforcement(Figure 8).
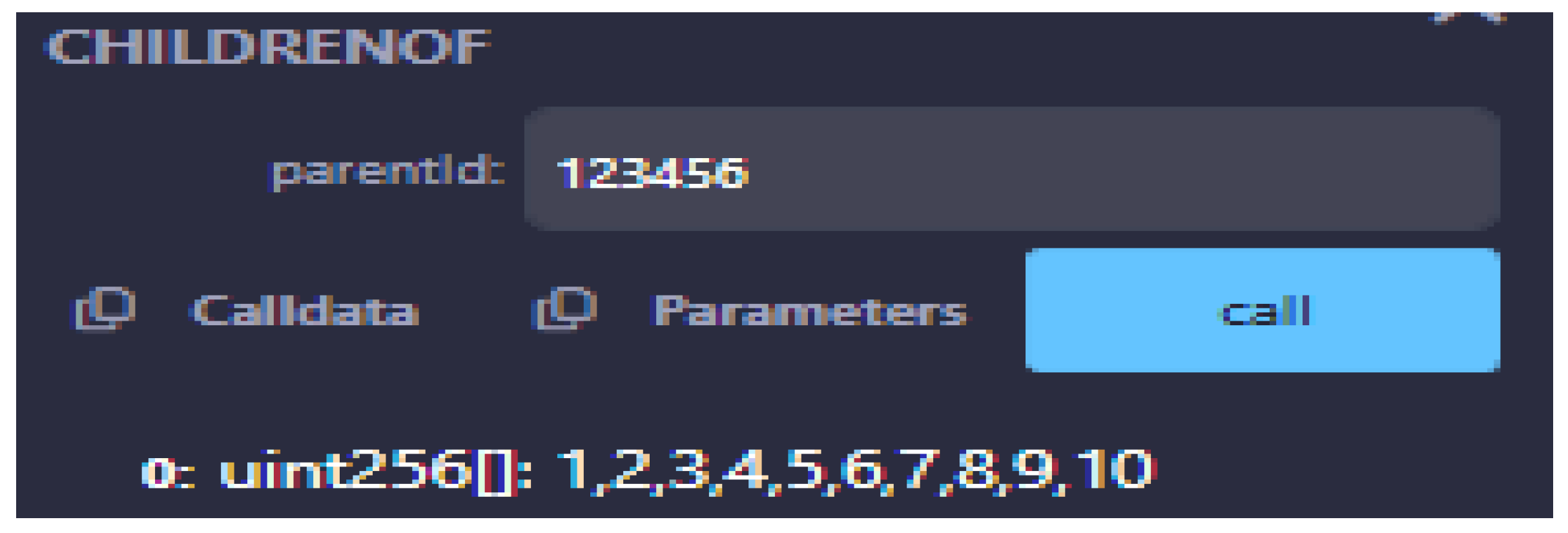
4.1.4. Child Token Retrieval Under the Parent (Figure 9)
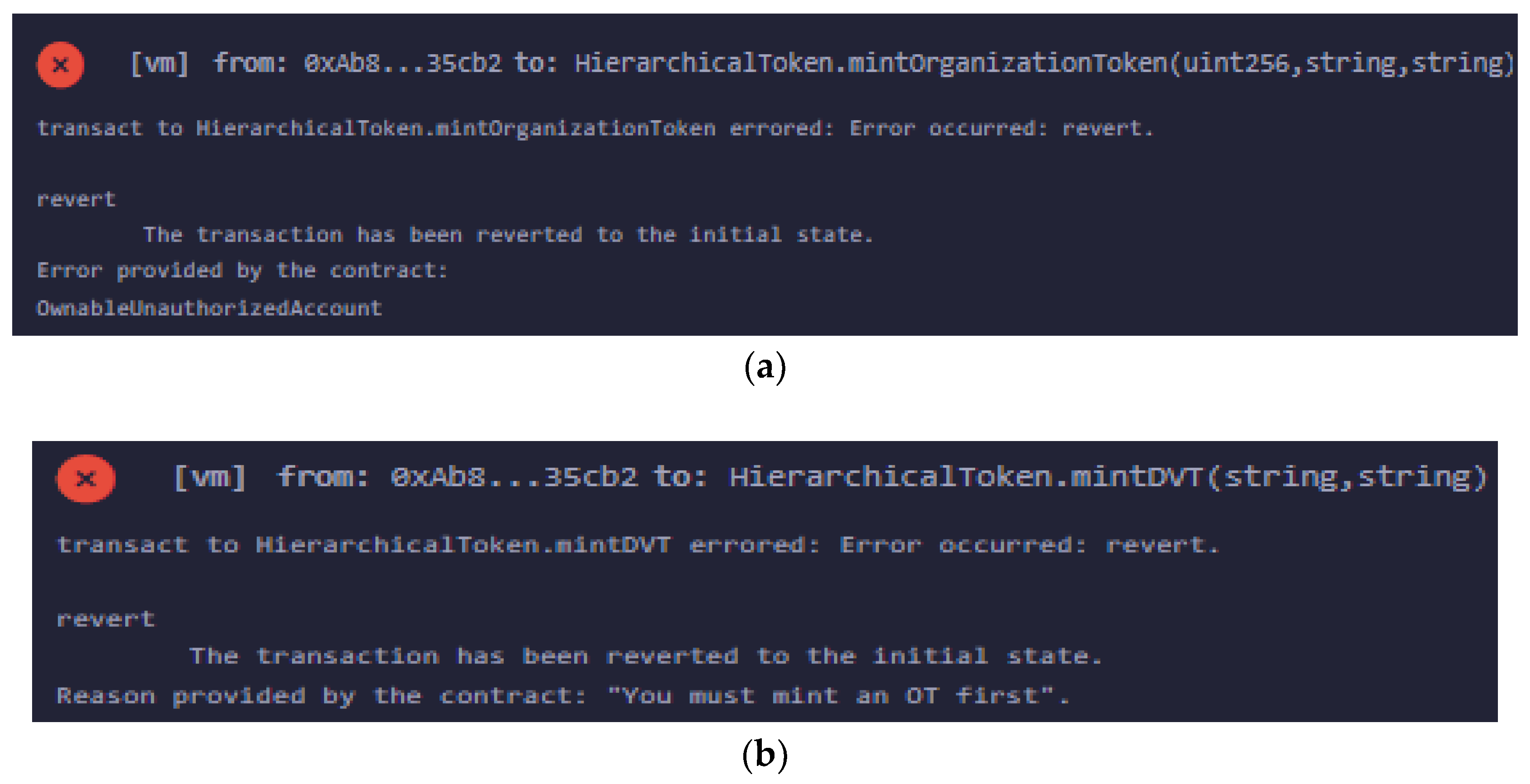
4.1.5. Access Control Checks (Figure 10)
4.2. Verifier User Interface
4.3. Functional Evaluation
| ID | Functional Requirement | Evidence (section / figure /algorithm) | Outcome |
|---|---|---|---|
| R1 | Only the designated organization node can mint an OT | Contract logic in Section 3.2.7; Algorithms 1 & 4; access-control results in Figure 10 (non-admin OT mint rejected) | Pass |
| R2 | Only OT holders can mint DVTs under their own OT | Contract logic in Section 3.2.7; Algorithms 2 & 4; Figure 10 (failed DVT mint from non-OT address) |
Pass |
| R3 | OT and DVTs are non-transferable (soulbound semantics) | Non-transferability design in Section 3.2.6; Algorithms 1 & 2 ; Figure 8 (transfer attempt revert) | Pass |
| R4 | Hierarchical OT→DVT linkage is correctly maintained and queryable | Hierarchy model in Section 3.2.4; Algorithm 3; Figure 9 (list of child DVT IDs under an OT) | Pass |
| R5 | Each document is uniquely represented by its hash and URI | DVT metadata design in Section 3.2.3; Algorithm 2; contract checks on usedDocumentHashes and usedDocumentURIs |
Pass |
| R6 | Off-chain verification of documents without new blockchain transactions for verifiers | Verification workflow in Section 3.6; Algorithm 5; verifier UI in Section 4.2 and Figure 11 | Pass |
| R7 | Permissioned network with separated roles (organization, consensus-only nodes, verifier) | System architecture in Section 3.3; smart-contract execution evidence in Section 4.1 |
Pass |
| R8 | Acceptable responsiveness for typical minting and verification operations | Qualitative observations from test runs in Section 4.1 and verifier UI interactions in Section 4.2 | Pass |
4.4. Basic Security Considerations
4.5. Tampering Scenario: Mutable Off-Chain Storage
5. Discussion
5.1. Known Limitations
5.1. Positioning and Implications
6. Conclusion and Future Work
6.1. Summary of Findings
6.1. Future Work
Supplementary Materials
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Afrakhteh, M., Ibrahim, S., & Salleh, M. (2010). Printed Document Authentication Using Watermarking Technique. 2010 Second International Conference on Computational Intelligence, Modelling and Simulation, 367–370. [CrossRef]
- Al-Ameri, M. A. A., Mahmood, B., Ciylan, B., & Amged, A. (2023). Unsupervised Forgery Detection of Documents: A Network-Inspired Approach. Electronics, 12(7), 1682. [CrossRef]
- Ali, V. E., Asika, M. O., Elebesunu, E. E., Agbo, C., & Antwi, M. H. (2024). Cognizance and mitigation of falsified immunization documentation: Analyzing the consequences for public health in Nigeria, with a focus on counterfeited COVID-19 vaccination cards: A case report. Health Science Reports, 7(2), e1885. [CrossRef]
- Anwar, M. J., & Gill, A. Q. (2025). NFTs enabled federated digital identity data representation and management. Discover Data, 3(1), 19. [CrossRef]
- Artha, K. A. R., Zain, S. N., Alkautsar, A. A., & Widianto, M. H. (2022). Implementation of Smart Contracts for E-Certificate as Non-Fungible Token using Solana Network. Proceedings of the 2022 IEEE 7th International Conference on Information Technology and Digital Applications, ICITDA 2022. [CrossRef]
- Baechler, S. (2020). Document Fraud: Will Your Identity Be Secure in the Twenty-first Century? European Journal on Criminal Policy and Research, 26(3), 379–398. [CrossRef]
- Banaeian Far, S., & Hosseini Bamakan, S. M. (2023). NFT-based identity management in metaverses: challenges and opportunities. SN Applied Sciences, 5(10), 260. [CrossRef]
- Bhagat, N., Bae, J., & Lee, S.-H. (2025). Dynamic Management of Hierarchical NFTs: Efficient Splitting and Merging. Journal of the Korea Society of Computer and Information, 30(2), 73–82. [CrossRef]
- Blockcerts. (n.d.). Blockcerts: The open standard for blockchain credentials. Retrieved November 20, 2025, from https://www.blockcerts.org.
- Böhmecke-Schwafert, M. (2024). The role of blockchain for trade in global value chains: A systematic literature review and guidance for future research. Telecommunications Policy, 48(9), 102835. [CrossRef]
- ConsenSys, Inc. (2024). ConsenSys GoQuorum documentation. https://docs.goquorum.consensys.io/.
- Devlin, C., Chadwick, S., Moret, S., Baechler, S., Rossy, Q., & Morelato, M. (2024). Illuminating the dark web market of fraudulent identity documents and personal information: An international and Australian perspective. Forensic Science International, 363, 112203. [CrossRef]
- Eltuhami, M., Abdullah, M., & Talip, B. A. (2022). Identity Verification and Document Traceability in Digital Identity Systems using Non-Transferable Non-Fungible Tokens. 2022 International Visualization, Informatics and Technology Conference (IVIT), 136–142. [CrossRef]
- Ethereum Foundation. (2024, June 16). Private networks. Go-Ethereum Documentation. https://geth.ethereum.org/docs/fundamentals/private-network.
- Faccia, A., Pandey, V., & Banga, C. (2022). Is Permissioned Blockchain the Key to Support the External Audit Shift to Entirely Open Innovation Paradigm? Journal of Open Innovation: Technology, Market, and Complexity, 8(2), 85. [CrossRef]
- Gebreab, S. A., Salah, K., Jayaraman, R., & Zemerly, J. (2023). Trusted Traceability and Certification of Refurbished Medical Devices Using Dynamic Composable NFTs. IEEE Access, 11, 30373–30389. [CrossRef]
- Georgiou, I., Sapuric, S., Lois, P., & Thrassou, A. (2024). Blockchain for Accounting and Auditing—Accounting and Auditing for Cryptocurrencies: A Systematic Literature Review and Future Research Directions. Journal of Risk and Financial Management, 17(7), 276. [CrossRef]
- Guidi, B., & Michienzi, A. (2023). From NFT 1.0 to NFT 2.0: A Review of the Evolution of Non-Fungible Tokens. Future Internet, 15(6), 189. [CrossRef]
- Hammi, B., Zeadally, S., & Perez, A. J. (2023). Non-Fungible Tokens: A Review. IEEE Internet of Things Magazine, 6(1), 46–50. [CrossRef]
- Hasan, H. R., Madine, M., Musamih, A., Jayaraman, R., Salah, K., Yaqoob, I., & Omar, M. (2024). Non-fungible tokens (NFTs) for digital twins in the industrial metaverse: Overview, use cases, and open challenges. Computers & Industrial Engineering, 193, 110315. [CrossRef]
- Hyperledger Foundation. (2023). Hyperledger Fabric documentation (release 2.5). https://hyperledger-fabric.readthedocs.io/en/release-2.5/.
- Hyperledger Foundation. (2025, December 19). Besu for private (permissioned) networks. https://besu.hyperledger.org/private-networks.
- Jirgensons, M., & Kapenieks, J. (2018). Blockchain and the Future of Digital Learning Credential Assessment and Management. Journal of Teacher Education for Sustainability, 20(1), 145–156. [CrossRef]
- Khan, M. M., Khan, F. S., Nadeem, M., Khan, T. H., Haider, S., & Daas, D. (2025). Scalability and Efficiency Analysis of Hyperledger Fabric and Private Ethereum in Smart Contract Execution. Computers, 14(4), 132. [CrossRef]
- Kim, G., & Ryou, J. (2023). Digital Authentication System in Avatar Using DID and SBT. Mathematics, 11(20), 4387. [CrossRef]
- Kumar, N. N., Kumar, R. S., Basale, R. R., & Saffath, M. (2022). Decentralized Storage Of Educational Assets Using NFTs And Blockchain Technology. 2022 International Conference on Smart Systems and Inventive Technology (ICSSIT), 260–266. [CrossRef]
- Kuznetsov, O., Frontoni, E., Kuznetsova, K., Shevchuk, R., & Karpinski, M. (2024). NFT Technology for Enhanced Global Digital Registers: A Novel Approach to Tokenization. Future Internet, 16(7), 252. [CrossRef]
- Lee, H., & Yeon, C. (2021). Blockchain-Based Traceability for Anti-Counterfeit in Cross-Border E-Commerce Transactions. Sustainability, 13(19), 11057. [CrossRef]
- Lee, K., msfew, Kartin, & qizhou. (2022, December 15). ERC-6150: Hierarchical NFTs. Ethereum Improvement Proposals. https://eips.ethereum.org/EIPS/eip-6150.
- Lockyer, M., Mudge, N., Schalm, J., Echeverry, S., & Zhou, Z. V. (2018, July 7). ERC-998: Composable non-fungible token. Ethereum Improvement Proposals. https://eips.ethereum.org/EIPS/eip-998.
- López-Pimentel, J. C., Gonzalez-Sanchez, J., & Morales-Rosales, L. A. (2025). A Digital Identity Blockchain Ecosystem: Linking Government-Certified and Uncertified Tokenized Objects. Applied Sciences, 15(15), 8577. [CrossRef]
- Lunesu, M. I., Tonelli, R., Pinna, A., & Sansoni, S. (2023). Soulbound Token for Covid-19 Vaccination Certification. 2023 IEEE International Conference on Pervasive Computing and Communications Workshops and Other Affiliated Events (PerCom Workshops), 243–248. [CrossRef]
- Mohammad Saeidia, F., Zahedi, M. H., & Farahani, E. (2025). A Secure and Reliable Model for Financial Documents Using Digital Signature and Blockchain Technology. AI and Tech in Behavioral and Social Sciences, 3(1), 23–33. [CrossRef]
- Mohsin Arkah, Z., Alzubaidi, L., Ali, A. A., & Abdulameer, A. T. (2020). Digital Color Documents Authentication Using QR Code Based on Digital Watermarking. In Advances in Intelligent Systems and Computing (Vol. 940, pp. 1093–1101). Springer Verlag. [CrossRef]
- Nakamoto, S. (2008). Bitcoin: A Peer-to-Peer Electronic Cash System. https://bitcoin.org/bitcoin.pdf.
- Nita, S. L., & Mihailescu, M. I. (2024). A Novel Authentication Scheme Based on Verifiable Credentials Using Digital Identity in the Context of Web 3.0. Electronics, 13(6), 1137. [CrossRef]
- Weyl, E. G., Ohlhaver, P., & Buterin, V. (2022). Decentralized Society: Finding Web3’s Soul. SSRN Electronic Journal. [CrossRef]
- Ongwook Bae, J., Bhagat, N., Lee, S.-H., & Bae, J. (2024). Hierarchical NFT using Parent-Child Structure. Journal of The Korea Society of Computer and Information, 29(2), 127–136. [CrossRef]
- Patel, A., Sai, S., Daiya, A., Akolekar, H., & Chamola, V. (2025). Blockchain enabled traceability in the jewel supply chain. Scientific Reports, 15(1), 3837. [CrossRef]
- Peelam, M. S., Chamola, V., Sharma, A. K., & Chaurasia, B. K. (2025). Decentralized Trust: NFT and Blockchain-Enabled Evidence System using Fog Computing. Blockchain: Research and Applications, 100321. [CrossRef]
- Pericàs-Gornals, R., Mut-Puigserver, M., Payeras-Capellá, M. M., Cabot-Nadal, M. Á., & Ramis-Bibiloni, J. (2024). Digital credentials management system using rejectable soulbound tokens. Annals of Telecommunications, 79(11–12), 843–855. [CrossRef]
- Pierro, G. A., Cocco, L., & Tonelli, R. (2024). Besu vs. Quorum: Comparative analysis in the context of simulated energy communities. In M. Bartoletti, C. Schifanella, & A. Vitaletti (Eds.), Proceedings of the Sixth Distributed Ledger Technology Workshop (DLT 2024) (CEUR Workshop Proceedings, Vol. 3791) (pp. 1–16). CEUR-WS.org. https://ceur-ws.org/Vol-3791/paper24.pdf.
- Podda, E., Hölzmer, P., Amard, A., Sedlmeir, J., & Fridgen, G. (2025). The impact of zero-knowledge proofs on data minimisation compliance of digital identity wallets. Internet Policy Review, 14(3). [CrossRef]
- Precht, H., Hüllmann, J. A., & Marx Gómez, J. (2026). Paperless Everything: A Systematic Literature Review for the Design of Blockchain-based Document Management Systems. Distributed Ledger Technologies: Research and Practice, 5(2), 1–48. [CrossRef]
- Pu, S., & Lam, J. S. L. (2023). The benefits of blockchain for digital certificates: A multiple case study analysis. Technology in Society, 72, 102176. [CrossRef]
- Cardenas-Quispe, M. A., & Pacheco, A. (2025). Blockchain ensuring academic integrity with a degree verification prototype. Scientific Reports, 15(1), 9281. [CrossRef]
- Ramadhan, M. R., Mandala, S., & Yulianto, F. A. (2023). Analysis and Implementation of Digital Signature Algorithm in PDF Document. 2023 11th International Conference on Information and Communication Technology (ICoICT), 2023-August, 11–16. [CrossRef]
- Ramirez Lopez, L. J., & Morillo Ledezma, G. G. (2025). Employing Blockchain, NFTs, and Digital Certificates for Unparalleled Authenticity and Data Protection in Source Code: A Systematic Review. Computers, 14(4), 131. [CrossRef]
- Razi, Q., Devrani, A., Abhyankar, H., Chalapathi, G. S. S., Hassija, V., & Guizani, M. (2024). Non-Fungible Tokens (NFTs)—Survey of Current Applications, Evolution, and Future Directions. IEEE Open Journal of the Communications Society, 5, 2765–2791. [CrossRef]
- Satybaldy, A., Subedi, A., & Nowostawski, M. (2022). A Framework for Online Document Verification Using Self-Sovereign Identity Technology. Sensors, 22(21), 8408. [CrossRef]
- Silaghi, D. L., & Popescu, D. E. (2025). A Systematic Review of Blockchain-Based Initiatives in Comparison to Best Practices Used in Higher Education Institutions. Computers, 14(4), 141. [CrossRef]
- Singh, P., Sagar, S., Singh, S., Alshahrani, H. M., Getahun, M., & Soufiene, B. O. (2024). Blockchain-enabled verification of medical records using soul-bound tokens and cloud computing. Scientific Reports, 14(1), 24830. [CrossRef]
- Subramanya, S. R., & Yi, B. K. (2006). Digital signatures. IEEE Potentials, 25(2), 5–8. [CrossRef]
- Susik, R., Nowotniak, R., & Kulczycki, E. (2023). Blockchain-based certification of research outputs and academic achievements: A case of scientific conference. Communication Papers of the 18th Conference on Computer Science and Intelligence Systems, 37, 329–333. [CrossRef]
- Szyjewski, G. (2023). Securing Digital Copies of the Documents to Ensure Documents’ Integrity. EUROPEAN RESEARCH STUDIES JOURNAL, XXVI(Issue 4), 718–726. [CrossRef]
- Teraura, N., Echizen, I., & Iwamura, K. (2020). A QR Symbol with ECDSA for Both Public and Secret Areas using Rhombic Sub-cells. 2020 Asia-Pacific Signal and Information Processing Association Annual Summit and Conference (APSIPA ASC), 1392–1399.
- Usha, B. A., Monish, S., Murali Manohara Hegde, A. S., Kumar, N., Aditya, P., & Manjunath, A. (2023). Blockchain Technology in Document Authentication: A Comprehensive Literature Review. 2023 4th International Conference on Communication, Computing and Industry 6.0 (C216), 1–5. [CrossRef]
- Walidaniy, W. D., Yuliana, M., & Darwito, H. A. (2023). Enhancing Document Authenticity with QR Codes and ECC-Based Digital Signatures. 2023 International Electronics Symposium (IES), 238–243. [CrossRef]
- Wellem, T., Nataliani, Y., & Iriani, A. (2022). Academic Document Authentication using Elliptic Curve Digital Signature Algorithm and QR Code. JOIV : International Journal on Informatics Visualization, 6(3), 667. [CrossRef]
- Yerpude, S., Sood, K., & Grima, S. (2022). Blockchain-Augmented Digital Supply Chain Management: A Way to Sustainable Business. Journal of Risk and Financial Management, 16(1), 7. [CrossRef]
- Zhai, X., Pang, S., Wang, M., Qiao, S., & Lv, Z. (2023). TVS: a trusted verification scheme for office documents based on blockchain. Complex & Intelligent Systems, 9(3), 2865–2877. [CrossRef]
| Feature | ERC-721 | ERC-6150 |
|---|---|---|
| Parent–child token relationship | Not natively supported; requires manual mappings | Natively supported via parentOf() and related functions |
| Multi-level hierarchy | Flat, single-level ownership | Supports tree-like multi-level hierarchies |
| Transferability | Transferable by default; must be overridden for non-transfer | Transferable by default; allows hierarchy-aware transfer restrictions |
| Suitability for document issuance | Feasible with workarounds (e.g., external mappings) | Well-suited to issuer–document hierarchies |
| Customizability for the DVT use case | Requires extensive custom logic for hierarchy | Designed for hierarchical assets; aligns more naturally with the DVT model. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




