Submitted:
04 February 2026
Posted:
05 February 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Materials and Methods
2.1. Research Scope and Sources
2.2. Architectural and Behavioral Mapping
- Human Layer – factors such as awareness, training, policy compliance, and insider risk
- Identity & Access Layer – authentication assurance, trust scores, role management
- Communication & Infrastructure Layer – encryption, QKD, blockchain throughput, hardware security
3. Research Algorithms and Equations
4. Practical Implementation
- security awareness score (0–100);
- phishing click rate, defined as the fraction of simulated phishing tests clicked in the recent period;
- number of failed login attempts in the last 24 hours;
- number of policy violations in the last 90 days (e.g., data-leak prevention events, shadow IT usage);
- a Boolean flag indicating whether the login occurred at an unusual time relative to typical working hours.
- number of independent authentication factors used (1, 2, or 3+);
- level of the strongest factor (1–3), loosely corresponding to NIST AAL1–AAL3;
- recent MFA failure rate (0–1);
- presence of MFA bypass mechanisms (e.g., SMS backup codes or e-mail links);
- age of the session in minutes since the last full authentication.
- negotiated TLS version (TLS 1.3, TLS 1.2, legacy TLS, or none);
- a flag indicating whether a secure, authenticated channel is actually used;
- round-trip network latency in milliseconds;
- packet loss rate;
- a flag indicating whether quantum key distribution (QKD) is enabled;
- when QKD is enabled, a quantum bit error rate (QBER) in the range 0–0.15.
- low awareness (< 40) or high phishing click rate (> 0.15);
- many failed logins (> 5) or frequent recent policy violations (≥ 3);
- single-factor authentication, low-assurance factors, high MFA failure rate (> 0.2), presence of bypass mechanisms, or very old sessions (> 180 minutes);
- lack of TLS or usage of legacy TLS, insecure channel flags, very high latency (> 600 ms), high packet loss (> 0.05);
- The human-layer score increases with higher awareness, lower phishing click rates, fewer failed logins and policy violations, and normal login times. It penalizes excessive login failures and repeated policy infractions, capturing both individual and organisational behaviour in line with [7], [8], [14], [15].
- The MFA-layer score rewards the use of multiple independent factors, higher-assurance factors (e.g., cryptographic authenticators over SMS codes), low MFA failure rates, absence of bypass mechanisms, and short session ages. This is consistent with risk-based MFA recommendations for digital payments [3], [5].
- The communication-layer score combines TLS strength, latency, packet loss, and QKD quality. TLS 1.3 with low latency and low packet loss yields high scores, while legacy or missing TLS and unstable channels reduce the score. When QKD is enabled, QBER is incorporated as an additional signal: very low QBER is treated as strong assurance, whereas high QBER sharply degrades the score, reflecting the security properties of QKD-based systems [2], [6], [10], [12].
- human layer weight: 0.40;
- MFA layer weight: 0.35;
- communication layer weight: 0.25.
- LOW RISK: score ≥ 85;
- MODERATE RISK: 65 ≤ score < 85;
- HIGH RISK: 45 ≤ score < 65;
- CRITICAL RISK: score < 45.
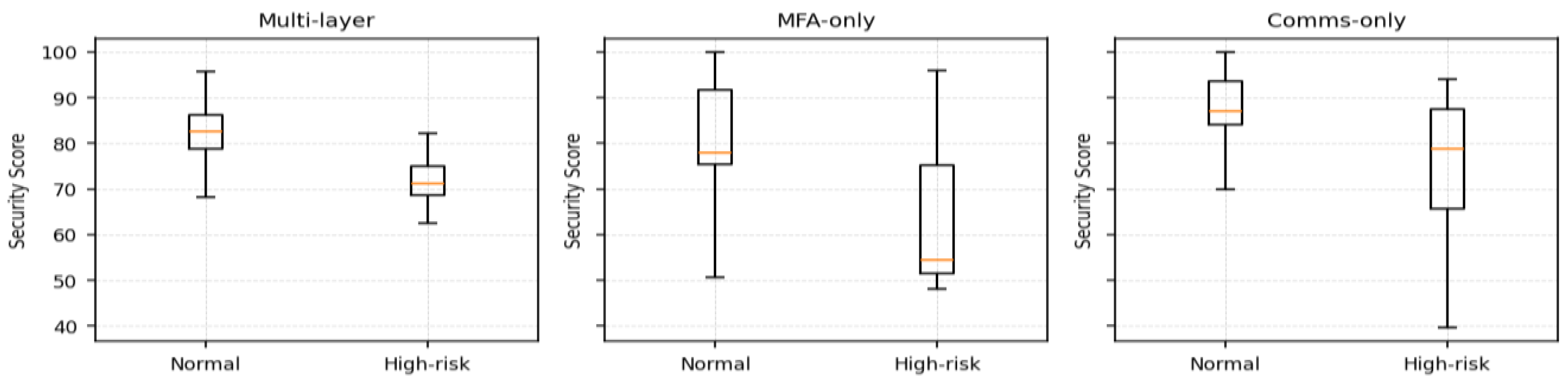
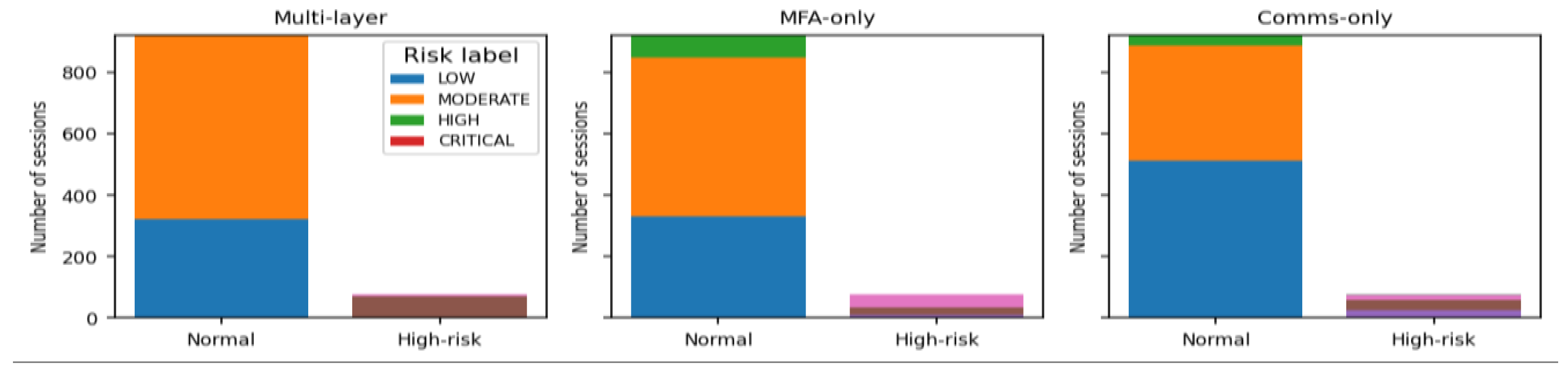
5. Results
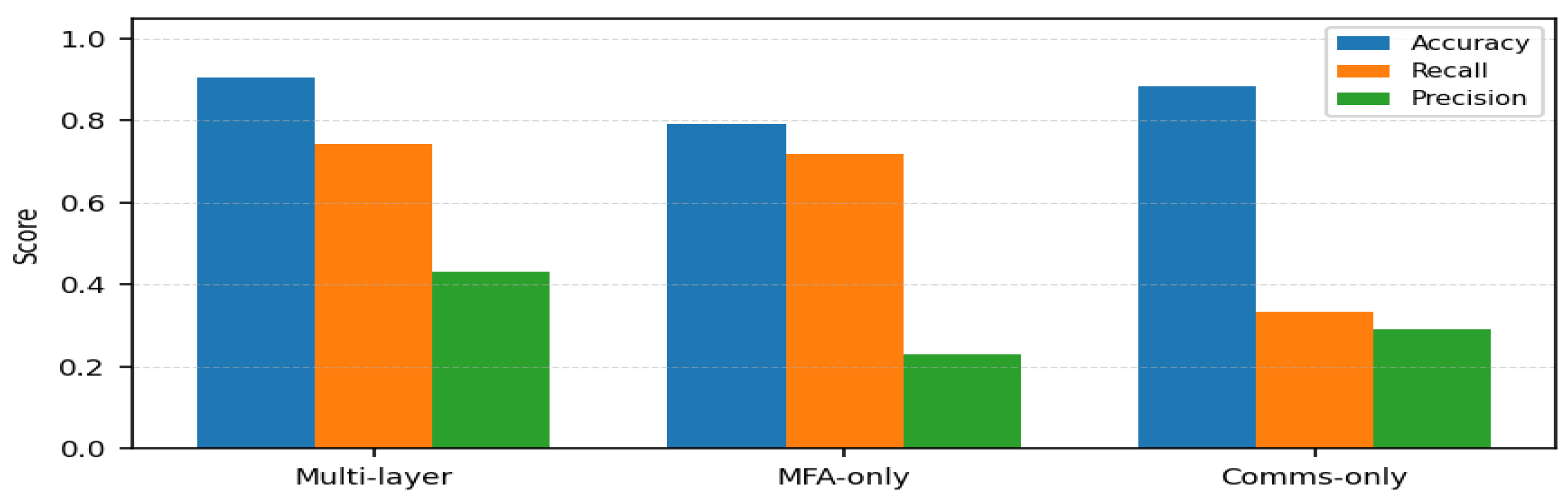
| Detector | TP | FP | FN | TN | Accuracy | Recall | Precision | FPR |
|---|---|---|---|---|---|---|---|---|
| Multi-layer (human + MFA + comms) | 58 | 76 | 20 | 846 | 0.904 | 0.744 | 0.433 | 0.082 |
| MFA-only | 56 | 187 | 22 | 735 | 0.791 | 0.718 | 0.230 | 0.203 |
| Communication-only | 26 | 63 | 52 | 859 | 0.885 | 0.333 | 0.292 | 0.068 |
- 0.919 for the multi-layer Security Score;
- 0.820 for the MFA-only score;
- 0.713 for the communication-only score.
6. Discussion
- better alignment with an explicitly multi-factor ground truth (higher ROC-AUC);
- substantially fewer false positives at a given recall level;
7. Conclusions
References
- Altaibek, M.; et al. A survey of cross-layer security for resource-constrained IoT devices. Appl. Sci. 2025, 15, 9691. [Google Scholar] [CrossRef]
- Sykot, A.; et al. Multi-layered security system: Integrating quantum key distribution with classical cryptography to enhance steganographic security. Alexandria Eng. J. 2025. [Google Scholar] [CrossRef]
- Tran-Truong, P.T.; et al. A systematic review of multi-factor authentication in digital payment systems: NIST standards alignment and industry implementation analysis. J. Syst. Archit. 2025, 162, 103402. [Google Scholar] [CrossRef]
- Elomda, O.; et al. Multi-layer blockchain security model for IoT communication. J. IoT Secur. Res. 2025, 14, 1–12. [Google Scholar] [CrossRef]
- Yeoh, W.; et al. Zero trust cybersecurity: Critical success factors and a maturity assessment framework. Comput. Secur. 2023, 133, 103412. [Google Scholar] [CrossRef]
- Sykot, K.; Rahman, F.; Lee, D. Multi-layered security system integrating QKD with classical cryptography. Int. J. Quantum Commun. 2025, 9, 165–178. [Google Scholar] [CrossRef]
- Annarelli, A.; et al. A multi-layer attack model integrating human factors in delivering cybersecurity. Strategic Leadersh. J. 2023. Available online: https://iris.uniroma1.it/bitstream/11573/1693741/1/Annarelli_A-Multilayer_2023.pdf.
- Panteli, N.; Nthubu, B.R.; Mersinas, K. Being responsible in cybersecurity: A multi-layered perspective. Inf. Syst. Front. 2025. [Google Scholar] [CrossRef]
- Wai, H.; Lee, J. Seamless Industry 4.0 integration: A multilayered cybersecurity framework for resilient SCADA deployments in CPPS. Ind. Cybersecur. Rev. 2023, 22, 1–10. [Google Scholar] [CrossRef]
- Elomda, B.M.; et al. An enhanced multi-layer blockchain security model for improved latency and scalability. Information 2025, 16, 241. [Google Scholar] [CrossRef]
- He, Y.; et al. A survey on zero trust architecture: Challenges and future trends. Wirel. Commun. Mob. Comput. 2022, 6476274. [Google Scholar] [CrossRef]
- Kallapu, B.; et al. Multi-layered security framework combining steganography and DNA coding. Systems 2023, 13, 341. [Google Scholar] [CrossRef]
- Chatterjee, D.; et al. Hardware security in the connected world. WIREs Data Min. Knowl. Discov. 2025, 15, e70034. [Google Scholar] [CrossRef]
- Galadima, I.B.; et al. Multi-layered security model to counter social engineering attacks. Res. Sq. 2024, preprint. [Google Scholar] [CrossRef]
- Spanakis, E.G.; et al. Cyber-attacks and threats for healthcare—A multi-layer threat analysis. In Proceedings of the IEEE EMBS Conference; 2020; pp. 5705–5708. Available online: https://ieeexplore.ieee.org/document/9176690.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




