Submitted:
05 January 2026
Posted:
07 January 2026
You are already at the latest version
Abstract
Keywords:
1. Introduction
1.1. The Tactical Edge Challenge
1.2. The Next-Generation Security Triad and DIL Gap
1.3. Contributions
2. Background and Related Work
2.1. Tactical Edge Sensor Networks
2.2. Next-Generation Security Triad Foundations
2.3. PQC and ZTA in Constrained Environments
2.3.1. CNSA 2.0 vs. Expeditionary Edge Algorithm Selection
2.4. Governance and Behavioral Security Foundations
3. DIL Threat Model
3.1. Threat Environment Characterization
3.2. DIL-Amplified Attack Vectors
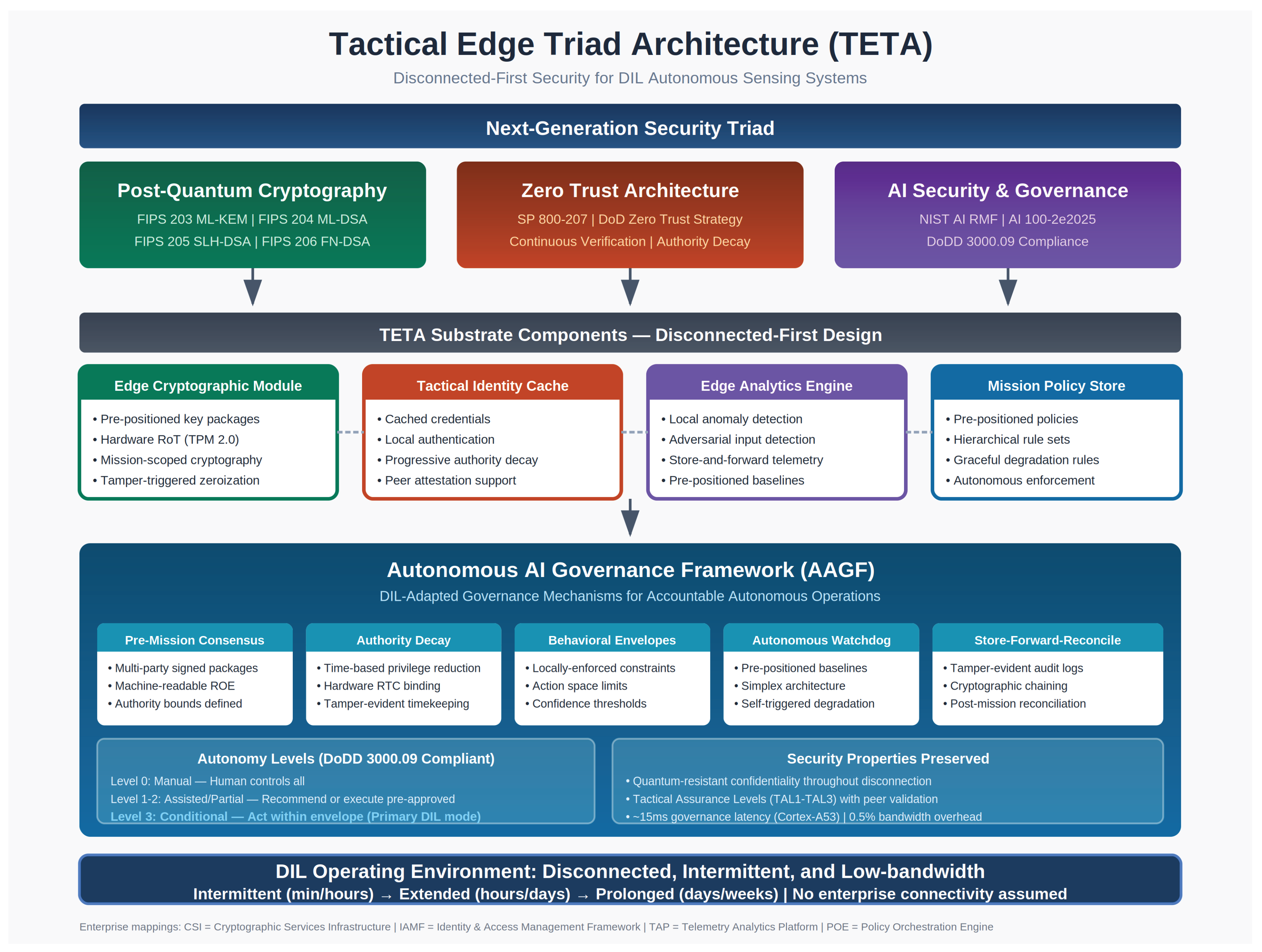
4. Tactical Edge Triad Architecture (TETA)
4.1. Design Principles and Substrate Overview
4.2. Substrate Components
4.3. Autonomous AI Governance Framework (AAGF)
4.3.1. Pre-Mission Consensus and Pre-Authorized Envelopes
4.3.2. Locally-Enforced Behavioral Bounds
4.3.3. Autonomous Watchdog and Self-Triggered Degradation
4.3.4. Store-Forward-Reconcile and Conservative Bias
5. Case Study Scenarios
5.1. Scenario Selection
5.2. Scenario 1: Airborne ISR Platform (UAV Swarm)
5.3. Scenario 2: Dismounted Ground Sensors
5.4. Evaluation Targets
6. Quantitative Analysis
6.1. Quantitative Model Methodology
6.2. Computational Overhead
6.3. Bandwidth, Storage, and Power
6.4. Security Property Preservation
6.5. Worked Example: Tactical Sensor Report
7. Discussion and Conclusion
7.1. Contributions and Significance
7.2. Comparison with Existing Approaches
7.3. Limitations and Future Work
7.4. Conclusion
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Department of Defense. Summary of the Joint All-Domain Command and Control (JADC2) Strategy; DoD: Washington, DC, USA, 2022. [Google Scholar]
- Bronk, J.; Reynolds, N.; Watling, J. The Russian Air War and Ukrainian Requirements for Air Defence; RUSI: London, UK, 2022. [Google Scholar]
- Watling, J.; Reynolds, N. Ukraine at War: Paving the Road from Survival to Victory; RUSI: London, UK, 2022. [Google Scholar]
- Department of Defense. DoD Zero Trust Strategy; DoD CIO: Washington, DC, USA, 2022. [Google Scholar]
- Department of Defense. DTM 25-003: Implementing the DoD Zero Trust Strategy; Washington, DC, USA, 2025.
- Campbell, R.E. Operationalizing the Next-Generation Security Triad: AI Security, PQC, and Zero Trust in Federal Compliance. Preprints 2025, 202512.2298.v1. [Google Scholar]
- Humayed, A.; Lin, J.; Li, K.; Luo, B. Cyber-Physical Systems Security—A Survey. IEEE IoT J. 2017, 4, 1802–1831. [Google Scholar] [CrossRef]
- National Security Agency. Announcing the Commercial National Security Algorithm Suite 2.0; NSA: Fort Meade, MD, USA, 2022. [Google Scholar]
- NIST. Module-Lattice-Based Key-Encapsulation Mechanism Standard; FIPS 203; NIST: Gaithersburg, MD, USA, 2024. [Google Scholar]
- NIST. Module-Lattice-Based Digital Signature Standard; FIPS 204; NIST: Gaithersburg, MD, USA, 2024. [Google Scholar]
- NIST. Stateless Hash-Based Digital Signature Standard; FIPS 205; NIST: Gaithersburg, MD, USA, 2024. [Google Scholar]
- Rose, S.; Borchert, O.; Mitchell, S.; Connelly, S. Zero Trust Architecture; SP 800-207; NIST: Gaithersburg, MD, USA, 2020. [Google Scholar]
- Vassilev, A.; Oprea, A.; Fordyce, A.; Anderson, H. Adversarial Machine Learning; AI 100-2e2025; NIST: Gaithersburg, MD, USA, 2025.
- Tabassi, E. Artificial Intelligence Risk Management Framework (AI RMF 1.0); NIST: Gaithersburg, MD, USA, 2023. [Google Scholar]
- Department of Defense. Zero Trust for Operational Technology; DoD CIO: Washington, DC, USA, 2024. [Google Scholar]
- Department of Defense. DoD Directive 3000.09: Autonomy in Weapon Systems; DoD: Washington, DC, USA, 2023. [Google Scholar]
- NIST. FIPS 206: FN-DSA (Falcon); NIST: Gaithersburg, MD, USA, 2025. [Google Scholar]
- Kannwischer, M.J.; Rijneveld, J.; Schwabe, P.; Stoffelen, K. pqm4: Testing and Benchmarking NIST PQC on ARM Cortex-M4. In Proceedings of the Second NIST PQC Standardization Conference; 2019. [Google Scholar]
- Kannwischer, M.J.; Krausz, M.; Petri, R.; Yang, S.-Y. pqm4: Benchmarking NIST Additional Post-Quantum Signature Schemes. IACR ePrint 2024, 112. [Google Scholar]
- Heinz, D.; Kannwischer, M.J.; Land, G.; et al. First-Order Masked Kyber on ARM Cortex-M4. IACR TCHES 2022, 479–505. [Google Scholar]
- Chan, K.S.; Johnsen, F.T. Cybersecurity in Tactical Edge Networks. IEEE Secur. Priv. 2025, 23, 10–20. [Google Scholar] [CrossRef]
- Prest, T.; Fouque, P.-A.; Hoffstein, J.; et al. FALCON: Fast-Fourier Lattice-based Compact Signatures over NTRU; NIST PQC Round 3 Submission. 2020. [Google Scholar]
- Grassi, P.A.; Garcia, M.E.; Fenton, J.L. Digital Identity Guidelines; SP 800-63B; NIST: Gaithersburg, MD, USA, 2017. [Google Scholar]
- The White House. Removing Barriers to American Leadership in Artificial Intelligence; Executive Order 14179;Washington, DC, USA, 2025.
- Office of Management and Budget. M-22-09: Moving the U.S. Government Toward Zero Trust; OMB: Washington, DC, USA, 2022. [Google Scholar]
- Burleigh, S.; Fall, K.; Birrane, E., III. Bundle Protocol Version 7; RFC 9171; IETF, 2022.
- Moody, D.; Perlner, R.; Regenscheid, A.; et al. Transition to Post-Quantum Cryptography Standards. NIST IR 8547; NIST. 2024. [Google Scholar]
- Cooper, D.; Ferraiolo, H.; Johnson, V.C.; et al. Recommendations for Key-Encapsulation Mechanisms; SP 800-227; NIST, 2025.
- Koontz, B. At the Tactical Edge, Army Wants 58 Zero Trust Capabilities. Federal News Network, 7 March 2025. [Google Scholar]
- Birrane, E., III; McKeever, K. Bundle Protocol Security (BPSec); RFC 9172; IETF, 2022.
- Hu, V.C.; Ferraiolo, D.; Kuhn, R.; et al. Guide to Attribute Based Access Control (ABAC); SP 800-162; NIST, 2014.
- Pang, R.; Caceres, R.; Burrows, M.; et al. Zanzibar: Google’s Consistent, Global Authorization System. In Proceedings of USENIX ATC, 2019; 33–46. [Google Scholar]
- Birgisson, A.; Politz, J.G.; Erlingsson, Ú.; et al. Macaroons: Cookies with Contextual Caveats. In Proceedings of NDSS, 2014. [Google Scholar]
- McGraw, R. Risk-Adaptable Access Control (RAdAC). In Proceedings of NIST Privilege Management Workshop, 2009. [Google Scholar]
- Kandala, S.; Sandhu, R.; Bhamidipati, V. An Attribute Based Framework for Risk-Adaptive Access Control Models. In Proceedings of ARES, 2011; 236–241. [Google Scholar]
- Seto, D.; Krogh, B.; Sha, L.; Chutinan, A. The Simplex Architecture for Safe Online Control System Upgrades. In Proceedings of ACC, 1998; 3504–3508. [Google Scholar]
- Mehmood, U.; Sheikhi, S.; Bak, S.; et al. The Black-Box Simplex Architecture for Runtime Assurance. In Proceedings of NFM, 2022; 231–250. [Google Scholar]
- Mehmood, U.; Stoller, S.D.; Grosu, R.; et al. A Distributed Simplex Architecture for Multi-Agent Systems. In Proceedings of SETTA, 2021; 239–257. [Google Scholar]
- Ross, R.; Pillitteri, V.; Graubart, R.; et al. Developing Cyber-Resilient Systems; SP 800-160 Vol. 2 Rev. 1; NIST, 2021.
- Committee on National Security Systems. National Information Assurance (IA) Glossary; CNSSI No. 4009; CNSS, 2015.
- Lin, J.; Chen, W.-M.; Lin, Y.; et al. MCUNet: Tiny Deep Learning on IoT Devices. In Proceedings of NeurIPS, 2020. [Google Scholar]
- Sudharsan, B.; Salerno, S.; Nguyen, D.-D.; et al. TinyML Benchmark. In Proceedings of IEEE WF-IoT, 2021. [Google Scholar]
- Housley, R.; Regenscheid, A.; Celi, C. Recommendations for Stateful Hash-Based Signature Schemes; SP 800-208; NIST, 2020.
- The White House. Initial Rescissions of Harmful Executive Orders; Executive Order 14148; Washington, DC, USA, 2025.
- Office of Management and Budget. M-25-21: Accelerating Federal Use of AI; OMB: Washington, DC, USA, 2025. [Google Scholar]
- ASTM International. F3269-17: Standard Practice for Methods to Safely Bound Flight Behavior of UAS. ASTM. 2017. [Google Scholar]
| Triad Element | Enterprise Assumption | DIL Reality |
|---|---|---|
| PQC | Bandwidth for larger keys/signatures | Constrained tactical links (kbps) |
| ZTA | Continuous verification via enterprise IdP | No connectivity for authentication |
| AI Security | Cloud-based monitoring and governance | No cloud access for validation |
| Governance | Real-time multi-party consensus | Single isolated platform |
| Observability | Real-time SIEM integration | No telemetry path; delayed visibility |
| Characteristic | Enterprise | Tactical Edge |
|---|---|---|
| Connectivity | Always-on, high bandwidth | DIL: hours to weeks disconnected |
| Power | Unlimited (grid) | Battery/solar constrained |
| Compute | Cloud-scale resources | Embedded/microcontroller class |
| Physical Security | Data center controls | Contested environment, capture risk |
| Failure Consequence | Business disruption | Mission failure, casualties |
| System Type | Support/Prefer CNSA 2.0 | Exclusive CNSA 2.0 |
|---|---|---|
| Software/firmware signing | 2025 | 2030 |
| Web browsers/servers, cloud services | 2025 | 2033 |
| Traditional networking equipment | 2026 | 2030 |
| Operating systems | 2027 | 2033 |
| Niche equipment (constrained devices, large PKI) | 2030 | 2033 |
| Custom applications, legacy equipment | — | 2033 |
| Mechanism | Function | Connectivity Assumption |
|---|---|---|
| Behavioral envelopes | Constrain actions | Cloud monitoring validates compliance |
| Watchdog models | Monitor anomalies | Report to SOC for human review |
| Autonomy-downgrade | Reduce AI authority | Human/external triggers reduction |
| Consensus governance | Multi-party approval | Real-time consensus nodes reachable |
| Observability | Detection/response | Real-time telemetry to SIEM |
| DIL Level | Disconnection | Bandwidth | Example Platform |
|---|---|---|---|
| Intermittent | Minutes to hours | kbps burst | UAV swarm |
| Extended | Hours to days | Sporadic kbps | Maritime patrol |
| Prolonged | Days to weeks | bps opportunistic | Ground sensor |
| Attack Vector | DIL Amplification | Triad Response |
|---|---|---|
| HNDL collection | Tactical traffic high-value intelligence | PQC protection; short-lived session keys |
| Credential theft | Extended validity; no real-time detection | Time-bounded credentials; authority decay |
| Sensor spoofing | No cloud correlation for detection | Local anomaly detection; peer validation |
| AI manipulation | No remote model validation | Pre-positioned baselines; local watchdog |
| Model poisoning | Compromised models undetected | Pre-deployment validation; integrity checks |
| Physical capture | Governance parameters exposed | Platform-specific packages; tamper response |
| Enterprise | TETA Component | Key Adaptations |
|---|---|---|
| CSI | Edge Cryptographic Module | Pre-positioned keys; lightweight PQC; hardware RoT |
| IAMF | Tactical Identity Cache | Cached credentials; local auth; authority decay |
| TAP | Edge Analytics Engine | Local anomaly detection; store-and-forward |
| POE | Mission Policy Store | Pre-positioned policies; autonomous enforcement |
| (New) | AI Governance Framework | DIL-adapted governance mechanisms |
| Platform Type | KEM | Signature | Rationale |
|---|---|---|---|
| UAV (moderate) | ML-KEM-768 | ML-DSA-65 | Balanced security/perf |
| Ground sensor | ML-KEM-512 | SLH-DSA-128s | Compact keys; PQC for high-value only |
| Maritime | ML-KEM-512 | FN-DSA (draft FIPS 206) | Compact signatures for SATCOM |
| Vehicle (high) | ML-KEM-1024 | ML-DSA-87 | Maximum security margin |
| Mechanism | Enterprise Approach | DIL Adaptation |
|---|---|---|
| Consensus | Real-time multi-party agreement | Pre-mission consensus via signed packages |
| Multi-party approval | Approval authorities reachable | Pre-authorized decision envelopes |
| Behavioral envelopes | Cloud monitoring | Locally-enforced hard constraints |
| Watchdog models | Report to SOC | Autonomous watchdog with local response |
| Autonomy-downgrade | Human/external triggers | Self-triggered degradation |
| Observability | Real-time SIEM | Store-forward-reconcile |
| Authority Level | Time Window | Permitted Actions | Prohibited Actions |
|---|---|---|---|
| 0–24h | All pre-authorized actions | None within envelope | |
| 24–48h | Sensing, classification, reporting | Engagement recommendations | |
| 48–72h | Passive sensing, status reporting | Active classification, targeting | |
| >72h | Self-preservation, beacon only | All mission actions |
| Attack Vector | Threat Description | Mitigation |
|---|---|---|
| Clock rollback | The adversary manipulates the local clock to restore expired authority | Hardware RTC with tamper detection; monotonic counters in TPM; cross-check against peer clocks |
| Time manipulation | Captured device clock advanced/rewound | Signed timestamps from pre-mission epoch; GPS time when available; clock drift bounds |
| Credential replay | Previously-valid credentials reused after refresh | Nonce binding; epoch counters in credential structure; hash chain to last known state |
| Peer collusion | Colluding peers falsely attest to continued validity | Quorum requirements (k-of-n); behavioral anomaly detection; audit trail |
| Decision Category | Authority Required | DIL Authorization |
|---|---|---|
| Routine sensing | Autonomous | Fully pre-authorized |
| Target classification | Supervised | Pre-authorized within the envelope |
| Engagement recommendation | Human approval | Conditional pre-authorization |
| Engagement execution | Command approval | Time-limited or wait |
| Policy modification | Multi-party consensus | Never authorized in DIL |
| Dimension | Description | Example Constraint |
|---|---|---|
| Action space | What actions are possible | Classification permitted; engagement prohibited |
| Rate limiting | Action frequency limits | Max 3 targeting recommendations/hour |
| Confidence floor | Minimum certainty threshold | 95% classification confidence required |
| Consequence bounds | Expected impact limits | Collateral estimate below threshold |
| Geographic bounds | Spatial restrictions | Within the defined AO only |
| Temporal bounds | Time window restrictions | Mission window only |
| Watchdog | Detection Target | Autonomous Response |
|---|---|---|
| Behavioral | Action pattern deviation | Autonomy reduction |
| Integrity | Model tampering indicators | Safe mode entry |
| Input | Adversarial/anomalous inputs | Reject input; alert |
| Output | Unreasonable decisions | Flag for review; reduce confidence |
| Level | Name | AI Authority | DIL Applicability |
|---|---|---|---|
| 0 | Manual | None—human controls all | Emergency fallback |
| 1 | Assisted | Recommend only | Human co-located |
| 2 | Partial | Execute pre-approved routine | Intermittent connectivity |
| 3 | Conditional | Act within envelope | Primary DIL mode |
| 4 | Supervised | Full authority, monitored | High-trust scenarios |
| 5 | Full | Unrestricted | NEVER AUTHORIZED |
| Characteristic | Airborne ISR (UAV) | Ground Sensor |
|---|---|---|
| DIL Severity | Intermittent (min/hour) | Prolonged (days-weeks) |
| Mission Duration | 8–12 hours | 30 days |
| Bandwidth | 256 kbps tactical link | bps opportunistic |
| Compute Class | Embedded GPU | Microcontroller (Cortex-M4) |
| AI Complexity | Neural network classification | Threshold detection only |
| Maximum Autonomy | Level 3–4 | Level 2 |
| Watchdog Approach | Peer-based swarm consensus | Self-diagnostic only |
| Governance | Collective (quorum required) | Individual (limited scope) |
| Metric | Airborne ISR | Ground Sensor |
|---|---|---|
| Swarm coordination / Detection accuracy | 100% | >90% at day 30 |
| Adversarial input detection | >90% | N/A (no ML) |
| Governance compliance | 100% | 100% |
| Security power budget | N/A | <10% |
| Tamper detection | N/A | >99% |
| Authority handoff / Zeroization | 100% | 100% |
| Parameter | Value | Source Type | Derivation/Assumption |
|---|---|---|---|
| ML-KEM-768 encaps | 1.4M cycles | Measured | pqm4 opt implementation [18] |
| ML-DSA-65 sign | 4.0M cycles | Measured | pqm4 opt implementation [18] |
| ML-DSA-65 verify | 1.5M cycles | Measured | pqm4 opt implementation [18] |
| Envelope check | 1–5 ms | Estimated | Policy engine: ~100 rules × 10–50 s/rule |
| Watchdog inference | 10–50 ms | Estimated | 10K-param NN; TinyML benchmarks [41,42] |
| Link rate | 9.6 kbps | Assumed | Representative HF radio data mode |
| Cortex-M4 power | 165 mW active | Measured | STM32F4 datasheet @ 168 MHz |
| Operation | Cortex-M4 | Cortex-A53 | Source |
|---|---|---|---|
| ML-KEM-768 encapsulation | 15–25 ms | 2–4 ms | pqm4 cycles |
| ML-DSA-65 signature | 40–70 ms | 5–10 ms | pqm4 cycles |
| ML-DSA-65 verification | 15–25 ms | 2–4 ms | pqm4 cycles |
| Envelope check (per decision) | 5 ms | 1 ms | Estimate |
| Watchdog inference cycle | 50 ms | 10 ms | Estimate |
| Autonomy evaluation | 2 ms | 0.5 ms | Estimate |
| Audit log entry | 5 ms | 1 ms | Estimate |
| Total governance/decision | ~65 ms | ~15 ms | Sum (estimate) |
| Resource | Value | Assessment |
|---|---|---|
| Bandwidth overhead (9.6 kbps) | 0.5% increase for PQC | Acceptable |
| Session establishment | 2.4–7.7 KB per handshake | Infrequent |
| Pre-positioned material (72h) | ~370 KB/platform | Accommodated |
| Runtime storage (per 24h) | ~1.8 MB | Acceptable |
| Security power (Cortex-M4) | ~3.0 J/day (~0.3%) | Negligible |
| Disconnection | Without Peer Validation | With Peer Validation |
|---|---|---|
| 0–24 hours | TAL3 (high) | TAL3 (high) |
| 24–48 hours | TAL2 (moderate) | TAL3 (high) |
| 48–72 hours | TAL2 (moderate) | TAL2 (moderate) |
| >72 hours | TAL1 (basic) | TAL2 (moderate) |
| Field | Legacy (bytes) | TETA (bytes) | Notes |
|---|---|---|---|
| Header (msg type, seq, timestamp) | 12 | 12 | Identical |
| Sensor ID | 8 | 8 | Platform identifier |
| Location (MGRS + alt) | 15 | 15 | 10-digit MGRS + 2-byte altitude |
| Classification payload | 24 | 24 | Class ID, confidence, hash |
| Governance envelope header | — | 16 | Version, epoch, authority |
| Action authorization bitmap | — | 4 | Permitted actions |
| Decay schedule reference | — | 8 | Schedule ID + decay tier |
| Envelope constraints hash | — | 32 | SHA-256 integrity |
| Signature (ECDSA / ML-DSA-65) | 64 | 3,309 | Quantum-resistant overhead |
| Total message size | 123 | 3,428 | 27.9× increase |
| Framework | Triad Coverage | DIL Support | Governance |
|---|---|---|---|
| NIST SP 800-207 | ZTA only | Partial | Limited |
| CNSA 2.0 | PQC only | Guidance only | None |
| NIST AI RMF 1.0 | AI only | Not addressed | Framework |
| ZT for OT | ZTA + OT | Degraded only | Limited |
| TETA-AAGF | Full Triad | Native DIL | Comprehensive |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




