Submitted:
01 December 2025
Posted:
24 December 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Background: Edge-Swarm Computing and the Information Sharing
2.1. From Cloud to Edge-Swarm Computing
2.2. Decentralized Technology Components for Enhancing Information Sharing and Security
4. Related Works Studies, and Scientific Contributions
4.1. Related Studies
4.2. Comparative Analysis and Positioning
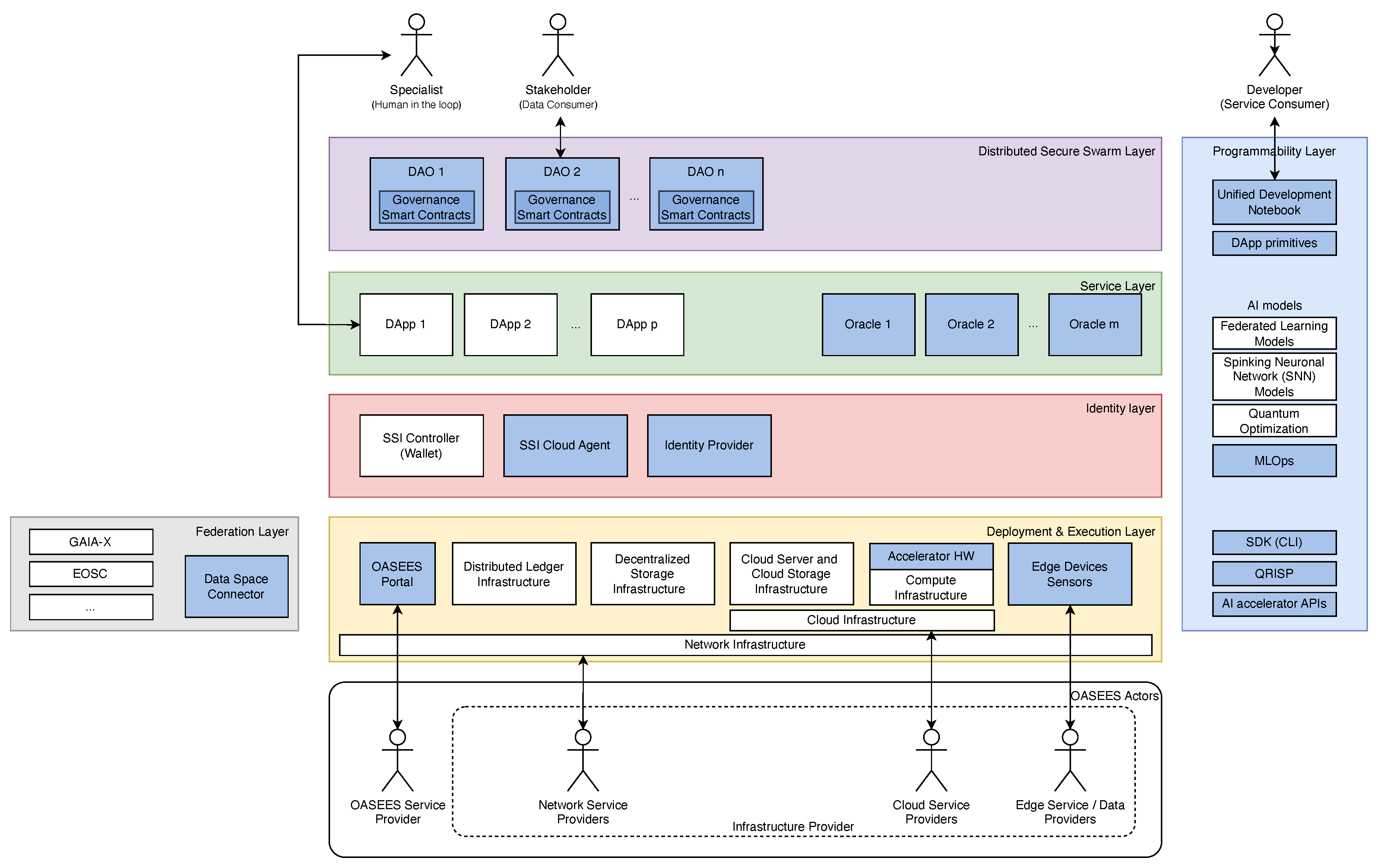
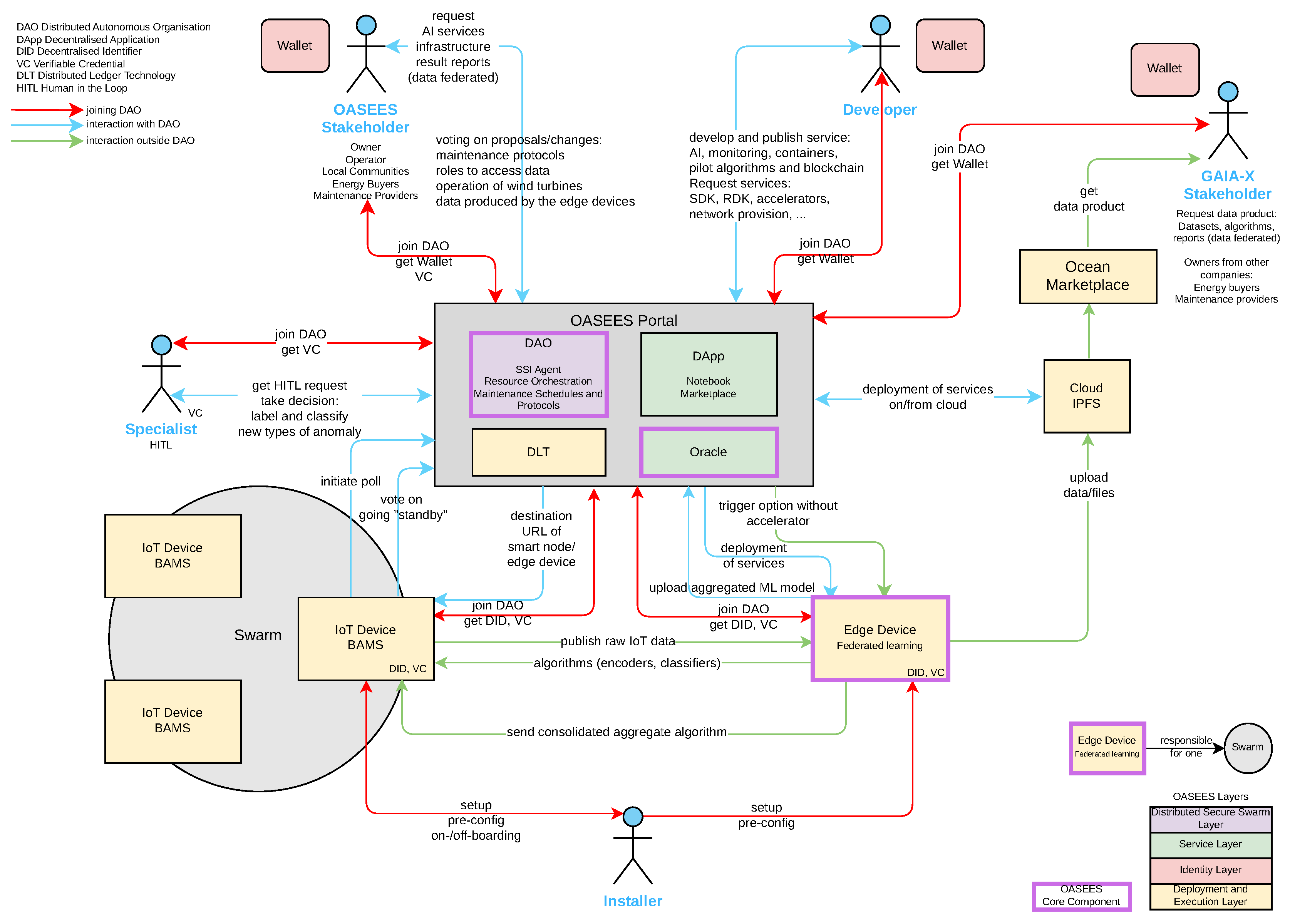
5. OASEES: The DAO as a Service for Decentralized Edge-Cloud Use Cases
5.1. OASEES High-Level Architecture
5.2. Actors
6. Leveraging DAOs and DApp for Secure Data Sharing and Availability
- UC Energy Grid: Support of optimal operation of the electricity grid via coordinated recharging of fleets of electric vehicles
- UC Structural Safety: Structural safety assessment of buildings and critical infrastructure
- UC Windmill Maintenance: Predictive maintenance of windmills
- UC Antenna Inspection: Drone-based hight mast inspection of 5G antennas
- UC Smart Manufacturing: Collaborative robotic powered smart manufacturing
- UC Parkinson: Analysis of voice, articulation, and fluency disorders in Parkinson’s Disease
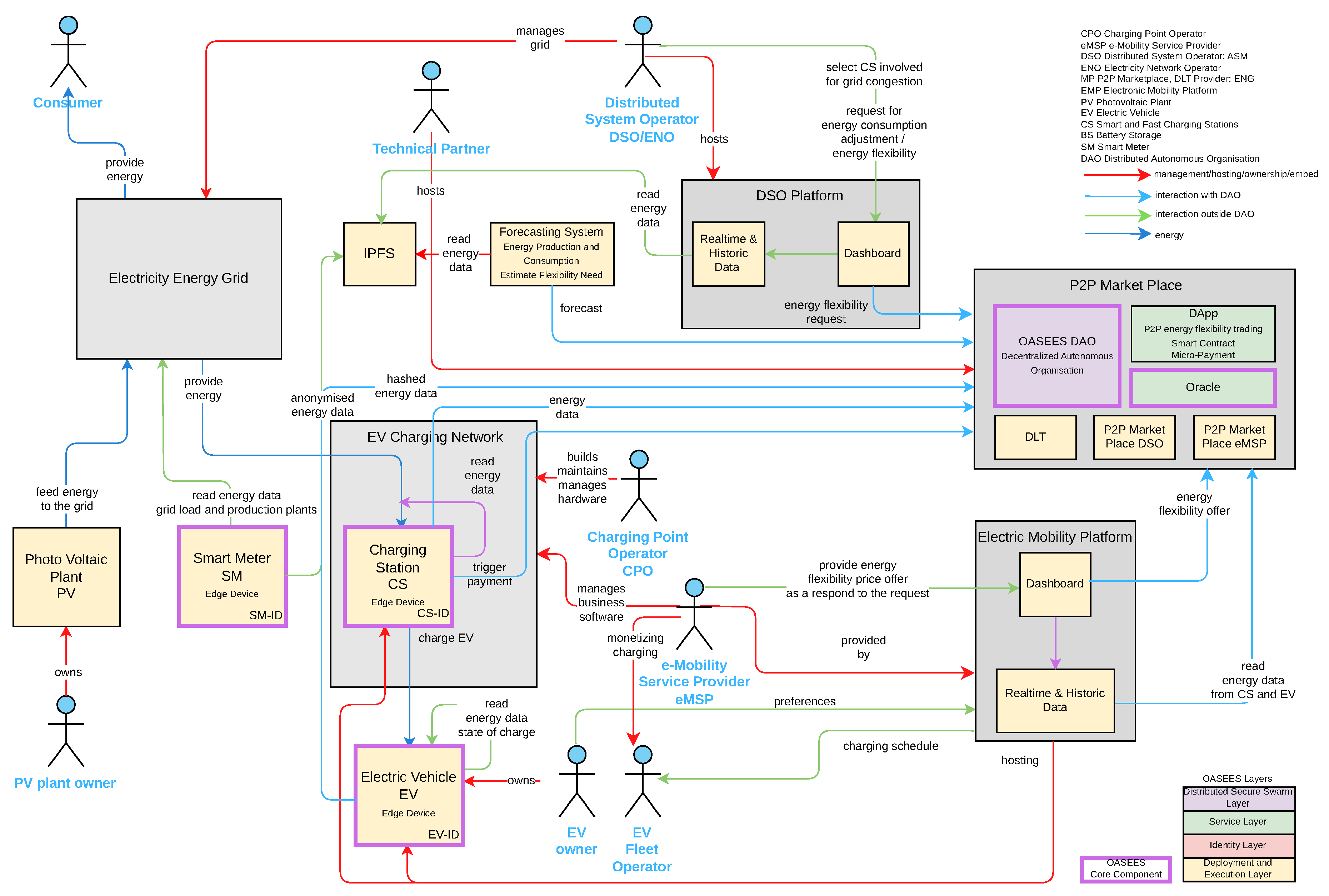
6.1. UC Energy Grid: Support of Optimal Operation of Electricity Grid via Coordinated Recharging of Fleets of Electric Vehicles
6.1.1. DAO Proposals and Activities
-
Market and pricing regulation:
- –
- Proposals to set or update electricity prices offered by the DSO.
- –
- Proposals to determine the CPO selling prices, including specification of payment timing and conditional settlement rules.
- –
- Proposals to automatically adopt the lowest available selling price for efficiency and fairness.
-
Infrastructure management:
- –
- Onboarding of new edge devices (e.g., Smart Meters, Charging Station (CS) units), validated by the relevant authority.
- –
- Removal of malfunctioning or compromised edge devices.
- –
- Addition or removal of organizations participating in the network.
-
Incentive and economic models:
- –
- Proposals to define or update incentive mechanisms for participating members, executed through a treasury smart contract.
- –
- Proposals to initiate micro-payments between stakeholders to support dynamic energy exchanges.
-
Data governance and access control:
- –
- Proposals for data-sharing rules, specifying update, removal, or addition of data governance policies.
- –
- Proposals for access control and data management, including specification of which datasets (e.g., smart meter readings, Electric Vehicle (EV) telemetry, charging schedules) can be accessed by which actor.
6.1.2. Interaction Schema
- Data collection and storage: Smart Meters and CS units provide real-time consumption and pricing data, transmitted via ORACLE services and stored in the decentralized storage (IPFS). EVs also contribute usage and charging demand data, which are hashed on-chain for auditability.
-
Data sharing and notifications:
- –
- eMSPs notify the DSO of business activity changes.
- –
- The DSO provides and requests data from the CPO, stored in IPFS for later use in scheduling and forecasting.
- –
- The EV drivers are informed of updated charging options and schedules.
- Forecasting and decision-making: The DSO feeds forecasted production and consumption data into the DAO, which becomes accessible to DApps for demand–supply balancing. Proposals for new pricing models are triggered, disseminated to stakeholders, and voted upon.
- Voting and consensus: DAO members vote on submitted proposals (e.g., pricing, onboarding devices, data access rules). Once consensus is achieved, the proposal is executed through its associated smart contract.
- Execution and settlement: Actions such as micro-payments are performed automatically via the treasury smart contract, ensuring immediate settlement of economic transactions according to DAO-approved rules.
6.1.3. HITL Interaction and Incentives
6.1.4. Swarm Intelligence Perspective
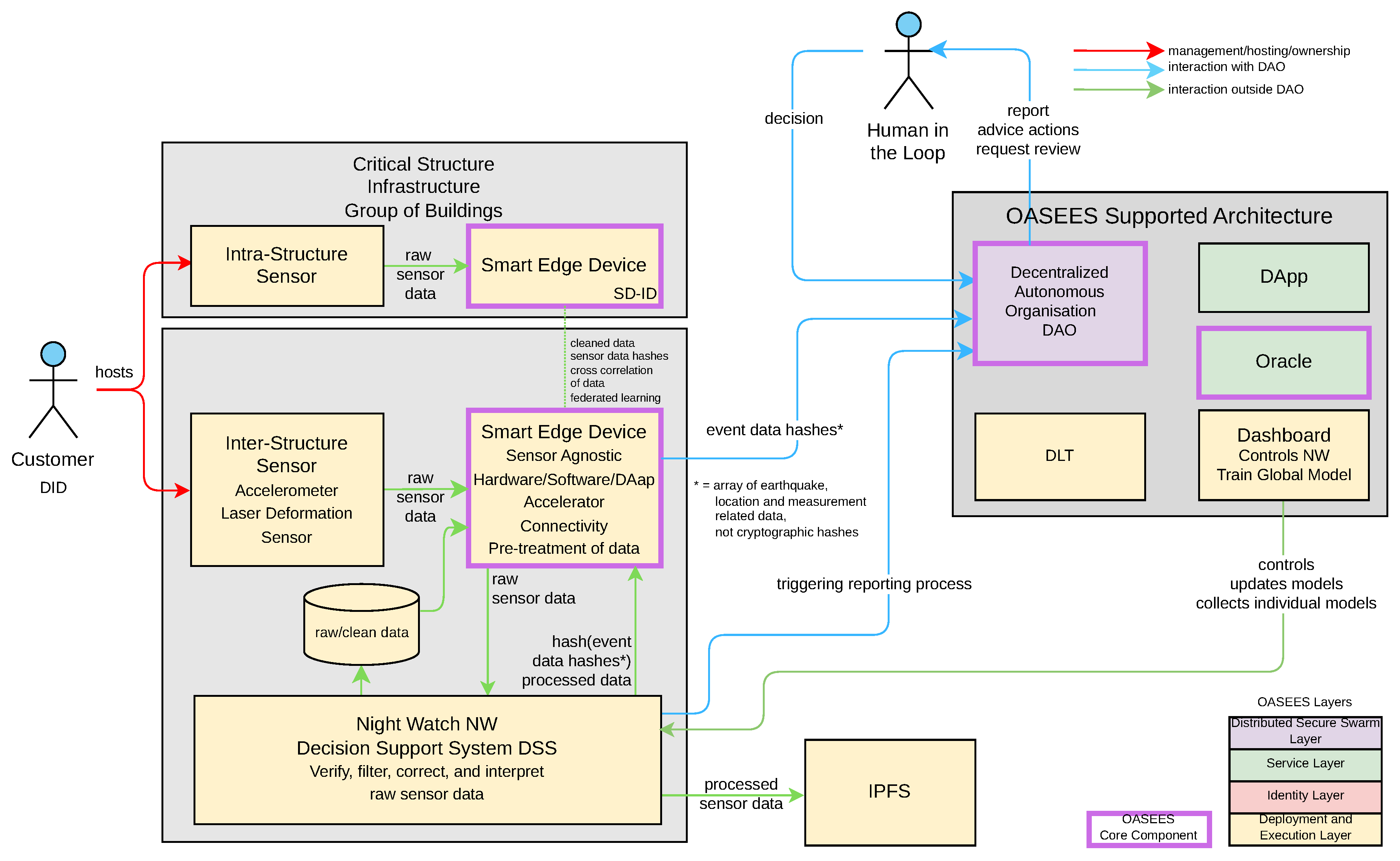
6.2. UC Structural Safety: Structural Safety Assessment of Buildings and Critical Infrastructure
6.2.1. DAO Activities and Proposals
-
HITL Proposals:
- –
- Register or update decision algorithms for safety measurement (NW configuration).
- –
- Verify or approve changes to NW-DSS algorithms.
- –
- Onboard or remove swarm edge devices.
-
DApp/Smart Contract Proposals:
- –
- Request access to data streams or stored features.
- –
- Enable DApp activities such as event-triggered reporting and notifications.
- –
- Communicate with edge devices to trigger specific swarm activities.
6.2.2. Interaction Schema
- –
- Smart edge devices authenticate sensors, filter and cross-correlate raw data, store processed data in IPFS, and commit hashes to the DAO.
- –
- The DAO manages proposals for algorithm updates, device onboarding, and reporting triggers.
- –
- The HITL evaluates DAO-generated reports, validates classifications, and proposes reconfigurations.
- –
- External agencies access DAO/DApp outputs for emergency interventions and reporting.
6.2.3. HITL Interaction and Incentives
6.2.4. Swarm Intelligence Perspective
6.3. UC Windmill Maintenance: Predictive Maintenance of Windmills
6.3.1. DAO Activities and Proposals
- DAO joining members: Proposal for allowing new stakeholders (e.g., maintenance operators, specialists) to join the DAO.
- New maintenance protocol: Proposal for collective definition and approval of maintenance procedures based on acoustic fault detection.
- DAO data-access voting: Proposal for granting or denying developer and researcher access to datasets generated by IoT and edge devices.
- New model voting: Proposal for evaluating and adopting new anomaly-detection algorithms for wind turbine monitoring.
- Proposal: Standby of idle assets: Temporarily disabling devices such as turbines not detected by the monitoring system.
6.3.2. Interaction Scheme
- Authentication: All stakeholders and devices are authenticated through the OASEES DID-based identity layer. IoT and edge devices must be verified, configured, and installed prior to operation.
- IoT Devices: Acoustic sensors continuously sense data from turbine blades, transmitting signals to edge devices.
- Edge Devices: Edge devices identify datasets, perform preliminary fault analysis, and store data hashes on the blockchain. Anomalies or predicted failures trigger notifications to DAO and maintenance operators.
- DAO and HITL Specialists: HITL specialists initiate DAO membership proposals, propose maintenance protocols, and oversee the validation of new models. DAO members vote on maintenance protocols, data access, and algorithmic updates.
- Data Governance: Developers requesting access to datasets are subject to DAO voting. Notifications are distributed to HITL specialists for oversight.
- Model Governance: Developers and HITL specialists propose new models for acoustic fault detection. Approved models are disseminated through the DApp to maintenance operators for integration into workflows.
- Smart Contracts/DApp: These ensure secure data hashing, record DAO decisions, and automate the distribution of maintenance protocols, algorithmic instructions, and off-chain guidance.
- Maintenance Operators: Receive protocol updates or model adoption instructions, enabling real-time adjustment of inspection and maintenance activities.
6.3.3. HITL Interaction and Incentives
6.3.4. Swarm Intelligence Perspective
6.4. Mapping Scientific Contributions to Results
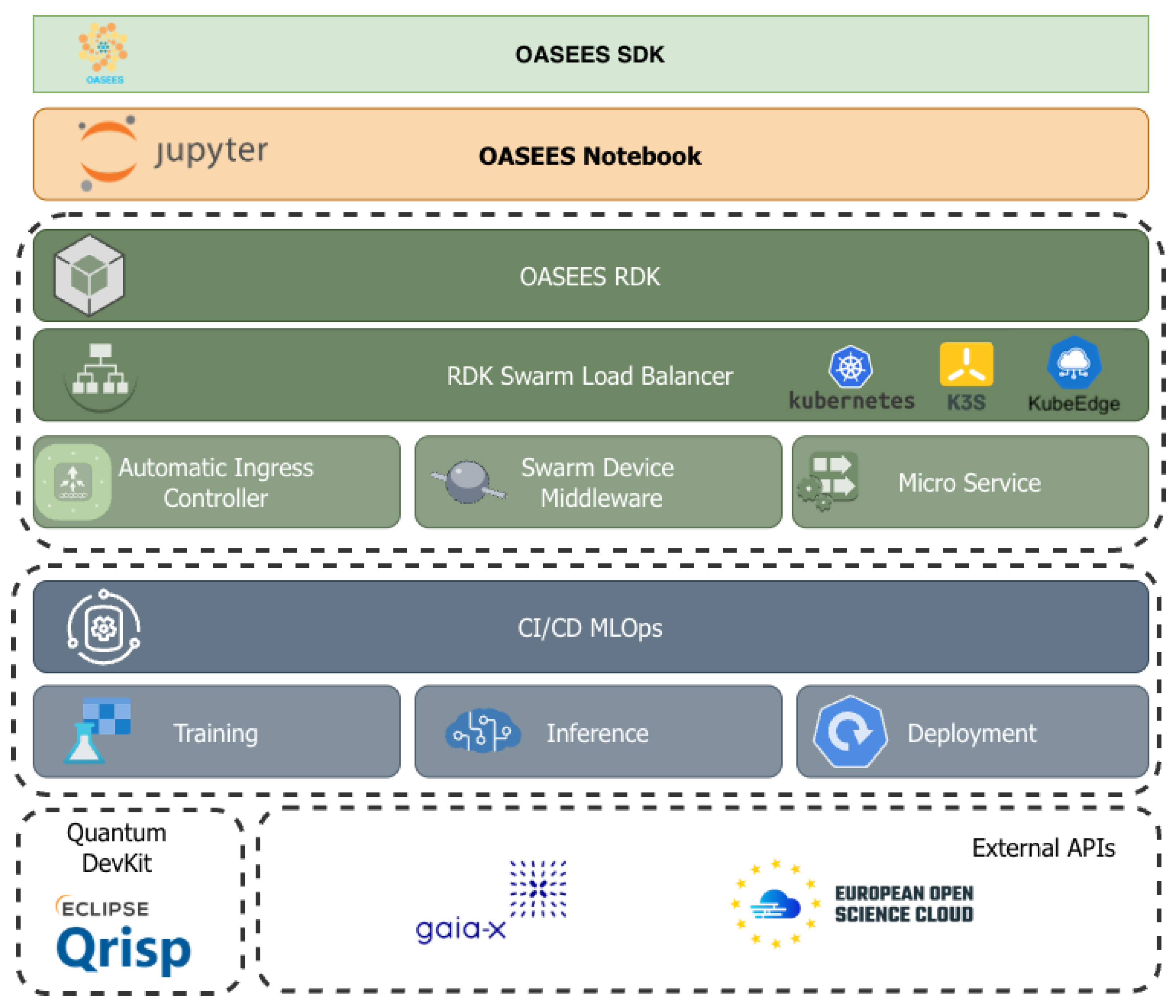
7. OASEES Platform Implementation
- –
- Init-cluster (CLI) on the master installs all K3s components.
- –
- Register-cluster (internal) records the K3s master in the OASEES marketplace/DAO.
- –
- Join-cluster (CLI) on each edge device installs K3s and joins the cluster.
- –
- Register-new-nodes (CLI and internal) detects unregistered workers and registers them.
- –
- After all workers register, the cluster is DAO-registered and visible in the Portal.
7.1. Security Analysis and Threat Mitigation
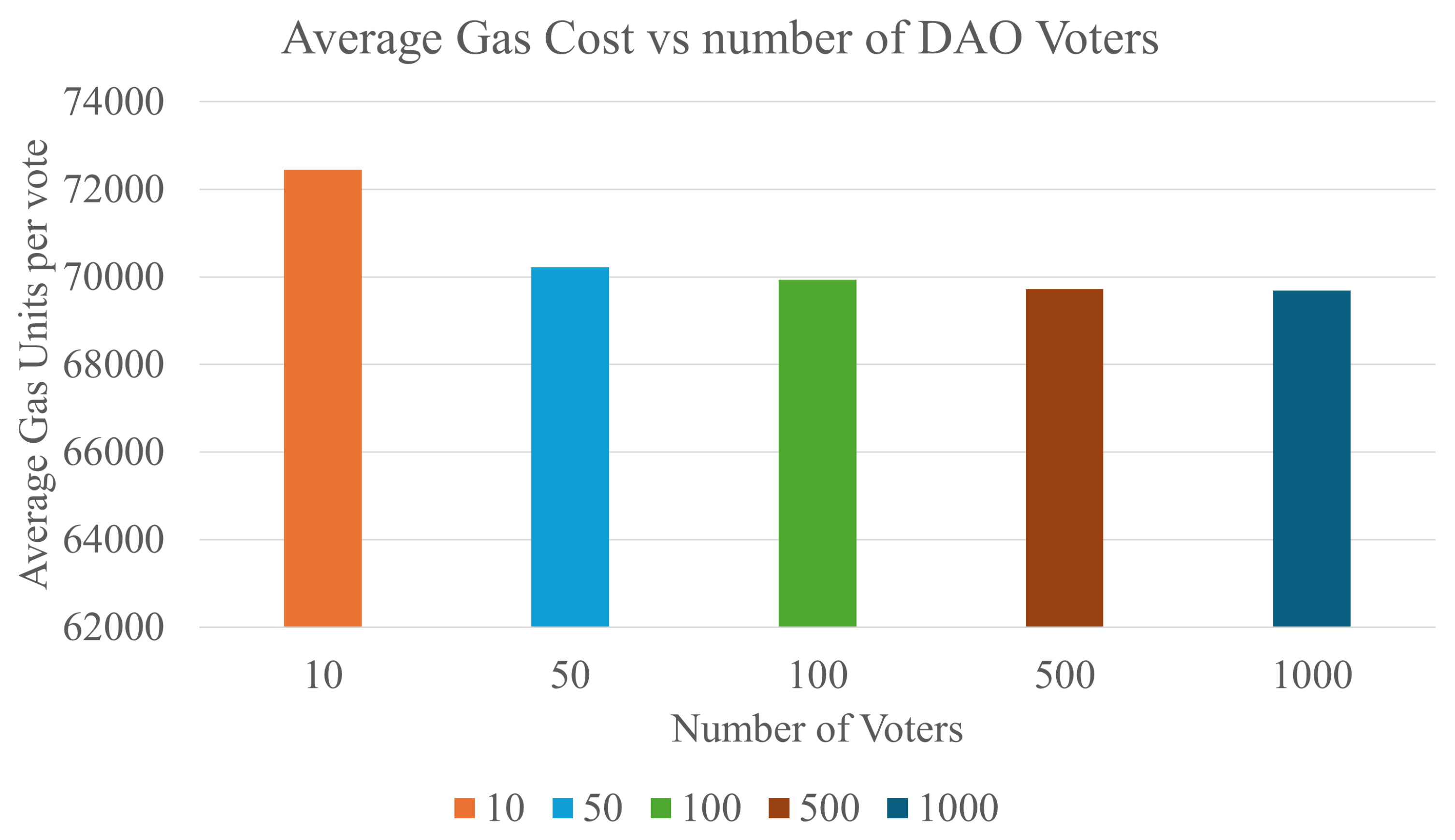
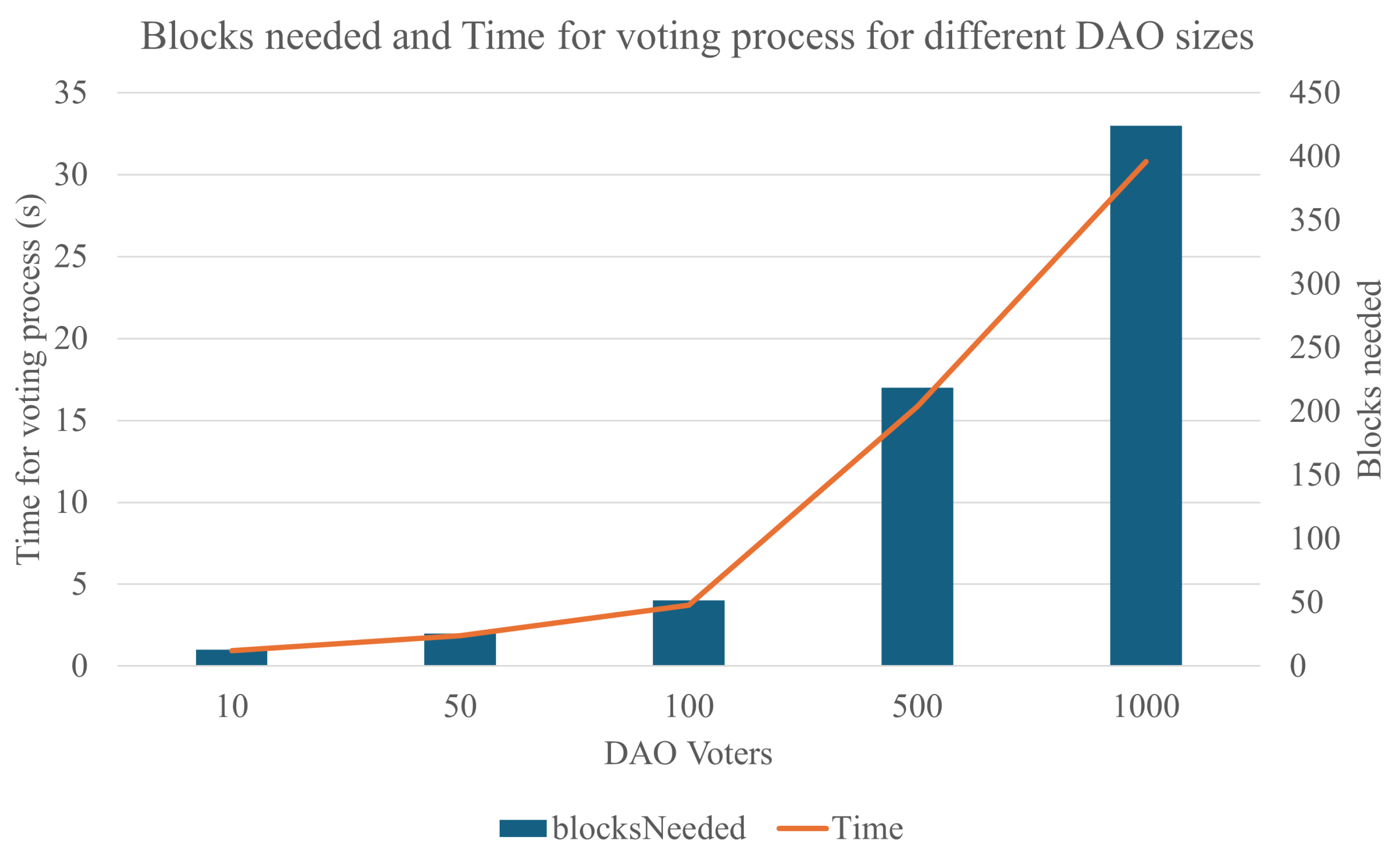
7.2. Experimental Evaluation of Smart Contract Performance
7.2.1. Evaluation of Gas Cost, Block Number and Time
7.2.2. Evaluation of Latency and System Response Time
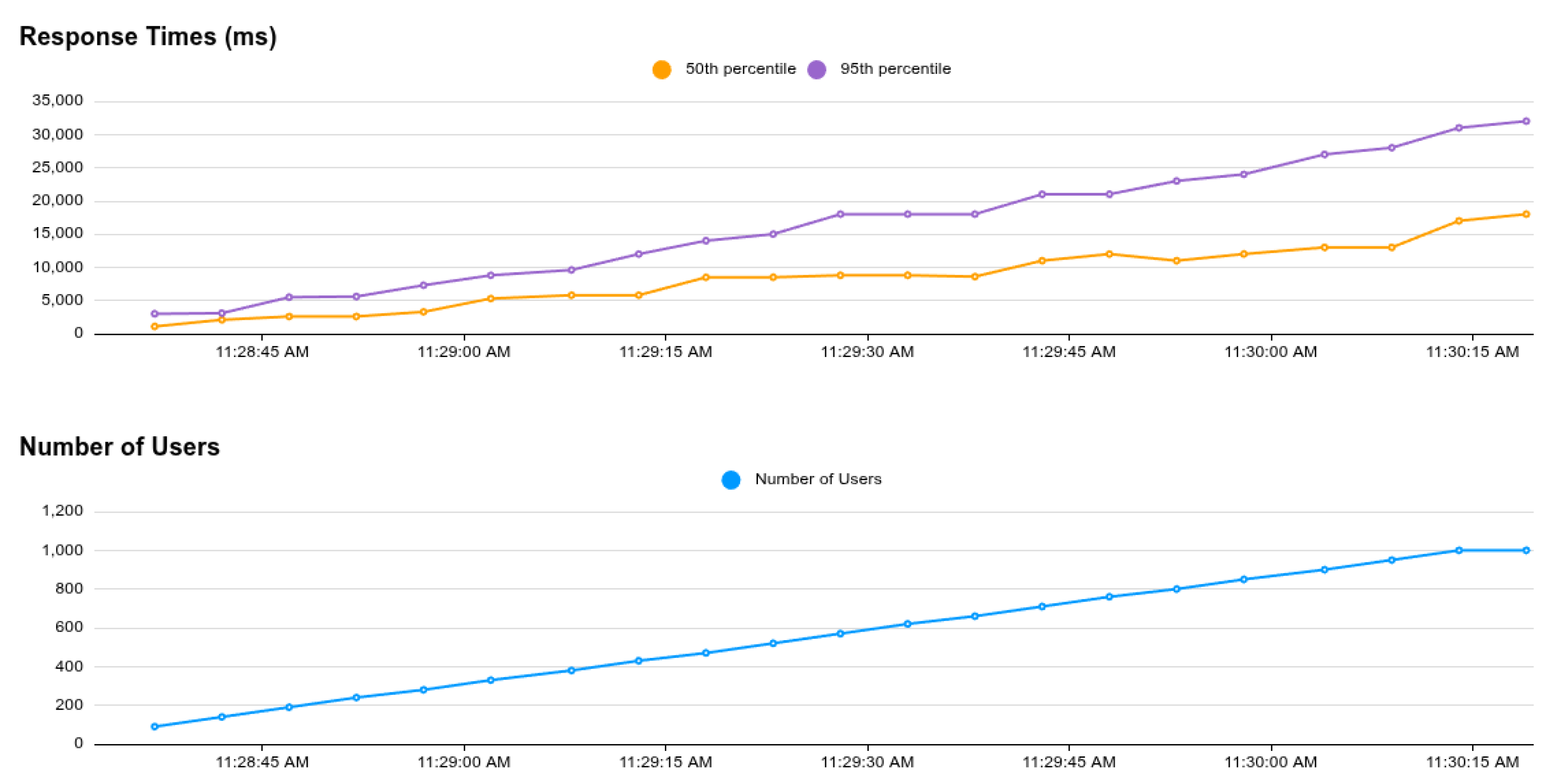
7.2.3. Evaluation of UC-Focused Scalability Measurements
8. Evaluation and Discussions
8.1. Failure and Adversarial Scenario Generation
8.2. Scale and Latency Considerations
8.3. The DAPP Impact on Swarm-Based Use Cases
8.4. Evaluation Matrix: Centralized vs Decentralized
8.5. Blockchain-Based Trust and Security Implications
8.6. OASEES Approach Results
8.7. Blockchain-Based Limitations for Swarm Computing
9. Conclusions and Future Works
9.1. Conclusions
9.2. Future Research Directions
References
- Leskinen, J. Evaluation Criteria for Future Identity Management. In Proceedings of the 2012 IEEE 11th International Conference on Trust, Security and Privacy in Computing and Communications, 2012; pp. 801–806. [Google Scholar] [CrossRef]
- Thakur, M.A.; Gaikwad, R. User identity and Access Management trends in IT infrastructure- an overview. In Proceedings of the 2015 International Conference on Pervasive Computing (ICPC), 2015; pp. 1–4. [Google Scholar] [CrossRef]
- IBM. What is cloud hosting. Available online: https://www.ibm.com/cloud/learn/what-is-cloud-hosting (accessed on 2023-07-05).
- Zareen, M.S.; Tahir, S.; Akhlaq, M.; Aslam, B. Artificial Intelligence/ Machine Learning in IoT for Authentication and Authorization of Edge Devices. In Proceedings of the 2019 International Conference on Applied and Engineering Mathematics (ICAEM), 2019; pp. 220–224. [Google Scholar] [CrossRef]
- Vorakulpipat, C.; Rattanalerdnusorn, E.; Pichetjamroen, S. Comprehensive-Factor Authentication in Edge Devices in Smart Environments: A Case Study. In Proceedings of the 2022 11th International Conference on Control, Automation and Information Sciences (ICCAIS), 2022; pp. 391–396. [Google Scholar] [CrossRef]
- Castellano, G.; Esposito, F.; Risso, F. A Service-Defined Approach for Orchestration of Heterogeneous Applications in Cloud/Edge Platforms. IEEE Transactions on Network and Service Management 2019, 16, 1404–1418. [Google Scholar] [CrossRef]
- Taleb, T.; Samdanis, K.; Mada, B.; Flinck, H.; Dutta, S.; Sabella, D. On Multi-Access Edge Computing: A Survey of the Emerging 5G Network Edge Cloud Architecture and Orchestration. IEEE Communications Surveys & Tutorials 2017, 19, 1657–1681. [Google Scholar] [CrossRef]
- Sonmez, C.; Ozgovde, A.; Ersoy, C. Fuzzy Workload Orchestration for Edge Computing. IEEE Transactions on Network and Service Management 2019, 16, 769–782. [Google Scholar] [CrossRef]
- Ranjan, A.; Guim, F.; Chincholkar, M.; Ramchandran, P.; Mishra, R.; Ranganath, S. Convergence of Edge Services & Edge Infrastructure. In Proceedings of the 2021 IEEE Conference on Network Function Virtualization and Software Defined Networks (NFV-SDN), 2021; pp. 96–99. [Google Scholar] [CrossRef]
- Loghin, D.; Ramapantulu, L.; Teo, Y.M. Towards Analyzing the Performance of Hybrid Edge-Cloud Processing. In Proceedings of the 2019 IEEE International Conference on Edge Computing (EDGE), 2019; pp. 87–94. [Google Scholar] [CrossRef]
- Risso, F. Creating an Edge-to-Cloud Computing Continuum: Status and Perspective. In Proceedings of the 2022 3rd International Conference on Embedded & Distributed Systems (EDiS), 2022; pp. 4–4. [Google Scholar] [CrossRef]
- Kourtis, M.A.; Gutierrez, I.; Areizaga, E.; Alexandridis, G.; Tavernier, W.; Imeri, A.; Tcholtchev, N.; Xilouris, G.; Trakadas, P.; Chochliouros, I.; et al. OASEES: Leveraging DAO-Based Programmable Swarms for Optimized Edge-to-Cloud Data Processing. In Proceedings of the Distributed Computing and Artificial Intelligence, Special Sessions I, 21st International Conference; Cham, Mehmood, R., Hernández, G., Praça, I., Wikarek, J., Loukanova, R., Monteiro dos Reis, A., Skarmeta, A., Lombardi, E., Eds.; 2025; pp. 311–318. [Google Scholar] [CrossRef]
- OASEES. OASEES – Open autonomous programmable cloud apps & smart sensors. Available online: https://oasees-project.eu/ (accessed on 2025-01-08).
- Imeri, A.; Gharsallaoui, O.; Grandjean, T.; Roth, U. A Blockchain-based data management approach for swarm-edge computing. In Proceedings of the 2025 12th IFIP International Conference on New Technologies, Mobility and Security (NTMS), 2025; pp. 136–143. [Google Scholar] [CrossRef]
- Sadiku, M.N.; Musa, S.M.; Momoh, O.D. Cloud Computing: Opportunities and Challenges. IEEE Potentials 2014, 33, 34–36. [Google Scholar] [CrossRef]
- Peter Mell, T.G. The NIST Definition of Cloud Computing. Available online: https://nvlpubs.nist.gov/nistpubs/legacy/sp/nistspecialpublication800-145.pdf (accessed on 2025-12-17).
- Cao, K.; Liu, Y.; Meng, G.; Sun, Q. An Overview on Edge Computing Research. IEEE Access 2020, 8, 85714–85728. [Google Scholar] [CrossRef]
- Kaur, G.; Batth, R.S. Edge Computing: Classification, Applications, and Challenges. In Proceedings of the 2021 2nd International Conference on Intelligent Engineering and Management (ICIEM), 2021; IEEE; pp. 254–259. [Google Scholar] [CrossRef]
- Ahmed, H.; Glasgow, J. Swarm intelligence: concepts, models and applications. School Of Computing, Queens University Technical Report; 2012. [Google Scholar]
- Yang, J.; Qu, L.; Shen, Y.; Shi, Y.; Cheng, S.; Zhao, J.; Shen, X. Swarm Intelligence in Data Science: Applications, Opportunities and Challenges. In Proceedings of the Advances in Swarm Intelligence; Tan, Y., Shi, Y., Tuba, M., Eds.; Cham, 2020; pp. 3–14. [Google Scholar]
- Nguyen, L.V. Swarm Intelligence-Based Multi-Robotics: A Comprehensive Review. AppliedMath 2024, 4, 1192–1210. [Google Scholar] [CrossRef]
- Imeri, A.; Agoulmine, N.; Khadraoui, D. Smart Contract modeling and verification techniques: A survey. In Proceedings of the Proc. of the 8th International Workshop on ADVANCEs in ICT Infrastructures and Services (ADVANCE 2020) Proc. of the 8th International Workshop on ADVANCEs in ICT Infrastructures and Services (ADVANCE 2020), Cancún, Mexico, January 2020; pp. 1–8. [Google Scholar]
- Wang, S.; Ding, W.; Li, J.; Yuan, Y.; Ouyang, L.; Wang, F.Y. Decentralized Autonomous Organizations: Concept, Model, and Applications. IEEE Transactions on Computational Social Systems 2019, 6, 870–878. [Google Scholar] [CrossRef]
- Antal, C.; Cioara, T.; Anghel, I.; Antal, M.; Salomie, I. Distributed Ledger Technology Review and Decentralized Applications Development Guidelines. Future Internet 2021, 13. [Google Scholar] [CrossRef]
- Pons, M.; Valenzuela, E.; Rodríguez, B.; Nolazco-Flores, J.A.; Del-Valle-Soto, C. Utilization of 5G Technologies in IoT Applications: Current Limitations by Interference and Network Optimization Difficulties—A Review. Sensors 2023, 23. [Google Scholar] [CrossRef]
- Wang, Y.; Tian, Z.; Fan, X.; Cai, Z.; Nowzari, C.; Zeng, K. Distributed Swarm Learning for Edge Internet of Things. IEEE Communications Magazine 2024, 62, 160–166. [Google Scholar] [CrossRef]
- Chochliouros, I.P.; Kourtis, M.A.; Xilouris, G.; Tavernier, W.; Sanchez, E.A.; Anastassova, M.; Bolzmacher, C.; Tcholtchev, N.; Corsi, A.; Trakadas, P.; et al. OASEES: An Innovative Scope for a DAO-Based Programmable Swarm Solution, for Decentralizing AI Applications Close to Data Generation Locations. In Proceedings of the Artificial Intelligence Applications and Innovations. AIAI 2023 IFIP WG 12.5 International Workshops, Cham, 2023; pp. 91–105. [Google Scholar] [CrossRef]
- Babaioff, M.; Mansour, Y.; Nisan, N.; Noti, G.; Curino, C.; Ganapathy, N.; Menache, I.; Reingold, O.; Tennenholtz, M.; Timnat, E. ERA: A Framework for Economic Resource Allocation for the Cloud. In Proceedings of the Proceedings of the 26th International Conference on World Wide Web Companion, Republic and Canton of Geneva, CHE, WWW ’17 Companion, 2017; pp. 635–642. [Google Scholar] [CrossRef]
- Furman, E.; Senderovich, A.; Bergsma, S.; Beck, J.C. Capacity Allocation for Clouds with Parallel Processing, Batch Arrivals, and Heterogeneous Service Requirements. arXiv 2022, arXiv:2209.08820. [Google Scholar] [CrossRef]
- Rac, S.; Brorsson, M. At the Edge of a Seamless Cloud Experience. arXiv 2021, arXiv:2111.06157. [Google Scholar] [CrossRef]
- Gurkok, C. Securing Cloud Computing Systems. In Computer and Information Security Handbook (Second Edition), Second Edition ed.; Vacca, J.R., Ed.; Morgan Kaufmann: Boston, 2013; pp. 97–123. [Google Scholar] [CrossRef]
- Abadi, D.J. Data management in the cloud: Limitations and opportunities. IEEE Data Eng. Bull. 2009, 32, 3–12. [Google Scholar]
- Kokila, M.; Reddy K, S. Authentication, access control and scalability models in Internet of Things Security–A review. Cyber Security and Applications 2025, 3, 100057. [Google Scholar] [CrossRef]
- Hassan, S.; De Filippi, P. Decentralized autonomous organization. Internet Policy Review 2021, 10(2). [Google Scholar] [CrossRef]
- Sun, Y.; Shao, Y. Research on Data Security Communication Scheme of Heterogeneous Swarm Robotics System in Emergency Scenarios. Sensors 2022, 22. [Google Scholar] [CrossRef]
- Strobel, V.; Ferrer, E.C.; Dorigo, M. Blockchain Technology Secures Robot Swarms: A Comparison of Consensus Protocols and Their Resilience to Byzantine Robots. Frontiers in Robotics and AI 2020, 7, 54. [Google Scholar] [CrossRef]
- Pacheco, A.; Strobel, V.; Reina, A.; Dorigo, M. Real-time coordination of a foraging robot swarm using blockchain smart contracts. In Swarm Intelligence – Proceedings of ANTS 2022; Lecture Notes in Computer Science; Springer: Cham, 2022; Vol. 13491, pp. 196–208. [Google Scholar] [CrossRef]
- Tran, J.A.; Ramachandran, G.S.; Shah, P.M.; Danilov, C.B.; Santiago, R.A.; Krishnamachari, B. SwarmDAG: A partition-tolerant distributed ledger protocol for swarm robotics. Ledger 2019, 4, 1–19. [Google Scholar] [CrossRef]
- Ibrahim, H.A.; Shouman, M.A.; El-Fishawy, N.A. Improving the reliability of nanosatellite swarms by adopting blockchain technology. In Complex & Intelligent Systems; 2024. [Google Scholar] [CrossRef]
- Bulgakov, A.L.; Aleshina, A.V.; Smirnov, S.D.; Demidov, A.D.; Milyutin, M.A.; Xin, Y. Scalability and security in blockchain networks: Evaluation of sharding algorithms and prospects for decentralized data storage. Mathematics 2024, 12, 3860. [Google Scholar] [CrossRef]
- Wu, J.; Yuan, L.; Xie, T.; Dai, H. A sharding blockchain protocol for enhanced scalability and performance optimization through account transaction reconfiguration. Journal of King Saud University - Computer and Information Sciences 2024. [Google Scholar] [CrossRef]
- Strobel, V.; Pacheco, A.; Dorigo, M. Robot swarms neutralize harmful Byzantine robots using a blockchain-based token economy. Science Robotics 2023, 8, eabm4636. [Google Scholar] [CrossRef] [PubMed]
- Li, T.; Sahu, A.K.; Talwalkar, A.; Smith, V. Federated Learning: Challenges, Methods, and Future Directions. IEEE Signal Processing Magazine 2020, 37, 50–60. [Google Scholar] [CrossRef]
- Nguyen, D.C.; Pathirana, P.N.; Ding, M.; Seneviratne, A. Integration of Blockchain and Cloud of Things: Architecture, Applications and Challenges. IEEE Communications Surveys & Tutorials 2020, 22, 2521–2549. [Google Scholar] [CrossRef]
- Wang, S.; Ding, W.; Li, J.; Yuan, Y.; Ouyang, L.; Wang, F.Y. Decentralized Autonomous Organizations: Concept, Model, and Applications. IEEE Transactions on Computational Social Systems 2019, 6, 870–878. [Google Scholar] [CrossRef]
- Beck, R.; Müller-Bloch, C.; King, J.L. Governance in the Blockchain Economy: A Framework and Research Agenda. Journal of the Association for Information Systems 2018, 19, 1020–1034. [Google Scholar] [CrossRef]
- Lustenberger, M. DAO Research Trends: Reflections and Learnings from the First European DAO Workshop. Applied Sciences 2025, 15, 3491. [Google Scholar] [CrossRef]
- Bonnet, S. DAO: A Systematic Literature Review and Research Agenda. International Journal of Emerging Technologies and Society 2024. [Google Scholar] [CrossRef]
- Ly, R.; Shojaei, A. Decentralized Autonomous Organization in Built Environments: Applications, Potential and Limitations. In Information Systems Frontiers; 2025. [Google Scholar] [CrossRef]
- Al Jasem, M.S.; De Clark, T.; Shrestha, A.K. Toward Decentralized Intelligence: A Systematic Literature Review of Blockchain-Enabled AI Systems. Information 2025, 16, 765. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Derdour, M.; Mukherjee, M.; Derhab, A.; Maglaras, L.; Janicke, H. Blockchain Technologies for the Internet of Things: Research Issues and Challenges. IEEE Internet of Things Journal 2019, 6, 2188–2204. [Google Scholar] [CrossRef]
- Dorigo, M.; Theraulaz, G.; Trianni, V. Swarm Robotics: Past, Present, and Future. Proceedings of the IEEE 2021, 109, 1152–1165. [Google Scholar] [CrossRef]
- Benet, J. IPFS - Content Addressed, Versioned, P2P File System. arXiv 2014, arXiv:1407.3561. [Google Scholar] [CrossRef]
- Protocol Labs. Filecoin: A Decentralized Storage Network. Technical report. Protocol Labs, 2017. [Google Scholar]
- Oliveira, M.; Chauhan, S.; Pereira, F.; Felgueiras, C.; et al. Blockchain protocols and edge computing targeting Industry 5.0 needs: A survey. Sensors 2023, 23, 9174. [Google Scholar] [CrossRef]
- Nguyen, T.; Nguyen, H.; Nguyen Gia, T.; et al. Exploring the integration of edge computing and blockchain into IoT systems: principles, architectures, security, and applications. Journal of Network and Computer Applications 2024. [Google Scholar] [CrossRef]
- Zhu, J.; Li, F.; Chen, J. A survey of blockchain, artificial intelligence, and edge computing for Web 3.0. arXiv 2024. [Google Scholar] [CrossRef]
- OASEES Consortium GitHub. OASEES Web3.0 Cloud native Swarm Computing - oasees/oasees-stack-prototype. Available online: https://github.com/oasees/oasees-stack-prototype (accessed on 2025-07-16).
| 1 | OASEES: Open autonomous programmable cloud apps & smart sensors; https://oasees-project.eu/
|
| 2 | Gaia-X: Federated Secure Data Infrastructure; https://gaia-x.eu/
|
| 3 | EOCS European Open Science Cloud; https://open-science-cloud.ec.europa.eu/
|
| Evaluation Metric | Blockchain-Based Swarm Coordination [36,37,38] | DAO-Enabled Edge/CPS Systems [45,46] | OASEES (this research paper) |
|---|---|---|---|
| Primary objective | Secure coordination and consensus among swarm agents | Automation of selected cyber–physical processes | Governance-driven data availability and decision-making across edge–cloud swarms |
| Governance model | Implicit or protocol-level coordination | Partial DAO usage, often limited to voting | DAO-as-a-Service with explicit proposal, voting, execution, and treasury mechanisms |
| Data availability handling | Assumed through ledger replication | Application-specific and limited | Explicit design combining on-chain governance, off-chain storage, and oracle-based ingestion |
| Identity and access control | Typically absent or centralized | Basic role-based or token-based mechanisms | SSI-based identity with verifiable credentials and policy-driven access control |
| Human-in-the-Loop support | Generally not considered | Occasionally included for exceptional decisions | Native HITL integration for critical governance and operational actions |
| Validation scope | Simulations or single-domain experiments | Single use-case deployments | Multiple real-world use cases across energy, infrastructure, and industrial domains |
| Known limitations | Limited governance and data lifecycle management | Participation and scalability challenges | Governance latency and reliance on permissioned stakeholder participation |
| Main Actors | |
|---|---|
| DSO ENO |
Distributed System Operator Electricity Network Operator Manages the energy grid |
| eMSP | e-Mobility Service Provider Manages the business side of the changing network with its charging stations for electric vehicles (customers and monetising EV charging) |
| CPO | Charging Point Operator Builds, manages and maintains the charging network with the charging stations |
| EV Owner EV Fleet Operator |
Owner of electric vehicles |
| Main Involved Systems | |
| EV | Electric Vehicles |
| CS | Charging Station |
| SM | Smart Meter Real-time readings of energy consumption data. |
| New Platforms/Systems | |
| EMP | Electronic Mobility Platform Hosts charging stations Hosts electric vehicles |
| DSO Platform | Distributed System Operator Platform Manages DSO activities |
| P2P Marketplace with DLT |
P2P energy flexibility trading Access via the DSO Platform and the EMP |
| Forecasting System |
Estimates energy production and energy consumption Estimates the flexibility needs |
| New Sub-Systems | |
| DApp | Decentralised Application Aligns charging available and energy flexibility requests via the DAO |
| DAO | Decentralised Autonomous Organization |
| Dashboards | Provide access to the P2P Marketplace Accessed via the DSO platform and EMP Show real-time payment data. Manage access control |
| Important Data Structures | |
| Smart Meter Energy Data |
Energy grid monitoring data |
| Charging Station Energy Data |
Charged energy to the electric vehicle |
| Electric Vehicle Energy Data |
Consumed energy by the electric vehicle State of charge |
| Energy Flexibility Request | Energy need Time indication for flexibility service provision |
| Energy Flexibility Offer | Remuneration asked for flexibility service provision |
| Main Actors | |
|---|---|
| Customer | Hosts multiple sensors |
| HITL | Human in the Loop Takes decisions based on decision support |
| Main Involved Systems | |
| Smart Edge Device | Accelerator Runs decentralized application (DApp) Provides federated learning for information collection Features pre-treatement of data and sharing it with other Smart Edge Devices |
| Intra-Structure Sensor | Allows internal scanning of objects |
| New Platforms/Systems | |
| Night Watch | Monitors structures before, during and after an event. Placed on each sensor or a few clusters of sensors depending on how close the sensors are placed to each other Decision-Support System Verifies, filters, corrects, and interprets raw sensor data. |
| OASEES Supported Architecture |
Governance and process optimization |
| New Sub-Systems | |
| DApp | Decentralised Application via the DAO |
| DAO | Reports to the Human in the Loop Asks for advice actions Requests to review |
| Dashboards | Controls all the NightWatch clients running at each location Collect the individual models from each NightWatch to update a global model. Collect data from various sensors to manually train a model. |
| Important Data Structures | |
| Raw Sensor Data | Collected by the sensors |
| Clean Sensor Data | Pre-treated data Verified, filtered, and corrected raw data by the Night Watch System Stored in the database of the smart-edge device. |
| Processed Data | Interpreted version of the clean data created by the Night Watch System, stored in the IPFS |
| Event Data Hashes | Summary/array of processed data created by the Night Watch System, stored in the blockchain. |
| Main Actors | |
|---|---|
| OASEES Stakeholder | Access the portal to request algorithm services, results and reports Involved in DAO proposals (voting) for improvement of the ecosystem |
| GAIA-X Stakeholder | Energy company interested in data product of another energy company Access to the Ocean Marketplace and purchase data product |
| Specialist | Specialist on wind turbines and their failures. Human in the Loop (HITL) Labels and classifies new types of newly detected anomalies Take decisions over the devices for monitoring schedules Check result reports and maintenance plans to verify their quality |
| Installer | Setup, pre-configuration, and on/off-boarding of IoT and edge devices |
| Developer | Develops and publishes services and functionalities |
| Main Involved Systems | |
| IoT Device | Blade Acoustic-Monitoring System BAMS Initiate polls and votes |
| Edge Device | Assigned to one swarm of IoT devices with the BAMSReceives the raw IoT data Has an attached accelerator Manages the federated learning between IoT devices and the accelerator |
| Accelerator | Machine-learning algorithm Failure prediction Generates a consolidated algorithm from fragmented algorithms |
| Cloud | Provides services, e.g., failure-prediction algorithm Off-chain storage Offer data in the Ocean Marketplace |
| New Platforms/Systems | |
| OAEES Portal | Monitors structures before, during and after an event. Placed on each sensor or a few clusters of sensors depending on how close the sensors are placed to each other Decision-Support System Verifies, filters, corrects, and interprets raw sensor data. |
| New Sub-Systems | |
| DApp | Decentralised Application Monitors health status of blade wind turbines Shows meteorological conditions of wind farm Show geographical position of devices Notebook Marketplace |
| DAO | Distributed Autonomous Organisation Resource orchestration Managing polls Wind turbine blades test report |
| Important Data Structures | |
| Verifiable Credentials |
Attributes of the IoT and edge devices Location of the wind farm where it is located Used to access the portal to request algorithm services, result reports Needed by specialists to access the data without purchasing it, to supervise the results of the algorithms and labelling new anomalies Needed by edge devices for uploading aggregated algorithms to the marketplace |
| Data Product | Technical reports based on the processed acoustic dataset Wind-turbine blades anomalies detection Maintenance prediction and impact on Levelized Cost of Energy (LCOE) Dynamic maintenance plan according to blade health status Anonymized blade-acoustic data |
| Scientific Contribution) | Artifact Demonstrated in the Paper |
|---|---|
| Novel decentralized governance model for edge–swarm computing | Architecture design in Section 5; DAO governance workflows in the Energy Grid UC (Figure 2), the Structural Safety UC (Figure 3), the Windmill Maintenance UC (Figure 4); proposal and voting mechanisms described in Section 6.1.1 - Section 6.3. |
| SSI-based identity and access-control mechanism | Identity Layer description in Section 5.2; DID/VC-based onboarding and authentication flows in the Energy Grid UC; sensor/device verification in Structural Safety UC; stakeholder-controlled data access in the Windmill Maintenance UC. |
| Validated architecture for real-time decentralized data availability | OASEES high-level architecture in Section 5; empirical validation in the Energy Grid UC (real-time energy flexibility coordination), the Structural Safety UC (low-latency seismic event reporting), and Windmill Maintenance UC (federated BAMS-based anomaly detection). |
| Empirical assessment of DLT limitations in resource-constrained environments | Performance-oriented discussions in the Structural Safety UC (edge latency, high-frequency sensor data) and Windmill Maintenance UC (on-device federated learning, hybrid on/off-chain processing); mitigation strategies across Section 5.1, Section 5.2, Section 6.2, and Section 6.3; and quantitative smart contract measurements presented in Section 7.2. |
| Evaluation Metric | Centralized Approach | DAO/Swarm-Based Approach |
|---|---|---|
| Pricing and Market Regulation | Central authority (e.g., utility or aggregator) sets prices, which may not reflect real-time local supply/demand. | DAO allows dynamic, transparent pricing proposals and adoption of the lowest available prices, reflecting swarm-level conditions. |
| Infrastructure Management | New device onboarding/removal is slow, requiring central validation and updates, creating bottlenecks. | Swarm-driven DAO governance enables rapid, collective onboarding/removal of edge devices and organizations, enhancing adaptability. |
| Incentive Mechanisms | Incentives are designed and distributed by a central body, with limited transparency and slow disbursement. | Smart contracts automate incentives and micro-payments across stakeholders, ensuring transparency and efficiency. |
| Data Governance | Centralized control of access rights and sharing rules, risking opacity and single points of manipulation. | DAO-managed rules ensure transparent, auditable data access and sharing policies, collectively validated by participants. |
| Resilience and Trust | Single point of failure: if the central operator is compromised, the entire system’s trust and functionality collapse. | Decentralized decision-making and blockchain auditability enhance trust, resilience, and fault tolerance across the swarm. |
| Evaluation Metric | Centralized Approach | DAO/Swarm-Based Approach |
|---|---|---|
| Latency in Event Detection | High latency is caused by centralized data transfer and sequential processing. Reports may take minutes to hours after the event. | Low latency through edge pre-processing, swarm coordination, and DAO-triggered reporting. Information can be delivered in near real-time. |
| Resilience and Fault Tolerance | Single point of failure: if the central server or DSS fails, the entire monitoring process collapses. | Distributed and fault-tolerant: swarm edge devices continue to operate even if some nodes fail; blockchain ensures data integrity. |
| Decision-Making Speed | Bottlenecked at the central DSS; limited scalability under heavy sensor load. | Parallel, local decision-making at edge nodes supported by DAO governance enables scalable and adaptive processing. |
| Transparency and Auditability | Opaque decision process, with limited visibility for external stakeholders. Logs may be fragmented or delayed. | Tamper-evident, auditable records stored on blockchain. DAO governance ensures accountability and traceability of proposals and reports. |
| Emergency Response Efficiency | Critical stakeholders (airports, tunnels, emergency teams) often receive delayed notifications, limiting early intervention. | Near real-time delivery of validated safety assessments to critical stakeholders, enabling faster and potentially life-saving interventions. |
| Evaluation Metric | Centralized Approach | DAO/Swarm-Based Approach |
|---|---|---|
| Membership Onboarding | Stakeholders (operators, developers, specialists) are added manually by a central authority, which can be slow and opaque. | DAO proposals allow transparent, auditable joining of new members, validated collectively by existing DAO participants. |
| Maintenance Protocols | Protocols for inspection and maintenance are defined and updated by a central operator; limited responsiveness to anomalies. | HITL specialists propose maintenance protocols, which are voted on by DAO members, enabling rapid and democratic updates. |
| Data Access | A central authority controls access to sensor and acoustic datasets; limited traceability and accountability. | DAO governs dataset access via collective voting, ensuring transparency, traceability, and secure authorization. |
| Model Governance | Algorithmic updates for anomaly detection or predictive maintenance are imposed centrally, with minimal stakeholder involvement. | New models are proposed by developers or HITL specialists and evaluated collectively by DAO members before deployment. |
| Fault Detection and Response | Centralized monitoring may delay anomaly detection and response; single point of failure reduces resilience. | Swarm IoT devices and edge analytics enable near real-time detection, coordinated responses, and distributed resilience. |
| Transparency and Trust | Decision-making processes are largely opaque; stakeholders must trust the central operator. | On-chain governance and smart contracts provide auditable records of proposals, votes, and maintenance actions, enhancing trust. |
| Security Objective | Blockchain Role in Swarm Systems | Threats Mitigated | Applied to Use Cases |
|---|---|---|---|
| Decentralized Trust | Removes need for a central coordinator; uses cryptographic validation among nodes | Compromised leader nodes, central point of failure |
Energy Grid: Transparent market pricing without central DSO. Structural Safety: Distributed validation of safety alerts. Windmill Maintenance: Collective validation of blade fault reports. |
| Authentication | Agents identified via blockchain-based public/private keys | Spoofing, unauthorized access, Sybil attacks |
Energy Grid: Smart meters and EVs verified via blockchain IDs. Structural Safety: Only authenticated sensors/HITL experts can submit data. Windmill Maintenance: Acoustic IoT devices authenticated for secure monitoring. |
| Data Integrity | Swarm data verified using hashes stored on-chain | Tampering, false data injection |
Energy Grid: Energy usage data anchored on-chain. Structural Safety: Seismic/structural readings validated. Windmill Maintenance: Acoustic blade monitoring logs secured immutably. |
| Consensus and Coordination | Smart contracts and consensus rules for task assignment and conflict resolution | Conflicting commands, behavior hijacking |
Energy Grid: DAO resolves price-setting conflicts. Structural Safety: Conflicting safety reports reconciled. Windmill Maintenance: DAO coordinates fault detection & maintenance schedules. |
| Traceability and Audit | Logs of actions and decisions stored immutably | Lack of accountability, undetected malicious behavior |
Energy Grid: Auditable pricing and incentive proposals. Structural Safety: Transparent safety event handling. Windmill Maintenance: Maintenance actions recorded for compliance. |
| Access Control | Smart contracts enforce access rules for shared swarm resources | Unauthorized usage, denial of service |
Energy Grid: DAO manages access to EV/charging data. Structural Safety: Only verified stakeholders access safety data. Windmill Maintenance: DAO-voted rules govern acoustic dataset sharing. |
| Resilience to Collusion | Immutable logs and decentralized consensus expose rogue or colluding agents | Insider threats, swarm manipulation |
Energy Grid: Prevents operator collusion on prices. Structural Safety: Detects false alerts from compromised sensors. Windmill Maintenance: Identifies coordinated misreporting of blade faults. |
| Objective | How It Is Achieved | Fulfillment |
|---|---|---|
| Decentralized Governance Model for Edge–Swarm Computing | DAO-centric governance replaces single-operator control with proposal–vote–execute loops across human stakeholders and edge nodes. Each swarm executes decisions autonomously while maintaining a shared, immutable governance record. Use cases demonstrate distributed coordination (e.g., pricing rules, data-sharing policies, anomaly validation) managed collectively through DAOs. | The use cases Energy Grid, Structural Safety, and Windmill Maintenance show transparent, tamper-proof decision trails replacing centralized control. DAO proposals, votes, and on-chain logs provide full auditability and accountability for multi-stakeholder collaboration. |
| Identity-Based Access Control (SSI) | Integration of a Self-Sovereign Identity (SSI) layer employing Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs) for actors and devices. Smart contracts enforce access control rules for data and actions, ensuring trustless authentication and authorization across DAOs. | Architecture and UC diagrams show DIDs/VCs used by EV chargers, sensors, and maintenance devices. Access to datasets and smart contracts is restricted to verified participants, demonstrating decentralized identity enforcement across all pilots. |
| Validated Architecture for Real-Time Data Availability | Hybrid on-chain/off-chain design: governance and hashes on DLT, data stored in IPFS and edge devices. “Near-happening” data processing ensures low latency, while decentralized federation avoids central data silos. | All UCs validate this design: UC Energy Grid integrates forecasts and grid data via oracles; UC Structural Safety uses edge processing for safety alerts; UC Windmill Maintenance deploys federated learning and IPFS anchoring for maintenance data. Evaluation shows improved scalability and reduced latency. |
| Empirical Analysis of Blockchain Limitations in Edge–Swarm Systems | Hybrid orchestration mitigates DLT constraints (latency, energy) by pushing analytics off-chain, batching DAO proposals, and minimizing on-chain data. Comparative discussions show trade-offs between transparency, efficiency, and performance. | Performance evaluation identifying latency, energy consumption, scalability, privacy, and integration challenges. A hybrid architecture with Layer-2 protocols and edge-native processing is proposed as a mitigation. Table 11 documents five key limitations. Section 7.2.3 on page 28 provides benchmarks: 3.2s transaction latency, 0.02 ETH for device registration, and linear scalability through sharding. |
| Limitation | Explanation |
|---|---|
| Latency | Blockchain consensus (especially on public networks) introduce delays unsuitable for real-time swarm control |
| Energy Consumption | Running full or even lightweight blockchain clients may exceed the energy budget of small, mobile agents |
| Scalability Issues | Large swarm populations can overwhelm the blockchain with transactions or coordination overhead |
| Privacy Concerns | Public or poorly designed blockchain ledgers may expose sensitive swarm data or strategies |
| Integration Complexity | Swarm protocols need modification to support blockchain-based identities, logging, and coordination |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




