Submitted:
17 December 2025
Posted:
18 December 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Encryption Method
2.1. Chaotic Functions and Encryption
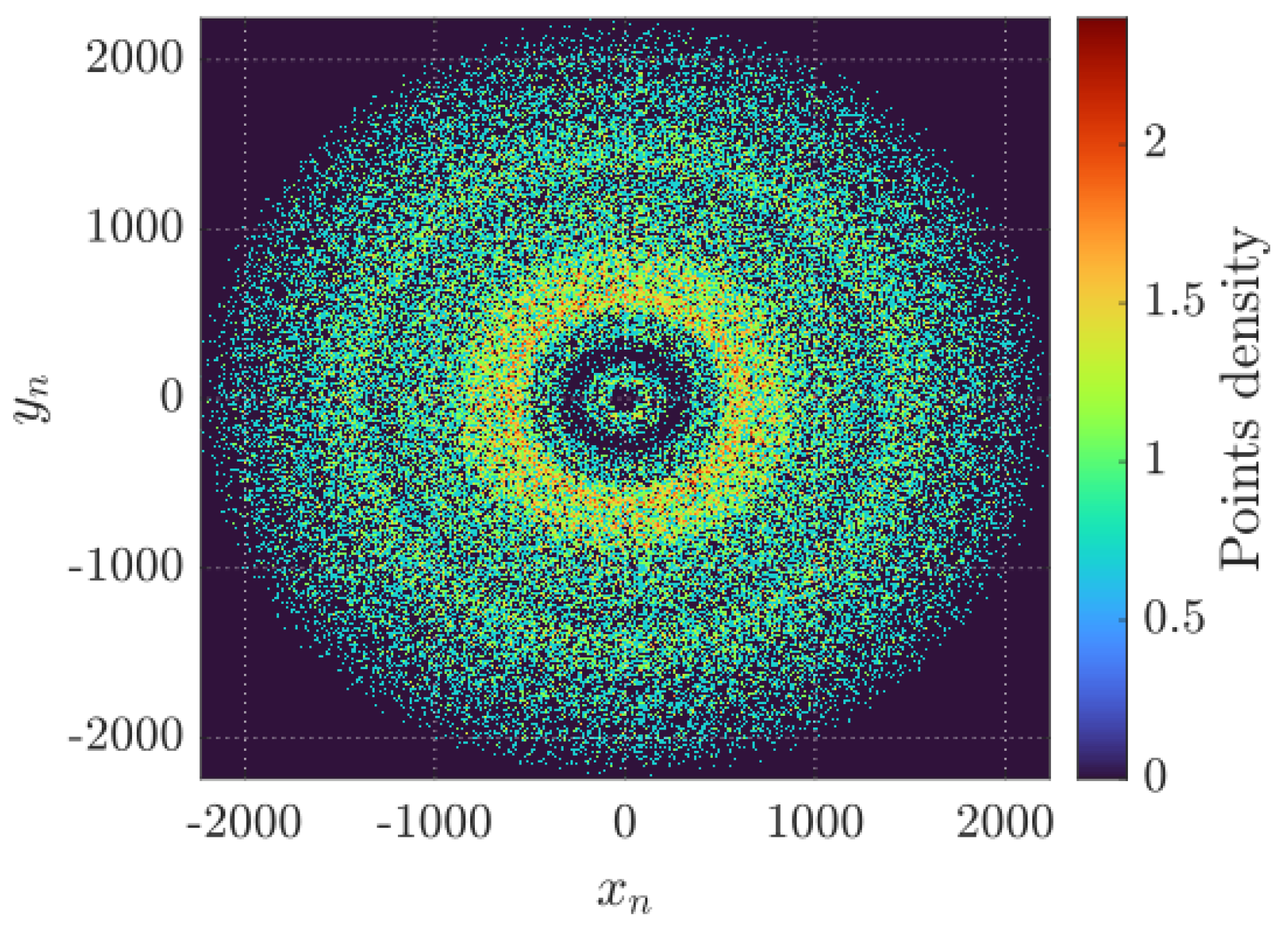
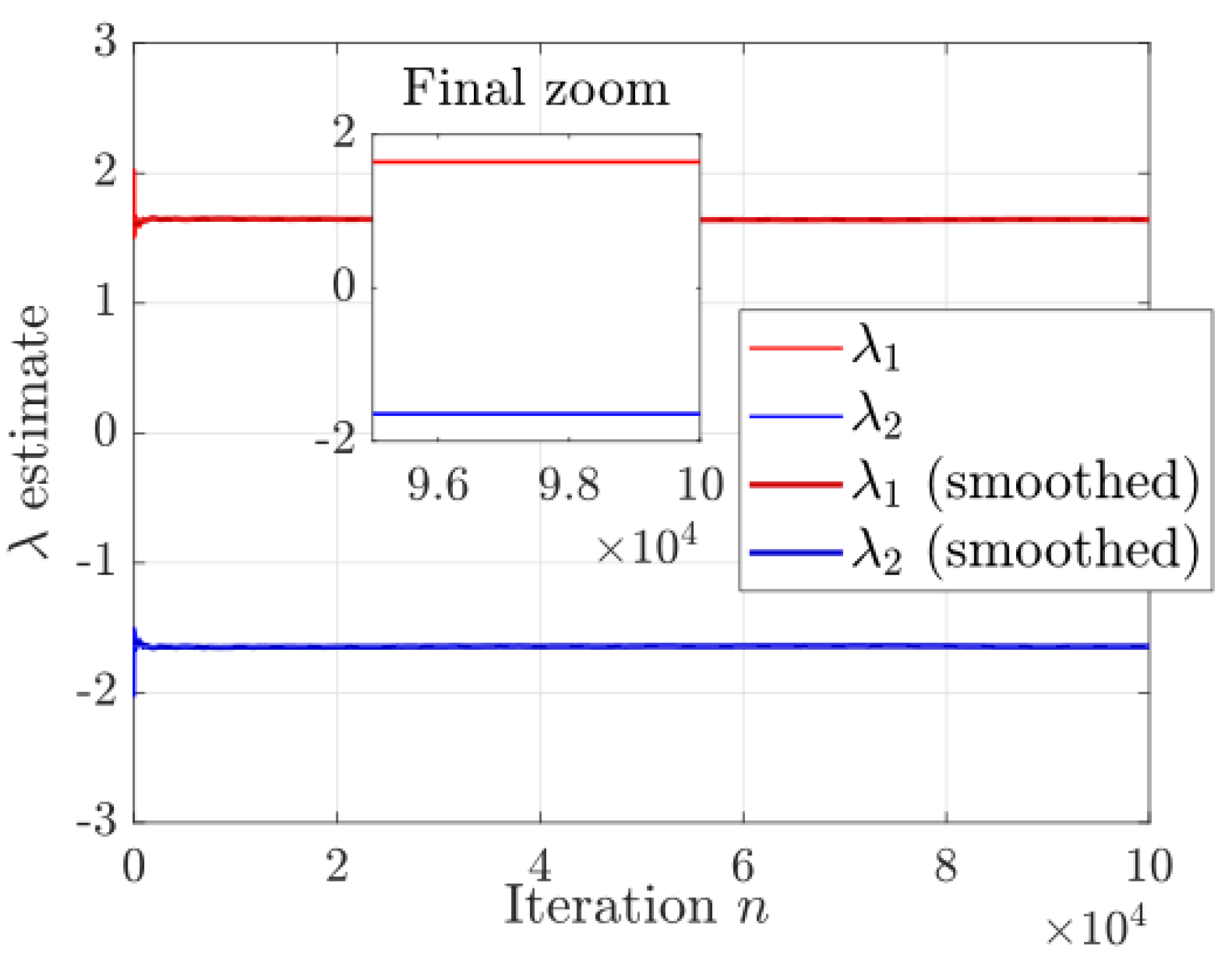
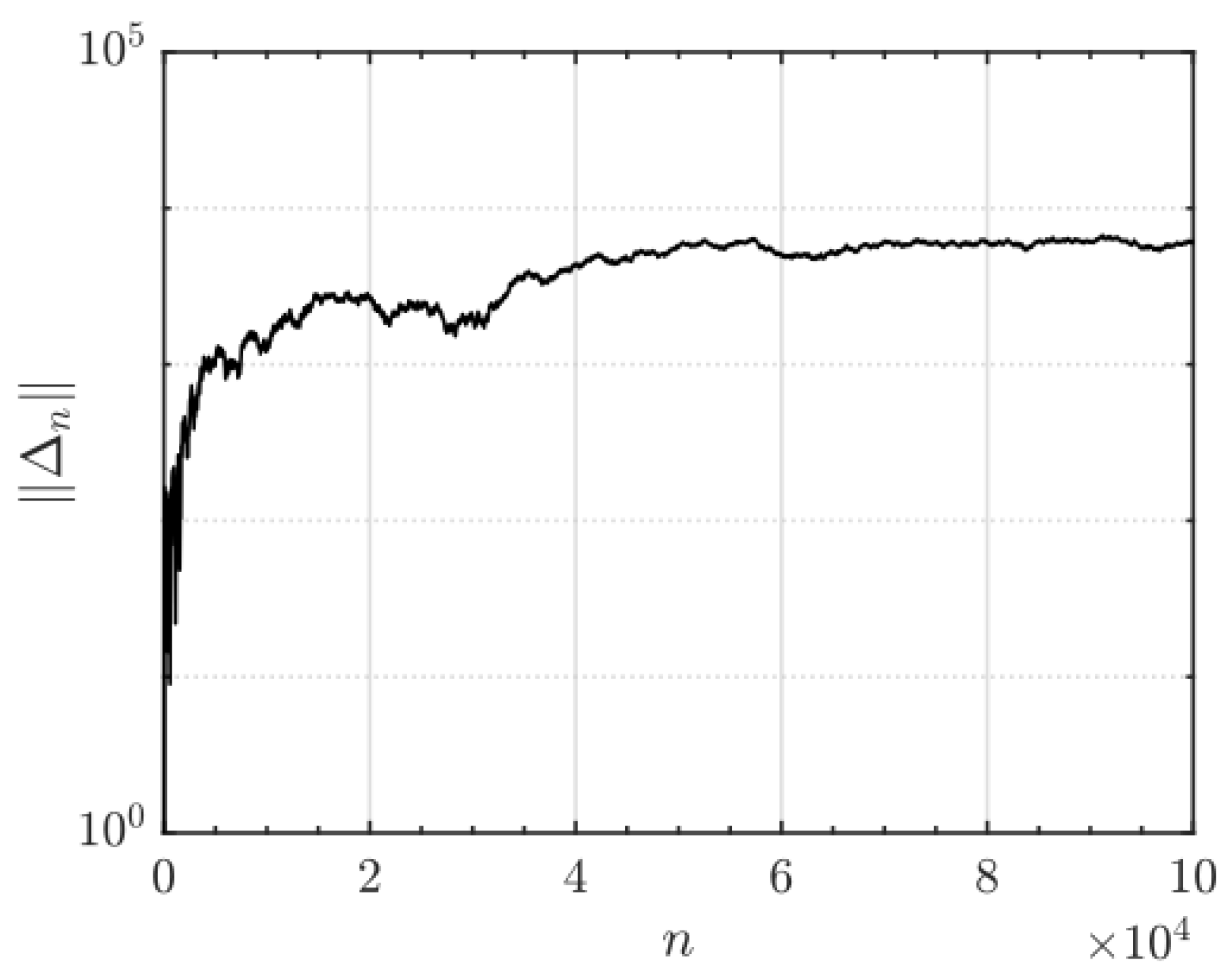
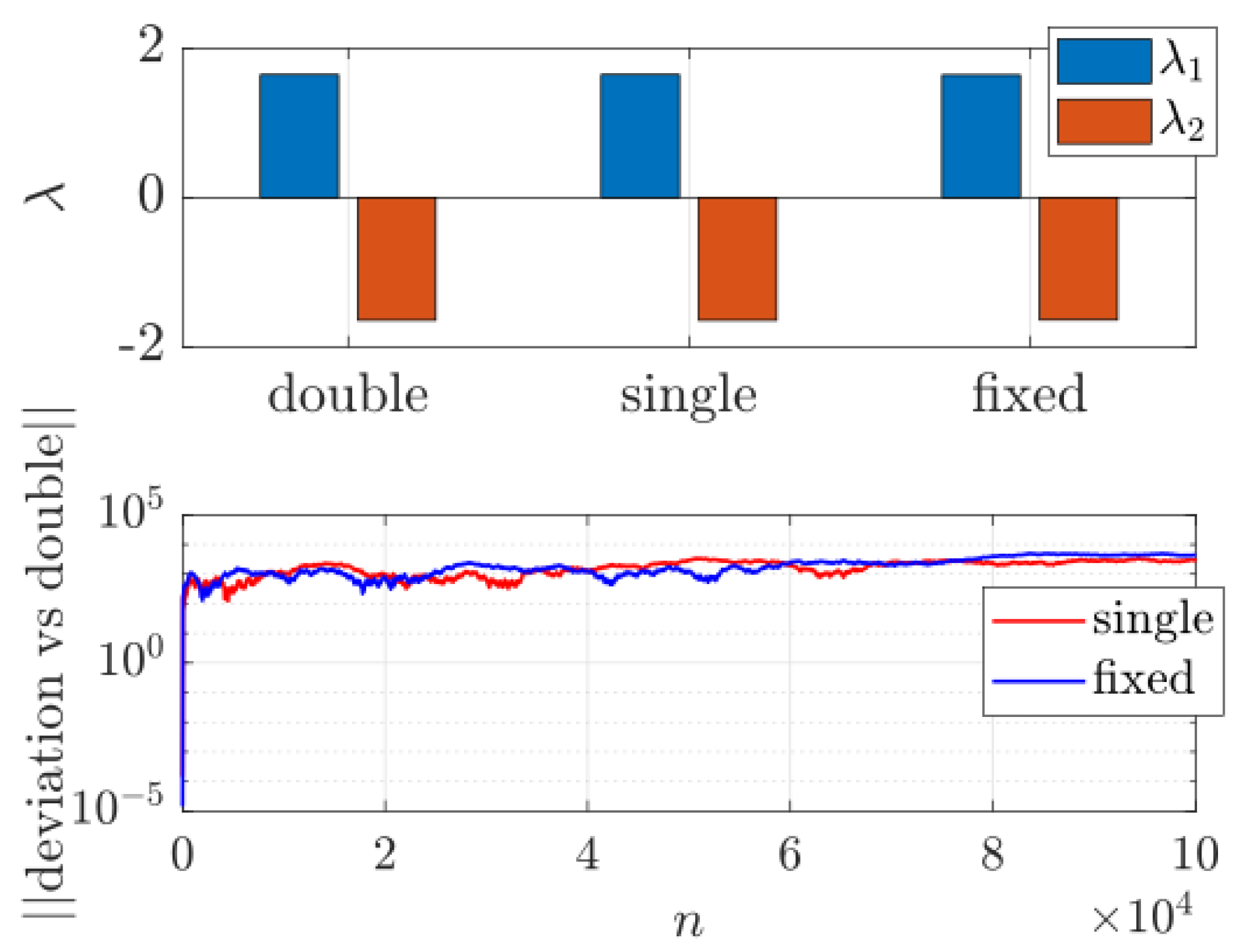
2.1.1. Dynamical Analysis of the Chaotic System
2.1.2. Parameter Space and Robust Chaos
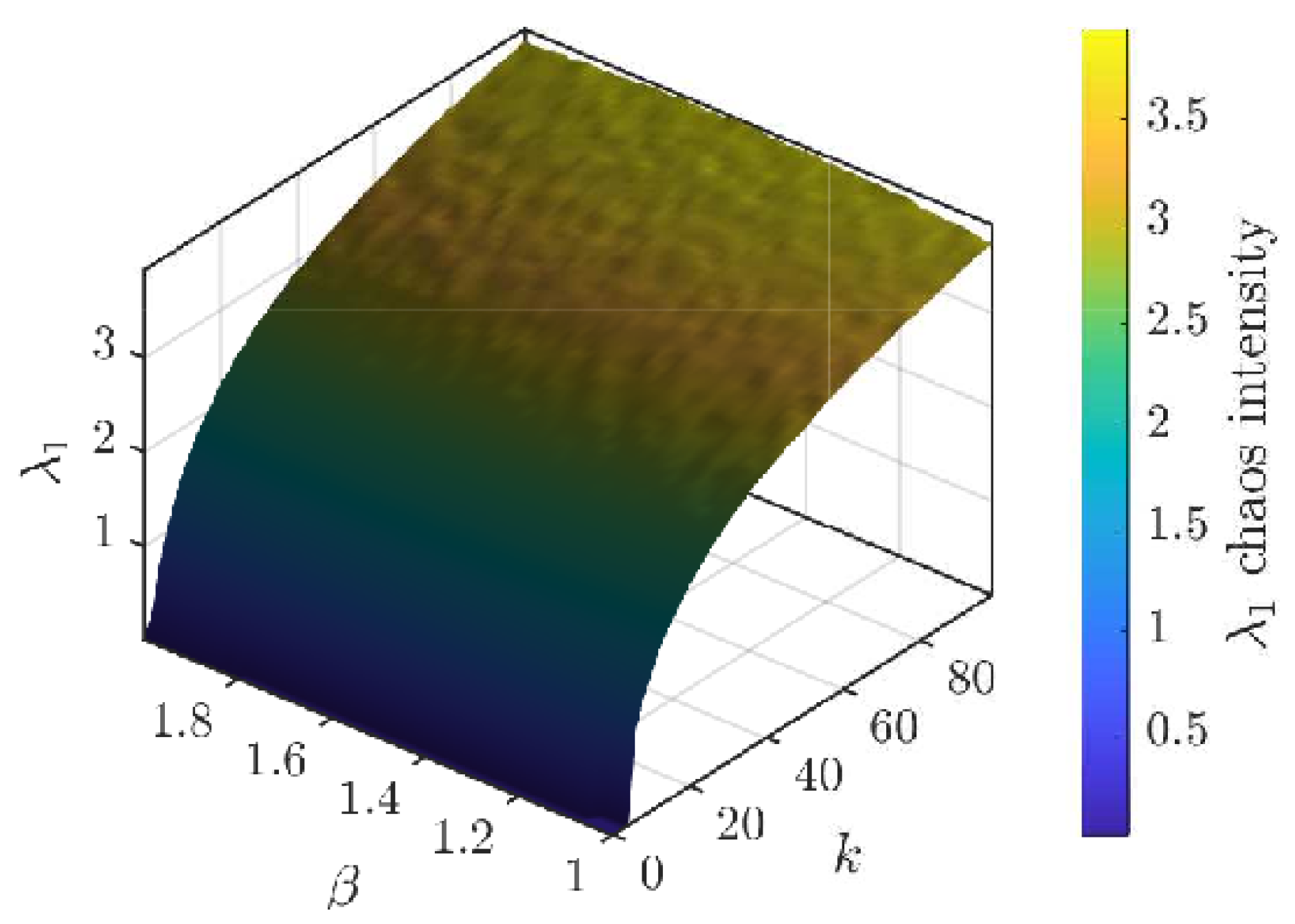
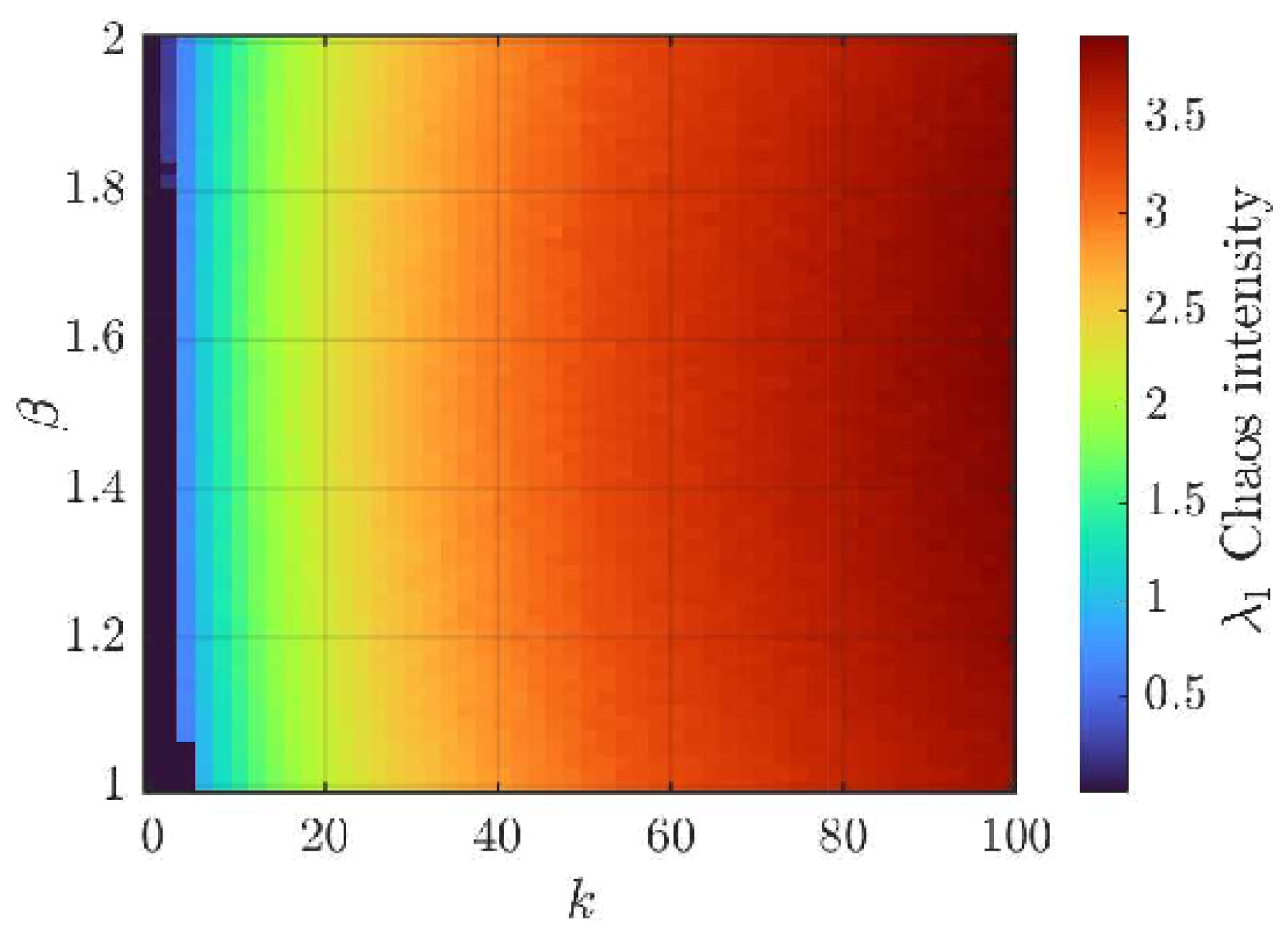
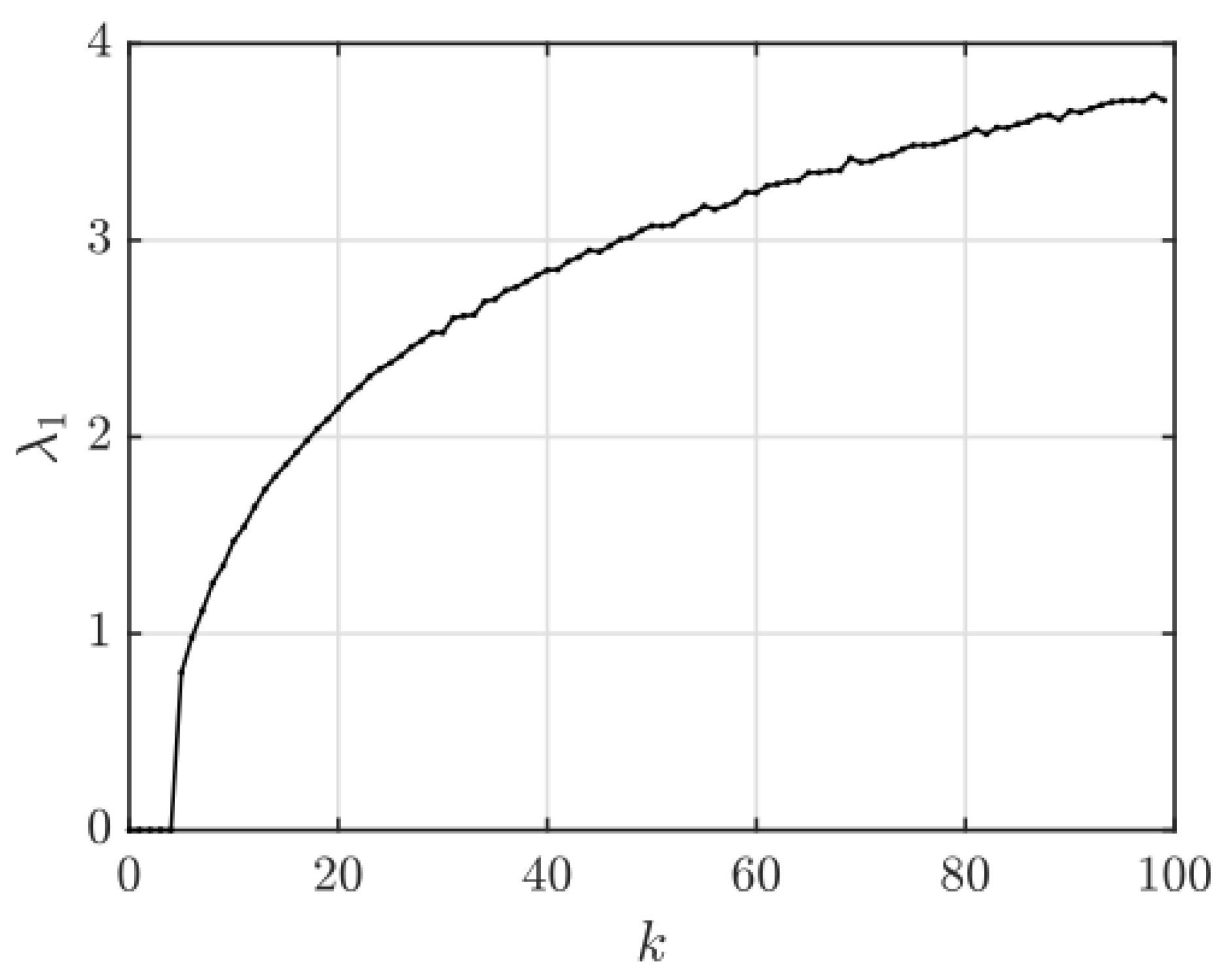
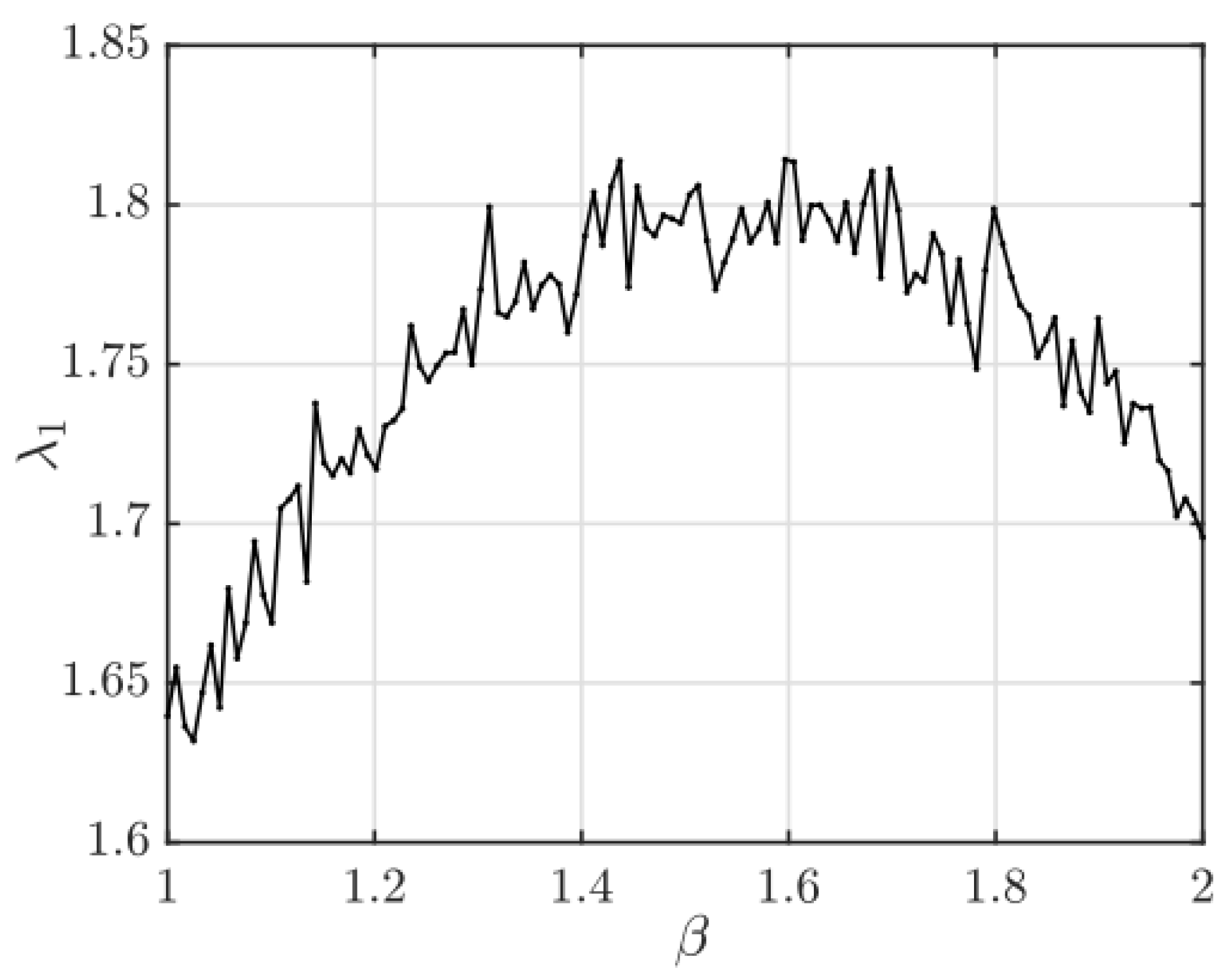
2.2. Generation of Encryption Chaotic Arrays
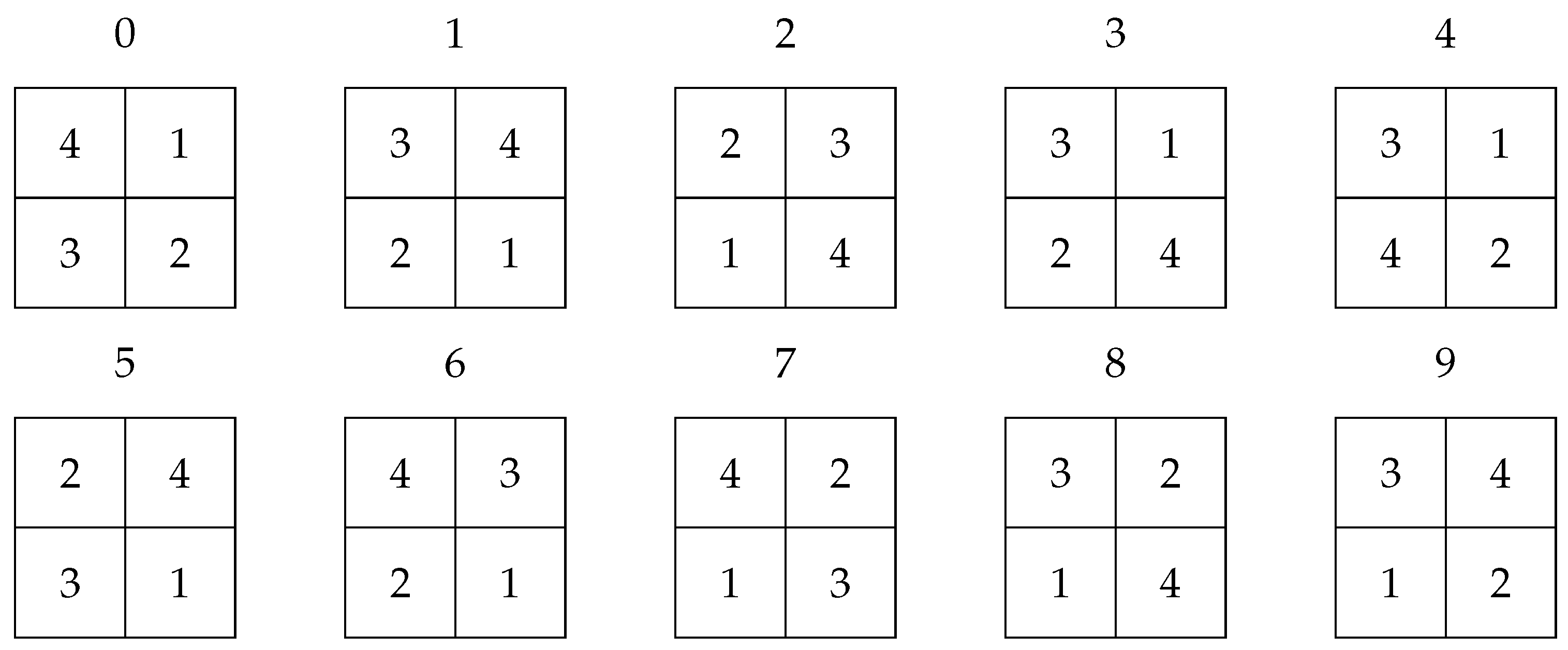
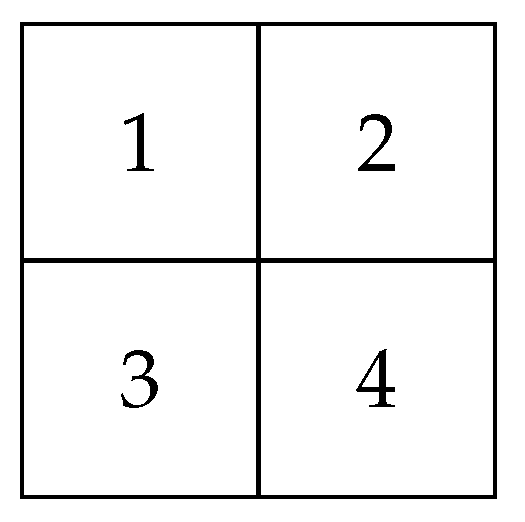
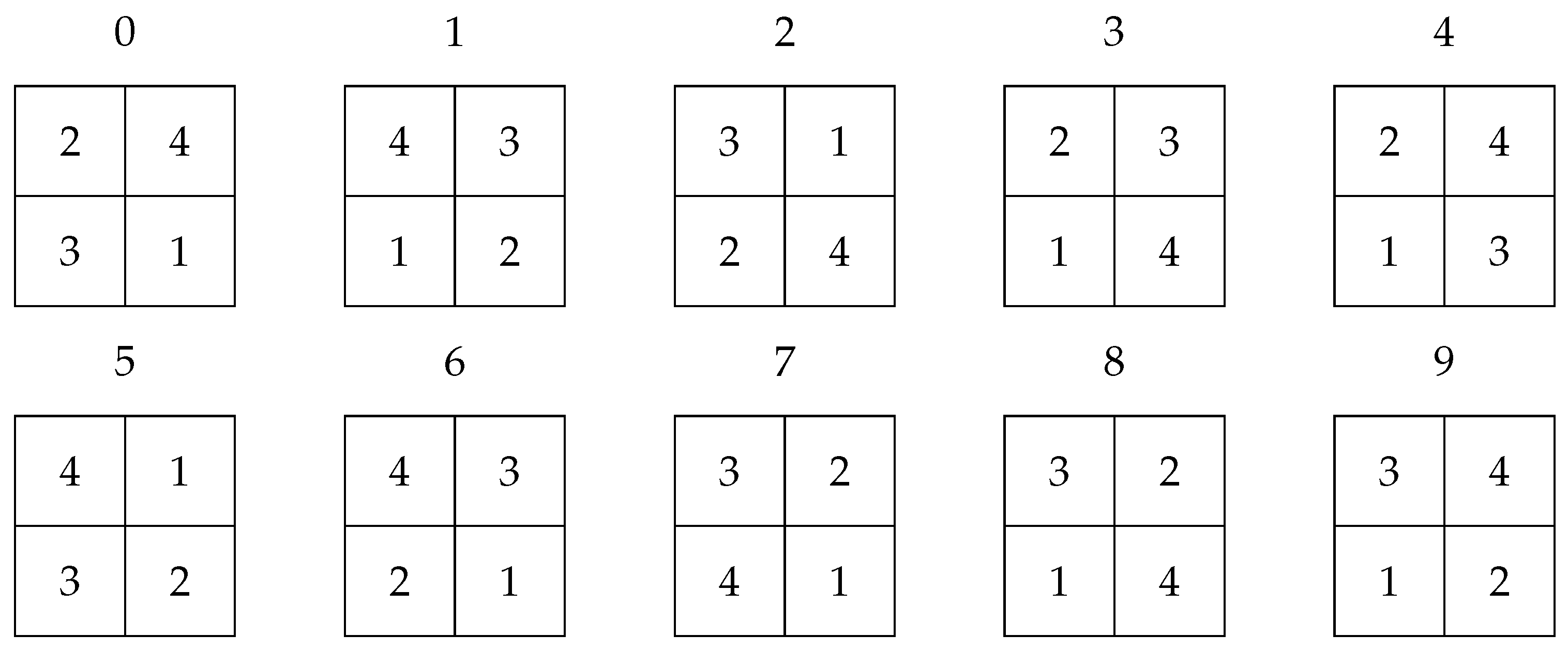
2.3. Mechanisms of Confusion and Diffusion
2.4. Decryption of Information
3. Results
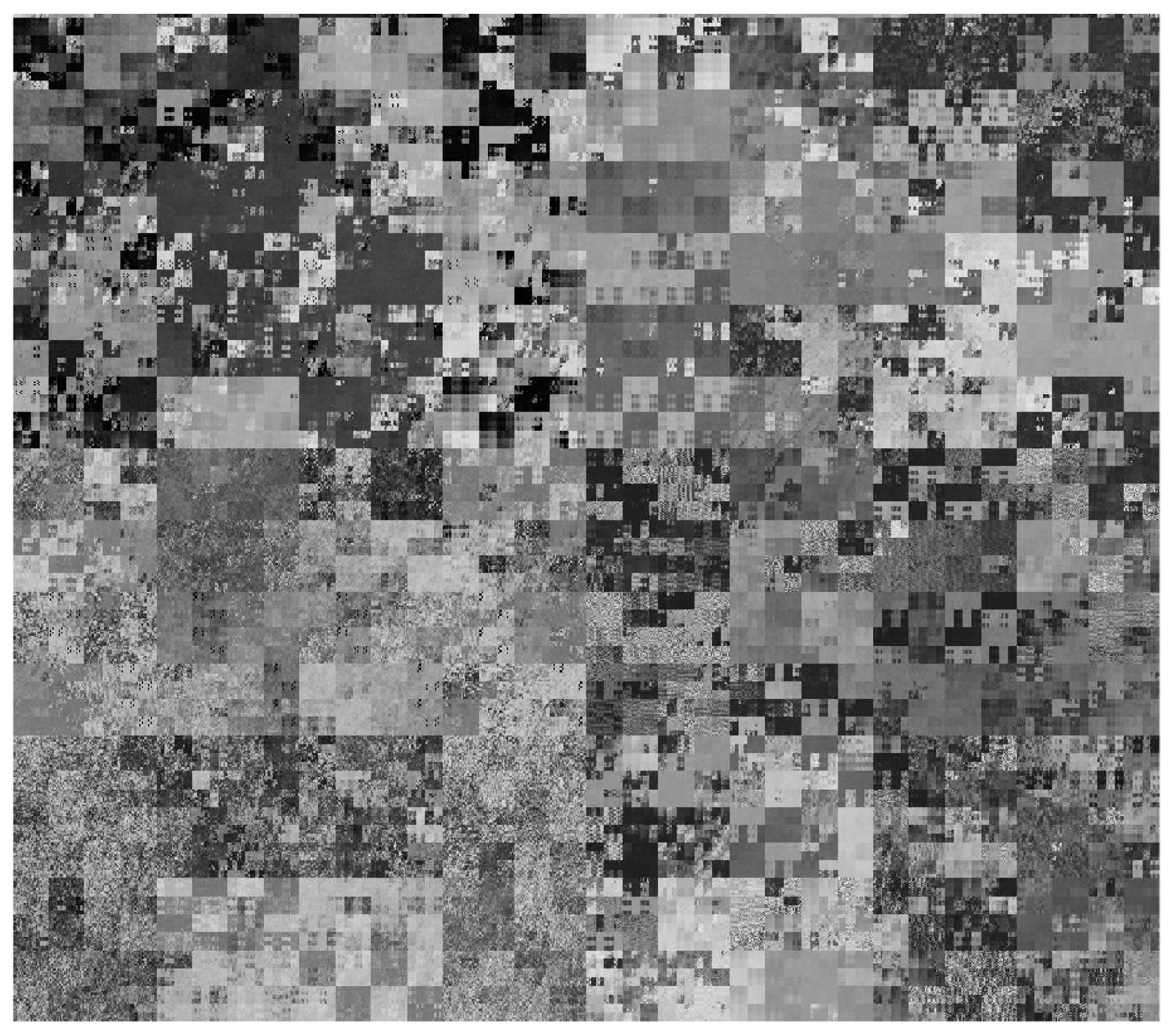
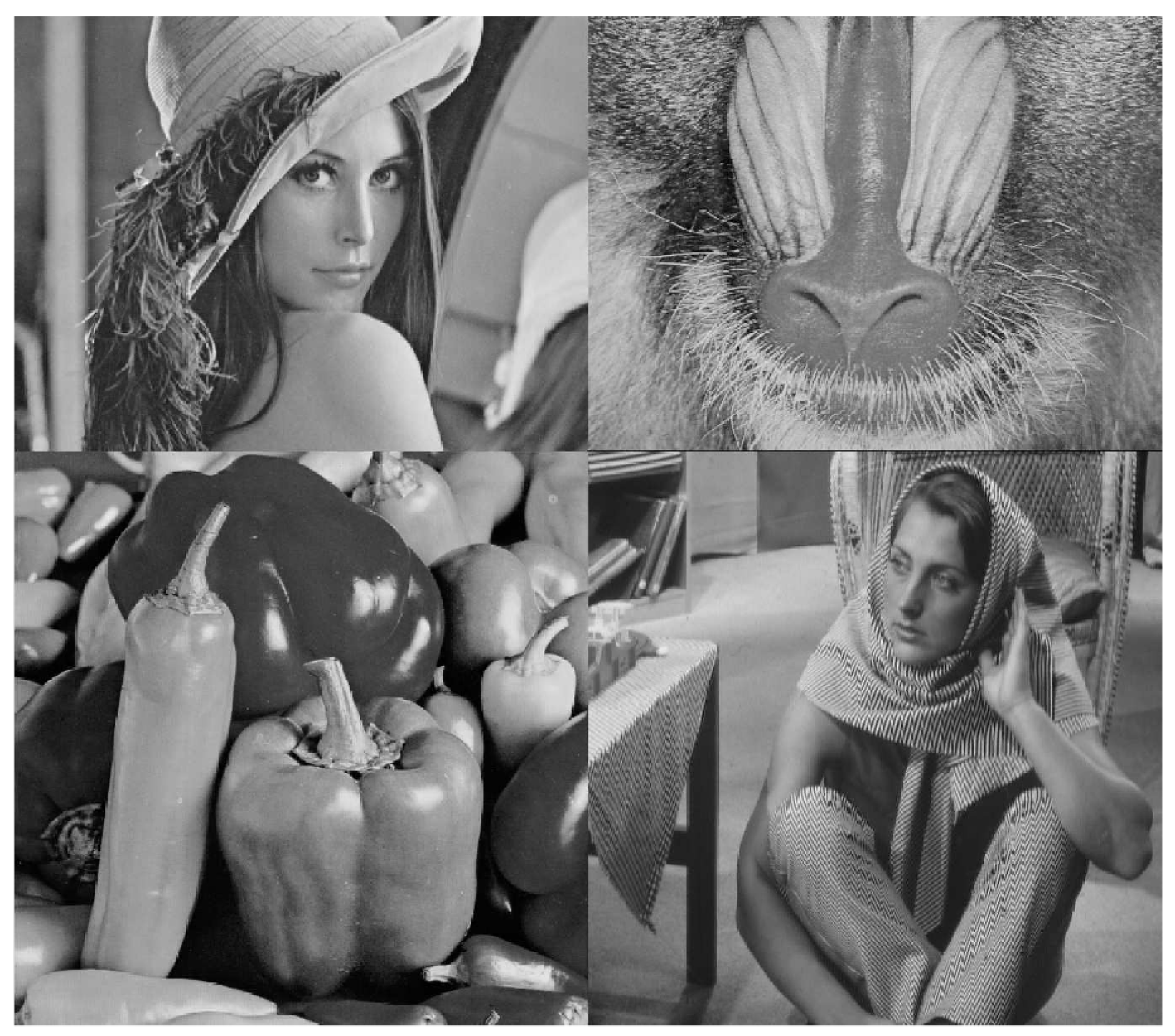
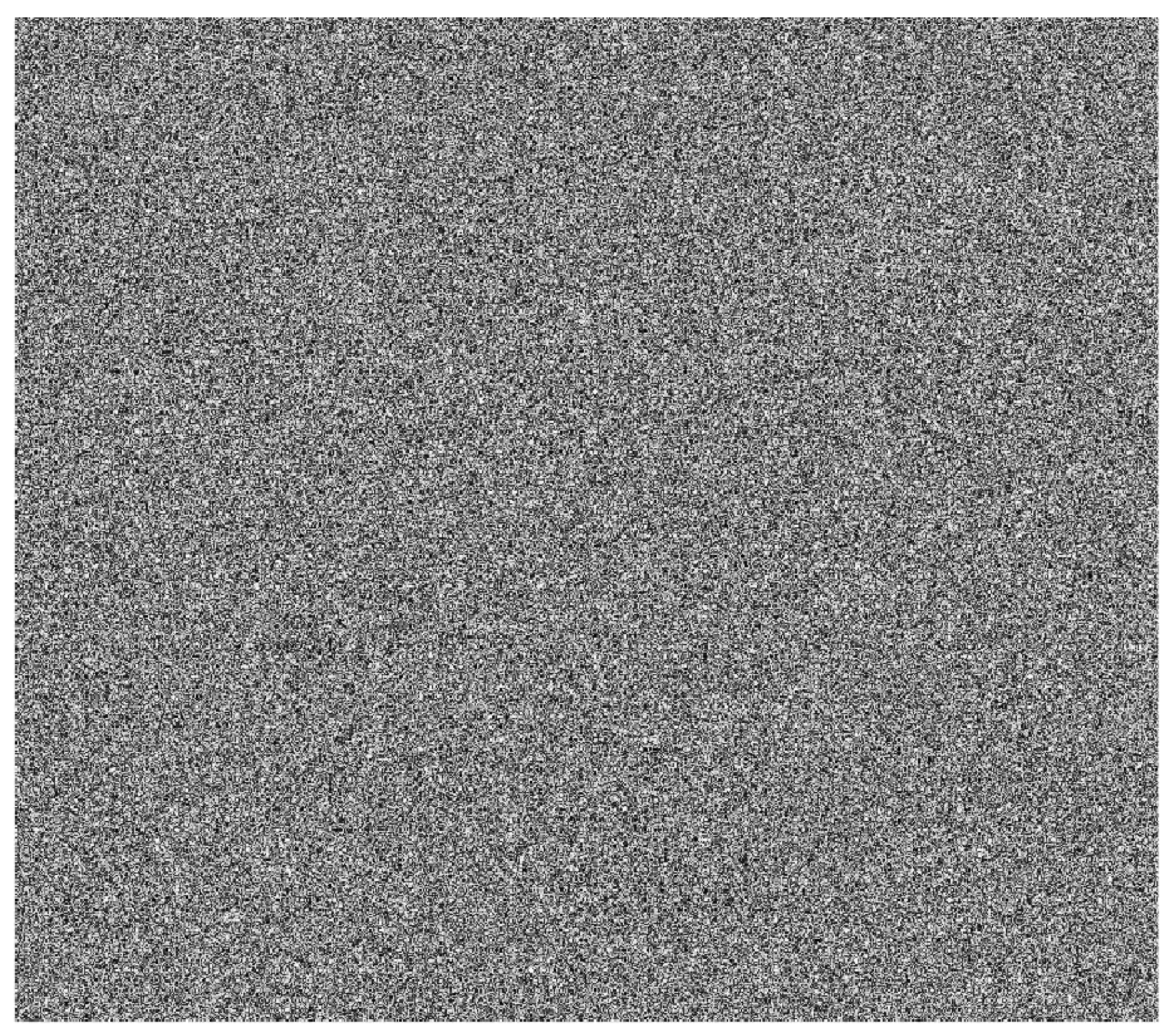
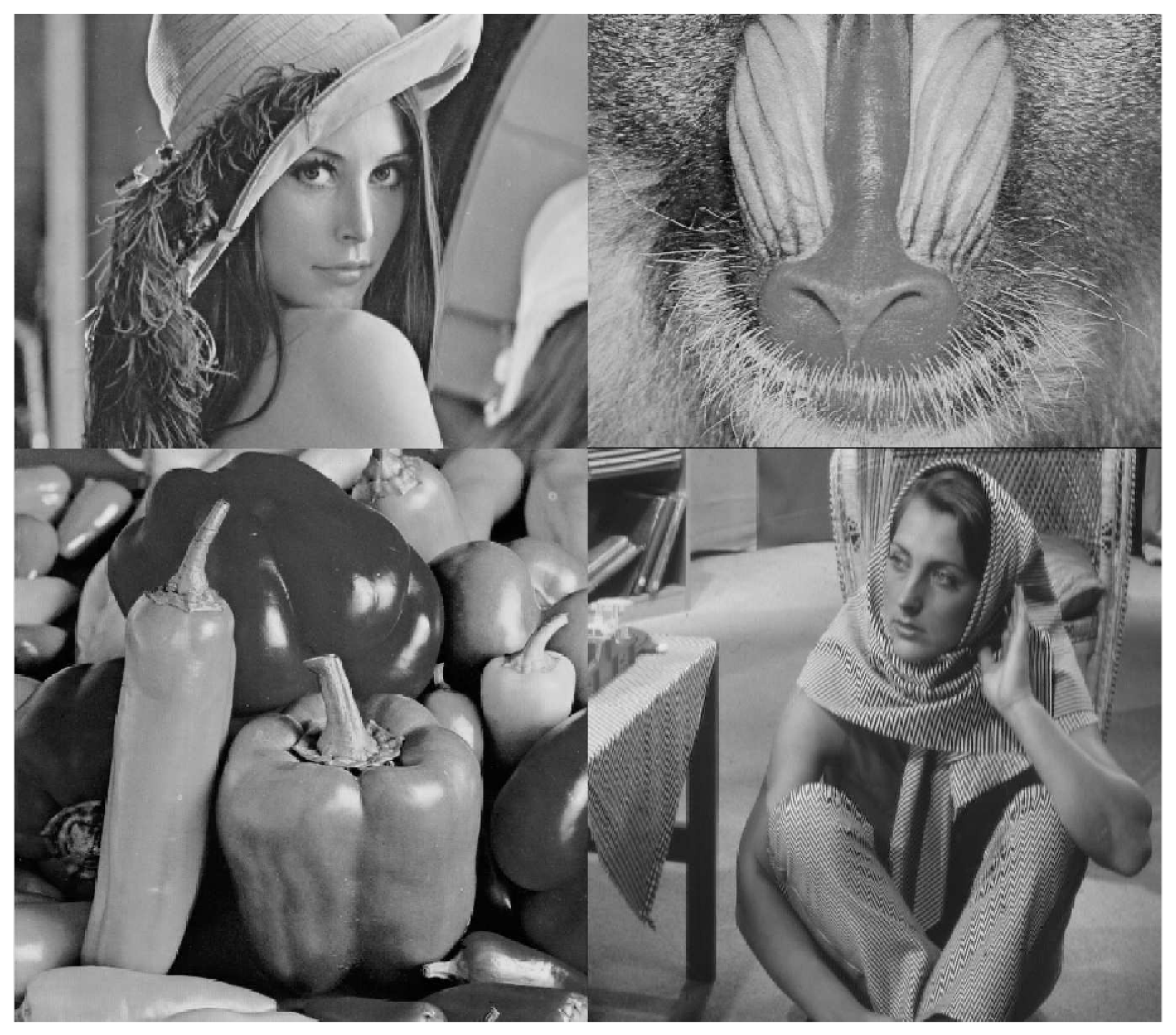
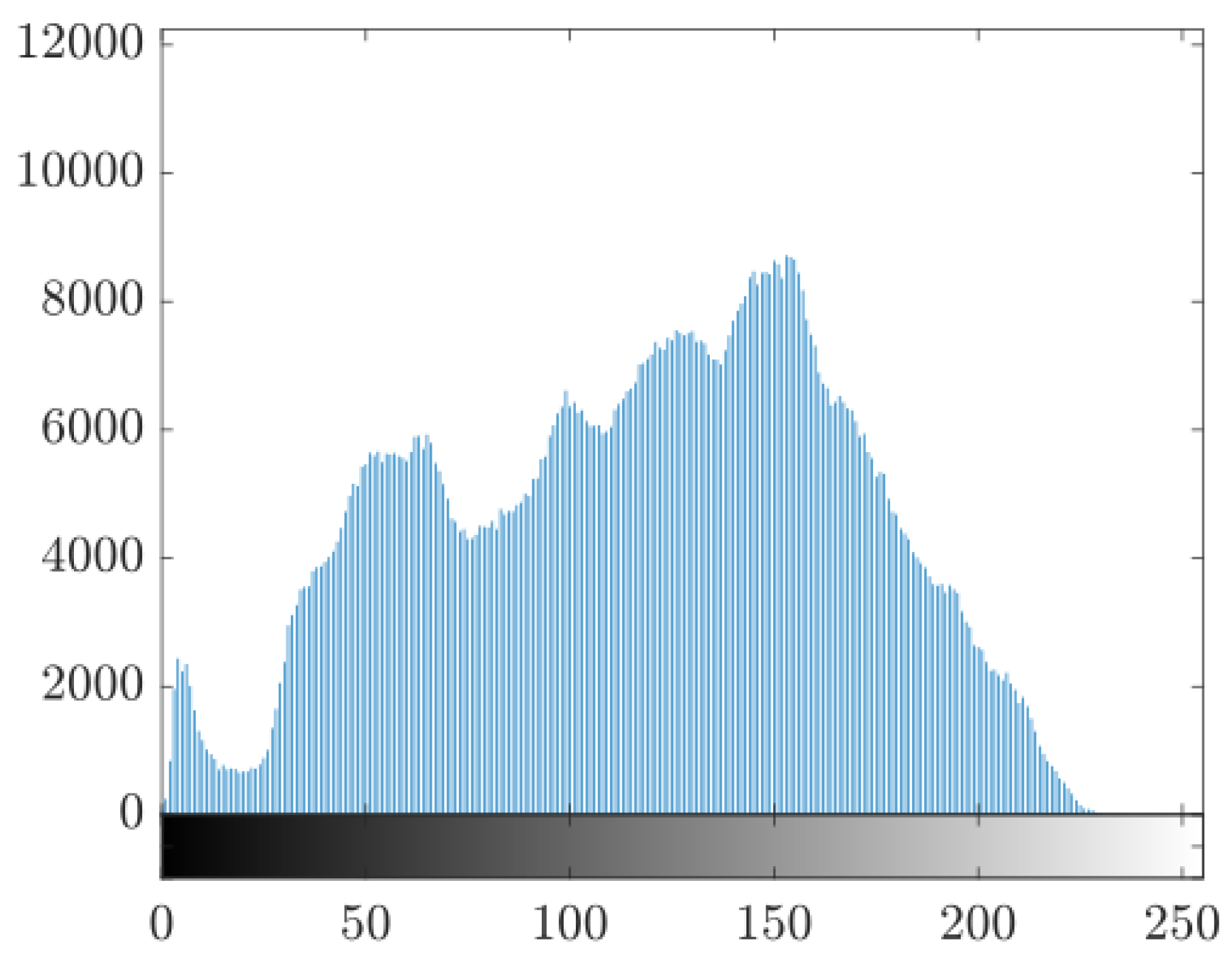
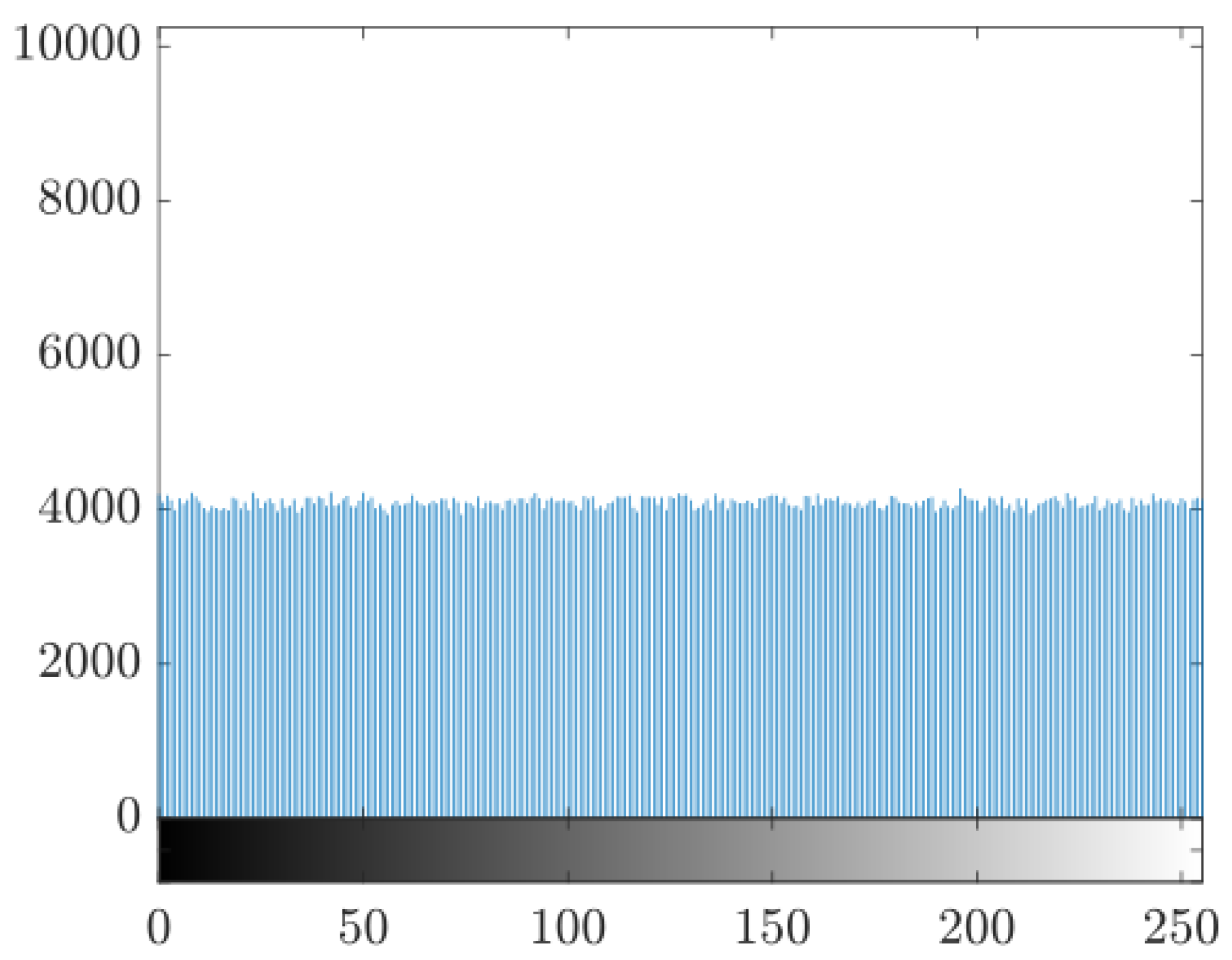
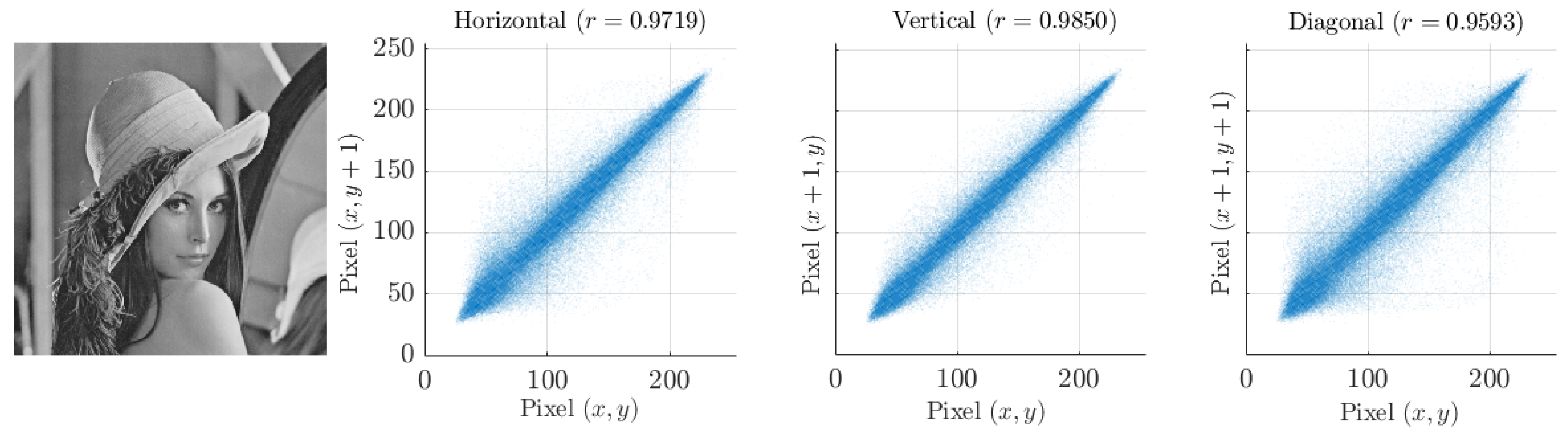
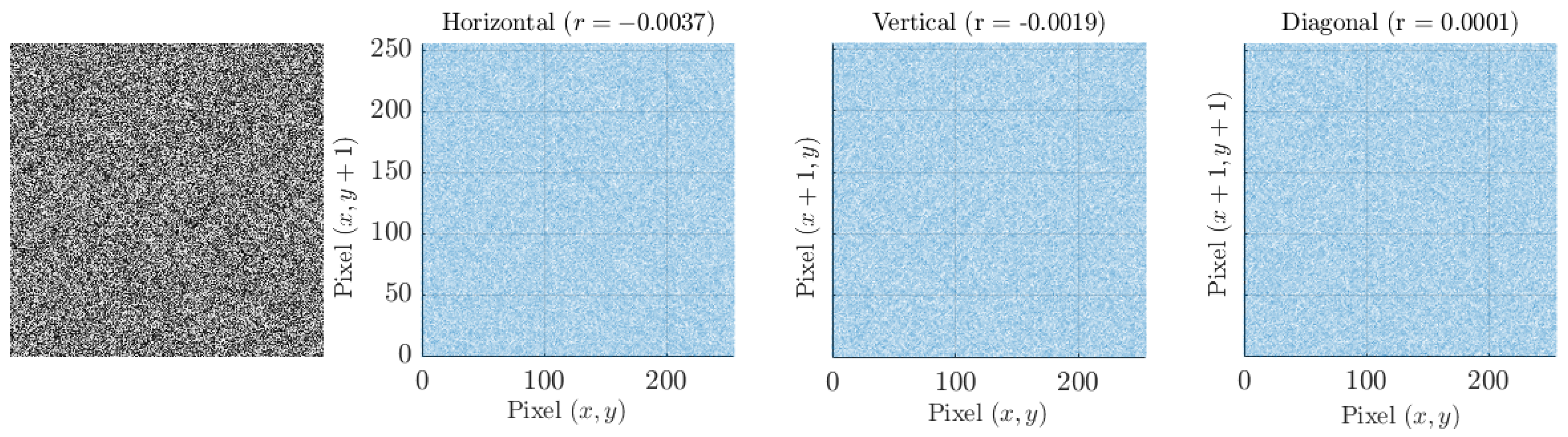
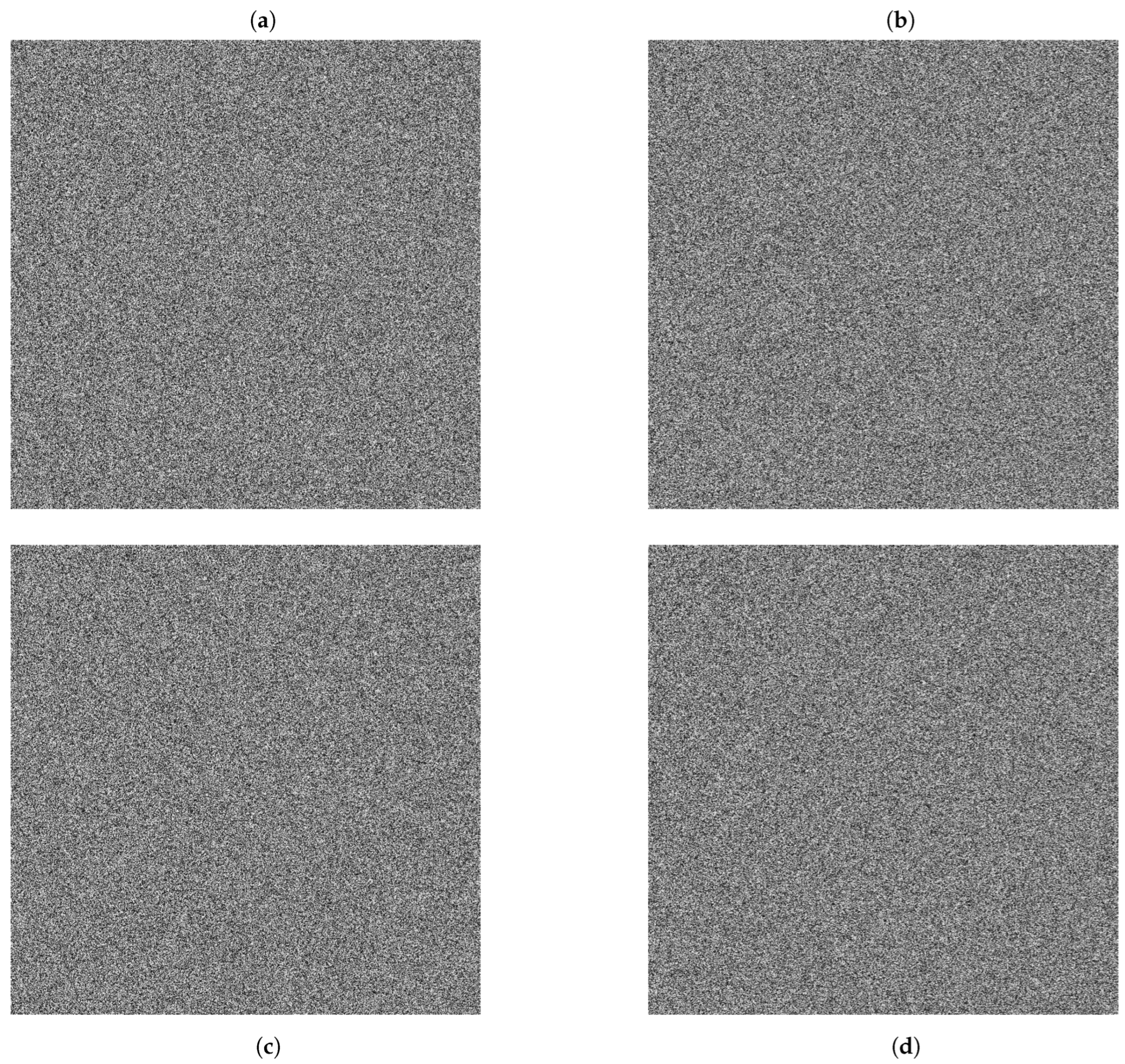
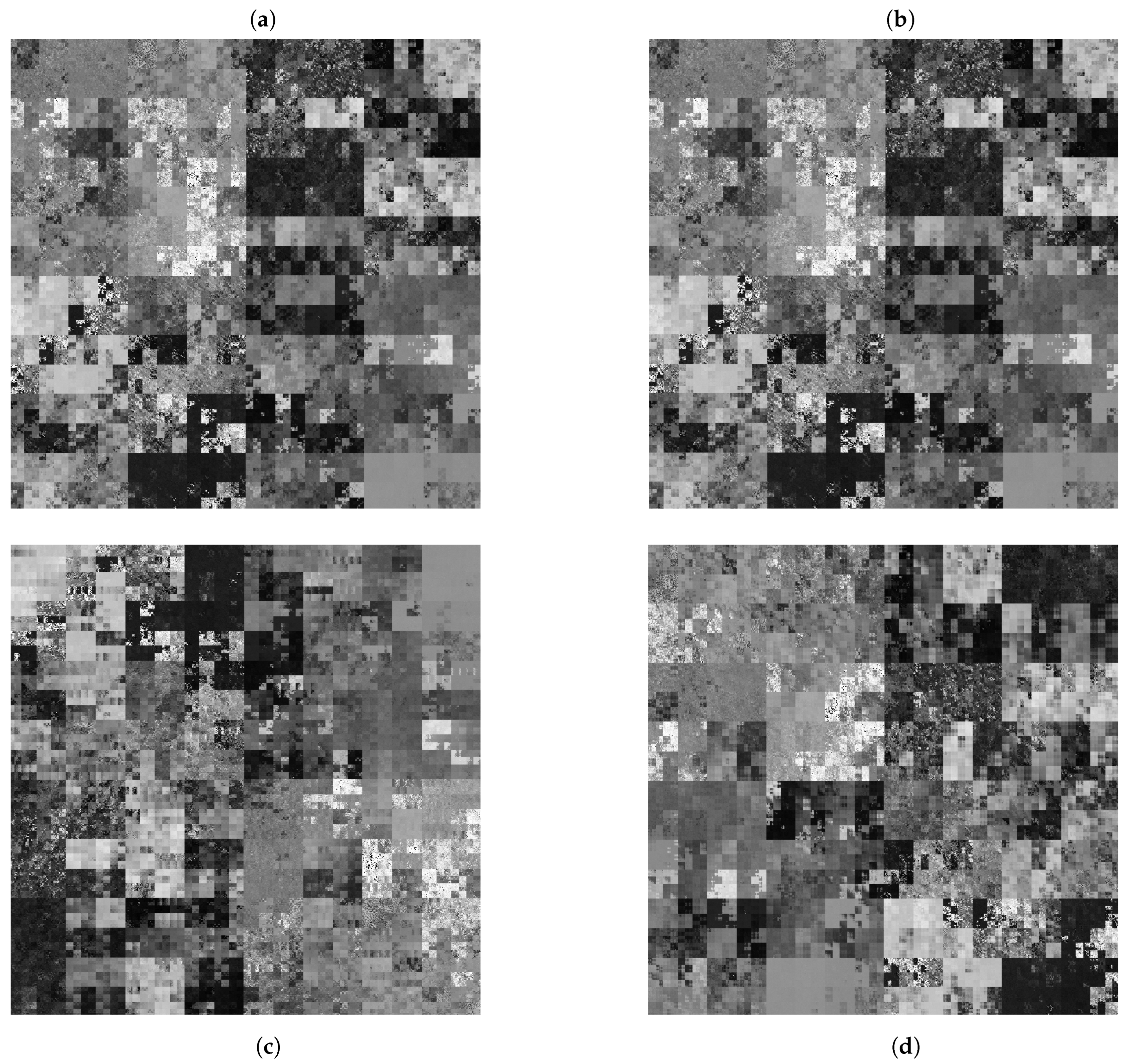
3.1. Encryption Features
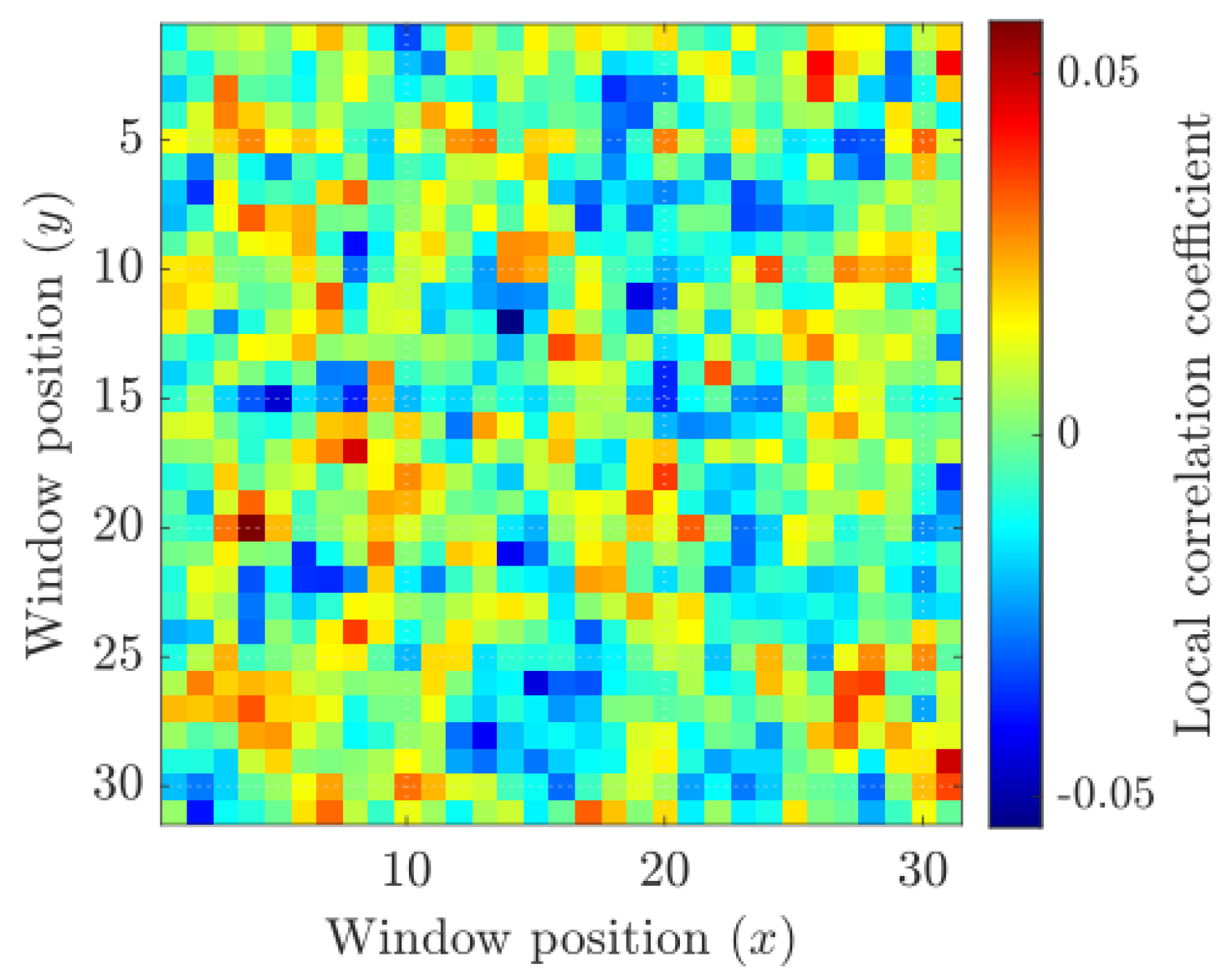
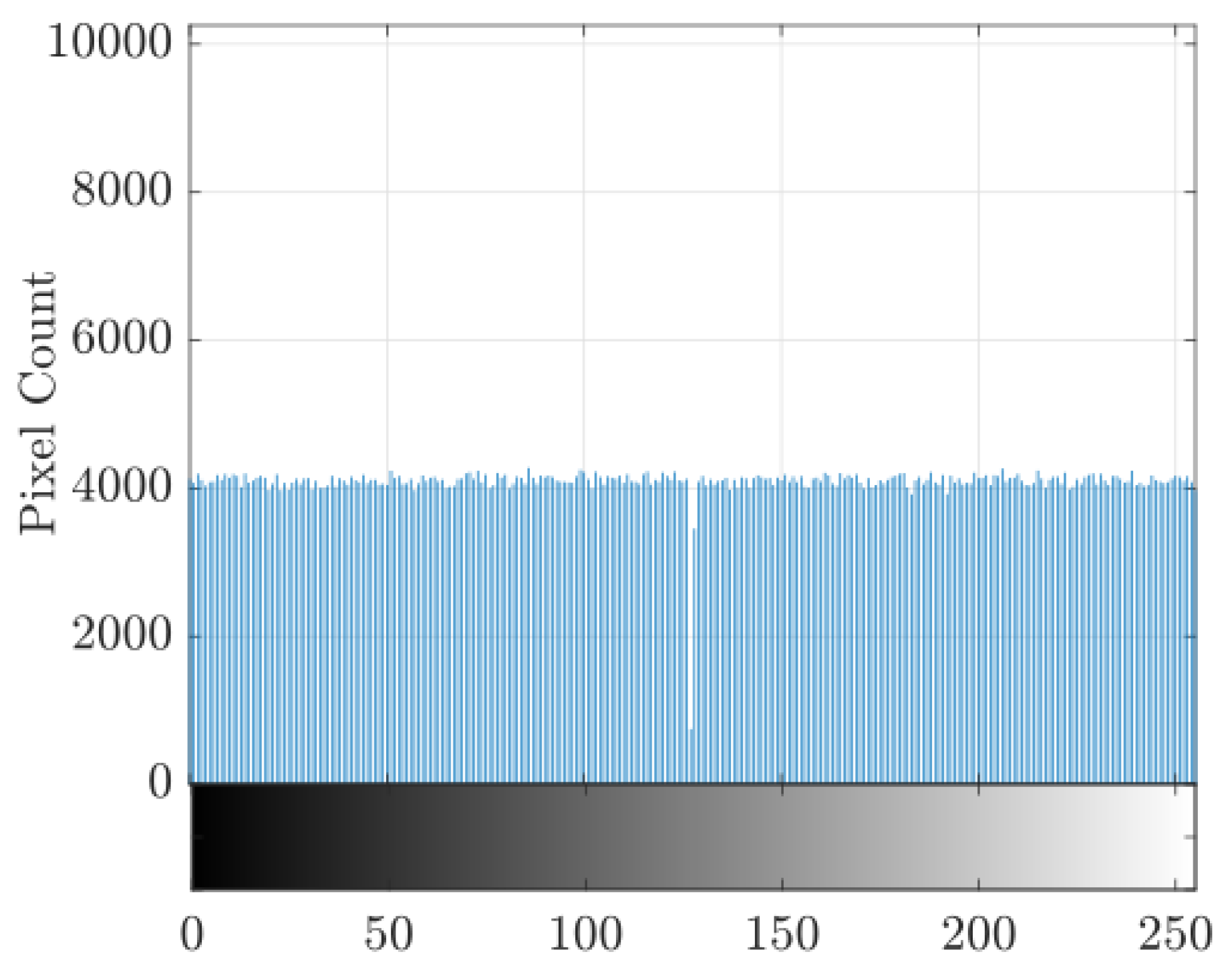
3.2. Cryptanalysis
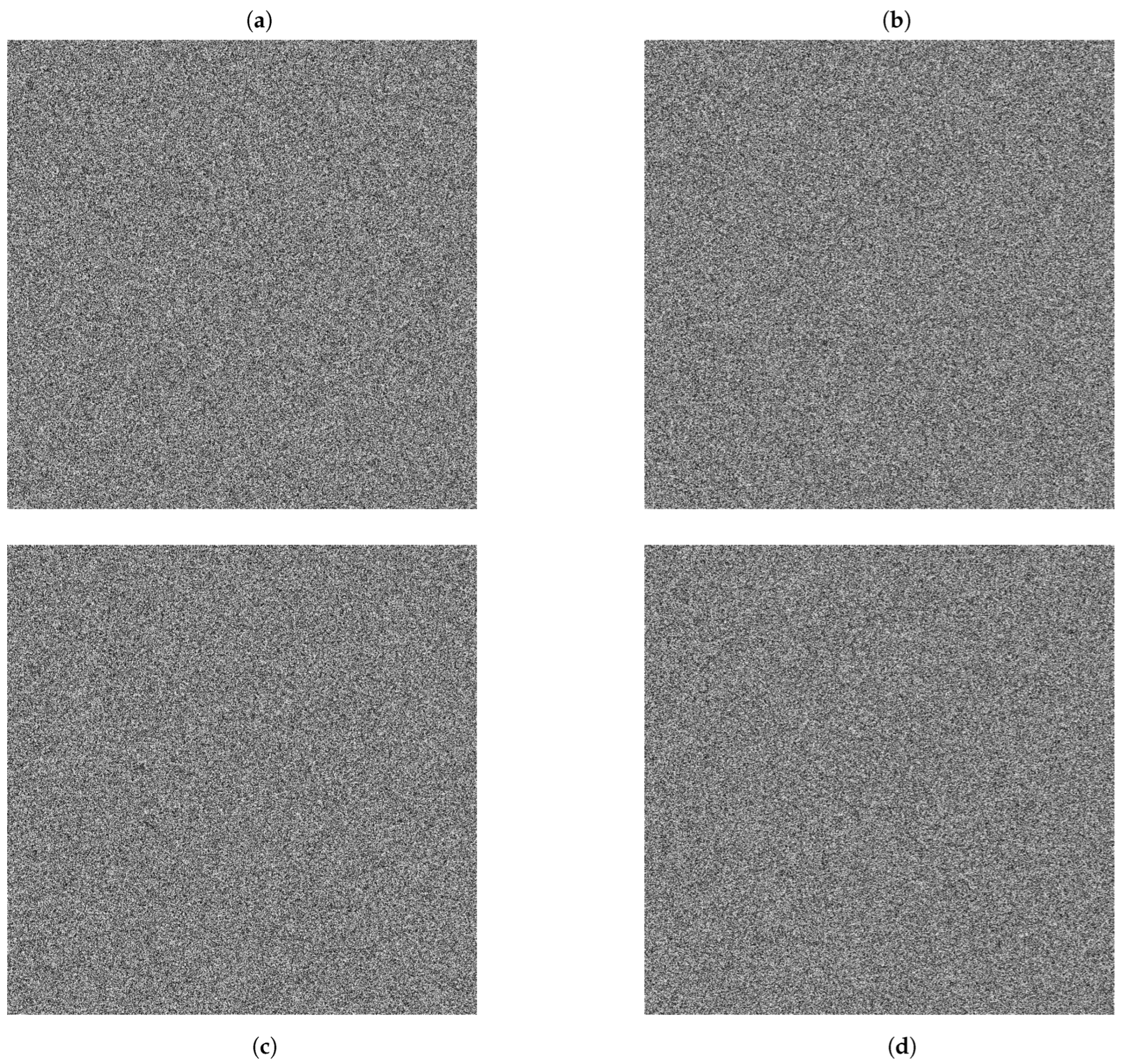
3.3. Sensitivity Test
3.3.1. Numerical Stability and Chaotic Dynamics
3.3.2. Key Security and Brute-Force Resistance
3.3.3. Resistance to Known-Plaintext and Chosen-Plaintext Attacks
3.3.4. Differential Attack and NPCR–UACI Metrics
4. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Use of Artificial Intelligence
Abbreviations
| KDF | Key Derivation Function |
| SSIM | Structural Similarity Index Measure |
| NPCR | Number of Pixels Change Rate |
| UACI | Unified Average Changing Intensity |
| GL | Gray Level |
| PP | Partition-permutation matrix |
References
- Alshahrani, A.A.; Jaha, E.S.; Alowidi, N. Fusion of Hash-Based Hard and Soft Biometrics for Enhancing Face Image Database Search and Retrieval. Computers, Materials and Continua 2023, 77, 3489–3509. [Google Scholar] [CrossRef]
- Yang, W.; Wang, S.; Cui, H.; Tang, Z.; Li, Y. A Review of Homomorphic Encryption for Privacy-Preserving Biometrics. Sensors número no especificado. 2023, 23. [Google Scholar] [CrossRef]
- Liu, J.; Wang, Y.; Wang, K.; Liu, Z. A Secure and Efficient Face Template Protection Scheme Based on Chaos. Journal of Information Security and Applications 2025, 93, 104111. [Google Scholar] [CrossRef]
- Al-Hyari, A.; Abu-Faraj, M.; Obimbo, C.; Alazab, M. Chaotic Hénon–Logistic Map Integration: A Powerful Approach for Safeguarding Digital Images. Journal of Cybersecurity and Privacy 2025, 5, 8. [Google Scholar] [CrossRef]
- Sirisha, U.; Chandana, B.S. Privacy Preserving Image Encryption with Optimal Deep Transfer Learning Based Accident Severity Classification Model. Sensors 2023, 23, 519. [Google Scholar] [CrossRef] [PubMed]
- Barik, K.; Misra, S.; Sanz, L.F.; Chockalingam, S. Enhancing Image Data Security Using the APFB Model. Connection Science 2024, 36, 2379275. [Google Scholar] [CrossRef]
- Tian, M.; Zhang, Y.; Zhang, Y.; Xiao, X.; Wen, W. A Privacy-Preserving Image Retrieval Scheme with Access Control Based on Searchable Encryption in Media Cloud. Cybersecurity 2024, 7, 213. [Google Scholar] [CrossRef]
- Khurana, N.; Dua, M. A Novel One-Dimensional Cosine within Sine Chaotic Map and Novel Permutation–Diffusion Based Medical Image Encryption. Nonlinear Dynamics 2025, 113, 4839–4859. [Google Scholar] [CrossRef]
- Mishra, P.; Bhaya, C.; Pal, A.K.; Singh, A.K. A Novel Binary Operator for Designing Medical and Natural Image Cryptosystems. Signal Processing: Image Communication 2021, 98, 116377. [Google Scholar] [CrossRef]
- Teng, L.; Wang, X.; Xian, Y. Image Encryption Algorithm Based on a 2D-CLSS Hyperchaotic Map Using Simultaneous Permutation and Diffusion. Information Sciences 2022, 605, 71–85. [Google Scholar] [CrossRef]
- Zhang, H.; Liu, X.; Chen, K.; Te, R.; Yan, F. Robust Image Encryption with 2D Hyperchaotic Map and Dynamic DNA-Zigzag Encoding. Entropy 2025, 27, 606. [Google Scholar] [CrossRef] [PubMed]
- Umar, T.; Nadeem, M.; Anwer, F. Chaos Based Image Encryption Scheme to Secure Sensitive Multimedia Content in Cloud Storage. Expert Systems with Applications 2024, 257, 125050. [Google Scholar] [CrossRef]
- Alexan, W.; Elbeltagy, M.; Aboshousha, A. RGB Image Encryption through Cellular Automata, S-Box and the Lorenz System. Symmetry 2022, 14, 443. [Google Scholar] [CrossRef]
- Safdar, M.U.; Shah, T.; Ali, A. Multiple-Image Encryption Algorithm Based on S-Boxes and DNA Sequences. Signal Processing: Image Communication 2025, 138, 117353. [Google Scholar] [CrossRef]
- Cui, G.; Zhou, X.; Wang, H.; Hao, W.; Zhou, A.; Ma, J. Optical Color Image Encryption Algorithm Based on Two-Dimensional Quantum Walking. Electronics 2024, 13, 2026. [Google Scholar] [CrossRef]
- Tian, P.; Su, R. A Novel Virtual Optical Image Encryption Scheme Created by Combining Chaotic S-Box with Double Random Phase Encoding. Sensors 2022, 22, 5325. [Google Scholar] [CrossRef]
- Li, X.; Peng, H. Chaotic Medical Image Encryption Method Using Attention Mechanism Fusion ResNet Model. Frontiers in Neuroscience 2023, 17, 1226154. [Google Scholar] [CrossRef]
- Feng, L.; Du, J.; Fu, C.; Song, W. Image Encryption Algorithm Combining Chaotic Image Encryption and Convolutional Neural Network. Electronics 2023, 12, 3455. [Google Scholar] [CrossRef]
- Abdullaev, S. S. Canonical Stochastic Web Map. Physical Review E 2007, 76, 026216. [Google Scholar] [CrossRef]
- Carvalho, A.R.R.; de Matos Filho, R.L.; Davidovich, L. Environmental Effects in the Quantum-Classical Transition for the Delta-Kicked Harmonic Oscillator. Physical Review E 2004, 70, 026211. [Google Scholar] [CrossRef]
- Dieci, L.; Van Vleck, E.S. Computation of a Few Lyapunov Exponents for Continuous and Discrete Dynamical Systems. Applied Numerical Mathematics 1995, 17, 275–291. [Google Scholar] [CrossRef]
- De La Fontaine, X. Image Encryption Real Plane 01: Source Code and Dataset. GitHub repository. 2024. Available online: https://github.com/xavierdelafontaine-boop/Image_Encryption_Real_Plane_01 (accessed on 27 November 2025).
- Abusham, E.; Ibrahim, B.; Zia, K.; Rehman, M. Facial Image Encryption for Secure Face Recognition System. Electronics 2023, 12, 774. [Google Scholar] [CrossRef]
- Naik, R.B.; Singh, U. A Review on Applications of Chaotic Maps in Pseudo-Random Number Generators and Encryption. Annals of Data Science 2024, 11, 25–50. [Google Scholar] [CrossRef]
- Rahul, B.; Kuppusamy, K.; Senthilrajan, A. Dynamic DNA Cryptography-Based Image Encryption Scheme Using Multiple Chaotic Maps and SHA-256 Hash Function. Optik 2023, 289, 171253. [Google Scholar] [CrossRef]
- Shafique, A.; Mehmood, A.; Alawida, M.; Khan, A.N. Enhancing Privacy in Data Transmission between IoT Devices: A Robust Encryption and Embedding Framework for Secure and Meaningful Image Communication. Journal of Information Security and Applications 2025, 93, 104112. [Google Scholar] [CrossRef]
- Zhang, B.; Liu, L. Chaos-Based Image Encryption: Review, Application, and Challenges. Mathematics número no especificado. 2023, 11. [Google Scholar] [CrossRef]
- Zhang, W.; Xu, J.; Zhao, B. DNA Image Encryption Algorithm Based on Serrated Spiral Scrambling and Cross Bit Plane. Journal of King Saud University - Computer and Information Sciences 2023, 35, 101858. [Google Scholar] [CrossRef]
- Zhang, J.; Guo, J.; Lu, D. An Efficient Image Encryption Algorithm Based on S-Box and DNA Code. Measurement: Sensors 2023, 29, 100894. [Google Scholar] [CrossRef]
| 3 | 3 | 9 | 7 | 0 | 5 | 8 | 7 | 1 | 3 | 6 | 6 | 1 | 3 | 2 | 3 |
| 4 | 1 | 3 | 3 | 9 | 7 | 9 | 7 | 6 | 0 | 2 | 7 | 3 | 3 | 7 | 6 |
| Trial | ||
| 1 | 99.5981 | 33.3347 |
| 2 | 99.6030 | 33.4018 |
| 3 | 99.6139 | 33.4298 |
| 4 | 99.6036 | 33.4103 |
| 5 | 99.6072 | 35.7299 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




