Submitted:
10 December 2025
Posted:
11 December 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
- •
- We propose 5G-DAuth, a cross-domain 5G NF service authorization scheme based on a consortium blockchain and off-chain TEE. Our scheme constructs the consortium blockchain for NF communication between multiple PLMNs, utilizing smart contracts to provide NF management and service authorization, thereby addressing the single point of failure of NRF.
- •
- We design an off-chain TEE based on Intel SGX to reduce block synchronization waiting time, enhance the computational efficiency of smart contracts, and ensure security and privacy for both smart contracts and on-chain data.
- •
- We conduct serious security analysis and performance evaluation on 5G-DAuth to demonstrate that it meets security and privacy protection requirements while offering certain performance advantages.
2. Related Work
2.1. Token-Based Service Authorization and Access Control
2.2. Identity-Based Service Authorization and Access Control
3. Problem Statements
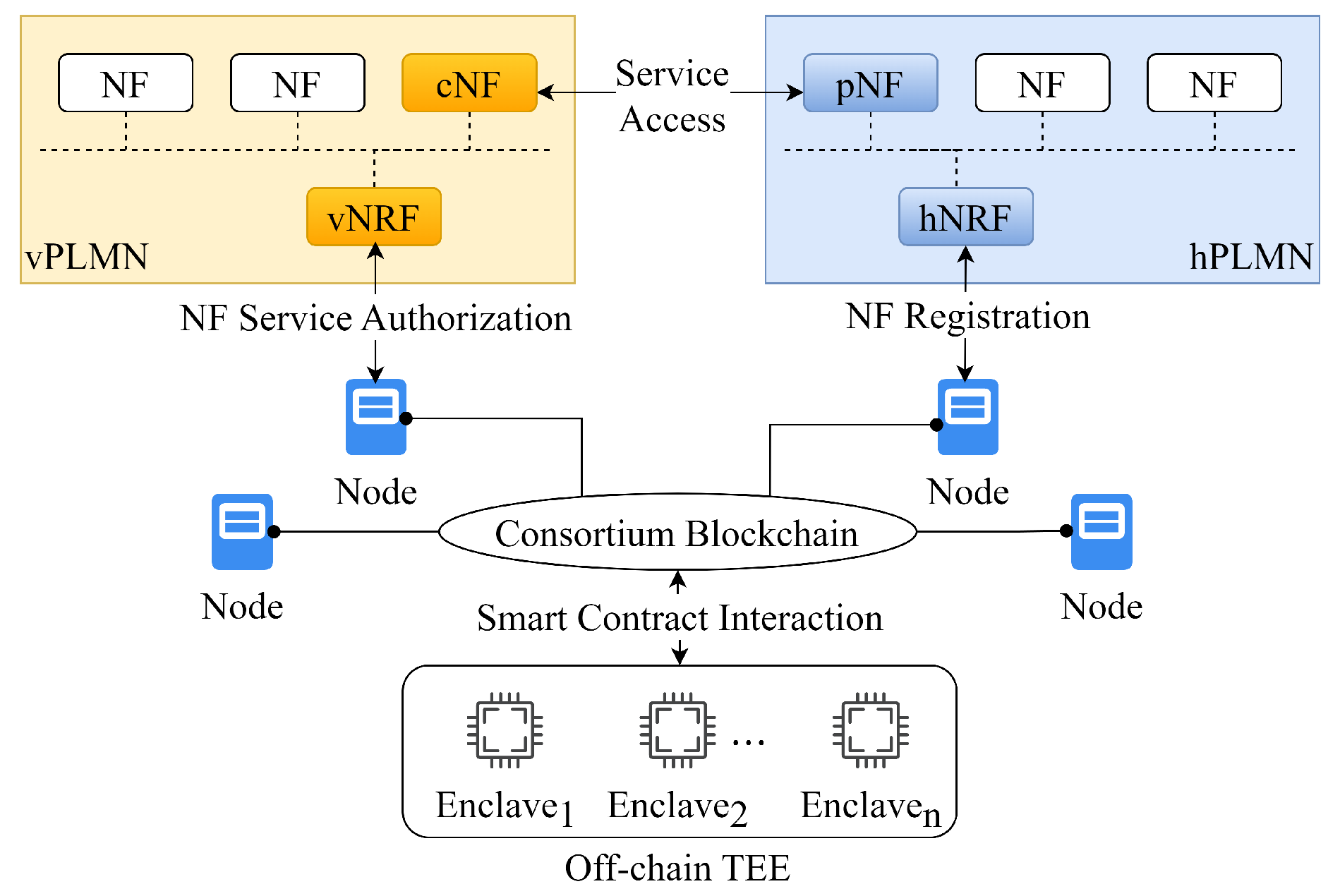
3.1. System Model
- •
- NF is the network function that provides various network services. Before it can offer services, the NF must first register with the NRF. NFs can be categorized as either Network Functions consumer (cNF) in a vPLMN or Network Functions provider (pNF) in hPLMN during a service invocation. To ensure that the invocation between different NFs is credible, the cNF requires service authorization from the NRF and must adhere to the access control set by the pNF. NFs communicate with one another through Service-Based Interfaces defined within the core network.
- •
- NRF handles registration and authorization requests from NFs, functioning as a client for the consortium blockchain. It initiates transactions and invokes smart contracts with the blockchain nodes. In 3GPP specifications [6], NRF serves as a central server for NF management. In the 5G-DAuth system, to reduce the risk of a single point of failure, most functions of the NRF are transferred to a consortium blockchain and smart contracts. The NRF operates as a blockchain client, initiating service requests and invoking the relevant smart contracts.
- •
- The consortium blockchain is responsible for processing smart contract invocation requests related to the registration, management, and authorization of NRFs in PLMNs. It selects a group of Enclaves from the off-chain TEE pool to execute the corresponding smart contracts. Each PLMN can establish multiple nodes on the consortium blockchain. These nodes receive smart contract invocations from the NRFs and respond with the execution outcomes. A management smart contract, referred to as M, is deployed on the consortium blockchain to oversee the lifecycle of the Enclaves within the TEE pool. This contract M is responsible for creating the Enclaves for smart contract execution, instantiating the smart contracts, and logging the status of the Enclaves on the consortium blockchain. Any PLMN that connects to the consortium blockchain can access the on-chain ledger to view the status of enclaves and the smart contracts deployed within those enclaves. We design three essential contracts, namely the NF management contract, service authorization contract, and service subscription contract.
- •
- The off-chain TEE pool selects an enclave as an Executor and initializes and executes smart contracts within the Executor. In the 5G-DAuth, TEE is deployed outside the consortium blockchain, while smart contracts are executed within the off-chain enclaves. By this design, 5G-DAuth provides a reliable and efficient computation and storage environment for smart contract and NF data. The Executor receives smart contract execution requests from the consortium blockchain nodes and executes the smart contract code within a protected memory area. This ensures the security of the smart contract code and prevents attackers from eavesdropping on and stealing data during code execution. The Enclaves utilize the sealing mechanism to encrypt and store data on the consortium blockchain and interact with the blockchain to achieve state synchronization. To ensure the availability of the off-chain TEE pool, we learn a resilience scheme from POSE [13]. Before executing a smart contract, two additional enclaves known as Monitors are chosen to oversee the executor’s operational status. If the Executor does not return results within a specified time, the Monitors initiate an inquiry mechanism to question the executor or switch to another available Executor.
3.2. Security Model
4. 5D-DAuth Design
4.1. 5G-DAuth Overview
4.2. System Setup
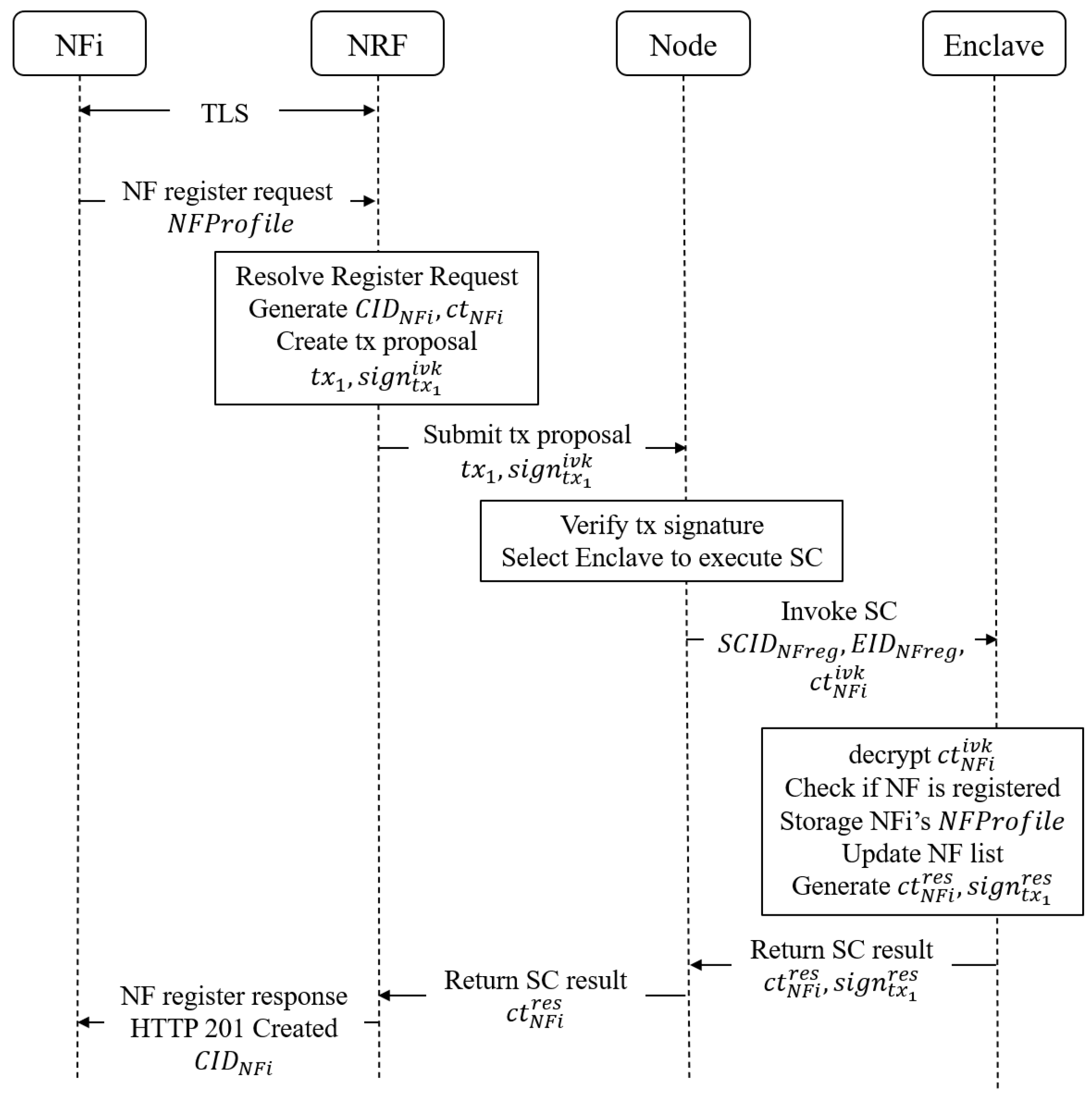
4.3. NF Management
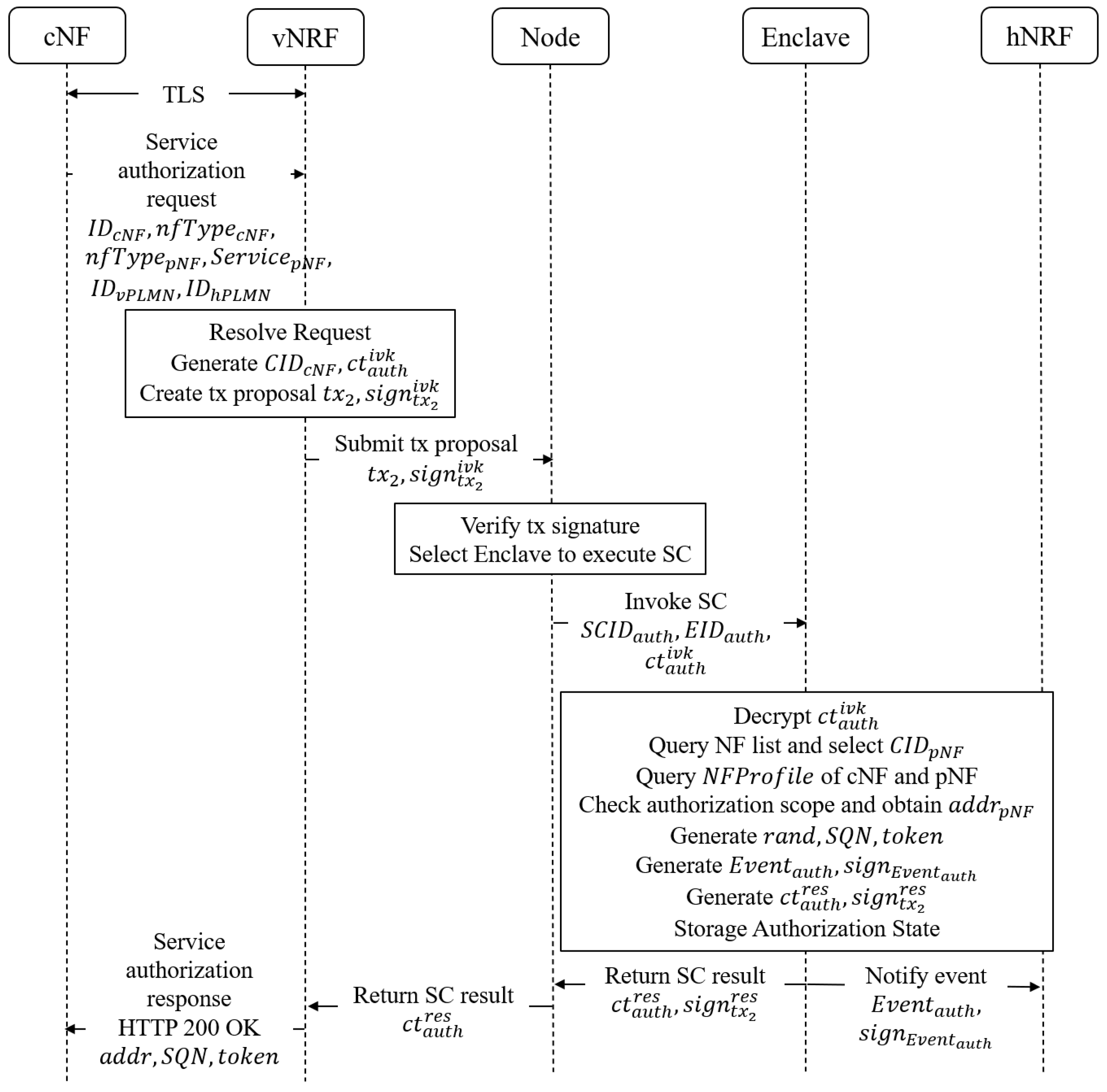
4.4. Service Authorization
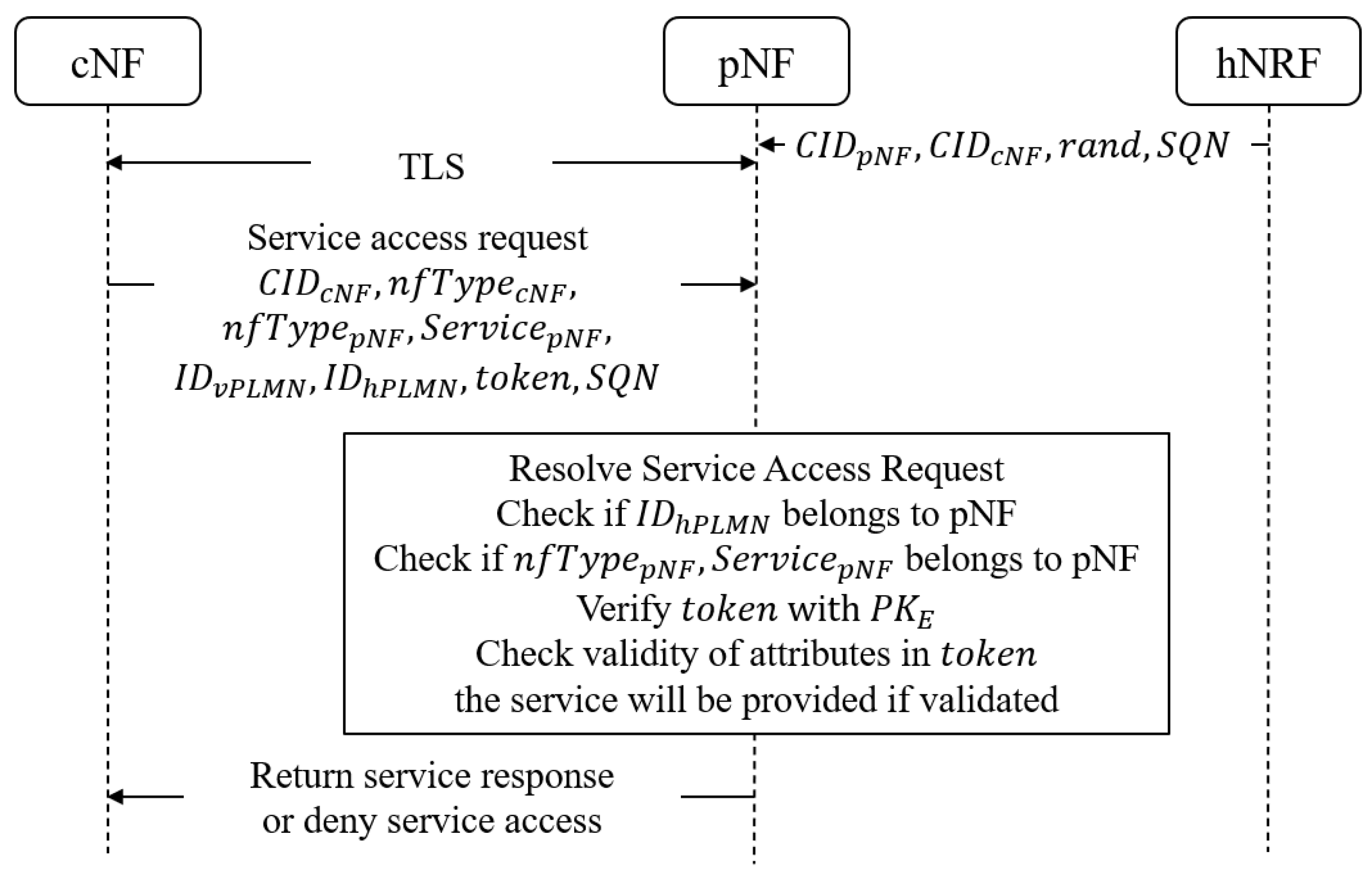
4.5. Service Access
5. Security and Performance Evaluation
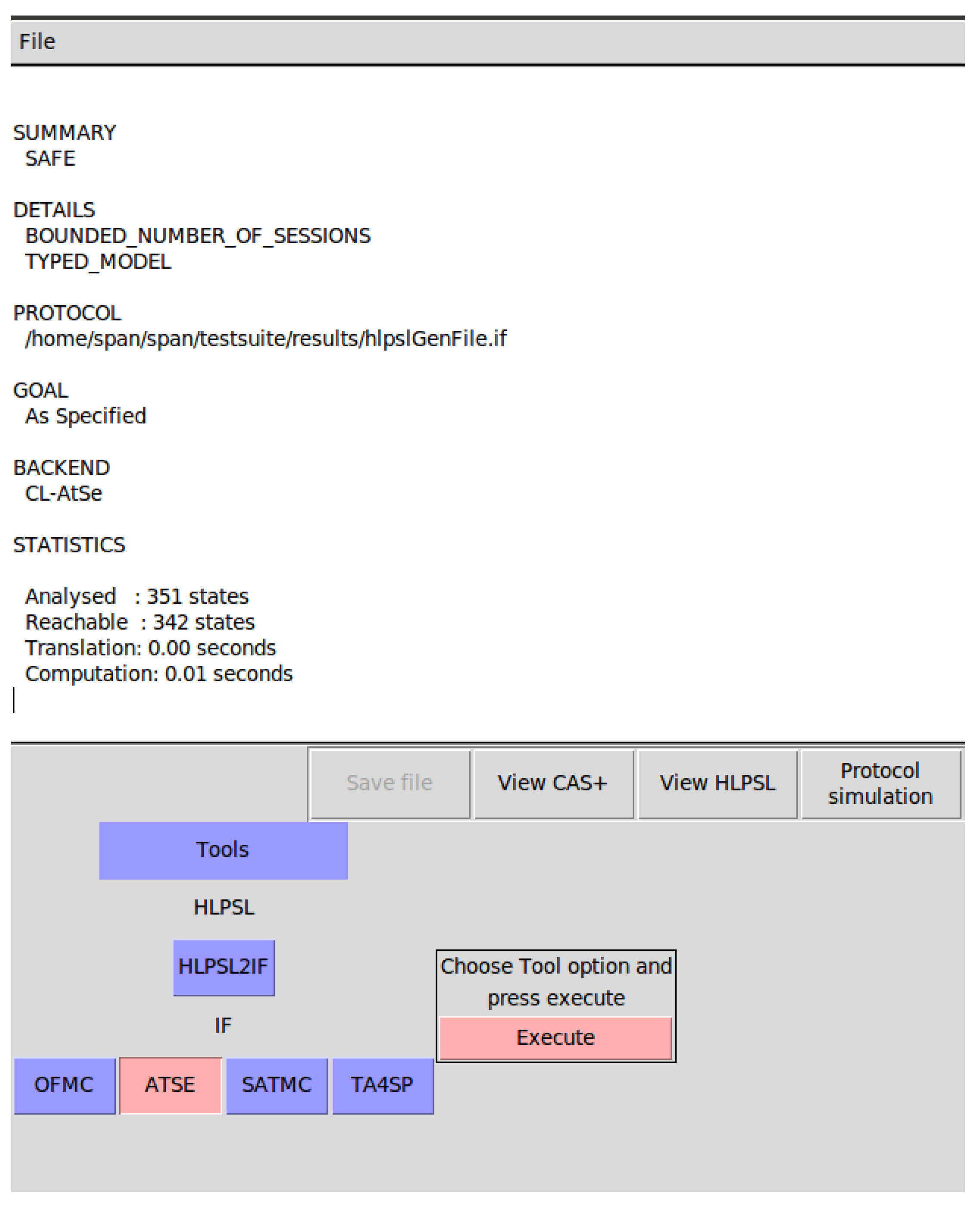
5.1. Security Analysis
5.2. Experimental Setup
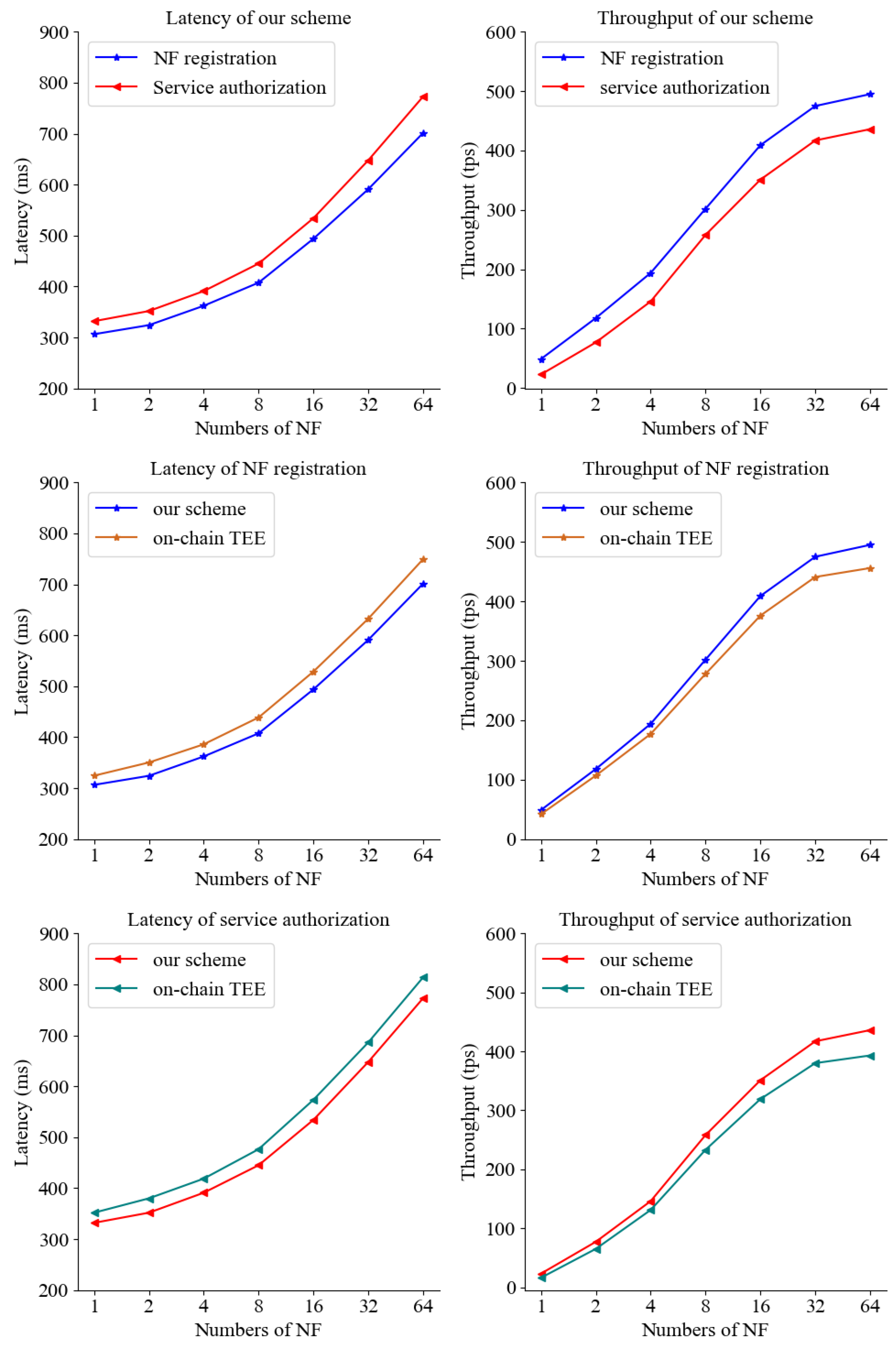
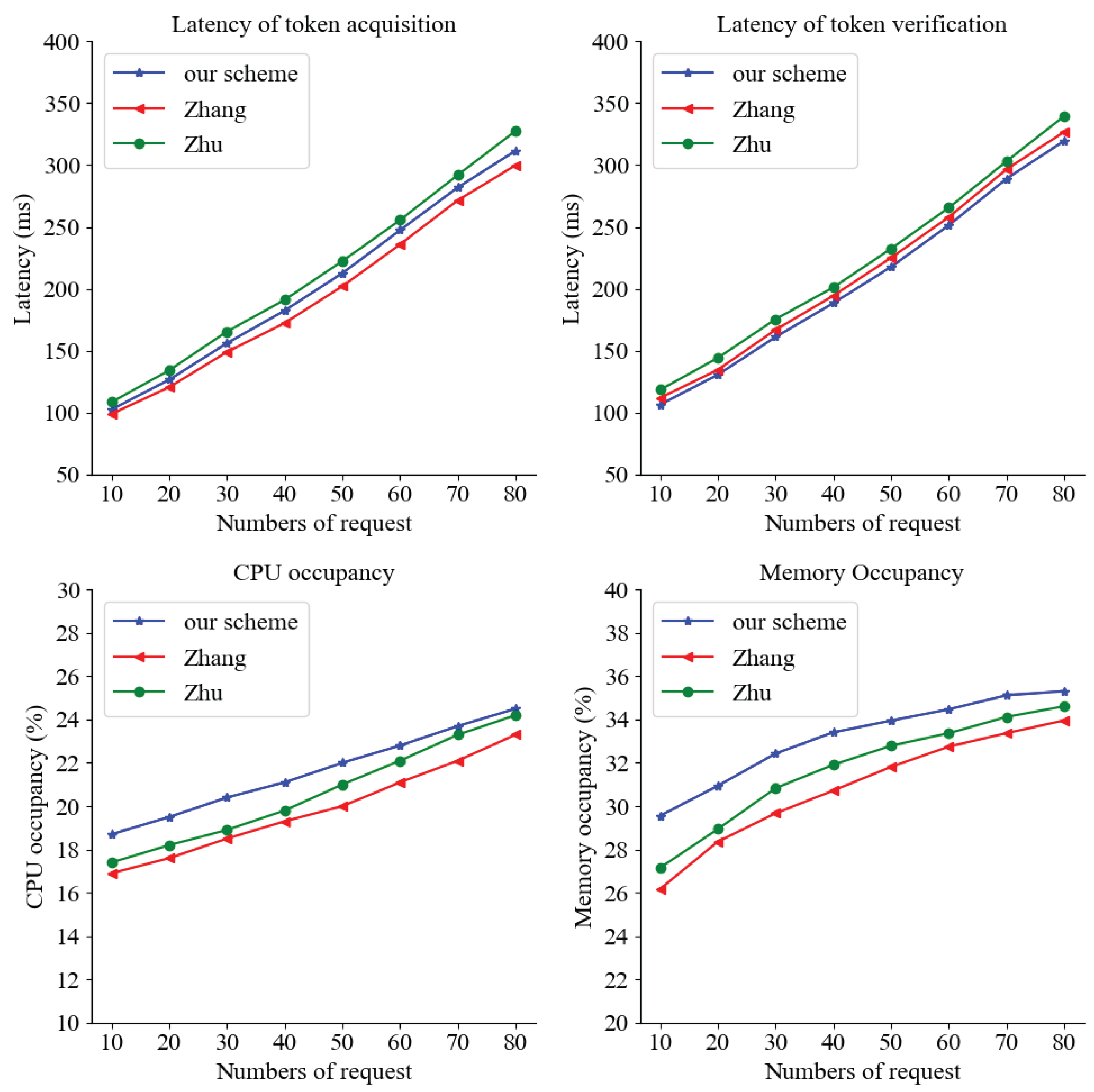
5.3. Experimental Results
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| 5G | the fifth generation mobile networks |
| JWT | JSON Web Token |
| MEC | Mobile Edge Computing |
| MitM | Man-in-the-Middle Attack |
| NF | Network Function |
| NFV | Network Function Virtualization |
| NRF | Network Repository Function |
| PLMN | Public Land Mobile Networks |
| SBA | Service-based Architecture |
| SBI | ervice-based Interfaces |
| SDN | Software-Defined Network |
| TEE | Trusted Execution Environment |
References
- Shafi, M.; Molisch, A.F.; Smith, P.J.; Haustein, T.; Zhu, P.; De Silva, P.; Tufvesson, F.; Benjebbour, A.; Wunder, G. 5G: A Tutorial Overview of Standards, Trials, Challenges, Deployment, and Practice. IEEE Journal on Selected Areas in Communications 2017, 35, 1201–1221. [Google Scholar] [CrossRef]
- Li, Y.; Huang, J.; Sun, Q.; Sun, T.; Wang, S. Cognitive Service Architecture for 6G Core Network. IEEE Transactions on Industrial Informatics 2021, 17, 7193–7203. [Google Scholar] [CrossRef]
- 3GPP TS 33.855. Study on security aspects of the 5G Service Based Architecture (SBA). Technical report, The 3rd Generation Partnership Project, 2024.
- Kim, H. 5G core network security issues and attack classification from network protocol perspective. Journal of Internet Services and Information Security (JISIS) 2020, 10, 1–15. [Google Scholar]
- Ahmad, I.; Shahabuddin, S.; Kumar, T.; Okwuibe, J.; Gurtov, A.; Ylianttila, M. Security for 5G and Beyond. IEEE Communications Surveys & Tutorials 2019, 21, 3682–3722. [Google Scholar] [CrossRef]
- 3GPP TS 23.501. System Architecture for the 5G System (5GS). Technical report, The 3rd Generation Partnership Project, 2024.
- Akon, M.; Yang, T.; Dong, Y.; Hussain, S.R. Formal Analysis of Access Control Mechanism of 5G Core Network. In Proceedings of the Proceedings of the 2023 ACM SIGSAC Conference on Computer and Communications Security. Association for Computing Machinery, 2023, CCS ’23, p. 666–680.
- Zhang, Y.; Liu, C.; Liu, S.; Pan, F. SETOKEN: A secure protection mechanism based on service API for 5G network access token. In Proceedings of the 2021 2nd International Conference on Electronics, Communications and Information Technology (CECIT), 2021; pp. 1139–1143. [Google Scholar]
- Zhu, Y.; Liu, C.; You, W.; Zhang, Y.; Zhang, W. A Business Process-Based Security Enhancement Scheme for the Network Function Service Access Procedure in the 5G Core Network. Electronics 2023, 12. [Google Scholar] [CrossRef]
- Ferdi, S.; Shah, Y.; Kumar Choyi, V.; Brusilovsky, A. Dynamic Authorization for 5G Systems. In Proceedings of the 2018 IEEE Conference on Standards for Communications and Networking (CSCN), 2018; pp. 1–5. [Google Scholar]
- Kiyemba Edris, E.K.; Aiash, M.; Loo, J.K.K. Network Service Federated Identity (NS- FId) Protocol for Service Authorization in 5G Network. In Proceedings of the 2020 Fifth International Conference on Fog and Mobile Edge Computing (FMEC), 2020; pp. 128–135. [Google Scholar]
- Luo, Y.; Li, H.; Ma, R.; Guo, Z. A Composable Multifactor Identity Authentication and Authorization Scheme for 5G Services. Security and Communication Networks 2021, 2021, 1–18. [Google Scholar] [CrossRef]
- Frassetto, T.; Jauernig, P.; Koisser, D.; Kretzler, D.; Schlosser, B.; Faust, S.; Sadeghi, A. POSE: Practical Off-chain Smart Contract Execution. In Proceedings of the 30th Annual Network and Distributed System Security Symposium, NDSS. The Internet Society, 2023. [Google Scholar]
- 3GPP TS 33.501. Security Architecture and Procedures for 5G System. Technical report, The 3rd Generation Partnership Project, 2024.
- Fei, S.; Yan, Z.; Ding, W.; Xie, H. Security Vulnerabilities of SGX and Countermeasures: A Survey. ACM Comput. Surv. 2021, 54. [Google Scholar] [CrossRef]
- Hassan, A.; Ishaq, I.; Minilla, J. Automated verification tools for cryptographic protocols. In Proceedings of the 2021 International Conference on Promising Electronic Technologies (ICPET), 2021; IEEE; pp. 58–65. [Google Scholar]
- Brandenburger, M.; Cachin, C.; Kapitza, R.; Sorniotti, A. Trusted Computing Meets Blockchain: Rollback Attacks and a Solution for Hyperledger Fabric. In Proceedings of the 2019 38th Symposium on Reliable Distributed Systems (SRDS), 2019; pp. 324–32409. [Google Scholar]
| Security Requirement |
[8] | [9] | [10] | [11] | [12] | 5G-DAuth |
|---|---|---|---|---|---|---|
| PP | ○ | ○ | ○ | ○ | ● | ● |
| AC | ● | ● | ● | ● | ● | ● |
| RAR | ● | ● | ○ | ○ | ● | ● |
| MAR | ● | ● | ○ | ○ | ● | ● |
| CD | ○ | ○ | ● | ● | ○ | ● |
| SPFP | ○ | ○ | ○ | ○ | ○ | ● |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




