Submitted:
29 November 2025
Posted:
02 December 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
- We explore the authentication weaknesses of the AKA protocol in different generations of mobile communication and study the existing vulnerabilities.
- We propose a security-enhanced 5G AKA protocol that will address the security and privacy issues identified earlier.
- We provide a formal analysis of the proposed security-enhanced 5G AKA protocol.
2. Background
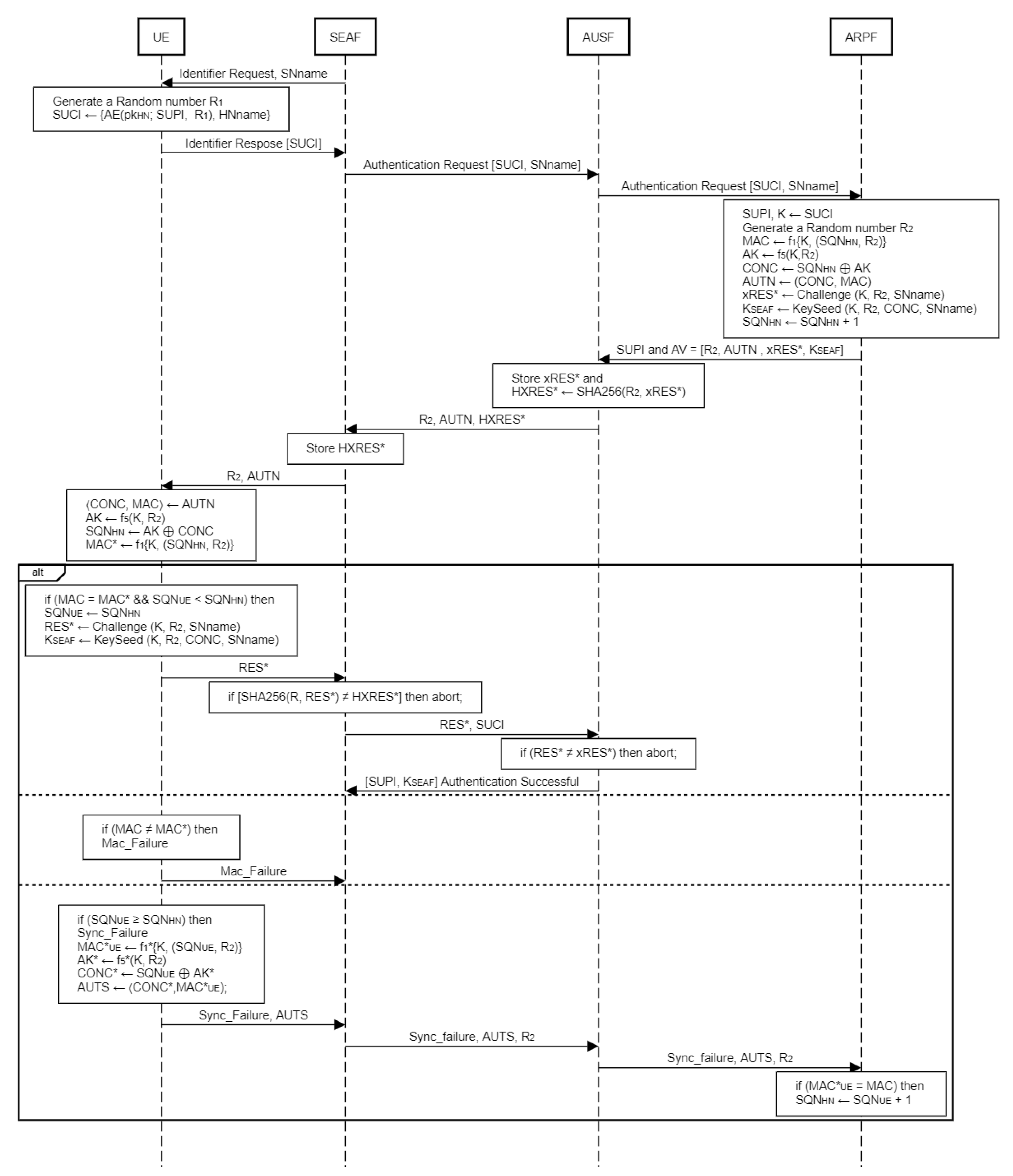
- For user identification, the SN will first want to know the identity of the UE by sending an identity request message to the UE. When UE receives the message, it generates an Identity response message containing SUCI, in which SUPI is encrypted with a Random number R1 and HNname is remains unencrypted.
- UE sends the encrypted SUPI and HNname to the SEAF and then SEAF sends it to AUSF together with SNname instead of HNname. Then AUSF forwards the message to ARPF.
- When the SUCI and SNname are received, the ARPF’s SIDF function is used to decrypt the encrypted SUPI with HN’s private key and obtain the SUPI after decrypting it. Then ARPF retrieves the long term shared secret key K of the corresponding SUPI and SQNHN, which are both used to generate AV.
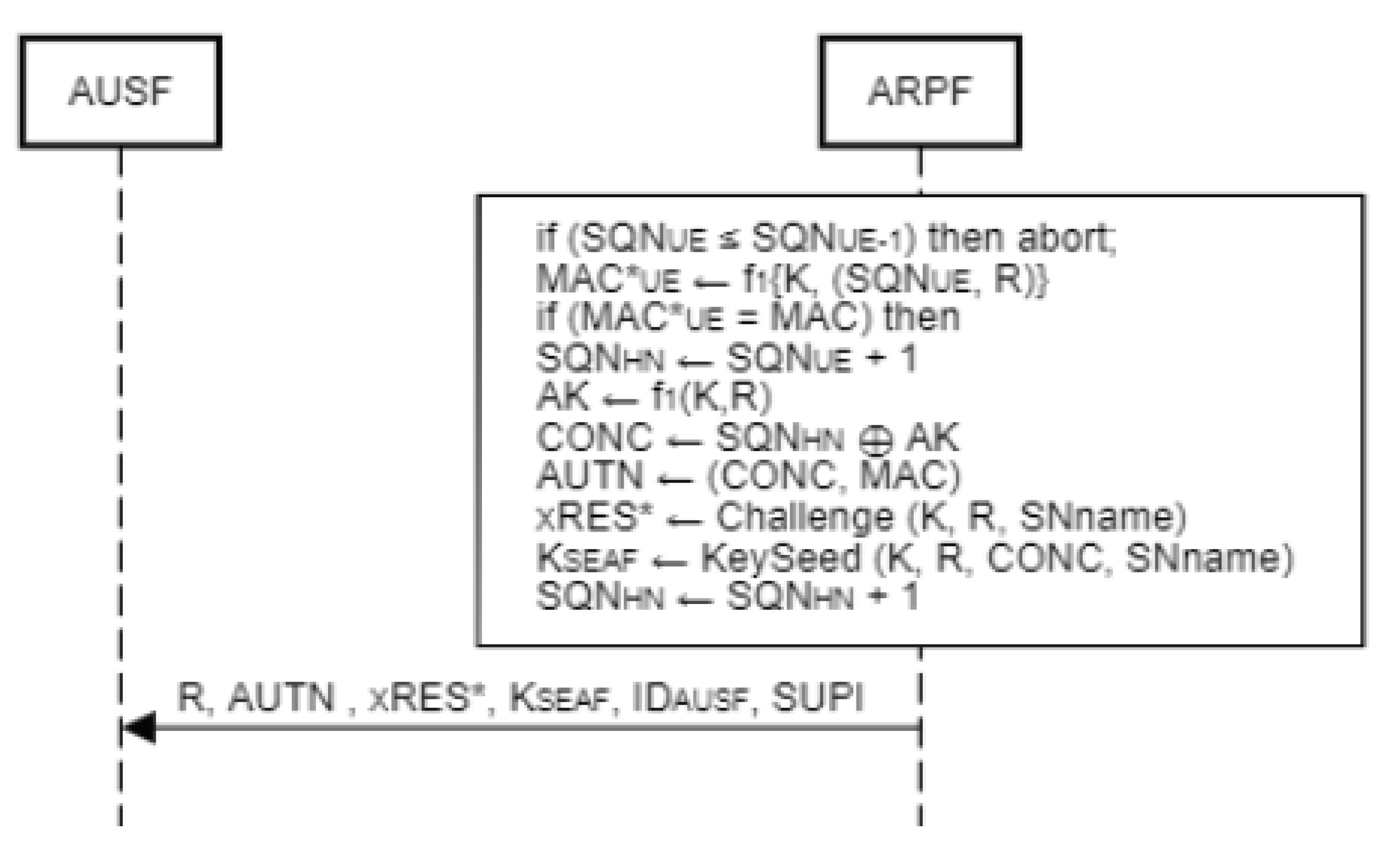
- The ARPF sends the SUPI and AV of the corresponding SUPI to the AUSF in an “authentication response” message. The AV contains R2, AUTN, xRES* and KSEAF. The detailed calculation of AV is shown in Figure 1.
- After receiving SUPI and AV from ARPF, AUSF stores the xRES* and uses the SHA256 function to compute the hash value HXRES* from the received and sends it to SEAF instead of xRES* within AV. When AUSF delivers the AV to SEAF, it simply contains R2, AUTN and HXRES*.
- After receiving the Authentication Response message from AUSF, SEAF stores the HXRES* and delivers only R2 and AUTN to UE as the Authentication Request Message.
- 7.
- After 2. and the stored long term secret key K of the user which is only known to UE and HN’s ARPF. Using that AK, UE calculates the sequence number of HN. After regenerating the sequence number of HN, MAC* will be regenerated, which is the same procedure in UE as ARPF and compare it to MAC, which is derived from received AUTN.
- 1.
- After recalculating SQNHN and MAC*, the UE will perform two tests: MAC and SQN checks to ensure the authenticity and freshness of the authentication challenge received from the network as an Authentication Request Message. MAC check confirms the authenticity of the challenge, while SQN check verifies the freshness of the authentication request. Figure 1 depicts in detail the verification of AUTN in UE.
- 1.
- a. If both checks succeed, SQN of UE will be updated to HN’s SQN and the UE will send an authentication response RES* to SEAF for further verification. The SEAF then computes the hash value of the RES* using the SHA256 function and compares it to the previously stored HXRES*. If the comparison succeeds, the RES* will be transmitted to AUSF; otherwise, the session will be terminated. In AUSF, the received RES* is compared to the previously saved xRES* from AV, and if this check is successful, AUSF sends the previously stored SUPI and KSEAF to SEAF.
- 1.
- b. If the MAC check fails, the UE will send a MAC failure message to SEAF.
- 1.
- c. If the MAC check is successful but the SQN check fails, the UE will calculate an AUTS and send it to SEAF along with a Sync failure message for re-synchronization.
Existing Security Threats
Parallel Session Attack
Linkability Attack
- MAC failure,
- Sync failure and
- AUTN verified successfully with a RES message.
SUCI Replay Attack
3. Related Works
4. Proposed Security Enhanced 5G AKA Protocol
4.1. Operation and Modification of UE
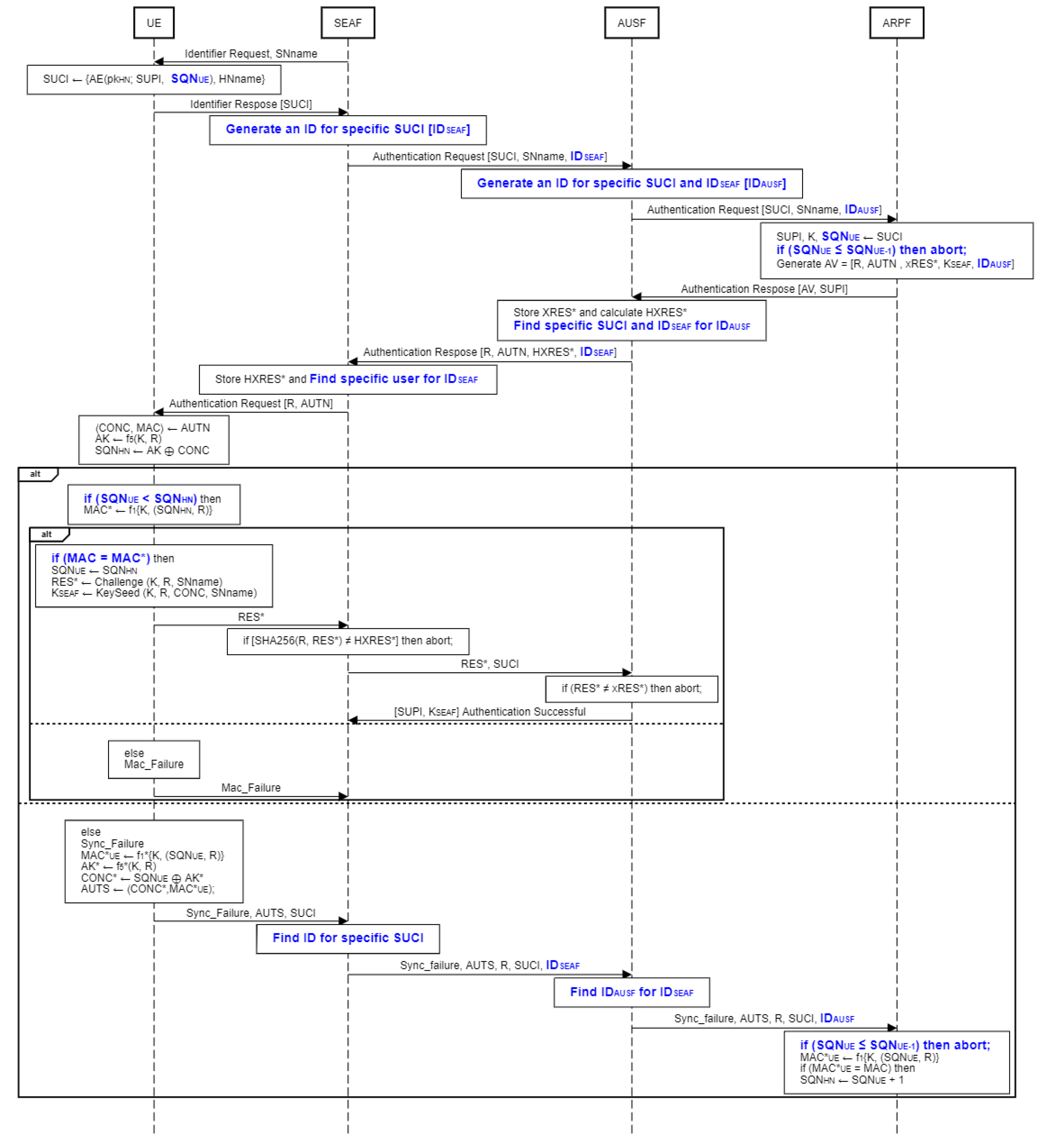
- UE generates an identity response message which contains SUCI upon receiving an identity request message from SN. The SUCI is calculated by an ECIES-based scheme that encrypts the UE’s SUPI and SQNUE with the HN public key pkHN. The SUCI is then delivered with HNname without encryption where,
- After obtaining R and AUTN from SEAF, UE does the same computation as ARPF.First CONC and MAC are derived from received AUTN where,
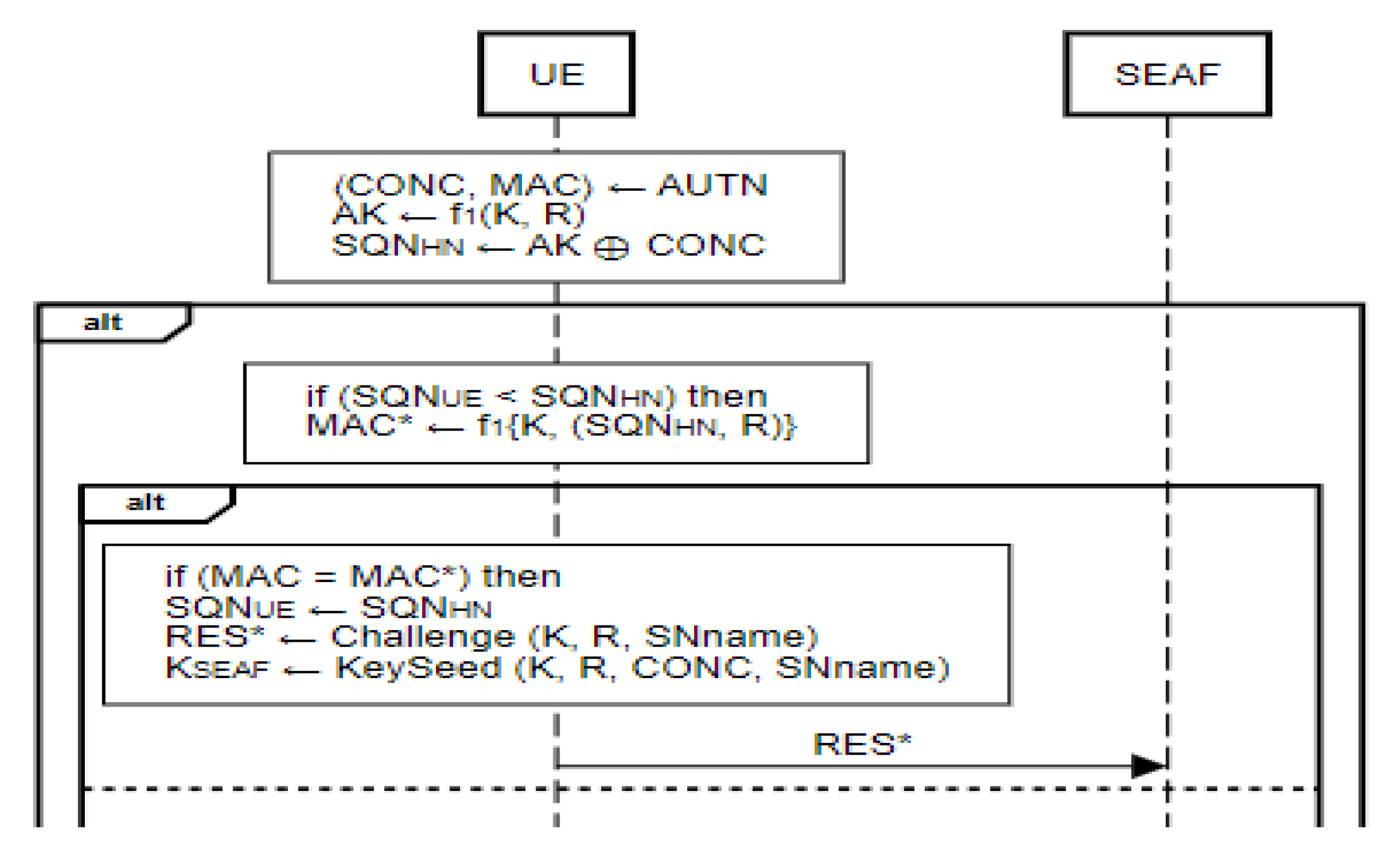
- If SQNHN > SQNUE, MAC* will be regenerated using SQNHN, K, and R, and then compared to MAC, which is derived from received AUTN where,
- If MAC* = MAC, SQNHN is updated as SQNUE and RES* are regenerated and KSEAF is derived in the same manner as in ARPF where,
- 2.
- If MAC* ≠ MAC, then the UE sends a Mac_failure message to SEAF to terminate the authentication procedure.

4.2. Operation and Modification of SEAF
- When SEAF obtains the identity response message containing SUCI from the UE, SEAF will generate a unique 128-bit random number for that specific SUCI as a session id [IDSEAF].
- After receiving the R, AUTN, and IDSEAF from AUSF, SEAF uses the received IDSEAF to locate the specific UE and deliver the R and AUTN.
- SEAF receives RES* from UE and computes the hash value of RES* using SHA256 and compares it to HXRES* which is received during AV transmission. If both are found to be equal, RES* and its matching SUCI are sent to AUSF.
4.3. Operation and Modification of AUSF
- After getting the IDSEAF, SUCI, and SNname from SEAF, AUSF stores the IDSEAF and produces a 128-bit random number [IDAUSF].
- After receiving AV from ARPF, which consists of R, AUTN, xRES*, KSEAF, SUPI, and IDAUSF, AUSF stores the xRES* and uses the SHA256 function to compute the hash of the response HXRES* from the received xRES*. Then AUSF finds the IDSEAF for the received IDAUSF and sends it in place of IDAUSF. When AUSF delivers the AV to SEAF, it simply contains R and AUTN.
- If the hash of RES* and HXRES* check is passed the AUSF receives RES* and SUCI from SEAF. Then compares RES* with the recorded xRES*. If the comparison succeeds, the authentication is successful, and AUSF will send the stored SUPI and KSEAF to SEAF; otherwise, the session will be terminated.
4.4. Operation and Modification of ARPF
- Upon reception of the SUCI, the ARPF’s SIDF function is used to decrypt the SUCI using HN’s private key. After decrypting SUCI we obtain SUPI and SQNUEwhere,
- A 128-bit random number R is generated.
- A 64-bit MAC is calculated as MAC = f1 (K, SQN || R).
- A n-bit xRES* is calculated where n is a multiple of 8 and in the range between 32-128 as xRES* = Challenge (K, R, SNname), where Challenge () is a key derivation function.
- An anchor key KSEAF is calculated by ARPF as KeySeed (K, R, CONC, SN name), where KeySeed () is a complex key derivation function.
- The 128-bit ciphering key CK is computed by the ARPF CK = f5 (K, R).
- The 128-bit integrity key IK is computed by the ARPF as IK = f4 (K,R).
- The 48-bit anonymity key AK is computed by the ARPF as AK = f5(K, R).
- A 48-bit CONC is calculated as CONC = (SQNHN ⊕ AK).
- The 128-bit authentication token AUTN is generated by ARPF as AUTN = (SQNHN ⊕ AK) || MAC, where || signifies concatenation and ⊕ denotes bitwise exclusive-or.
- The ARPF forwards the 5G AV = [R, AUTN, xRES*, KSEAF, IDAUSF] and SUPI in an “authenticate response” message to the AUSF.
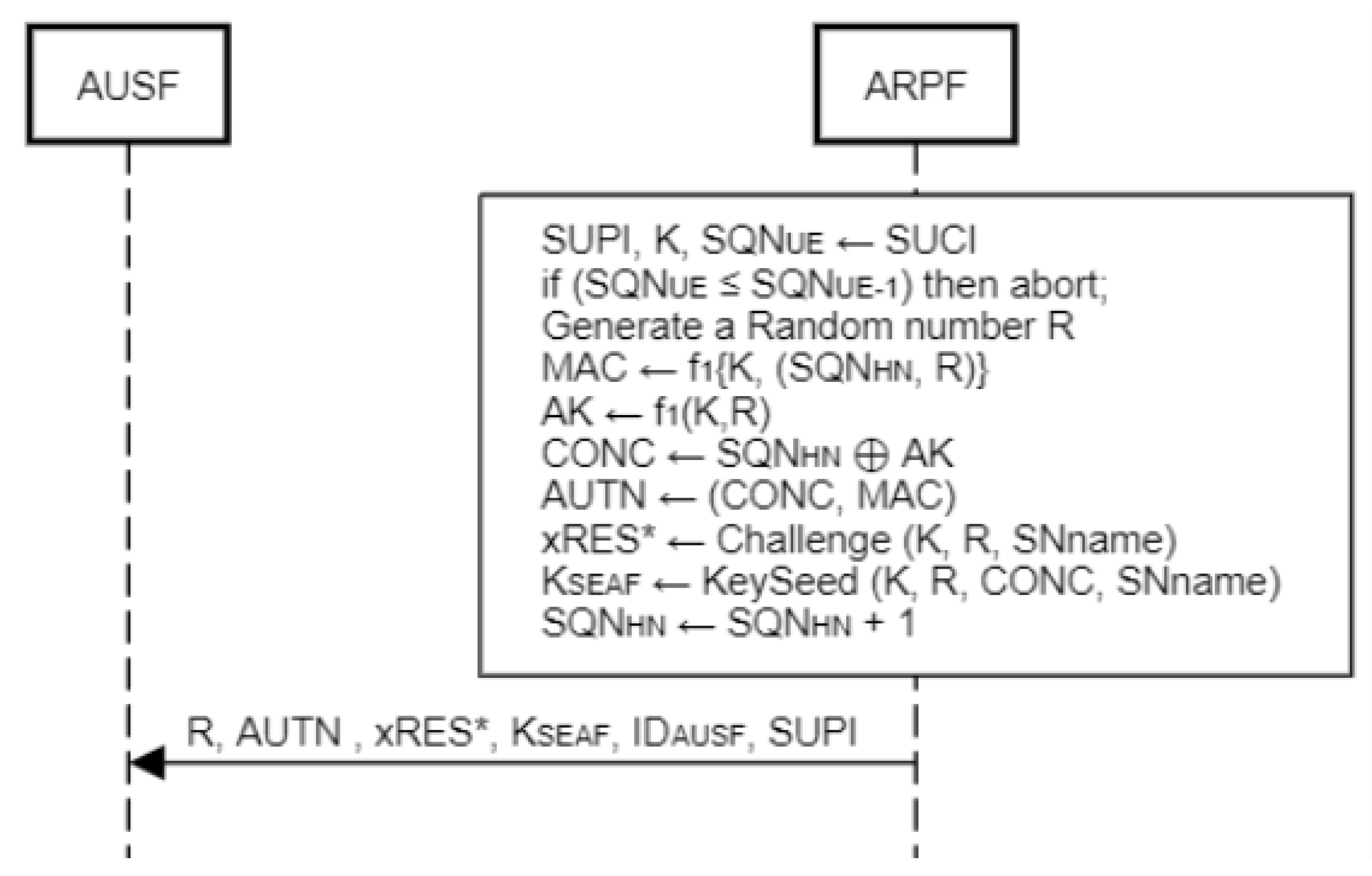
- When Sync_failure occurs in the authentication procedure, ARPF needs to adjust its SQNHN and recalculate the AUTN. In this procedure, ARPF first compares the received SQNUE with previously stored SQNUE-1. If condition is fulfilled, then MAC*UE will be generated using the received SQNUE with the help of k and R using the message authentication function f1. After that, if the comparison of MAC*UE and MAC holds, the sequence number of HN will be updated as SQNHN = SQNUE + 1 and the rest of the computation will be the same as before applying the updated SQNHN.
5. Analysis of the Proposed Protocol
6. Conclusions
Supplementary Materials
Author Contributions
Funding
Informed Consent Statement
Conflicts of Interest
Abbreviations
| AK | Anonymity key |
| AMF | Authentication management field |
| AUTN | Authentication token |
| AUTS | Authentication token in SQN re-synchronization |
| CK | 3GPP cipher key |
| EK | Encryption key in the Modifiable multiple IMSIs scheme |
| f1 | 3GPP network authentication function |
| f1* | 3GPP re-synchronization message authentication function |
| f2 | 3GPP user authentication function |
| f3 | 3GPP cipher key derivation function |
| f4 | 3GPP integrity key derivation function |
| f5 | 3GPP anonymity key derivation function for normal operation |
| f5* | 3GPP anonymity key derivation function for re-synchronization |
| IK | 3GPP integrity key |
| KA | Attacker’s long-term key |
| SUCIV | Victims concealed SUPI |
| SUCIA | Attacker concealed SUPI |
| KASME | Local master key in EPS |
| KSEAF | Security anchor function key |
| K Long | term shared secret key |
| HXRES* | Hash response |
| MAC | Message authentication code |
| MAC* | Regenerate message authentication code |
| SQNHN | Sequence number of home network |
| SQNUE | Sequence number of user equipment |
| SQNUE-1 | Previously stored number of user equipment |
| R | Random number |
| MACUE | User equipment message authentication code |
| MACHN | Home network authentication code |
| pkHN | Home network public key |
| SNname | Serving network name |
| AE | Asymmetric encryption |
| IDSEAF | ID of security anchor function |
| IDAUSF | ID of authentication server function |
| HNname | Home network name |
| RAND | Random challenge |
| RES | Authentication response |
| xRES* | Expected response |
| RES* | Generated response |
| SQN | Sequence number |
| XMAC | Expected MAC |
| XOR | Boolean exclusive-OR operation |
| LTE | Long Term Evolution |
| 2G | Second Generation |
| 3G | Third Generation |
| 4G | Fourth Generation |
| 5G | Fifth Generation |
| IoT | Internet of Things |
| 3GPP | Third Generation Partnership Project |
| AKA | Authentication and Key Agreement |
| IMSI | International Mobile Subscriber Identity |
| GUTI | Globally Unique Temporary User Equipment Identity |
| UE | User Equipment |
| HN | Home Network |
| MAC | Message Authentication Code |
| AMA | Activity Monitoring Attack |
| LCA | Location Confidentiality Attack |
| SUCI | Subscriber Concealed Identifier |
| SUPI | Subscriber Permanent Identifier |
| SEAF | Security Anchor Function |
| AUSF | Authentication Server Function |
| ARPF | Authentication Credential Repository and Processing Function |
| UMTS | Universal Mobile Telecommunication System |
| IP | Internet Protocol |
| RAN | Radio Access Network |
| GSM | Global System for Mobile Communications |
| UTRAN | Universal Terrestrial Radio Access Network |
| GERAN | GSM Edge Radio Access Network |
| BTS | Base Transceiver Station |
| RNC | Radio Network Controller |
| ME | Mobile Equipment |
| MSC | Mobile Switching center |
| VLR | Visitor Location Register |
| HLR | Home Location Register |
| GMSC | Getaway Mobile Switching Center |
| GPRS | General Packet Radio Service |
| SGSN | Serving GPRS Support Node |
| GGSM | Getaway GPRS Support Node |
| MNO | Mobile Network Operator |
| EPS | Evolved Packet System |
| EUTRAN | Evolved Universal Terrestrial Radio Access Network |
| eNB | Evolved Node |
| gNB | Next Generation Node B |
| MME | Mobility Management Entity |
| S-GW | Serving Getaway |
| PDN | Public Data Network |
| HSS | Home Subscriber Server |
| AuC | Authentication Center |
| USIM | Universal Subscriber Identity Module |
| P-TMSI | Packet Temporary Mobile Subscriber Identity |
| TMSI | Temporary Mobile Subscriber Identity |
| LAI | Location Area Identity |
| MCC | Mobile Country Code |
| MNC | Mobile Network Code |
| MSIN | Mobile Subscriber Identification Number |
| ECIES | Elliptic Curve Integrated Encryption Scheme |
| AV | Authentication Vector |
| SIDF | Subscription Identifier De-concealing function |
| HPLMN | Home Public Land Mobile Network |
| VPLMN | Visited Public Land Mobile Network |
| AMF | Access and Mobility Management Function |
| NAS | Non-Access Stratum |
| RRC | Radio Resource Control |
| SUPA | Symmetric Updatable Private Authentication |
| PPKA | Privacy Preserving Key Agreement |
| UICC | Universal Integrated Circuit Curve |
| TPM | Trusted Platform Module |
References
- Turner, A. How Many People Have Smartphones Worldwide (Oct 2021). Bank My Cell. 2021. Available online: https://www.bankmycell.com/blog/how-many-phones-are-in-the-world (accessed on 21 October 2021).
- 5G Americas. Global—5G Americas . 2021. Available online: https://www.5gamericas.org/resources/charts-statistics/global/ (accessed on 2 September 2021).
- Khan, Mohammed Shafiul Alam. Improving Security and Privacy in Current Mobile Systems. Ph.D. dissertation, Information Security Group, Royal Holloway, Univ., London, United Kingdom, 2017. [Google Scholar]
- Khan, Haibat; Martin, Keith M. On the Efficacy of New Privacy Attacks against 5G AKA. In Proceedings of the 16th International Joint Conference on e-Business and Telecommunications, ICETE 2019—; Prague, Czech Republic, Obaidat, Mohammad S., Samarati, Pierangela, Eds.; SciTePress, 26-28 July 2019; Volume 2, pp. pages 431–438. [Google Scholar]
- Cremers, C.; Dehnel-Wild, M. Component-based formal analysis of 5G-aka: Channel assumptions and session confusion. Proceedings 2019 Network and Distributed System Security Symposium, 2019. [Google Scholar]
- Wang, Y.; Zhang, Z.; Xie, Y. Privacy-Preserving and Standard-Compatible AKA Protocol for 5G. 30th {USENIX} Security Symposium ({USENIX} Security 21, Aug. 21AD.
- Basin, D.; Dreier, J.; Hirschi, L.; Radomirovic, S.; Sasse, R.; Stettler, V. A formal analysis of 5G authentication. In Proceedings of the 2018 ACM SIGSAC Conference on Computer and Communications Security, 2018. [Google Scholar]
- Pari, S.N.; Azhagu Vasanth, R.; Amuthini, M.; Balaji, M. Randomized 5G AKA Protocol Ensembling Security in Fast Forward Mobile Device. 2019 11th International Conference on Advanced Computing (ICoAC), 2019; pp. 295–301. [Google Scholar] [CrossRef]
- Khan, Haibat. Security and Privacy in Emerging Communication Standards. In Information Security Group; Royal Holloway Univ.: London,United Kingdom, 2020. [Google Scholar]
- HU, X.; LIU, C.; LIU, S.; LI, J.; CHENG, X. “A Vulnerability in 5G Authentication Protocols and Its Countermeasure”. IEICE Transactions on Information and Systems 2020, vol. 103(no. 8), 1806–1809. [Google Scholar] [CrossRef]
- Braeken, A. “Symmetric key based 5G AKA authentication protocol satisfying anonymity and unlinkability”. Computer Networks 2020, vol. 181, 107424. [Google Scholar] [CrossRef]
- Braeken, A.; Liyanage, M.; Kumar, P.; Murphy, J. “Novel 5G Authentication Protocol to Improve the Resistance Against Active Attacks and Malicious Serving Networks”. IEEE Access 2019, vol. 7, 64040–64052. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).