Submitted:
12 November 2025
Posted:
13 November 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Related Work
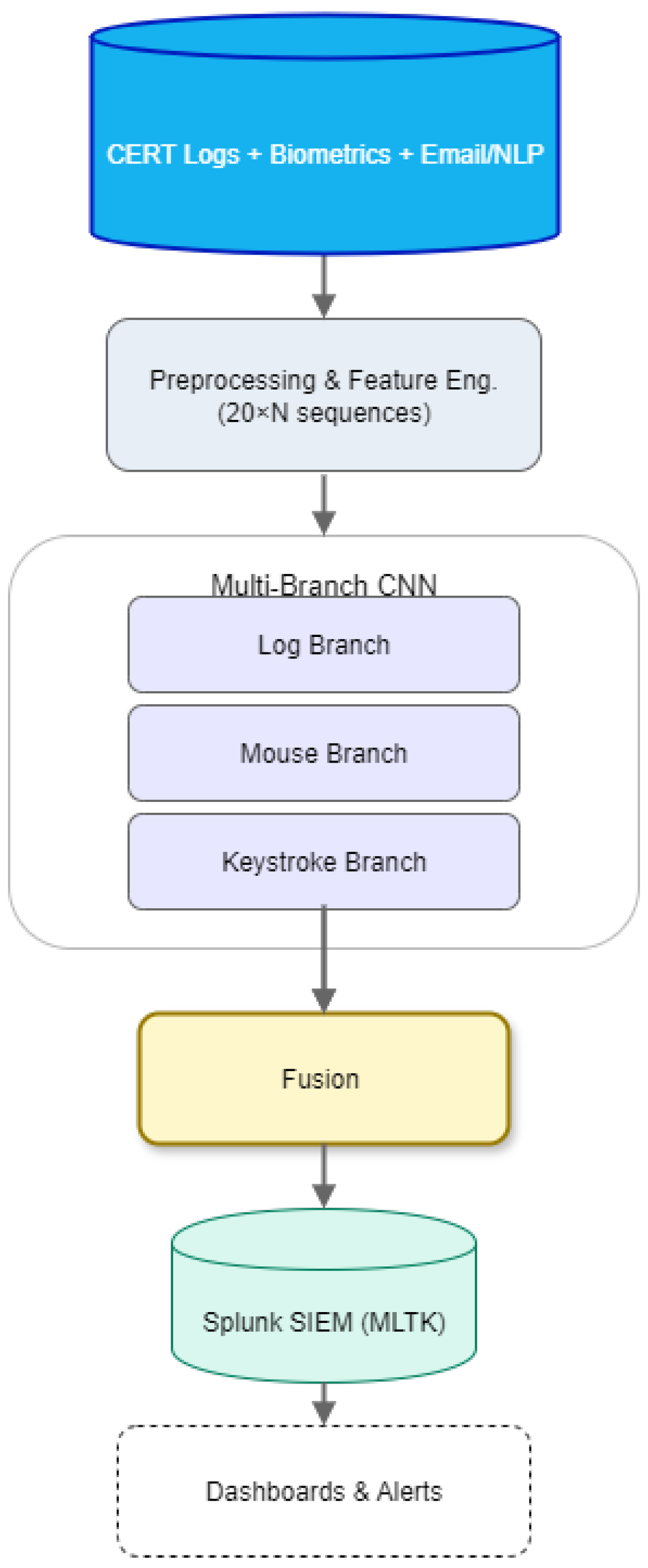
3. Methodology
3.1. Data Sources and Ground Truth
3.2. Pre-processing
-
Logon/Device/HTTP/File:(id) if unique, otherwise(user, pc, timestamp[, url/filename]).
- Email:(id) or (user, timestamp, to, size).
| Log file | Canonical fields (representative) | Count |
|---|---|---|
| logon.csv | id, date, user, pc, activity (Logon/Logoff) | 5 |
| device.csv | id, date, user, pc, activity (connect/disconnect) | 5 |
| http.csv | id, date, user, pc, url, content | 6 |
| file.csv | id, date, user, pc, filename, content | 6 |
| email.csv | id, date, user, pc, to, cc, bcc, from, size, attachment_count, content | 11 |
3.3. Sequence Windowing and Split Protocol
3.4. Feature Engineering Overview
3.4.1. Logon (Event-Level, )
- events_last_5min, fail_count_5min
- simul_login, max_events_5min, gap, max_gap
- off_hours_ratio, user_pc_novel, pc_user_entropy
- wkday_wkend_ratio, last3_short_cnt, last3_mean_dur, delta_last3
- sess_dur_z, daily_login_z
3.4.2. Device (Event-Level, )
- device_session_duration, off_hours_device, is_weekend
- file_count_to_usb, usb_file_tree_entropy
- activity_encoded, inter_event_time, hour_of_day, day_of_week
3.4.3. Email, File, HTTP, and Behavioural Biometrics
3.5. Models and Training
- negative downsampling to a target ratio (20:1 or 10:1 normal:anomaly per epoch),
- class weights in the loss (heavier weight on ),
- class-balanced mini-batches (per-batch pos:neg ).
- Optimizer: Adam (initial learning rate ).
- Scheduler: ReduceLROnPlateau (monitor val PR-AUC, factor 0.5, patience 3, minimum LR ).
- EarlyStopping: patience 6 with best-weights restore.
- Typical batch sizes: 4096 windows (logs) and 128 sequences (Balabit).
- L2 regularization on dense layers; Dropout in heads.
3.5.1. Logon CNN (Splunk Deployed)
3.5.2. Device CNN (Splunk Deployed)
3.5.3. Email CNN (Partial; Offline)
3.5.4. HTTP CNN (Partial; Offline)
3.5.5. Balabit (Mouse), ResConv + BiLSTM (Offline)
3.5.6. Training Data Assembly and Loaders (All Logs)
3.5.7. Post-Training Calibration and Operating Thresholds (Used in Splunk)
3.5.8. Regularisation, Ablations, and Stability Checks
3.5.9. Compute and Limits
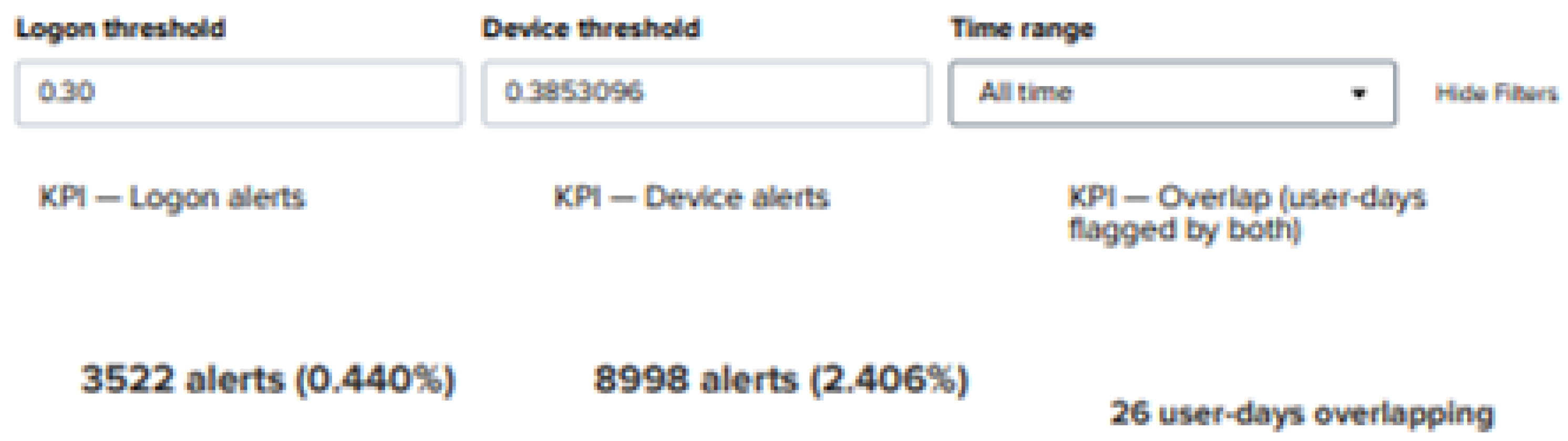
4. Results
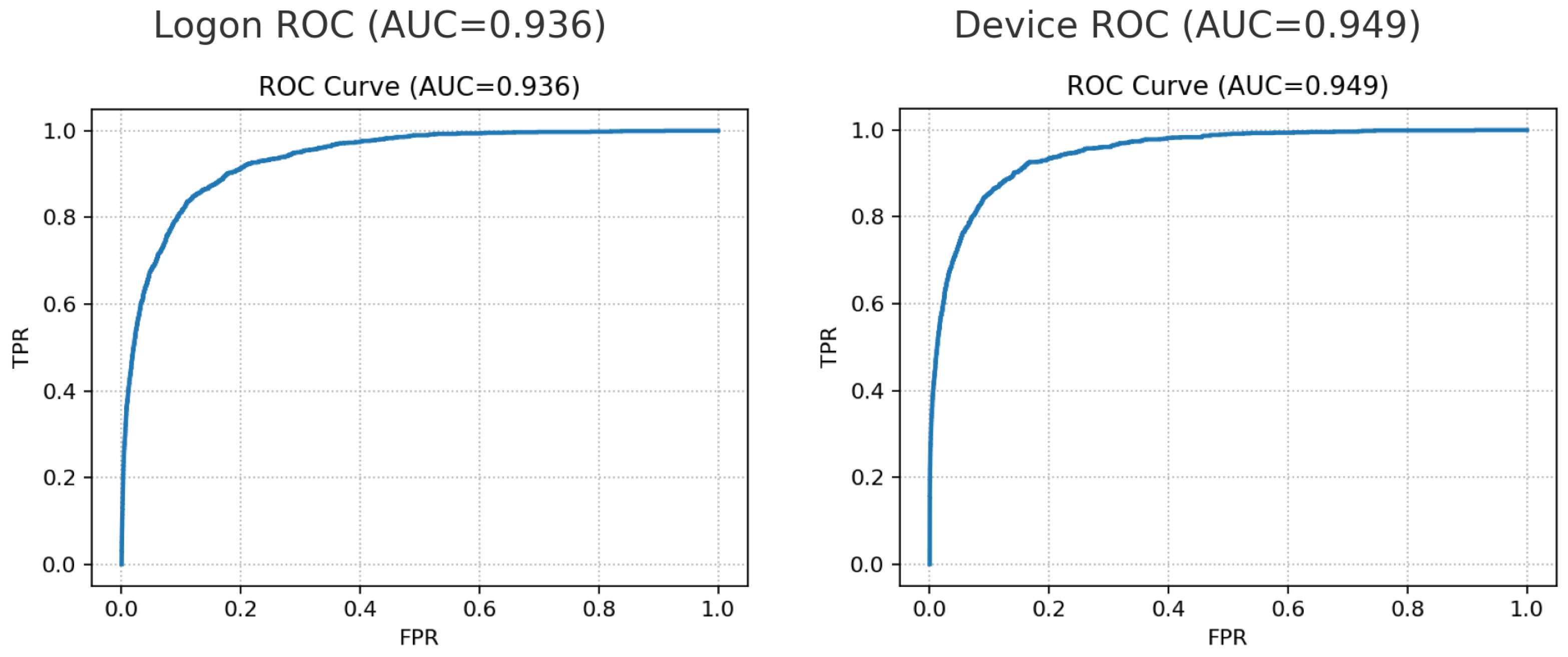
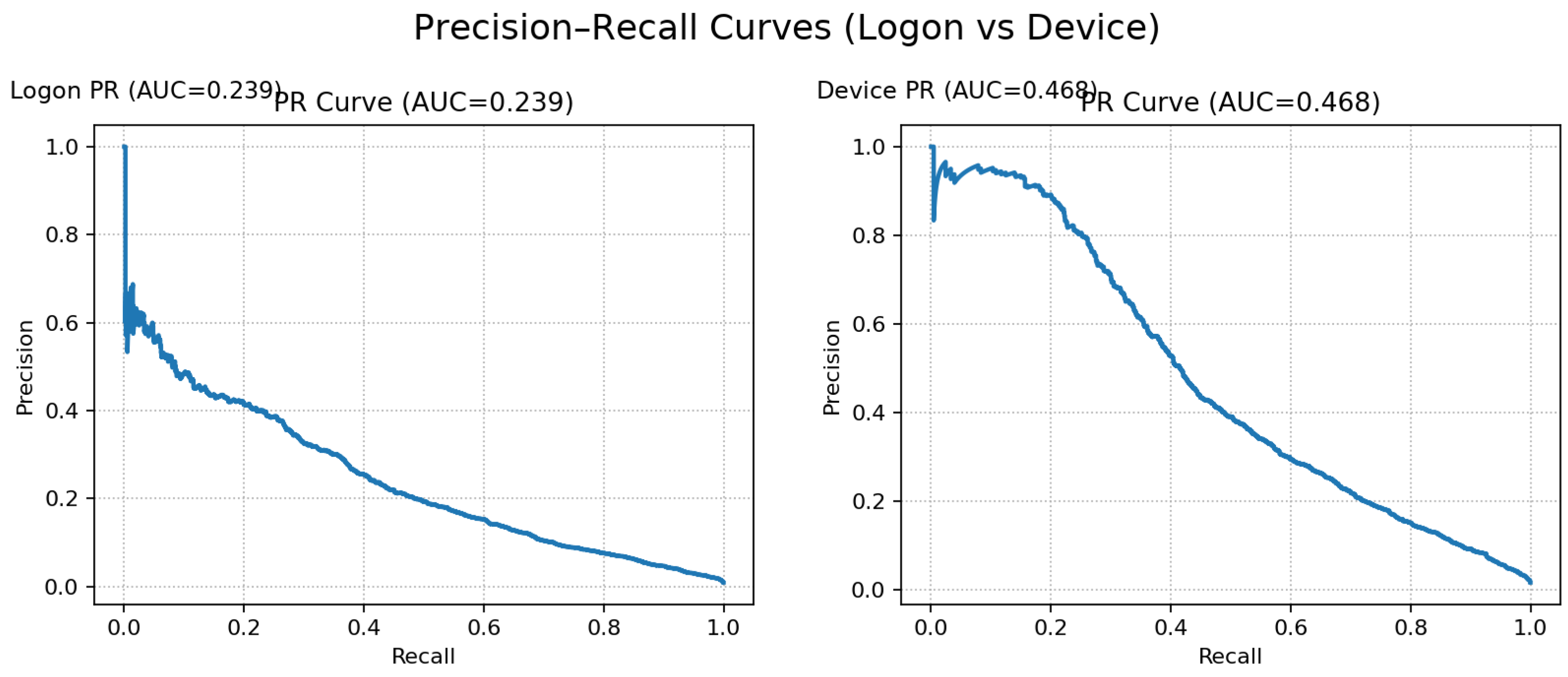
| Model | Split | PR-AUC | ROC-AUC | Threshold | Precision | Recall | FPR |
|---|---|---|---|---|---|---|---|
| Logon | test | 0.239 | 0.936 | 0.4663 | 0.750 | 0.0020 | |
| Device | test | 0.468 | 0.949 | 0.4443 | 0.700 | 0.3010 | 0.0020 |
| Balabit (val) | val | 0.867 | 0.835 | 0.0829 | 0.935 | 0.8300 | 0.0507 |
| Balabit (test) | test | 0.409 | 0.382 | 0.0829 | 0.051 | 0.4170 | 0.4510 |
| Seed | PR-AUC | ROC-AUC | P@50 | P@60 | P@70 |
|---|---|---|---|---|---|
| 13 | 0.468 | 0.949 | 0.416 | 0.354 | 0.301 |
| 42 | 0.457 | 0.944 | 0.397 | 0.333 | 0.289 |
| 77 | 0.406 | 0.942 | 0.340 | 0.269 | 0.204 |
5. Evaluation and Discussion
5.1. Evaluation Objectives and Protocol Recap
5.2. Ranking Quality versus Operating Points
5.3. Calibration and Alert Budgeting
5.4. Latency and Throughput (Operational)
5.5. Error Analysis and Failure Modes
5.6. Baselines and Comparison to Prior Work
5.7. Limitations and Threats to Validity
5.8. Operational Guidance and Implications
5.9. Future Work
6. Conclusions
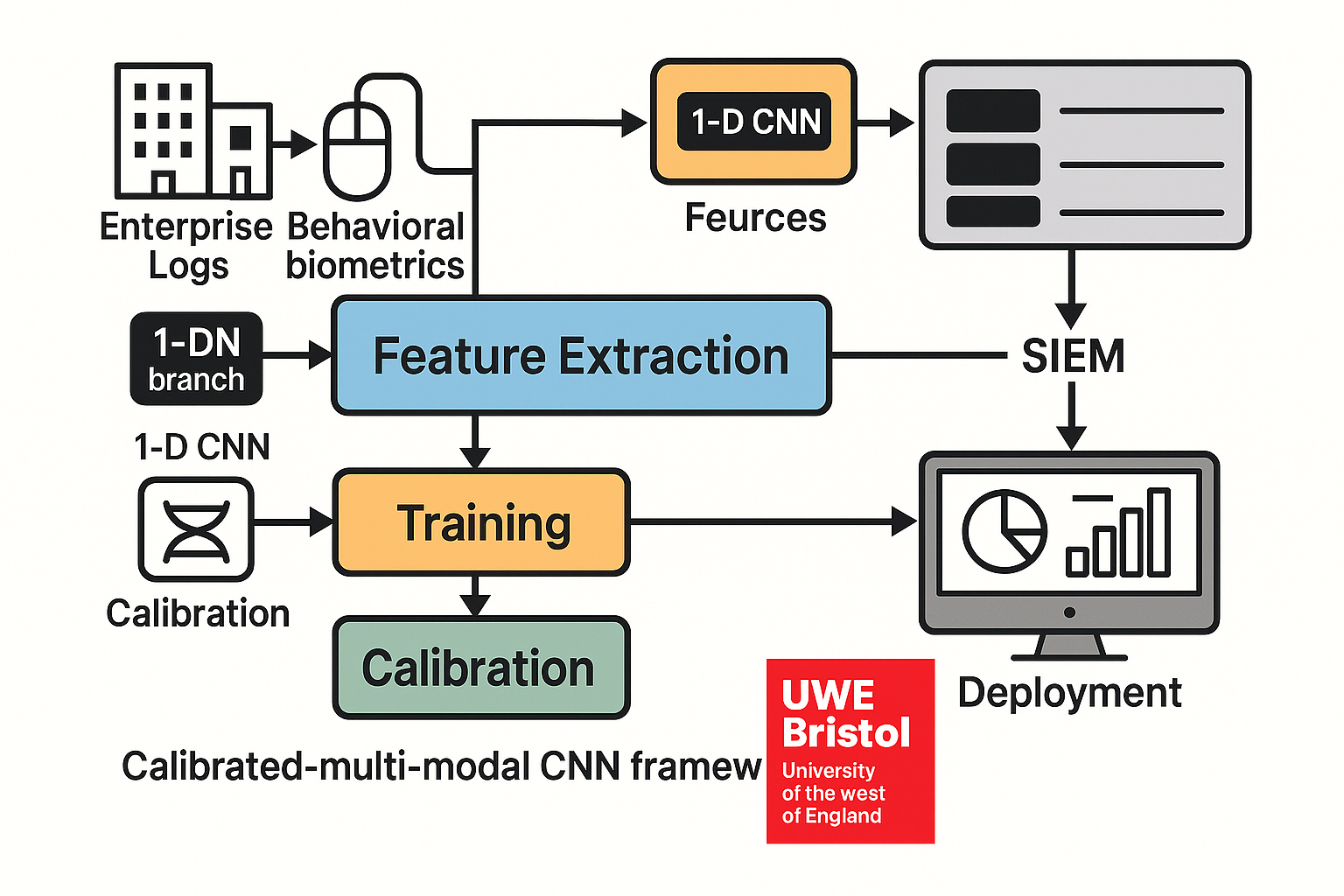
- Development of a calibrated, multimodal CNN framework integrating directly into a live SIEM environment.
- A reproducible, imbalance-aware training and calibration process enabling stable alert budgeting for analysts.
- Demonstration of end-to-end deployment feasibility in Splunk MLTK with manifest-validated feature ingestion and dashboards for alert triage and overlap analysis.
- Empirical validation using user- and time-disjoint splits to ensure operational realism and prevent identity leakage.
Author Contributions
References
- Anju, A.; Krishnamurthy, M. M-EOS: Modified equilibrium optimisation based stacked CNN for insider threat detection. Wireless Networks 2024, 30, 2819–2838. [Google Scholar] [CrossRef]
- CNN LSTM based insider threat detection model. Proc. 2025 Int. Conf. on Electrical Automation and Artificial Intelligence (ICEAAI), Guangzhou, China, 10–12 January 2025. [CrossRef]
- Narmadha, S.; Balaji, N.V. Improved network anomaly detection system using optimized autoencoder-LSTM. Expert Systems with Applications 2025, 273, 126854. [Google Scholar] [CrossRef]
- Alabadi, M.; Celik, Y. Anomaly detection for cyber security based on convolutional neural network: A survey. In 2020 Int. Congress on Human Computer Interaction, Optimization and Robotic Applications (HORA); IEEE, 2020. [CrossRef]
- Lee, J.; Kim, J.; Kim, I.; Han, K. Cyber threat detection based on artificial neural networks using event profiles. IEEE Access 2019, 7, 165607–165626. [Google Scholar] [CrossRef]
- Duary, S.; et al. Cybersecurity threats detection in intelligent networks using predictive analytics approaches. In Proc. 4th Int. Conf. on Innovative Practices in Technology and Management (ICIPTM); IEEE: Noida, India, 23 February 2024. [Google Scholar] [CrossRef]
- Ismail, W.S. Threat detection and response using AI and NLP in cybersecurity. Journal of Internet Services and Information Security 2024, 14, 195–205. [Google Scholar] [CrossRef]
- He, D.; Lv, X.; Xu, X.; Chan, S.; Choo, K.-K.R. Double layer detection of internal threat in enterprise systems based on deep learning. IEEE Transactions on Information Forensics and Security 2024, 19, 4741–4751. [Google Scholar] [CrossRef]
- Villarreal Vasquez, M.; Modelo Howard, G.; Dube, S.; Bhargava, B. Hunting for insider threats using LSTM based anomaly detection. IEEE Transactions on Dependable and Secure Computing 2023, 20. [Google Scholar] [CrossRef]
- Manoharan, P.; Yin, J.; Wang, H.; Zhang, Y.; Ye, W. Insider threat detection using supervised machine learning algorithms. Telecommunication Systems 2024, 87, 899–915. [Google Scholar] [CrossRef]
- Manoharan, P.; Hong, W.; Yin, J.; Wang, H.; Zhang, Y.; Ye, W. Optimising insider threat prediction: Exploring BiLSTM networks and sequential features. Data Science and Engineering 2024, 9, 393–408. [Google Scholar] [CrossRef]
- Bin Sarhan, B.; Altwaijry, N. Insider threat detection using machine learning approach. Applied Sciences 2023, 13. [Google Scholar] [CrossRef]
- Al Shehari, T.; Al Razgan, M.; Alfakih, T.; Alsowail, R.A.; Pandiaraj, S. Insider threat detection model using anomaly-based Isolation Forest algorithm. IEEE Access 2023, 11. [Google Scholar] [CrossRef]
- Baghalizadeh Moghadam, N.; Neal, C.; Cuppens, F.; Boulahia Cuppens, N. NLP and neural networks for insider threat detection. In Proc. IEEE TrustCom, 2024. [CrossRef]
- Kılıç, A.A.; Yıldırım, M.; Anarım, E. Bogazici mouse dynamics dataset. Data in Brief 2021, 36, 107094. [Google Scholar] [CrossRef] [PubMed]
- Tao, X.; Yu, Y.; Fu, L.; Liu, J.; Zhang, Y. An insider user authentication method based on improved temporal convolutional network. High Confidence Computing 2023, 3, 100169. [Google Scholar] [CrossRef]
- AbouRida, O.; Nashaat, M.; Saad, N.G.E.d. Deep learning driven user legitimacy prediction using keystroke and mouse behavioural dynamics. In 2024 Int. Conf. on Computer and Applications (ICCA); IEEE, 2024; pp. 1–8. [CrossRef]
- Sahu, A.K.; Jha, V. Survey on continuous authentication using keystroke dynamics: Taxonomy, challenges, and future directions. Computer Science Review 2021, 40, 100376. [Google Scholar] [CrossRef]
- Medvedev, V.; Budžys, A.; Kurasova, O. A decision making framework for user authentication using keystroke dynamics. Computers & Security 2025, 155, 104494. [Google Scholar] [CrossRef]
- Ramu, P.; Parida, P.; Bellamkonda, P.; Panda, M.K. Keystroke authentication using a novel RTS framework. In Proc. IEEE 4th Int. Conf. on Applied Electromagnetics, Signal Processing, & Communication (AESPC), 2024. [CrossRef]
- Fridman, L.; Stolerman, A.; Acharya, S.; Brennan, P.; Juola, P.; Greenstadt, R.; Kam, M. Multi modal decision fusion for continuous authentication. Computers & Electrical Engineering 2015, 41, 142–156. [Google Scholar] [CrossRef]
- Yang, X.; Howley, E.; Schukat, M. Agent based dynamic thresholding for adaptive anomaly detection using reinforcement learning. Neural Computing and Applications 2025, 37, 18775–18791. [Google Scholar] [CrossRef]
- Guo, H.; Yuan, S.; Wu, X. LogBERT: Log anomaly detection via BERT. In Proc. 2021 Int. Joint Conf. on Neural Networks (IJCNN); IEEE, 2021. [CrossRef]
- Killourhy, K.S.; Maxion, R.A. Comparing anomaly detection algorithms for keystroke dynamics. In 2009 IEEE/IFIP Int. Conf. on Dependable Systems & Networks (DSN); Estoril, Portugal, 2009; pp. 125–134.
- Dewa, Z. The relationship between biometric technology and privacy: A systematic review. In Future Technologies Conf. (FTC) 2017; Vancouver, 2017; pp. 739–748.
- Walter, W.H. Insider Threat Detection Using Neural Networks: A Statistical Comparison of the CERT Insider Threat Database; Doctor of Engineering Praxis, George Washington University, 18 May 2025; ProQuest No. 31933040.
- Palaniappan, S.; Logeswaran, R.; Khanam, S. Anomaly detection in network traffic for insider threat identification: A comparative study of unsupervised and supervised machine learning approaches. Journal of Informatics and Web Engineering 2025, 4, 146–156. [Google Scholar] [CrossRef]
- Singh, M.; Mehtre, B.M.; Sangeetha, S.; Govindaraju, V. User behaviour based insider threat detection using a hybrid learning approach. Journal of Ambient Intelligence and Humanized Computing 2023, 14, 4573–4593. [Google Scholar] [CrossRef]
- Carnegie Mellon University, Software Engineering Institute. CERT Insider Threat Test Dataset (r4.2/r6.2). Available online: https://www.sei.cmu.edu/library/insider-threat-test-dataset/ (accessed on 7 October 2025).
- Killourhy, K.S.; Maxion, R.A. Keystroke dynamics benchmark data set. Available online: https://www.cs.cmu.edu/~keystroke/ (accessed on 7 October 2025).
- Balabit. Mouse dynamics challenge data set. Available online: https://github.com/balabit/Mouse-Dynamics-Challenge (accessed on 7 October 2025).
- Splunk Inc. About the Splunk Machine Learning Toolkit. Available online: https://docs.splunk.com/Documentation/MLApp/5.6.1/User/AboutMLTK (accessed on 7 October 2025).

| Ref | Domain | Model | Dataset | Metrics reported | Notes / Comparative remarks |
|---|---|---|---|---|---|
| [1] | Insider (CERT) | CNN+BiGRU | CERT | Acc 92.5; Prec 98; AUC = 0.95 | Strong temporal model; leakage risk; no PR-AUC or alert budgeting. |
| [2] | Insider (CERT) | CNN-LSTM | CERT r4.2 | Acc > 0.90; Prec > 0.90; Rec ≈ 0.95 | CNN→LSTM; narrow scope; no user/time disjoint split; no PR-AUC. |
| [5] | SOC alert triage | TF-IDF+ANN | NSL-KDD, CICIDS-2017 | Acc = 0.93–0.95; ROC-AUC ≈ 0.97 | Fast triage; no time-disjoint evaluation or PR-AUC. |
| [8] | Enterprise phishing + insider | BiLSTM +XGB Phish | Enron /monkey emails; CERT r6.2 | Phishing: Prec 98.6, FPR 1.4; Insider: Acc ≈ 96.4, AUC ≈ 0.72, FPR ≈ 3.5 | Two-layer; small CERT subset; look-ahead risk. |
| [9] | EDR insider anomaly | LSTM-LM | Enterprise EDR | TPR 97.29; FPR 0.38; detects novel events | Per-process LM + dynamic thresholds; low FPR; no operational SIEM link. |
| [10] | Insider (CERT) | Classical ML (RF) | CERT r4.2 | Acc = F1 = 0.96 (balanced); drops under imbalance | Solid baselines; random-split leakage; no PR-AUC. |
| [11] | Insider prediction | BiLSTM-Emb | CERT r4.2 | Acc 0.911; F1 0.908 | Sequential gains; GT flag confounds realism. |
| [12] | Insider (CERT) | DFS +Classifiers | CERT r4.2 | OCSVM: P 0.94/R 0.86/A 0.86; iForest: 0.92/0.91/0.91; SVM: 1.00 | Heavy feature engineering; no file/email; Acc/PR/F1 only. |
| [13] | Insider (anomaly) | Isolation Forest | CERT r4.2 | c = 0.02 → Acc 0.98; Rec 0.98; F1 0.99 | IForest; random split + global threshold; weak SOC realism. |
| [14] | Insider as NLP | NLP-LLM (LLaMA-3) | CERT r4.2 | Acc 98.0; Prec 90.4; Rec 90.0; FPR 1.07; RoBERTa+GRU FPR 0.94 | LLM approach; Brier/ROC only; no PR-AUC or SIEM integration. |
| [16] | Insider auth (keystroke) | Temporal CNN | Keystroke auth data | N/A | Temporal CNN captures micro-patterns; relevant to biometrics. |
| [17] | Legitimacy (behav. biometrics) | Biometric Fusion | Keystroke + mouse | N/A | Keystroke+mouse gains; supports multimodal fusion rationale. |
| [21] | Continuous auth (biometrics) | Decision Fusion (EER-focused) | Multimodal dataset | N/A | Decision-fusion blueprint; guides late fusion used in this paper. |
| [23] | Log anomaly (unsupervised) | LogBERT | System logs | AUC/F1 > classic baselines | Self-supervised log modelling; useful pretext signal; no PR-AUC or real-time calibration. |
| Branch | Inference path | Measured throughput | Notes |
|---|---|---|---|
| Logon | Python + Keras (CPU), batch = 1k windows | ≈70.5k windows/s (∼14.2 ms / 1k) | From test run |
| Device | Same stack | Same latency class (identical backbone) | SIEM-ready |
| Balabit | Keras (GPU/CPU), batch = 64 sessions | Real-time per session | One-hot adds minor cost |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




