Submitted:
04 November 2025
Posted:
05 November 2025
You are already at the latest version
Abstract
Keywords:
1. Introduction
2. Overview
2.1. Algorithmic Outline of a FIPS 140-2/3-Compliant Hardware Solution
Module Initialization (Power-On Self-Tests)
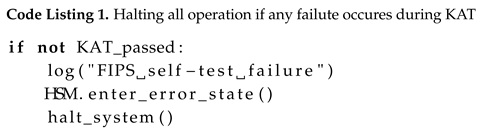
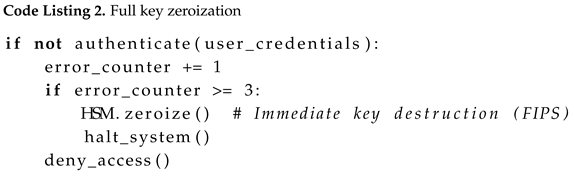
User Authentication
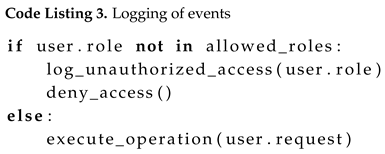
Access and Role Management
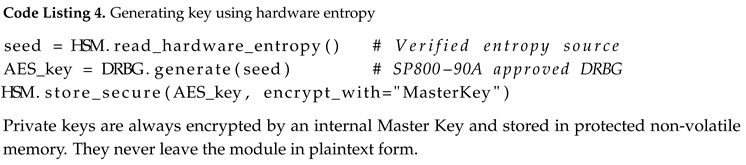
Key Generation and Secure Storage
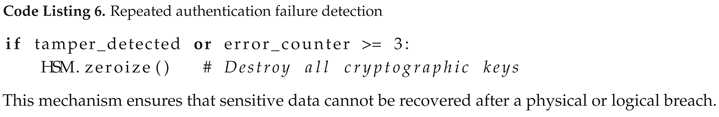
Data Encryption, Signing, and Integrity Verification
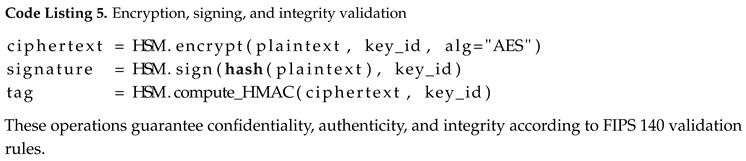
Zeroization and Tamper Response
2.2. Methodology for Comparative Evaluation
Evaluation Criteria
Data Collection and Normalization
Analytical Framework
Limitations
Synthesis
3. Methods
3.1. Definition of Evaluation Criteria
3.2. Feature Matrix and Platform Comparison
| Function / Platform | ATECC608B/C | TPM 2.0 (Infineon SLB9672) | NXP i.MX 8X + SE050 | AWS Nitro Enclaves |
|---|---|---|---|---|
| Secure Boot | Firmware validation | via PCRs + UEFI | via CAAM + SE050 support | Isolated attestation (not firmware) |
| Physical Tamper Detection | None | FIPS 140 - 2 Level 3 | FIPS 140 - 2 Level 3 | Hypervisor isolation |
| HSM / Secure Storage | Key storage | Dedicated hardware crypto | HSM via SE050 | via AWS KMS HSM |
| FIPS - certified RNG | SP800 - 90B FIPS 140 - 3 | NDRNG FIPS 140 - 2 | SE FIPS - certified | KMS with FIPS - certified HSM |
| FIPS Certification | FIPS 140 - 3 | FIPS 140 - 2 Level 2 | FIPS 140 - 2 Level 3 | KMS / CloudHSM FIPS - certified |
3.3. Data Collection and Validation
3.4. Interpretive Framework and Theoretical Context
3.5. Limitations and Mitigation Strategies
3.6. Implementation Cost and Compliance Estimate
4. Results
4.1. Comparative Overview of Evaluated Architectures
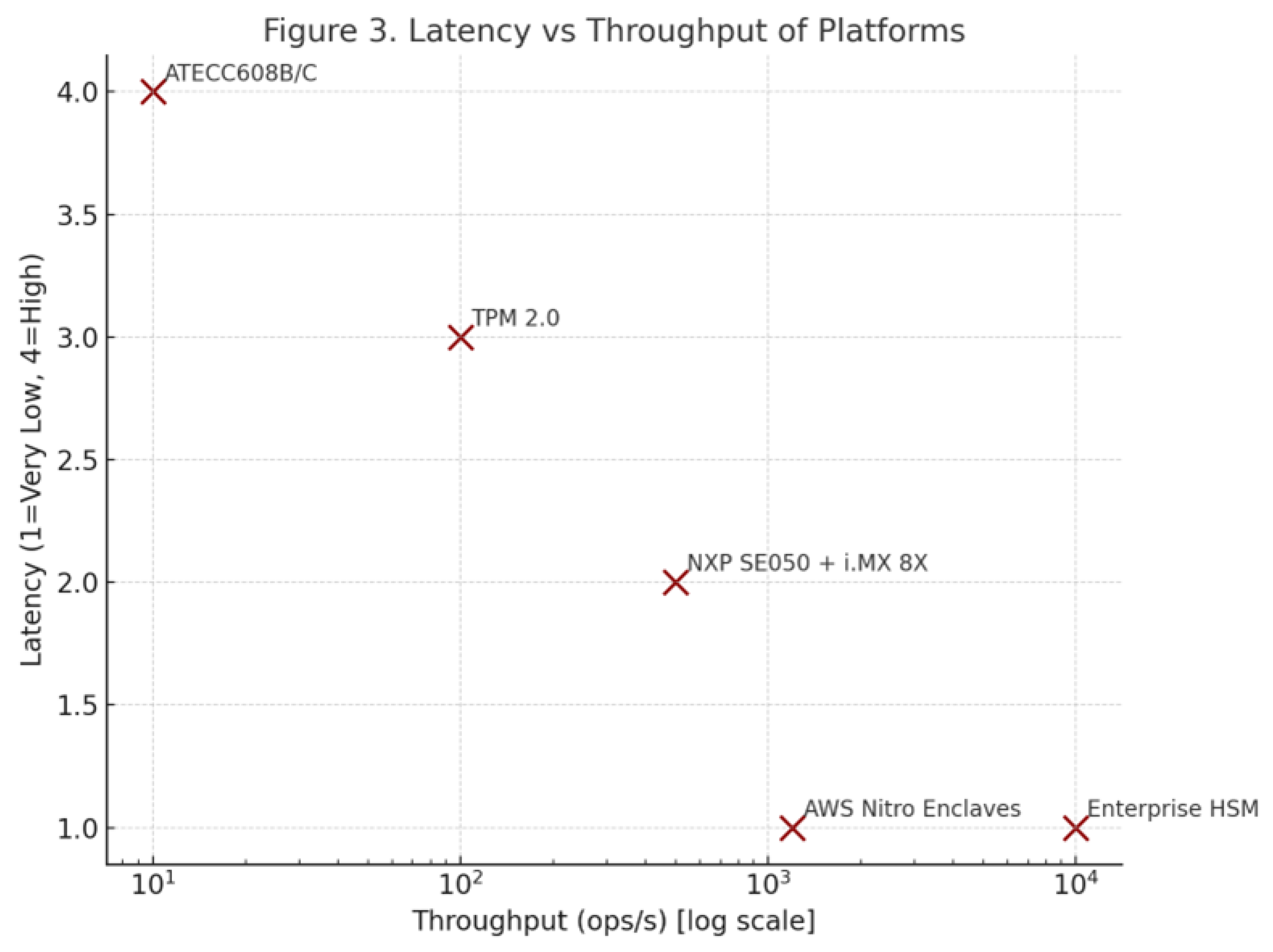
- NXP SE050 with i.MX 8X: Combines embedded secure element and hardware root-of-trust for advanced IoT devices. This configuration achieves FIPS 140-3 Level 3 compliance with moderate energy overhead [9,10]. Studies such as [13,36] demonstrate that such hybrid architectures provide a good balance between isolation and throughput.
- Enterprise HSMs (Entrust nShield, Thales Luna): Offer unmatched security, scalability, and performance (>10,000 ops/s) with FIPS 140-3 Level 3-4 certification [12]. These solutions remain essential for high-assurance industrial control or financial infrastructures, where compliance and latency guarantees are critical.
4.2. Performance and Cost Correlation
4.3. Latency and Throughput Trade-Offs
4.4. Security and Integration Complexity
4.5. Sustainability and Energy Efficiency
4.6. Cross-Domain Implications
5. Discussion
5.1. Data Reliability and Benchmarking Constraints
5.2. Broader Security Considerations
5.3. Post-Quantum and Future-Proofing Perspectives
5.4. Interoperability and Cloud Integration
5.5. Application Domains and Societal Impact
5.6. Energy Efficiency and Sustainability Outlook
5.7. Future Work and Recommendations
6. Conclusions
Author Contributions
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Yang, G.; Guan, K.; Zou, L.; Sun, Y.; Yang, X. Weld Defect Detection of a CMT Arc-Welded Aluminum Alloy Sheet Based on Arc Sound Signal Processing. Applied Sciences 2023, 13, 5152. [Google Scholar] [CrossRef]
- Mrabet, H.; Belguith, S.; Alhomoud, A.; Jemai, A. A Survey of IoT Security Based on a Layered Architecture of Sensing and Data Analysis. Sensors 2020, 20, 3625. [Google Scholar] [CrossRef]
- Chui, K.T.; Gupta, B.B.; Liu, J.; Arya, V.; Nedjah, N.; Almomani, A.; Chaurasia, P. A Survey of Internet of Things and Cyber-Physical Systems: Standards, Algorithms, Applications, Security, Challenges, and Future Directions. Information 2023, 14, 388. [Google Scholar] [CrossRef]
- Lim, K.; Ooi, S.; Sayeed, M.; Chew, Y.; Ahmad, N. Securing the Internet of Things: Systematic Insights into Architectures, Threats, and Defenses. Electronics 2025, 14, 3972. [Google Scholar] [CrossRef]
- Chen, Z.; Sun, X.; Li, Y.; Wang, J.; Zhao, H. A Survey on Zero-Knowledge Authentication for Internet of Things. Electronics 2023, 12, 1145. [Google Scholar] [CrossRef]
- eska, S.; Furtak, J. Procedures for Building a Secure Environment in IoT Networks Using the LoRa Interface. Sensors 2025, 25, 3881. [Google Scholar] [CrossRef]
- Zhou, X.; Wang, P.; Zhou, L.; Xun, P.; Lu, K. A Survey of the Security Analysis of Embedded Devices. Sensors 2023, 23, 9221. [Google Scholar] [CrossRef] [PubMed]
- Radhakrishnan, I.; Shanmugam, P.; Lakshmanan, S.; Venkatesan, S. Efficiency and Security Evaluation of Lightweight Cryptographic Algorithms for IoT Devices. Sensors 2024, 24, 4008. [Google Scholar] [CrossRef] [PubMed]
- Dione, D.; Seck, B.; Diop, I.; Cayrel, P.; Faye, D.; Gueye, I. Hardware Security for IoT in the Quantum Era: Survey and Challenges. Journal of Information Security 2023, 14, 227. [Google Scholar] [CrossRef]
- Noseda, M.; Zimmerli, L.; Schläpfer, T.; Rüst, A. Performance Analysis of Secure Elements for IoT. IoT 2022, 3, 1–28. [Google Scholar] [CrossRef]
- Potestad-Ordóñez, F.; Casado-Galán, A.; Tena-Sánchez, E. Protecting FPGA-Based Cryptohardware Implementations from Fault Attacks Using ADCs. Sensors 2024, 24, 1598. [Google Scholar] [CrossRef] [PubMed]
- Aref, Y.; Ouda, A. HSM4SSL: Leveraging HSMs for Enhanced Intra-Domain Security. Future Internet 2024, 16, 148. [Google Scholar] [CrossRef]
- Leonardi, L.; Lettieri, G.; Perazzo, P.; Saponara, S. On the Hardware–Software Integration in Cryptographic Accelerators for Industrial IoT. Applied Sciences 2022, 12, 9948. [Google Scholar] [CrossRef]
- Cabrera-Gutiérrez, A.; Castillo, E.; Escobar-Molero, A.; Cruz-Cozar, J.; Morales, D.; Parrilla, L. Secure Sensor Prototype Using Hardware Security Modules and Trusted Execution Environments in a Blockchain Application: Wine Logistic Use Case. Electronics 2023, 12, 2987. [Google Scholar] [CrossRef]
- Mengistu, T.M.; Kim, T.; Lin, J.W. A Survey on Heterogeneity Taxonomy, Security and Privacy Preservation in the Integration of IoT, Wireless Sensor Networks and Federated Learning. Sensors 2024, 24, 968. [Google Scholar] [CrossRef]
- Ahsan, M.S.; Pathan, A.S.K. A Comprehensive Survey on the Requirements, Applications, and Future Challenges for Access Control Models in IoT: The State of the Art. IoT 2025, 6, 9. [Google Scholar] [CrossRef]
- Andrade, R.O.; Yoo, S.G.; Ortiz-Garces, I.; Barriga, J. Security Risk Analysis in IoT Systems through Factor Identification over IoT Devices. Applied Sciences 2022, 12, 2976. [Google Scholar] [CrossRef]
- Radulescu, C.; Roman, M. A Hybrid Group Multi-Criteria Approach Based on SAW, VIKOR, TOPSIS and COPRAS for IoT Platform Selection. Electronics 2024, 13, 789. [Google Scholar] [CrossRef]
- National Institute of Standards and Technology. Security Requirements for Cryptographic Modules. Technical Report FIPS 140-3, U.S. Department of Commerce, NIST, 2019. [CrossRef]
- He, P.; Zhou, Y.; Qin, X. A Survey on Energy-Aware Security Mechanisms for the Internet of Things. Future Internet 2024, 16, 128. [Google Scholar] [CrossRef]
- Dirin, A.; Oliver, I.; Laine, T.H. A Security Framework for Increasing Data and Device Integrity in Internet of Things Systems. Sensors 2023, 23, 7532. [Google Scholar] [CrossRef]
- Dawod, A.; Georgakopoulos, D.; Jayaraman, P.; Nirmalathas, A. A Survey of Techniques for Discovering, Using, and Paying for Third-Party IoT Sensors. Sensors 2024, 24, 2539. [Google Scholar] [CrossRef]
- Sadhu, P.K.; Yanambaka, V.P.; Abdelgawad, A. Internet of Things: Security and Solutions Survey. Sensors 2022, 22, 7433. [Google Scholar] [CrossRef]
- Abosata, N.; Al-Rubaye, S.; Inalhan, G.; Emmanouilidis, C. Internet of Things for System Integrity: A Comprehensive Survey on Security, Attacks and Countermeasures for Industrial Applications. Sensors 2021, 21, 3654. [Google Scholar] [CrossRef]
- Hossain, M.; Kayas, G.; Hasan, R.; Skjellum, A.; Noor, S.; Islam, S.M.R. A Holistic Analysis of Internet of Things (IoT) Security: Principles, Practices, and New Perspectives. Future Internet 2024, 16, 40. [Google Scholar] [CrossRef]
- Almutairi, M.; Sheldon, F.T. IoT–Cloud Integration Security: A Survey of Challenges, Solutions, and Directions. Electronics 2025, 14, 1394. [Google Scholar] [CrossRef]
- Canavese, D.; Mannella, L.; Regano, L.; Basile, C. Security at the Edge for Resource-Limited IoT Devices. Sensors 2024, 24, 590. [Google Scholar] [CrossRef] [PubMed]
- Obaidat, M.A.; Rawashdeh, M.; Alja’afreh, M.; Abouali, M.; Thakur, K.; Karime, A. Exploring IoT and Blockchain: A Comprehensive Survey on Security, Integration Strategies, Applications and Future Research Directions. Big Data and Cognitive Computing 2024, 8, 174. [Google Scholar] [CrossRef]
- Albarrak, K.M. Securing the Future of Web-Enabled IoT: A Critical Analysis of Web of Things Security. Applied Sciences 2024, 14, 10867. [Google Scholar] [CrossRef]
- Singh, N.; Buyya, R.; Kim, H. Securing Cloud-Based Internet of Things: Challenges and Mitigations. Sensors 2025, 25, 79. [Google Scholar] [CrossRef] [PubMed]
- Kaur, N.; Gupta, L. Securing the 6G–IoT Environment: A Framework for Enhancing Transparency in Artificial Intelligence Decision-Making Through Explainable Artificial Intelligence. Sensors 2025, 25, 854. [Google Scholar] [CrossRef]
- AlQahtani, A.A.S.; Sulaiman, M.; Alshayeb, T.; Alamleh, H. From Inception to Innovation: A Comprehensive Review and Bibliometric Analysis of IoT-Enabled Fire Safety Systems. Safety 2025, 11, 41. [Google Scholar] [CrossRef]
- Stergiou, C.L.; Plageras, A.P.; Memos, V.A.; Koidou, M.P.; Psannis, K.E. Secure Monitoring System for IoT Healthcare Data in the Cloud. Applied Sciences 2024, 14, 120. [Google Scholar] [CrossRef]
- Gómez-Marín, E.; Martintoni, D.; Senni, V.; Castillo, E.; Parrilla, L. Fine-Grained Access Control with User Revocation in Smart Manufacturing. Electronics 2023, 12, 2843. [Google Scholar] [CrossRef]
- Simian, D.; Ticleanu, O.A.; Constantinescu, N. Deterministic Systems for Cryptographic Primitives Used in Security Models in Particular IoT Configurations. Applied Sciences 2025, 15, 3048. [Google Scholar] [CrossRef]
- Gaina, L.; Stangaciu, C.S.; Stanescu, D.; Gusita, B.; Micea, M.V. Unidirectional Communications in Secure IoT Systems—A Survey. Sensors 2024, 24, 7528. [Google Scholar] [CrossRef]
- Soto-Cruz, J.; Ruiz-Ibarra, E.; Vázquez-Castillo, J.; Espinoza-Ruiz, A.; Castillo-Atoche, A.; Mass-Sanchez, J. A Survey of Efficient Lightweight Cryptography for Power-Constrained Microcontrollers. Technologies 2025, 13, 3. [Google Scholar] [CrossRef]
- Dauda, A.; Flauzac, O.; Nolot, F. A Survey on IoT Application Architectures. Sensors 2024, 24, 5320. [Google Scholar] [CrossRef] [PubMed]
- Enaya, A.; Fernando, X.; Kashef, R. Survey of Blockchain-Based Applications for IoT. Applied Sciences 2025, 15, 4562. [Google Scholar] [CrossRef]
- Arif, T.; Jo, B.; Park, J.H. A Comprehensive Survey of Privacy-Enhancing and Trust-Centric Cloud-Native Security Techniques Against Cyber Threats. Sensors 2025, 25, 2350. [Google Scholar] [CrossRef]
- Almarri, S.; Aljughaiman, A. Blockchain Technology for IoT Security and Trust: A Comprehensive SLR. Sustainability 2024, 16, 10177. [Google Scholar] [CrossRef]
- Bakhshi, T.; Ghita, B.; Kuzminykh, I. A Review of IoT Firmware Vulnerabilities and Auditing Techniques. Sensors 2024, 24, 708. [Google Scholar] [CrossRef] [PubMed]
- Wu, L.; Zhang, L.; Chen, K. Machine Learning-Based Security Solutions for IoT Networks: A Survey. Sensors 2024, 25, 3341. [Google Scholar] [CrossRef]
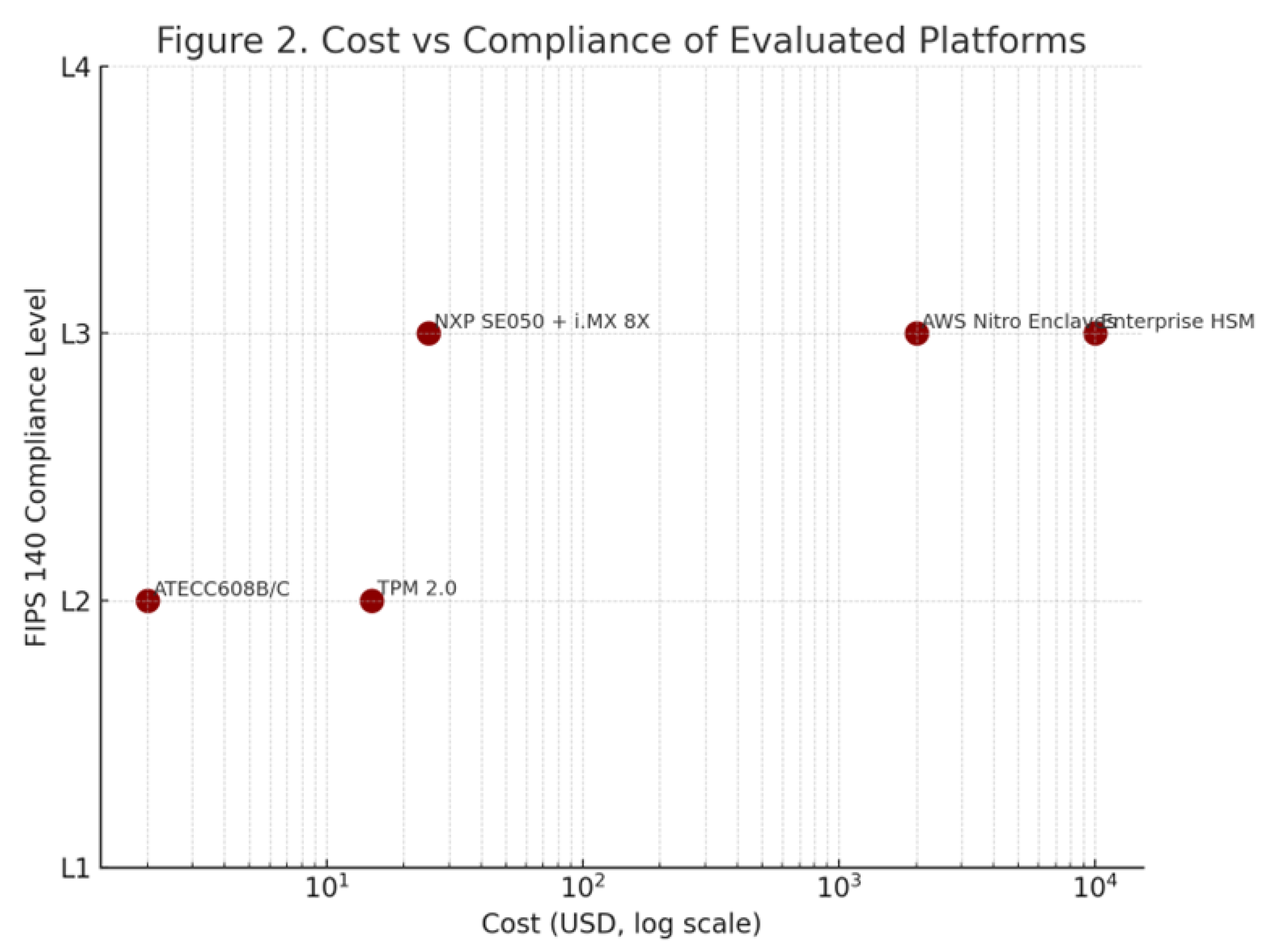
| Platform | Unit Cost (Eur) | Integration Difficulty | Compliance Level (/5) | Remarks |
|---|---|---|---|---|
| ATECC608B/C | 1 - 2 | Easy | 4.0 | Low - cost, ideal for IoT and embedded devices. |
| TPM 2.0 (Infineon) | 5 - 10 | Easy - Medium | 5.0 | Mature standard for PCs and servers; strong tamper protection. |
| NXP i.MX 8X + SE050 | 25 - 40 | Medium - Complex | 4.5 | High - end embedded systems with strong certification. |
| AWS Nitro Enclaves | Pay - as - you - go | Complex (Cloud) | 4.5 | Cloud - grade security; cost varies with usage. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).




