Submitted:
11 February 2026
Posted:
13 February 2026
Read the latest preprint version here
Abstract
Keywords:
1. Introduction
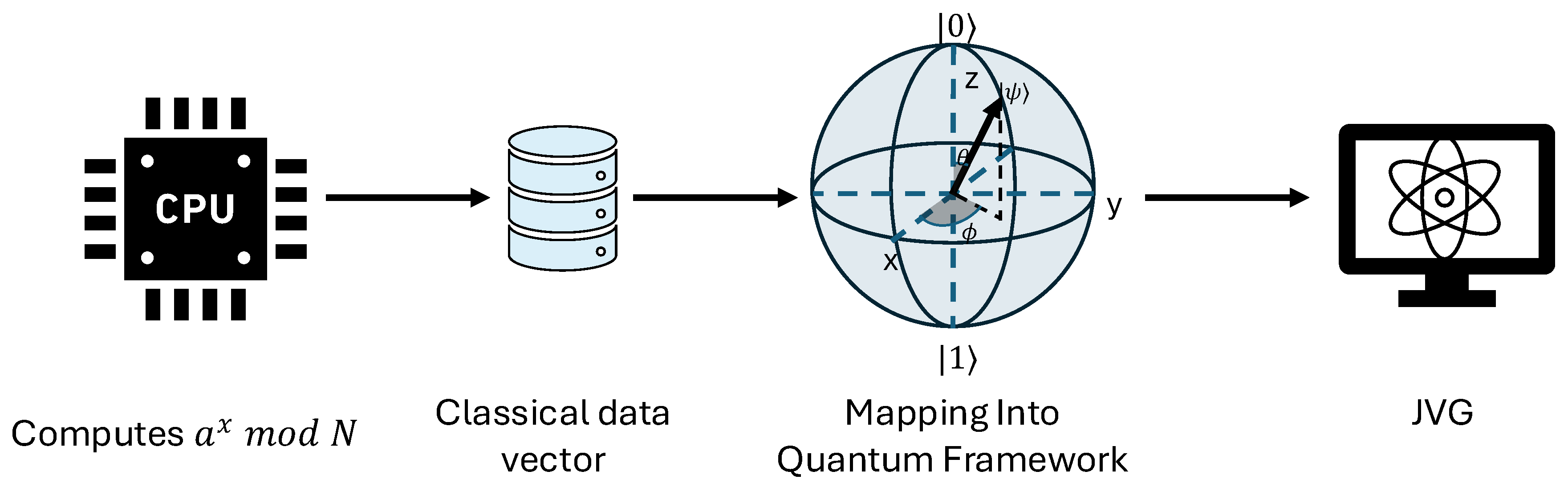
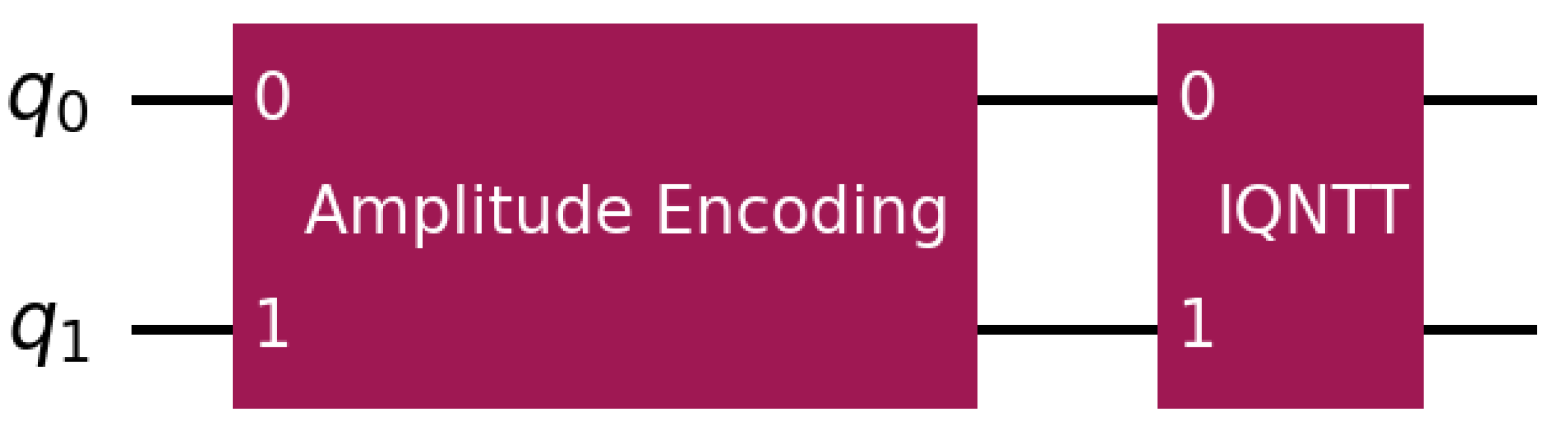
2. Methodology
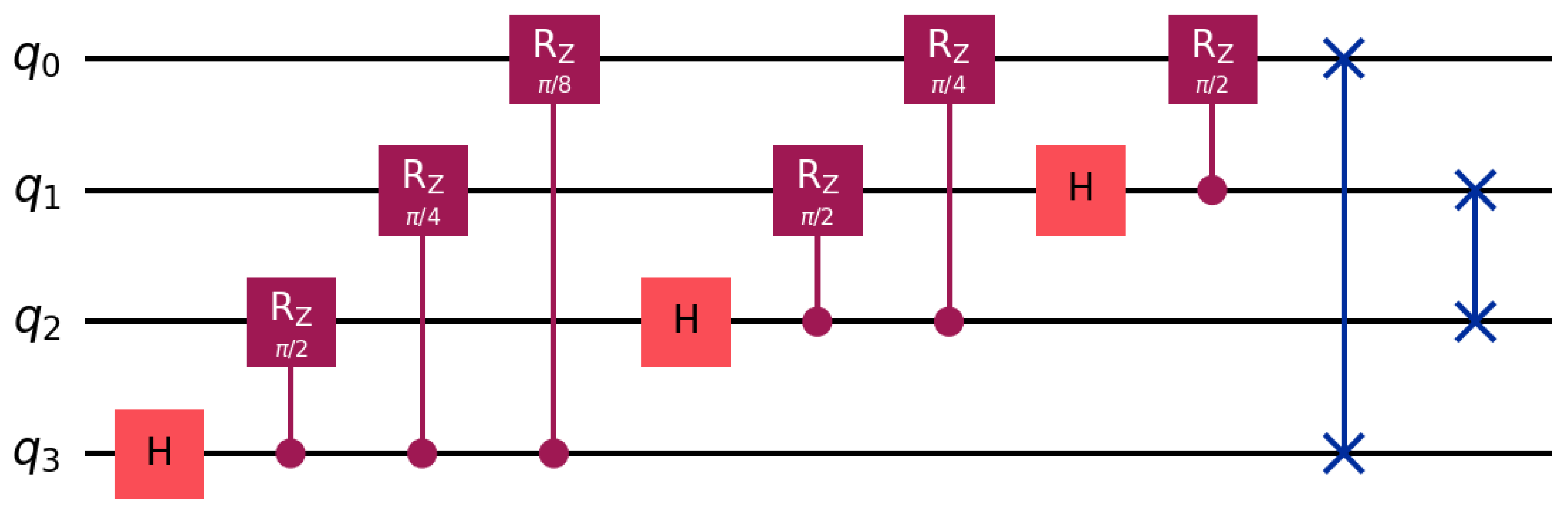
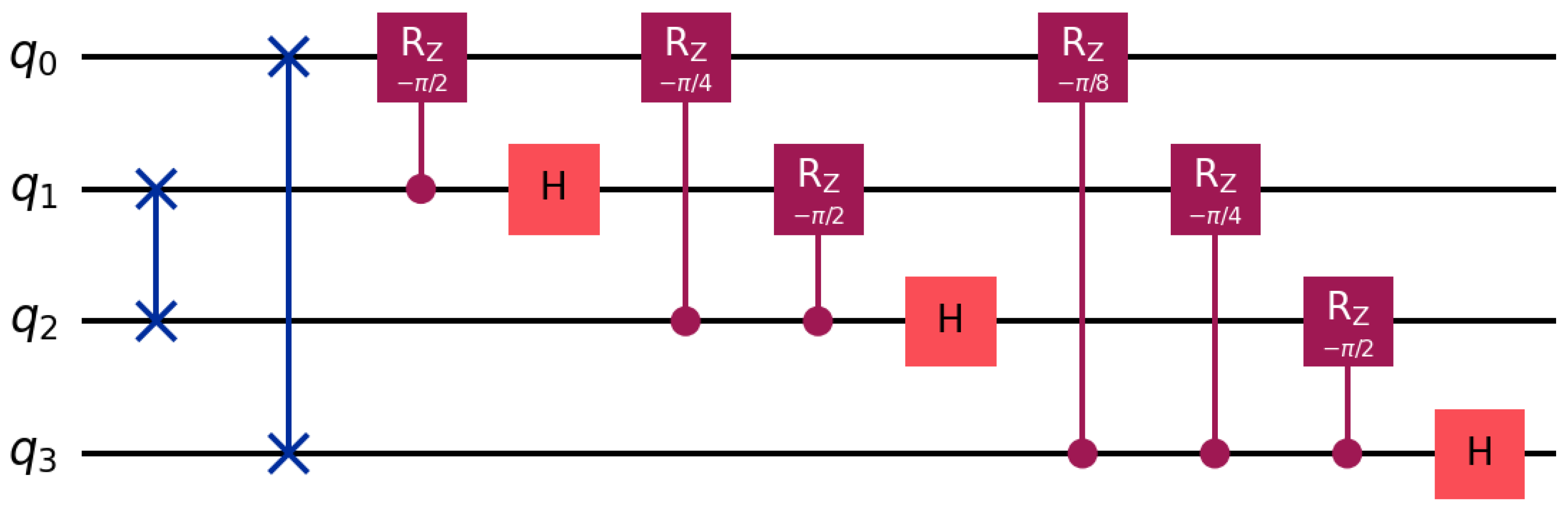
2.1. Quantum Fourier Transform
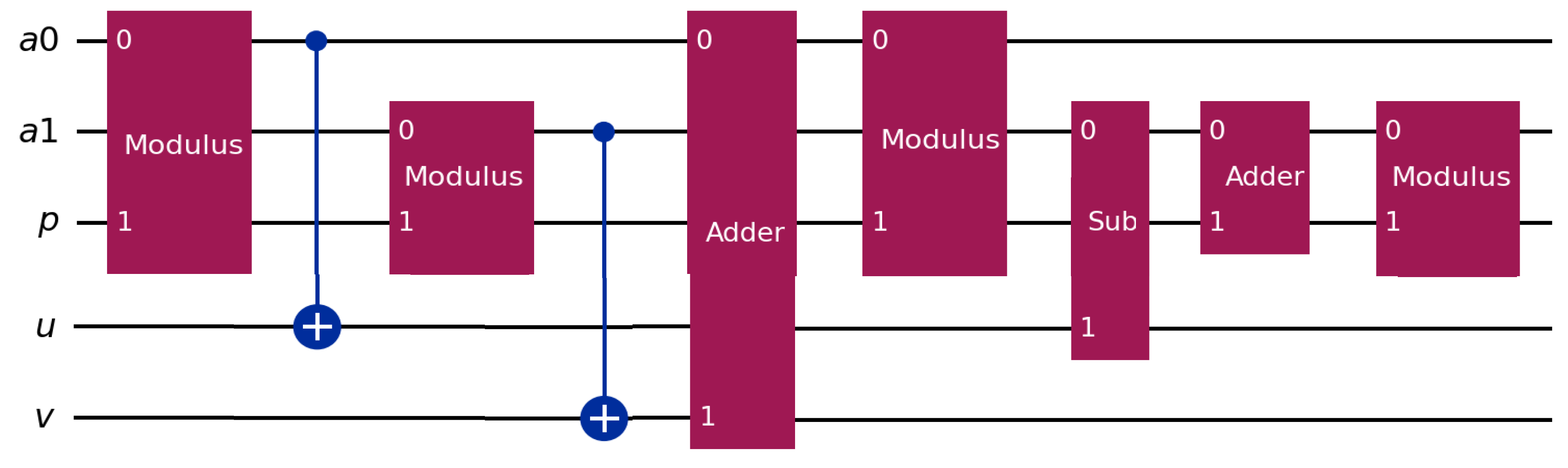
2.2. Number Theoretic Transform
2.3. Quantum Number Theoretic Transform
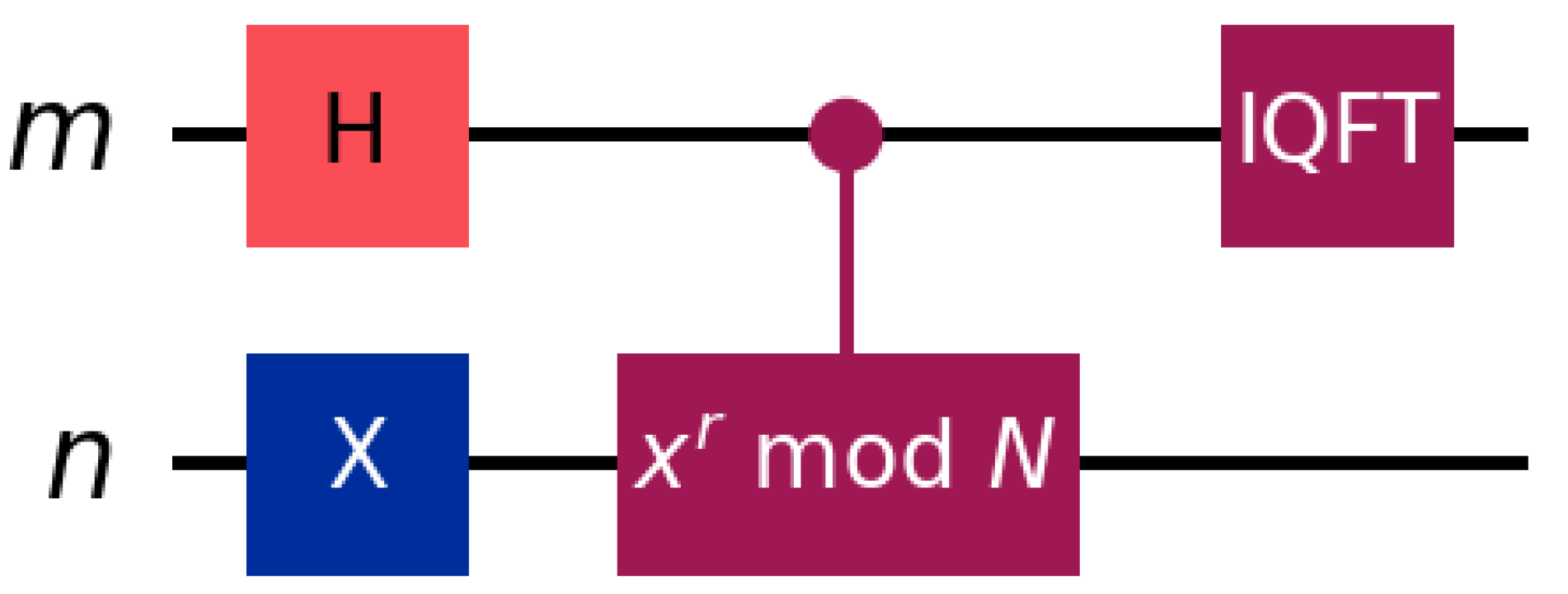
2.4. Shor’s Algorithm
2.5. The New Proposed Algorithm
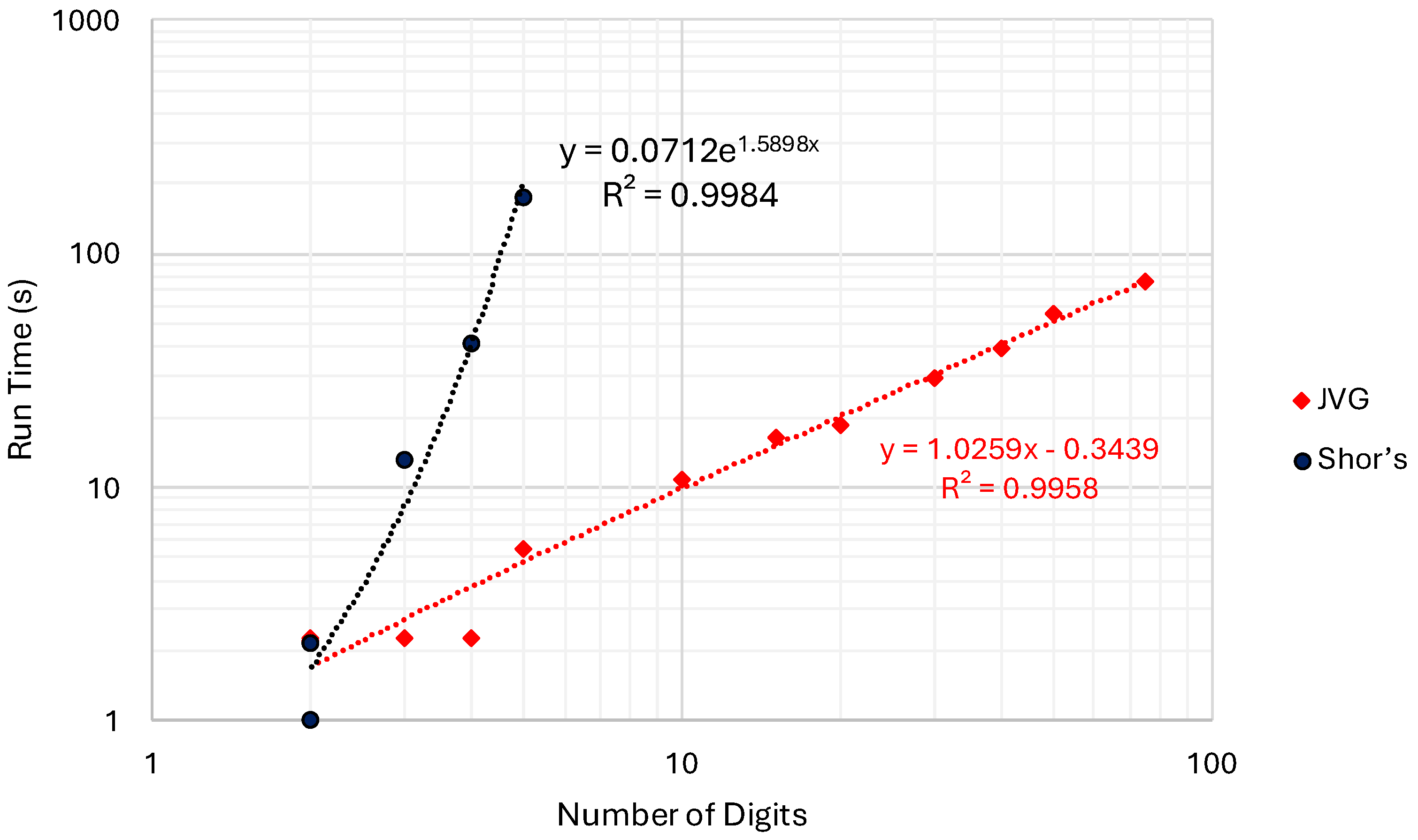
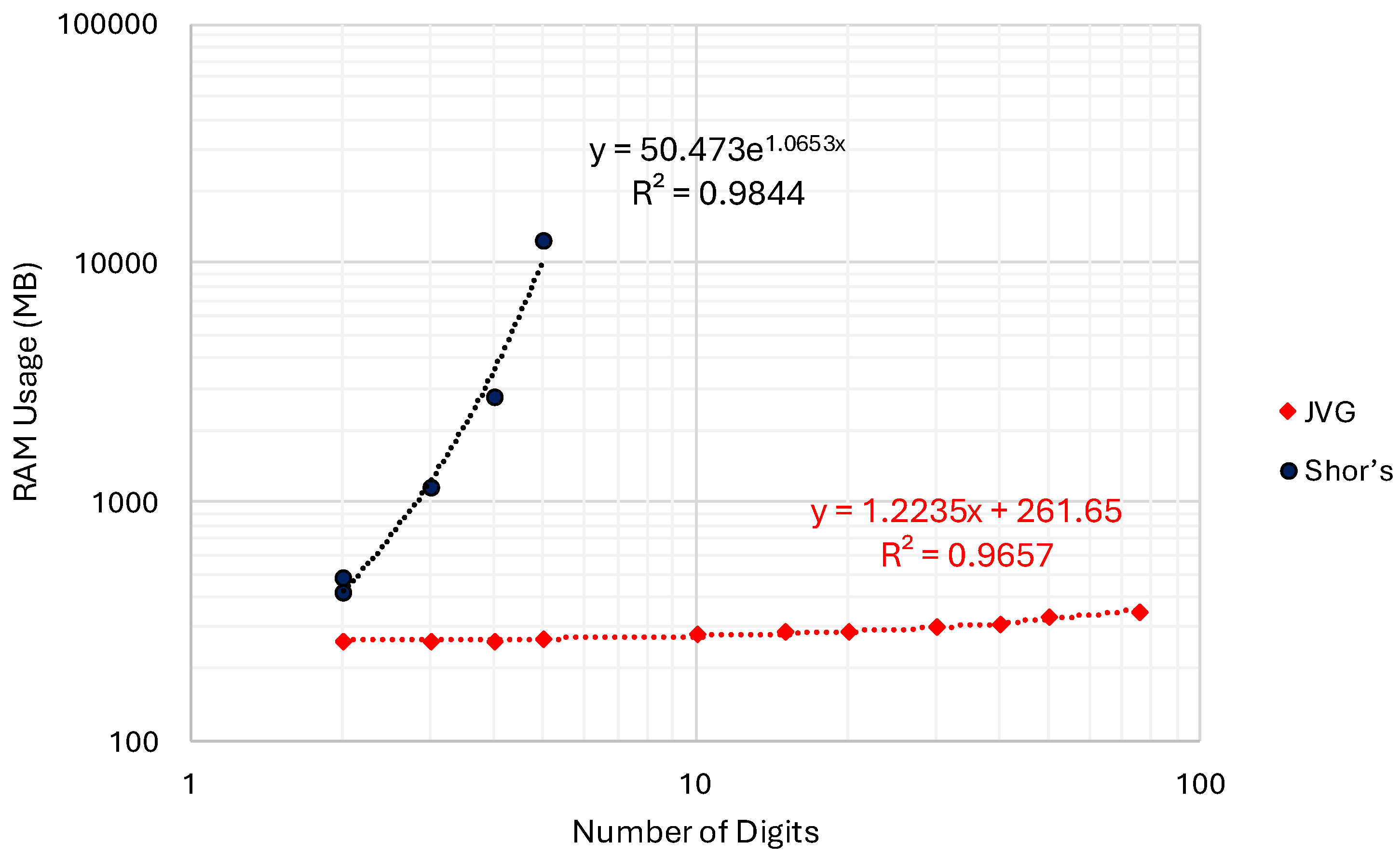
3. Results
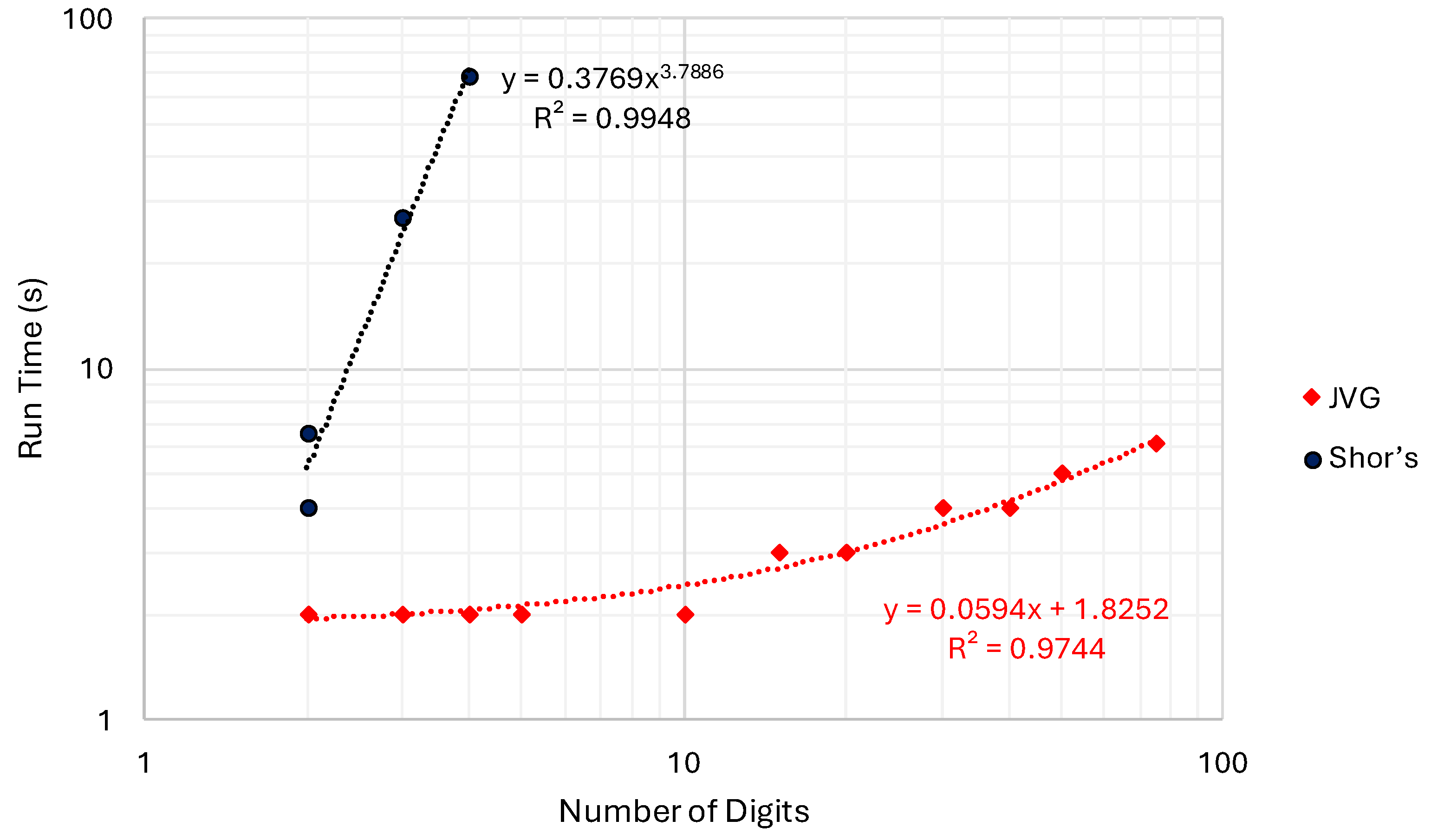
3.1. Results for Quantum Simulation
3.2. Results for Implementation on a Real Quantum Hardware
3.3. Projections for RSA Relevant Scenario
4. Discussion
4.1. Implications of Simulated Results for JVG’s Algorithm
4.2. Implications of Experimental Quantum Results for the JVG Algorithm
4.3. Implications of the Projected Values for RSA Relevant Scenario
4.4. Statistical Consistency and Implications on NISQ Hardware Devices
4.5. Impact of Classical Modular Exponentiation and QNTT-Based Period Finding
5. Conclusion
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Dam, D.-T.; Tran, T.-H.; Hoang, V.-P.; Pham, C.-K.; Hoang, T.-T. A Survey of Post-Quantum Cryptography: Start of a New Race. Cryptography 2023, 7, 40. [Google Scholar] [CrossRef]
- Baseri, Y.; Chouhan, V.; Hafid, A. Navigating Quantum Security Risks in Networked Environments: A Comprehensive Study of Quantum-Safe Network Protocols. Comput. Secur. 2024, 142, 103883. [Google Scholar] [CrossRef]
- McKinsey & Company Quantum Technology Monitor 2025: From Concept to Reality; McKinsey & Company, 2025.
- Kshetri, N. Monetizing Quantum Computing. IT Prof. 2024, 26, 10–15. [Google Scholar] [CrossRef]
- Cap, Companies Market. IonQ Market Capitalization. Available online: https://companiesmarketcap.com/ionq/marketcap/ (accessed on 30 September 2025).
- Sun, L. Better Quantum Computing Stock: D-Wave Quantum vs. IonQ. Available online: https://www.fool.com/investing/2025/09/24/better-quantum-computing-stock-d-wave-vs-ionq/ (accessed on 30 September 2025).
- The Motley Fool A Once-in-a-Decade Opportunity: 10 Billion Reasons to Pay Attention to This Monster Quantum Computing Company (Hint: Not IonQ). Available online: https://www.theglobeandmail.com/investing/markets/stocks/JPM-N/pressreleases/34998073/a-once-in-a-decade-opportunity-10-billion-reasons-to-pay-attention-to-this-monster-quantum-computing-company-hint-not-ionq/ (accessed on 30 September 2025).
- Bunescu, L.; Vârtei, A.M. Modern Finance through Quantum Computing—A Systematic Literature Review. PLOS ONE 2024, 19, e0304317. [Google Scholar] [CrossRef]
- Zhou, J. Quantum Finance: Exploring the Implications of Quantum Computing on Financial Models. Comput. Econ. 2025. [Google Scholar] [CrossRef]
- Camino, B.; Buckeridge, J.; Warburton, P.A.; Kendon, V.; Woodley, S.M. Quantum Computing and Materials Science: A Practical Guide to Applying Quantum Annealing to the Configurational Analysis of Materials. J. Appl. Phys. 2023, 133, 221102. [Google Scholar] [CrossRef]
- Guo, Z.; Li, R.; He, X.; Guo, J.; Ju, S. Harnessing Quantum Power: Revolutionizing Materials Design through Advanced Quantum Computation. Mater. Genome Eng. Adv. 2024, 2, e73. [Google Scholar] [CrossRef]
- Weidman, J.D.; Sajjan, M.; Mikolas, C.; Stewart, Z.J.; Pollanen, J.; Kais, S.; Wilson, A.K. Quantum Computing and Chemistry. Cell Rep. Phys. Sci. 2024, 5, 102105. [Google Scholar] [CrossRef]
- Li, W.; Yin, Z.; Li, X.; Ma, D.; Yi, S.; Zhang, Z.; Zou, C.; Bu, K.; Dai, M.; Yue, J.; et al. A Hybrid Quantum Computing Pipeline for Real World Drug Discovery. Sci. Rep. 2024, 14, 16942. [Google Scholar] [CrossRef]
- Patra, D.; Rajagopalan, N. Integration of Emerging Technologies in Cybersecurity for Healthcare: A Systematic Review. Comput. Secur. 2026, 161, 104763. [Google Scholar] [CrossRef]
- Oliveira Santos, V.; Marinho, F.P.; Costa Rocha, P.A.; Thé, J.V.G.; Gharabaghi, B. Application of Quantum Neural Network for Solar Irradiance Forecasting: A Case Study Using the Folsom Dataset, California. Energies 2024, 17, 3580. [Google Scholar] [CrossRef]
- Oliveira Santos, V.; Costa Rocha, P.A.; Thé, J.V.G.; Gharabaghi, B. Optimizing the Architecture of a Quantum–Classical Hybrid Machine Learning Model for Forecasting Ozone Concentrations: Air Quality Management Tool for Houston, Texas. Atmosphere 2025, 16, 255. [Google Scholar] [CrossRef]
- Prasad, N.; Diro, A.; Warren, M.; Fernando, M. A Survey of Cyber Threat Attribution: Challenges, Techniques, and Future Directions. Comput. Secur. 2025, 157, 104606. [Google Scholar] [CrossRef]
- Abbasi, M.; Cardoso, F.; Váz, P.; Silva, J.; Martins, P. A Practical Performance Benchmark of Post-Quantum Cryptography Across Heterogeneous Computing Environments. Cryptography 2025, 9, 32. [Google Scholar] [CrossRef]
- Baseri, Y.; Chouhan, V.; Ghorbani, A.; Chow, A. Evaluation Framework for Quantum Security Risk Assessment: A Comprehensive Strategy for Quantum-Safe Transition. Comput. Secur. 2025, 150, 104272. [Google Scholar] [CrossRef]
- Shor, P.W. Algorithms for Quantum Computation: Discrete Logarithms and Factoring. In Proceedings of the Proceedings 35th Annual Symposium on Foundations of Computer Science, November 1994; pp. 124–134. [Google Scholar]
- Coppersmith, D. An Approximate Fourier Transform Useful in Quantum Factoring 2002.
- Lipton, R.J.; Regan, K.W. Quantum Algorithms via Linear Algebra: A Primer; MIT Press, 2014; ISBN 978-0-262-32357-4. [Google Scholar]
- Amirkhanova, D.S.; Iavich, M.; Mamyrbayev, O. Lattice-Based Post-Quantum Public Key Encryption Scheme Using ElGamal’s Principles. Cryptography 2024, 8, 31. [Google Scholar] [CrossRef]
- Liang, X.; Xu, Y. A Novel Framework to Identify Cybersecurity Challenges and Opportunities for Organizational Digital Transformation in the Cloud. Comput. Secur. 2025, 151, 104339. [Google Scholar] [CrossRef]
- Meter, R.V.; Itoh, K.M. Fast Quantum Modular Exponentiation. Phys. Rev. A 2005, 71, 052320. [Google Scholar] [CrossRef]
- Markov, I.L.; Saeedi, M. Constant-Optimized Quantum Circuits for Modular Multiplication and Exponentiation. Quantum Info Comput 2012, 12, 361–394. [Google Scholar] [CrossRef]
- Ekerå, M. Modifying Shor’s Algorithm to Compute Short Discrete Logarithms 2016.
- Ekerå, M.; Håstad, J. Quantum Algorithms for Computing Short Discrete Logarithms and Factoring RSA Integers. In Proceedings of the Post-Quantum Cryptography; Lange, T., Takagi, T., Eds.; Springer International Publishing: Cham, 2017; pp. 347–363. [Google Scholar]
- Chevignard, C.; Fouque, P.-A.; Schrottenloher, A. Reducing the Number of Qubits in Quantum Factoring 2024.
- Gidney, C. How to Factor 2048 Bit RSA Integers with Less than a Million Noisy Qubits 2025, arXiv:2505.15917.
- Xu, N.; Zhu, J.; Lu, D.; Zhou, X.; Peng, X.; Du, J. Quantum Factorization of 143 on a Dipolar-Coupling NMR System. Phys. Rev. Lett. 2012, 109, 269902. [Google Scholar] [CrossRef]
- Pal, S.; Moitra, S.; Anjusha, V.S.; Kumar, A.; Mahesh, T.S. Hybrid Scheme for Factorisation: Factoring 551 Using a 3-Qubit NMR Quantum Adiabatic Processor. Pramana 2019, 92, 26. [Google Scholar] [CrossRef]
- Saxena, A.; Shukla, A.; Pathak, A. A Hybrid Scheme for Prime Factorization and Its Experimental Implementation Using IBM Quantum Processor. Quantum Inf. Process. 2021, 20, 112. [Google Scholar] [CrossRef]
- Brigham, E.O. The Fast Fourier Transform and Its Applications; Prentice Hall, 1988; ISBN 978-0-13-307505-2. [Google Scholar]
- Nussbaumer, H.J. Fast Fourier Transform and Convolution Algorithms; Springer Science & Business Media, 2012; ISBN 978-3-642-81897-4. [Google Scholar]
- Satriawan, A.; Syafalni, I.; Mareta, R.; Anshori, I.; Shalannanda, W.; Barra, A. Conceptual Review on Number Theoretic Transform and Comprehensive Review on Its Implementations. IEEE Access 2023, 11, 70288–70316. [Google Scholar] [CrossRef]
- Gyongyosi, L.; Imre, S. A Survey on Quantum Computing Technology. Comput. Sci. Rev. 2019, 31, 51–71. [Google Scholar] [CrossRef]
- Bharti, K.; Cervera-Lierta, A.; Kyaw, T.H.; Haug, T.; Alperin-Lea, S.; Anand, A.; Degroote, M.; Heimonen, H.; Kottmann, J.S.; Menke, T.; et al. Noisy Intermediate-Scale Quantum Algorithms. Rev. Mod. Phys. 2022, 94, 015004. [Google Scholar] [CrossRef]
- Kan, S.; Li, Y.; Wang, H.; Mouradian, S.; Mao, Y. Circuit Folding: Modular and Qubit-Level Workload Management in Quantum-Classical Systems 2024.
- Tomčala, J. On the Various Ways of Quantum Implementation of the Modular Exponentiation Function for Shor’s Factorization. Int. J. Theor. Phys. 2024, 63, 14. [Google Scholar] [CrossRef]
- Brunton, S.L.; Kutz, J.N. Data-Driven Science and Engineering: Machine Learning, Dynamical Systems, and Control; Cambridge University Press, 2022; ISBN 978-1-009-09848-9. [Google Scholar]
- Cormen, T.H.; Leiserson, C.E.; Rivest, R.L.; Stein, C. Introduction to Algorithms, Third Edition; MIT Press, 2009; ISBN 978-0-262-03384-8. [Google Scholar]
- Nielsen, M.A.; Chuang, I.L. Quantum Computation and Quantum Information, 10th anniversary ed.; Cambridge University Press: Cambridge; New York, 2010; ISBN 978-1-107-00217-3. [Google Scholar]
- Schuld, M.; Petruccione, F. Machine Learning with Quantum Computers; Springer Nature, 2021; ISBN 978-3-030-83098-4. [Google Scholar]
- Sutor, R.S. Dancing with Qubits: How Quantum Computing Works and How It May Change the World; Expert insight; Packt: Birmingham Mumbai, 2019; ISBN 978-1-83882-736-6. [Google Scholar]
- Cohn, P.M. Introduction to Ring Theory; Springer Science & Business Media, 2012; ISBN 978-1-4471-0475-9. [Google Scholar]
- Nussbaumer, H.J. Fast Fourier Transform and Convolution Algorithms; Springer Series in Information Sciences; Springer Berlin Heidelberg: Berlin, Heidelberg, 1982; Vol. 2, ISBN 978-3-540-11825-1. [Google Scholar]
- Satriawan, A.; Mareta, R.; Lee, H. A Complete Beginner Guide to the Number Theoretic Transform (NTT) 2024.
- Gentleman, W.M.; Sande, G. Fast Fourier Transforms: For Fun and Profit. In Proceedings of the Proceedings of the November 7-10, 1966, fall joint computer conference on XX - AFIPS ’66 (Fall), 1966; ACM Press: San Francisco, California; p. 563. [Google Scholar]
- Cooley, J.W.; Tukey, J.W. An Algorithm for the Machine Calculation of Complex Fourier Series. Math. Comput. 1965, 19, 297–301. [Google Scholar] [CrossRef]
- Lu, C.; Kundu, S.; Kuruvila, A.; Ravichandran, S.M.; Basu, K. Design and Logic Synthesis of a Scalable, Efficient Quantum Number Theoretic Transform. In Proceedings of the Proceedings of the ACM/IEEE International Symposium on Low Power Electronics and Design, August 2022; ACM: Boston MA USA; pp. 1–6. [Google Scholar]
- Draper, T.G. Addition on a Quantum Computer 2000.
- Thapliyal, H. Mapping of Subtractor and Adder-Subtractor Circuits on Reversible Quantum Gates; 2016; Vol. 9570, pp. 10–34. ISBN 978-3-662-50411-6. [Google Scholar]
- Ruiz-Perez, L.; Garcia-Escartin, J.C. Quantum Arithmetic with the Quantum Fourier Transform. Quantum Inf. Process. 2017, 16, 152. [Google Scholar] [CrossRef]
- Thapliyal, H.; MuÑoz-Coreas, E.; Varun, T.S.S.; Humble, T.S. Quantum Circuit Designs of Integer Division Optimizing T-Count and T-Depth. IEEE Trans. Emerg. Top. Comput. 2021, 9, 1045–1056. [Google Scholar] [CrossRef]
- Arute, F.; Arya, K.; Babbush, R.; Bacon, D.; Bardin, J.C.; Barends, R.; Biswas, R.; Boixo, S.; Brandao, F.G.S.L.; Buell, D.A.; et al. Quantum Supremacy Using a Programmable Superconducting Processor. Nature 2019, 574, 505–510. [Google Scholar] [CrossRef]
- AbuGhanem, M.; Eleuch, H. NISQ Computers: A Path to Quantum Supremacy. IEEE Access 2024, 12, 102941–102961. [Google Scholar] [CrossRef]
- Preskill, J. Quantum Computing in the NISQ Era and Beyond. Quantum 2018, 2, 79. [Google Scholar] [CrossRef]
- King, A.D.; Nocera, A.; Rams, M.M.; Dziarmaga, J.; Wiersema, R.; Bernoudy, W.; Raymond, J.; Kaushal, N.; Heinsdorf, N.; Harris, R.; et al. Beyond-Classical Computation in Quantum Simulation. Science 2025, 388, 199–204. [Google Scholar] [CrossRef]
- Chenu, M. Quantum Emulators: CPU, Single GPU and Multiple GPUs Performance Comparison. Procedia Comput. Sci. 2025, 267, 218–226. [Google Scholar] [CrossRef]
- Qiskit Shor’s Factoring Algorithm. Available online: https://github.com/Qiskit/qiskit/blob/stable/0.18/qiskit/algorithms/factorizers/shor.py (accessed on 29 September 2025).
- AbuGhanem, M. IBM Quantum Computers: Evolution, Performance, and Future Directions. J. Supercomput. 2025, 81, 687. [Google Scholar] [CrossRef]
- Aghaee Rad, H.; Ainsworth, T.; Alexander, R.N.; Altieri, B.; Askarani, M.F.; Baby, R.; Banchi, L.; Baragiola, B.Q.; Bourassa, J.E.; Chadwick, R.S.; et al. Scaling and Networking a Modular Photonic Quantum Computer. Nature 2025, 638, 912–919. [Google Scholar] [CrossRef] [PubMed]
- Jones, T.; Brown, A.; Bush, I.; Benjamin, S.C. QuEST and High Performance Simulation of Quantum Computers. Sci. Rep. 2019, 9, 10736. [Google Scholar] [CrossRef]
- Guerreschi, G.G. Fast Simulation of Quantum Algorithms Using Circuit Optimization. Quantum 2022, 6, 706. [Google Scholar] [CrossRef]
- Willsch, D.; Willsch, M.; Jin, F.; De Raedt, H.; Michielsen, K. Large-Scale Simulation of Shor’s Quantum Factoring Algorithm. Mathematics 2023, 11, 4222. [Google Scholar] [CrossRef]
- Evered, S.J.; Bluvstein, D.; Kalinowski, M.; Ebadi, S.; Manovitz, T.; Zhou, H.; Li, S.H.; Geim, A.A.; Wang, T.T.; Maskara, N.; et al. High-Fidelity Parallel Entangling Gates on a Neutral-Atom Quantum Computer. Nature 2023, 622, 268–272. [Google Scholar] [CrossRef]
- Huang, J.Y.; Su, R.Y.; Lim, W.H.; Feng, M.; van Straaten, B.; Severin, B.; Gilbert, W.; Dumoulin Stuyck, N.; Tanttu, T.; Serrano, S.; et al. High-Fidelity Spin Qubit Operation and Algorithmic Initialization above 1 K. Nature 2024, 627, 772–777. [Google Scholar] [CrossRef]
- Gidney, C.; Ekerå, M. How to Factor 2048 Bit RSA Integers in 8 Hours Using 20 Million Noisy Qubits. Quantum 2021, 5, 433. [Google Scholar] [CrossRef]
- Shor, P.W. Polynomial-Time Algorithms for Prime Factorization and Discrete Logarithms on a Quantum Computer. SIAM J. Comput. 1997, 26, 1484–1509. [Google Scholar] [CrossRef]
| RAM (GB) | CPU | GPU |
| 32 | 13th Generation i7 | RTX 4080 16 GB |
|
Number of Digits |
Tested Using Shor’s Algorithm | Tested Using JVG’s Algorithm |
| 2 | Solved | Solved |
| 3 | Solved | Solved |
| 4 | Solved | Solved |
| 5 | Solved | Solved |
| 10 | Not Capable | Solved |
| 15 | Not Capable | Solved |
| 20 | Not Capable | Solved |
| 30 | Not Capable | Solved |
| 40 | Not Capable | Solved |
| 50 | Not Capable | Solved |
| 75 | Not Capable | Solved |
| Algorithm | Number of digits (qubits) |
Run Time (s) |
RAM Usage (MB) |
CX | U | |
| Shor’s | 2 (18) | 1.01 ± 0.01 | 419 ± 1.22 | 10541 ± 7 | 13971 ± 10 | |
| JVG | 2 (6) | 2.20 ± 0.27 | 261 ± 2.46 | 552 ± 0 | 657 ± 0 | |
| Shor’s | 2 (22) | 2.15 ± 0.02 | 488 ± 7.61 | 21840 ± 6 | 29448 ± 18 | |
| JVG | 2 (6) | 2.26 ± 0.05 | 260 ± 0.38 | 552 ± 0 | 657 ± 0 | |
| Shor’s | 3 (34) | 13.16 ± 0.13 | 1159 ± 10.30 | 109994 ± 9 | 153827 ± 40 | |
| JVG | 3 (6) | 2.26 ± 0.05 | 261 ± 0.5 | 552 ± 0 | 657 ± 0 | |
| Shor’s | 4 (46) | 40.91 ± 0.63 | 2794 ± 26.30 | 344116 ± 12 | 490193 ± 42 | |
| JVG | 4 (6) | 2.24 ± 0.06 | 260 ± 0.66 | 552 ± 0 | 657 ± 0 | |
| Shor’s | 5 (70) | 174.11 ± 2.40 | 12505 ± 297.68 | 1713476 ± 16 | 2485724 ± 130 | |
| JVG | 5 (10) | 5.48 ± 0.14 | 267 ± 0.66 | 1720 ± 0 | 1975 ± 0 | |
| Shor’s | - | - | - | - | - | |
| JVG | 10 (16) | 10.70 ± 0.31 | 278 ± 0.72 | 3475 ± 0 | 3962 ± 2 | |
| Shor’s | - | - | - | - | - | |
| JVG | 15 (22) | 16.43 ± 0.56 | 289 ± 0.59 | 5238 ± 0 | 5958 ± 1 | |
| Shor’s | - | - | - | - | - | |
| JVG | 20 (24) | 18.57 ± 0.83 | 289 ± 2.03 | 5821 ± 0 | 6618 ± 0 | |
| Shor’s | - | - | - | - | - | |
| JVG | 30 (34) | 28.98 ± 0.90 | 303 ± 3.93 | 8736 ± 0 | 9918 ± 0 | |
| Shor’s | - | - | - | - | - | |
| JVG | 40 (42) | 39.19 ± 0.92 | 312 ± 1.01 | 11098 ± 0 | 12590 ± 0 | |
| Shor’s | - | - | - | - | - | |
| JVG | 50 (54) | 54.49 ± 0.98 | 328 ± 3.31 | 14596 ± 0 | 16550 ± 0 | |
| Shor’s | - | - | - | - | - | |
| JVG | 75 (70) | 75.69 ± 1.46 | 345 ± 1.49 | 19322 ± 0 | 21894 ± 0 | |
| Average Coefficient of Variation | Shor’s | 1.17% | 1.21% | 0.02% | 0.03% | |
| JVG | 5.53% | 0.50% | 0.00% | 0.00% | ||
| Algorithm | Number of digits (qubits) |
QR (s) |
SX | CZ | RZ | ||
| Shor’s | 2 (18) | 4.0 ± 0 | 54390 ± 230 | 26444 ± 129 | 24761 ± 142 | ||
| JVG | 2 (6) | 2.00 ± 0 | 2019 ± 10 | 1023 ± 7 | 1350 ± 4 | ||
| Shor’s | 2 (22) | 6.5 ± 0.5 | 116626 ± 397 | 56942 ± 210 | 50738 ± 176 | ||
| JVG | 2 (6) | 2 ± 0 | 2014 ± 3 | 1020 ± 3 | 1351 ± 3 | ||
| Shor’s | 3 (34) | 26.8 ± 0.9 | 642895 ± 1098 | 314000 ± 536 | 254806 ± 456 | ||
| JVG | 3 (6) | 2 ± 0 | 2031 ± 3 | 1018 ± 4 | 1333 ± 8 | ||
| Shor’s | 4 (46) | 67.8 ± 2.5 | 2085030 ± 2554 | 1013958 ± 1468 | 805239 ± 1627 | ||
| JVG | 4 (6) | 2 ± 0 | 2013 ± 4 | 1019 ± 3 | 1350 ± 4 | ||
| Shor’s | 5 (70) | - | - | - | - | ||
| JVG | 5 (10) | 2 ± 0 | 6762 ± 84 | 3387 ± 47 | 4184 ± 21 | ||
| Shor’s | - | - | - | - | - | ||
| JVG | 10 (16) | 2 ± 0 | 14423 ± 118 | 7203 ± 61 | 8532 ± 62 | ||
| Shor’s | - | - | - | - | - | ||
| JVG | 15 (22) | 3 ± 0 | 22541 ± 255 | 11283 ± 129 | 12952 ± 62 | ||
| Shor’s | - | - | - | - | - | ||
| JVG | 20 (24) | 3 ± 0 | 25282 ± 197 | 12652 ± 97 | 14338 ± 75 | ||
| Shor’s | - | - | - | - | - | ||
| JVG | 30 (34) | 4 ± 0 | 39313 ± 228 | 19688 ± 150 | 21598 ± 69 | ||
| Shor’s | - | - | - | - | - | ||
| JVG | 40 (42) | 4 ± 0 | 50762 ± 355 | 25416 ± 170 | 27469 ± 97 | ||
| Shor’s | - | - | - | - | - | ||
| JVG | 50 (54) | 5 ± 0 | 68143 ± 1138 | 34134 ± 587 | 36130 ± 61 | ||
| Shor’s | - | - | - | - | - | ||
| JVG | 75 (70) | 6.1 ± 0.32 | 91734 ± 771 | 45951 ± 397 | 47823 ± 111 | ||
| Average Coefficient of Variation | Shor’s | 3.80% | 0.26% | 0.29% | 0.33% | ||
| JVG | 0.43% | 0.73% | 0.82% | 0.39% | |||
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




